| File name: | _d9b01a4e8529655fff9f35abda18fb311400003c51345f0627a534df5785f3e6.txt |
| Full analysis: | https://app.any.run/tasks/c4b856e4-cacc-4223-b37d-38003213b933 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 25, 2026, 16:32:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF, LF line terminators |
| MD5: | 69D7E7890E622C8C2FC4D5E3D3C624E8 |
| SHA1: | A84F349A6DE349F656B948B9256AD857F2EA5A6E |
| SHA256: | D9B01A4E8529655FFF9F35ABDA18FB311400003C51345F0627A534DF5785F3E6 |
| SSDEEP: | 24576:e+6SBQso2bT0Anawi2CZA3Umiwj4oKnt56FAv0fyu18Yb9Xz:B6SBUWN9hunmFa/i |
MALICIOUS
Renames files like ransomware
- powershell.exe (PID: 5420)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 2528)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 2528)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 2528)
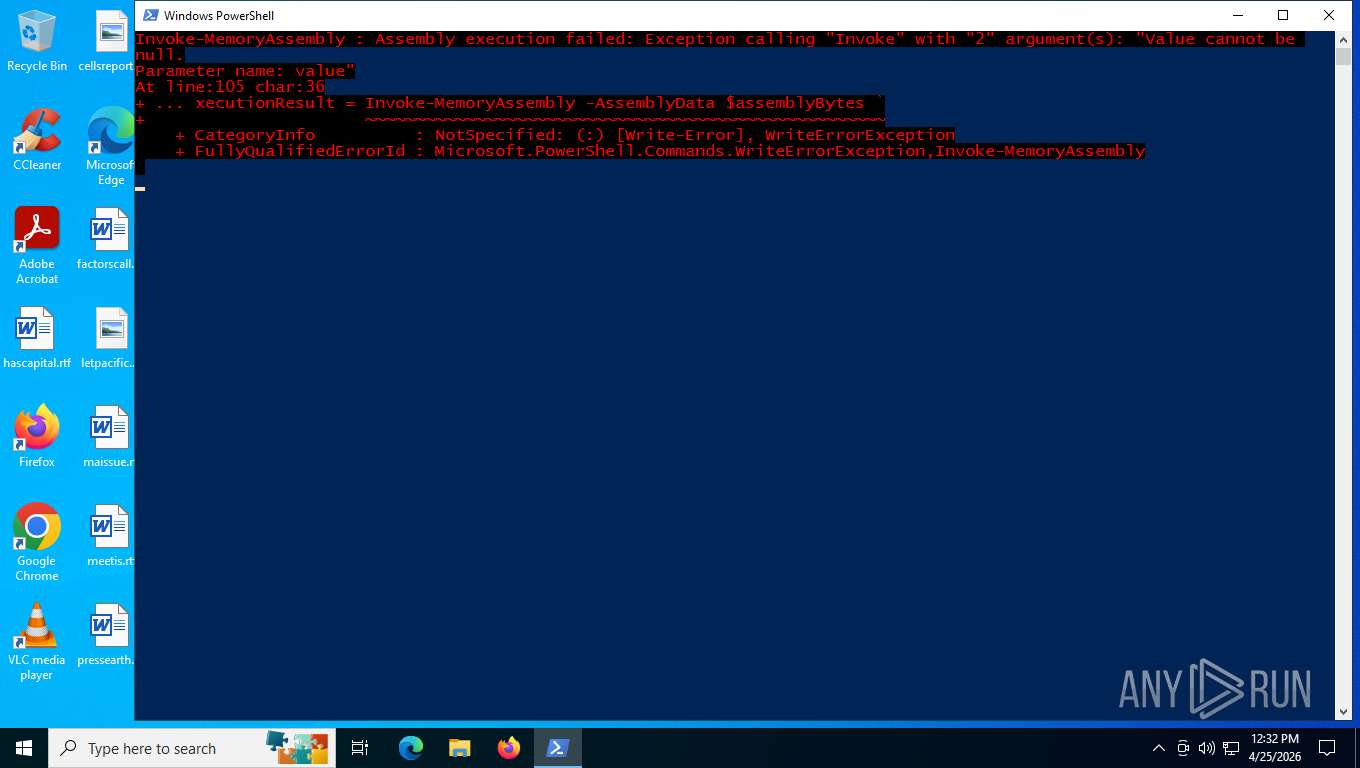
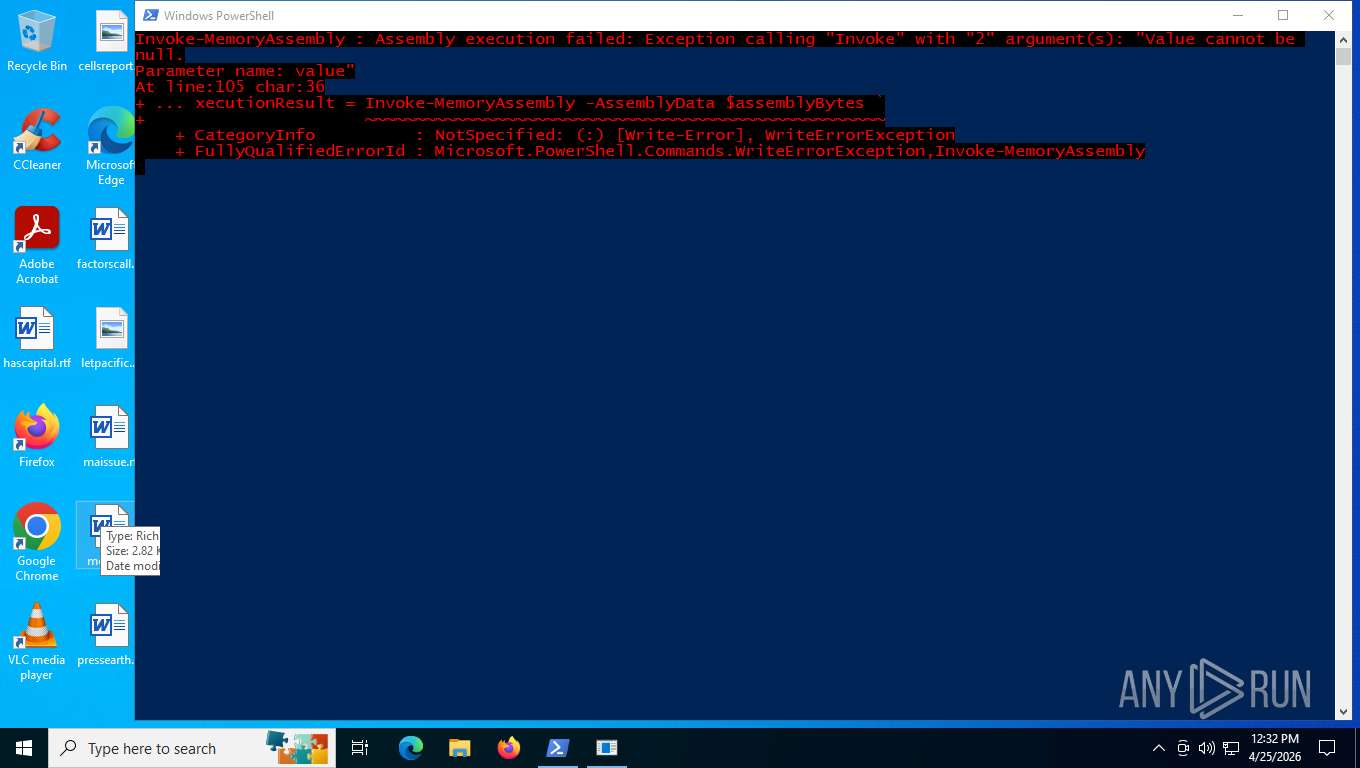
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 2528)
AGENTTESLA has been detected (YARA)
- aspnet_compiler.exe (PID: 8036)
SUSPICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 2528)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2528)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 2528)
Checks for external IP
- aspnet_compiler.exe (PID: 8036)
Potential Corporate Privacy Violation
- aspnet_compiler.exe (PID: 8036)
INFO
Manual execution by a user
- powershell.exe (PID: 2528)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2528)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 2528)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2528)
Reads the machine GUID from the registry
- aspnet_compiler.exe (PID: 8036)
Checks supported languages
- aspnet_compiler.exe (PID: 8036)
Reads the computer name
- aspnet_compiler.exe (PID: 8036)
Disables trace logs
- aspnet_compiler.exe (PID: 8036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(8036) aspnet_compiler.exe
Hosts (1)box5585.bluehost.com
Ports (1)26
Protocolsmtp
Usernamecontactus7708080200@atlantapostcaps.com
PasswordSnugglebus2212!
Total processes
143
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1152 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1312 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2528 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\_d9b01a4e8529655fff9f35abda18fb311400003c51345f0627a534df5785f3e6.txt.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2840 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4312 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4336 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4968 | \??\C:\WINDOWS\system32\conhost.exe 0x4 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5420 | powershell -NoProfile -NonInteractive -ExecutionPolicy Bypass -Command "& { $ErrorActionPreference = 'Stop'; $src = [Environment]::ExpandEnvironmentVariables('C:\Users\admin\Desktop\_d9b01a4e8529655fff9f35abda18fb311400003c51345f0627a534df5785f3e6.txt'); $dst = [Environment]::ExpandEnvironmentVariables('C:\Users\admin\Desktop\_d9b01a4e8529655fff9f35abda18fb311400003c51345f0627a534df5785f3e6.txt.ps1'); Move-Item -LiteralPath $src -Destination $dst -Force }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6804 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 7936 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
11 822
Read events
11 807
Write events
15
Delete events
0
Modification events
| (PID) Process: | (4312) slui.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\sppcomapi.dll,-3200 |
Value: Software Licensing | |||
| (PID) Process: | (8036) aspnet_compiler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\aspnet_compiler_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (8036) aspnet_compiler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\aspnet_compiler_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (8036) aspnet_compiler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\aspnet_compiler_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (8036) aspnet_compiler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\aspnet_compiler_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (8036) aspnet_compiler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\aspnet_compiler_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (8036) aspnet_compiler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\aspnet_compiler_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (8036) aspnet_compiler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\aspnet_compiler_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (8036) aspnet_compiler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\aspnet_compiler_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (8036) aspnet_compiler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\aspnet_compiler_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
4
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5420 | powershell.exe | C:\Users\admin\Desktop\_d9b01a4e8529655fff9f35abda18fb311400003c51345f0627a534df5785f3e6.txt.ps1 | text | |
MD5:69D7E7890E622C8C2FC4D5E3D3C624E8 | SHA256:D9B01A4E8529655FFF9F35ABDA18FB311400003C51345F0627A534DF5785F3E6 | |||
| 2528 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7PF9HEKV4ZYZDDWIROP2.temp | binary | |
MD5:F2A37DBAC1B06C768FB3269EC5480294 | SHA256:E37E28144BEE52172D7110E38E24A040C4614E8CF56DB38F5492B1604720976C | |||
| 5420 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:6786C895213007FE4F7A5690FAD139CE | SHA256:96E619E223F9B7785B3C393BF0D2C55395C52DE1D5417C97D59722A2DE7DAAE3 | |||
| 2528 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:F2A37DBAC1B06C768FB3269EC5480294 | SHA256:E37E28144BEE52172D7110E38E24A040C4614E8CF56DB38F5492B1604720976C | |||
| 2528 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qypna2b2.y5g.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2528 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hftqmyrp.ccg.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2528 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RFe0f4d.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
22
DNS requests
10
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.96:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
4312 | slui.exe | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
8036 | aspnet_compiler.exe | GET | 200 | 104.26.12.205:443 | https://api.ipify.org/ | US | text | 14 b | unknown |
8036 | aspnet_compiler.exe | GET | 200 | 104.26.13.205:443 | https://api.ipify.org/ | US | text | 14 b | unknown |
3280 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | US | binary | 400 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | US | binary | 400 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | US | binary | 813 b | whitelisted |
4312 | slui.exe | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8124 | slui.exe | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.143:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5392 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5392 | svchost.exe | 2.16.164.96:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5276 | MoUsoCoreWorker.exe | 2.16.164.96:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5392 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
api.ipify.org |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5276 | MoUsoCoreWorker.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2232 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
8036 | aspnet_compiler.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
8036 | aspnet_compiler.exe | Potential Corporate Privacy Violation | ET INFO Possible IP Check api.ipify.org |
— | — | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
— | — | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
8036 | aspnet_compiler.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
8036 | aspnet_compiler.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
8036 | aspnet_compiler.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |