| File name: | 70ee09a57333d0d1232ac6f3bdabac72 |
| Full analysis: | https://app.any.run/tasks/bb1ff90f-08bb-4180-837f-e3643a035e3d |
| Verdict: | Malicious activity |
| Threats: | Sality is a highly sophisticated malware known for infecting executable files and rapidly spreading across networks. It primarily creates a peer-to-peer botnet that is used for malicious activities such as spamming, data theft, and downloading additional malware. Sality has strong persistence mechanisms, including disabling security software, making it difficult to remove. Its ability to spread quickly and silently, along with its polymorphic nature, allows it to evade detection by traditional antivirus solutions. |
| Analysis date: | July 14, 2020, 08:18:04 |
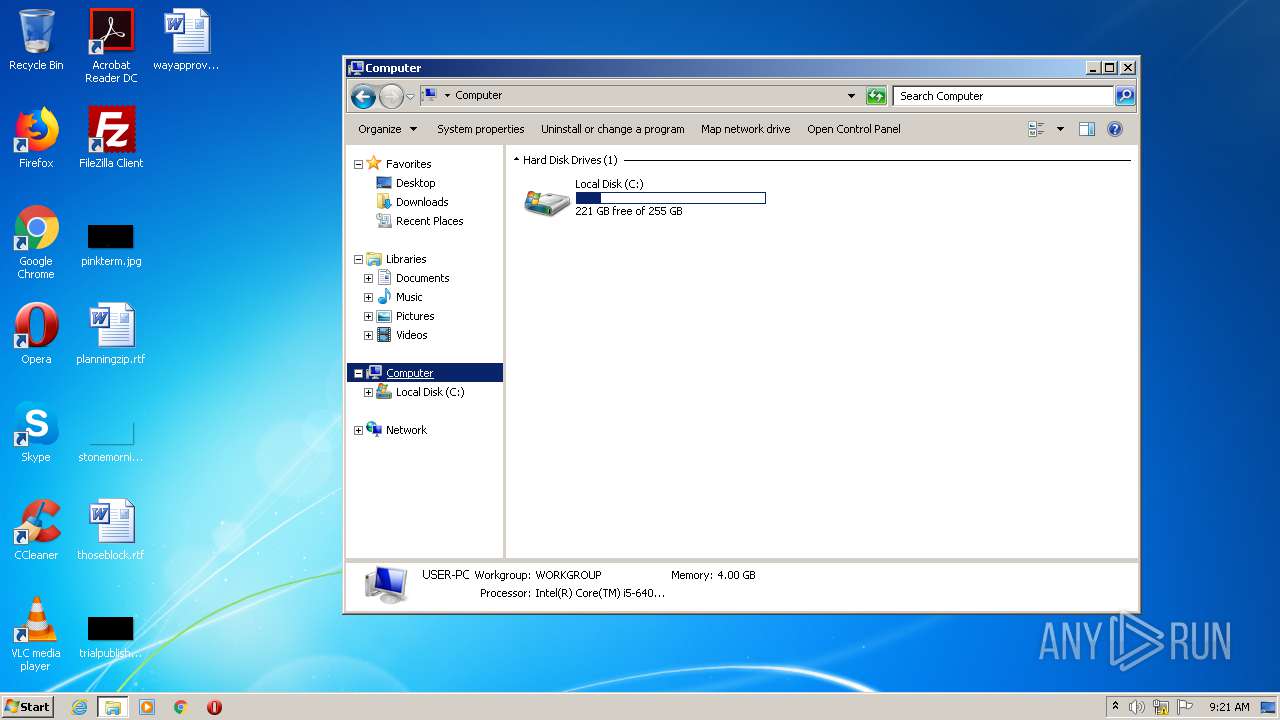
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 70EE09A57333D0D1232AC6F3BDABAC72 |
| SHA1: | 218CE521A5AC32DC6A5FB4EBD7F4DB4447974DF1 |
| SHA256: | D88DD03514200D4C181616A23B1A2DDDCC64003D45B949507CF2291386DED277 |
| SSDEEP: | 3072:dDV6dArrRdWmJSrvAhpVYXj61nDmROh1KFpNU4PMWUkk:73+XIb+XjSmUh1KFs4PM8k |
MALICIOUS
Changes Security Center notification settings
- 70ee09a57333d0d1232ac6f3bdabac72.exe (PID: 3864)
Application was injected by another process
- explorer.exe (PID: 1688)
- dwm.exe (PID: 1580)
- taskeng.exe (PID: 1516)
- windanr.exe (PID: 3832)
- ctfmon.exe (PID: 1740)
- DllHost.exe (PID: 3916)
Runs injected code in another process
- 70ee09a57333d0d1232ac6f3bdabac72.exe (PID: 3864)
- taskeng.exe (PID: 1516)
UAC/LUA settings modification
- 70ee09a57333d0d1232ac6f3bdabac72.exe (PID: 3864)
Changes firewall settings
- 70ee09a57333d0d1232ac6f3bdabac72.exe (PID: 3864)
SALITY was detected
- taskeng.exe (PID: 1516)
Connects to CnC server
- taskeng.exe (PID: 1516)
SUSPICIOUS
Executable content was dropped or overwritten
- 70ee09a57333d0d1232ac6f3bdabac72.exe (PID: 3864)
Application launched itself
- explorer.exe (PID: 1688)
Reads Internet Cache Settings
- taskeng.exe (PID: 1516)
Creates files in the user directory
- vlc.exe (PID: 892)
- taskeng.exe (PID: 1516)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:12:24 22:04:20+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 22528 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30be |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.5.26.0 |
| ProductVersionNumber: | 5.5.26.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| Comments: | tomcat.apache.org |
| CompanyName: | Apache Software Foundation |
| FileDescription: | Apache Tomcat Installer |
| FileVersion: | 2 |
| InternalName: | apache-tomcat-5.5.26.exe |
| LegalCopyright: | Copyright (c) 1999-2005 The Apache Software Foundation |
| ProductName: | Apache Tomcat |
| ProductVersion: | 5.5.26 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Dec-2007 21:04:20 |
| Detected languages: |
|
| Comments: | tomcat.apache.org |
| CompanyName: | Apache Software Foundation |
| FileDescription: | Apache Tomcat Installer |
| FileVersion: | 2.0 |
| InternalName: | apache-tomcat-5.5.26.exe |
| LegalCopyright: | Copyright (c) 1999-2005 The Apache Software Foundation |
| ProductName: | Apache Tomcat |
| ProductVersion: | 5.5.26 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Dec-2007 21:04:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000057B4 | 0x00005800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.49505 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.17644 |
.data | 0x00009000 | 0x0001AFD8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96056 |
.ndata | 0x00024000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002E000 | 0x00018000 | 0x00017E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.3363 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10609 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.58585 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 4.1463 | 3240 | UNKNOWN | English - United States | RT_ICON |
4 | 3.71606 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 2.64646 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 2.71436 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 4.23914 | 872 | UNKNOWN | English - United States | RT_ICON |
8 | 2.95894 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 2.78721 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
41
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\AppData\Local\Temp\70ee09a57333d0d1232ac6f3bdabac72.exe" | C:\Users\admin\AppData\Local\Temp\70ee09a57333d0d1232ac6f3bdabac72.exe | — | explorer.exe | |||||||||||
User: admin Company: Apache Software Foundation Integrity Level: MEDIUM Description: Apache Tomcat Installer Exit code: 3221226540 Version: 2.0 Modules
| |||||||||||||||
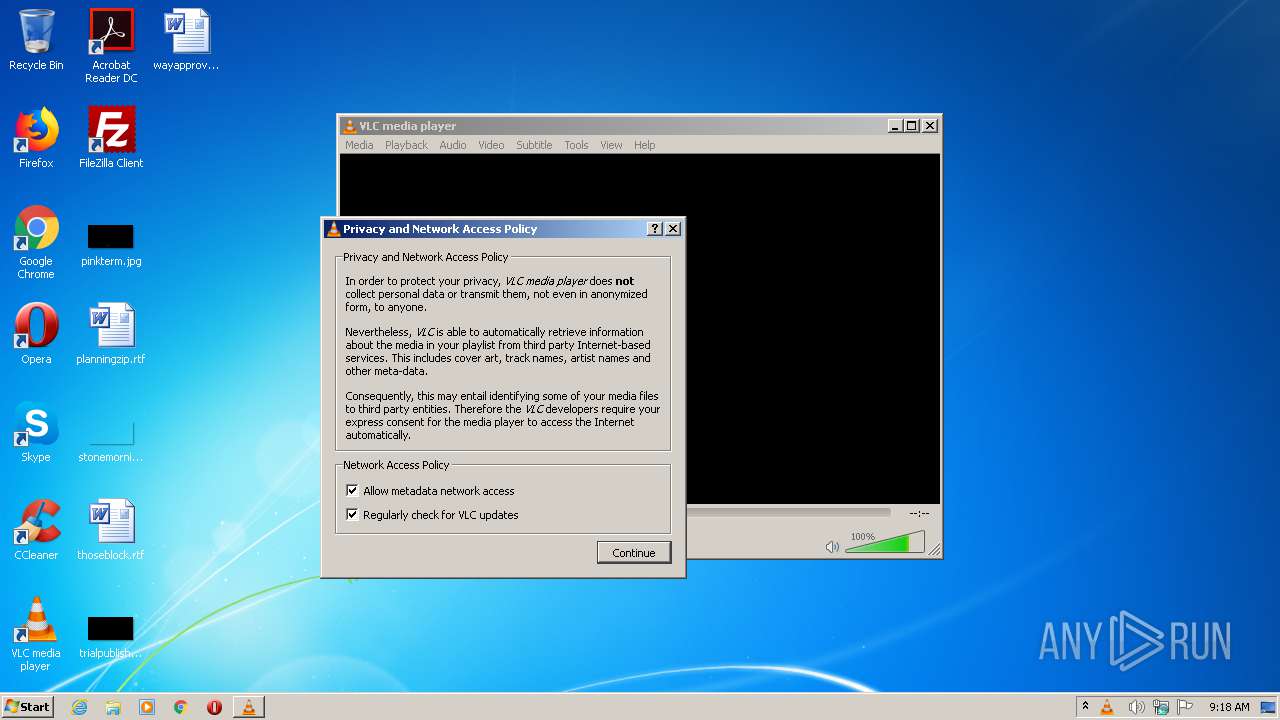
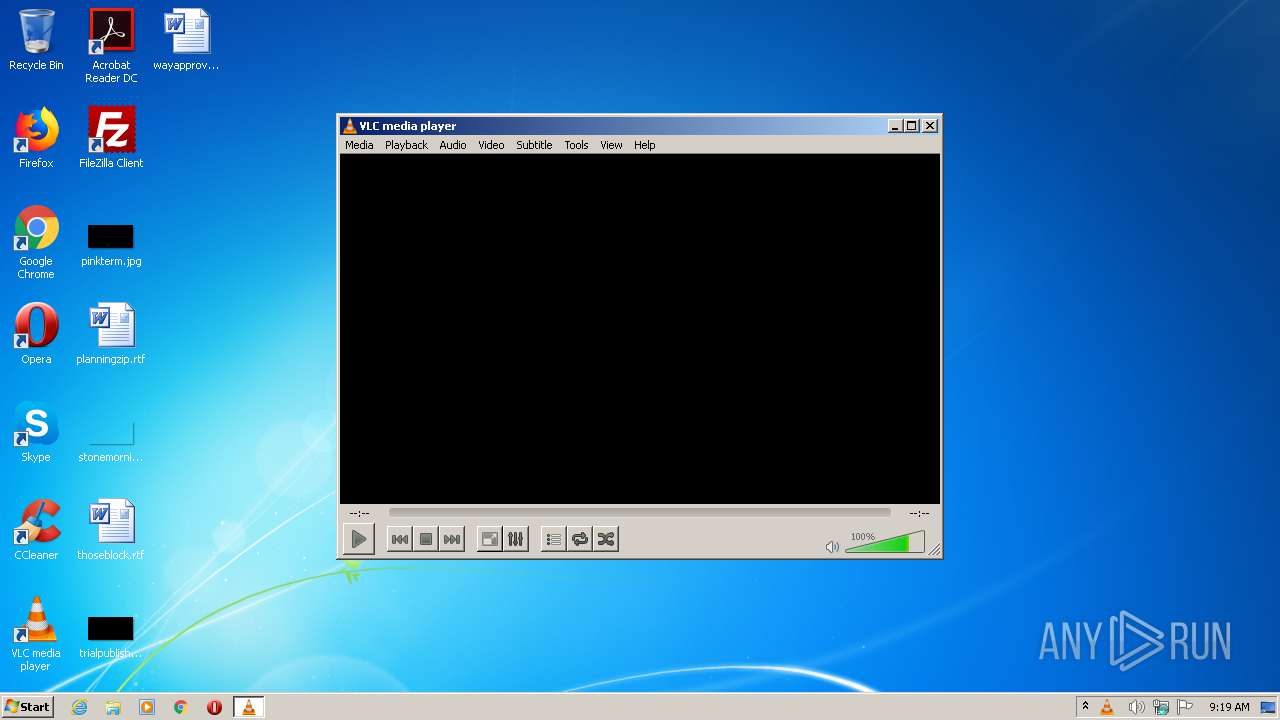
| 892 | "C:\Program Files\VideoLAN\VLC\vlc.exe" | C:\Program Files\VideoLAN\VLC\vlc.exe | explorer.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 1516 | taskeng.exe {8A729502-1DC5-4010-BCE0-307C09FA4DB9} | C:\Windows\System32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1580 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1688 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1740 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3600 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3832 | "windanr.exe" | C:\Windows\system32\windanr.exe | q.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3864 | "C:\Users\admin\AppData\Local\Temp\70ee09a57333d0d1232ac6f3bdabac72.exe" | C:\Users\admin\AppData\Local\Temp\70ee09a57333d0d1232ac6f3bdabac72.exe | explorer.exe | ||||||||||||
User: admin Company: Apache Software Foundation Integrity Level: HIGH Description: Apache Tomcat Installer Exit code: 3221225477 Version: 2.0 Modules
| |||||||||||||||
| 3916 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
942
Read events
736
Write events
206
Delete events
0
Modification events
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
1
Suspicious files
3
Text files
7
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1516 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\winjtqn.exe | — | |
MD5:— | SHA256:— | |||
| 892 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlcrc.892 | — | |
MD5:— | SHA256:— | |||
| 892 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\ml.xspf.tmp892 | — | |
MD5:— | SHA256:— | |||
| 1516 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\Cab96E4.tmp | — | |
MD5:— | SHA256:— | |||
| 1516 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\Tar96E5.tmp | — | |
MD5:— | SHA256:— | |||
| 1516 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\gbibm.exe | — | |
MD5:— | SHA256:— | |||
| 1516 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\winjikwwf.exe | — | |
MD5:— | SHA256:— | |||
| 1516 | taskeng.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\NXG27ELV.txt | — | |
MD5:— | SHA256:— | |||
| 1516 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\dowl.exe | — | |
MD5:— | SHA256:— | |||
| 1516 | taskeng.exe | C:\Users\admin\AppData\Local\Temp\iwoi.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
13
DNS requests
16
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1516 | taskeng.exe | GET | 200 | 173.231.189.26:80 | http://eylenirik.biz/logo.gif?139d2d=6427105 | US | — | — | malicious |
1516 | taskeng.exe | GET | — | 174.143.121.176:80 | http://ads.yuppads.com/logo.gif?13ce5f=3894045 | US | — | — | malicious |
1516 | taskeng.exe | GET | 200 | 162.217.99.134:80 | http://esource.co.in/images/logo2.gif?13cc2d=3892359 | US | — | — | malicious |
1516 | taskeng.exe | GET | 302 | 216.10.240.89:80 | http://eskimovie.com/images/logo.gif?13c5e3=9070901 | IN | html | 245 b | suspicious |
1516 | taskeng.exe | GET | 200 | 216.10.240.89:80 | http://eskimovie.com/cgi-sys/suspendedpage.cgi?13c5e3=9070901 | IN | html | 7.44 Kb | suspicious |
1516 | taskeng.exe | GET | 200 | 206.189.61.126:80 | http://cart133.org/images/main.gif?143e11=13266090 | US | — | — | malicious |
1516 | taskeng.exe | GET | 301 | 85.187.128.7:80 | http://www.eri.edu.pk/images/logo.gif?138e78=7689936 | US | html | 706 b | malicious |
1516 | taskeng.exe | GET | 200 | 2.16.186.35:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
1516 | taskeng.exe | GET | 404 | 173.236.154.78:80 | http://www.finepearl.com.hk/images/logo.gif?143f0b=6634295 | US | html | 315 b | malicious |
1516 | taskeng.exe | GET | 404 | 88.86.100.181:80 | http://fotbalbaska.yc.cz/images/fmain.gif?13c509=1295625 | CZ | html | 263 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1516 | taskeng.exe | 85.187.128.7:80 | www.eri.edu.pk | A2 Hosting, Inc. | US | malicious |
1516 | taskeng.exe | 85.187.128.7:443 | www.eri.edu.pk | A2 Hosting, Inc. | US | malicious |
1516 | taskeng.exe | 2.16.186.35:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
1516 | taskeng.exe | 185.126.217.46:80 | fourline.com.tr | Netinternet Bilisim Teknolojileri AS | TR | malicious |
1516 | taskeng.exe | 173.231.189.26:80 | eylenirik.biz | Voxel Dot Net, Inc. | US | malicious |
— | — | 88.86.100.181:80 | fotbalbaska.yc.cz | SuperNetwork s.r.o. | CZ | malicious |
1516 | taskeng.exe | 216.10.240.89:80 | eskimovie.com | PDR | IN | malicious |
— | — | 162.241.203.186:80 | esteticaespacobemestar.com.br | CyrusOne LLC | US | malicious |
1516 | taskeng.exe | 162.217.99.134:80 | esource.co.in | Voxel Dot Net, Inc. | US | malicious |
1516 | taskeng.exe | 174.143.121.176:80 | ads.yuppads.com | Rackspace Ltd. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.eri.edu.pk |
| unknown |
eri.edu.pk |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
fourline.com.tr |
| unknown |
eylenirik.biz |
| malicious |
fotbalbaska.yc.cz |
| malicious |
eskimovie.com |
| suspicious |
esteticaespacobemestar.com.br |
| malicious |
forceline.com.tr |
| unknown |
esource.co.in |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1516 | taskeng.exe | A Network Trojan was detected | ET TROJAN Win32.Sality-GR Checkin |
1516 | taskeng.exe | A Network Trojan was detected | MALWARE [PTsecurity] Sality.bh Check-in .gif |
1516 | taskeng.exe | A Network Trojan was detected | ET TROJAN Win32.Sality-GR Checkin |
1516 | taskeng.exe | A Network Trojan was detected | MALWARE [PTsecurity] Sality.bh Check-in .gif |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1516 | taskeng.exe | A Network Trojan was detected | ET TROJAN Win32.Sality-GR Checkin |
1516 | taskeng.exe | A Network Trojan was detected | MALWARE [PTsecurity] Sality.bh Check-in .gif |
1516 | taskeng.exe | A Network Trojan was detected | ET TROJAN Possible Compromised Host AnubisNetworks Sinkhole Cookie Value Snkz |
1516 | taskeng.exe | A Network Trojan was detected | ET TROJAN Win32.Sality-GR Checkin |
1516 | taskeng.exe | A Network Trojan was detected | MALWARE [PTsecurity] Sality.bh Check-in .gif |
Process | Message |
|---|---|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|