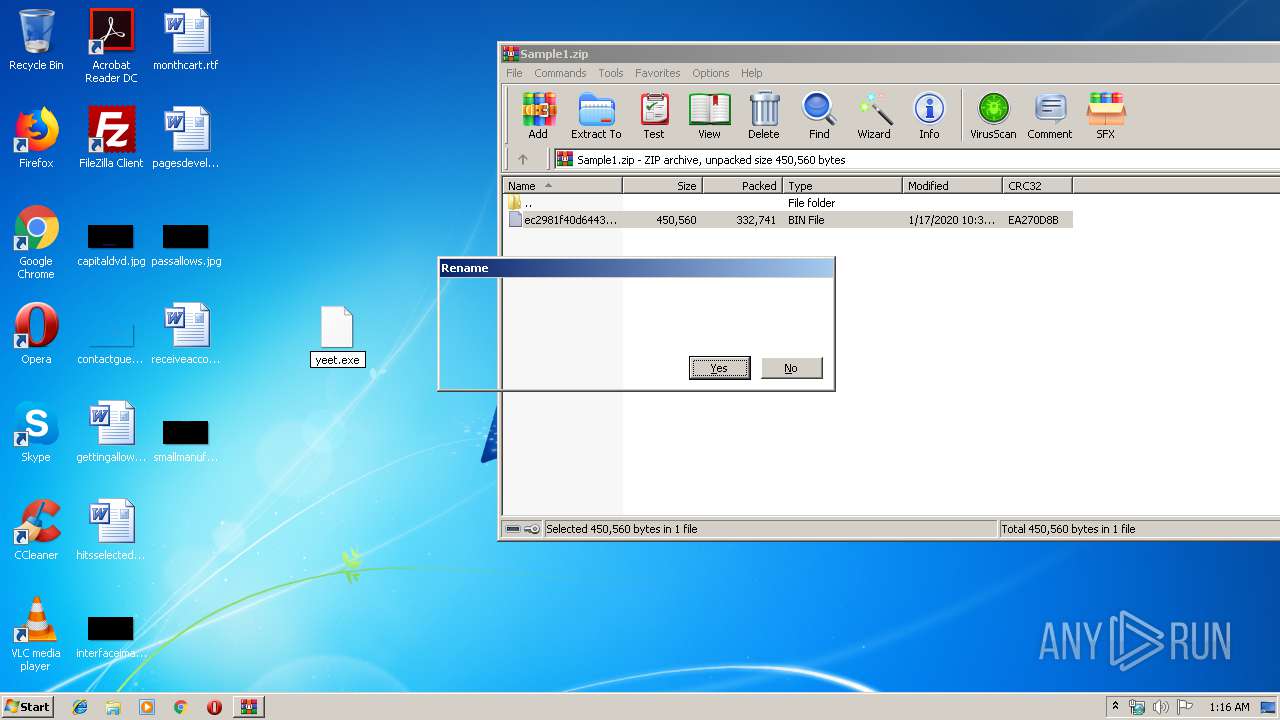
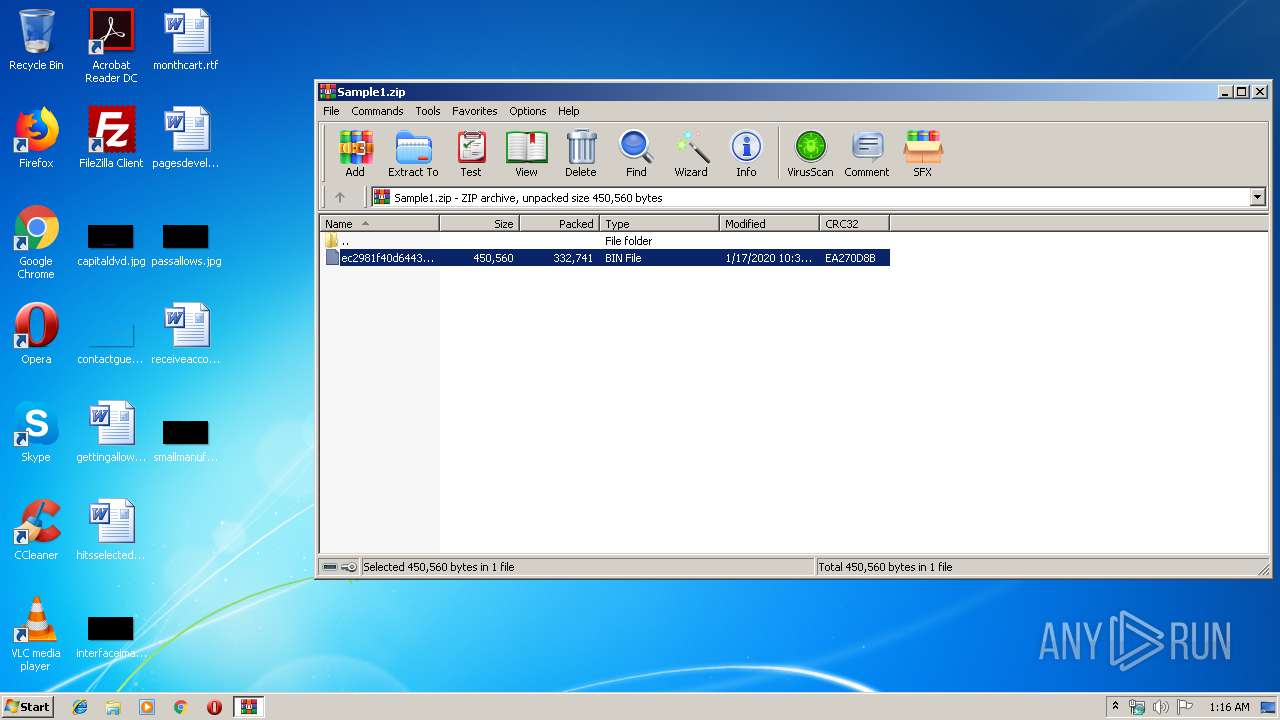
| File name: | Sample1.zip |
| Full analysis: | https://app.any.run/tasks/35133008-5c55-4dcd-9104-b9f16cf6c85c |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | January 18, 2020, 01:16:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
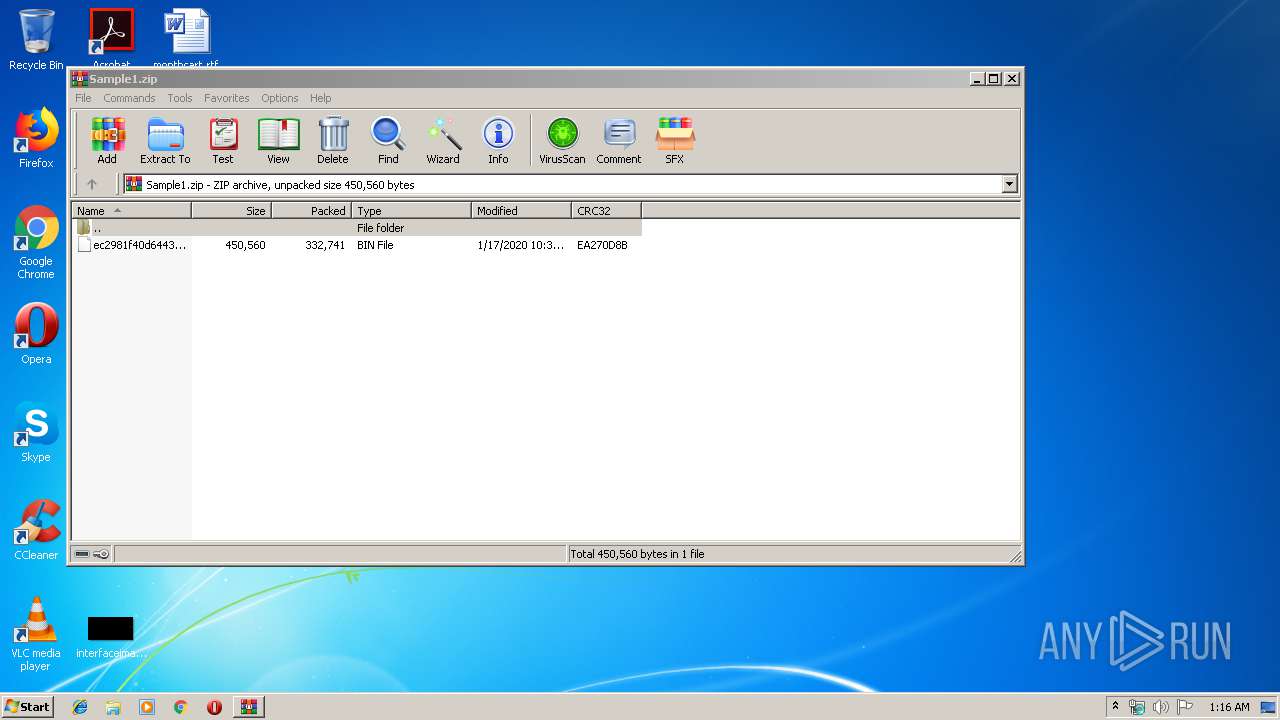
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E768C1F6CC44D3776AB9C9EE92C8C0D8 |
| SHA1: | 906E04A33C4E081A8B83E877F25BBD158FCF0567 |
| SHA256: | D7B1D3CFF374E29E166F0A03761F670FA4DB012E0894977C46F2336A4F56DCBB |
| SSDEEP: | 6144:2bZ8E7CPsBxTddI/CdAtAb0aRnXiObpawayRElken8MBs3VVU6IyI:a8QCPsLTDWBQnXiiawpEke/C7U61I |
MALICIOUS
Application was dropped or rewritten from another process
- yeet.exe (PID: 1648)
- Explorers.exe (PID: 4924)
- Explorers.exe (PID: 7984)
- WHost.exe (PID: 9312)
- Explorers.exe (PID: 2484)
Changes the autorun value in the registry
- Explorers.exe (PID: 4924)
- Explorers.exe (PID: 7984)
- WHost.exe (PID: 9312)
NANOCORE was detected
- Explorers.exe (PID: 7984)
Uses Task Scheduler to run other applications
- Explorers.exe (PID: 7984)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 10204)
- schtasks.exe (PID: 11200)
Connects to CnC server
- Explorers.exe (PID: 2484)
AVEMARIA was detected
- Explorers.exe (PID: 2484)
SUSPICIOUS
Reads Internet Cache Settings
- yeet.exe (PID: 1648)
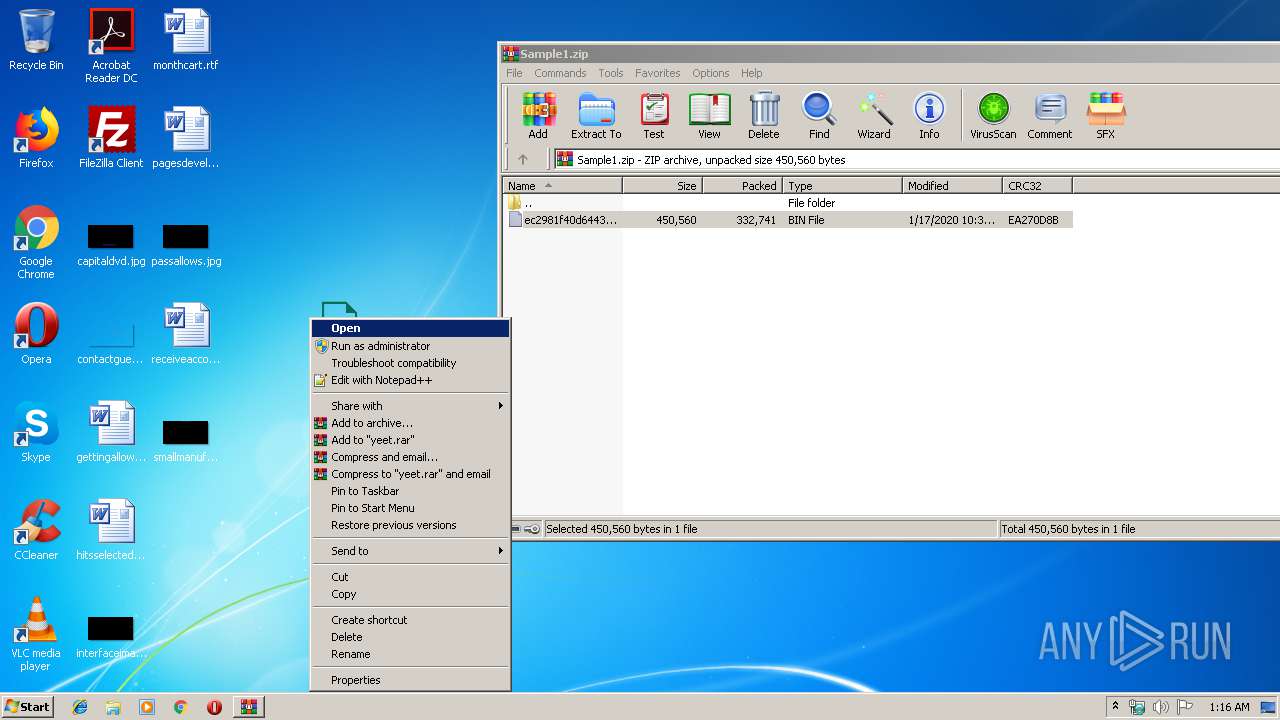
Executable content was dropped or overwritten
- yeet.exe (PID: 1648)
- Explorers.exe (PID: 4924)
- Explorers.exe (PID: 7984)
- WHost.exe (PID: 9312)
Creates files in the user directory
- yeet.exe (PID: 1648)
- Explorers.exe (PID: 4924)
- Explorers.exe (PID: 7984)
Starts itself from another location
- yeet.exe (PID: 1648)
- WHost.exe (PID: 9312)
Application launched itself
- Explorers.exe (PID: 4924)
Creates files in the program directory
- Explorers.exe (PID: 7984)
- WHost.exe (PID: 9312)
Connects to unusual port
- Explorers.exe (PID: 7984)
- Explorers.exe (PID: 2484)
Reads the machine GUID from the registry
- Explorers.exe (PID: 2484)
INFO
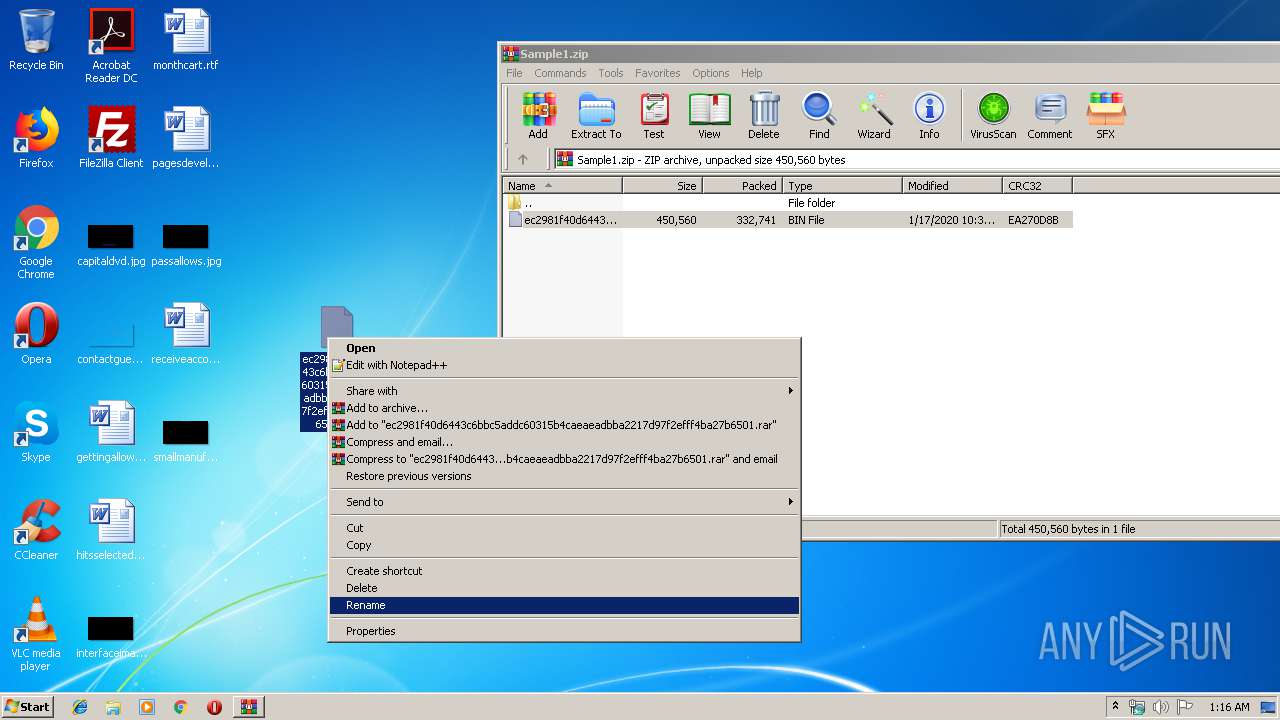
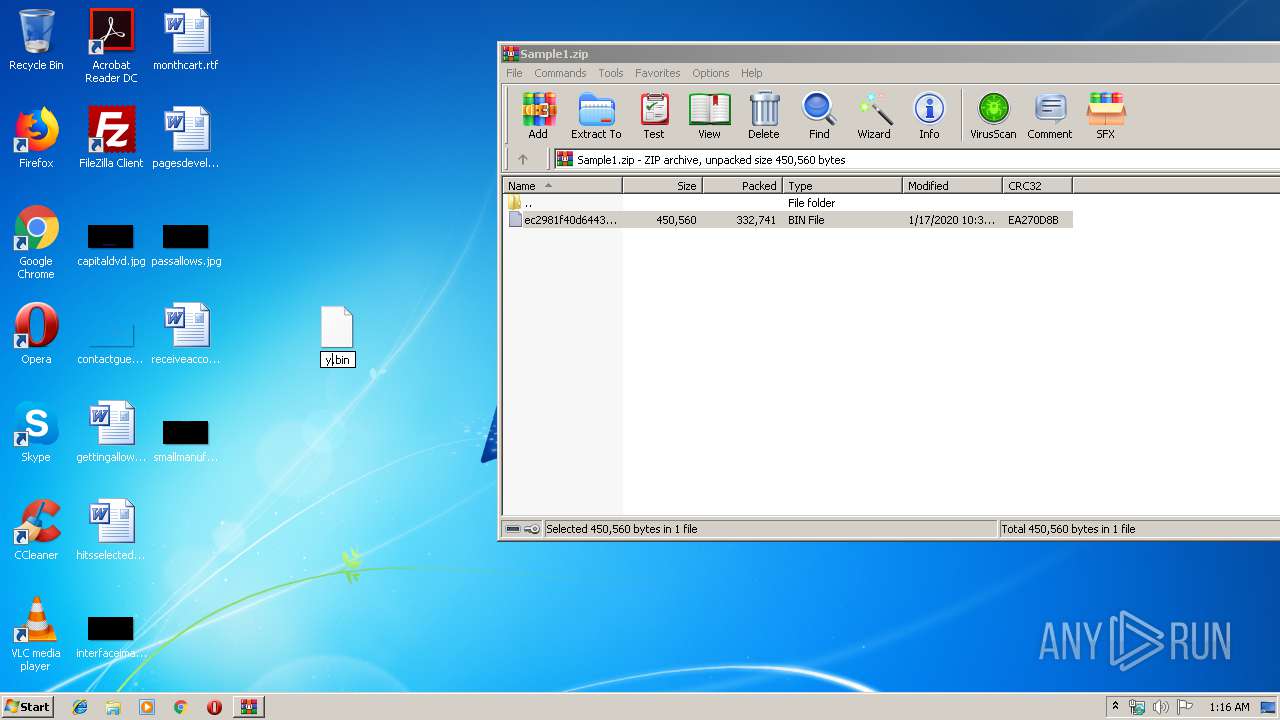
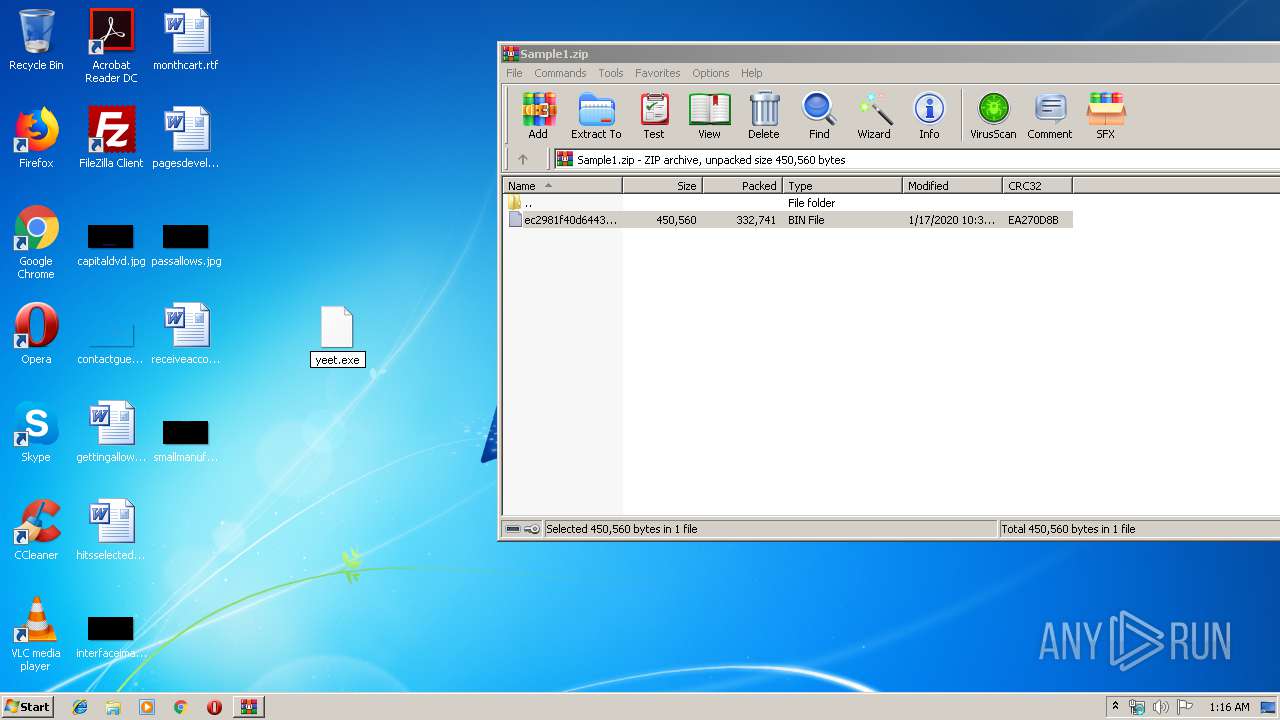
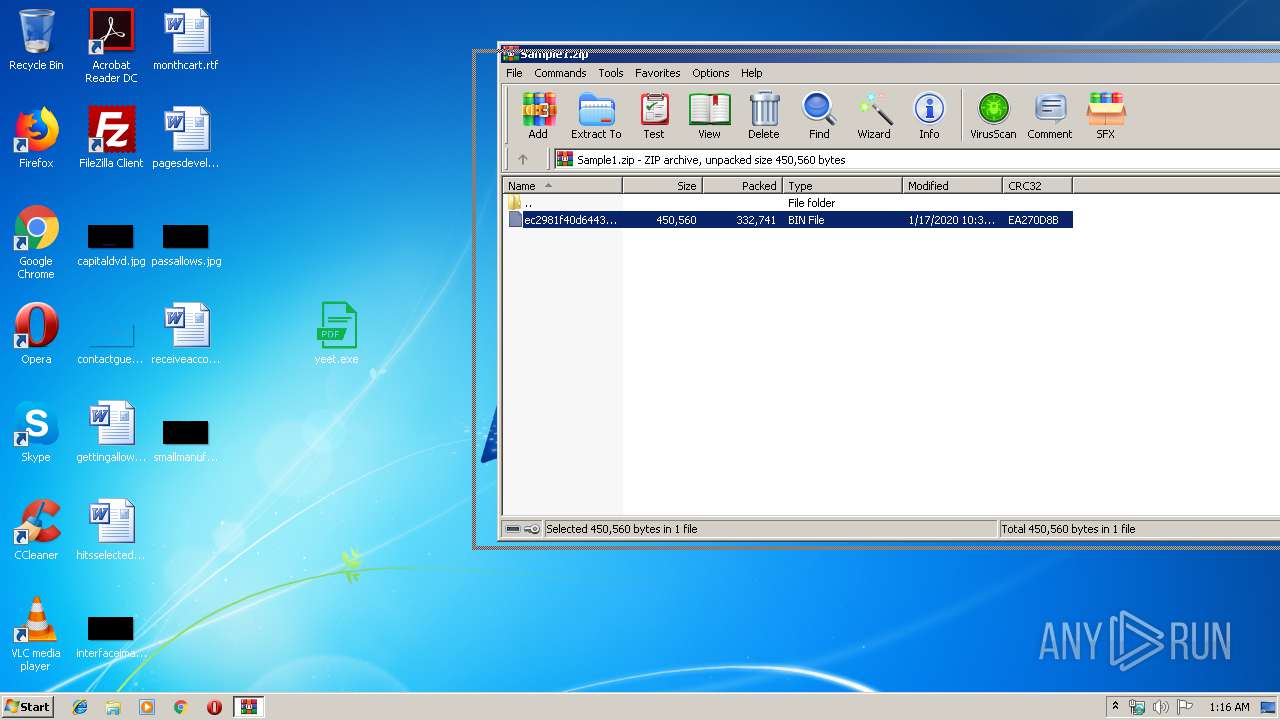
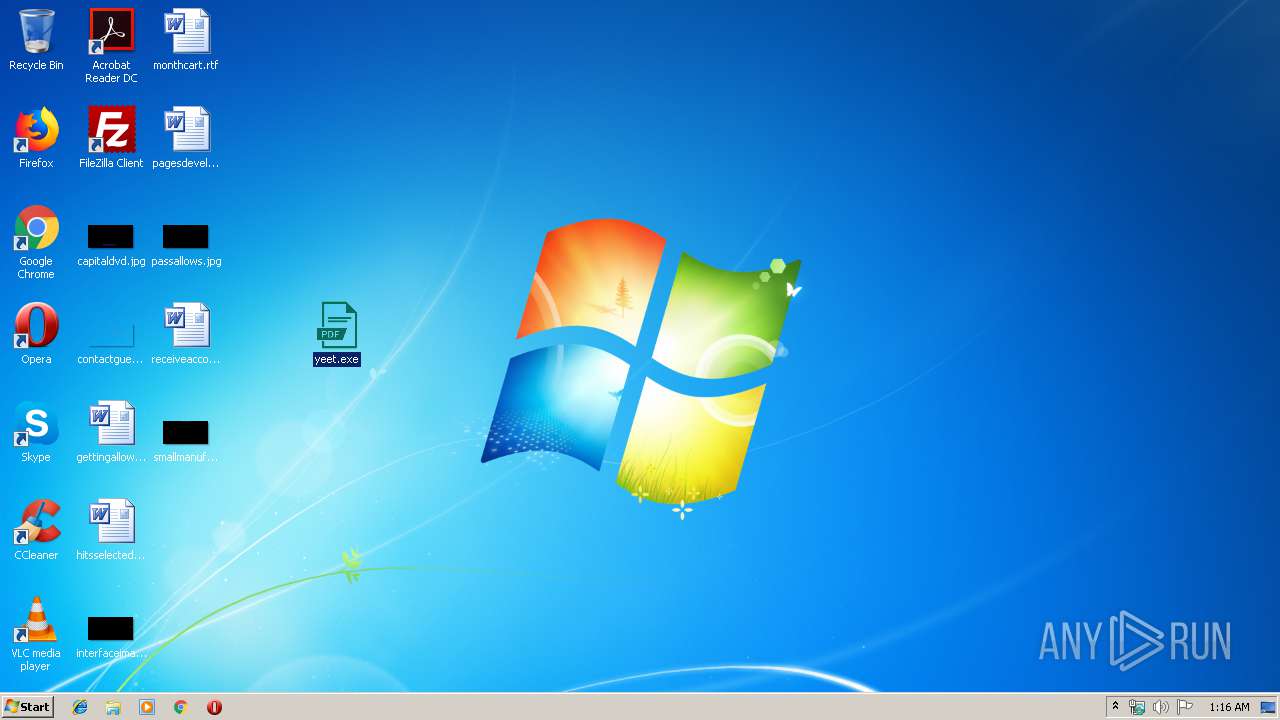
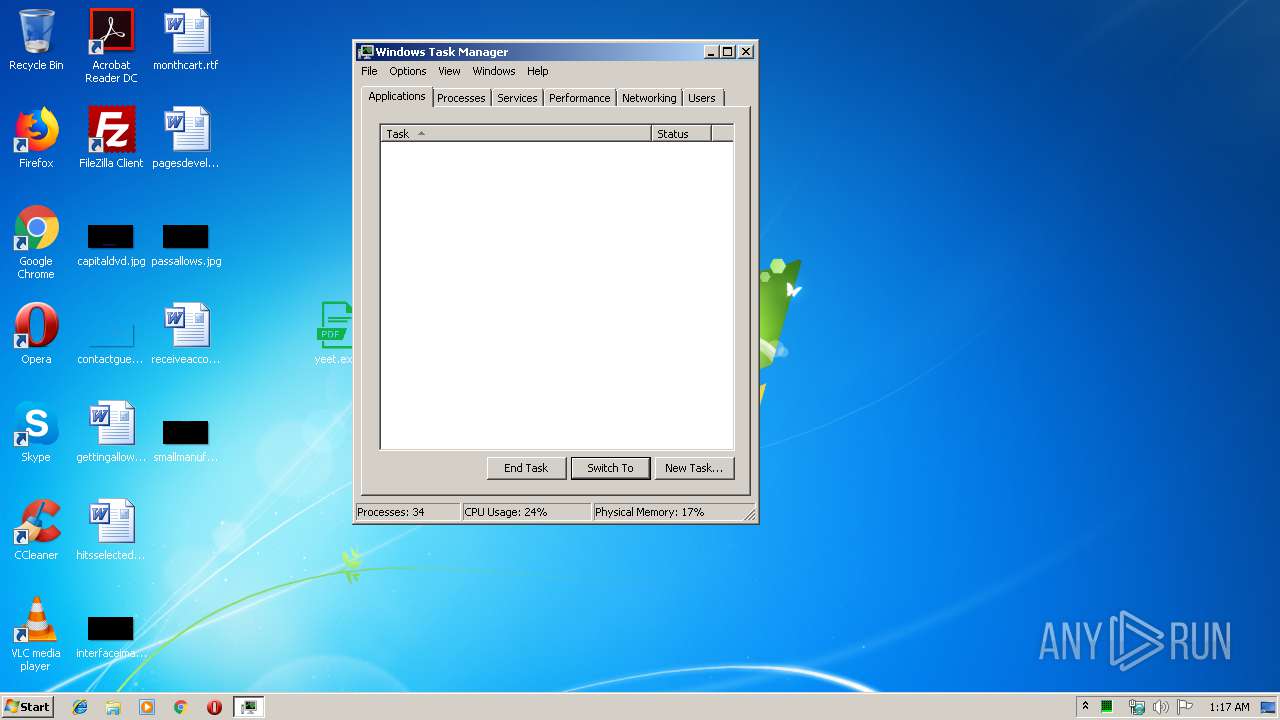
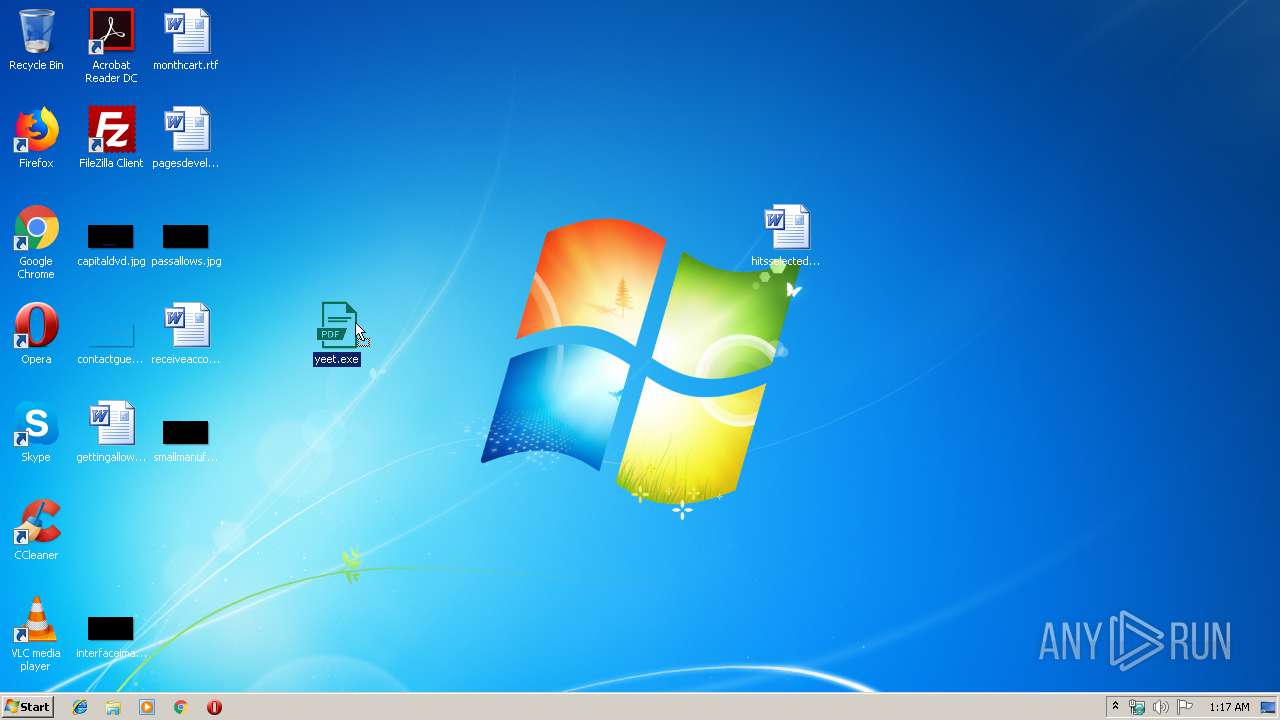
Manual execution by user
- yeet.exe (PID: 1648)
- taskmgr.exe (PID: 11744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:01:17 22:34:21 |
| ZipCRC: | 0xea270d8b |
| ZipCompressedSize: | 332741 |
| ZipUncompressedSize: | 450560 |
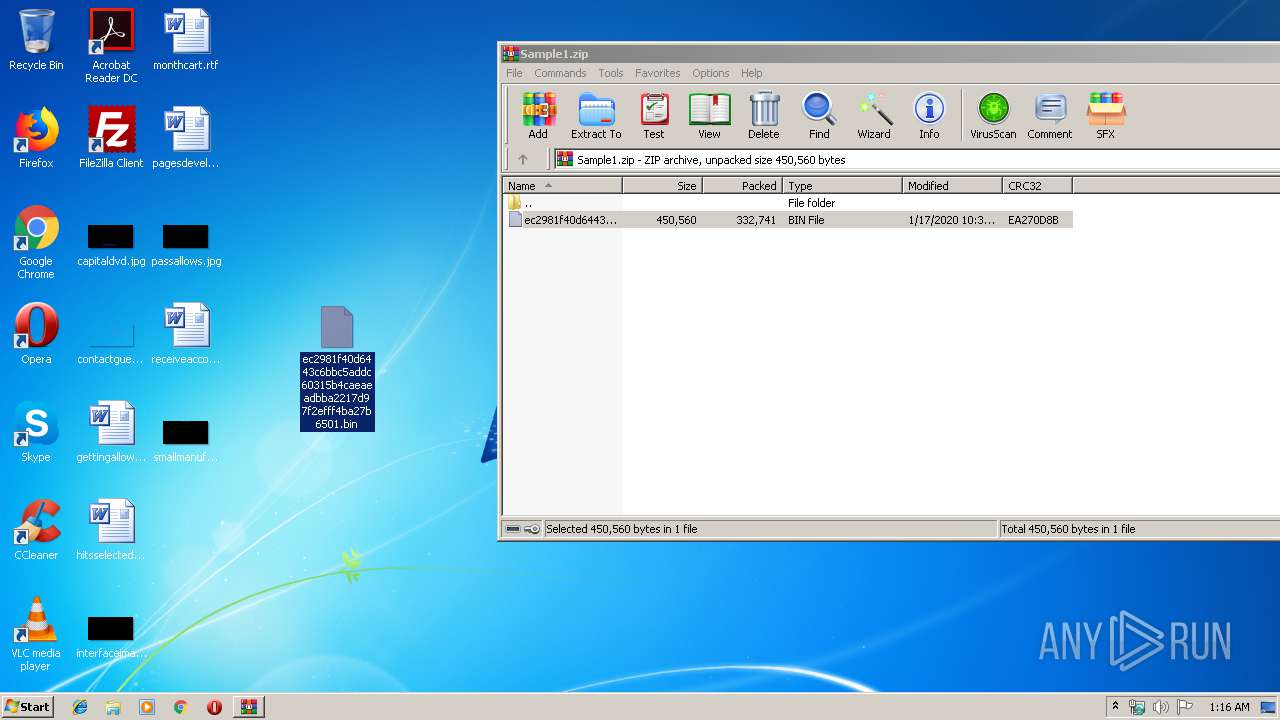
| ZipFileName: | ec2981f40d6443c6bbc5addc60315b4caeaeadbba2217d97f2efff4ba27b6501.bin |
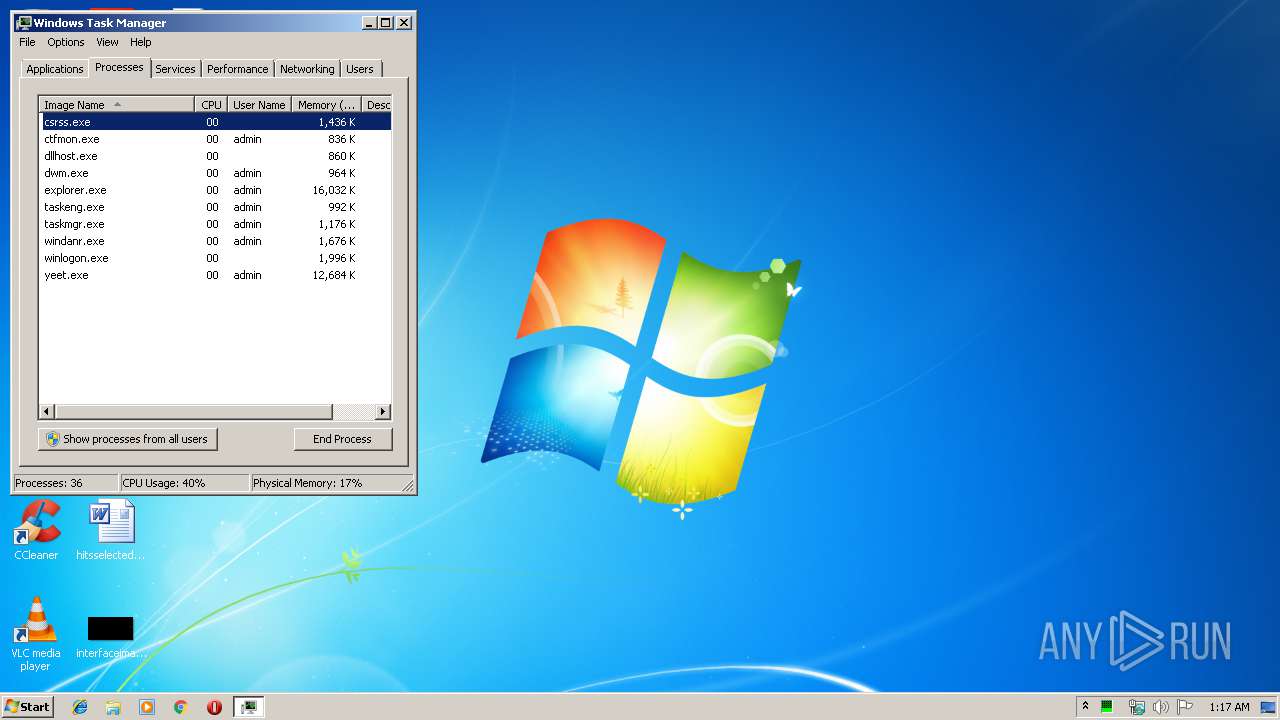
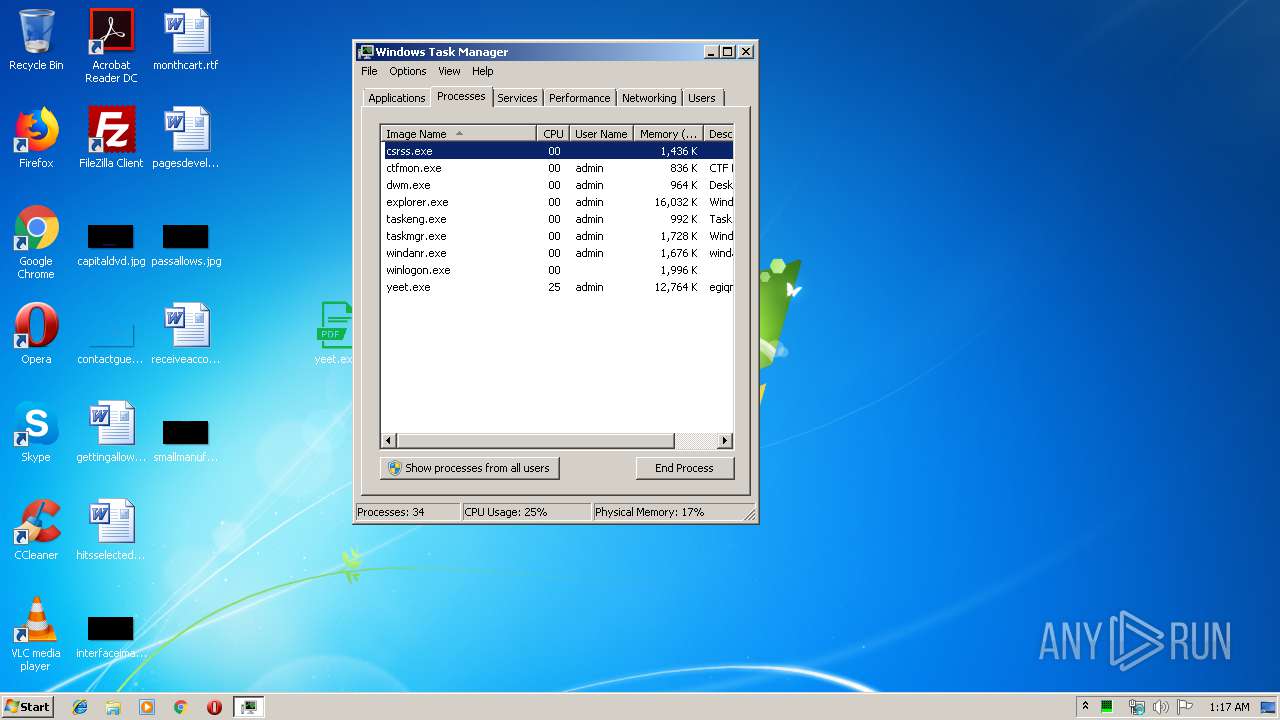
Total processes
50
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1648 | "C:\Users\admin\Desktop\yeet.exe" | C:\Users\admin\Desktop\yeet.exe | explorer.exe | ||||||||||||
User: admin Company: enxzoli Integrity Level: HIGH Description: egiqmo Exit code: 0 Version: 2.6.81.71 Modules
| |||||||||||||||
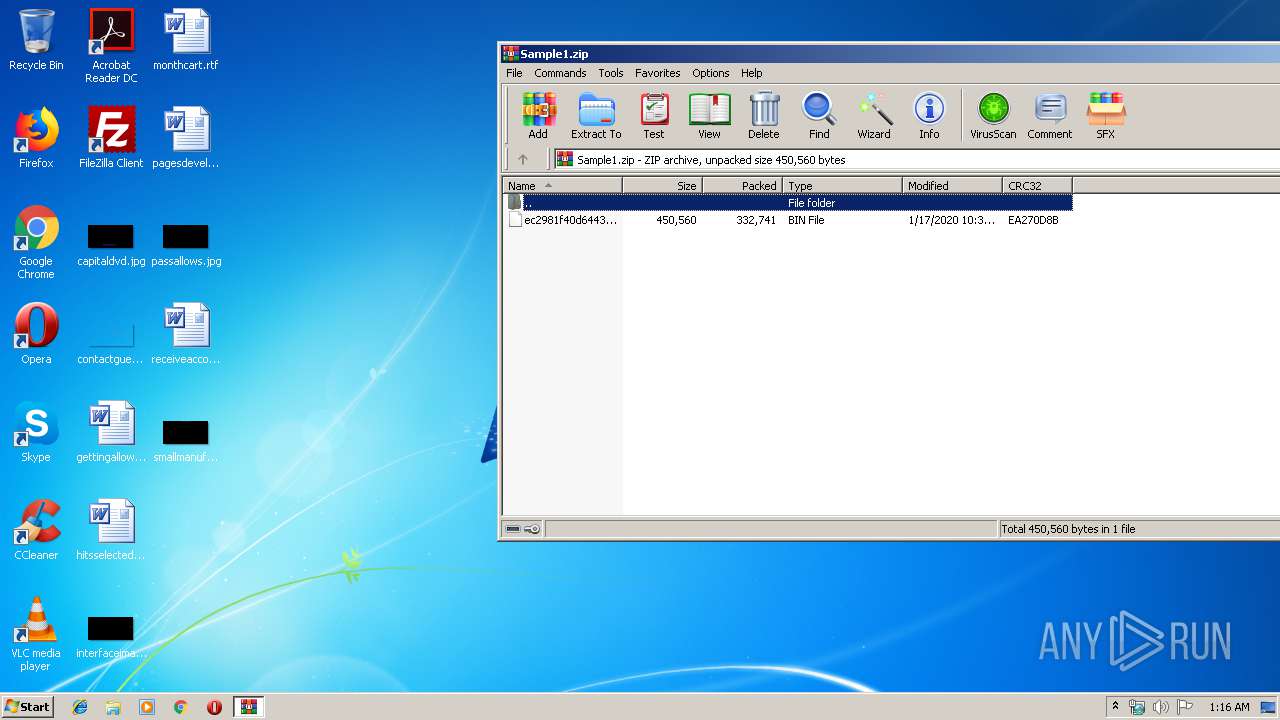
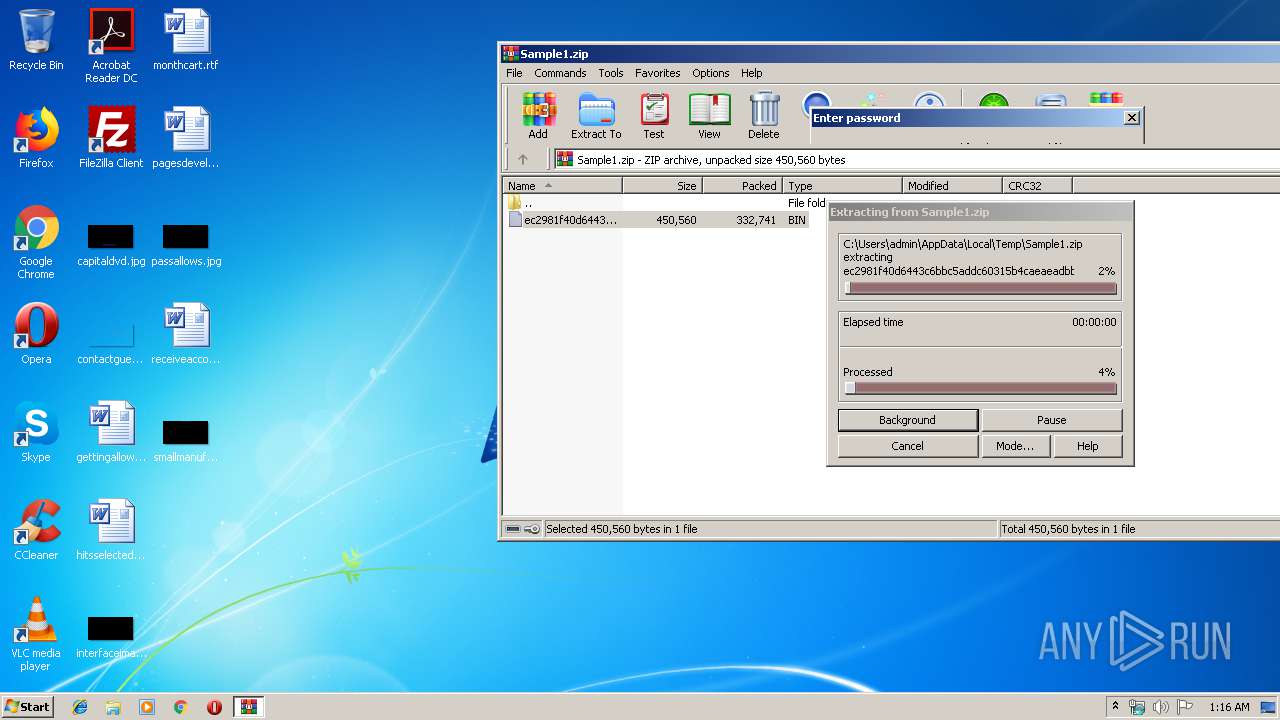
| 1752 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Sample1.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2484 | "C:\ProgramData\Explorers.exe" | C:\ProgramData\Explorers.exe | WHost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4924 | "C:\Users\admin\AppData\Roaming\Explorers\Explorers.exe" | C:\Users\admin\AppData\Roaming\Explorers\Explorers.exe | yeet.exe | ||||||||||||
User: admin Company: enxzoli Integrity Level: HIGH Description: egiqmo Exit code: 0 Version: 2.6.81.71 Modules
| |||||||||||||||
| 7984 | "C:\Users\admin\AppData\Roaming\Explorers\Explorers.exe" | C:\Users\admin\AppData\Roaming\Explorers\Explorers.exe | Explorers.exe | ||||||||||||
User: admin Company: enxzoli Integrity Level: HIGH Description: egiqmo Exit code: 0 Version: 2.6.81.71 Modules
| |||||||||||||||
| 9312 | "C:\Users\admin\AppData\Roaming\Explorers\WHost.exe" | C:\Users\admin\AppData\Roaming\Explorers\WHost.exe | Explorers.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 10204 | "schtasks.exe" /create /f /tn "TCP Monitor" /xml "C:\Users\admin\AppData\Local\Temp\tmp5ECF.tmp" | C:\Windows\system32\schtasks.exe | — | Explorers.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 11200 | "schtasks.exe" /create /f /tn "TCP Monitor Task" /xml "C:\Users\admin\AppData\Local\Temp\tmp5F3D.tmp" | C:\Windows\system32\schtasks.exe | — | Explorers.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 11744 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 355
Read events
1 263
Write events
92
Delete events
0
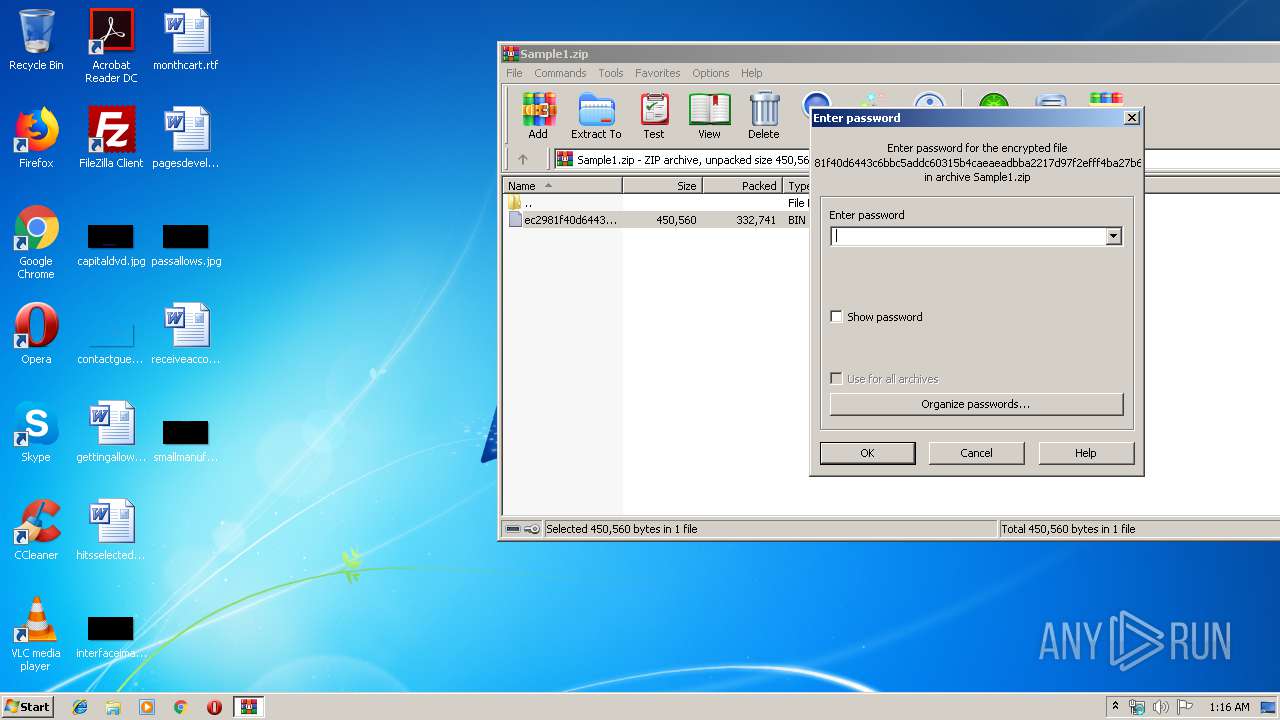
Modification events
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Sample1.zip | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1648) yeet.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
4
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1752.20604\ec2981f40d6443c6bbc5addc60315b4caeaeadbba2217d97f2efff4ba27b6501.bin | — | |
MD5:— | SHA256:— | |||
| 7984 | Explorers.exe | C:\Users\admin\AppData\Local\Temp\tmp5ECF.tmp | — | |
MD5:— | SHA256:— | |||
| 1648 | yeet.exe | C:\Users\admin\AppData\Roaming\Explorers\Explorers.exe | executable | |
MD5:— | SHA256:— | |||
| 7984 | Explorers.exe | C:\Users\admin\AppData\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\run.dat | binary | |
MD5:— | SHA256:— | |||
| 4924 | Explorers.exe | C:\Users\admin\AppData\Roaming\Explorers\WHost.exe | executable | |
MD5:— | SHA256:— | |||
| 7984 | Explorers.exe | C:\Program Files\TCP Monitor\tcpmon.exe | executable | |
MD5:— | SHA256:— | |||
| 9312 | WHost.exe | C:\ProgramData\Explorers.exe | executable | |
MD5:— | SHA256:— | |||
| 4924 | Explorers.exe | C:\Users\admin\AppData\Roaming\Explorers\egiqmo.url | text | |
MD5:— | SHA256:— | |||
| 7984 | Explorers.exe | C:\Users\admin\AppData\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\task.dat | text | |
MD5:— | SHA256:— | |||
| 7984 | Explorers.exe | C:\Users\admin\AppData\Local\Temp\tmp5F3D.tmp | xml | |
MD5:E4118E3EC98934AA1D4235C87B44AA31 | SHA256:EFC475D73603DF6A26978D7BCAC27004830137E97FDD1656140B4A08C07470D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2484 | Explorers.exe | GET | — | 146.185.195.20:80 | http://146.185.195.20/upnp.exe | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7984 | Explorers.exe | 105.112.117.70:55190 | rubenbakerr.ddns.net | — | NG | unknown |
2484 | Explorers.exe | 149.202.110.30:18982 | meki.duckdns.org | OVH SAS | FR | malicious |
2484 | Explorers.exe | 146.185.195.20:80 | — | Petersburg Internet Network ltd. | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
rubenbakerr.ddns.net |
| malicious |
meki.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2484 | Explorers.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
2484 | Explorers.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |