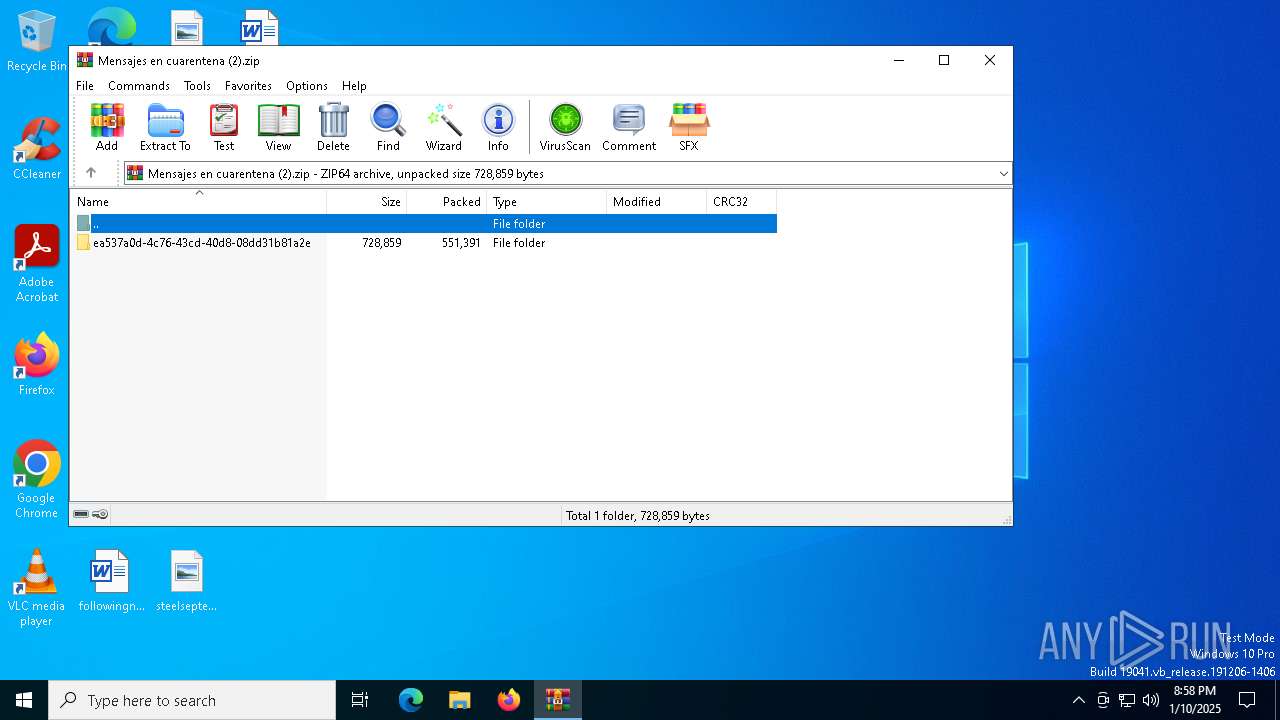
| File name: | Mensajes en cuarentena (2).zip |
| Full analysis: | https://app.any.run/tasks/d6c4f21f-6c19-448c-9521-e4667d6cf636 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | January 10, 2025, 20:58:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | E59D7DA9EA3112DF8D097A3DC75CBBA5 |
| SHA1: | ADB0F354A75BE0ABAC24A2E5E7EEF399EA1DB71B |
| SHA256: | D7F7DF47472593076077B7052725B8440A32637BC54FB8AFAB9FE3868C50A443 |
| SSDEEP: | 24576:WXoPVvDWrFUL15HhiNkBZhy2w+eL6THb4FgCM4FHs8URzVgz2:WXoPVvDWrFUL15HhiNaZhy2w+eL6THbB |
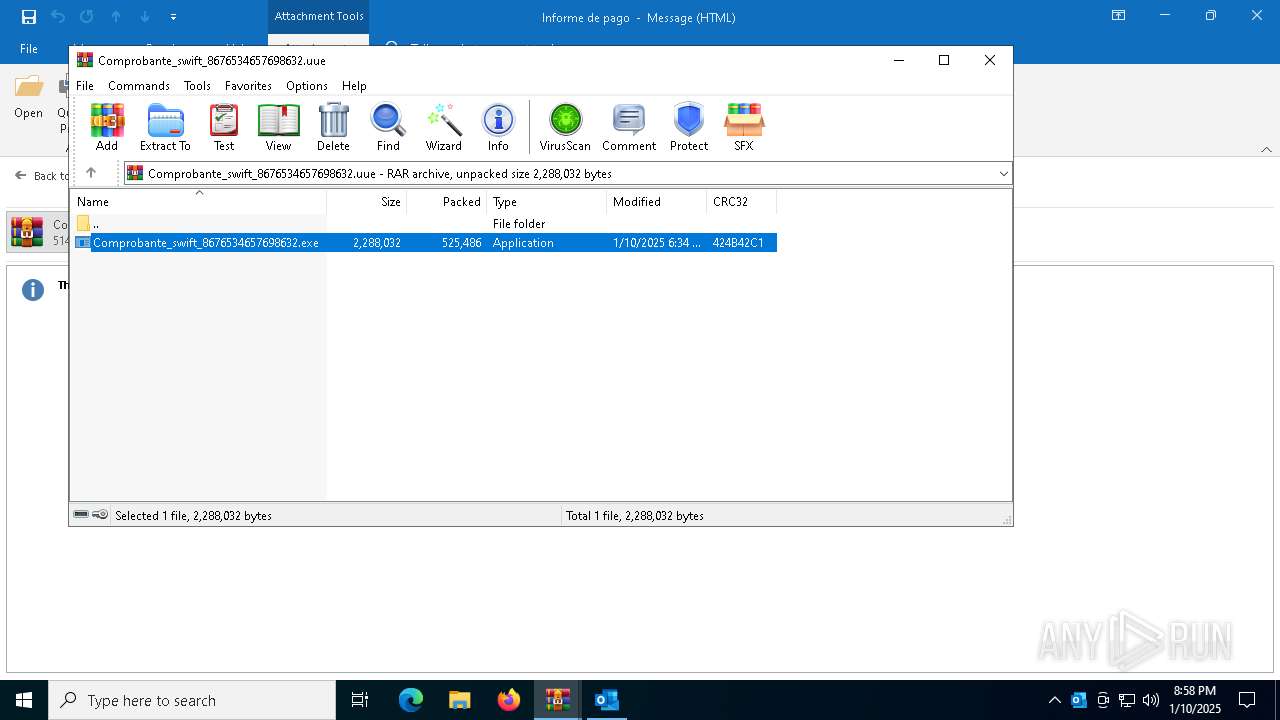
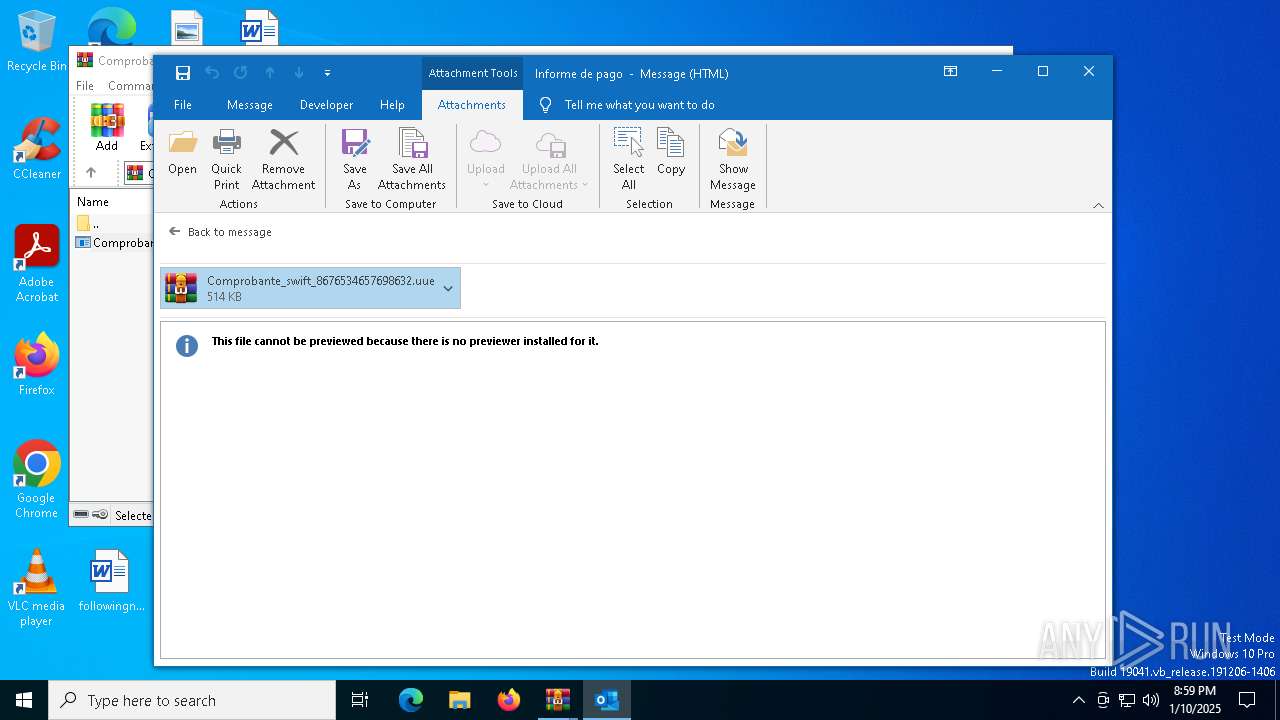
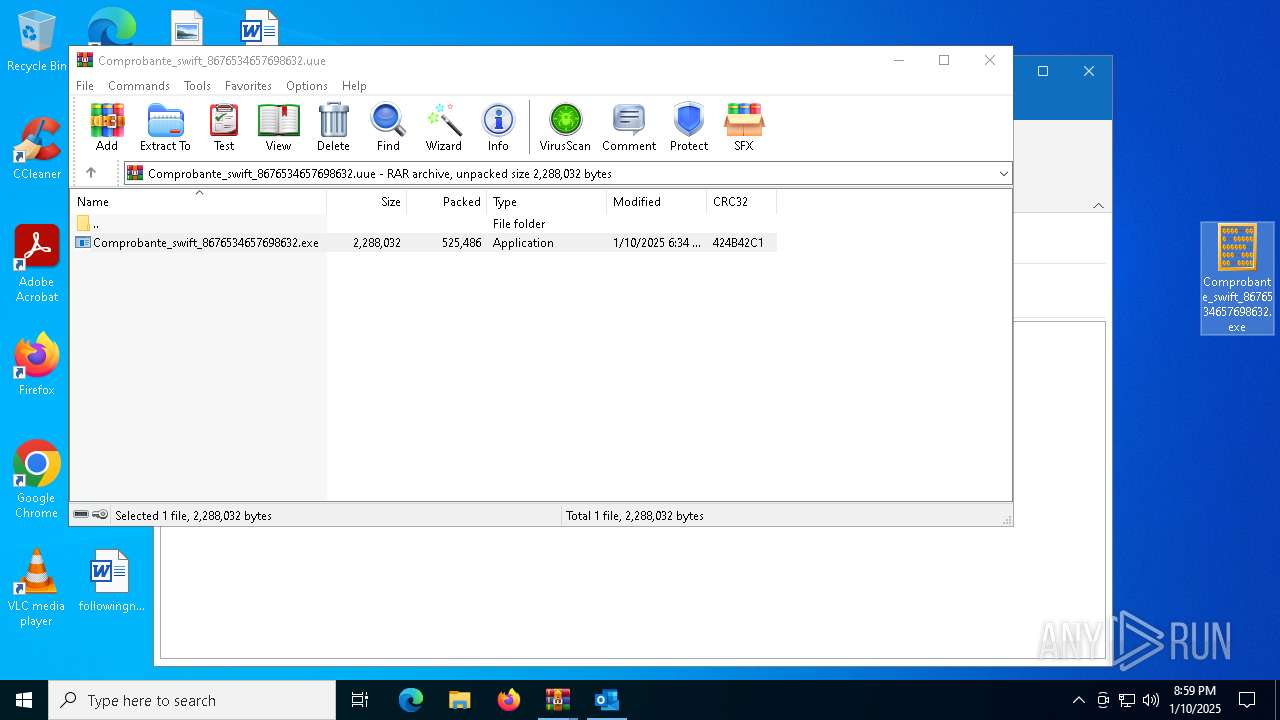
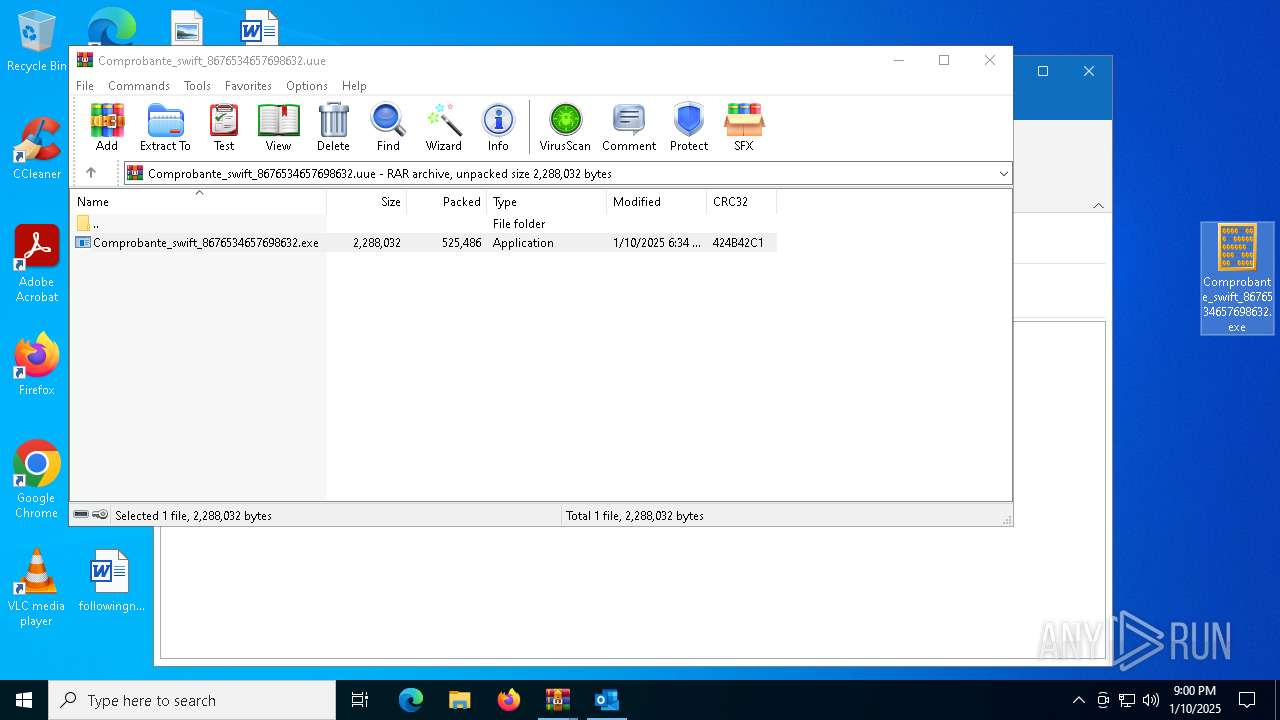
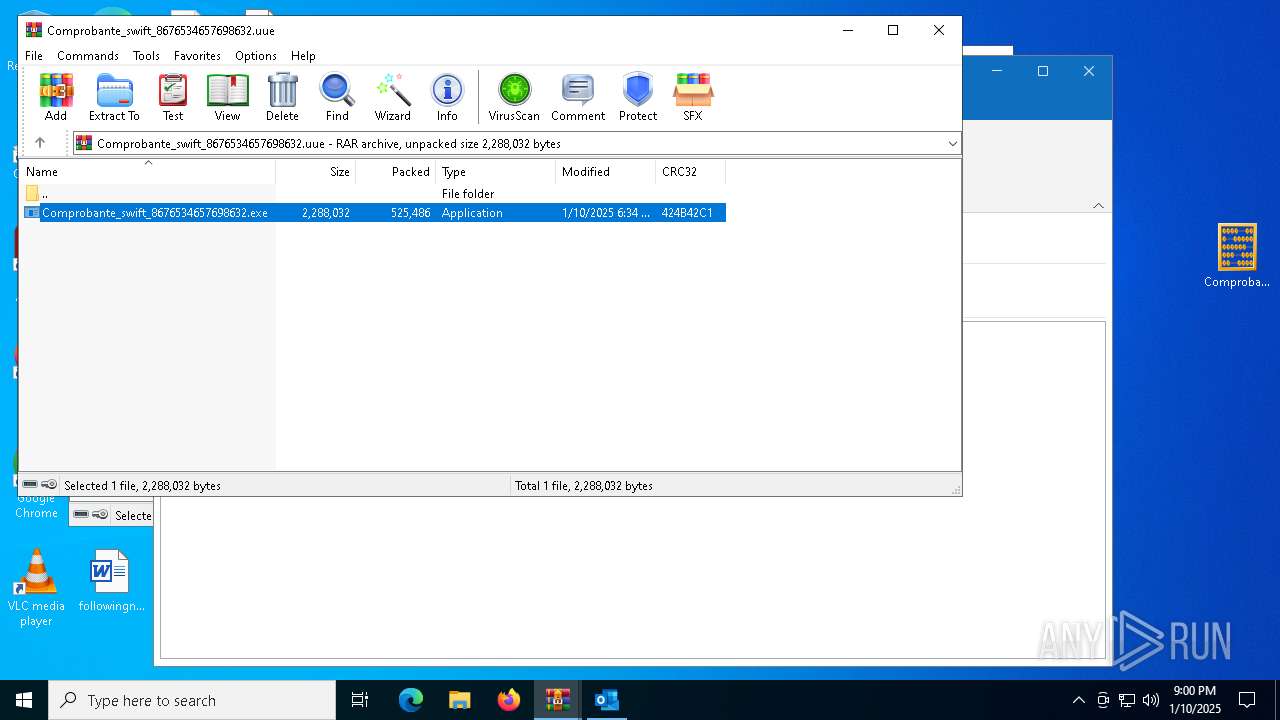
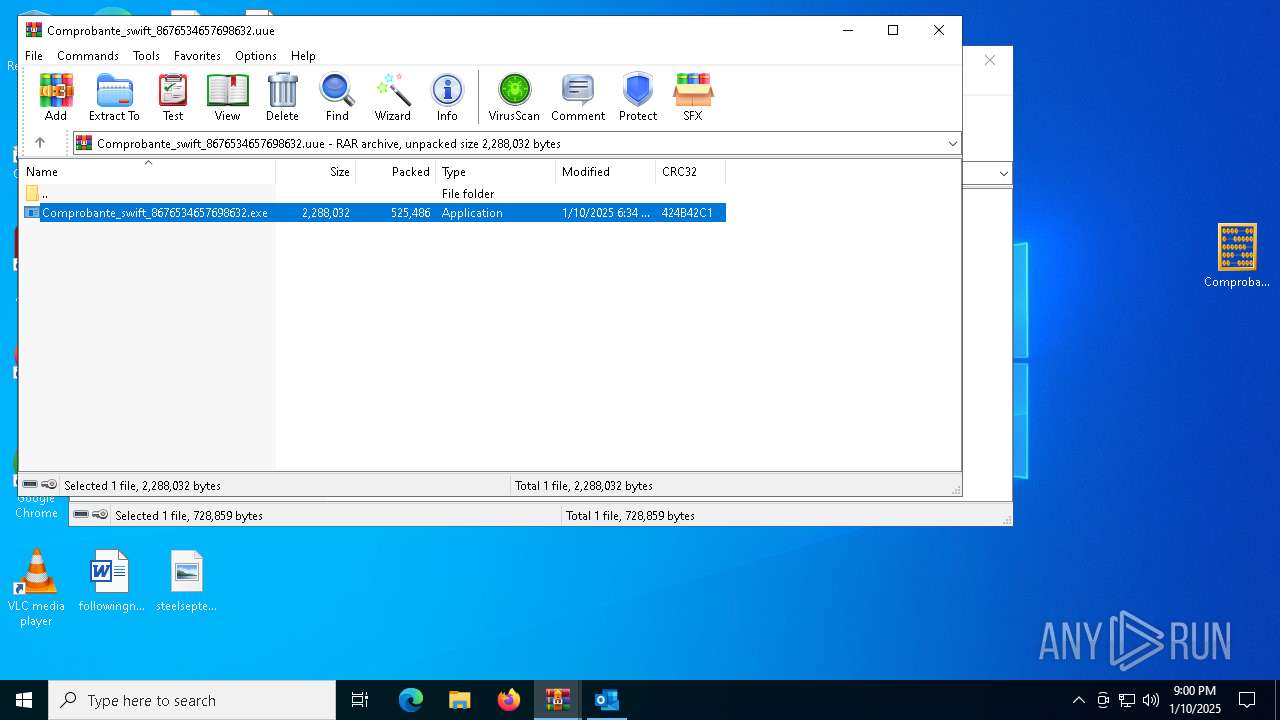
MALICIOUS
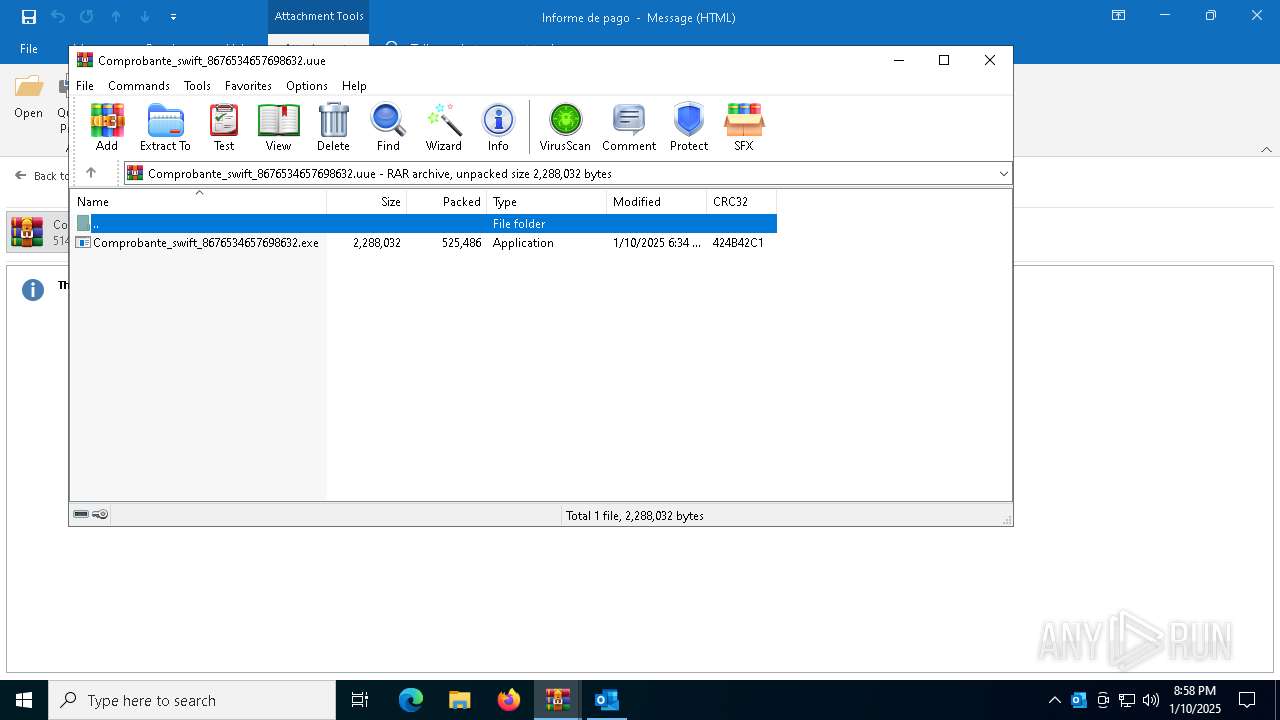
Executing a file with an untrusted certificate
- Comprobante_swift_8676534657698632.exe (PID: 6832)
- Comprobante_swift_8676534657698632.exe (PID: 3612)
- Comprobante_swift_8676534657698632.exe (PID: 6268)
- Comprobante_swift_8676534657698632.exe (PID: 4864)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 6928)
- RegAsm.exe (PID: 2756)
- RegAsm.exe (PID: 6164)
- RegAsm.exe (PID: 1020)
Steals credentials from Web Browsers
- RegAsm.exe (PID: 6928)
- RegAsm.exe (PID: 2756)
- RegAsm.exe (PID: 6164)
- RegAsm.exe (PID: 1020)
AGENTTESLA has been detected (YARA)
- RegAsm.exe (PID: 6928)
- RegAsm.exe (PID: 2756)
- RegAsm.exe (PID: 6164)
- RegAsm.exe (PID: 1020)
AGENTTESLA has been detected (SURICATA)
- RegAsm.exe (PID: 6928)
- RegAsm.exe (PID: 2756)
- RegAsm.exe (PID: 6164)
- RegAsm.exe (PID: 1020)
Connects to the CnC server
- RegAsm.exe (PID: 6928)
- RegAsm.exe (PID: 2756)
- RegAsm.exe (PID: 6164)
- RegAsm.exe (PID: 1020)
SUSPICIOUS
Reads security settings of Internet Explorer
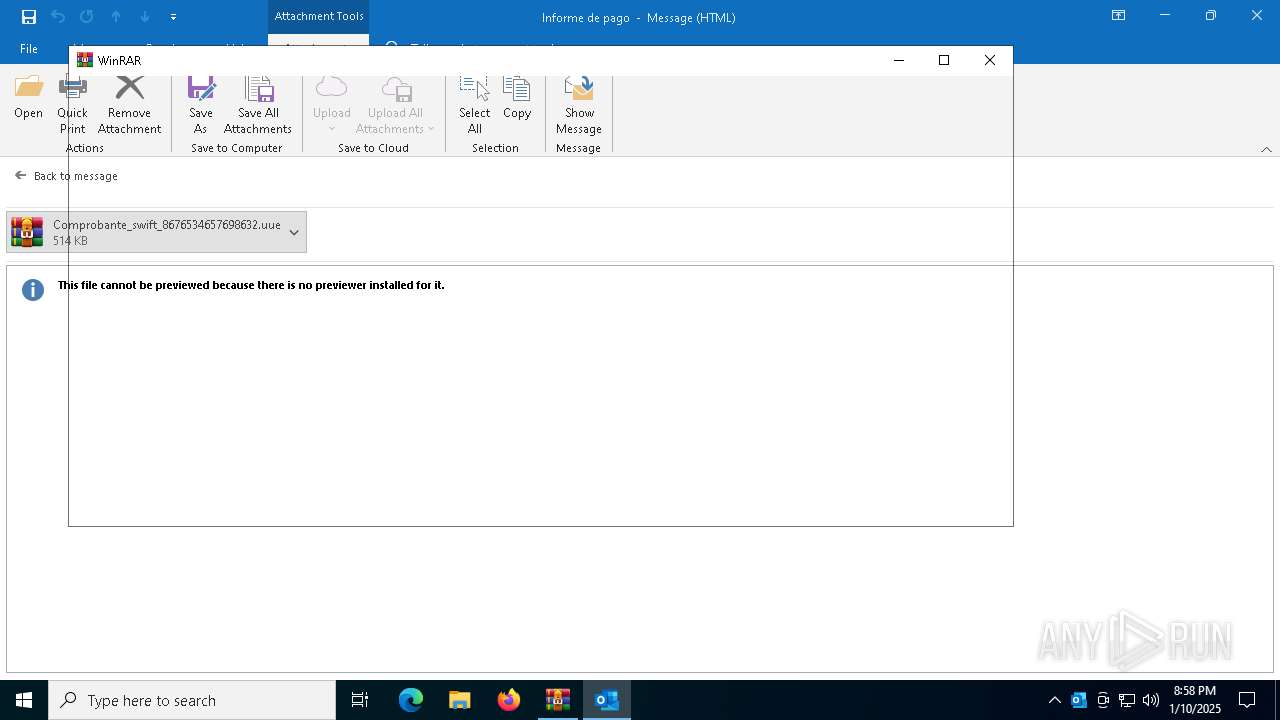
- WinRAR.exe (PID: 6308)
- WinRAR.exe (PID: 6720)
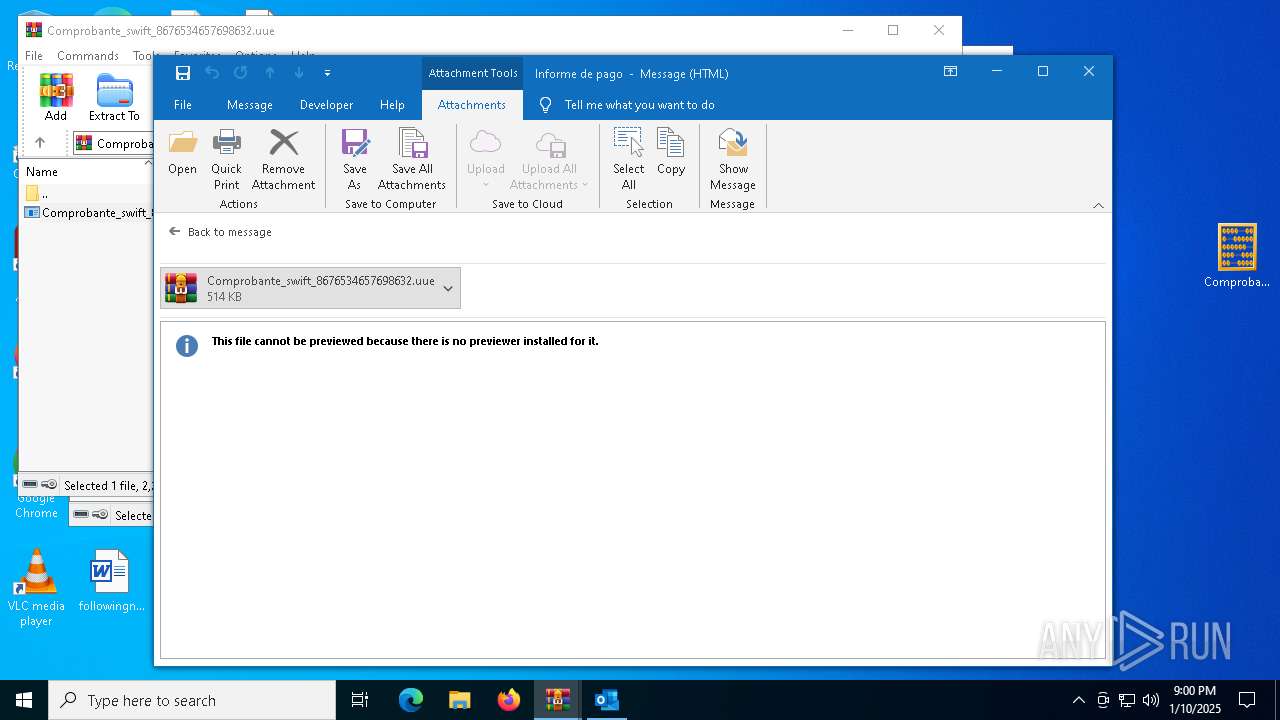
Reads Microsoft Outlook installation path
- WinRAR.exe (PID: 6308)
Checks for external IP
- svchost.exe (PID: 2192)
- RegAsm.exe (PID: 6928)
- RegAsm.exe (PID: 2756)
- RegAsm.exe (PID: 6164)
- RegAsm.exe (PID: 1020)
Connects to FTP
- RegAsm.exe (PID: 6928)
- RegAsm.exe (PID: 2756)
- RegAsm.exe (PID: 6164)
- RegAsm.exe (PID: 1020)
Connects to unusual port
- RegAsm.exe (PID: 6928)
- RegAsm.exe (PID: 2756)
- RegAsm.exe (PID: 6164)
- RegAsm.exe (PID: 1020)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6308)
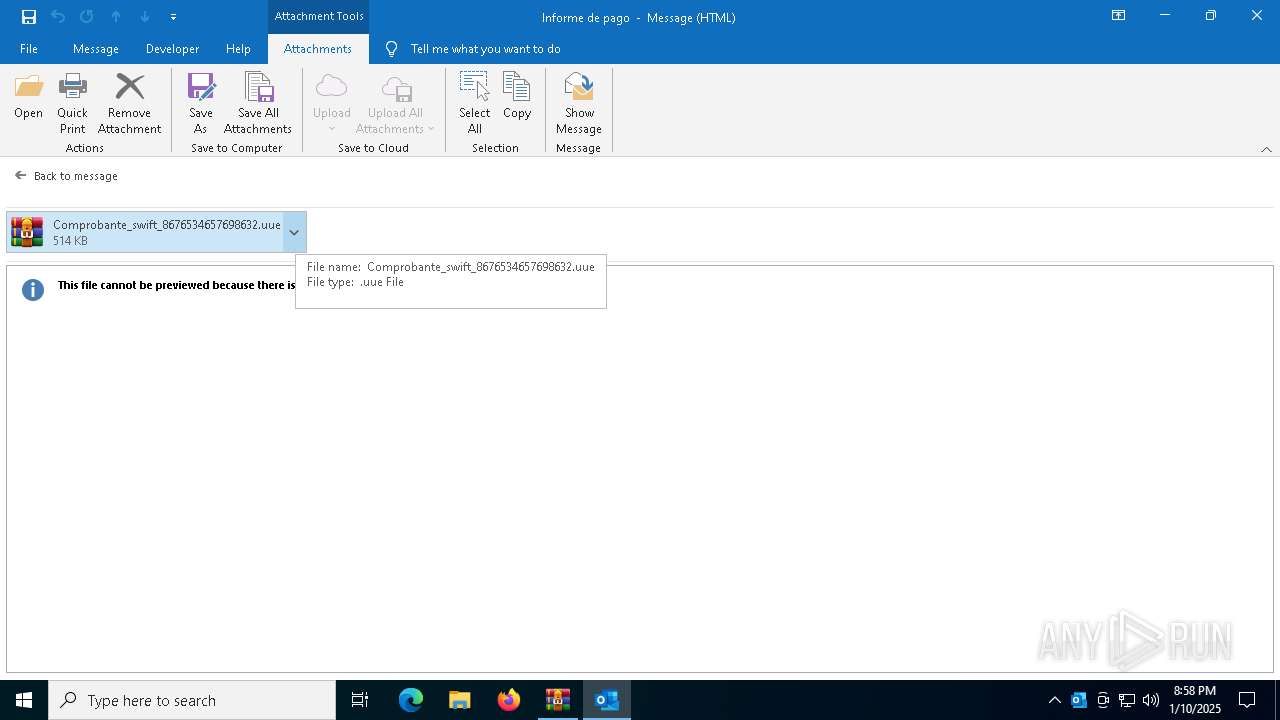
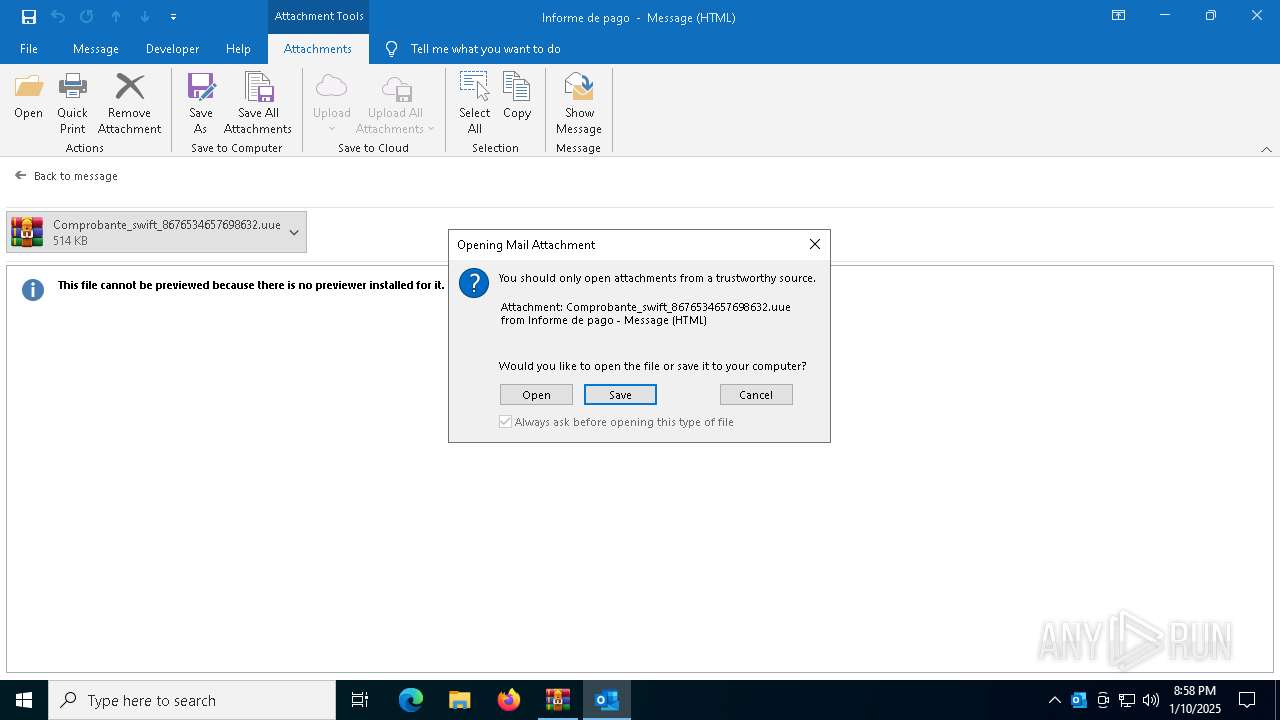
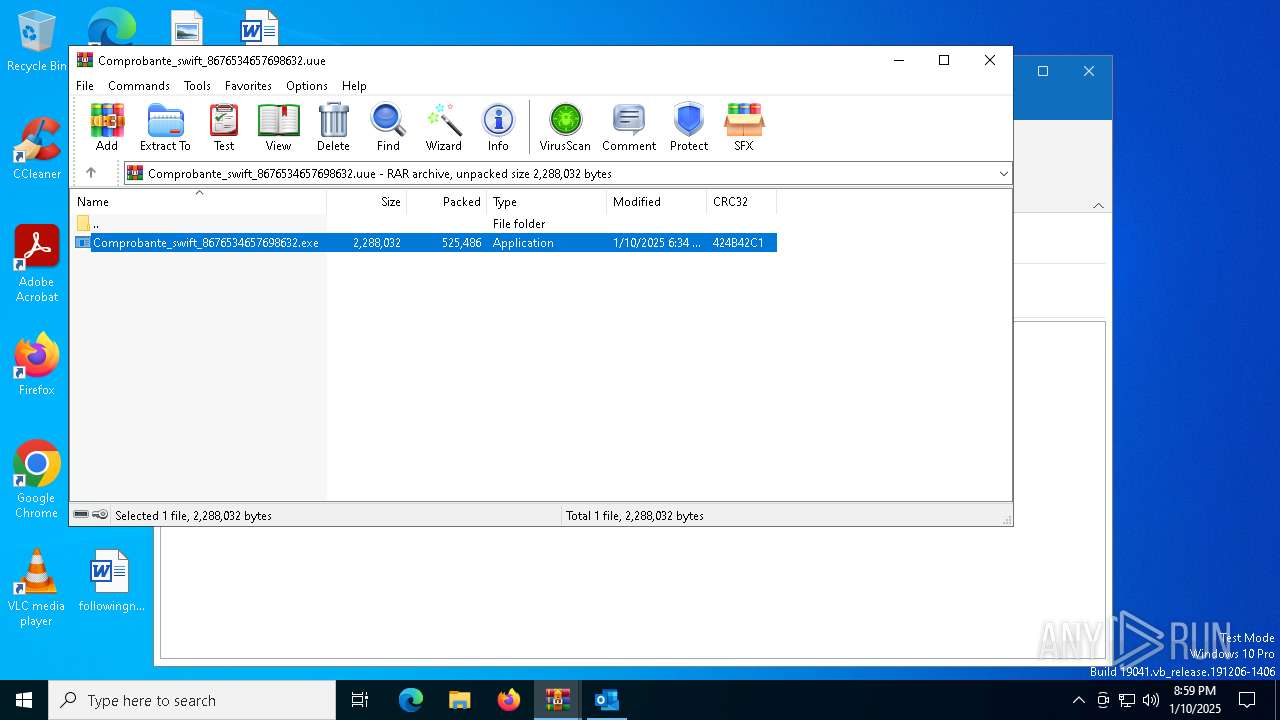
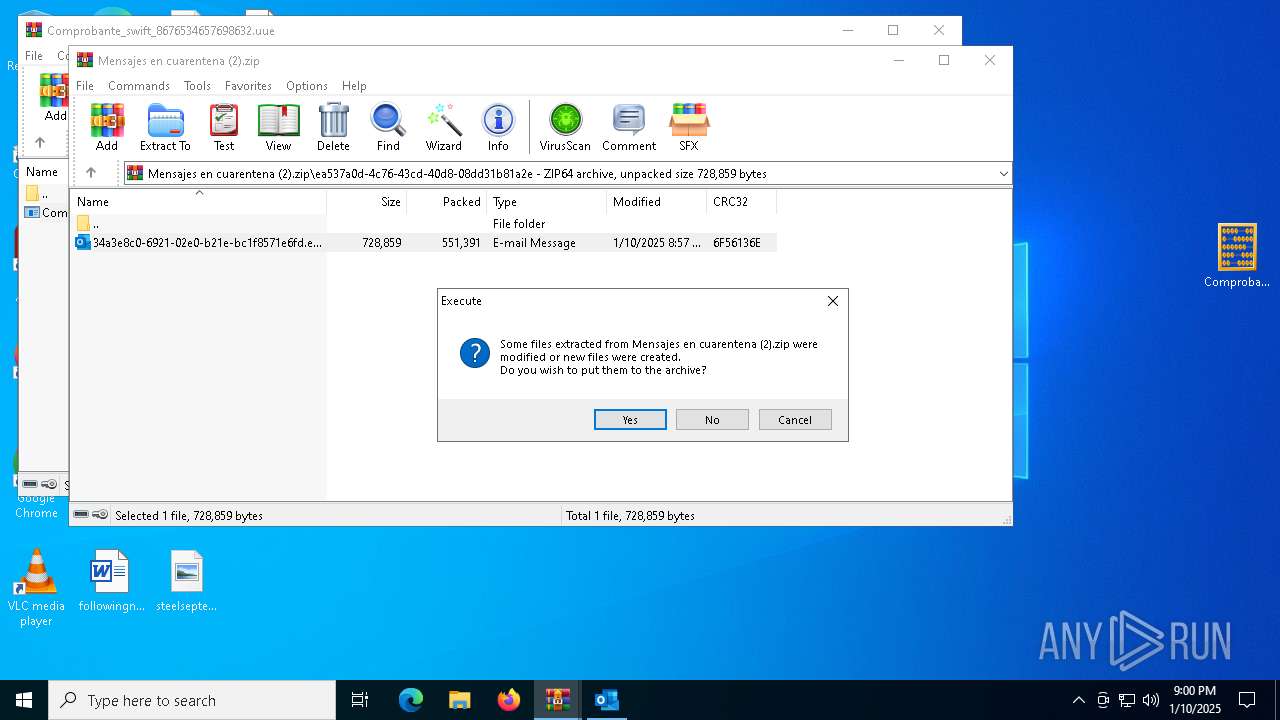
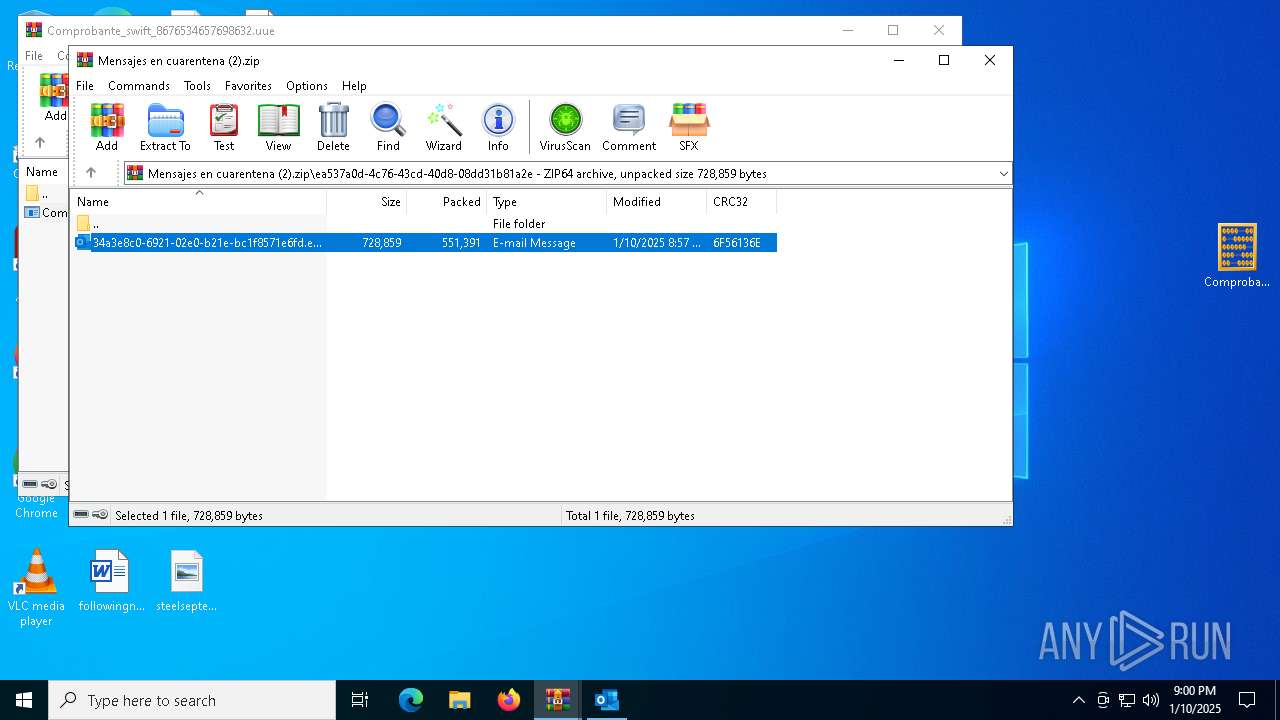
The process uses the downloaded file
- WinRAR.exe (PID: 6308)
- OUTLOOK.EXE (PID: 6988)
- WinRAR.exe (PID: 6720)
The sample compiled with german language support
- WinRAR.exe (PID: 6308)
- OUTLOOK.EXE (PID: 6988)
- WinRAR.exe (PID: 6720)
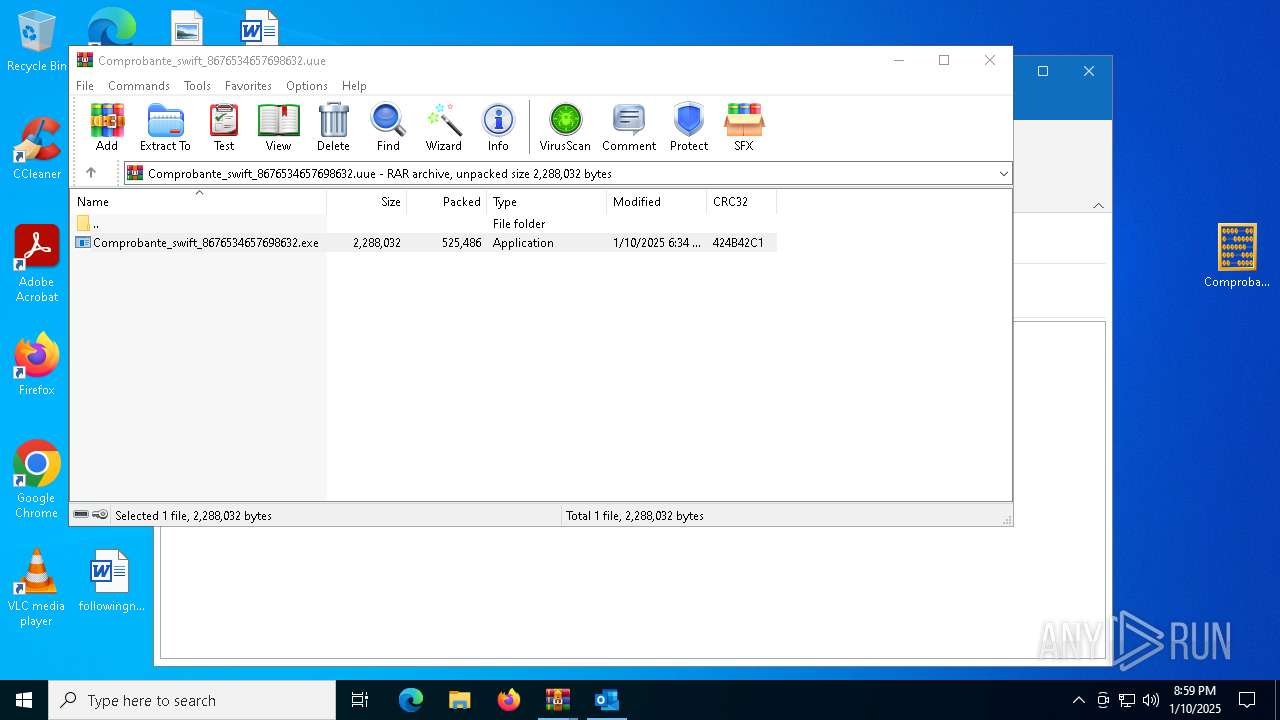
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6720)
Reads the computer name
- Comprobante_swift_8676534657698632.exe (PID: 6832)
- RegAsm.exe (PID: 6928)
- RegAsm.exe (PID: 2756)
- Comprobante_swift_8676534657698632.exe (PID: 3612)
- Comprobante_swift_8676534657698632.exe (PID: 6268)
- RegAsm.exe (PID: 6164)
- Comprobante_swift_8676534657698632.exe (PID: 4864)
- RegAsm.exe (PID: 1020)
Reads the machine GUID from the registry
- Comprobante_swift_8676534657698632.exe (PID: 6832)
- RegAsm.exe (PID: 6928)
- Comprobante_swift_8676534657698632.exe (PID: 3612)
- RegAsm.exe (PID: 2756)
- Comprobante_swift_8676534657698632.exe (PID: 6268)
- RegAsm.exe (PID: 6164)
- Comprobante_swift_8676534657698632.exe (PID: 4864)
- RegAsm.exe (PID: 1020)
Checks supported languages
- Comprobante_swift_8676534657698632.exe (PID: 6832)
- RegAsm.exe (PID: 6928)
- Comprobante_swift_8676534657698632.exe (PID: 3612)
- RegAsm.exe (PID: 2756)
- RegAsm.exe (PID: 6164)
- Comprobante_swift_8676534657698632.exe (PID: 6268)
- Comprobante_swift_8676534657698632.exe (PID: 4864)
- RegAsm.exe (PID: 1020)
Disables trace logs
- RegAsm.exe (PID: 6928)
- RegAsm.exe (PID: 2756)
- RegAsm.exe (PID: 6164)
- RegAsm.exe (PID: 1020)
Checks proxy server information
- RegAsm.exe (PID: 6928)
- RegAsm.exe (PID: 2756)
- RegAsm.exe (PID: 6164)
- RegAsm.exe (PID: 1020)
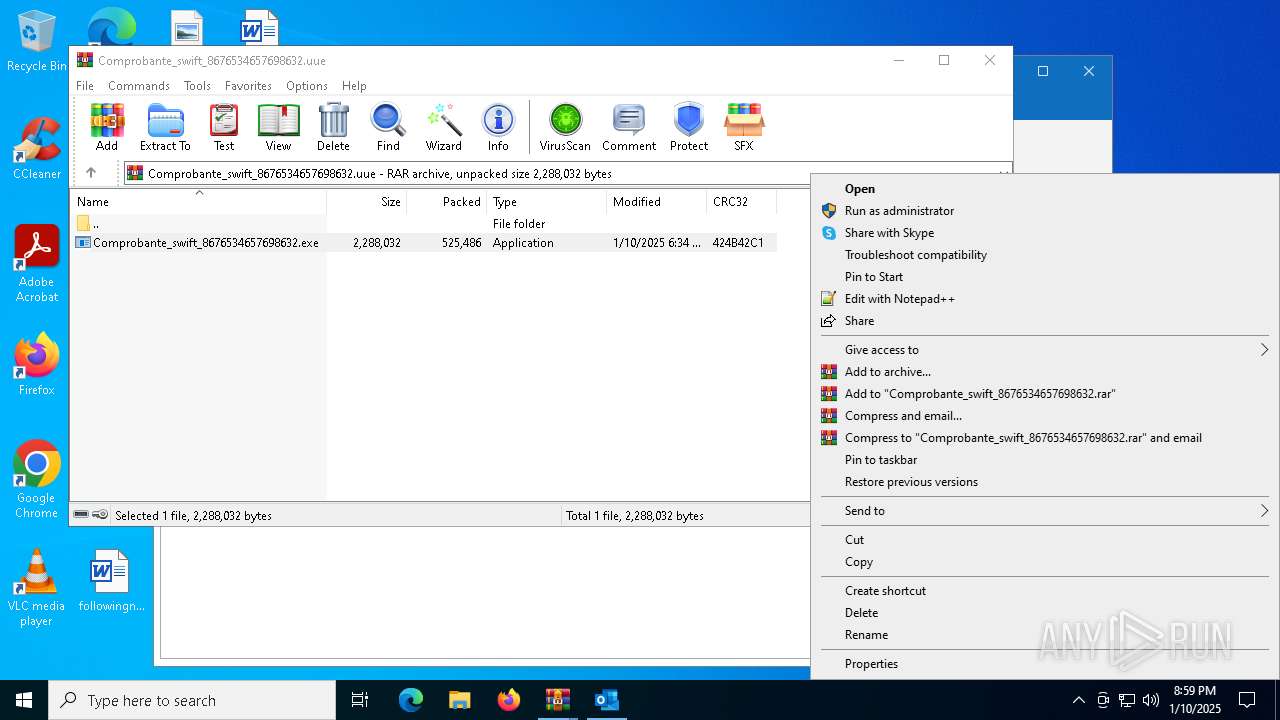
Manual execution by a user
- Comprobante_swift_8676534657698632.exe (PID: 6268)
- Comprobante_swift_8676534657698632.exe (PID: 4864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 45 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:01:10 20:57:50 |
| ZipCRC: | 0x6f56136e |
| ZipCompressedSize: | 4294967295 |
| ZipUncompressedSize: | 4294967295 |
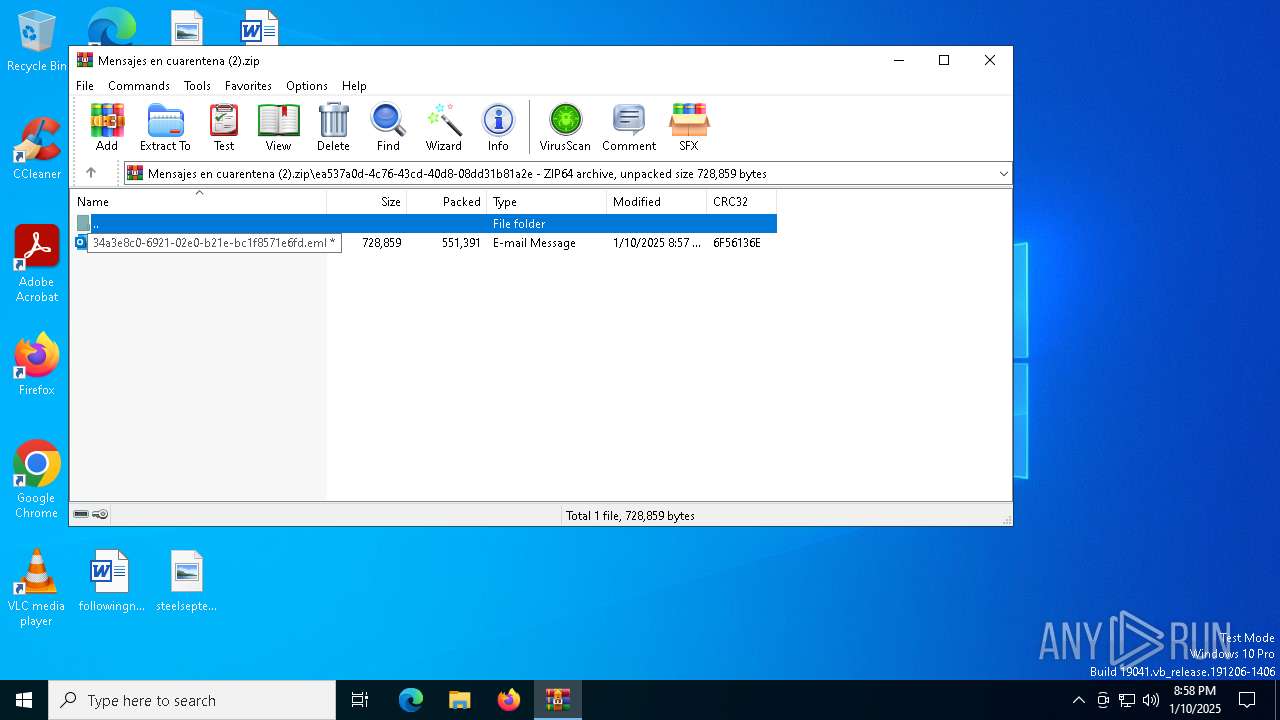
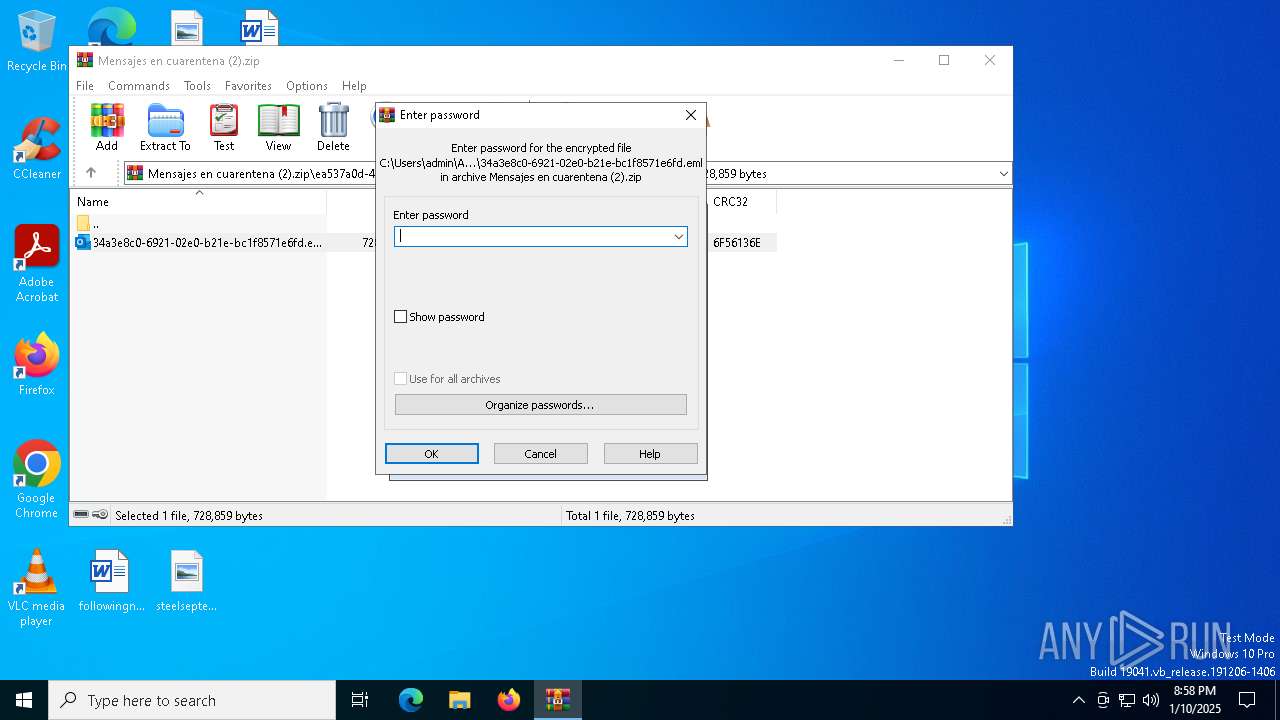
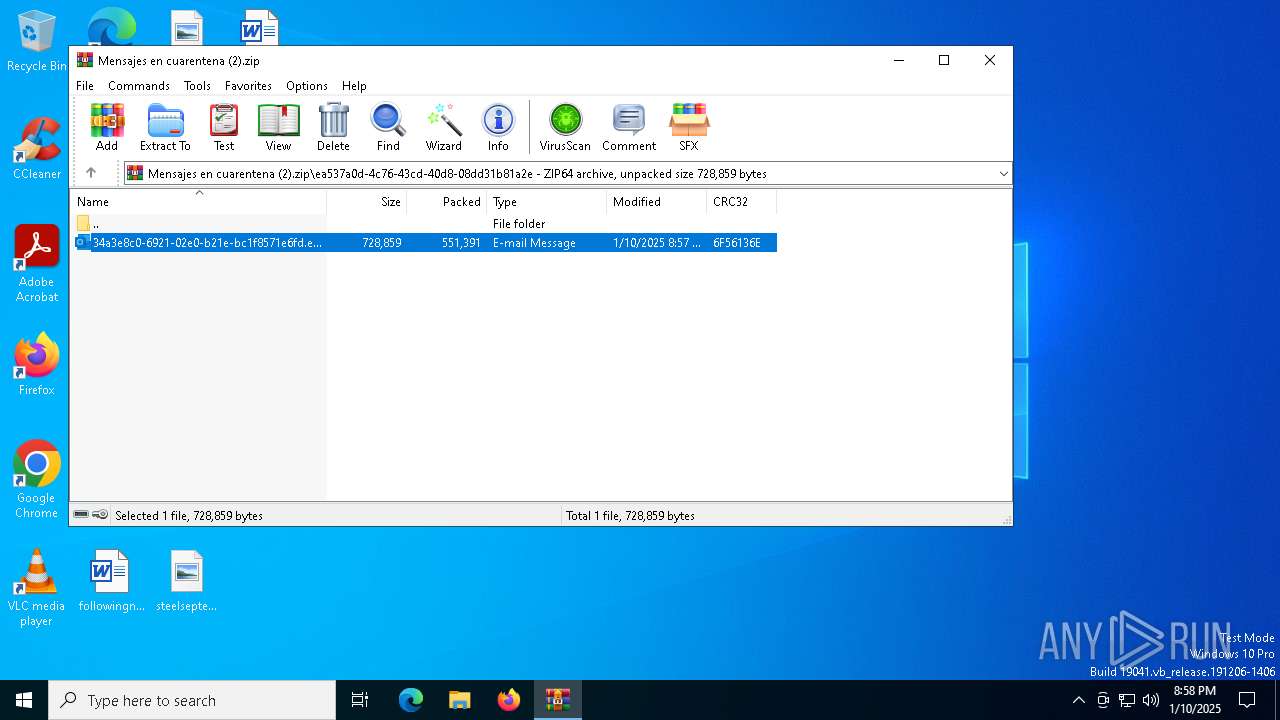
| ZipFileName: | ea537a0d-4c76-43cd-40d8-08dd31b81a2e/34a3e8c0-6921-02e0-b21e-bc1f8571e6fd.eml |
Total processes
146
Monitored processes
15
Malicious processes
12
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | Comprobante_swift_8676534657698632.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "9B53A711-71A1-4D26-B106-9A1FA105C4C9" "876FD6C0-CACD-4310-99FB-EF65255C79D6" "6988" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2456 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | Comprobante_swift_8676534657698632.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2756 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | Comprobante_swift_8676534657698632.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 3612 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6720.5721\Comprobante_swift_8676534657698632.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6720.5721\Comprobante_swift_8676534657698632.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 4824 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | Comprobante_swift_8676534657698632.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4864 | "C:\Users\admin\Desktop\Comprobante_swift_8676534657698632.exe" | C:\Users\admin\Desktop\Comprobante_swift_8676534657698632.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 6164 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | Comprobante_swift_8676534657698632.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 6268 | "C:\Users\admin\Desktop\Comprobante_swift_8676534657698632.exe" | C:\Users\admin\Desktop\Comprobante_swift_8676534657698632.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
21 326
Read events
20 032
Write events
1 122
Delete events
172
Modification events
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Mensajes en cuarentena (2).zip | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (6308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.eml\OpenWithProgids |
| Operation: | write | Name: | Outlook.File.eml.15 |
Value: | |||
Executable files
3
Suspicious files
12
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6988 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 6988 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:BED9E11D6B0C2000F1A2686A8724A074 | SHA256:5D3D93495CCE8C454A1F7A5D536A6AD9B4BFDCAF4AC66EDC0B514EB29DD06A2D | |||
| 6988 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\D5873B44-5411-4ED6-9F97-981FA46589A3 | xml | |
MD5:CD9DA2383ECDE19D168B0C1EFAAA18D6 | SHA256:92F3264B35D4C131210FBC3E870DC04DA483793E0D083159C1A325FE283BEC98 | |||
| 6988 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\olk9696.tmp | binary | |
MD5:13AB33633D1EB79455ABDC598B373402 | SHA256:D7250F51131DD2B8285F2703832879AE3D245721ECB1DE955CD8499BD265F23D | |||
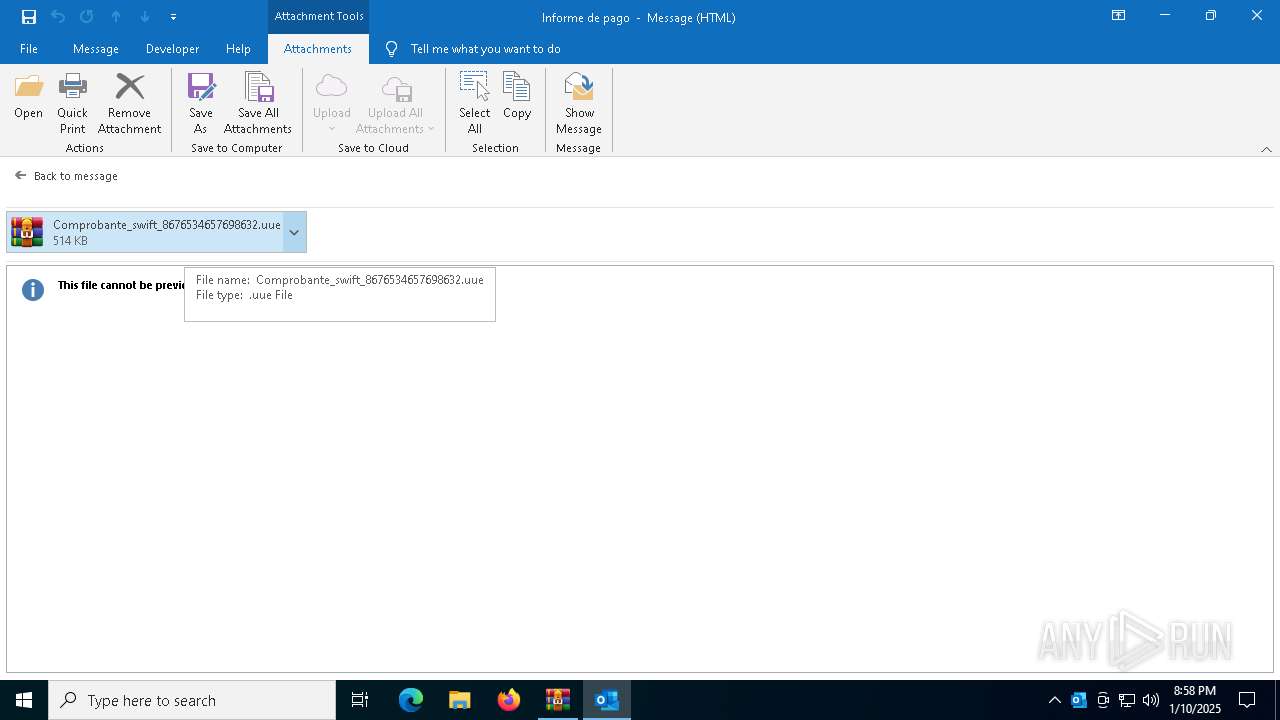
| 6988 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\4L1OS0A8\Comprobante_swift_8676534657698632 (002).uue | compressed | |
MD5:1720019D950FDA4F8F10BF52F77A2A6C | SHA256:757BEB4F94AABE0A81B9502B1AC2ACB45C6C93B48118A116DE10D7C85C718473 | |||
| 6308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb6308.1791\34a3e8c0-6921-02e0-b21e-bc1f8571e6fd.eml:OECustomProperty | binary | |
MD5:D651CE128A7834CA1ED398336D085042 | SHA256:1F000015313DDB29B0B81FC8229958A625236C93CAEACE0E94F54520E5D39B2B | |||
| 6988 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:DD2FFA07581F36C5E0EBC329CB941EDF | SHA256:4E6B8776DFA146BAC3FA1A12F8FED42799538F35BC3D3D8633EFEAD9AAFDC2CF | |||
| 6988 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:2FD53B782FCA2CBB1D795F2F312E35A9 | SHA256:A906D1C813445B37889FF72AED877A0B80E2F902C9875313B9A99EAA6E29A32A | |||
| 6988 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 6988 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:80B7420576EAEF769CBC2A4155E88C86 | SHA256:C733F62A8C0108E72530BE147A1FFFD718D6A5E8F571B838D08AC119899B45F3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
54
DNS requests
29
Threats
42
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
488 | svchost.exe | GET | 200 | 23.48.23.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6524 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
488 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6988 | OUTLOOK.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6988 | OUTLOOK.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
6604 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2756 | RegAsm.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | shared |
6928 | RegAsm.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
488 | svchost.exe | 23.48.23.139:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
488 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.154:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6928 | RegAsm.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
6928 | RegAsm.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
6928 | RegAsm.exe | A Network Trojan was detected | ET MALWARE AgentTesla Exfil via FTP |
6928 | RegAsm.exe | Misc activity | INFO [ANY.RUN] FTP protocol command for uploading a file |
6928 | RegAsm.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
6928 | RegAsm.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
2756 | RegAsm.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2756 | RegAsm.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
8 ETPRO signatures available at the full report