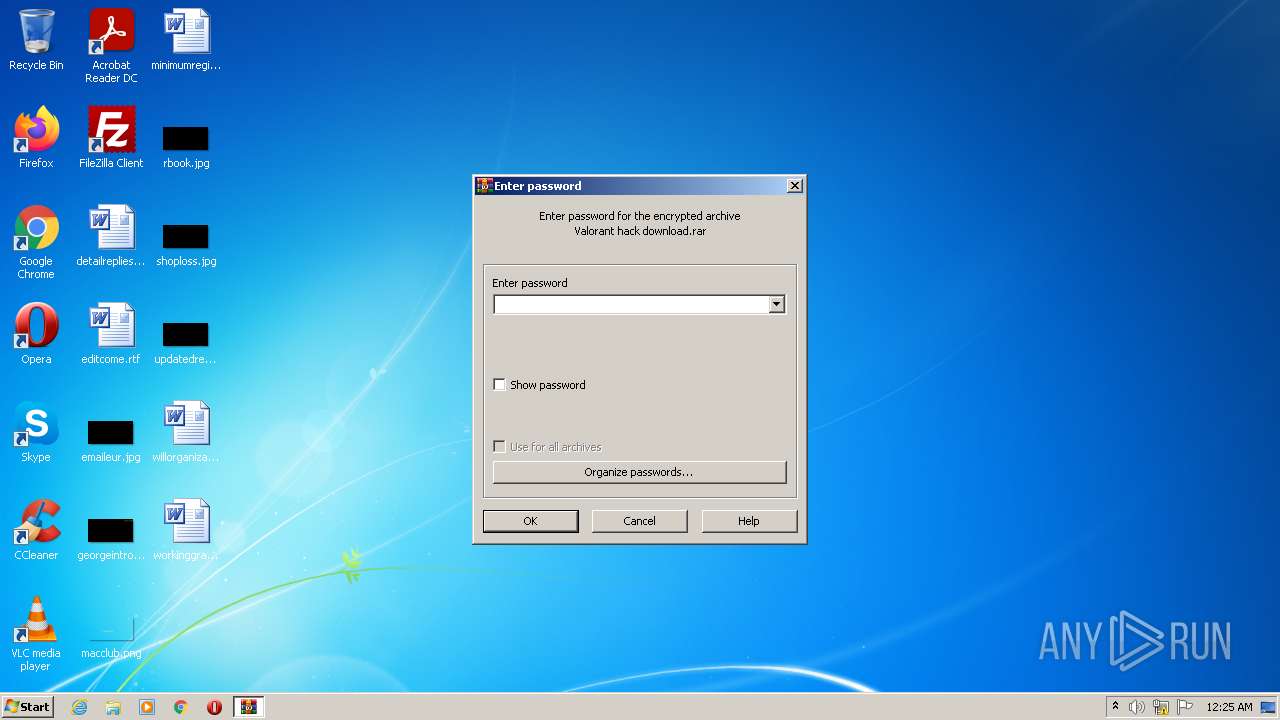
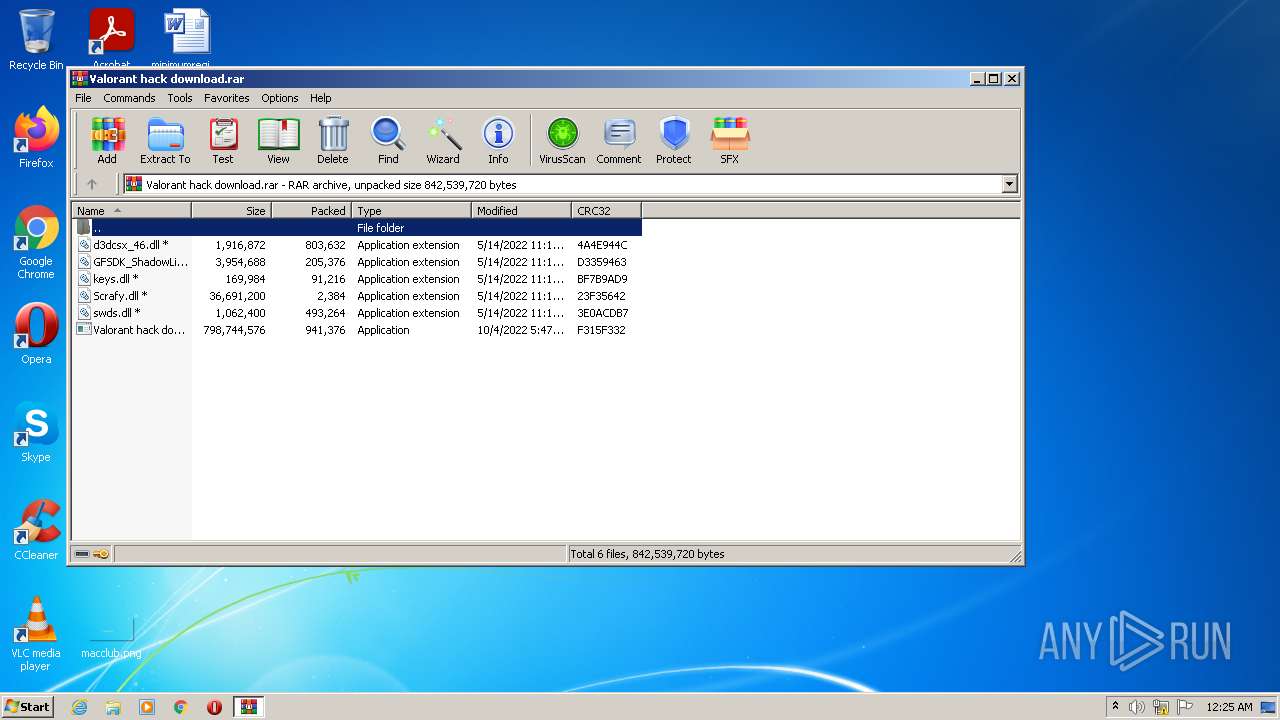
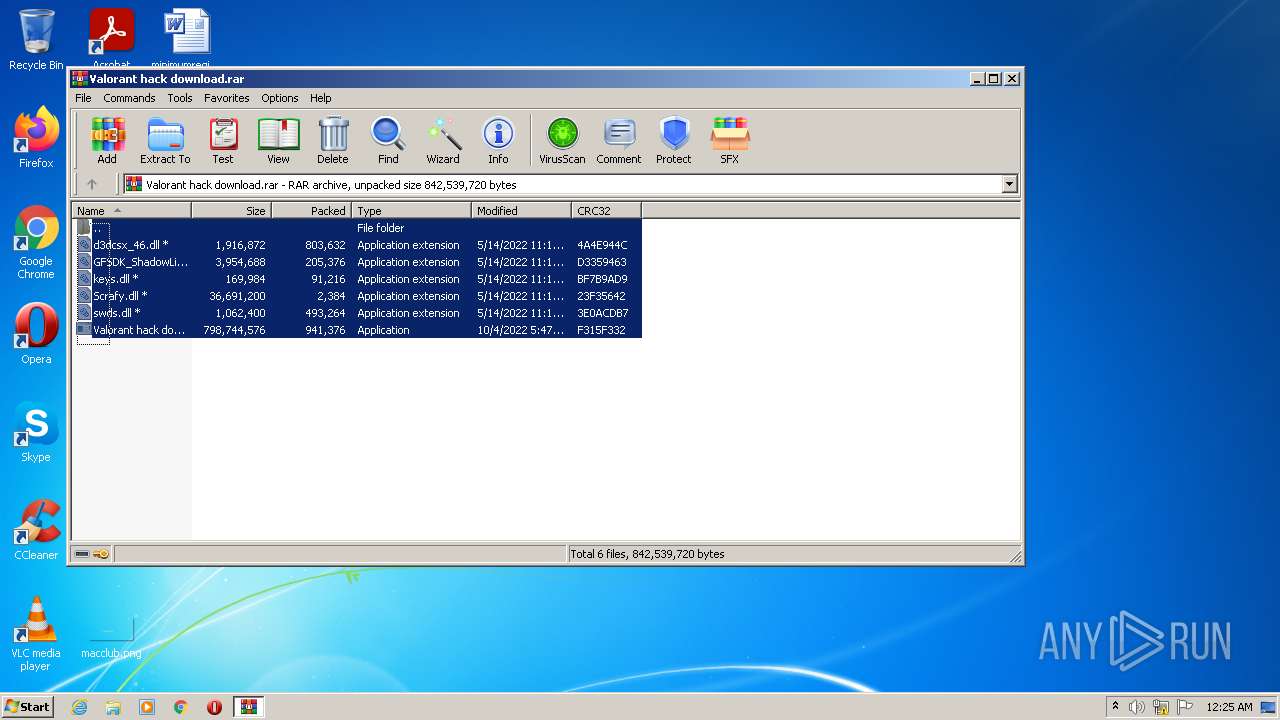
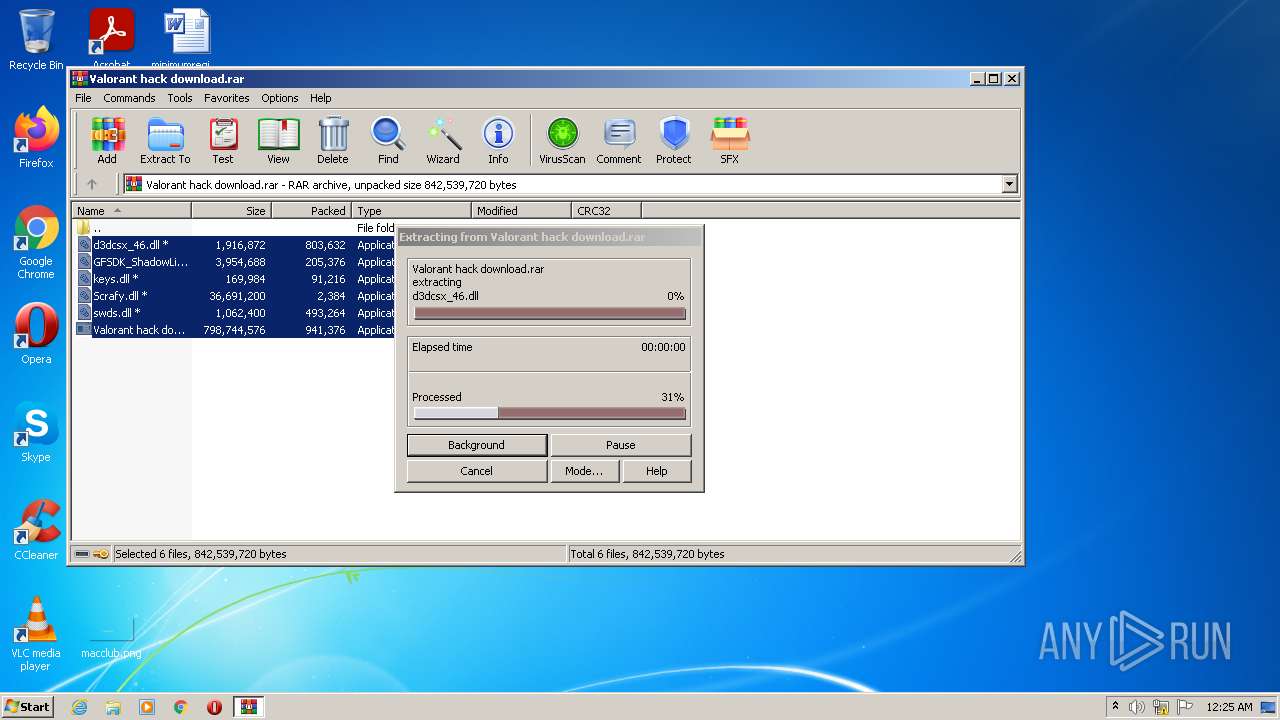
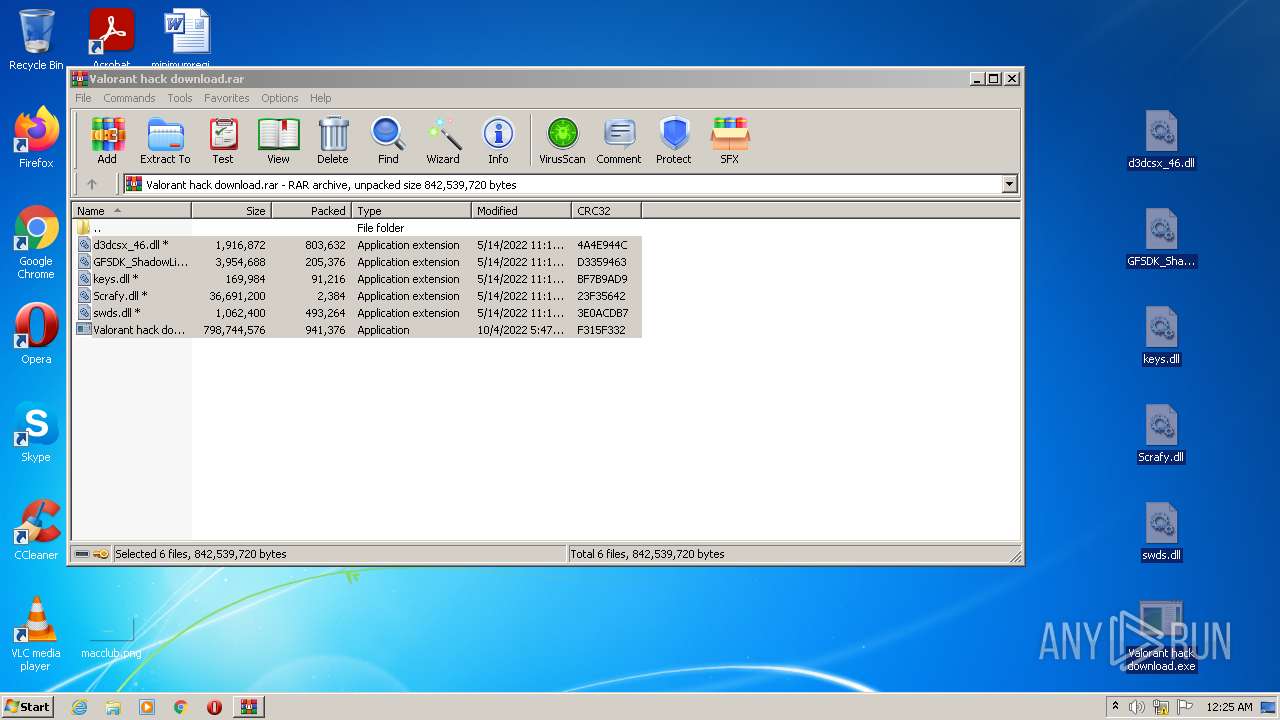
| File name: | Valorant hack download.rar |
| Full analysis: | https://app.any.run/tasks/6d41a7b8-3ef4-40d5-b2eb-4dc4ce997587 |
| Verdict: | Malicious activity |
| Threats: | Arkei is a stealer type malware capable of collecting passwords, autosaved forms, cryptocurrency wallet credentials, and files. |
| Analysis date: | October 04, 2022, 23:25:12 |
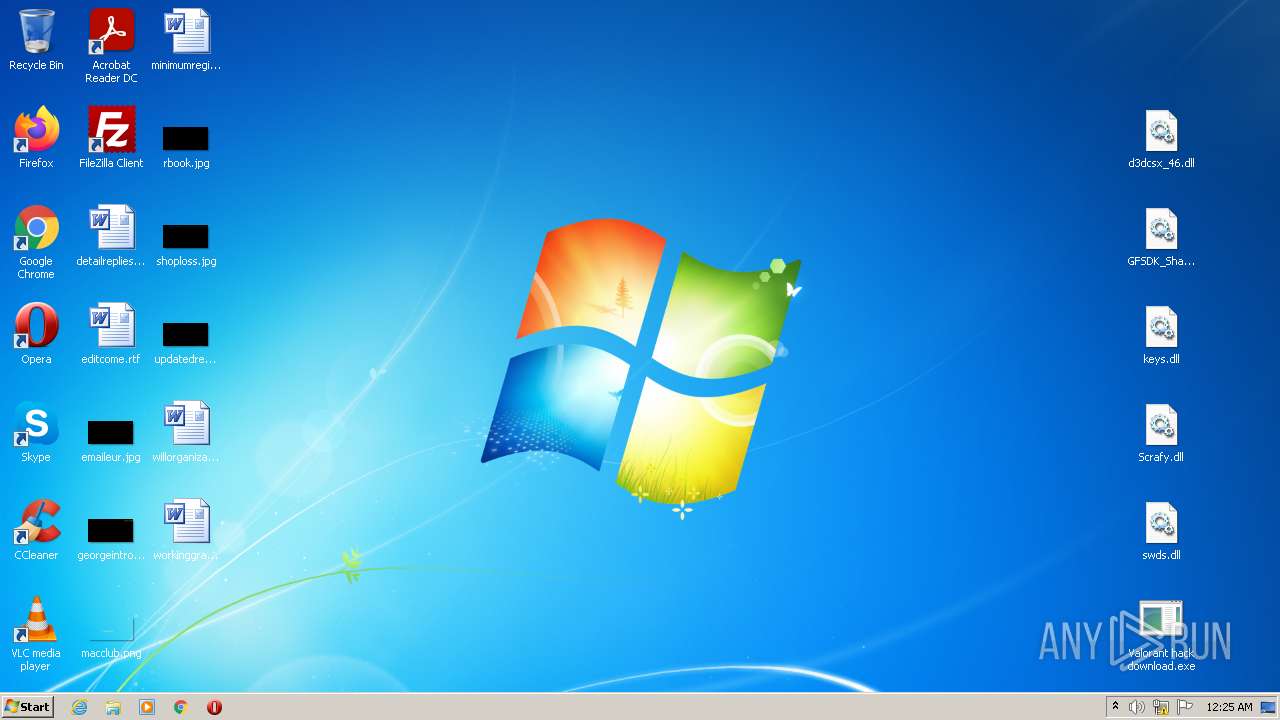
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 808B0141529E2BDD361720A68C299E80 |
| SHA1: | 60AE2B934E7992A4A64B1F151108F17D13137E26 |
| SHA256: | DA5A993C5A4F77518E5729FA50715CE28ADDBCC25E4953DA41C933BEAF9B2F46 |
| SSDEEP: | 49152:llAauaqwcxs4nqdCRgVUXWYxuVIAhpo2LslFJ+PibN2u96r4/0LXD4AG9Ta7PDJB:llAg10SnVUpxuVvhpoBlFJC42uIrXXEq |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 676)
- AppLaunch.exe (PID: 99096)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3660)
- AppLaunch.exe (PID: 99096)
Steals credentials from Web Browsers
- AppLaunch.exe (PID: 99096)
Stealing of credential data
- AppLaunch.exe (PID: 99096)
ARKEI detected by memory dumps
- AppLaunch.exe (PID: 99096)
Actions looks like stealing of personal data
- AppLaunch.exe (PID: 99096)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 676)
- AppLaunch.exe (PID: 99096)
Checks supported languages
- WinRAR.exe (PID: 676)
- AppLaunch.exe (PID: 99096)
- Valorant hack download.exe (PID: 984)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 676)
- AppLaunch.exe (PID: 99096)
Creates files in the user directory
- AppLaunch.exe (PID: 99096)
Reads the cookies of Mozilla Firefox
- AppLaunch.exe (PID: 99096)
Creates files in the program directory
- AppLaunch.exe (PID: 99096)
Drops a file with a compile date too recent
- AppLaunch.exe (PID: 99096)
- WinRAR.exe (PID: 676)
Reads Environment values
- AppLaunch.exe (PID: 99096)
Reads the cookies of Google Chrome
- AppLaunch.exe (PID: 99096)
Reads CPU info
- AppLaunch.exe (PID: 99096)
Searches for installed software
- AppLaunch.exe (PID: 99096)
INFO
Checks Windows Trust Settings
- AppLaunch.exe (PID: 99096)
Reads settings of System Certificates
- AppLaunch.exe (PID: 99096)
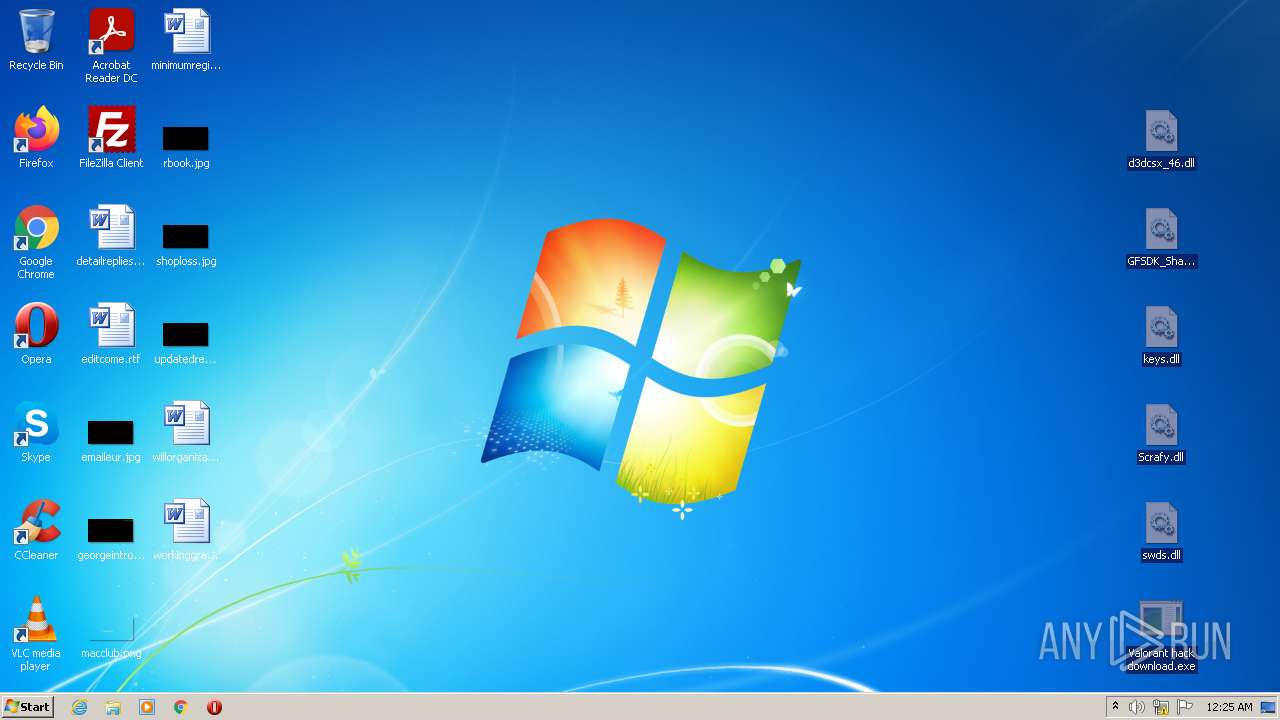
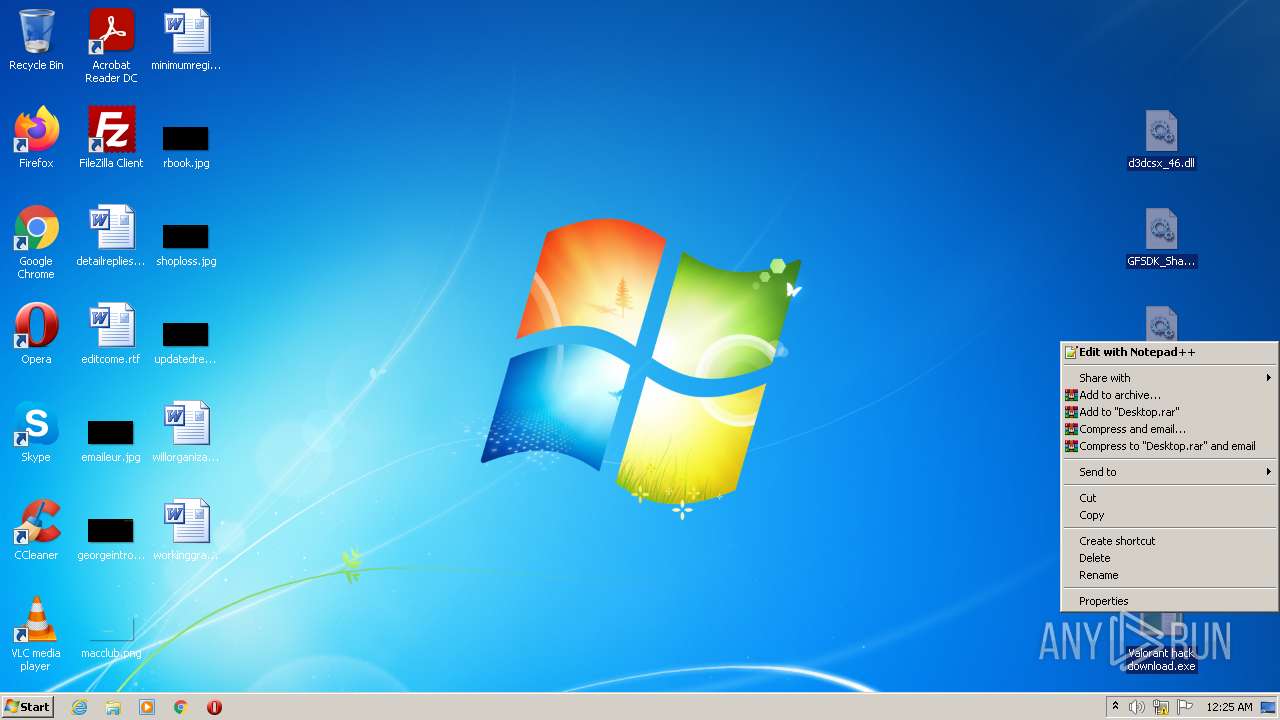
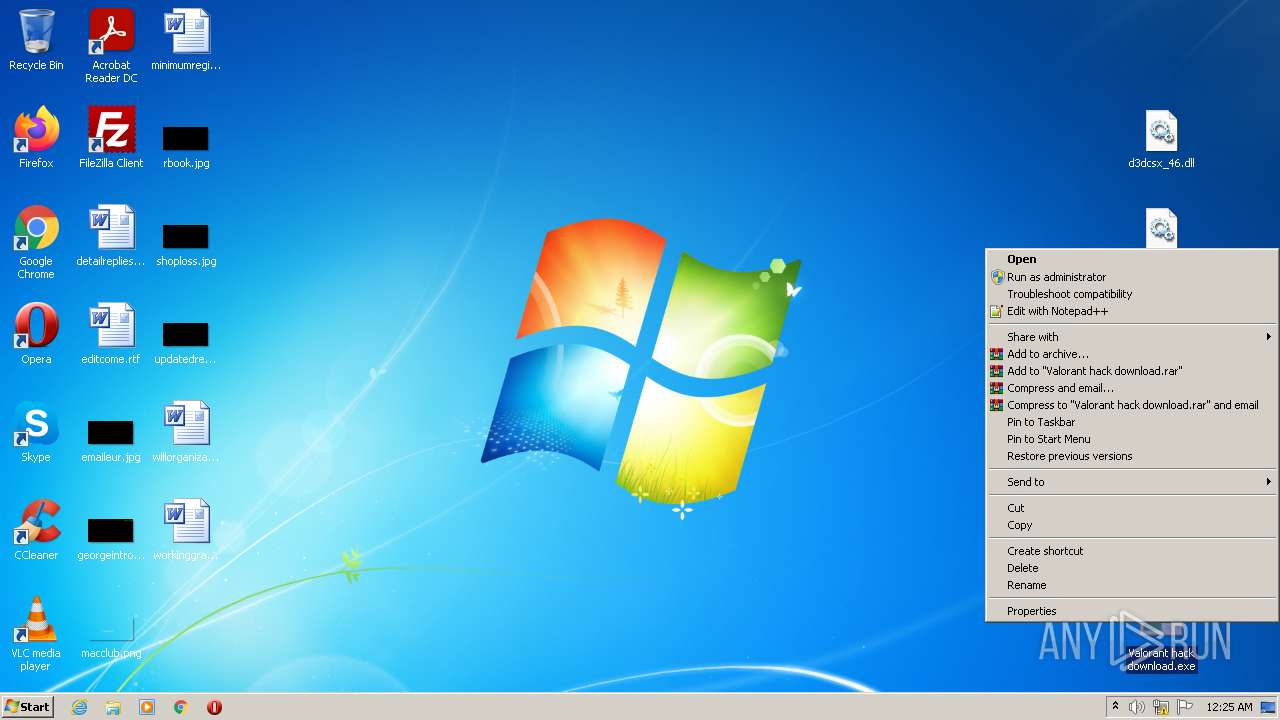
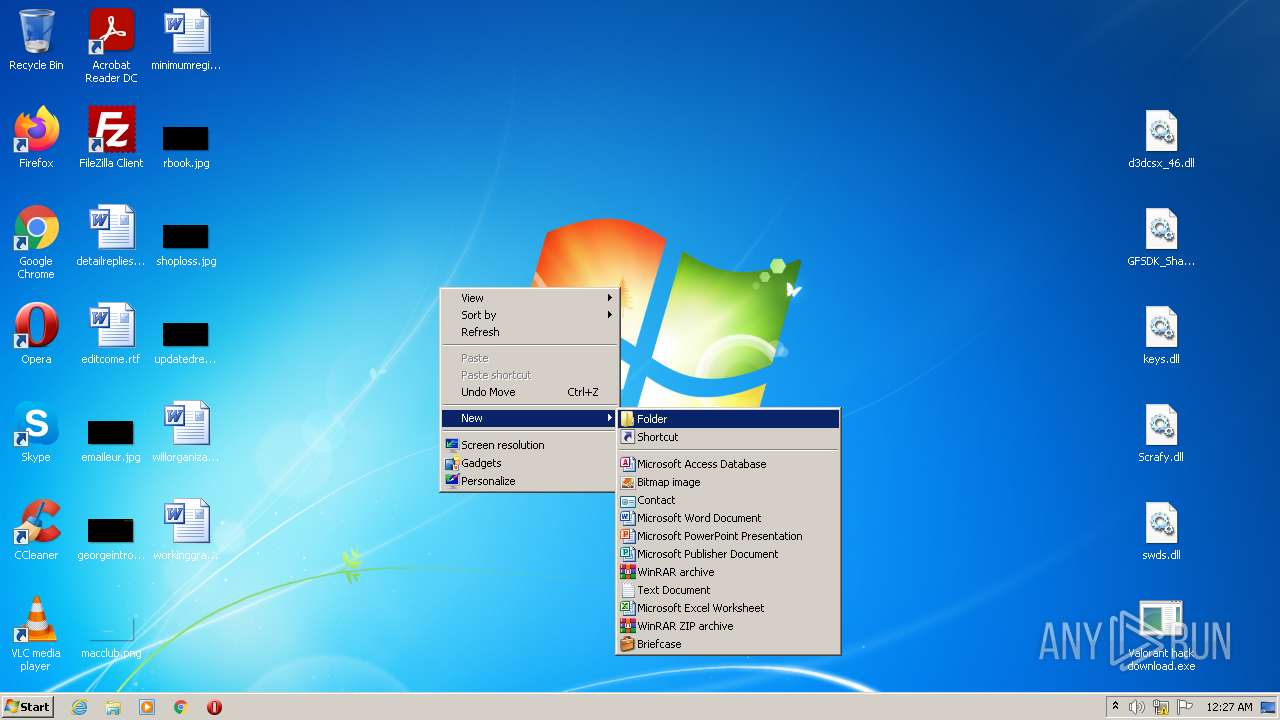
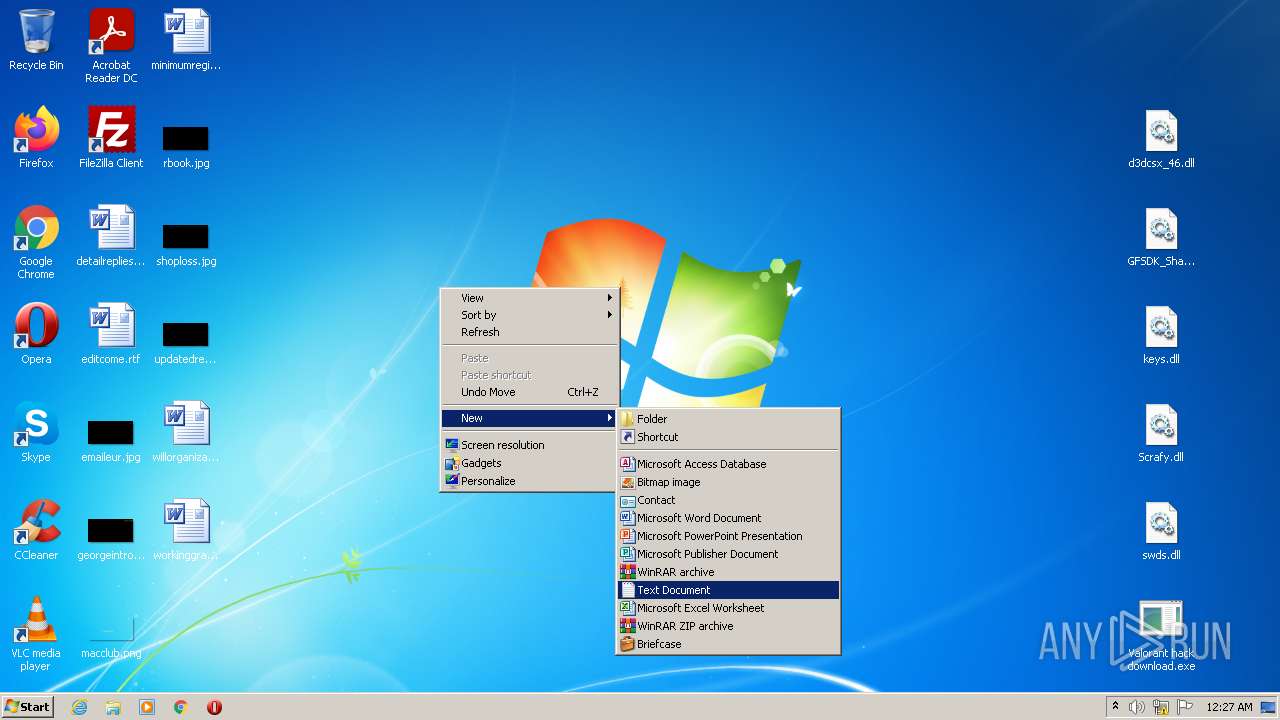
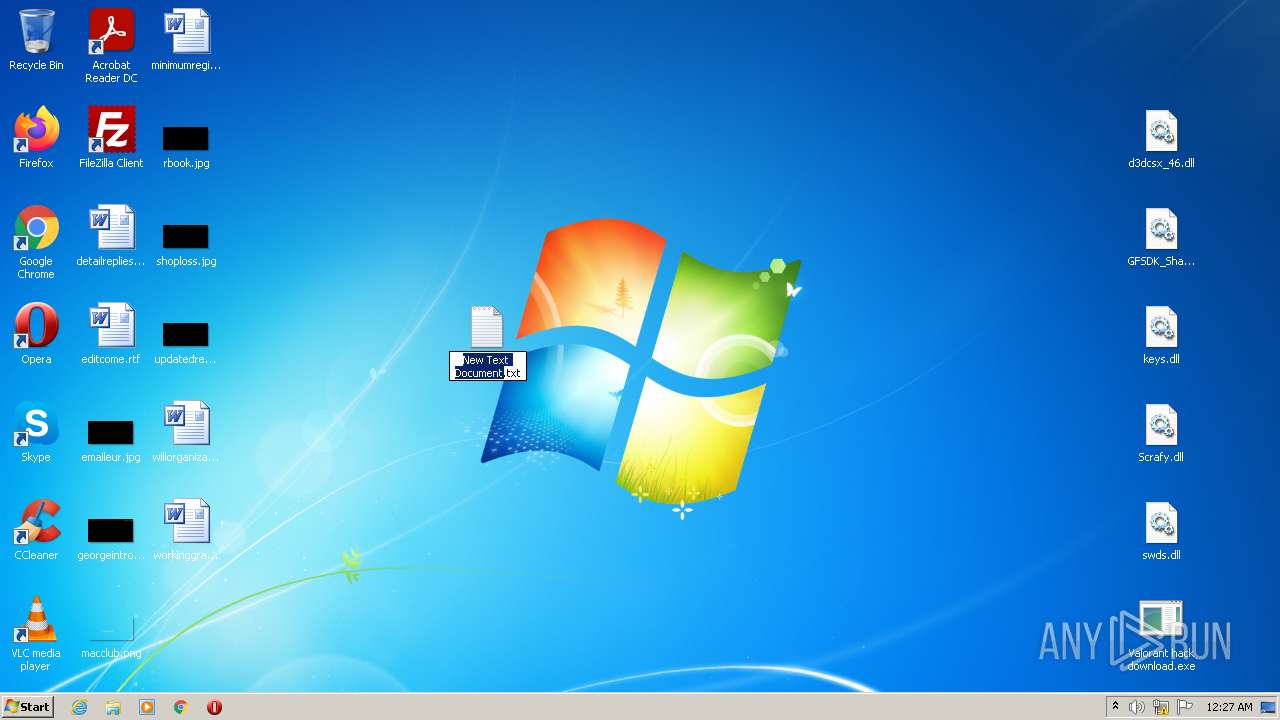
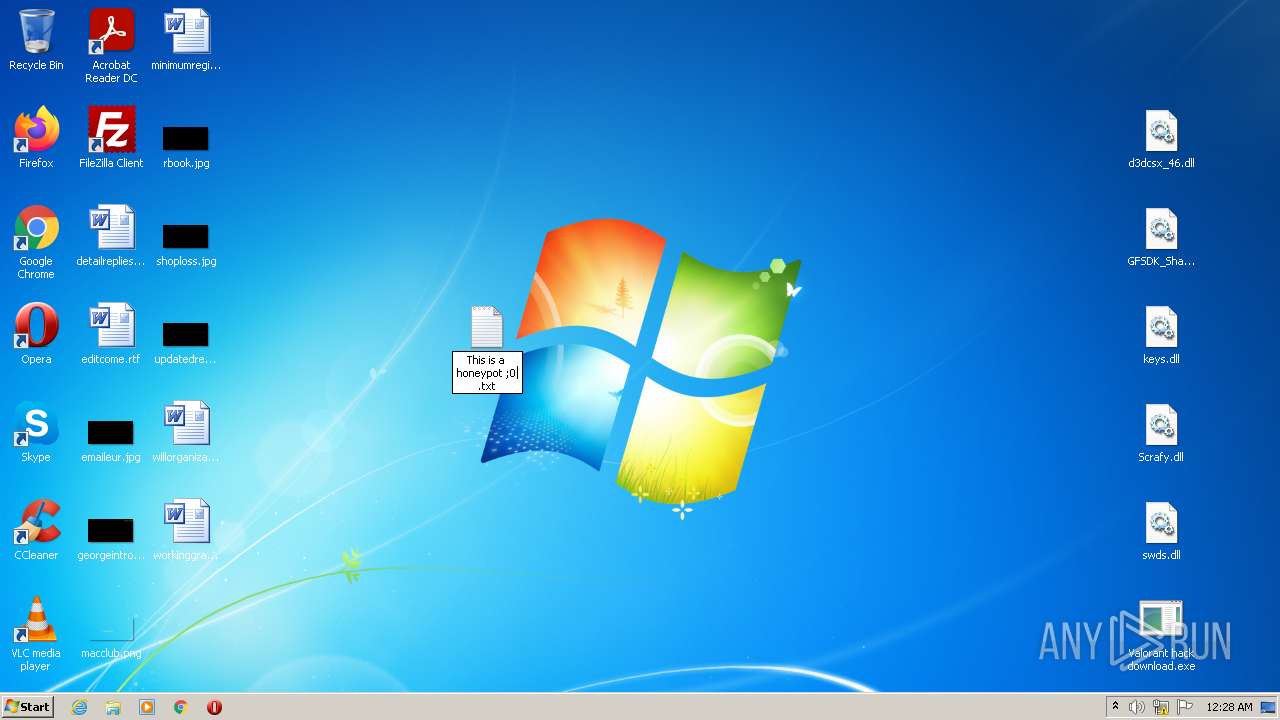
Manual execution by user
- Valorant hack download.exe (PID: 984)
- NOTEPAD.EXE (PID: 9648)
Dropped object may contain Bitcoin addresses
- AppLaunch.exe (PID: 99096)
Checks supported languages
- NOTEPAD.EXE (PID: 9648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Arkei
(PID) Process(99096) AppLaunch.exe
C2 (3)https://t.me/larsenup
https://ioc.exchange/@zebra54
http://5.161.120.43:80hello
Version54.9
BotNet1375
Options
URL marker927
Strings (502)%;vu E_
9GEYacq
keystore
Ethereum"
\Ethereum\
Electrum
\Electrum\wallets\
ElectrumLTC
\Electrum-LTC\wallets\
Exodus
\Exodus\
exodus.conf.json
window-state.json
\Exodus\exodus.wallet\
passphrase.json
seed.seco
info.seco
ElectronCash
\ElectronCash\wallets\
default_wallet
MultiDoge
\MultiDoge\
multidoge.wallet
Jaxx_Desktop_Old
\jaxx\Local Storage\
file__0.localstorage
Atomic
\atomic\Local Storage\leveldb\
000003.log
CURRENT
LOCK
LOG
MANIFEST-000001
0000*
Binance
\Binance\
app-store.json
Coinomi
\Coinomi\Coinomi\wallets\
*.wallet
*.config
wallet_path
SOFTWARE\monero-project\monero-core
\Monero\
C:\ProgramData\
.exe
RECYCLE.BIN
Config.Msi
System Volume Information
msdownld.tmp
Recovery
Local\Temp
Recycle.Bin
MicrosoftEdge\Cookies
Local\Packages
Local\NuGet
Roaming\WinRAR
Local\Microsoft
fee_estimates
peers
mempool
banlist
governance
mncache
mnpayments
netfulfilled
Login Data
Cookies
Web Data
logins.json
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
guid
SELECT origin_url, username_value, password_value FROM logins
SELECT name, value FROM autofill
SELECT name_on_card, expiration_month, expiration_year, card_number_encrypted FROM credit_cards
SELECT target_path, tab_url from downloads
SELECT url FROM urls
SELECT HOST_KEY, is_httponly, path, is_secure, (expires_utc/1000000)-11644480800, name, encrypted_value from cookies
\AppData\Roaming\FileZilla\recentservers.xml
<Host>
<Port>
<User>
<Pass encoding="base64">
Soft: FileZilla
Mozilla Firefox
\Mozilla\Firefox\Profiles\
Pale Moon
\Moonchild Productions\Pale Moon\Profiles\
Google Chrome
\Google\Chrome\User Data\
Chromium
\Chromium\User Data\
Amigo
\Amigo\User Data\
Torch
\Torch\User Data\
Comodo Dragon
\Comodo\Dragon\User Data\
Epic Privacy Browser
\Epic Privacy Browser\User Data\
Vivaldi
\Vivaldi\User Data\
CocCoc
\CocCoc\Browser\User Data\
Cent Browser
\CentBrowser\User Data\
TorBro Browser
\TorBro\Profile\
Chedot Browser
\Chedot\User Data\
Brave_Old
\brave\
7Star
\7Star\7Star\User Data\
Microsoft Edge
\Microsoft\Edge\User Data\
360 Browser
\360Browser\Browser\User Data\
QQBrowser
\Tencent\QQBrowser\User Data\
Opera
\Opera Software\Opera Stable\
OperaGX
\Opera Software\Opera GX Stable\
Local State
Cookies
TRUE
FALSE
gdi32.dll
ole32.dll
user32.dll
psapi.dll
BCRYPT.DLL
BCryptCloseAlgorithmProvider
BCryptDestroyKey
BCryptOpenAlgorithmProvider
BCryptSetProperty
BCryptGenerateSymmetricKey
BCryptDecrypt
CRYPT32.DLL
CryptUnprotectData
CryptStringToBinaryA
C:\ProgramData\nss3.dll
NSS_Init
NSS_Shutdown
PK11_GetInternalKeySlot
PK11_FreeSlot
PK11_Authenticate
PK11SDR_Decrypt
RegOpenKeyExA
RegQueryValueExA
RegCloseKey
RegOpenKeyExW
RegGetValueW
RegEnumKeyExA
RegGetValueA
GetCurrentHwProfileA
wininet.dll
InternetCloseHandle
InternetReadFile
HttpSendRequestA
HttpOpenRequestA
InternetConnectA
InternetOpenA
HttpAddRequestHeadersA
HttpQueryInfoA
InternetSetFilePointer
InternetOpenUrlA
InternetSetOptionA
DeleteUrlCacheEntry
CreateCompatibleBitmap
SelectObject
BitBlt
DeleteObject
CreateDCA
GetDeviceCaps
CreateCompatibleDC
CoCreateInstance
CoUninitialize
GetDesktopWindow
ReleaseDC
GetKeyboardLayoutList
CharToOemA
GetDC
wsprintfA
EnumDisplayDevicesA
GetSystemMetrics
GetModuleFileNameExA
GetModuleBaseNameA
EnumProcessModules
ibnejdfjmmkpcnlpebklmnkoeoihofec
TronLink
nkbihfbeogaeaoehlefnkodbefgpgknn
MetaMask
fhbohimaelbohpjbbldcngcnapndodjp
BinanceChainWallet
ffnbelfdoeiohenkjibnmadjiehjhajb
Yoroi
jbdaocneiiinmjbjlgalhcelgbejmnid
NiftyWallet
afbcbjpbpfadlkmhmclhkeeodmamcflc
MathWallet
hnfanknocfeofbddgcijnmhnfnkdnaad
Coinbase
hpglfhgfnhbgpjdenjgmdgoeiappafln
Guarda
blnieiiffboillknjnepogjhkgnoapac
EQUALWallet
cjelfplplebdjjenllpjcblmjkfcffne
JaxxLiberty
fihkakfobkmkjojpchpfgcmhfjnmnfpi
BitAppWallet
kncchdigobghenbbaddojjnnaogfppfj
iWallet
amkmjjmmflddogmhpjloimipbofnfjih
Wombat
nlbmnnijcnlegkjjpcfjclmcfggfefdm
MewCx
nanjmdknhkinifnkgdcggcfnhdaammmj
GuildWallet
fnjhmkhhmkbjkkabndcnnogagogbneec
RoninWallet
cphhlgmgameodnhkjdmkpanlelnlohao
NeoLine
nhnkbkgjikgcigadomkphalanndcapjk
CloverWallet
kpfopkelmapcoipemfendmdcghnegimn
LiqualityWallet
aiifbnbfobpmeekipheeijimdpnlpgpp
Terra_Station
dmkamcknogkgcdfhhbddcghachkejeap
Keplr
fhmfendgdocmcbmfikdcogofphimnkno
Sollet
cnmamaachppnkjgnildpdmkaakejnhae
AuroWallet
jojhfeoedkpkglbfimdfabpdfjaoolaf
PolymeshWallet
flpiciilemghbmfalicajoolhkkenfel
ICONex
fnnegphlobjdpkhecapkijjdkgcjhkib
Harmony
aeachknmefphepccionboohckonoeemg
Coin98
cgeeodpfagjceefieflmdfphplkenlfk
EVER Wallet
pdadjkfkgcafgbceimcpbkalnfnepbnk
KardiaChain
imloifkgjagghnncjkhggdhalmcnfklk
Trezor Password Manager
acmacodkjbdgmoleebolmdjonilkdbch
Rabby
bfnaelmomeimhlpmgjnjophhpkkoljpa
Phantom
ejbalbakoplchlghecdalmeeeajnimhm
odbfpeeihdkbihmopkbjmoonfanlbfcl
BraveWallet
fhilaheimglignddkjgofkcbgekhenbh
Oxygen (Atomic)
mgffkfbidihjpoaomajlbgchddlicgpn
PaliWallet
aodkkagnadcbobfpggfnjeongemjbjca
BoltX
hmeobnfnfcmdkdcmlblgagmfpfboieaf
XdefiWallet
lpfcbjknijpeeillifnkikgncikgfhdo
NamiWallet
dngmlblcodfobpdpecaadgfbcggfjfnm
MaiarDeFiWallet
lpilbniiabackdjcionkobglmddfbcjo
WavesKeeper
bhhhlbepdkbapadjdnnojkbgioiodbic
Solflare
dkdedlpgdmmkkfjabffeganieamfklkm
CyanoWallet
hcflpincpppdclinealmandijcmnkbgn
KHC
mnfifefkajgofkcjkemidiaecocnkjeh
TezBox
ookjlbkiijinhpmnjffcofjonbfbgaoc
Temple
jnkelfanjkeadonecabehalmbgpfodjm
Goby
bhghoamapcdpbohphigoooaddinpkbai
Authenticator
gaedmjdfmmahhbjefcbgaolhhanlaolb
Authy
oeljdldpnmdbchonielidgobddffflal
EOS Authenticator
ilgcnhelpchnceeipipijaljkblbcobl
GAuth Authenticator
\com.liberty.jaxx\IndexedDB\file__0.indexeddb.leveldb\
Jaxx_Desktop
\Daedalus Mainnet\wallets\
Daedalus Mainnet
she*.sqlite
\Blockstream\Green\wallets\
Blockstream Green
\WalletWasabi\Client\Wallets\
Wasabi Wallet
\discord\
Discord
Local Storage
leveldb
Session Storage
\Soft\Discord\discord_tokens.txt
dQw4w9WgXcQ:
Discord Token:
CreateThread
GlobalMemoryStatusEx
IsWow64Process
GetUserDefaultLocaleName
GetSystemInfo
WideCharToMultiByte
LocalFree
HeapAlloc
GetProcessHeap
CreateFileA
GetFileSize
ReadFile
CloseHandle
GetLogicalDriveStringsA
lstrlenA
GetDriveTypeA
lstrcpyA
MultiByteToWideChar
FindFirstFileA
FindNextFileA
FindClose
GetLastError
lstrcpynA
GlobalLock
GlobalSize
FreeLibrary
GetLocaleInfoA
GetCurrentProcessId
OpenProcess
GetFileSizeEx
GetTimeZoneInformation
TzSpecificLocalTimeToSystemTime
CopyFileA
DeleteFileA
GetCurrentDirectoryA
SetFilePointer
HeapFree
SystemTimeToFileTime
GetLocalTime
SetFileTime
WriteFile
GetFileAttributesA
GetFileAttributesW
LocalFileTimeToFileTime
MapViewOfFile
UnmapViewOfFile
FileTimeToSystemTime
CreateFileMappingA
GetFileInformationByHandle
GetEnvironmentVariableA
SetEnvironmentVariableA
GetTickCount
OpenEventA
CreateEventA
CreateToolhelp32Snapshot
Process32First
Process32Next
GetWindowsDirectoryA
GetVolumeInformationA
shell32.dll
shlwapi.dll
dbghelp.dll
gdiplus.dll
CryptBinaryToStringA
RegEnumValueA
GetFileSecurityA
OpenProcessToken
DuplicateToken
MapGenericMask
AccessCheck
InternetCrackUrlA
CoInitialize
CreateStreamOnHGlobal
GetHGlobalFromStream
GetWindowRect
GetWindowDC
CloseWindow
ShellExecuteExA
SHFileOperationA
SHGetFolderPathA
PathMatchSpecW
PathMatchSpecA
StrCmpCA
StrCmpCW
StrStrA
PathFindFileNameA
SymMatchString
GdipGetImageEncodersSize
GdipGetImageEncoders
GdipCreateBitmapFromHBITMAP
GdiplusStartup
GdiplusShutdown
GdipSaveImageToStream
GdipDisposeImage
GdipFree
sqlite3_open
sqlite3_prepare_v2
sqlite3_step
sqlite3_column_text
sqlite3_finalize
sqlite3_close
sqlite3_column_bytes
sqlite3_column_blob
\Opera Software\
\Opera Stable\
\Opera GX Stable\
\CryptoTab Browser\User Data\
CryptoTab Browser
\BraveSoftware\Brave-Browser\User Data\
Brave
\Thunderbird\Profiles\
Thunderbird
\Telegram Desktop\
key_datas
map*
D877F783D5D3EF8C*
A7FDF864FBC10B77*
A92DAA6EA6F891F2*
F8806DD0C461824F*
\Soft\Telegram\
\passwords.txt
"os_crypt":{"encrypted_key":"
Soft:
Host:
Login:
Password:
Network
SELECT host, isHttpOnly, path, isSecure, expiry, name, value FROM moz_cookies
SELECT url FROM moz_places
SELECT fieldname, value FROM moz_formhistory
History
cookies.sqlite
formhistory.sqlite
places.sqlite
*.localstorage
\Authy Desktop\Local Storage\
\Soft\Authy\
\Authy Desktop\Local Storage\leveldb\
\Soft\AuthyNew\
Soft: WinSCP
HostName
PortNumber
UserName
Password
Security
UseMasterPassword
Local Extension Settings
Sync Extension Settings
IndexedDB
kjmoohlgokccodicjjfebfomlbljgfhk
RoninWalletEdge
sqlite3.dll
Version:
Date:
MachineID:
GUID:
HWID:
Path:
Work Dir: In memory
Windows:
Computer Name:
User Name:
Display Resolution:
Display Language:
Keyboard Languages:
Local Time:
TimeZone:
[Hardware]
Processor:
CPU Count:
RAM:
VideoCard:
[Processes]
[Software]
\information.txt
%APPDATA%
%LOCALAPPDATA%
%USERPROFILE%
%DESKTOP%
%DOCUMENTS%
%PROGRAMFILES%
%PROGRAMFILES_86%
%RECENT%
%DRIVE_FIXED%
%DRIVE_REMOVABLE%
*%RECENT%*
*%DRIVE_FIXED%*
*%DRIVE_REMOVABLE%*
C:\Windows\
C:\\Windows\
C:\\\Windows\
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
48
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Valorant hack download.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 984 | "C:\Users\admin\Desktop\Valorant hack download.exe" | C:\Users\admin\Desktop\Valorant hack download.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3660 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
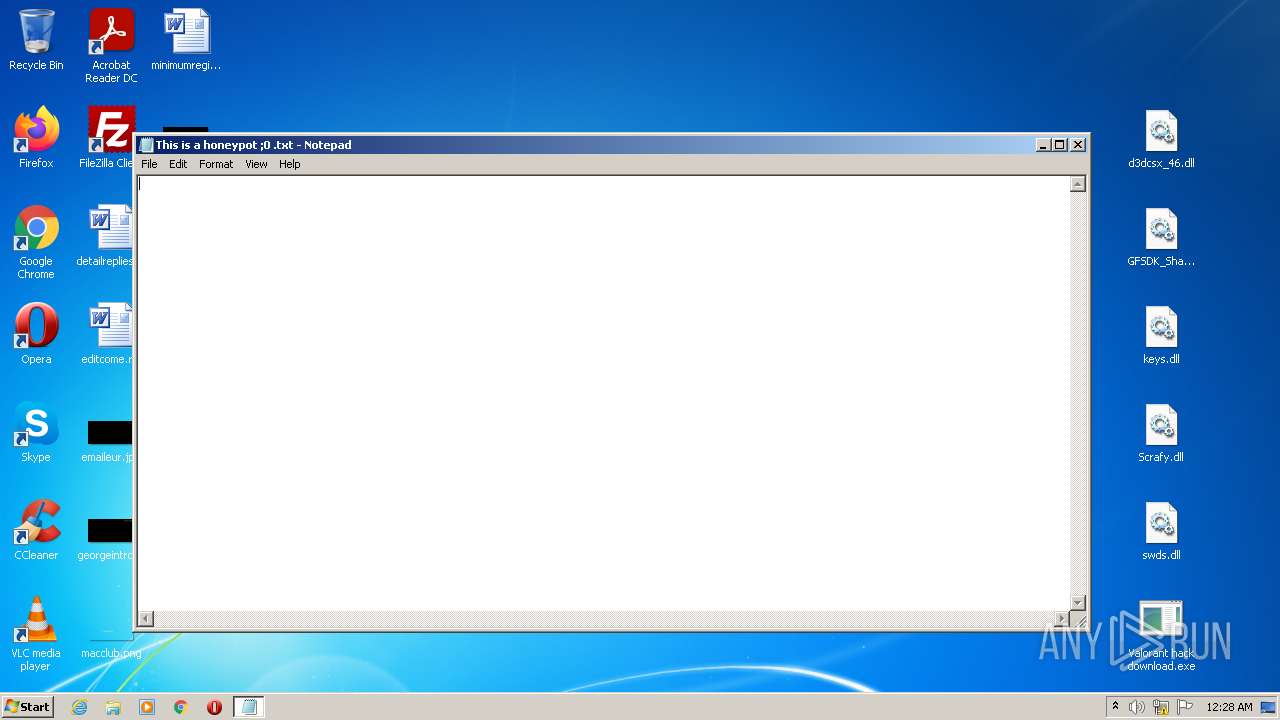
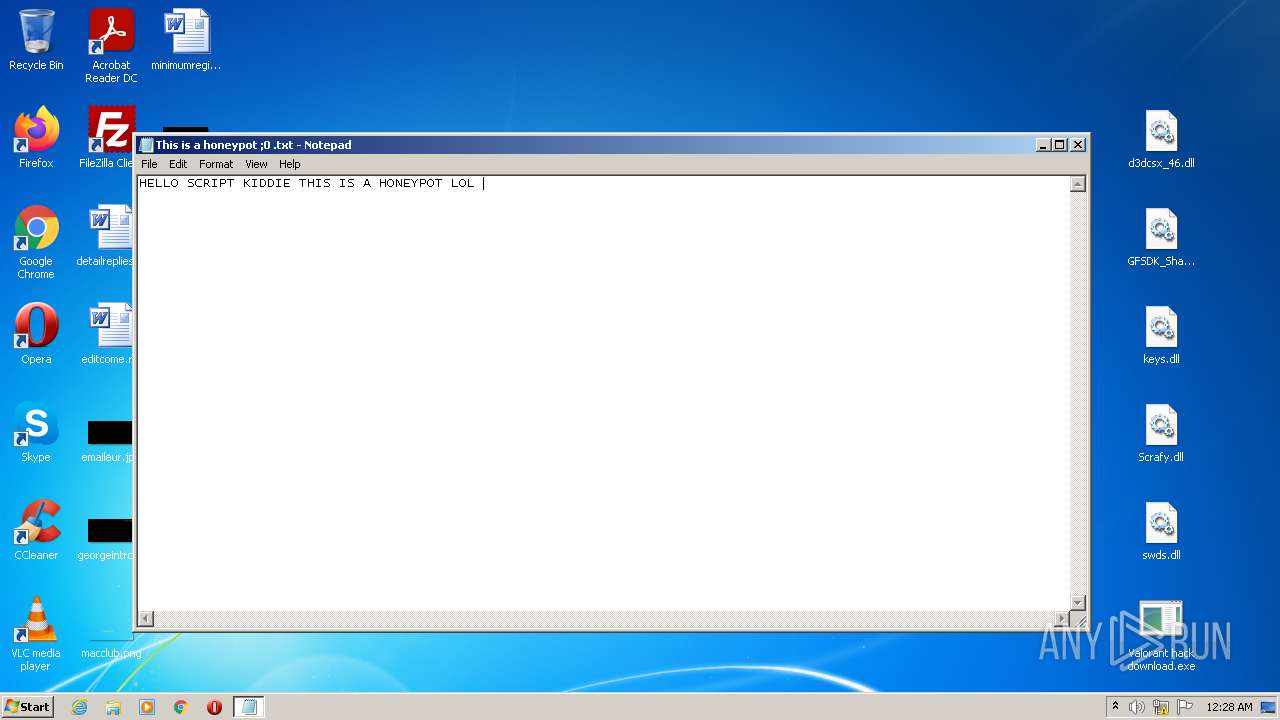
| 9648 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\This is a honeypot ;0 .txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
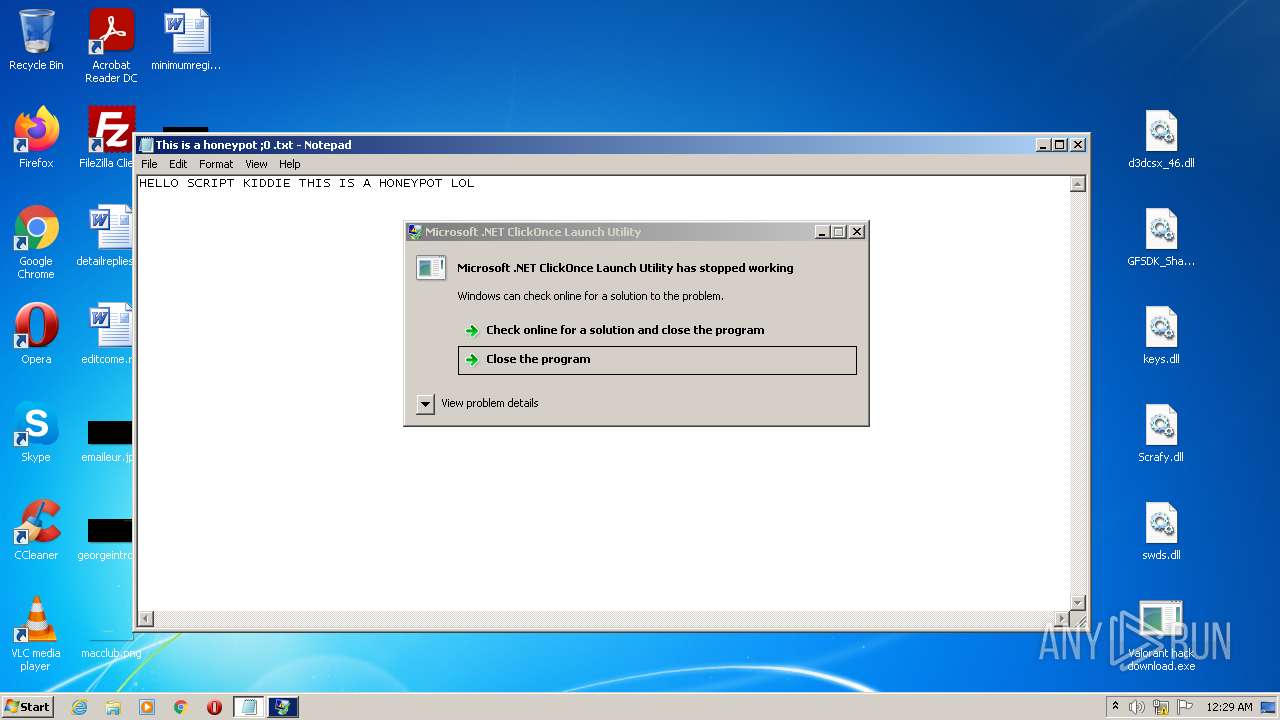
| 99096 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe | Valorant hack download.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET ClickOnce Launch Utility Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
Arkei(PID) Process(99096) AppLaunch.exe C2 (3)https://t.me/larsenup https://ioc.exchange/@zebra54 http://5.161.120.43:80hello Version54.9 BotNet1375 Options URL marker927 Strings (502)%;vu E_ 9GEYacq keystore Ethereum" \Ethereum\ Electrum \Electrum\wallets\ ElectrumLTC \Electrum-LTC\wallets\ Exodus \Exodus\ exodus.conf.json window-state.json \Exodus\exodus.wallet\ passphrase.json seed.seco info.seco ElectronCash \ElectronCash\wallets\ default_wallet MultiDoge \MultiDoge\ multidoge.wallet Jaxx_Desktop_Old \jaxx\Local Storage\ file__0.localstorage Atomic \atomic\Local Storage\leveldb\ 000003.log CURRENT LOCK LOG MANIFEST-000001 0000* Binance \Binance\ app-store.json Coinomi \Coinomi\Coinomi\wallets\ *.wallet *.config wallet_path SOFTWARE\monero-project\monero-core \Monero\ C:\ProgramData\ .exe RECYCLE.BIN Config.Msi System Volume Information msdownld.tmp Recovery Local\Temp Recycle.Bin MicrosoftEdge\Cookies Local\Packages Local\NuGet Roaming\WinRAR Local\Microsoft fee_estimates peers mempool banlist governance mncache mnpayments netfulfilled Login Data Cookies Web Data logins.json formSubmitURL usernameField encryptedUsername encryptedPassword guid SELECT origin_url, username_value, password_value FROM logins SELECT name, value FROM autofill SELECT name_on_card, expiration_month, expiration_year, card_number_encrypted FROM credit_cards SELECT target_path, tab_url from downloads SELECT url FROM urls SELECT HOST_KEY, is_httponly, path, is_secure, (expires_utc/1000000)-11644480800, name, encrypted_value from cookies \AppData\Roaming\FileZilla\recentservers.xml <Host> <Port> <User> <Pass encoding="base64"> Soft: FileZilla Mozilla Firefox \Mozilla\Firefox\Profiles\ Pale Moon \Moonchild Productions\Pale Moon\Profiles\ Google Chrome \Google\Chrome\User Data\ Chromium \Chromium\User Data\ Amigo \Amigo\User Data\ Torch \Torch\User Data\ Comodo Dragon \Comodo\Dragon\User Data\ Epic Privacy Browser \Epic Privacy Browser\User Data\ Vivaldi \Vivaldi\User Data\ CocCoc \CocCoc\Browser\User Data\ Cent Browser \CentBrowser\User Data\ TorBro Browser \TorBro\Profile\ Chedot Browser \Chedot\User Data\ Brave_Old \brave\ 7Star \7Star\7Star\User Data\ Microsoft Edge \Microsoft\Edge\User Data\ 360 Browser \360Browser\Browser\User Data\ QQBrowser \Tencent\QQBrowser\User Data\ Opera \Opera Software\Opera Stable\ OperaGX \Opera Software\Opera GX Stable\ Local State Cookies TRUE FALSE gdi32.dll ole32.dll user32.dll psapi.dll BCRYPT.DLL BCryptCloseAlgorithmProvider BCryptDestroyKey BCryptOpenAlgorithmProvider BCryptSetProperty BCryptGenerateSymmetricKey BCryptDecrypt CRYPT32.DLL CryptUnprotectData CryptStringToBinaryA C:\ProgramData\nss3.dll NSS_Init NSS_Shutdown PK11_GetInternalKeySlot PK11_FreeSlot PK11_Authenticate PK11SDR_Decrypt RegOpenKeyExA RegQueryValueExA RegCloseKey RegOpenKeyExW RegGetValueW RegEnumKeyExA RegGetValueA GetCurrentHwProfileA wininet.dll InternetCloseHandle InternetReadFile HttpSendRequestA HttpOpenRequestA InternetConnectA InternetOpenA HttpAddRequestHeadersA HttpQueryInfoA InternetSetFilePointer InternetOpenUrlA InternetSetOptionA DeleteUrlCacheEntry CreateCompatibleBitmap SelectObject BitBlt DeleteObject CreateDCA GetDeviceCaps CreateCompatibleDC CoCreateInstance CoUninitialize GetDesktopWindow ReleaseDC GetKeyboardLayoutList CharToOemA GetDC wsprintfA EnumDisplayDevicesA GetSystemMetrics GetModuleFileNameExA GetModuleBaseNameA EnumProcessModules ibnejdfjmmkpcnlpebklmnkoeoihofec TronLink nkbihfbeogaeaoehlefnkodbefgpgknn MetaMask fhbohimaelbohpjbbldcngcnapndodjp BinanceChainWallet ffnbelfdoeiohenkjibnmadjiehjhajb Yoroi jbdaocneiiinmjbjlgalhcelgbejmnid NiftyWallet afbcbjpbpfadlkmhmclhkeeodmamcflc MathWallet hnfanknocfeofbddgcijnmhnfnkdnaad Coinbase hpglfhgfnhbgpjdenjgmdgoeiappafln Guarda blnieiiffboillknjnepogjhkgnoapac EQUALWallet cjelfplplebdjjenllpjcblmjkfcffne JaxxLiberty fihkakfobkmkjojpchpfgcmhfjnmnfpi BitAppWallet kncchdigobghenbbaddojjnnaogfppfj iWallet amkmjjmmflddogmhpjloimipbofnfjih Wombat nlbmnnijcnlegkjjpcfjclmcfggfefdm MewCx nanjmdknhkinifnkgdcggcfnhdaammmj GuildWallet fnjhmkhhmkbjkkabndcnnogagogbneec RoninWallet cphhlgmgameodnhkjdmkpanlelnlohao NeoLine nhnkbkgjikgcigadomkphalanndcapjk CloverWallet kpfopkelmapcoipemfendmdcghnegimn LiqualityWallet aiifbnbfobpmeekipheeijimdpnlpgpp Terra_Station dmkamcknogkgcdfhhbddcghachkejeap Keplr fhmfendgdocmcbmfikdcogofphimnkno Sollet cnmamaachppnkjgnildpdmkaakejnhae AuroWallet jojhfeoedkpkglbfimdfabpdfjaoolaf PolymeshWallet flpiciilemghbmfalicajoolhkkenfel ICONex fnnegphlobjdpkhecapkijjdkgcjhkib Harmony aeachknmefphepccionboohckonoeemg Coin98 cgeeodpfagjceefieflmdfphplkenlfk EVER Wallet pdadjkfkgcafgbceimcpbkalnfnepbnk KardiaChain imloifkgjagghnncjkhggdhalmcnfklk Trezor Password Manager acmacodkjbdgmoleebolmdjonilkdbch Rabby bfnaelmomeimhlpmgjnjophhpkkoljpa Phantom ejbalbakoplchlghecdalmeeeajnimhm odbfpeeihdkbihmopkbjmoonfanlbfcl BraveWallet fhilaheimglignddkjgofkcbgekhenbh Oxygen (Atomic) mgffkfbidihjpoaomajlbgchddlicgpn PaliWallet aodkkagnadcbobfpggfnjeongemjbjca BoltX hmeobnfnfcmdkdcmlblgagmfpfboieaf XdefiWallet lpfcbjknijpeeillifnkikgncikgfhdo NamiWallet dngmlblcodfobpdpecaadgfbcggfjfnm MaiarDeFiWallet lpilbniiabackdjcionkobglmddfbcjo WavesKeeper bhhhlbepdkbapadjdnnojkbgioiodbic Solflare dkdedlpgdmmkkfjabffeganieamfklkm CyanoWallet hcflpincpppdclinealmandijcmnkbgn KHC mnfifefkajgofkcjkemidiaecocnkjeh TezBox ookjlbkiijinhpmnjffcofjonbfbgaoc Temple jnkelfanjkeadonecabehalmbgpfodjm Goby bhghoamapcdpbohphigoooaddinpkbai Authenticator gaedmjdfmmahhbjefcbgaolhhanlaolb Authy oeljdldpnmdbchonielidgobddffflal EOS Authenticator ilgcnhelpchnceeipipijaljkblbcobl GAuth Authenticator \com.liberty.jaxx\IndexedDB\file__0.indexeddb.leveldb\ Jaxx_Desktop \Daedalus Mainnet\wallets\ Daedalus Mainnet she*.sqlite \Blockstream\Green\wallets\ Blockstream Green \WalletWasabi\Client\Wallets\ Wasabi Wallet \discord\ Discord Local Storage leveldb Session Storage \Soft\Discord\discord_tokens.txt dQw4w9WgXcQ: Discord Token: CreateThread GlobalMemoryStatusEx IsWow64Process GetUserDefaultLocaleName GetSystemInfo WideCharToMultiByte LocalFree HeapAlloc GetProcessHeap CreateFileA GetFileSize ReadFile CloseHandle GetLogicalDriveStringsA lstrlenA GetDriveTypeA lstrcpyA MultiByteToWideChar FindFirstFileA FindNextFileA FindClose GetLastError lstrcpynA GlobalLock GlobalSize FreeLibrary GetLocaleInfoA GetCurrentProcessId OpenProcess GetFileSizeEx GetTimeZoneInformation TzSpecificLocalTimeToSystemTime CopyFileA DeleteFileA GetCurrentDirectoryA SetFilePointer HeapFree SystemTimeToFileTime GetLocalTime SetFileTime WriteFile GetFileAttributesA GetFileAttributesW LocalFileTimeToFileTime MapViewOfFile UnmapViewOfFile FileTimeToSystemTime CreateFileMappingA GetFileInformationByHandle GetEnvironmentVariableA SetEnvironmentVariableA GetTickCount OpenEventA CreateEventA CreateToolhelp32Snapshot Process32First Process32Next GetWindowsDirectoryA GetVolumeInformationA shell32.dll shlwapi.dll dbghelp.dll gdiplus.dll CryptBinaryToStringA RegEnumValueA GetFileSecurityA OpenProcessToken DuplicateToken MapGenericMask AccessCheck InternetCrackUrlA CoInitialize CreateStreamOnHGlobal GetHGlobalFromStream GetWindowRect GetWindowDC CloseWindow ShellExecuteExA SHFileOperationA SHGetFolderPathA PathMatchSpecW PathMatchSpecA StrCmpCA StrCmpCW StrStrA PathFindFileNameA SymMatchString GdipGetImageEncodersSize GdipGetImageEncoders GdipCreateBitmapFromHBITMAP GdiplusStartup GdiplusShutdown GdipSaveImageToStream GdipDisposeImage GdipFree sqlite3_open sqlite3_prepare_v2 sqlite3_step sqlite3_column_text sqlite3_finalize sqlite3_close sqlite3_column_bytes sqlite3_column_blob \Opera Software\ \Opera Stable\ \Opera GX Stable\ \CryptoTab Browser\User Data\ CryptoTab Browser \BraveSoftware\Brave-Browser\User Data\ Brave \Thunderbird\Profiles\ Thunderbird \Telegram Desktop\ key_datas map* D877F783D5D3EF8C* A7FDF864FBC10B77* A92DAA6EA6F891F2* F8806DD0C461824F* \Soft\Telegram\ \passwords.txt "os_crypt":{"encrypted_key":" Soft: Host: Login: Password: Network SELECT host, isHttpOnly, path, isSecure, expiry, name, value FROM moz_cookies SELECT url FROM moz_places SELECT fieldname, value FROM moz_formhistory History cookies.sqlite formhistory.sqlite places.sqlite *.localstorage \Authy Desktop\Local Storage\ \Soft\Authy\ \Authy Desktop\Local Storage\leveldb\ \Soft\AuthyNew\ Soft: WinSCP HostName PortNumber UserName Password Security UseMasterPassword Local Extension Settings Sync Extension Settings IndexedDB kjmoohlgokccodicjjfebfomlbljgfhk RoninWalletEdge sqlite3.dll Version: Date: MachineID: GUID: HWID: Path: Work Dir: In memory Windows: Computer Name: User Name: Display Resolution: Display Language: Keyboard Languages: Local Time: TimeZone: [Hardware] Processor: CPU Count: RAM: VideoCard: [Processes] [Software] \information.txt %APPDATA% %LOCALAPPDATA% %USERPROFILE% %DESKTOP% %DOCUMENTS% %PROGRAMFILES% %PROGRAMFILES_86% %RECENT% %DRIVE_FIXED% %DRIVE_REMOVABLE% *%RECENT%* *%DRIVE_FIXED%* *%DRIVE_REMOVABLE%* C:\Windows\ C:\\Windows\ C:\\\Windows\ | |||||||||||||||
Total events
6 651
Read events
6 595
Write events
56
Delete events
0
Modification events
| (PID) Process: | (676) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (676) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (676) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (676) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (676) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (676) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (676) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Valorant hack download.rar | |||
| (PID) Process: | (676) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (676) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (676) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
10
Suspicious files
7
Text files
1
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb676.9655\Scrafy.dll | — | |
MD5:— | SHA256:— | |||
| 676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb676.9655\Valorant hack download.exe | — | |
MD5:— | SHA256:— | |||
| 99096 | AppLaunch.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
| 99096 | AppLaunch.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:— | SHA256:— | |||
| 99096 | AppLaunch.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\738FBC066DBD9E6001113366624890A3_53C5D34017BDB72400155AC2819BA60D | binary | |
MD5:— | SHA256:— | |||
| 99096 | AppLaunch.exe | C:\ProgramData\34293030441592792528436368 | — | |
MD5:— | SHA256:— | |||
| 99096 | AppLaunch.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\738FBC066DBD9E6001113366624890A3_53C5D34017BDB72400155AC2819BA60D | der | |
MD5:— | SHA256:— | |||
| 99096 | AppLaunch.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\513D4F0B.txt | text | |
MD5:— | SHA256:— | |||
| 99096 | AppLaunch.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 99096 | AppLaunch.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
4
DNS requests
3
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
99096 | AppLaunch.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
99096 | AppLaunch.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
99096 | AppLaunch.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQC2T6rhHiP0ng%3D%3D | US | der | 1.74 Kb | whitelisted |
99096 | AppLaunch.exe | POST | 200 | 23.88.115.141:80 | http://23.88.115.141/ | DE | text | 4 b | malicious |
99096 | AppLaunch.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b55ad62e5c2821cf | US | compressed | 4.70 Kb | whitelisted |
99096 | AppLaunch.exe | GET | 200 | 23.88.115.141:80 | http://23.88.115.141/1375 | DE | text | 107 b | malicious |
99096 | AppLaunch.exe | POST | 200 | 23.88.115.141:80 | http://23.88.115.141/ | DE | text | 4 b | malicious |
99096 | AppLaunch.exe | POST | 200 | 23.88.115.141:80 | http://23.88.115.141/ | DE | text | 4 b | malicious |
99096 | AppLaunch.exe | GET | 200 | 23.88.115.141:80 | http://23.88.115.141/4641438218.zip | DE | compressed | 2.56 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
99096 | AppLaunch.exe | 149.154.167.99:443 | t.me | Telegram Messenger Inc | GB | malicious |
99096 | AppLaunch.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
99096 | AppLaunch.exe | 192.124.249.23:80 | ocsp.godaddy.com | SUCURI-SEC | US | suspicious |
99096 | AppLaunch.exe | 23.88.115.141:80 | — | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t.me |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
99096 | AppLaunch.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
99096 | AppLaunch.exe | A Network Trojan was detected | ET TROJAN Arkei/Vidar/Mars Stealer Variant |
99096 | AppLaunch.exe | A Network Trojan was detected | ET TROJAN Arkei/Vidar/Mars Stealer Variant |
99096 | AppLaunch.exe | A Network Trojan was detected | ET TROJAN Arkei/Vidar/Mars Stealer Variant |
2 ETPRO signatures available at the full report