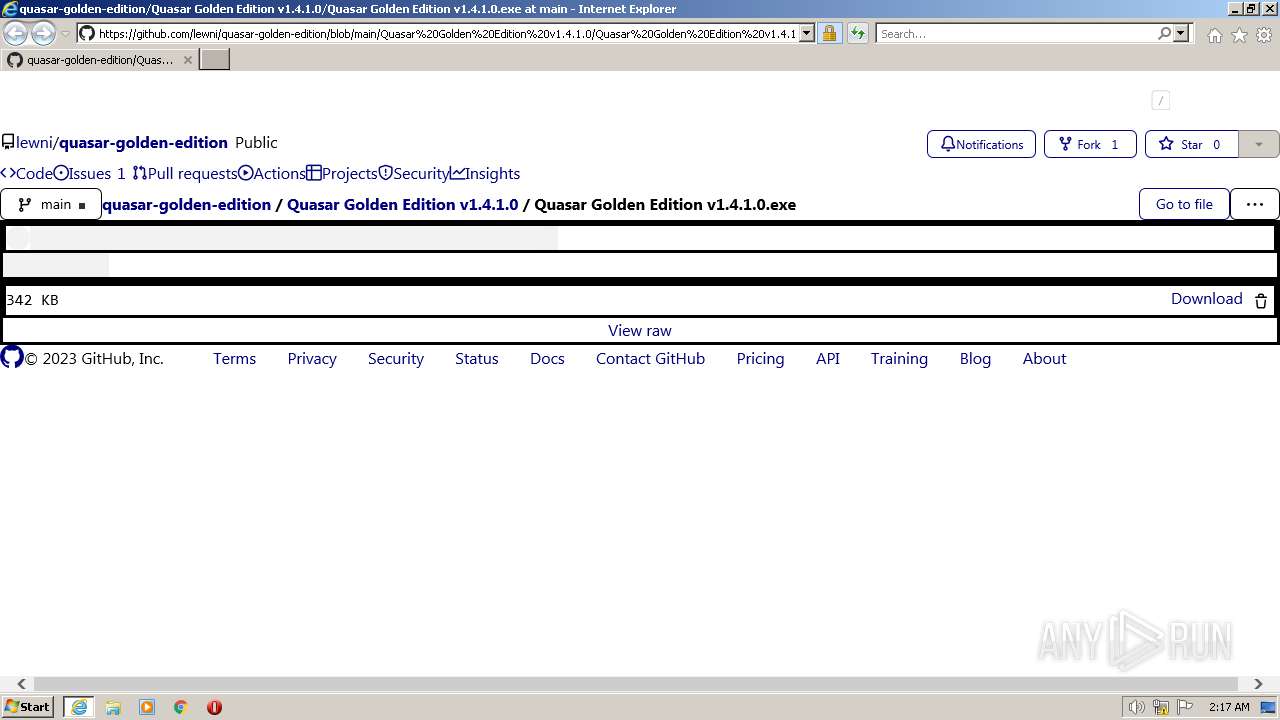
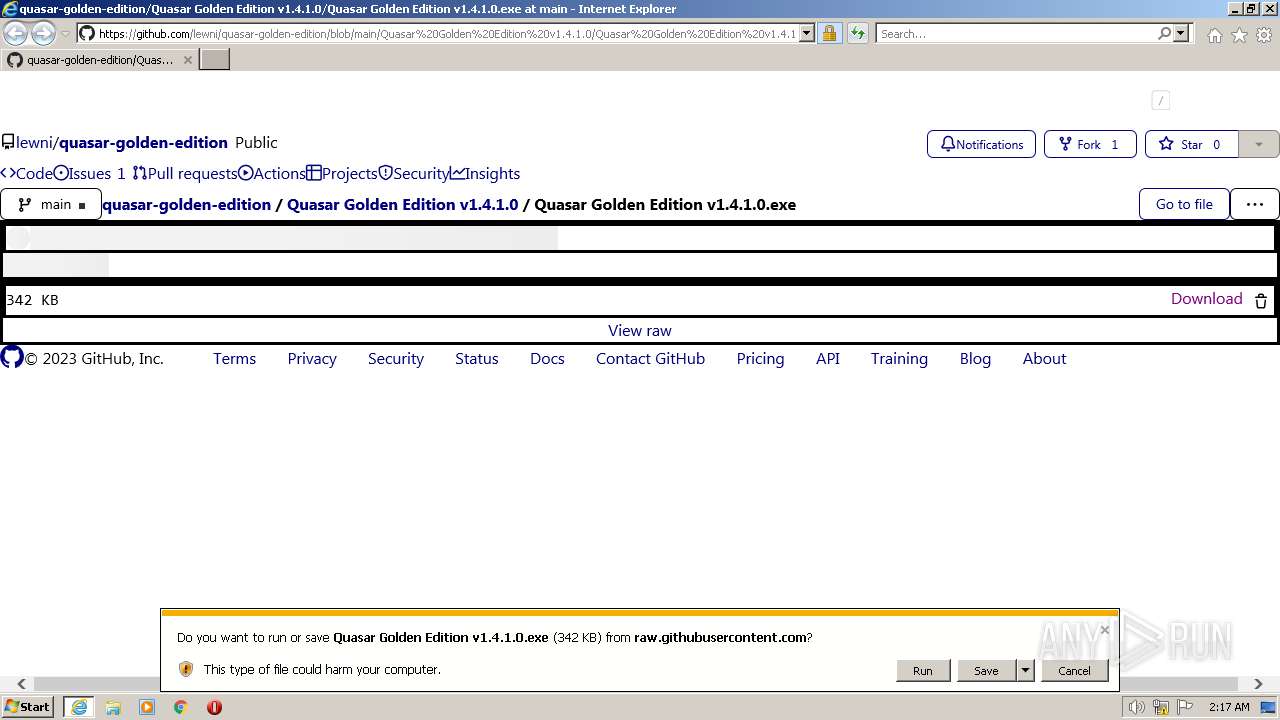
| URL: | https://github.com/lewni/quasar-golden-edition/blob/main/Quasar%20Golden%20Edition%20v1.4.1.0/Quasar%20Golden%20Edition%20v1.4.1.0.exe |
| Full analysis: | https://app.any.run/tasks/0700d6d1-7fc7-4551-b575-f434ed662d2d |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | June 15, 2023, 01:17:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C6FB272789D77FFF9221162AD6A12B9F |
| SHA1: | E8B4C606BF3E380A6B4C53DD0F17A695B79ED5B8 |
| SHA256: | D928F8A258BA0A50717379D3990A2CB9FC76C6A2CFDA669E431E2FF45A7D6CCC |
| SSDEEP: | 3:N8tEd5A4LURLIDycTERp/9igFgByy5SROVYigFgByy5SROVJn:2uY8URLIDycTsp/9iXBypiXByYn |
MALICIOUS
Application was dropped or rewritten from another process
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
- modded loudmic.exe (PID: 3164)
QUASAR was detected
- modded loudmic.exe (PID: 3164)
SUSPICIOUS
Reads the Internet Settings
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
- modded loudmic.exe (PID: 3164)
Cleans NTFS data stream (Zone Identifier)
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
Executable content was dropped or overwritten
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
Starts itself from another location
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
Checks for external IP
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
- modded loudmic.exe (PID: 3164)
INFO
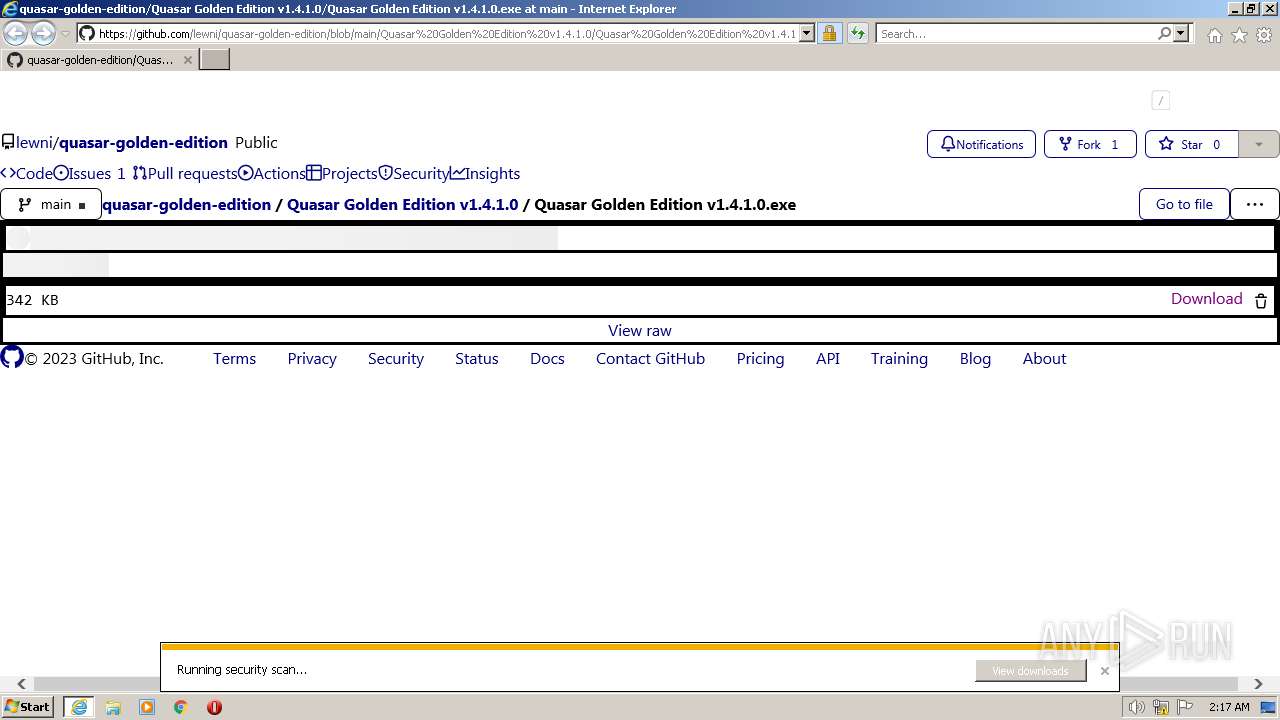
Application launched itself
- iexplore.exe (PID: 2524)
Checks supported languages
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
- modded loudmic.exe (PID: 3164)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2616)
- iexplore.exe (PID: 2524)
The process uses the downloaded file
- iexplore.exe (PID: 2524)
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
Reads Environment values
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
- modded loudmic.exe (PID: 3164)
Reads the machine GUID from the registry
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
- modded loudmic.exe (PID: 3164)
Reads the computer name
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
- modded loudmic.exe (PID: 3164)
The process checks LSA protection
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
- modded loudmic.exe (PID: 3164)
Creates files or folders in the user directory
- Quasar Golden Edition v1.4.1.0.exe (PID: 1248)
- modded loudmic.exe (PID: 3164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1248 | "C:\Users\admin\Downloads\Quasar Golden Edition v1.4.1.0.exe" | C:\Users\admin\Downloads\Quasar Golden Edition v1.4.1.0.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.3.0.0 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://github.com/lewni/quasar-golden-edition/blob/main/Quasar%20Golden%20Edition%20v1.4.1.0/Quasar%20Golden%20Edition%20v1.4.1.0.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2524 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Roaming\SubDir\modded loudmic.exe" | C:\Users\admin\AppData\Roaming\SubDir\modded loudmic.exe | Quasar Golden Edition v1.4.1.0.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Version: 1.3.0.0 Modules
| |||||||||||||||
Total events
14 365
Read events
14 265
Write events
99
Delete events
1
Modification events
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
4
Suspicious files
24
Text files
59
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2616 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\69C6F6EC64E114822DF688DC12CDD86C | binary | |
MD5:812BF8F29E5C51E609543851FE6AFAB3 | SHA256:4901D490B5B30C9B8187A35A074216A82E029F3BB8328AE48EBC2C88F41375AB | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_D222662A57BAA60D2F5EA0D2CC7B2F1C | binary | |
MD5:375494C4E7168073D76490269E4EB7D3 | SHA256:3D7965D68D3C6A1D60768DD1BEC9754D1113B7F1EA0F5ACA1014A9EF70F96D94 | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\light-946902aac6a1[1].css | text | |
MD5:ABF5C64E0F83D6967CB68D3DA8C3A283 | SHA256:D3C6F162D63AA9B7C3A86A7673C40C13194D90A3428AC98B16123DFBC361A43C | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\global-a55bf4a27d6d[1].css | text | |
MD5:E3377D2EDA0C45B921FE2F6410DAACA1 | SHA256:E61827815C41154AB1EF7EAD3B6948B3EE800018056511565D5179868F25870C | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JC0VA0QT.txt | text | |
MD5:4360A4E020E8355EFBA6334CC550E8DC | SHA256:3A49CCEE2AE5D30FB9F4582A13931578B6C8CAFD852248D5078017EB5F87DD9B | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Quasar%20Golden%20Edition%20v1.4.1.0[1].htm | html | |
MD5:FD04150FEBFE22F7753BA78192B8A514 | SHA256:040D30272809385DB39658BD05EF073B8353BE93BD8FA58ED22D8C440A6F3B7D | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\primer-0e3420bbec16[1].css | text | |
MD5:30F2A06E17A202D8F8AFE79405920683 | SHA256:C8E8E6DB20F7B9B971987BB79300F39DB43BCAD30FCB5F3DF16CA951F006BD95 | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:3300CEC21D66034EBDCAA805C49649CC | SHA256:142439DEA4DBB37C4791D5321848E0E20B4CB4D63CB6F524AF3FDC087298A944 | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\github-a03f5b7d8828[1].css | text | |
MD5:8C8558F421942396A086FE88D66849C0 | SHA256:40903560857CD4ACA63BCE16DCB11E275A23E475F454D5AF99C522DCFB9F485B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
39
DNS requests
18
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3164 | modded loudmic.exe | GET | 301 | 172.67.75.176:80 | http://freegeoip.net/xml/ | US | — | — | malicious |
2616 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | binary | 779 b | whitelisted |
3164 | modded loudmic.exe | GET | 200 | 104.237.62.211:80 | http://api.ipify.org/ | US | text | 12 b | shared |
2524 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | binary | 1.47 Kb | whitelisted |
2616 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAzQqL7GMs%2FmReygqbCE%2Bxw%3D | US | binary | 314 b | whitelisted |
1248 | Quasar Golden Edition v1.4.1.0.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | binary | 287 b | malicious |
2616 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1e838ca0fbdf23e2 | US | compressed | 4.70 Kb | whitelisted |
3164 | modded loudmic.exe | GET | 200 | 172.67.75.176:80 | http://freegeoip.net/shutdown | US | html | 1.00 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2616 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2524 | iexplore.exe | 185.199.110.154:443 | github.githubassets.com | FASTLY | US | suspicious |
1248 | Quasar Golden Edition v1.4.1.0.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | malicious |
2616 | iexplore.exe | 185.199.111.133:443 | avatars.githubusercontent.com | FASTLY | US | suspicious |
3164 | modded loudmic.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | malicious |
2524 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2524 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1248 | Quasar Golden Edition v1.4.1.0.exe | A Network Trojan was detected | ET MALWARE Common RAT Connectivity Check Observed |
1248 | Quasar Golden Edition v1.4.1.0.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
1248 | Quasar Golden Edition v1.4.1.0.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
1076 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (freegeiop .net in DNS lookup) |
3164 | modded loudmic.exe | A Network Trojan was detected | ET MALWARE W32/Quasar 1.3/Venom RAT Connectivity Check 3 |
3164 | modded loudmic.exe | A Network Trojan was detected | ET MALWARE W32/Quasar 1.3/Venom RAT Connectivity Check 2 |
3164 | modded loudmic.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup api.ipify.org |
1076 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a Reverse Proxy Service Observed |
2 ETPRO signatures available at the full report