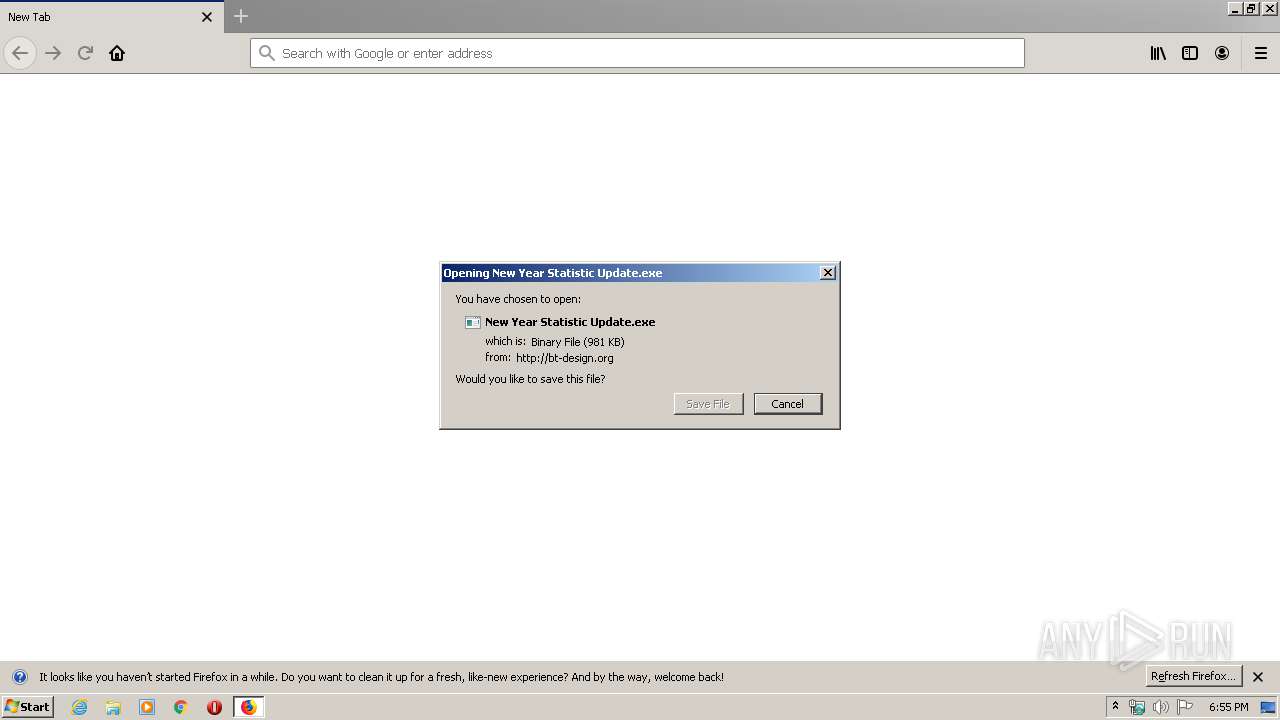
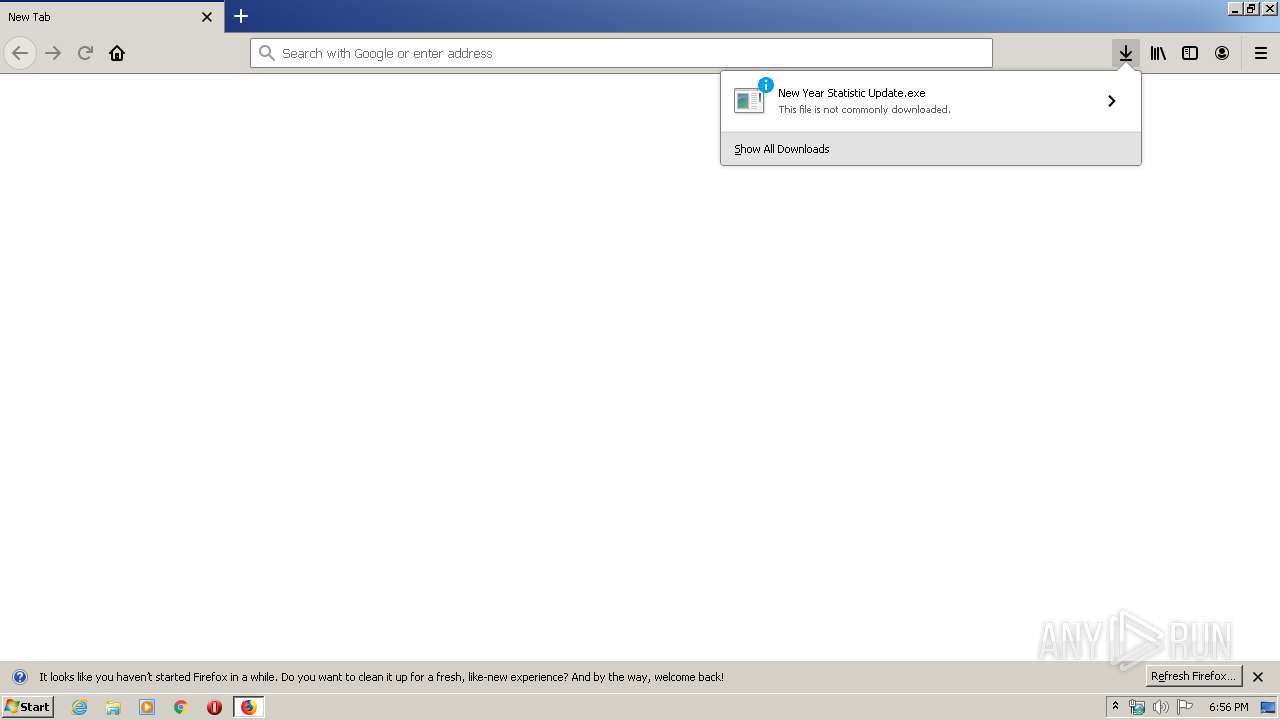
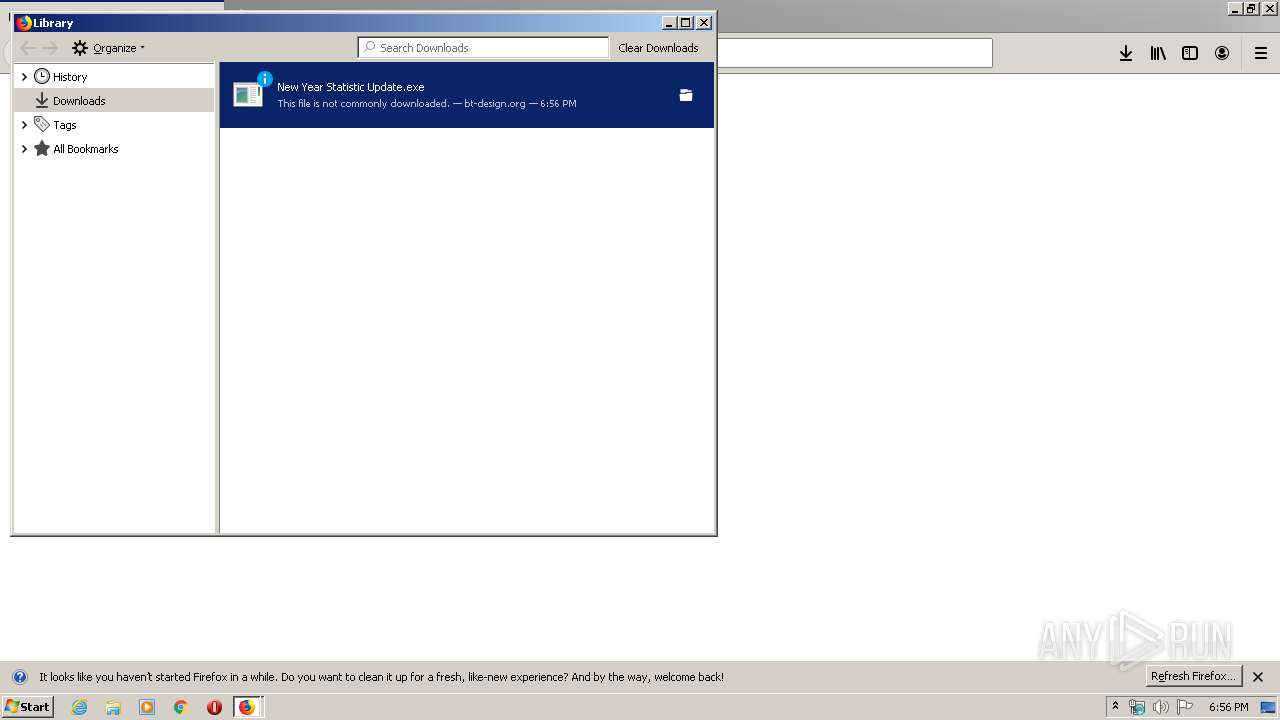
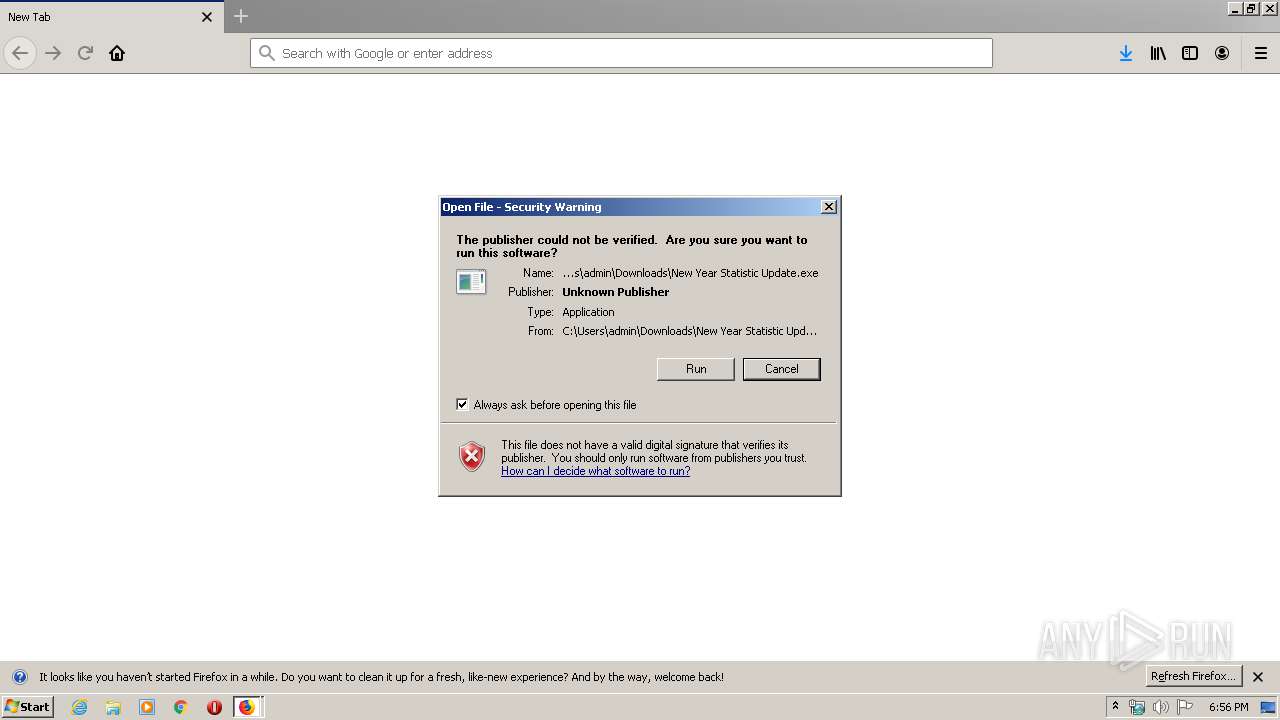
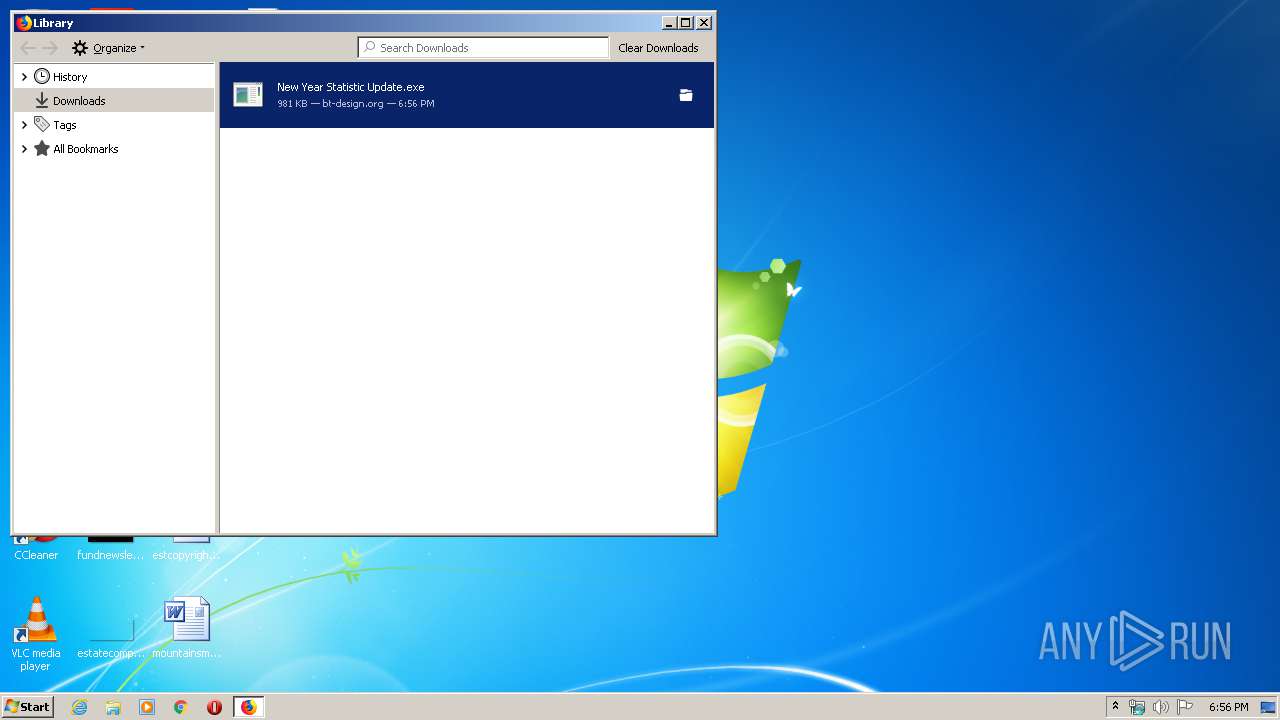
| URL: | http://bt-design.org/file04/New%20Year%20Statistic%20Update.exe |
| Full analysis: | https://app.any.run/tasks/43ea0695-320e-44da-81ed-cdf123b21dba |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | February 21, 2020, 18:55:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 887F5838E4DA13D2560D18AE3529AF5A |
| SHA1: | 49B70CC192A8D311091D023210315505183AB315 |
| SHA256: | D8DDBD59E4FEBC84BB482B81D60D2C7E9ACE15912A4357A4DC62B72E1321951B |
| SSDEEP: | 3:N1KcjIoCKQORGBAFtMWHGgBj:CcrQJg+WHGEj |
MALICIOUS
Application was dropped or rewritten from another process
- New Year Statistic Update.exe (PID: 2072)
- kxyl2v_zzq4an.exe (PID: 3276)
FORMBOOK was detected
- rundll32.exe (PID: 3104)
- explorer.exe (PID: 372)
- Firefox.exe (PID: 3596)
Connects to CnC server
- explorer.exe (PID: 372)
Changes the autorun value in the registry
- rundll32.exe (PID: 3104)
Downloads executable files from the Internet
- firefox.exe (PID: 1024)
Actions looks like stealing of personal data
- rundll32.exe (PID: 3104)
Stealing of credential data
- rundll32.exe (PID: 3104)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 1024)
- DllHost.exe (PID: 2972)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 372)
Executable content was dropped or overwritten
- firefox.exe (PID: 1024)
- explorer.exe (PID: 372)
- DllHost.exe (PID: 2972)
Loads DLL from Mozilla Firefox
- rundll32.exe (PID: 3104)
Creates files in the user directory
- rundll32.exe (PID: 3104)
Executed via COM
- DllHost.exe (PID: 2972)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 3104)
Uses NETSTAT.EXE to discover network connections
- explorer.exe (PID: 372)
INFO
Reads Internet Cache Settings
- firefox.exe (PID: 1024)
- pingsender.exe (PID: 1832)
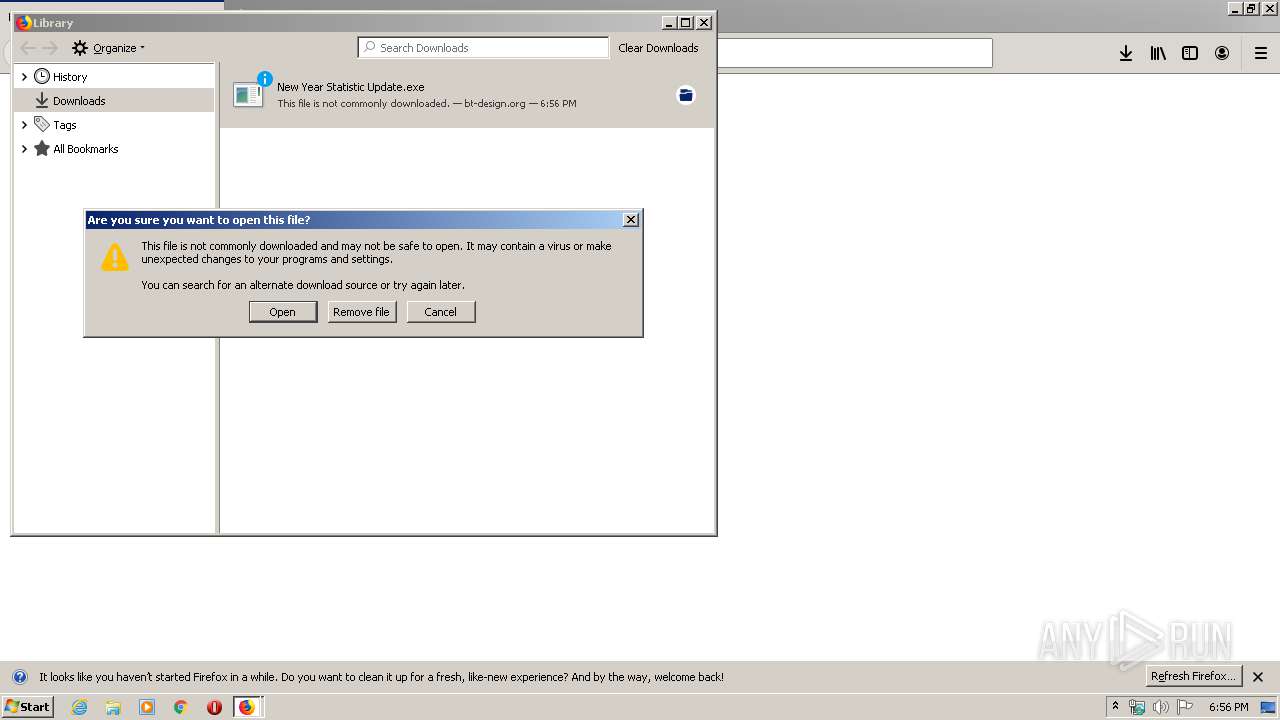
Manual execution by user
- rundll32.exe (PID: 3104)
Application launched itself
- firefox.exe (PID: 1024)
Reads CPU info
- firefox.exe (PID: 1024)
Reads the hosts file
- rundll32.exe (PID: 3104)
Creates files in the user directory
- firefox.exe (PID: 1024)
- Firefox.exe (PID: 3596)
Adds / modifies Windows certificates
- pingsender.exe (PID: 1832)
Changes settings of System certificates
- pingsender.exe (PID: 1832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
15
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://bt-design.org/file04/New%20Year%20Statistic%20Update.exe | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1632 | /c del "C:\Users\admin\Downloads\New Year Statistic Update.exe" | C:\Windows\System32\cmd.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/a8d5c4d6-abbd-4a4b-9e21-f55c1840bed5/main/Firefox/68.0.1/release/20190717172542?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\a8d5c4d6-abbd-4a4b-9e21-f55c1840bed5 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\Downloads\New Year Statistic Update.exe" | C:\Users\admin\Downloads\New Year Statistic Update.exe | — | firefox.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1024.20.1992007167\564075841" -childID 3 -isForBrowser -prefsHandle 3748 -prefMapHandle 3752 -prefsLen 7130 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1024 "\\.\pipe\gecko-crash-server-pipe.1024" 3764 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1024.13.835551517\591221846" -childID 2 -isForBrowser -prefsHandle 2932 -prefMapHandle 2928 -prefsLen 5997 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1024 "\\.\pipe\gecko-crash-server-pipe.1024" 2948 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2972 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3032 | "C:\Windows\System32\NETSTAT.EXE" | C:\Windows\System32\NETSTAT.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3104 | "C:\Windows\System32\rundll32.exe" | C:\Windows\System32\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 504
Read events
919
Write events
2 398
Delete events
1 187
Modification events
| (PID) Process: | (1024) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 0BD24CEE08000000 | |||
| (PID) Process: | (3328) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 545447EE08000000 | |||
| (PID) Process: | (1024) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | 308046O0NS4N39PO |
Value: 00000000090000000E000000CC190500000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF605D425CD146D50100000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003F00000050000000D0BA25000A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED01 | |||
| (PID) Process: | (1024) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1024) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | 308046O0NS4N39PO |
Value: 00000000090000000E000000292F0500000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF605D425CD146D50100000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003F000000500000002DD025000A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED01 | |||
| (PID) Process: | (1024) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
5
Suspicious files
143
Text files
36
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1024 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 1024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 1024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 1024 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 1024 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 1024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 1024 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 1024 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4 | jsonlz4 | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
39
DNS requests
81
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
372 | explorer.exe | GET | — | 184.168.221.51:80 | http://www.africapropertytrust.com/f3a/?BjM=9rxd8&Fdj8-=C4c7eEqenTaNCtU8QHxYIHt8rh6bebQiBX4tSoHM1qc+39pNaLsjfmOqukKEYP1mZ1Jagw== | US | — | — | malicious |
1832 | pingsender.exe | GET | — | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAd1LOvlIi%2FPXH0gOJhMUZg%3D | US | — | — | whitelisted |
1024 | firefox.exe | GET | 200 | 167.114.220.88:80 | http://bt-design.org/file04/New%20Year%20Statistic%20Update.exe | CA | executable | 980 Kb | suspicious |
1024 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
372 | explorer.exe | GET | 302 | 23.20.239.12:80 | http://www.axong.com/f3a/?BjM=9rxd8&Fdj8-=JRywxFHE1Bqh/SLGeRbJ4fpFxmAeKfT0DTyd2pUHr6jM1I+At/CzKtqLjfO9dKONCva1Yg== | US | html | 181 b | shared |
372 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.axong.com/f3a/ | US | — | — | shared |
1832 | pingsender.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/ssca-sha2-g6.crl | US | binary | 4.66 Mb | whitelisted |
372 | explorer.exe | POST | — | 199.188.206.146:80 | http://www.dronv.com/f3a/ | US | — | — | malicious |
372 | explorer.exe | GET | 404 | 199.188.206.146:80 | http://www.dronv.com/f3a/?Fdj8-=iWCR89SdPEq8EBQEurvnlNrMhiq3gvvAtb855XoXJxabysd83ZV2+czX6EqCYV5TB2OmhQ==&BjM=9rxd8 | US | html | 327 b | malicious |
372 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.axong.com/f3a/ | US | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1024 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
1024 | firefox.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1024 | firefox.exe | 172.217.23.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1024 | firefox.exe | 143.204.202.64:443 | tracking-protection.cdn.mozilla.net | — | US | suspicious |
1024 | firefox.exe | 143.204.202.13:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
1024 | firefox.exe | 13.35.253.78:443 | content-signature-2.cdn.mozilla.net | — | US | malicious |
1832 | pingsender.exe | 52.34.188.145:443 | incoming.telemetry.mozilla.org | Amazon.com, Inc. | US | unknown |
1832 | pingsender.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
372 | explorer.exe | 184.168.221.51:80 | www.africapropertytrust.com | GoDaddy.com, LLC | US | malicious |
372 | explorer.exe | 199.188.206.146:80 | www.dronv.com | Namecheap, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
bt-design.org |
| suspicious |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1024 | firefox.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
7 ETPRO signatures available at the full report