| File name: | d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe |
| Full analysis: | https://app.any.run/tasks/3451ceb0-ee3c-4697-a345-44d7497c30d5 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 25, 2026, 19:14:43 |
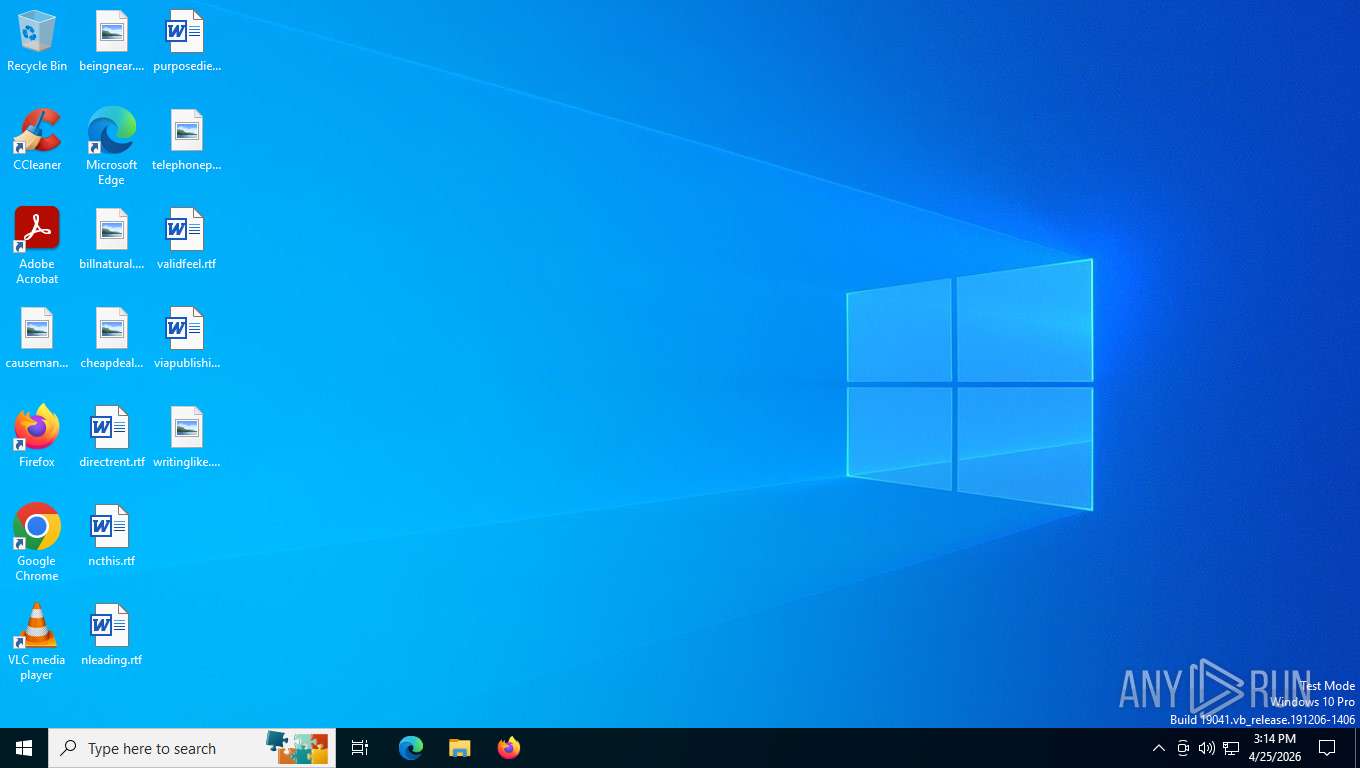
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 9BDB1229AC056E84CDB54AC831BF9006 |
| SHA1: | 0C4F12CE3073C1FD6085F1897DFF28C8A5A259BE |
| SHA256: | D7A73C6F89C3B4D0AE77DE1034A838373E295F250FB455BB87115418BEB41176 |
| SSDEEP: | 1536:ADWwvwAPVL344bz7HIgOUVbOOBYw9CPE+bSXSjRweQjm01YvvFZee8U:ADWwvwAPVL3RHIEUE+bSyVvvFUvU |
MALICIOUS
Changes the autorun value in the registry
- d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe (PID: 7224)
ASYNCRAT has been detected (YARA)
- AsyncRat.exe (PID: 5752)
SUSPICIOUS
Executable content was dropped or overwritten
- d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe (PID: 7224)
Executing commands from a ".bat" file
- d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe (PID: 7224)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7848)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7848)
The executable file from the user directory is run by the CMD process
- AsyncRat.exe (PID: 5224)
INFO
Reads the computer name
- d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe (PID: 7224)
- AsyncRat.exe (PID: 5752)
- AsyncRat.exe (PID: 5224)
Creates files or folders in the user directory
- d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe (PID: 7224)
Checks supported languages
- d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe (PID: 7224)
- AsyncRat.exe (PID: 5752)
- AsyncRat.exe (PID: 5224)
Reads the machine GUID from the registry
- d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe (PID: 7224)
- AsyncRat.exe (PID: 5752)
- AsyncRat.exe (PID: 5224)
Launching a file from a Registry key
- d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe (PID: 7224)
Create files in a temporary directory
- d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe (PID: 7224)
Manual execution by a user
- AsyncRat.exe (PID: 5752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(5752) AsyncRat.exe
C2 (1)rophim10.com.co
Ports (3)443
8848
8080
Version0.5.8
BotnetDefault
Options
AutoRuntrue
Mutexd4GOaWukwrCB
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE5DCCAsygAwIBAgIQAOc250/jBXH7PusRfV4KKzANBgkqhkiG9w0BAQ0FADATMREwDwYDVQQDDAhBc3luY1JBVDAgFw0yNTEyMTQxNTM0MjFaGA85OTk5MTIzMTIzNTk1OVowEzERMA8GA1UEAwwIQXN5bmNSQVQwggIiMA0GCSqGSIb3DQEBAQUAA4ICDwAwggIKAoICAQC3hbrOJGE/Ncxr2hD4zwR5WwrlT40PQHZSYRdpnqR2/7/cw8e4m6IS/kPj2TSnF3yYhOkR08loqxZDE8g9vaF8pLg+pyFw...
Server_Signaturedl4ZlMuuZZlyB9vmq5ZvzMTRlXJdxagj8PDiiLb9s/K4/Znar04M8u3pqO8UvMoigRbGkW+E6ikeZhkR8KmZyUjyjeIM/T5yArzbv2VfvUclMnt7nlGokXPYG42A8ZIbEMZTPSl0kAUMDRxqW1SadBq4vl1AbKhXO/yZvg63dqFiUemHZAIEuhOx6WdcbeTNzzEfZrAyg0UnAlXdzwRW1+JAQqPbxSo1j8E9P5tf07zghSyoPXz/yHwufiCcFwW5iXjdaJNwq0026VXqt7C6B9o4q+iCFyHTvtizD8XhFQDa...
Keys
AES33110e8278f0c93092a5361d10845b3df363802505fddfc24bf0f73bae9c93ed
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:16 21:40:53+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 43008 |
| InitializedDataSize: | 13824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc69e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 131.0.6778.123 |
| ProductVersionNumber: | 131.0.6778.123 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Google LLC |
| FileDescription: | Fast, secure web browser from Google |
| FileVersion: | 131.0.6778.123 |
| InternalName: | AsyncRat.exe |
| LegalCopyright: | Copyright © 2026 Google LLC. All rights reserved |
| LegalTrademarks: | Google™ |
| OriginalFileName: | AsyncRat.exe |
| ProductName: | Google Chrome |
| ProductVersion: | 131.0.6778.123 |
| AssemblyVersion: | 131.0.6778.123 |
Total processes
138
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2952 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5224 | "C:\Users\admin\AppData\Roaming\AsyncRat.exe" | C:\Users\admin\AppData\Roaming\AsyncRat.exe | — | cmd.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Fast, secure web browser from Google Exit code: 0 Version: 131.0.6778.123 Modules
| |||||||||||||||
| 5752 | "C:\Users\admin\AppData\Roaming\AsyncRat.exe" | C:\Users\admin\AppData\Roaming\AsyncRat.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Fast, secure web browser from Google Version: 131.0.6778.123 Modules
AsyncRat(PID) Process(5752) AsyncRat.exe C2 (1)rophim10.com.co Ports (3)443 8848 8080 Version0.5.8 BotnetDefault Options AutoRuntrue Mutexd4GOaWukwrCB InstallFolder%AppData% BSoDfalse AntiVMfalse Certificates Cert1MIIE5DCCAsygAwIBAgIQAOc250/jBXH7PusRfV4KKzANBgkqhkiG9w0BAQ0FADATMREwDwYDVQQDDAhBc3luY1JBVDAgFw0yNTEyMTQxNTM0MjFaGA85OTk5MTIzMTIzNTk1OVowEzERMA8GA1UEAwwIQXN5bmNSQVQwggIiMA0GCSqGSIb3DQEBAQUAA4ICDwAwggIKAoICAQC3hbrOJGE/Ncxr2hD4zwR5WwrlT40PQHZSYRdpnqR2/7/cw8e4m6IS/kPj2TSnF3yYhOkR08loqxZDE8g9vaF8pLg+pyFw... Server_Signaturedl4ZlMuuZZlyB9vmq5ZvzMTRlXJdxagj8PDiiLb9s/K4/Znar04M8u3pqO8UvMoigRbGkW+E6ikeZhkR8KmZyUjyjeIM/T5yArzbv2VfvUclMnt7nlGokXPYG42A8ZIbEMZTPSl0kAUMDRxqW1SadBq4vl1AbKhXO/yZvg63dqFiUemHZAIEuhOx6WdcbeTNzzEfZrAyg0UnAlXdzwRW1+JAQqPbxSo1j8E9P5tf07zghSyoPXz/yHwufiCcFwW5iXjdaJNwq0026VXqt7C6B9o4q+iCFyHTvtizD8XhFQDa... Keys AES33110e8278f0c93092a5361d10845b3df363802505fddfc24bf0f73bae9c93ed Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
| 6060 | timeout 3 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7224 | "C:\Users\admin\Desktop\d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe" | C:\Users\admin\Desktop\d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Fast, secure web browser from Google Exit code: 0 Version: 131.0.6778.123 Modules
| |||||||||||||||
| 7728 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7848 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmp2036.tmp.bat"" | C:\Windows\SysWOW64\cmd.exe | — | d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 180
Read events
4 178
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2952) slui.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\sppcomapi.dll,-3200 |
Value: Software Licensing | |||
| (PID) Process: | (7224) d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | AsyncRat |
Value: "C:\Users\admin\AppData\Roaming\AsyncRat.exe" | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7224 | d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe | C:\Users\admin\AppData\Local\Temp\tmp2036.tmp.bat | text | |
MD5:7B6FD0FE8B2053F695ABC3BAE23F1CF9 | SHA256:183040566EEDAE29114FDAE46173BACDAE4F32523876F2718EAF295DDE9E066F | |||
| 7224 | d7a73c6f89c3b4d0ae77de1034a838373e295f250fb455bb87115418beb41176.exe | C:\Users\admin\AppData\Roaming\AsyncRat.exe | executable | |
MD5:9BDB1229AC056E84CDB54AC831BF9006 | SHA256:D7A73C6F89C3B4D0AE77DE1034A838373E295F250FB455BB87115418BEB41176 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
29
DNS requests
12
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8000 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
8000 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
2952 | slui.exe | POST | 500 | 128.24.231.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
2952 | slui.exe | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | US | binary | 400 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | US | binary | 813 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | US | binary | 400 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | US | binary | 813 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
8000 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8040 | slui.exe | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.141:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8000 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
8000 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
rophim10.com.co |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5752 | AsyncRat.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Common RAT related JA3 hash observed |