| File name: | 5160514.doc |
| Full analysis: | https://app.any.run/tasks/80464c35-e9f8-44ed-a346-50bf0642cec9 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | April 23, 2019, 12:09:18 |
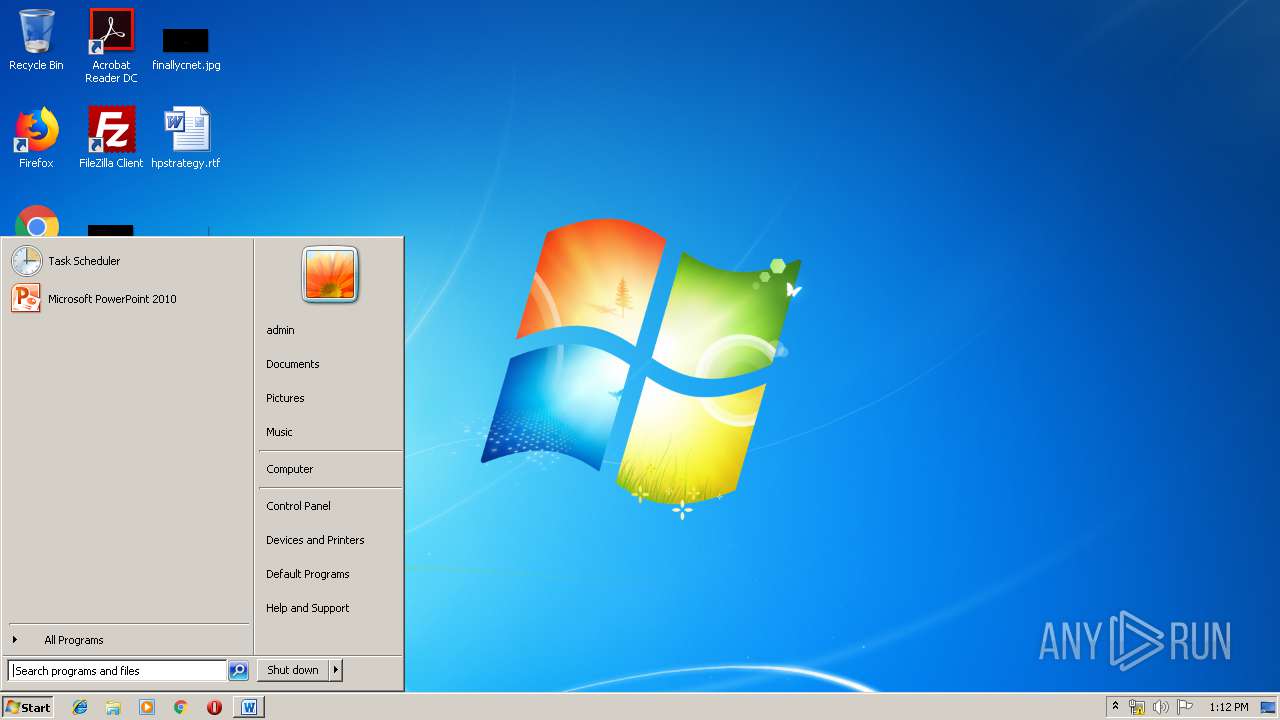
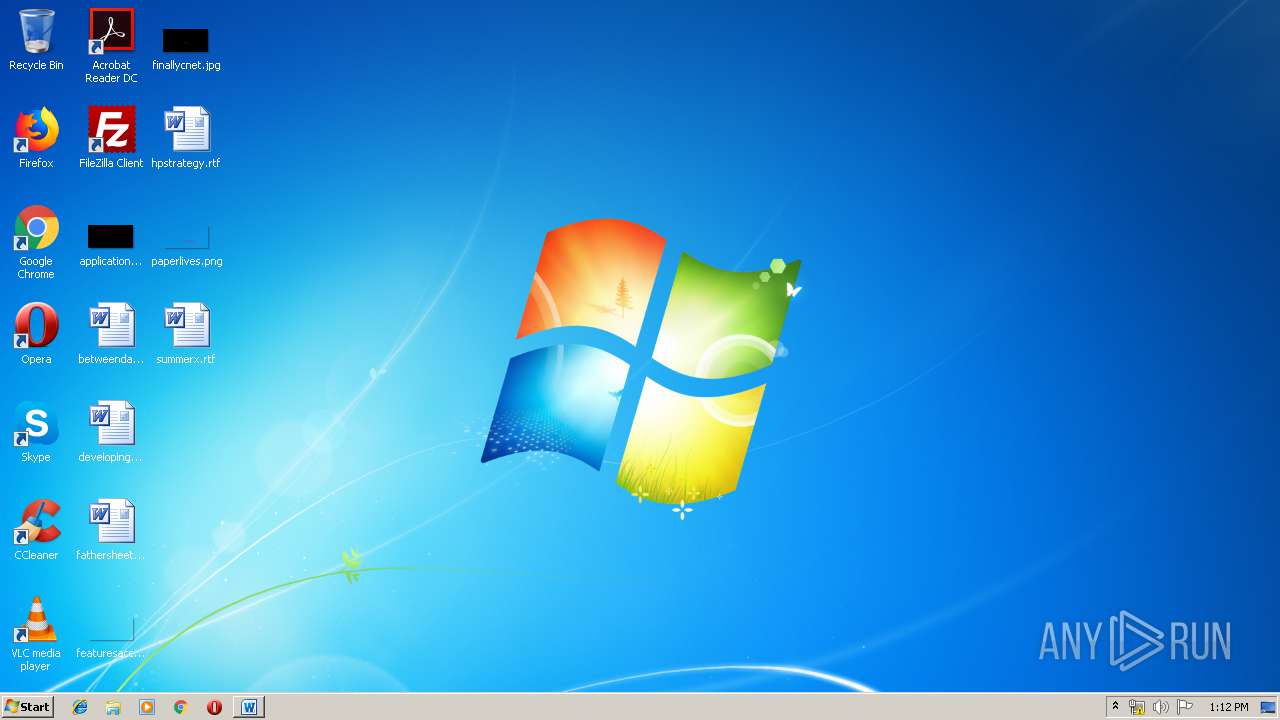
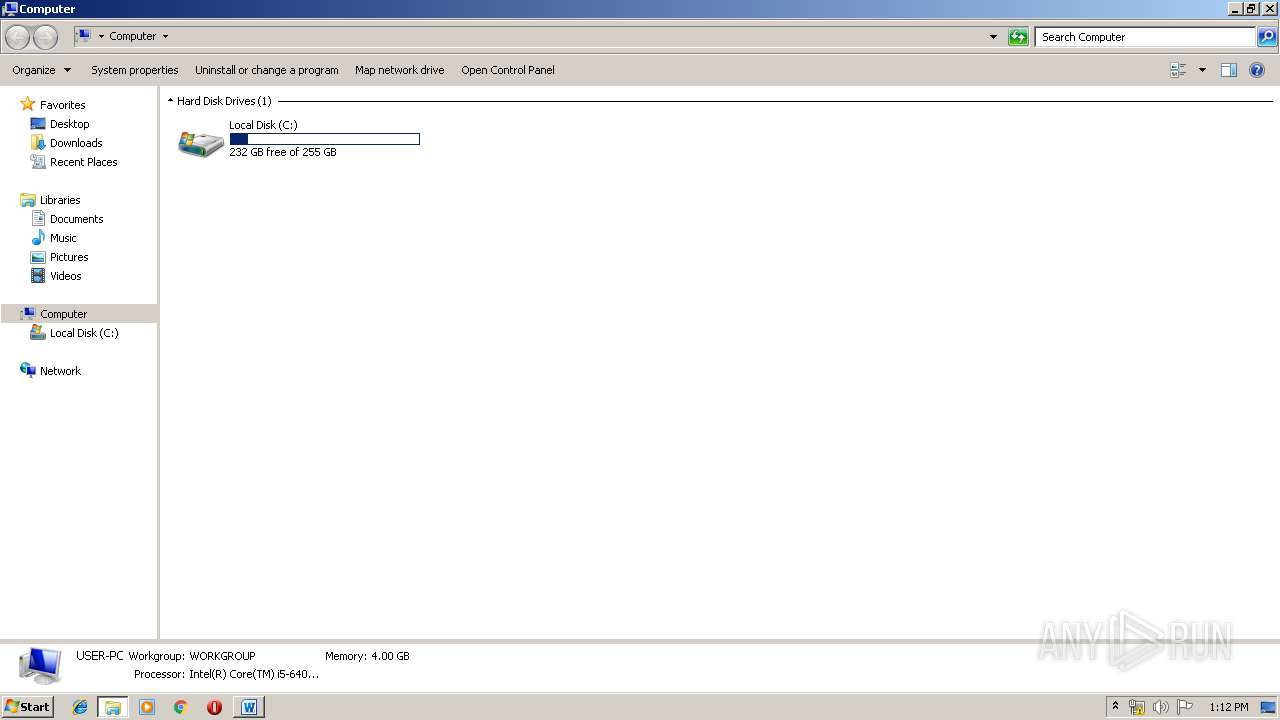
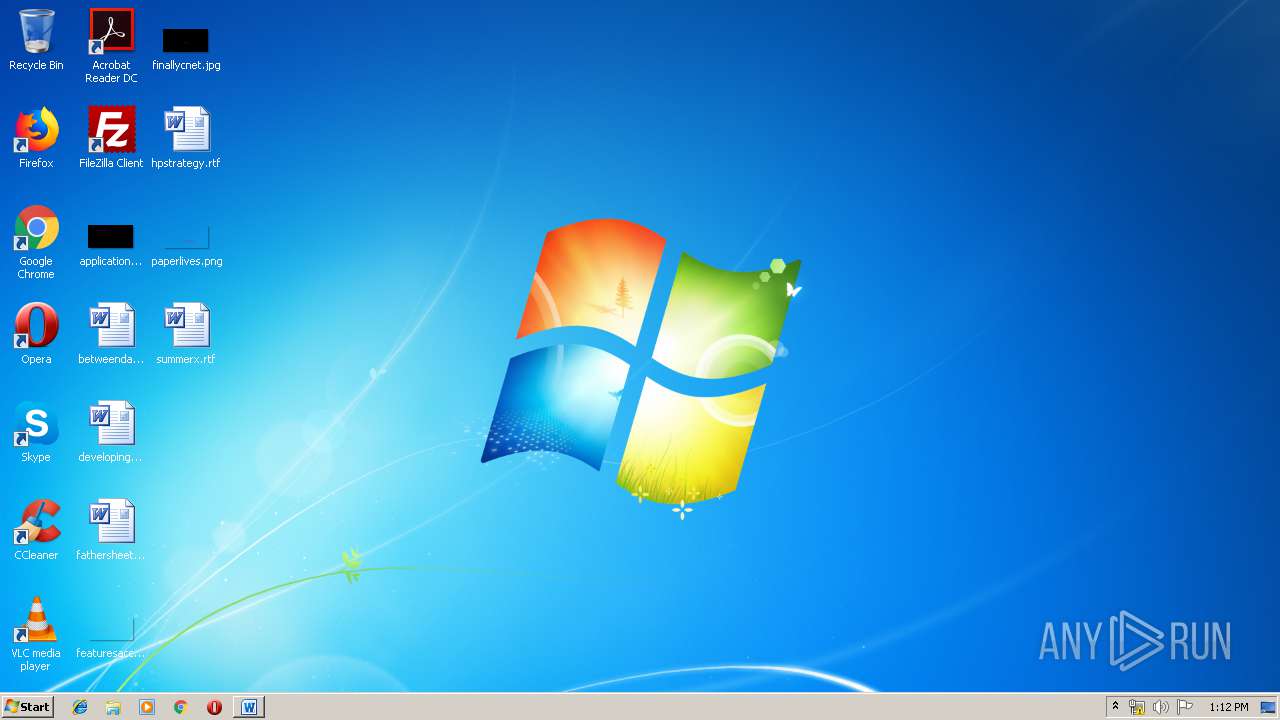
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | BB8F410028DA1CEDD5DC84CE3605894D |
| SHA1: | E10CBC7BD729FA3C63A4D5127BFD191D1A77B658 |
| SHA256: | D7E42CF34DCE49C1287EE180186863E8FA9CAF9ACD507A3DB3CA8798A1B8326E |
| SSDEEP: | 3072:8/luOqPkeSeJLZQMqkFbB/05GbLyAa71OtQvVZgK1sCIfBuZG:CUOoJmot1Pa71IQ3F1sCIz |
MALICIOUS
Application was dropped or rewritten from another process
- vuyj43.tmp (PID: 2660)
- smjalrc.exe (PID: 4036)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2912)
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 2912)
AMADEY was detected
- smjalrc.exe (PID: 4036)
Changes the Startup folder
- REG.exe (PID: 2148)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2912)
Connects to CnC server
- smjalrc.exe (PID: 4036)
SUSPICIOUS
Starts application with an unusual extension
- WINWORD.EXE (PID: 2912)
Executable content was dropped or overwritten
- vuyj43.tmp (PID: 2660)
Creates files in the program directory
- vuyj43.tmp (PID: 2660)
Uses REG.EXE to modify Windows registry
- smjalrc.exe (PID: 4036)
Starts itself from another location
- vuyj43.tmp (PID: 2660)
Connects to server without host name
- smjalrc.exe (PID: 4036)
INFO
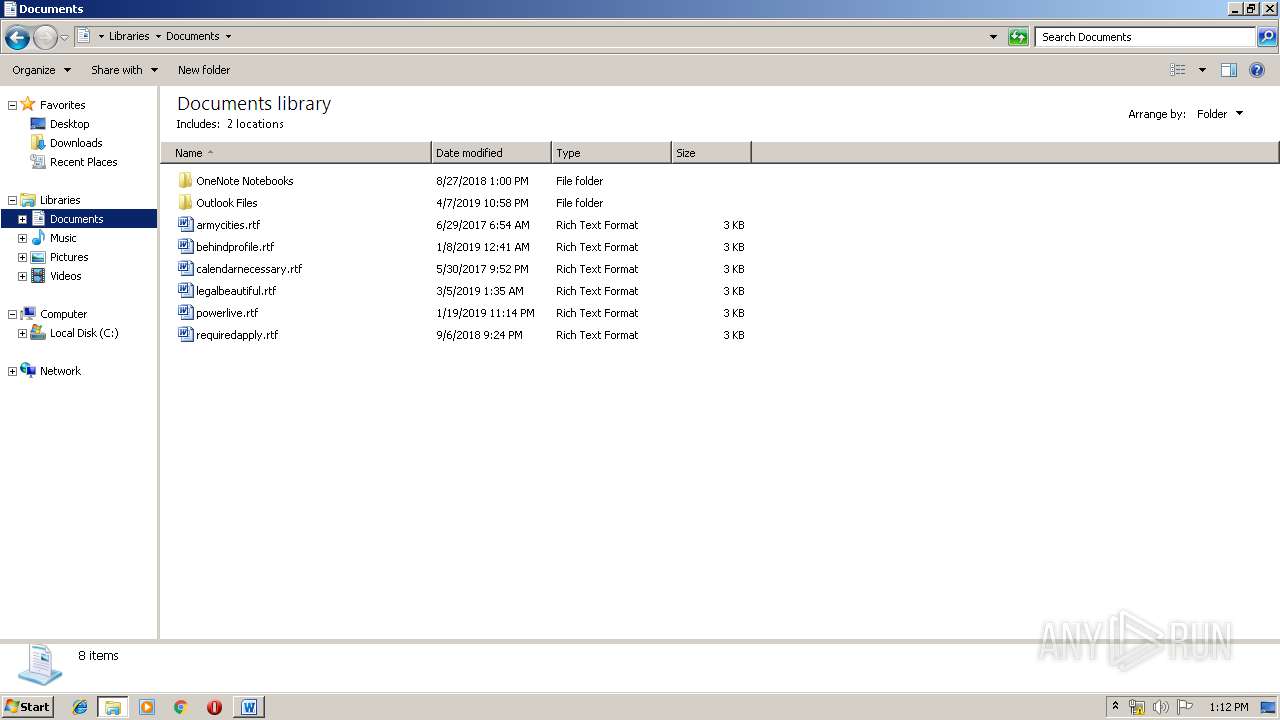
Creates files in the user directory
- WINWORD.EXE (PID: 2912)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2148 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /f /v Startup /t REG_SZ /d C:\ProgramData\fe97e9e43b | C:\Windows\system32\REG.exe | smjalrc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | C:\Users\admin\AppData\Local\Temp\vuyj43.tmp | C:\Users\admin\AppData\Local\Temp\vuyj43.tmp | WINWORD.EXE | ||||||||||||
User: admin Company: Social Finance Integrity Level: MEDIUM Description: Captcha Mother Iobjectaccesscontrol Duplexed Exit code: 0 Version: 6.8.2.5 Modules
| |||||||||||||||
| 2912 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\5160514.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4036 | c:\programdata\fe97e9e43b\smjalrc.exe | c:\programdata\fe97e9e43b\smjalrc.exe | vuyj43.tmp | ||||||||||||
User: admin Company: Social Finance Integrity Level: MEDIUM Description: Captcha Mother Iobjectaccesscontrol Duplexed Exit code: 0 Version: 6.8.2.5 Modules
| |||||||||||||||
Total events
1 158
Read events
824
Write events
329
Delete events
5
Modification events
| (PID) Process: | (2912) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ta> |
Value: 74613E00600B0000010000000000000000000000 | |||
| (PID) Process: | (2912) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2912) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2912) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318518814 | |||
| (PID) Process: | (2912) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318518936 | |||
| (PID) Process: | (2912) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318518937 | |||
| (PID) Process: | (2912) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 600B00006E76BE69CDF9D40100000000 | |||
| (PID) Process: | (2912) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | .b> |
Value: 2E623E00600B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2912) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | .b> |
Value: 2E623E00600B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2912) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFD54.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2912 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF7629F32AA914964E.TMP | — | |
MD5:— | SHA256:— | |||
| 2912 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF3F47E06D8EAE1BDE.TMP | — | |
MD5:— | SHA256:— | |||
| 2912 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF8BDC1FE20B619469.TMP | — | |
MD5:— | SHA256:— | |||
| 2912 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA2BA3C8A8DBE0D2B.TMP | — | |
MD5:— | SHA256:— | |||
| 2912 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF875721D01E0BEDA5.TMP | — | |
MD5:— | SHA256:— | |||
| 2912 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF6901483296D4B27B.TMP | — | |
MD5:— | SHA256:— | |||
| 2660 | vuyj43.tmp | C:\ProgramData\0 | — | |
MD5:— | SHA256:— | |||
| 2660 | vuyj43.tmp | C:\programdata\fe97e9e43b\smjalrc.exe:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 4036 | smjalrc.exe | C:\ProgramData\0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
1
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2912 | WINWORD.EXE | GET | 200 | 87.98.158.248:80 | http://trinatcapererpicel.info/word66.tmp | FR | executable | 383 Kb | suspicious |
4036 | smjalrc.exe | POST | 200 | 95.179.189.49:80 | http://95.179.189.49/CC/index.php | GR | text | 6 b | malicious |
4036 | smjalrc.exe | POST | 200 | 95.179.189.49:80 | http://95.179.189.49/CC/index.php | GR | text | 6 b | malicious |
4036 | smjalrc.exe | POST | 200 | 95.179.189.49:80 | http://95.179.189.49/CC/index.php | GR | text | 6 b | malicious |
4036 | smjalrc.exe | POST | 200 | 95.179.189.49:80 | http://95.179.189.49/CC/index.php | GR | text | 6 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2912 | WINWORD.EXE | 87.98.158.248:80 | trinatcapererpicel.info | OVH SAS | FR | suspicious |
4036 | smjalrc.exe | 95.179.189.49:80 | — | Cosmoline Telecommunication Services S.A. | GR | malicious |
— | — | 95.179.189.49:80 | — | Cosmoline Telecommunication Services S.A. | GR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
trinatcapererpicel.info |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2912 | WINWORD.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2912 | WINWORD.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
2912 | WINWORD.EXE | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
4036 | smjalrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
4036 | smjalrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
4036 | smjalrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
4036 | smjalrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
4036 | smjalrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
4036 | smjalrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
4036 | smjalrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
4 ETPRO signatures available at the full report