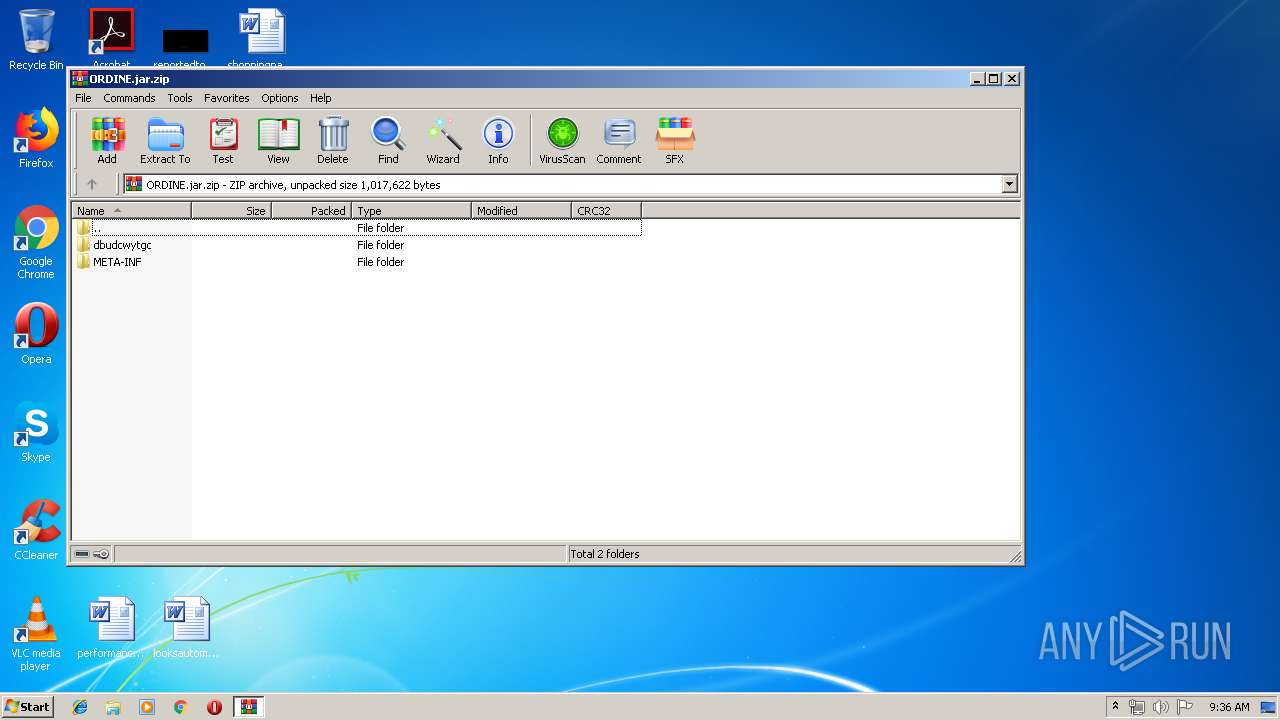
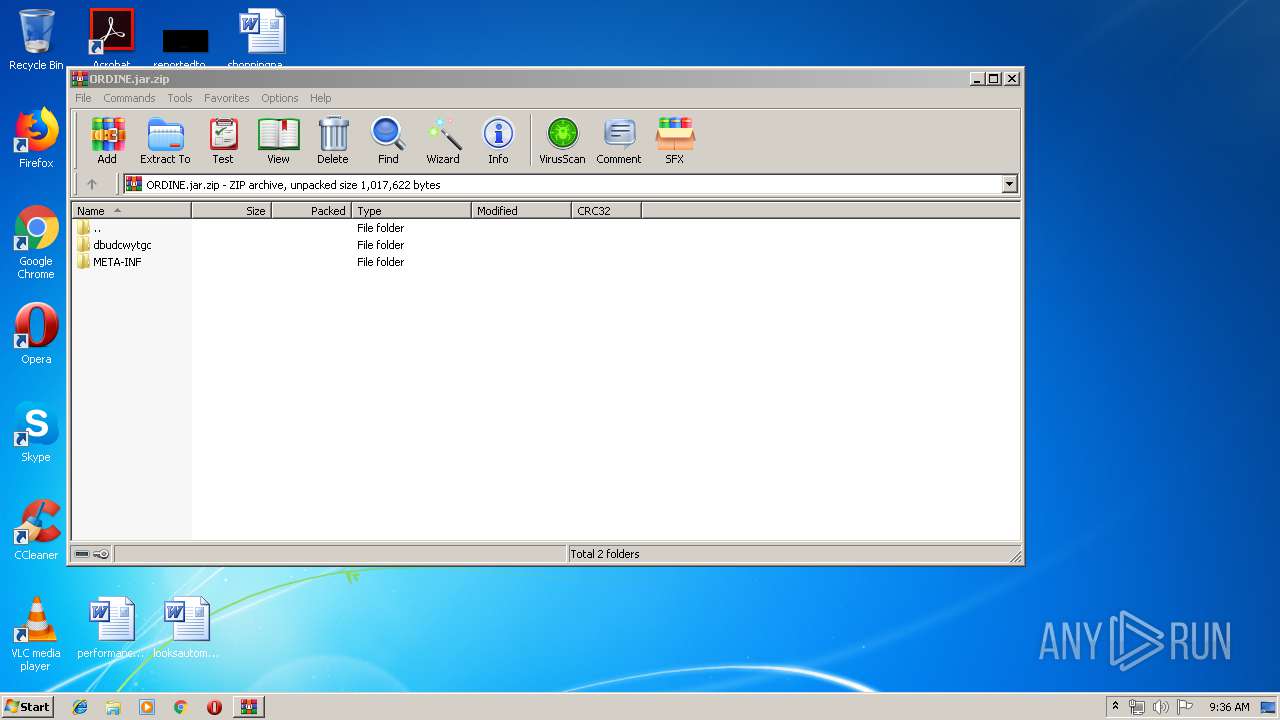
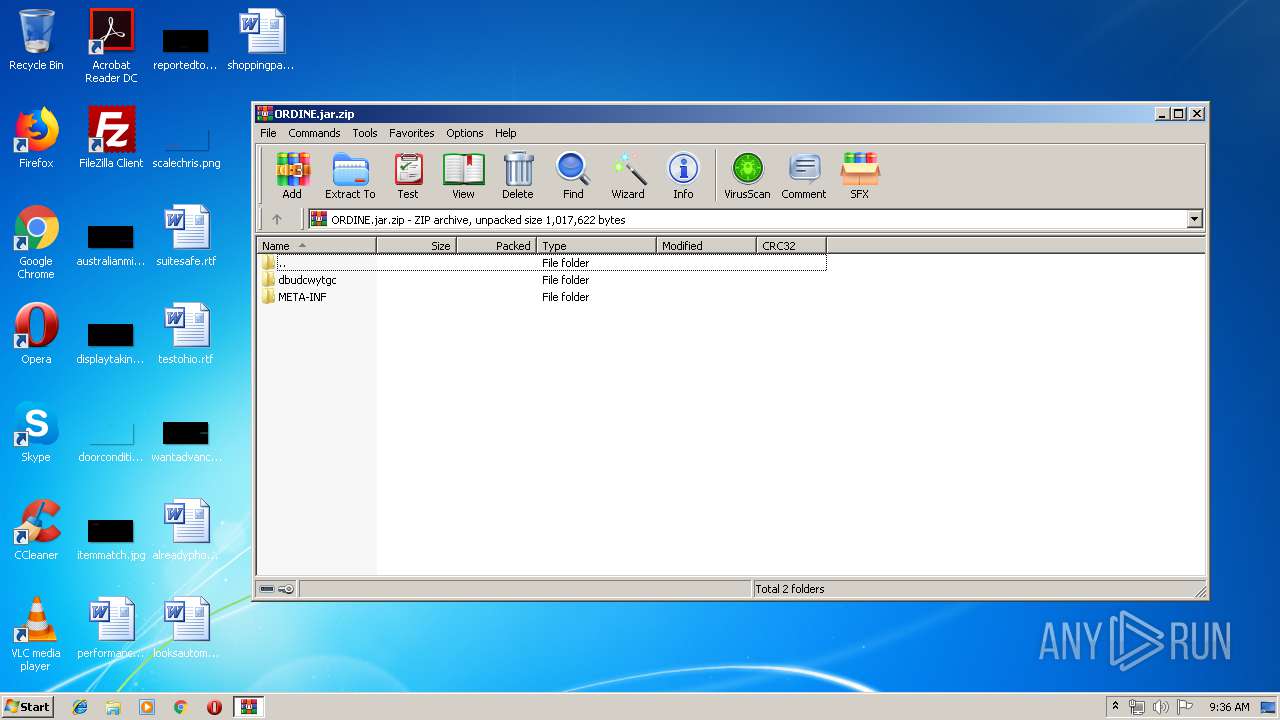
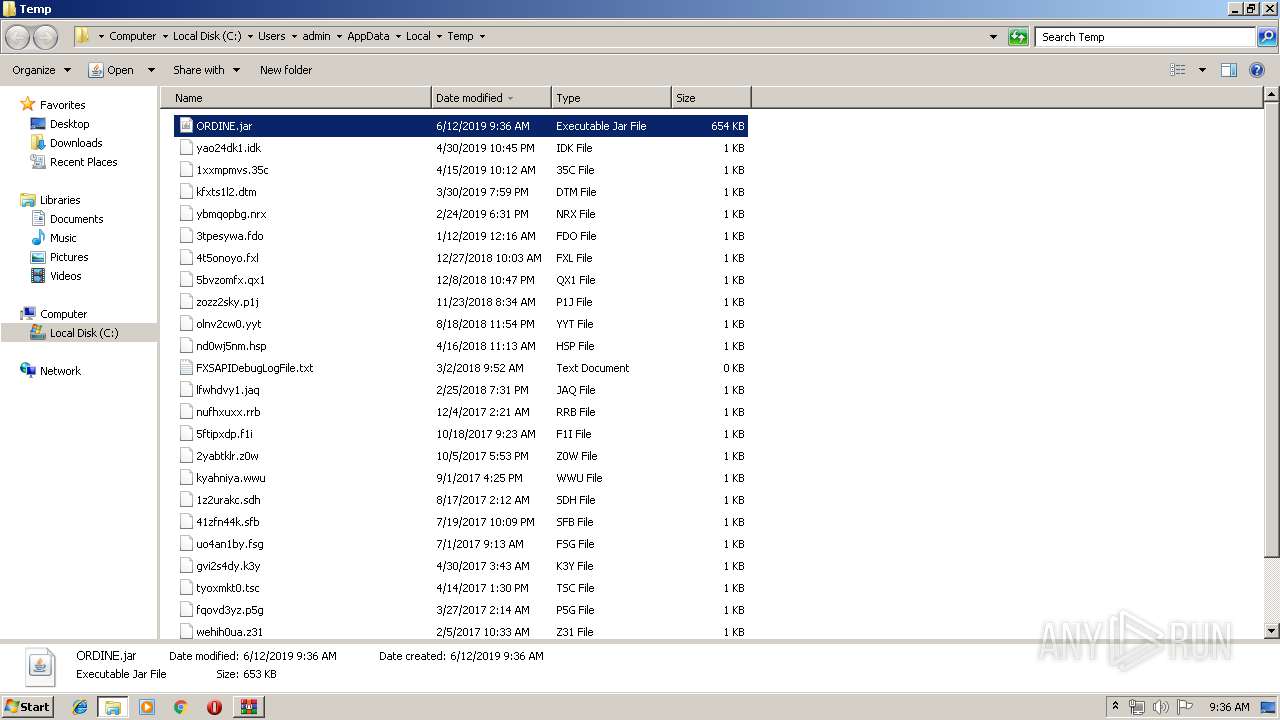
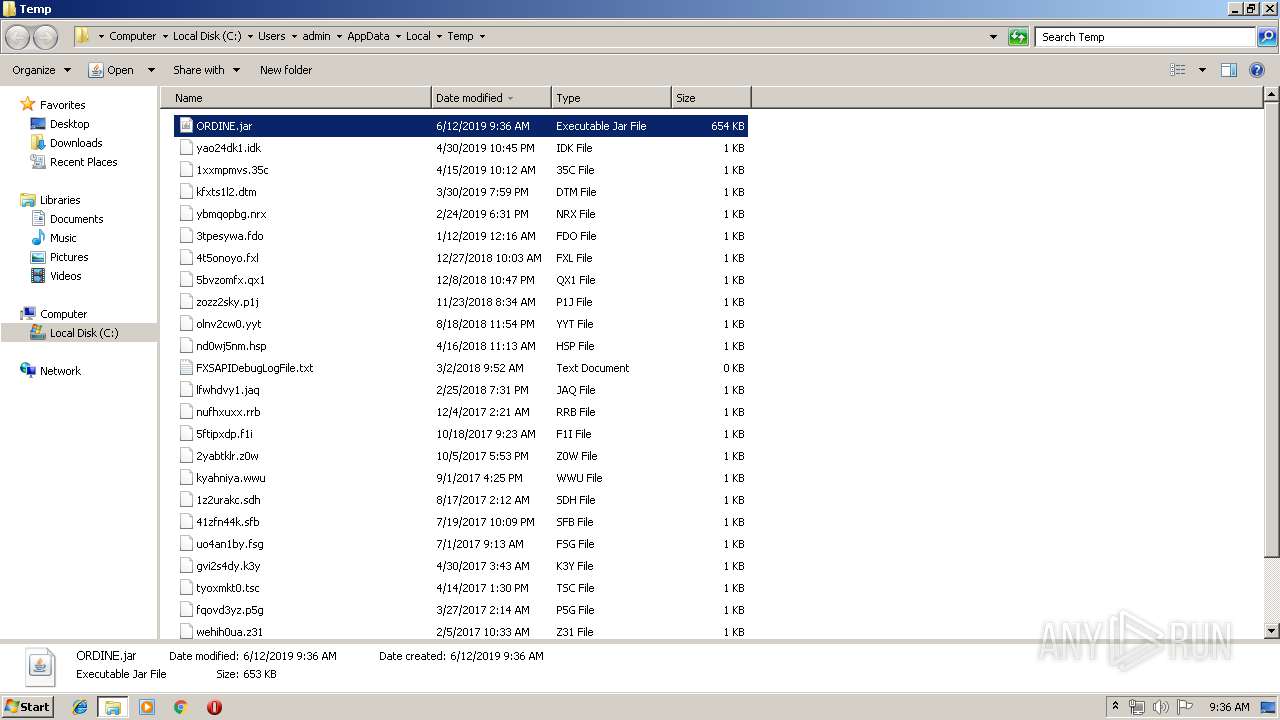
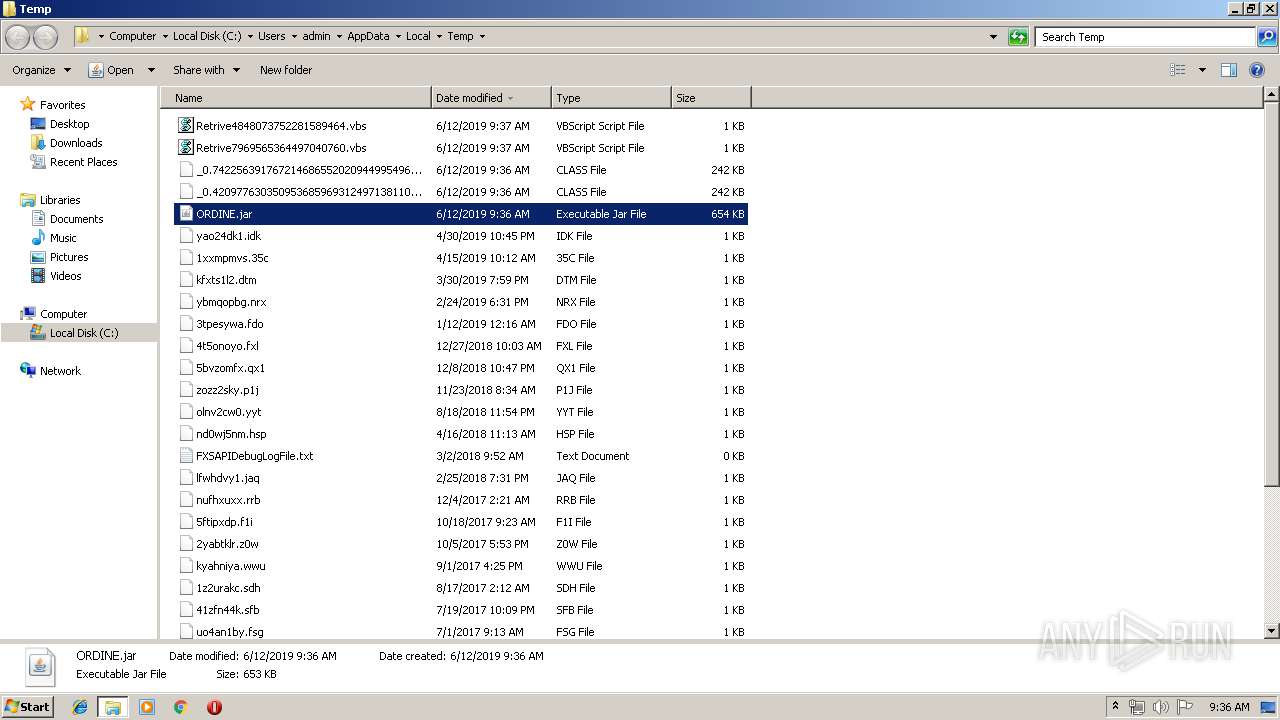
| File name: | ORDINE.jar |
| Full analysis: | https://app.any.run/tasks/2d82e089-0647-4af9-8a20-4968426b813d |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | June 12, 2019, 08:35:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
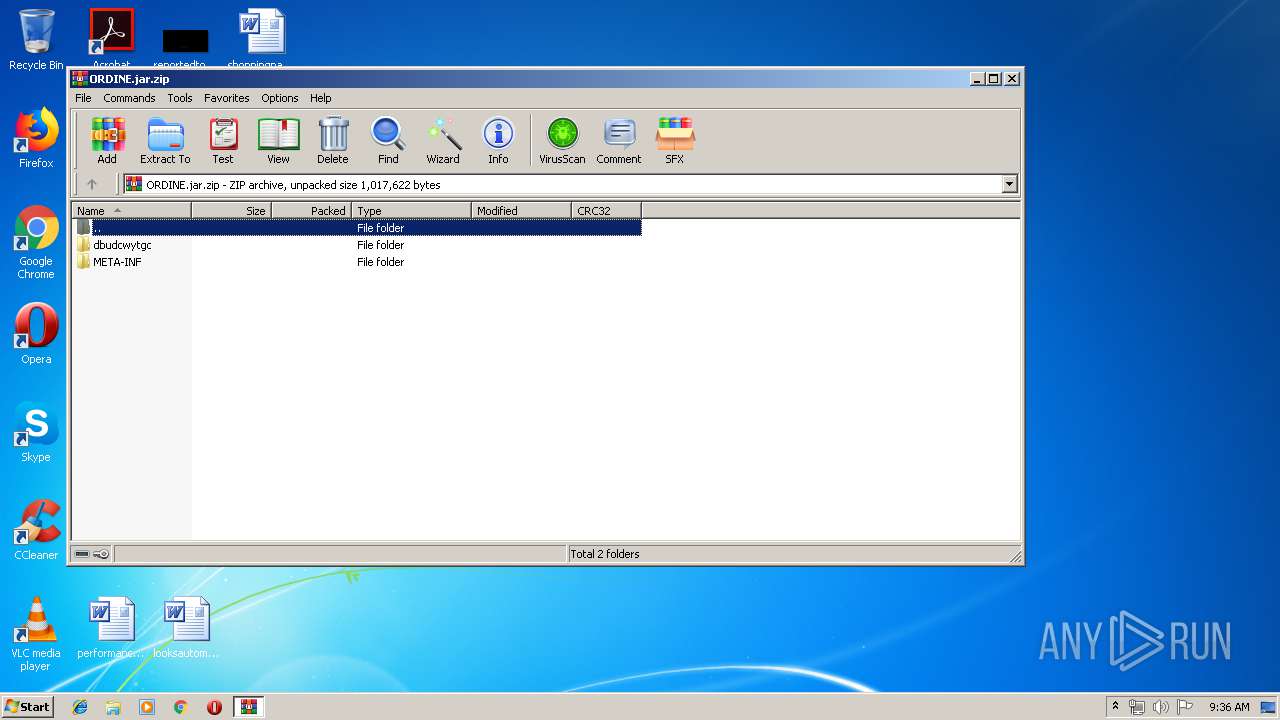
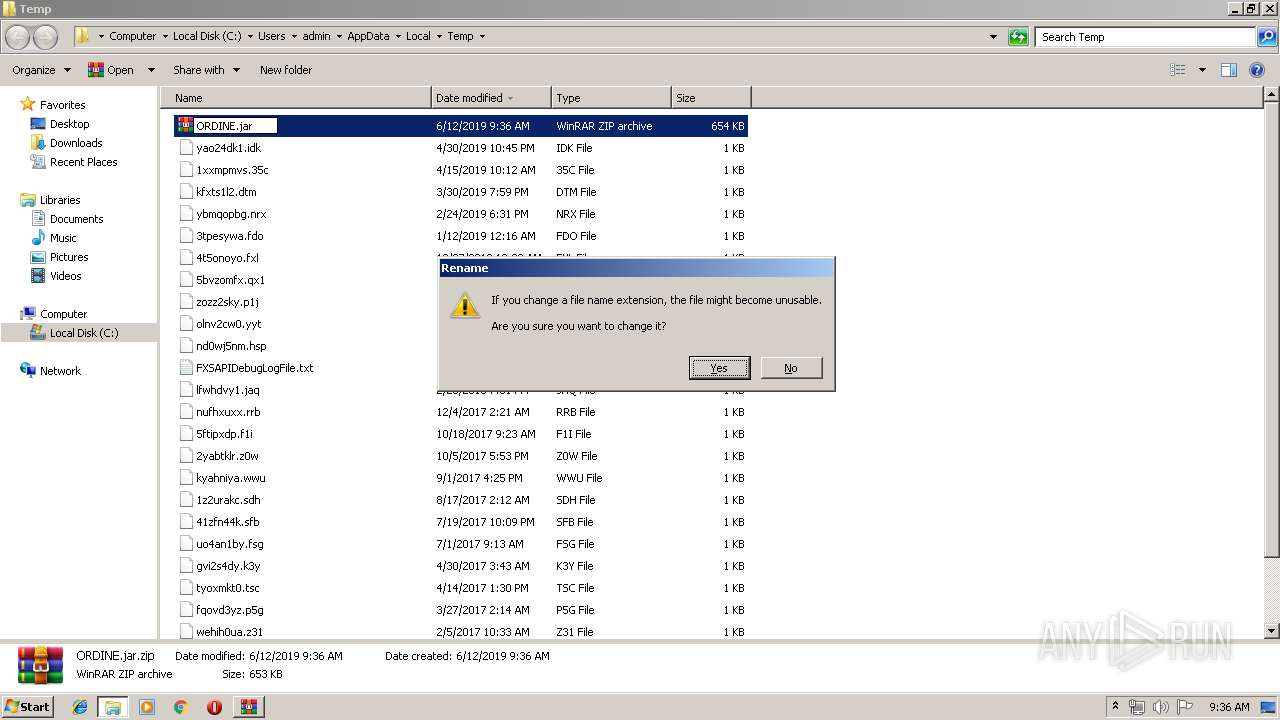
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8EC2CF6B3EEE8448E05EB231333C6E9A |
| SHA1: | B9BA016C99921BF522E500DBF31B2741AA97B025 |
| SHA256: | D8CD7E914884D8CF9F715E69826E6A871DC73697C2005535ABD578FF2BC5E4C3 |
| SSDEEP: | 12288:jcm9kVgAJ1HtemrN/NBZBrTYiGu3UuIIb59qH/wJwJIg05lT:jcpVgY1t9tTYPuUfLJheT |
MALICIOUS
AdWind was detected
- java.exe (PID: 3392)
- java.exe (PID: 3032)
Changes the autorun value in the registry
- WScript.exe (PID: 3444)
- reg.exe (PID: 2900)
Writes to a start menu file
- WScript.exe (PID: 3444)
Loads dropped or rewritten executable
- java.exe (PID: 3392)
- explorer.exe (PID: 2044)
- wscript.exe (PID: 960)
- svchost.exe (PID: 820)
- javaw.exe (PID: 2604)
- javaw.exe (PID: 3512)
- javaw.exe (PID: 2816)
- java.exe (PID: 3032)
Application was dropped or rewritten from another process
- javaw.exe (PID: 3512)
- javaw.exe (PID: 2816)
- java.exe (PID: 3392)
- javaw.exe (PID: 2604)
- java.exe (PID: 3032)
UAC/LUA settings modification
- regedit.exe (PID: 2196)
Uses TASKKILL.EXE to kill security tools
- javaw.exe (PID: 2816)
Turns off system restore
- regedit.exe (PID: 2196)
Changes Image File Execution Options
- regedit.exe (PID: 2196)
SUSPICIOUS
Executes scripts
- javaw.exe (PID: 3512)
- wscript.exe (PID: 960)
- cmd.exe (PID: 3904)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 1660)
- cmd.exe (PID: 1028)
- cmd.exe (PID: 2596)
- cmd.exe (PID: 2164)
- cmd.exe (PID: 2176)
- cmd.exe (PID: 2480)
Executes JAVA applets
- explorer.exe (PID: 2044)
- wscript.exe (PID: 960)
- javaw.exe (PID: 2604)
Application launched itself
- wscript.exe (PID: 960)
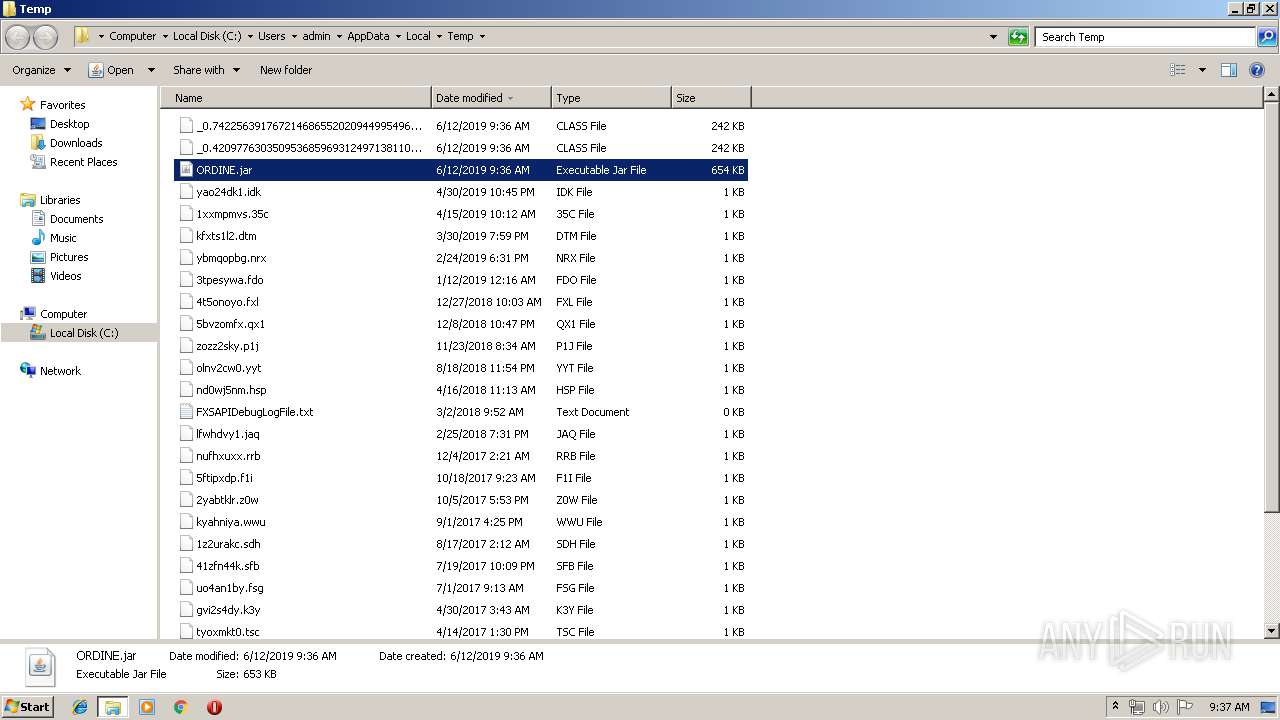
Creates files in the user directory
- wscript.exe (PID: 960)
- javaw.exe (PID: 2604)
- WScript.exe (PID: 3444)
- xcopy.exe (PID: 1908)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 2604)
- java.exe (PID: 3392)
- javaw.exe (PID: 2816)
- java.exe (PID: 3032)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 2604)
Executable content was dropped or overwritten
- xcopy.exe (PID: 1908)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 2604)
Starts itself from another location
- javaw.exe (PID: 2604)
Uses TASKKILL.EXE to kill process
- javaw.exe (PID: 2816)
INFO
Manual execution by user
- verclsid.exe (PID: 1876)
- javaw.exe (PID: 3512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:06:12 12:15:21 |
| ZipCRC: | 0xd265b8b6 |
| ZipCompressedSize: | 664217 |
| ZipUncompressedSize: | 1012809 |
| ZipFileName: | dbudcwytgc/resources/benyqlnwjz |
Total processes
214
Monitored processes
99
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | taskkill /IM mergecap.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | taskkill /IM cavwp.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 536 | taskkill /IM V3SP.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 536 | attrib +h "C:\Users\admin\Oracle Corporations" | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | taskkill /IM editcap.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 680 | taskkill /IM LittleHook.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 756 | taskkill /IM TRAYICOS.EXE /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 820 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 892 | taskkill /IM NisSrv.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive3135218121879757839.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
13 091
Read events
12 359
Write events
732
Delete events
0
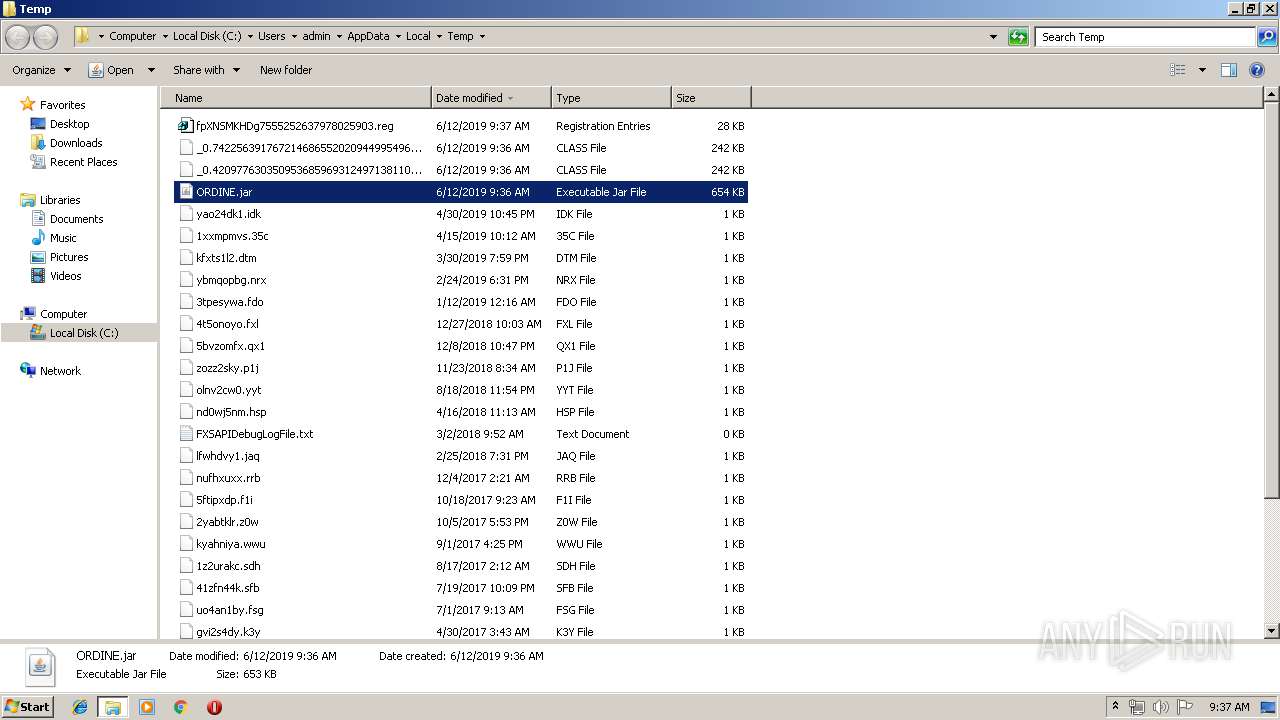
Modification events
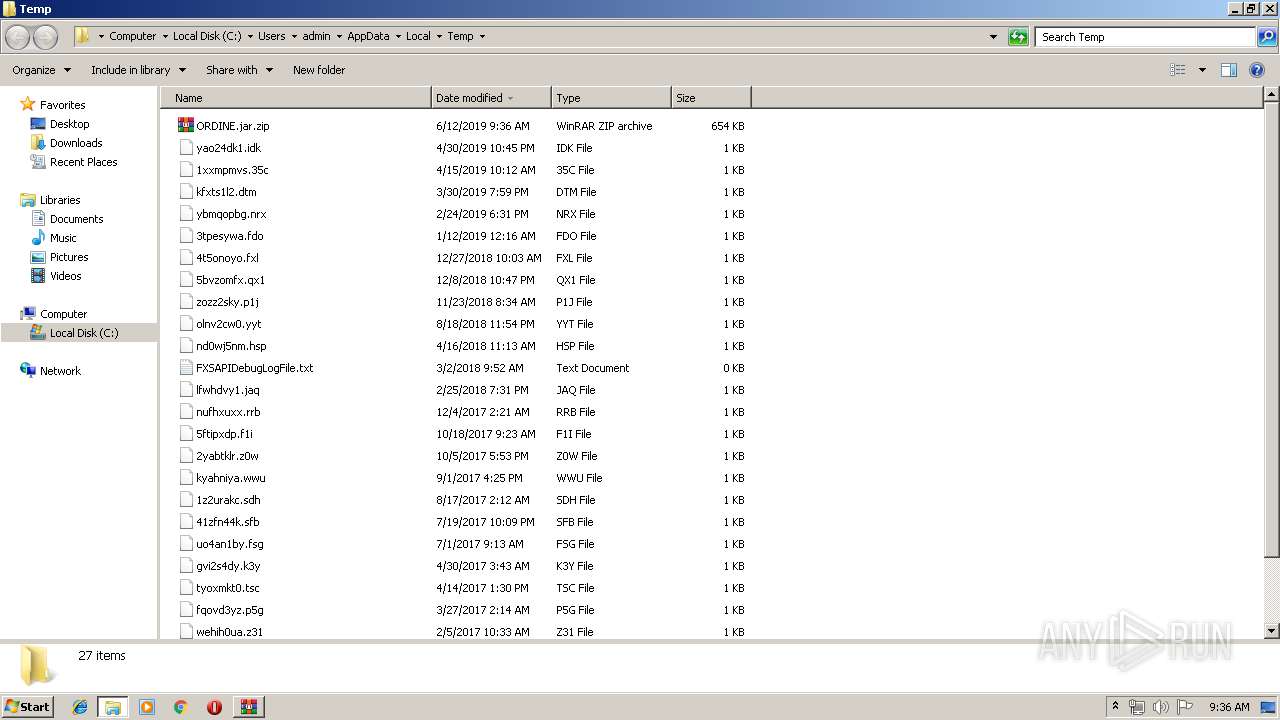
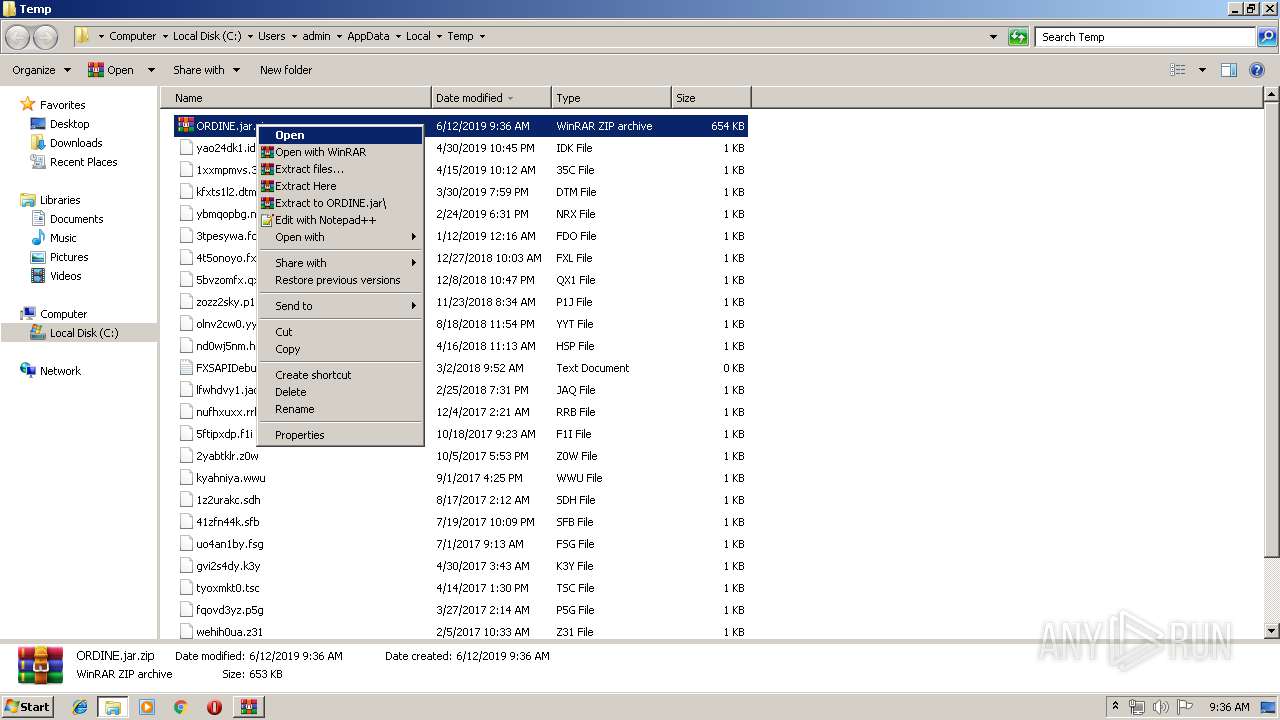
| (PID) Process: | (1372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1372) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
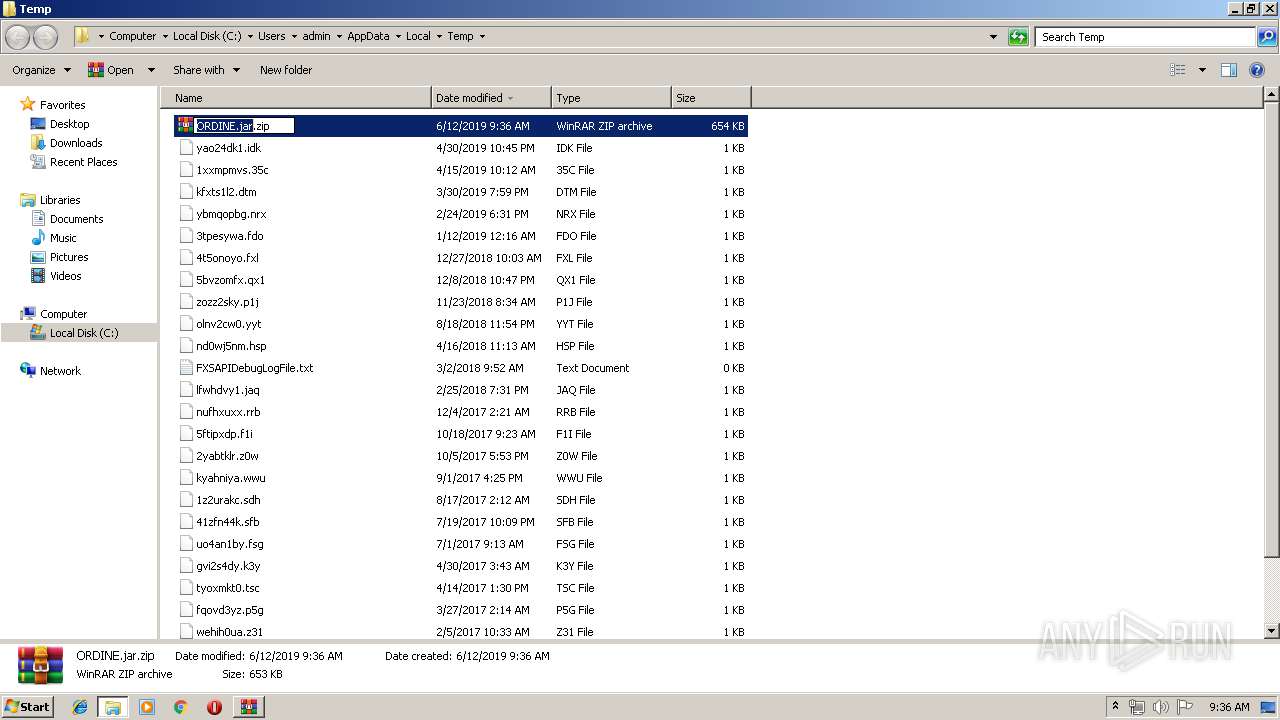
| (PID) Process: | (1372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ORDINE.jar.zip | |||
| (PID) Process: | (1372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
110
Suspicious files
11
Text files
81
Unknown types
15
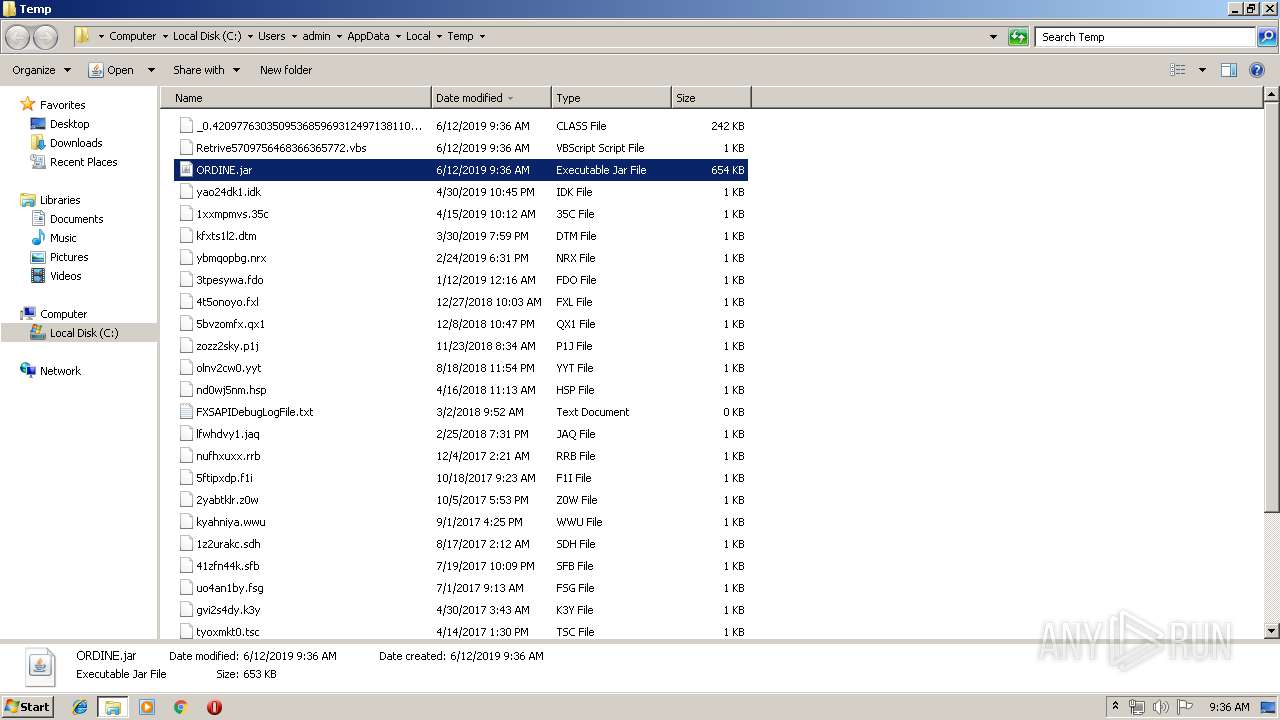
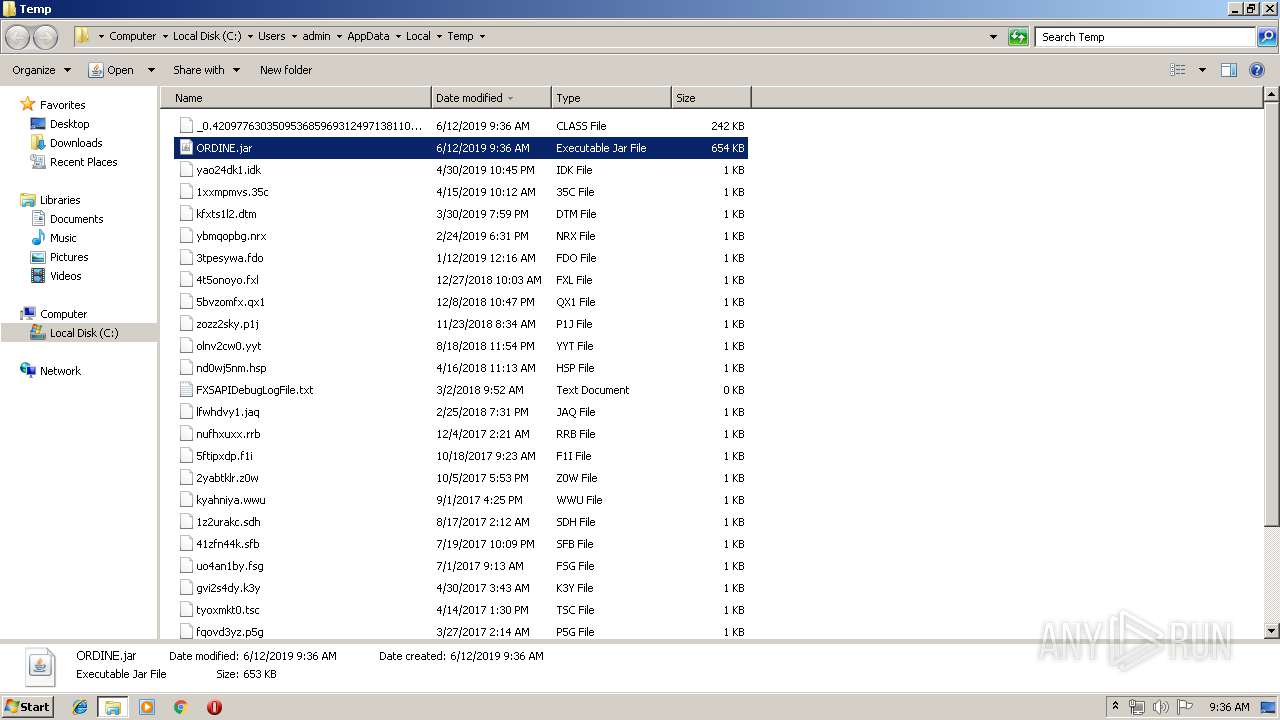
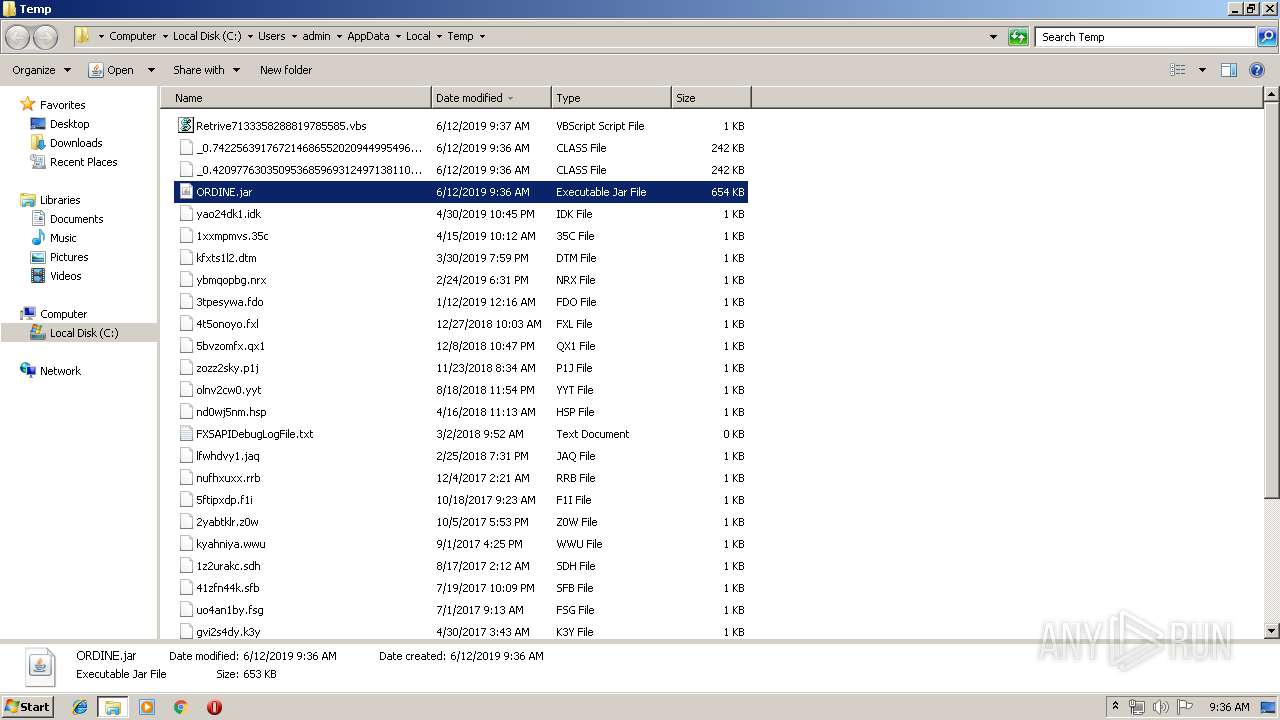
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | java.exe | C:\Users\admin\AppData\Local\Temp\Retrive3135218121879757839.vbs | — | |
MD5:— | SHA256:— | |||
| 3512 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Local\Temp\ORDINE.jar | compressed | |
MD5:— | SHA256:— | |||
| 960 | wscript.exe | C:\Users\admin\AppData\Roaming\magvwbu.txt | java | |
MD5:— | SHA256:— | |||
| 3512 | javaw.exe | C:\Users\admin\jyxsauqppe.js | text | |
MD5:— | SHA256:— | |||
| 2604 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3392 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3444 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\jPelBFjked.js | text | |
MD5:F88618764EAD42FFDFBC2BF457689AA6 | SHA256:DEB2B6C548A2FB838CFEE4E47EC752D12E6CC15AD06C2339F4D2AD690040BEFA | |||
| 960 | wscript.exe | C:\Users\admin\AppData\Roaming\jPelBFjked.js | text | |
MD5:F88618764EAD42FFDFBC2BF457689AA6 | SHA256:DEB2B6C548A2FB838CFEE4E47EC752D12E6CC15AD06C2339F4D2AD690040BEFA | |||
| 2604 | javaw.exe | C:\Users\admin\AppData\Local\Temp\Retrive4498287930391346465.vbs | text | |
MD5:A32C109297ED1CA155598CD295C26611 | SHA256:45BFE34AA3EF932F75101246EB53D032F5E7CF6D1F5B4E495334955A255F32E7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
11
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2816 | javaw.exe | 91.193.75.130:7075 | olavroy.duckdns.org | WorldStream B.V. | RS | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
brothersjoy.nl |
| unknown |
olavroy.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1068 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |