| File name: | drw_tr_installer.17451388361620b3111595a016885895.exe |
| Full analysis: | https://app.any.run/tasks/e7a77fcf-fb7a-434c-b8d5-3c9a60bec5c6 |
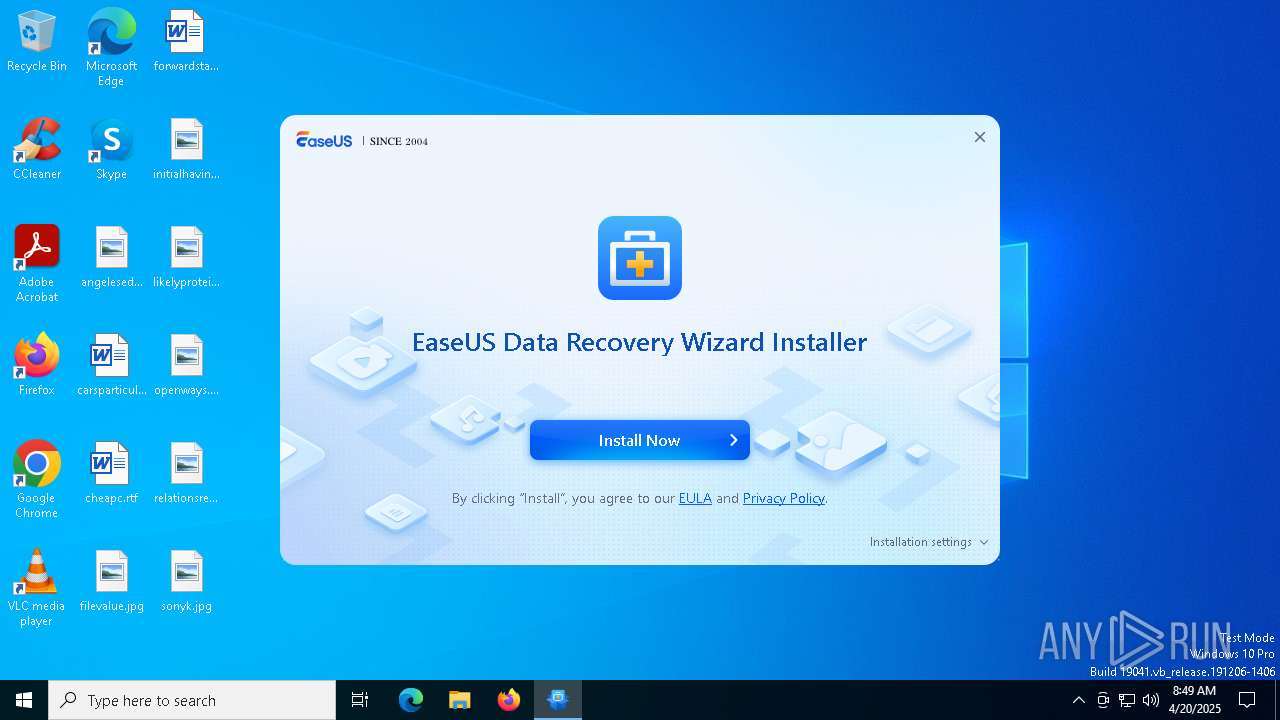
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | April 20, 2025, 08:49:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 84778E894637450FBEA537FE69F942D4 |
| SHA1: | 80384F14A4529181ABF39B14645F0F605CC797E4 |
| SHA256: | D8CEB664154C4B0CEB3A299A89537BC6EDFB637214D36F798EFDFEF336D6D81C |
| SSDEEP: | 98304:CR63l82ZJBM7TQfycwA3bjJD8sBAIzXiN00f6gwmQznz2ALjfZkxjLelce0k0esS:MmKyuS |
MALICIOUS
GEXIN has been detected (SURICATA)
- AliyunWrapExe.exe (PID: 5512)
SUSPICIOUS
Executable content was dropped or overwritten
- drw_tr_installer.17451388361620b3111595a016885895.exe (PID: 2140)
- drw19.3.5.0_trial.exe (PID: 1228)
- drw19.3.5.0_trial.tmp (PID: 5384)
The process drops C-runtime libraries
- drw_tr_installer.17451388361620b3111595a016885895.exe (PID: 2140)
- drw19.3.5.0_trial.tmp (PID: 5384)
Process drops legitimate windows executable
- drw_tr_installer.17451388361620b3111595a016885895.exe (PID: 2140)
- drw19.3.5.0_trial.tmp (PID: 5384)
Reads security settings of Internet Explorer
- EDownloader.exe (PID: 5176)
- AliyunWrapExe.exe (PID: 5512)
- AliyunWrapExe.exe (PID: 2240)
Access to an unwanted program domain was detected
- AliyunWrapExe.exe (PID: 5512)
Reads Microsoft Outlook installation path
- EDownloader.exe (PID: 5176)
Reads Internet Explorer settings
- EDownloader.exe (PID: 5176)
Reads the Windows owner or organization settings
- drw19.3.5.0_trial.tmp (PID: 5384)
INFO
Checks supported languages
- drw_tr_installer.17451388361620b3111595a016885895.exe (PID: 2140)
- EDownloader.exe (PID: 5176)
- InfoForSetup.exe (PID: 7012)
- InfoForSetup.exe (PID: 6808)
- AliyunWrapExe.exe (PID: 5512)
- InfoForSetup.exe (PID: 2096)
- InfoForSetup.exe (PID: 5892)
- InfoForSetup.exe (PID: 920)
- InfoForSetup.exe (PID: 728)
- InfoForSetup.exe (PID: 1328)
- drw19.3.5.0_trial.exe (PID: 1228)
- InfoForSetup.exe (PID: 1532)
- InfoForSetup.exe (PID: 6028)
- drw19.3.5.0_trial.tmp (PID: 5384)
- InfoForSetup.exe (PID: 1568)
- AliyunWrapExe.exe (PID: 2240)
- InfoForSetup.exe (PID: 5364)
- InfoForSetup.exe (PID: 1040)
The sample compiled with english language support
- drw_tr_installer.17451388361620b3111595a016885895.exe (PID: 2140)
- drw19.3.5.0_trial.tmp (PID: 5384)
Create files in a temporary directory
- EDownloader.exe (PID: 5176)
- drw_tr_installer.17451388361620b3111595a016885895.exe (PID: 2140)
- InfoForSetup.exe (PID: 6808)
- AliyunWrapExe.exe (PID: 5512)
- InfoForSetup.exe (PID: 1328)
- drw19.3.5.0_trial.exe (PID: 1228)
- drw19.3.5.0_trial.tmp (PID: 5384)
- AliyunWrapExe.exe (PID: 2240)
Reads the computer name
- EDownloader.exe (PID: 5176)
- InfoForSetup.exe (PID: 7012)
- AliyunWrapExe.exe (PID: 5512)
- AliyunWrapExe.exe (PID: 2240)
- drw19.3.5.0_trial.tmp (PID: 5384)
Checks proxy server information
- AliyunWrapExe.exe (PID: 5512)
- EDownloader.exe (PID: 5176)
- AliyunWrapExe.exe (PID: 2240)
Creates files or folders in the user directory
- AliyunWrapExe.exe (PID: 5512)
- AliyunWrapExe.exe (PID: 2240)
- drw19.3.5.0_trial.tmp (PID: 5384)
Reads the machine GUID from the registry
- EDownloader.exe (PID: 5176)
Creates files in the program directory
- drw19.3.5.0_trial.tmp (PID: 5384)
The sample compiled with chinese language support
- drw19.3.5.0_trial.tmp (PID: 5384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 03:57:48+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
149
Monitored processes
21
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | /SendInfo Window "Home_Installer" Activity "Click_Install" Attribute "{\"Country\":\"United States\",\"Install_Path\":\"C:/Program Files/EaseUS/EaseUS Data Recovery Wizard\",\"Language\":\"English\",\"Os\":\"Microsoft Windows 10\",\"Pageid\":\"17451388361620b3111595a016885895\",\"Timezone\":\"GMT-00:00\"}" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 920 | /SendInfo Window "Home_Installer" Activity "Click_Fold_Custom" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 960 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "C:\Users\admin\AppData\Local\Temp\is-QGKS3.tmp\InfoForSetup.exe" /SendInfo "Window" "Licenseagreement" "Activity" "Click_Accept" "VID" "TR194_2025411AB1-02203" | C:\Users\admin\AppData\Local\Temp\is-QGKS3.tmp\InfoForSetup.exe | — | drw19.3.5.0_trial.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1228 | /verysilent /DIR="C:\Program Files\EaseUS\EaseUS Data Recovery Wizard" /LANG=en agreeImprove= GUID=S-1-5-21-1693682860-607145093-2874071422-1001 xurlID=17451388361620b3111595a016885895 TestID=TR194_2025411AB1-02203 | C:\Users\admin\AppData\Local\Temp\drw19.3.5.0_trial.exe | EDownloader.exe | ||||||||||||
User: admin Company: EaseUS Integrity Level: HIGH Description: EaseUS Data Recovery Wizard Setup Version: 19.3.5.0 Modules
| |||||||||||||||
| 1328 | "C:\Users\admin\AppData\Local\Temp\is-QGKS3.tmp\InfoForSetup.exe" /SendInfo "Window" "Langsel" "Activity" "Click_Confirm" "Attribute" "{\"Language\":\"en\"}" "VID" "TR194_2025411AB1-02203" | C:\Users\admin\AppData\Local\Temp\is-QGKS3.tmp\InfoForSetup.exe | — | drw19.3.5.0_trial.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1532 | /SendInfo Window "Installing" Activity "Info_Start_Install_Program" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1568 | "C:\Users\admin\AppData\Local\Temp\is-QGKS3.tmp\InfoForSetup.exe" /SendInfo "Window" "Selectdestinationlocation" "Activity" "Click_Confirm" "Attribute" "{\"Path\":\"C:/Program Files/EaseUS/EaseUS Data Recovery Wizard\"}" "VID" "TR194_2025411AB1-02203" | C:\Users\admin\AppData\Local\Temp\is-QGKS3.tmp\InfoForSetup.exe | — | drw19.3.5.0_trial.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2096 | /SendInfo Window "Downloading" Activity "Info_Start_Download_Program" Attribute "{\"Downloadfrom\":\"https://d1.easeus.com/drw/trial/drw19.3.5.0_trial.exe\",\"Pageid\":\"17451388361620b3111595a016885895\",\"Testid\":\"TR194_2025411AB1-02203\",\"Version\":\"trial\",\"Versionnumber\":\"19.4\"}" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Local\Temp\drw_tr_installer.17451388361620b3111595a016885895.exe" | C:\Users\admin\AppData\Local\Temp\drw_tr_installer.17451388361620b3111595a016885895.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
3 650
Read events
3 640
Write events
10
Delete events
0
Modification events
| (PID) Process: | (5512) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5512) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5512) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5176) EDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\EASEUS_DOWNLOADER |
| Operation: | write | Name: | test_version_name |
Value: drw_trial_a | |||
| (PID) Process: | (5176) EDownloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5176) EDownloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5176) EDownloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2240) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2240) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2240) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
329
Suspicious files
139
Text files
300
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | drw_tr_installer.17451388361620b3111595a016885895.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\Danish.ini | text | |
MD5:EB6CB6A1EA028CAC7AE61DADC568C2F9 | SHA256:4524116093969EE206FA4F04D84346349ED551B4D7B87D4206E9A12D32AF5D61 | |||
| 2140 | drw_tr_installer.17451388361620b3111595a016885895.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\Polish.ini | text | |
MD5:DEF85351F7FDA76B962D6DE5F86F5FE5 | SHA256:E833E96EA0E4568FDDF90386AFDFF3F9BED6EA643FAF9EE6BC0938BE71344294 | |||
| 2140 | drw_tr_installer.17451388361620b3111595a016885895.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\InitConfigure.ini | text | |
MD5:59585EE1CCA2648AD7A242CE5D531E00 | SHA256:79D7D5F6552BDDED7A3A89AD5458A63DBE49AC0F6AD59FAE523648AFF5141D93 | |||
| 2140 | drw_tr_installer.17451388361620b3111595a016885895.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\Norwegian.ini | text | |
MD5:74F6E38B2B7AC3893B1AB6C092B854D1 | SHA256:9692FECB48E8745F26C235C8925F106E56E862CD1B7B8CA8C84B8CB751B7A748 | |||
| 2140 | drw_tr_installer.17451388361620b3111595a016885895.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\Italian.ini | text | |
MD5:AF930A64DA61B99CB120C8A3222456EB | SHA256:1287CD9E6626EC2081379694A309578C1D83BCA25B2C621D1A5D4608CD7AF9BF | |||
| 2140 | drw_tr_installer.17451388361620b3111595a016885895.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\German.ini | text | |
MD5:DECAA2CBBACCAE2A64C588243FBD6435 | SHA256:4FFD51F20C76EE5D6CBAF16EA2AB9D0A0B0491E710C42D548724D5B5AAF3D55F | |||
| 2140 | drw_tr_installer.17451388361620b3111595a016885895.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\Indonesian.ini | text | |
MD5:38629FAB2999407FE8FA2DBABB097B57 | SHA256:13F413DBFCBC4537D83F77E34EF0C9FA868BFA07792E990F4E94526CCEB79848 | |||
| 2140 | drw_tr_installer.17451388361620b3111595a016885895.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\Japanese.ini | text | |
MD5:76E3CFD74C8A8C99CCD461F17CBABD4D | SHA256:64EFC20036A6CAD10DDBDB014444C55B6DB93A481EE5FE84210DEB2377918BB8 | |||
| 2140 | drw_tr_installer.17451388361620b3111595a016885895.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\Mungarian.ini | text | |
MD5:35331ED66C059568C54865EF7D41087C | SHA256:F55A35E6D3CCC944D4C264E34244A127BCE54079621CAB25D9E8E53CC1F9AC07 | |||
| 2140 | drw_tr_installer.17451388361620b3111595a016885895.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\LanguageTransfor.ini | text | |
MD5:FFE692A67871185785EC705B1CC12C81 | SHA256:373BEC6E7976324FF879C2988BAB772C69336D7BCB9A32386A6021568350A824 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
38
DNS requests
16
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5512 | AliyunWrapExe.exe | GET | 200 | 8.218.236.152:80 | http://track.easeus.com/product/index.php?c=main&a=getstatus&pid=2 | unknown | — | — | unknown |
5512 | AliyunWrapExe.exe | POST | 200 | 47.252.97.12:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5176 | EDownloader.exe | POST | 200 | 3.167.227.5:80 | http://download.easeus.com/api2/index.php/Apicp/Drwdl202004/index/ | unknown | — | — | unknown |
5512 | AliyunWrapExe.exe | POST | 200 | 47.252.97.12:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
5512 | AliyunWrapExe.exe | POST | 200 | 47.252.97.12:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
5512 | AliyunWrapExe.exe | POST | 200 | 47.252.97.12:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
5512 | AliyunWrapExe.exe | POST | 200 | 47.252.97.12:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
1452 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.22:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5512 | AliyunWrapExe.exe | 8.218.236.152:80 | track.easeus.com | Alibaba US Technology Co., Ltd. | HK | suspicious |
5512 | AliyunWrapExe.exe | 47.252.97.12:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba US Technology Co., Ltd. | US | unknown |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5176 | EDownloader.exe | 3.167.227.5:80 | download.easeus.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
track.easeus.com |
| unknown |
easeusinfo.us-east-1.log.aliyuncs.com |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
download.easeus.com |
| unknown |
d1.easeus.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
5512 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
5512 | AliyunWrapExe.exe | Possibly Unwanted Program Detected | ADWARE [ANY.RUN] Gexin Installer POST Request |
5512 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
5512 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
5512 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
5512 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
5512 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
5512 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
2240 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |