| File name: | 2025-05-15_f394bfc47e2a1f6de9a5a58cb2fb2cc6_agent-tesla_amadey_black-basta_cobalt-strike_darkgate_elex_luca-stealer |
| Full analysis: | https://app.any.run/tasks/1b60e120-4049-4475-9c95-465bdcceaa88 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 15, 2025, 21:45:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | F394BFC47E2A1F6DE9A5A58CB2FB2CC6 |
| SHA1: | 9CA6C8887FE36B7648D98E622DA30C2E93904950 |
| SHA256: | DA5D51DC6506CED2D759A82E9D3F7710301A9577F6428036F29CABDF45F0719C |
| SSDEEP: | 49152:gPPkzemqoSut3Jh4+QQ/btosJwIA4hHmZlKH2Tw/Pq83zw0bCjvk9G661QGtBZXo:CP/mp7t3T4+B/btosJwIA4hHmZlKH2T1 |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2088)
Run PowerShell with an invisible window
- powershell.exe (PID: 7152)
- powershell.exe (PID: 7148)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7152)
- powershell.exe (PID: 7148)
AMADEY mutex has been found
- TempO7C8NSKNRTCA4EC3ENKTABTPGNNRKACJ.EXE (PID: 6240)
- ramez.exe (PID: 2268)
- ramez.exe (PID: 6824)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 7148)
- powershell.exe (PID: 7152)
Connects to the CnC server
- ramez.exe (PID: 2268)
- svchost.exe (PID: 2196)
AMADEY has been detected (SURICATA)
- ramez.exe (PID: 2268)
AMADEY has been detected (YARA)
- ramez.exe (PID: 2268)
Changes the autorun value in the registry
- 3rrAdmR.exe (PID: 4212)
GCLEANER has been detected (SURICATA)
- 0c0dedc7d6.exe (PID: 5380)
- ra02W4S.exe (PID: 6744)
Executing a file with an untrusted certificate
- j6J70wm.exe (PID: 2772)
- ra02W4S.exe (PID: 6744)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 6300)
- MSBuild.exe (PID: 6512)
LUMMA has been detected (YARA)
- MSBuild.exe (PID: 6300)
Application was injected by another process
- svchost.exe (PID: 5740)
- svchost.exe (PID: 6048)
Runs injected code in another process
- e5jg7MM.exe (PID: 6972)
LUMMA mutex has been found
- MSBuild.exe (PID: 6300)
- MSBuild.exe (PID: 6512)
VIDAR mutex has been found
- lcyqrsfDC9gwl.exe (PID: 976)
- MSBuild.exe (PID: 3300)
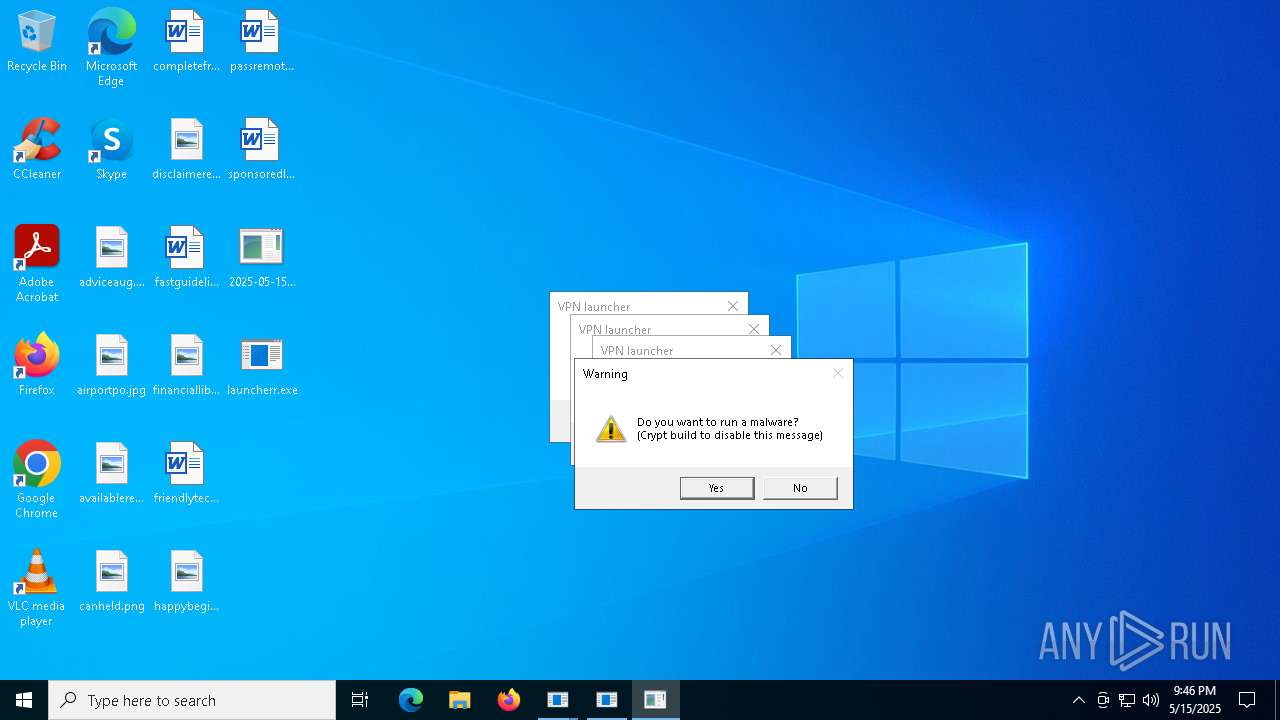
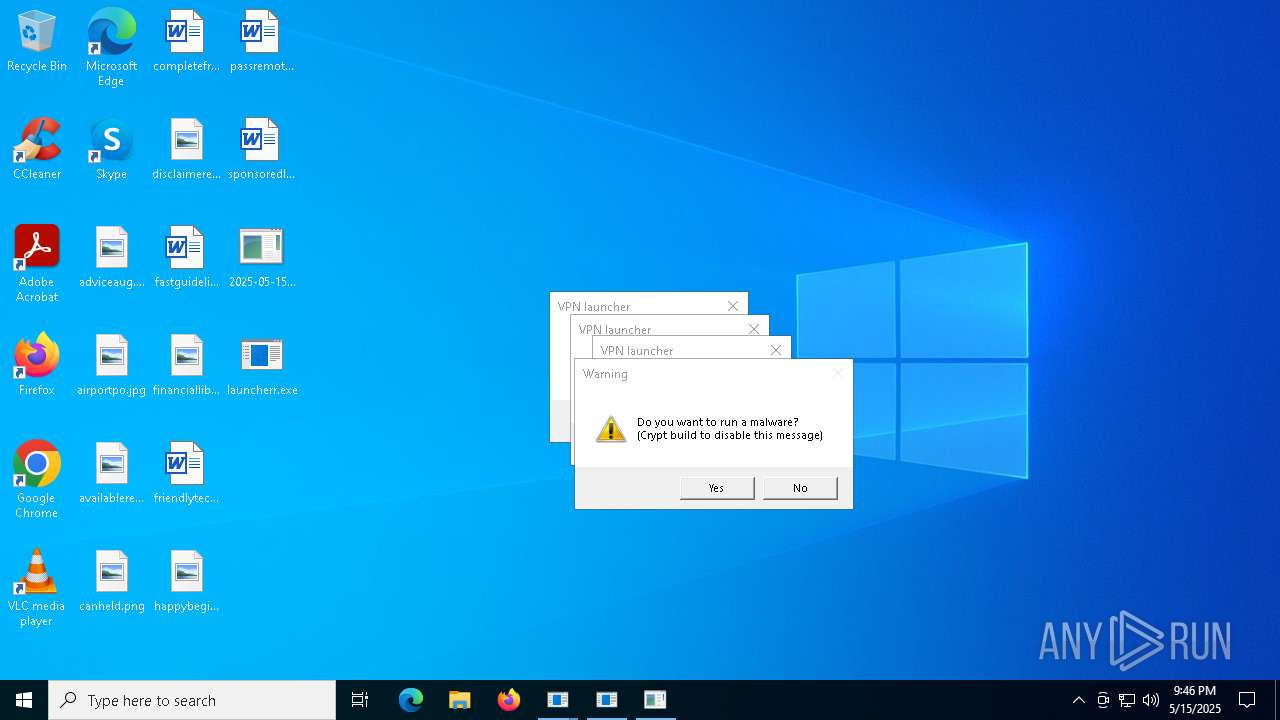
GENERIC has been found (auto)
- 0c0dedc7d6.exe (PID: 5380)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 2025-05-15_f394bfc47e2a1f6de9a5a58cb2fb2cc6_agent-tesla_amadey_black-basta_cobalt-strike_darkgate_elex_luca-stealer.exe (PID: 6872)
- 3rrAdmR.exe (PID: 4212)
- svchost.exe (PID: 6048)
Probably download files using WebClient
- mshta.exe (PID: 2244)
- mshta.exe (PID: 3888)
Starts process via Powershell
- powershell.exe (PID: 7152)
- powershell.exe (PID: 7148)
Manipulates environment variables
- powershell.exe (PID: 7152)
- powershell.exe (PID: 7148)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 2244)
- mshta.exe (PID: 3888)
- globalsynapse297.exe (PID: 3032)
- lcyqrsfDC9gwl.exe (PID: 976)
- globalsynapse297.exe (PID: 5596)
Found IP address in command line
- powershell.exe (PID: 7152)
- powershell.exe (PID: 7148)
Connects to the server without a host name
- powershell.exe (PID: 7152)
- powershell.exe (PID: 7148)
- ramez.exe (PID: 2268)
- 0c0dedc7d6.exe (PID: 5380)
- svchost.exe (PID: 6048)
- ra02W4S.exe (PID: 6744)
Process requests binary or script from the Internet
- powershell.exe (PID: 7152)
- powershell.exe (PID: 7148)
- ramez.exe (PID: 2268)
Executable content was dropped or overwritten
- powershell.exe (PID: 7152)
- TempO7C8NSKNRTCA4EC3ENKTABTPGNNRKACJ.EXE (PID: 6240)
- ramez.exe (PID: 2268)
- 3rrAdmR.exe (PID: 4212)
- 0c0dedc7d6.exe (PID: 5380)
- qUdcX6q8B8K.exe (PID: 6712)
- qUdcX6q8B8K.tmp (PID: 744)
- globalsynapse297.exe (PID: 5596)
- 7c30ae854e.exe (PID: 2096)
- 7c30ae854e.tmp (PID: 232)
- ra02W4S.exe (PID: 6744)
- MKQsy2OCVDQxh.exe (PID: 4776)
- MKQsy2OCVDQxh.tmp (PID: 3124)
Reads security settings of Internet Explorer
- ramez.exe (PID: 2268)
- TempO7C8NSKNRTCA4EC3ENKTABTPGNNRKACJ.EXE (PID: 6240)
- 0c0dedc7d6.exe (PID: 5380)
- globalsynapse297.exe (PID: 5596)
- ra02W4S.exe (PID: 6744)
- lcyqrsfDC9gwl.exe (PID: 976)
- 7c30ae854e.tmp (PID: 232)
Starts itself from another location
- TempO7C8NSKNRTCA4EC3ENKTABTPGNNRKACJ.EXE (PID: 6240)
Potential Corporate Privacy Violation
- powershell.exe (PID: 7148)
- ramez.exe (PID: 2268)
- powershell.exe (PID: 7152)
- 0c0dedc7d6.exe (PID: 5380)
- ra02W4S.exe (PID: 6744)
Contacting a server suspected of hosting an CnC
- ramez.exe (PID: 2268)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 6300)
- MSBuild.exe (PID: 6512)
There is functionality for enable RDP (YARA)
- ramez.exe (PID: 2268)
There is functionality for taking screenshot (YARA)
- ramez.exe (PID: 2268)
- 0c0dedc7d6.exe (PID: 5380)
- launcherr.exe (PID: 6324)
- launcherr.exe (PID: 6940)
- MSBuild.exe (PID: 6300)
- launcherr.exe (PID: 2516)
There is functionality for VM detection VirtualBox (YARA)
- 0c0dedc7d6.exe (PID: 5380)
Connects to unusual port
- 3rrAdmR.exe (PID: 4212)
Process drops legitimate windows executable
- ramez.exe (PID: 2268)
- qUdcX6q8B8K.tmp (PID: 744)
- MKQsy2OCVDQxh.tmp (PID: 3124)
Starts a Microsoft application from unusual location
- 08IyOOF.exe (PID: 5136)
- j6J70wm.exe (PID: 2772)
The process executes via Task Scheduler
- ramez.exe (PID: 6824)
- ramez.exe (PID: 2564)
Reads the Windows owner or organization settings
- qUdcX6q8B8K.tmp (PID: 744)
- 7c30ae854e.tmp (PID: 232)
The process drops C-runtime libraries
- qUdcX6q8B8K.tmp (PID: 744)
Reads the BIOS version
- e5jg7MM.exe (PID: 6972)
Application launched itself
- svchost.exe (PID: 5740)
Checks for external IP
- svchost.exe (PID: 2196)
- svchost.exe (PID: 6048)
Searches for installed software
- MSBuild.exe (PID: 6300)
- MSBuild.exe (PID: 6512)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- lcyqrsfDC9gwl.exe (PID: 976)
- MSBuild.exe (PID: 240)
Executes application which crashes
- core.exe (PID: 6972)
- 6caffd6177.exe (PID: 2152)
Base64-obfuscated command line is found
- lcyqrsfDC9gwl.exe (PID: 976)
BASE64 encoded PowerShell command has been detected
- lcyqrsfDC9gwl.exe (PID: 976)
The process hide an interactive prompt from the user
- lcyqrsfDC9gwl.exe (PID: 976)
The process bypasses the loading of PowerShell profile settings
- lcyqrsfDC9gwl.exe (PID: 976)
INFO
Checks supported languages
- 2025-05-15_f394bfc47e2a1f6de9a5a58cb2fb2cc6_agent-tesla_amadey_black-basta_cobalt-strike_darkgate_elex_luca-stealer.exe (PID: 6872)
- TempO7C8NSKNRTCA4EC3ENKTABTPGNNRKACJ.EXE (PID: 6240)
- ramez.exe (PID: 2268)
- ramez.exe (PID: 6824)
- 3rrAdmR.exe (PID: 4212)
- 0c0dedc7d6.exe (PID: 5380)
- launcherr.exe (PID: 6324)
- launcherr.exe (PID: 6940)
- 08IyOOF.exe (PID: 5136)
- MSBuild.exe (PID: 6300)
- launcherr.exe (PID: 2516)
- j6J70wm.exe (PID: 2772)
- MSBuild.exe (PID: 6512)
- ra02W4S.exe (PID: 6744)
- qUdcX6q8B8K.exe (PID: 6712)
- qUdcX6q8B8K.tmp (PID: 744)
- globalsynapse297.exe (PID: 5596)
- GlobalSynapse.exe (PID: 4740)
- BQRM9fqbO.exe (PID: 3176)
- e5jg7MM.exe (PID: 6972)
- bqxUv7C.exe (PID: 5228)
- 7c30ae854e.exe (PID: 2096)
- 7c30ae854e.tmp (PID: 232)
- MSBuild.exe (PID: 3300)
- ramez.exe (PID: 2564)
- lcyqrsfDC9gwl.exe (PID: 976)
- core.exe (PID: 6972)
- info.exe (PID: 3828)
Reads mouse settings
- 2025-05-15_f394bfc47e2a1f6de9a5a58cb2fb2cc6_agent-tesla_amadey_black-basta_cobalt-strike_darkgate_elex_luca-stealer.exe (PID: 6872)
The sample compiled with english language support
- 2025-05-15_f394bfc47e2a1f6de9a5a58cb2fb2cc6_agent-tesla_amadey_black-basta_cobalt-strike_darkgate_elex_luca-stealer.exe (PID: 6872)
- ramez.exe (PID: 2268)
- qUdcX6q8B8K.tmp (PID: 744)
- 0c0dedc7d6.exe (PID: 5380)
- MKQsy2OCVDQxh.tmp (PID: 3124)
Auto-launch of the file from Task Scheduler
- cmd.exe (PID: 2088)
Create files in a temporary directory
- 2025-05-15_f394bfc47e2a1f6de9a5a58cb2fb2cc6_agent-tesla_amadey_black-basta_cobalt-strike_darkgate_elex_luca-stealer.exe (PID: 6872)
- TempO7C8NSKNRTCA4EC3ENKTABTPGNNRKACJ.EXE (PID: 6240)
- ramez.exe (PID: 2268)
- 0c0dedc7d6.exe (PID: 5380)
- 3rrAdmR.exe (PID: 4212)
- qUdcX6q8B8K.exe (PID: 6712)
- qUdcX6q8B8K.tmp (PID: 744)
- 7c30ae854e.exe (PID: 2096)
- 7c30ae854e.tmp (PID: 232)
Reads the computer name
- 2025-05-15_f394bfc47e2a1f6de9a5a58cb2fb2cc6_agent-tesla_amadey_black-basta_cobalt-strike_darkgate_elex_luca-stealer.exe (PID: 6872)
- TempO7C8NSKNRTCA4EC3ENKTABTPGNNRKACJ.EXE (PID: 6240)
- ramez.exe (PID: 2268)
- 0c0dedc7d6.exe (PID: 5380)
- 3rrAdmR.exe (PID: 4212)
- launcherr.exe (PID: 6324)
- launcherr.exe (PID: 6940)
- MSBuild.exe (PID: 6300)
- launcherr.exe (PID: 2516)
- MSBuild.exe (PID: 6512)
- qUdcX6q8B8K.tmp (PID: 744)
- globalsynapse297.exe (PID: 5596)
- GlobalSynapse.exe (PID: 4740)
- BQRM9fqbO.exe (PID: 3176)
- ra02W4S.exe (PID: 6744)
- lcyqrsfDC9gwl.exe (PID: 976)
- 7c30ae854e.tmp (PID: 232)
- MSBuild.exe (PID: 3300)
Reads Internet Explorer settings
- mshta.exe (PID: 2244)
- mshta.exe (PID: 3888)
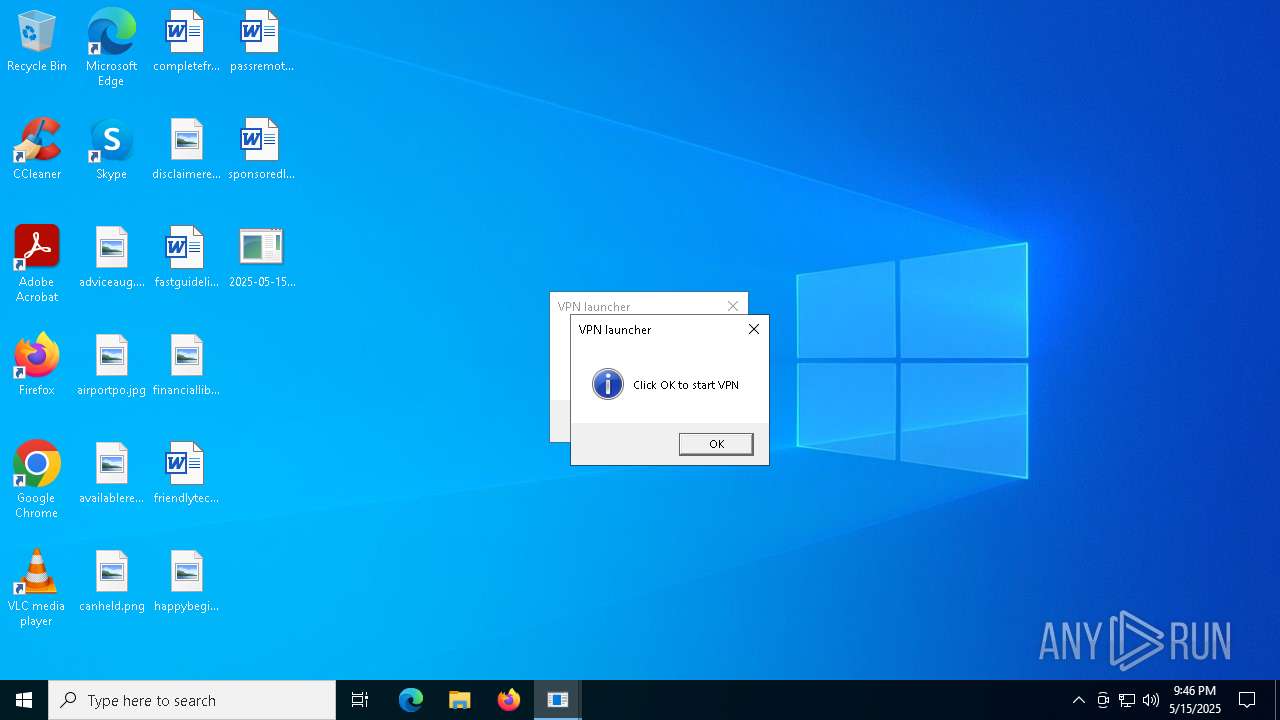
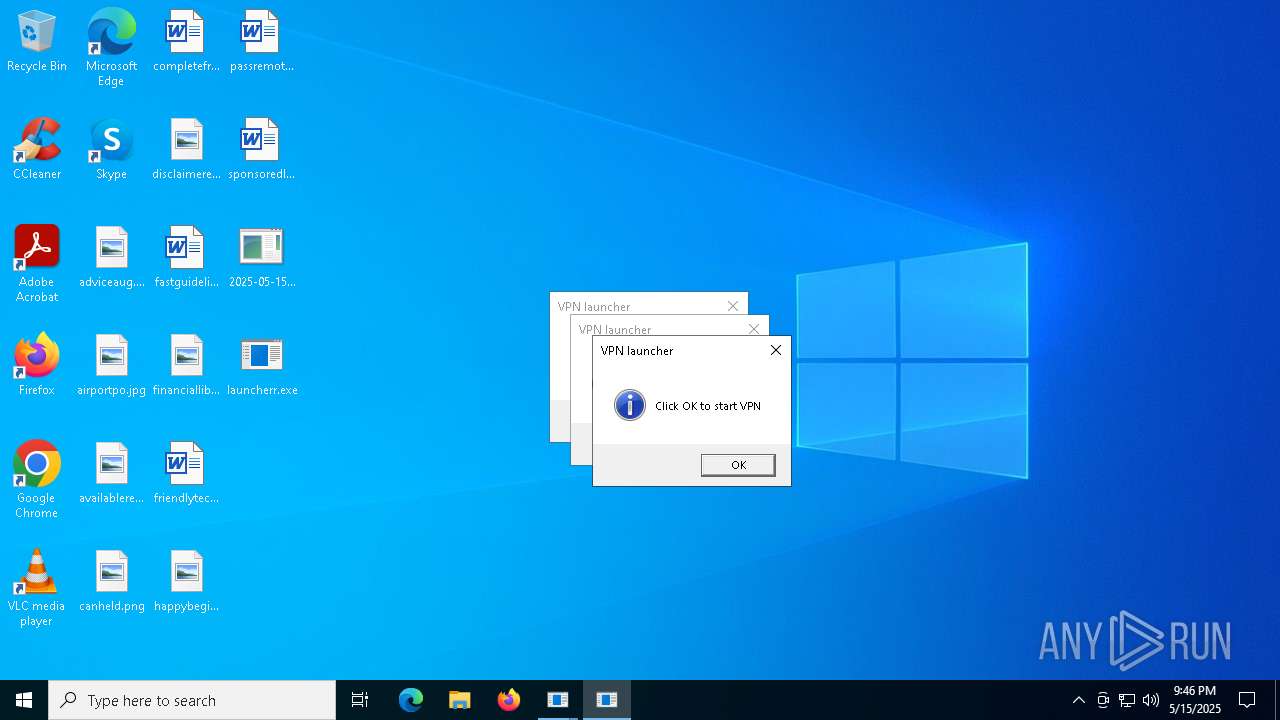
Manual execution by a user
- mshta.exe (PID: 3888)
- launcherr.exe (PID: 6940)
- launcherr.exe (PID: 2516)
- GlobalSynapse.exe (PID: 4740)
Disables trace logs
- powershell.exe (PID: 7152)
- powershell.exe (PID: 7148)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7152)
Checks proxy server information
- powershell.exe (PID: 7148)
- powershell.exe (PID: 7152)
- ramez.exe (PID: 2268)
- 0c0dedc7d6.exe (PID: 5380)
- 3rrAdmR.exe (PID: 4212)
- ra02W4S.exe (PID: 6744)
- lcyqrsfDC9gwl.exe (PID: 976)
The executable file from the user directory is run by the Powershell process
- TempO7C8NSKNRTCA4EC3ENKTABTPGNNRKACJ.EXE (PID: 6240)
Process checks computer location settings
- TempO7C8NSKNRTCA4EC3ENKTABTPGNNRKACJ.EXE (PID: 6240)
- ramez.exe (PID: 2268)
- globalsynapse297.exe (PID: 5596)
- 7c30ae854e.tmp (PID: 232)
Creates files or folders in the user directory
- ramez.exe (PID: 2268)
- 0c0dedc7d6.exe (PID: 5380)
- qUdcX6q8B8K.tmp (PID: 744)
- ra02W4S.exe (PID: 6744)
- 7c30ae854e.tmp (PID: 232)
- lcyqrsfDC9gwl.exe (PID: 976)
Enigma protector has been detected
- 0c0dedc7d6.exe (PID: 5380)
Compiled with Borland Delphi (YARA)
- 0c0dedc7d6.exe (PID: 5380)
Creates files in the program directory
- 3rrAdmR.exe (PID: 4212)
- globalsynapse297.exe (PID: 5596)
- lcyqrsfDC9gwl.exe (PID: 976)
Auto-launch of the file from Registry key
- 3rrAdmR.exe (PID: 4212)
Reads the machine GUID from the registry
- 0c0dedc7d6.exe (PID: 5380)
- MSBuild.exe (PID: 6300)
- MSBuild.exe (PID: 6512)
- ra02W4S.exe (PID: 6744)
- lcyqrsfDC9gwl.exe (PID: 976)
Reads the software policy settings
- 0c0dedc7d6.exe (PID: 5380)
- MSBuild.exe (PID: 6300)
- MSBuild.exe (PID: 6512)
- ra02W4S.exe (PID: 6744)
- lcyqrsfDC9gwl.exe (PID: 976)
Application based on Golang
- launcherr.exe (PID: 6324)
- launcherr.exe (PID: 6940)
- launcherr.exe (PID: 2516)
Detects GO elliptic curve encryption (YARA)
- launcherr.exe (PID: 6324)
- launcherr.exe (PID: 6940)
- launcherr.exe (PID: 2516)
Creates a software uninstall entry
- qUdcX6q8B8K.tmp (PID: 744)
- 7c30ae854e.tmp (PID: 232)
Changes the registry key values via Powershell
- globalsynapse297.exe (PID: 5596)
- globalsynapse297.exe (PID: 3032)
Attempting to use instant messaging service
- MSBuild.exe (PID: 240)
Application launched itself
- chrome.exe (PID: 7388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:05:14 22:30:14+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 633856 |
| InitializedDataSize: | 326144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20577 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Total processes
230
Monitored processes
94
Malicious processes
26
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Users\admin\AppData\Local\Temp\is-EO2VE.tmp\7c30ae854e.tmp" /SL5="$4024C,1182700,844800,C:\Users\admin\AppData\Local\Temp\10121120101\7c30ae854e.exe" | C:\Users\admin\AppData\Local\Temp\is-EO2VE.tmp\7c30ae854e.tmp | 7c30ae854e.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 240 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | 6caffd6177.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 744 | "C:\Users\admin\AppData\Local\Temp\is-70VDG.tmp\qUdcX6q8B8K.tmp" /SL5="$B02DE,3328372,54272,C:\Users\admin\AppData\Roaming\LskTti\qUdcX6q8B8K.exe" | C:\Users\admin\AppData\Local\Temp\is-70VDG.tmp\qUdcX6q8B8K.tmp | qUdcX6q8B8K.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Version: 51.52.0.0 Modules
| |||||||||||||||
| 920 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | info.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -c Set-ItemProperty -Path "HKCU:\Software\Microsoft\Windows\CurrentVersion\Run" -Name "GLSynapse" -Value "C:\ProgramData\GlobalSynapse\GlobalSynapse.exe" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | globalsynapse297.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 976 | "C:\Users\admin\AppData\Roaming\OnuoPBMZLqj\lcyqrsfDC9gwl.exe" | C:\Users\admin\AppData\Roaming\OnuoPBMZLqj\lcyqrsfDC9gwl.exe | 0c0dedc7d6.exe | ||||||||||||
User: admin Company: Optimized Plugin Corp. Integrity Level: MEDIUM Description: Tool to Implement Widget efficiently Version: 4.11.775.1446 Modules
| |||||||||||||||
| 1072 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | C:\WINDOWS\system32\cmd.exe /c schtasks /create /tn ePE55maOJ10 /tr "mshta C:\Users\admin\AppData\Local\Temp\SOXo7pSdk.hta" /sc minute /mo 25 /ru "admin" /f | C:\Windows\SysWOW64\cmd.exe | — | 2025-05-15_f394bfc47e2a1f6de9a5a58cb2fb2cc6_agent-tesla_amadey_black-basta_cobalt-strike_darkgate_elex_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
51 065
Read events
50 962
Write events
96
Delete events
7
Modification events
| (PID) Process: | (2244) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2244) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2244) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7152) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7152) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7152) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7152) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7152) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7152) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7152) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
74
Suspicious files
32
Text files
37
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ho0t04kh.pew.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6872 | 2025-05-15_f394bfc47e2a1f6de9a5a58cb2fb2cc6_agent-tesla_amadey_black-basta_cobalt-strike_darkgate_elex_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\SOXo7pSdk.hta | html | |
MD5:ABAADC529E1F19774840C1ABF931A37B | SHA256:2071633E430151B5FD401BEF7CAF89C0A8844D91EF2406B01FCCA1F3CFF8BD02 | |||
| 7152 | powershell.exe | C:\Users\admin\AppData\Local\TempO7C8NSKNRTCA4EC3ENKTABTPGNNRKACJ.EXE | executable | |
MD5:26CC5A6CFD8E8ECC433337413C14CDDB | SHA256:2D904D576B46236BAF504DBA21775F6EBBBD0F65272A9C2FCA1C6798184FA4E8 | |||
| 7152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qdmj5s4o.0xc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6240 | TempO7C8NSKNRTCA4EC3ENKTABTPGNNRKACJ.EXE | C:\Windows\Tasks\ramez.job | binary | |
MD5:AD450990B2382683FEEB474EF3ADC3AC | SHA256:DC72ECBE7F230FD4067E30FBB3D2FF1A7BF45E800CD835E0DBB025469CDC38D9 | |||
| 7152 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:A64CC8BCAE9524DD472EC8527212BEB9 | SHA256:071291B2FD354DFB3F0E313122FFFC6AFF00A5EA02F90AB8F217FB645E382F87 | |||
| 7148 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4ac02y5o.b0z.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7148 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_v1qpuskw.uuh.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2268 | ramez.exe | C:\Users\admin\AppData\Local\Temp\10121050101\0c0dedc7d6.exe | executable | |
MD5:B20DFC438760671893EC3E49DF9AFA35 | SHA256:4A991D77AFD122CBFEDC7D61F0EDF90F2907640A25C17FA4B9390E64A926E704 | |||
| 2268 | ramez.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\random[1].exe | executable | |
MD5:B20DFC438760671893EC3E49DF9AFA35 | SHA256:4A991D77AFD122CBFEDC7D61F0EDF90F2907640A25C17FA4B9390E64A926E704 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
260
TCP/UDP connections
116
DNS requests
41
Threats
95
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.8:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2268 | ramez.exe | POST | 200 | 185.156.72.96:80 | http://185.156.72.96/te4h2nus/index.php | unknown | — | — | malicious |
2268 | ramez.exe | POST | 200 | 185.156.72.96:80 | http://185.156.72.96/te4h2nus/index.php | unknown | — | — | malicious |
6132 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
2268 | ramez.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/files/unique2/random.exe | unknown | — | — | unknown |
6132 | SIHClient.exe | GET | 200 | 23.216.77.29:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
6132 | SIHClient.exe | GET | 200 | 23.216.77.29:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
6132 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2268 | ramez.exe | POST | 200 | 185.156.72.96:80 | http://185.156.72.96/te4h2nus/index.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.8:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7152 | powershell.exe | 185.156.72.2:80 | — | Tov Vaiz Partner | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
drive.usercontent.google.com |
| whitelisted |
pomelohgj.top |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7152 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 34 |
7152 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7152 | powershell.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
7152 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
7152 | powershell.exe | Misc activity | ET INFO Packed Executable Download |
7152 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
7148 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7148 | powershell.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
7148 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
7148 | powershell.exe | Misc activity | ET INFO Packed Executable Download |