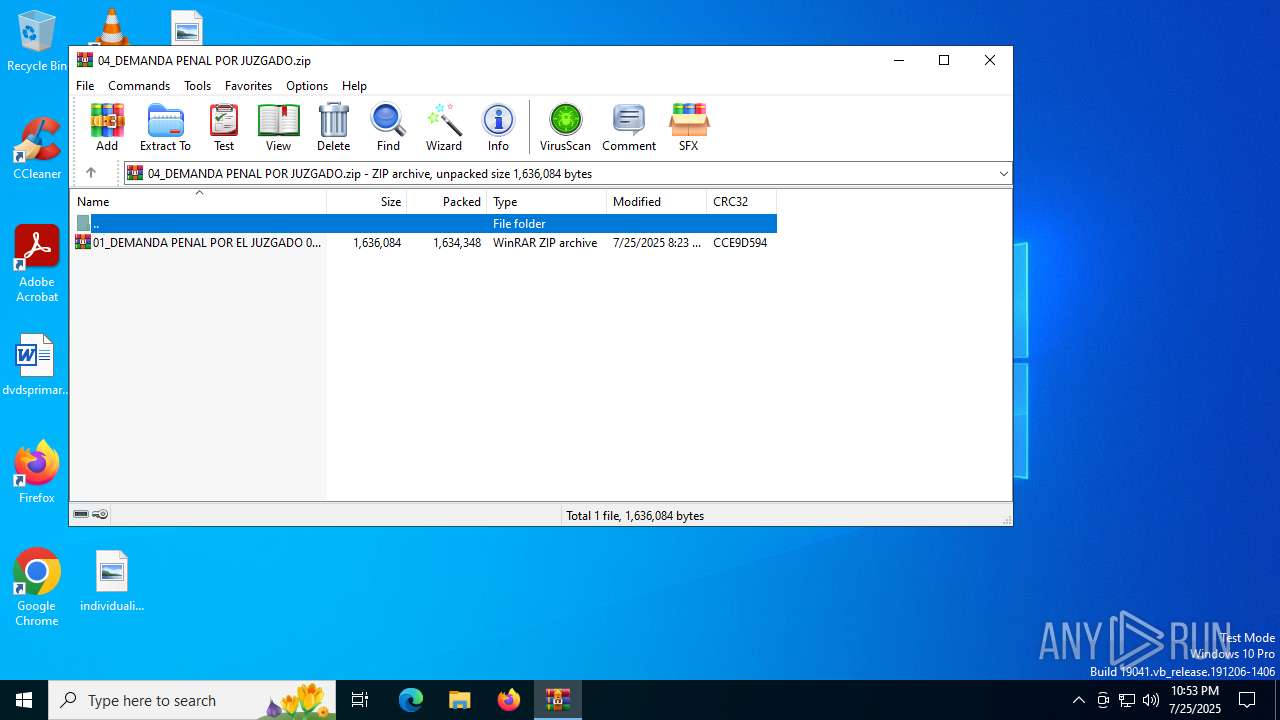
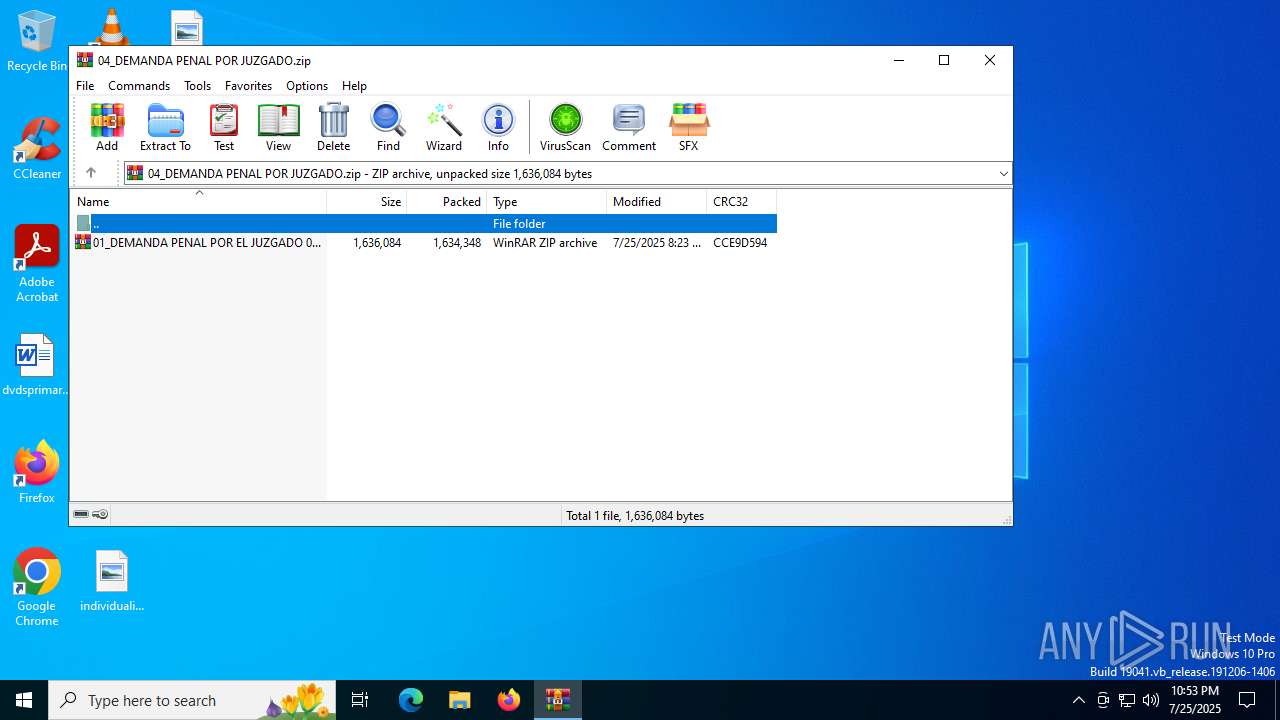
| File name: | 04_DEMANDA PENAL POR JUZGADO.zip |
| Full analysis: | https://app.any.run/tasks/420fd98d-6b54-48cf-a3a1-e0a29008af96 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | July 25, 2025, 22:53:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 7DE5D41C721CA48CD123D92978709034 |
| SHA1: | 3AD56C30F026843A9E145E132E353D28B18A61F8 |
| SHA256: | D94737879781E2FC04A978308E863157985500C31BD84D56C1EFC292048620FA |
| SSDEEP: | 49152:fkPcF2OQDqvsix499qnaQ6AfbRG+v+wDe7JAq4+V9dL2xxvWWDIymm0Aw20traFK:fkPcse54fqnaQZDRG+vze7JZjPl2O9Z1 |
MALICIOUS
ASYNCRAT has been detected (SURICATA)
- InstallUtil.exe (PID: 7032)
ASYNCRAT has been detected (YARA)
- InstallUtil.exe (PID: 7032)
Steals credentials from Web Browsers
- InstallUtil.exe (PID: 7032)
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 7032)
ASYNCRAT has been detected (MUTEX)
- InstallUtil.exe (PID: 7032)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 2972)
- WinRAR.exe (PID: 6668)
Contacting a server suspected of hosting an CnC
- InstallUtil.exe (PID: 7032)
Connects to unusual port
- InstallUtil.exe (PID: 7032)
INFO
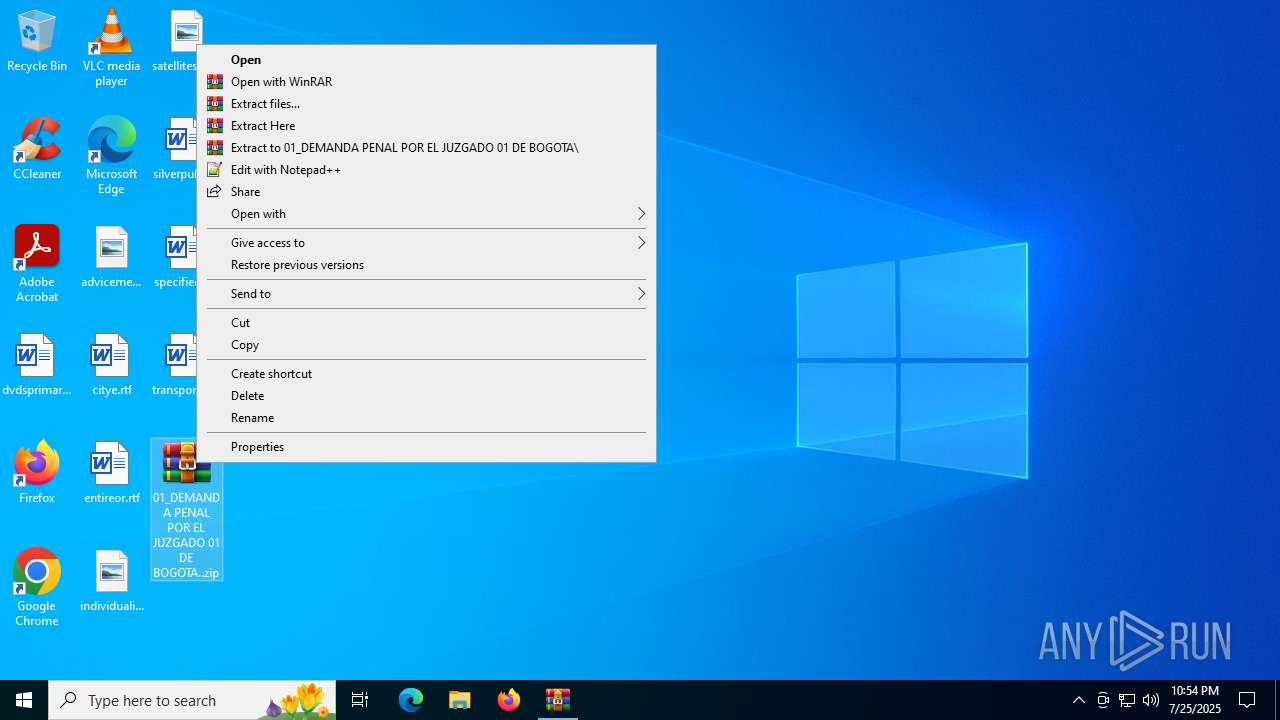
Manual execution by a user
- WinRAR.exe (PID: 6668)
- 01_DEMANDA PENAL POR EL JUZGADO 01 DE BOGOTA..exe (PID: 2140)
The sample compiled with english language support
- WinRAR.exe (PID: 6668)
- WinRAR.exe (PID: 2972)
Checks supported languages
- 01_DEMANDA PENAL POR EL JUZGADO 01 DE BOGOTA..exe (PID: 2140)
- InstallUtil.exe (PID: 7032)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6668)
Reads the computer name
- InstallUtil.exe (PID: 7032)
- 01_DEMANDA PENAL POR EL JUZGADO 01 DE BOGOTA..exe (PID: 2140)
Reads the machine GUID from the registry
- InstallUtil.exe (PID: 7032)
Reads the software policy settings
- InstallUtil.exe (PID: 7032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(7032) InstallUtil.exe
C2 (1)luisdiaz.kozow.com
Ports (1)1458
Version| CRACKED BY https://t.me/xworm_v2
Options
AutoRunfalse
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAOQb7nA/hP/L1XXxqdDJNzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjMwNTI1MDUyMTIyWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAIykAVxs0s6rZ/dwP6ujJtpnj6RSsCsZN6Cfj1InZxSIswX+zNiKJys8xyLlyexoya3ebLp5gOSz...
Server_SignatureCE76co1S6iHFqrHCO77/fjQT9/WqZGB8h7tFyAq4TWK2QwN/YZAaTQiAemDNnppuVpxcRyL4h1N5ZV0hAFIntdR3IKfJZ4tQwwDP2TSaEahotv14zsTkZ7dI3x2AeF36bOM7BUtPMVFETB3jOb54Sy1zdLKuFrzLymrmlpsd32g2oqOSBeG/ewkoBDUR+eEe38QEE7v7RItORkiyfWFTIIVXpOEDALCLnQh8Jnq6bn1Qv2r3IFRGXHs0lEdxVn6G9MgfgvZFSRqImd/GlnQx0+R/6Qs6DomzZzt82UddmbfG...
Keys
AESfa56367a5c1287410707593b21fed91086136e47048c5116e5b9d1a49580e73d
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0809 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:07:25 08:23:20 |
| ZipCRC: | 0xcce9d594 |
| ZipCompressedSize: | 1634348 |
| ZipUncompressedSize: | 1636084 |
| ZipFileName: | 01_DEMANDA PENAL POR EL JUZGADO 01 DE BOGOTA..zip |
Total processes
141
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1864 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\Desktop\01_DEMANDA PENAL POR EL JUZGADO 01 DE BOGOTA..exe" | C:\Users\admin\Desktop\01_DEMANDA PENAL POR EL JUZGADO 01 DE BOGOTA..exe | — | explorer.exe | |||||||||||
User: admin Company: JetBrains s.r.o. Integrity Level: MEDIUM Description: OpenJDK Platform binary Exit code: 4294967295 Version: 21.0.7.0 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
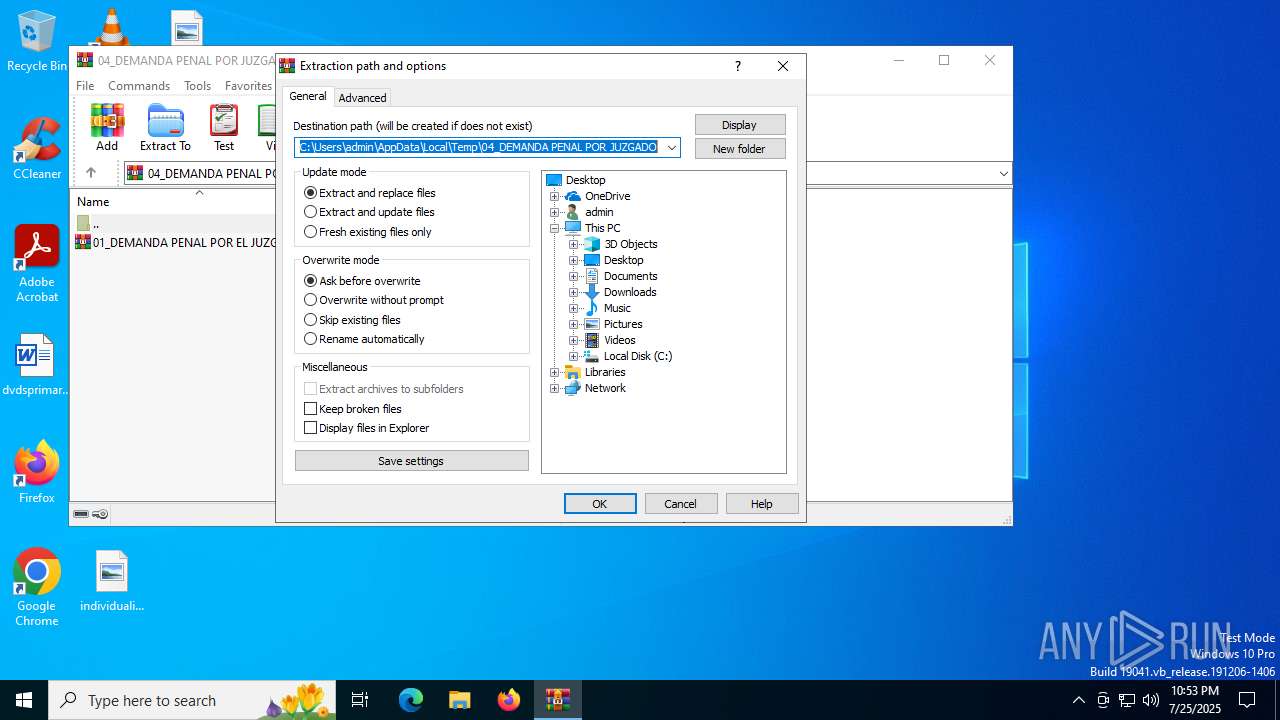
| 2972 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\04_DEMANDA PENAL POR JUZGADO.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 01_DEMANDA PENAL POR EL JUZGADO 01 DE BOGOTA..exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6312 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | — | 01_DEMANDA PENAL POR EL JUZGADO 01 DE BOGOTA..exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Version: 4.8.9037.0 built by: NET481REL1 | |||||||||||||||
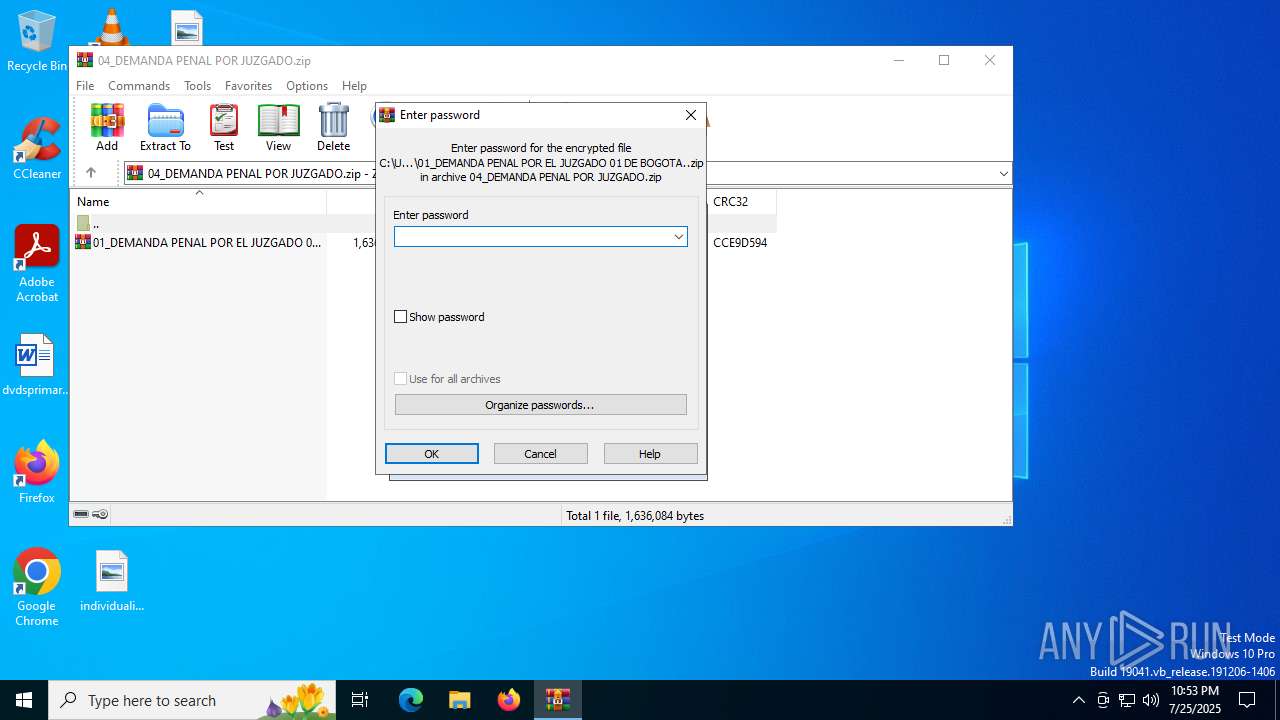
| 6668 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\01_DEMANDA PENAL POR EL JUZGADO 01 DE BOGOTA..zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7032 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\installutil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | 01_DEMANDA PENAL POR EL JUZGADO 01 DE BOGOTA..exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Version: 4.8.9037.0 built by: NET481REL1 Modules
AsyncRat(PID) Process(7032) InstallUtil.exe C2 (1)luisdiaz.kozow.com Ports (1)1458 Version| CRACKED BY https://t.me/xworm_v2 Options AutoRunfalse MutexAsyncMutex_6SI8OkPnk InstallFolder%AppData% Certificates Cert1MIIE8jCCAtqgAwIBAgIQAOQb7nA/hP/L1XXxqdDJNzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjMwNTI1MDUyMTIyWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAIykAVxs0s6rZ/dwP6ujJtpnj6RSsCsZN6Cfj1InZxSIswX+zNiKJys8xyLlyexoya3ebLp5gOSz... Server_SignatureCE76co1S6iHFqrHCO77/fjQT9/WqZGB8h7tFyAq4TWK2QwN/YZAaTQiAemDNnppuVpxcRyL4h1N5ZV0hAFIntdR3IKfJZ4tQwwDP2TSaEahotv14zsTkZ7dI3x2AeF36bOM7BUtPMVFETB3jOb54Sy1zdLKuFrzLymrmlpsd32g2oqOSBeG/ewkoBDUR+eEe38QEE7v7RItORkiyfWFTIIVXpOEDALCLnQh8Jnq6bn1Qv2r3IFRGXHs0lEdxVn6G9MgfgvZFSRqImd/GlnQx0+R/6Qs6DomzZzt82UddmbfG... Keys AESfa56367a5c1287410707593b21fed91086136e47048c5116e5b9d1a49580e73d Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
Total events
9 143
Read events
9 112
Write events
18
Delete events
13
Modification events
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\04_DEMANDA PENAL POR JUZGADO.zip | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
12
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6668 | WinRAR.exe | C:\Users\admin\Desktop\api-ms-win-crt-environment-l1-1-0.dll | executable | |
MD5:4779747A28D729B4D75A90597F77E3B8 | SHA256:DD94754CF7B40513B86C71A4F6E7F4637C9EB5FDE6F03C4AD352160D06D7AC55 | |||
| 6668 | WinRAR.exe | C:\Users\admin\Desktop\VCRUNTIME140.dll | executable | |
MD5:21A6D06CEFF732B7AB8824B299F5BD96 | SHA256:08DEA01A763865A126C2B5578F2D13B8057003AEE4634AAAFEDBB3CBFD89CBD9 | |||
| 6668 | WinRAR.exe | C:\Users\admin\Desktop\01_DEMANDA PENAL POR EL JUZGADO 01 DE BOGOTA..exe | executable | |
MD5:A65DEAEC0FE3861B9114D62E0F744B84 | SHA256:C39FC187F188D6A8218A89A2E158F570820EC600497FAE7F5111EAE02E56877B | |||
| 6668 | WinRAR.exe | C:\Users\admin\Desktop\api-ms-win-crt-heap-l1-1-0.dll | executable | |
MD5:C86C32C0DA9C3C8C962893BE6AFFD6E3 | SHA256:CDCA86F206568133AE030CBE6F0AED62FFD6F0D3DBF779DF4E58F89184ABC643 | |||
| 6668 | WinRAR.exe | C:\Users\admin\Desktop\api-ms-win-crt-filesystem-l1-1-0.dll | executable | |
MD5:688AAA69293546C85D4AC917A2B37E47 | SHA256:009C2EF68EBEB1B8ACD3D1184773BDA239F27D4AE012E6C504BB9D45B448DFF2 | |||
| 2972 | WinRAR.exe | C:\Users\admin\Desktop\01_DEMANDA PENAL POR EL JUZGADO 01 DE BOGOTA..zip | compressed | |
MD5:FDA2C7DFA2B696EA42E5F74564310ADB | SHA256:8E0770383C03CE69210798799D543B10DE088BAC147DCE4703F13F79620B68B1 | |||
| 6668 | WinRAR.exe | C:\Users\admin\Desktop\api-ms-win-crt-convert-l1-1-0.dll | executable | |
MD5:07C16BB5CC8248C2DB5DC01CFB4429A0 | SHA256:F3D1D6BEB302811E9A53622D0009B062AA5DDC0B745467E88E58026742465B96 | |||
| 6668 | WinRAR.exe | C:\Users\admin\Desktop\jli.dll | executable | |
MD5:7D9025845BBA5782BE9CAD1F90167153 | SHA256:C9DA552CCC4074DFC41810245F3637EA71911A4AA8EA35FE27A1C3F94DBBB73F | |||
| 6668 | WinRAR.exe | C:\Users\admin\Desktop\api-ms-win-crt-stdio-l1-1-0.dll | executable | |
MD5:F1762444047F53206D286EB489C066C5 | SHA256:FF1F67BB55CE3710A7BBD921C28F5E9CD027A1EDA81D426833503DE7F830F473 | |||
| 6668 | WinRAR.exe | C:\Users\admin\Desktop\api-ms-win-crt-runtime-l1-1-0.dll | executable | |
MD5:1AA4A74FF779EE4351A88C45AEF45111 | SHA256:5AA6D6D77F9A4C3DFDA8308521F61C2F56037771205BA536EEE709F43796C16F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
23
DNS requests
19
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3768 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5780 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5780 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2168 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
luisdiaz.kozow.com |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2200 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.kozow .com Domain |
7032 | InstallUtil.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
7032 | InstallUtil.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
7032 | InstallUtil.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
7032 | InstallUtil.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |