| File name: | VolcanoUpdater.exe |
| Full analysis: | https://app.any.run/tasks/6ec0437e-368e-403f-8b97-7ea8808aca5a |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | January 28, 2026, 12:29:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 14 sections |
| MD5: | 690B0BE88351C438FF24DBC67E50AE96 |
| SHA1: | 562C1AE7E92574FE1E73B1A9734ABF9F2CEF866B |
| SHA256: | D7907E93B9EE8ED2AC0B4C4F5C20A961A1A0BEE0000FBBD3A57E87ECBC846899 |
| SSDEEP: | 98304:Y5dEtqUtUK7HfktQ62o7fa3/q4lODvNn2deEUdnf+XCNlmKSyF/JylQZcvBL4j+5:RjRa4O92lbK/iF |
MALICIOUS
GENERIC has been found (auto)
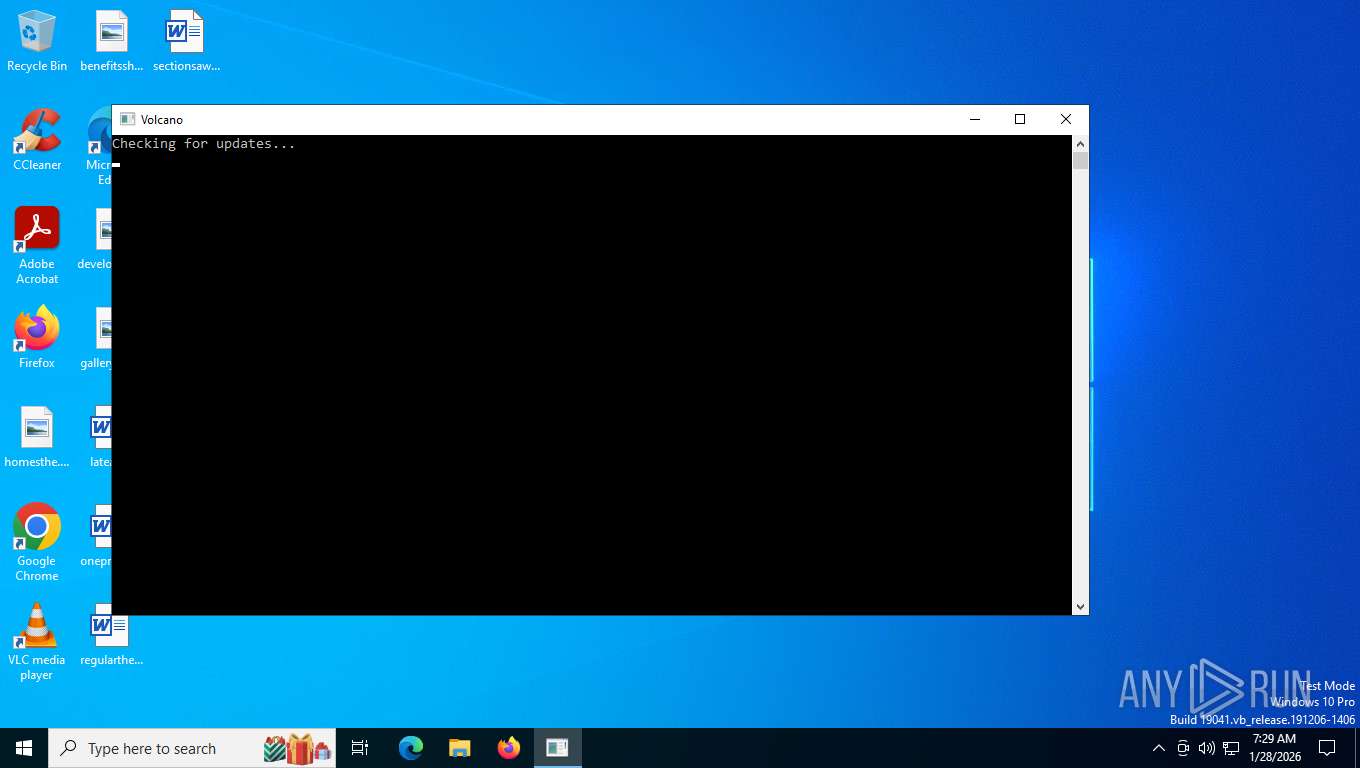
- VolcanoUpdater.exe (PID: 5728)
VALLEYRAT has been detected (YARA)
- VolcanoUI.exe (PID: 7228)
XORed URL has been found (YARA)
- VolcanoUI.exe (PID: 7228)
SUSPICIOUS
Reads the BIOS version
- VolcanoUpdater.exe (PID: 5728)
- VolcanoUI.exe (PID: 7228)
Reads the date of Windows installation
- VolcanoUpdater.exe (PID: 5728)
Executable content was dropped or overwritten
- VolcanoUpdater.exe (PID: 5728)
- VolcanoUI.exe (PID: 7228)
Process drops legitimate windows executable
- VolcanoUI.exe (PID: 7228)
INFO
Reads the computer name
- VolcanoUpdater.exe (PID: 5728)
- VolcanoUI.exe (PID: 7228)
Create files in a temporary directory
- VolcanoUpdater.exe (PID: 5728)
- VolcanoUI.exe (PID: 7228)
Checks supported languages
- VolcanoUpdater.exe (PID: 5728)
- VolcanoUI.exe (PID: 7228)
Reads security settings of Internet Explorer
- VolcanoUpdater.exe (PID: 5728)
Process checks computer location settings
- VolcanoUpdater.exe (PID: 5728)
Manual execution by a user
- firefox.exe (PID: 7932)
Process checks whether UAC notifications are on
- VolcanoUI.exe (PID: 7228)
The sample compiled with english language support
- VolcanoUI.exe (PID: 7228)
- firefox.exe (PID: 7704)
ROBLOX mutex has been found
- VolcanoUI.exe (PID: 7228)
Themida protector has been detected
- VolcanoUI.exe (PID: 7228)
Application launched itself
- firefox.exe (PID: 7704)
- firefox.exe (PID: 7932)
Drops script file
- firefox.exe (PID: 7704)
Executable content was dropped or overwritten
- firefox.exe (PID: 7704)
Checks proxy server information
- slui.exe (PID: 8512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(7228) VolcanoUI.exe
Decrypted-URLs (2)https://file.volcano.wtf/versio@-3%f7f81a39-5f63-5b42-9efd-1f13b5431005#39;%7%
https://key.vol
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:07:09 16:37:47+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.38 |
| CodeSize: | 801280 |
| InitializedDataSize: | 262656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7e3058 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
172
Monitored processes
18
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1188 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 2240 -prefsLen 36521 -prefMapHandle 2244 -prefMapSize 272981 -ipcHandle 2252 -initialChannelId {b9e4c681-b98d-41d9-bee0-7e0319f05a4d} -parentPid 7704 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7704" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 2 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1612 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 3368 -prefsLen 37207 -prefMapHandle 3372 -prefMapSize 272981 -ipcHandle 1900 -initialChannelId {8d6ebe64-f703-463d-bbe2-175b8c4d5ded} -parentPid 7704 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7704" -appDir "C:\Program Files\Mozilla Firefox\browser" - 4 rdd | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5000 -prefsLen 39330 -prefMapHandle 5004 -prefMapSize 272981 -jsInitHandle 5008 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5016 -initialChannelId {50e6a3a0-0485-4565-9197-88700429d352} -parentPid 7704 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7704" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 8 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 4064 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -sandboxingKind 0 -prefsHandle 4892 -prefsLen 45267 -prefMapHandle 4896 -prefMapSize 272981 -ipcHandle 4680 -initialChannelId {28f08e3e-c77b-46b6-8719-c7b8717dddbd} -parentPid 7704 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7704" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 6 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 4756 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5220 -prefsLen 39330 -prefMapHandle 5224 -prefMapSize 272981 -jsInitHandle 5228 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5232 -initialChannelId {d700d55d-6bf7-472b-8c99-48084b5d7530} -parentPid 7704 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7704" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 9 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 5108 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4080 -prefsLen 45165 -prefMapHandle 4100 -prefMapSize 272981 -jsInitHandle 4104 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4112 -initialChannelId {e64d0369-0787-45dd-a772-b515a3e99067} -parentPid 7704 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7704" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 5 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 5728 | "C:\Users\admin\AppData\Local\Temp\VolcanoUpdater.exe" | C:\Users\admin\AppData\Local\Temp\VolcanoUpdater.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6284 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 3260 -prefsLen 37207 -prefMapHandle 3264 -prefMapSize 272981 -jsInitHandle 3268 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 3276 -initialChannelId {45c735f6-7c9b-4c8f-babc-eb66d979297a} -parentPid 7704 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7704" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 3 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 6316 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5740 -prefsLen 39493 -prefMapHandle 5744 -prefMapSize 272981 -jsInitHandle 5748 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 2788 -initialChannelId {29a3cf70-13c6-4948-8dee-a925bcd4111d} -parentPid 7704 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7704" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 6624 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4968 -prefsLen 39330 -prefMapHandle 4972 -prefMapSize 272981 -jsInitHandle 4976 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4984 -initialChannelId {b0a439df-5e6a-4d42-8009-260940a2f767} -parentPid 7704 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7704" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 7 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
Total events
1 189
Read events
1 189
Write events
0
Delete events
0
Modification events
Executable files
7
Suspicious files
234
Text files
71
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:5152D8F49F1AD4219D935611EFE18437 | SHA256:9A6E50715E3C49A43E3D622EDE7E37ECF0767342B3039B8B0AE25BBE4FF6F66E | |||
| 5728 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\VolcanoUI.exe | executable | |
MD5:963C2C7BCCB53EAAE3E858D1C42097F1 | SHA256:1C7B65C31408655C62EE851B36EA76ED891CEA6FFFBF707DD0250246B567B971 | |||
| 5728 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\luau-lifter.exe | executable | |
MD5:F1246A49C8183FCFAC4D7669A6C50881 | SHA256:F5AD37B2293814CE33149CA8D8BF1D673AE0C8F3CB025D7B83954EB0E68E631D | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:3134ED3F12E4F4F8643DB90043B0FD7B | SHA256:26E4F122034D7A03F6DA0E707799B09CBEEBDAF8D7A3133A1F7BD894AC72EEA1 | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:017718D9990B8227B39B9D10E93E5073 | SHA256:73551820A01B8A3DD0961A59903E035DEC1A0B0BCA55405EA140AAB542EC5D70 | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | text | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5728 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\version.txt | text | |
MD5:207829A1286309D0DB8A370E22905FCF | SHA256:5437CC464B14081F7AFDE5AD5BCA184AFEEF981A9BDA0375BF18CE175CA64EDC | |||
| 7704 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
263
TCP/UDP connections
103
DNS requests
150
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5728 | VolcanoUpdater.exe | GET | 200 | 104.21.56.14:443 | https://file.volcano.wtf/Release_v3.2.2.zip | US | compressed | 128 Kb | unknown |
5728 | VolcanoUpdater.exe | GET | 404 | 104.21.56.14:443 | https://file.volcano.wtf/base.txt | US | html | 26.5 Kb | unknown |
5728 | VolcanoUpdater.exe | GET | 200 | 104.21.56.14:443 | https://file.volcano.wtf/version.txt | US | text | 6 b | unknown |
804 | lsass.exe | GET | 200 | 142.250.185.131:80 | http://c.pki.goog/r/r4.crl | US | binary | 530 b | whitelisted |
804 | lsass.exe | GET | 200 | 142.250.185.131:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
8380 | svchost.exe | GET | 200 | 95.101.54.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
4280 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7704 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | unknown |
7704 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | unknown |
7704 | firefox.exe | POST | 200 | 172.217.16.163:80 | http://o.pki.goog/s/wr3/peI | US | binary | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
9032 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8380 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5728 | VolcanoUpdater.exe | 104.21.56.14:443 | file.volcano.wtf | CLOUDFLARENET | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
804 | lsass.exe | 142.250.185.131:80 | c.pki.goog | GOOGLE | US | whitelisted |
4280 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4280 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
7228 | VolcanoUI.exe | 104.21.56.14:443 | file.volcano.wtf | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
file.volcano.wtf |
| unknown |
c.pki.goog |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
mozilla.map.fastly.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7704 | firefox.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7704 | firefox.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7704 | firefox.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7704 | firefox.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7704 | firefox.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7704 | firefox.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7704 | firefox.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
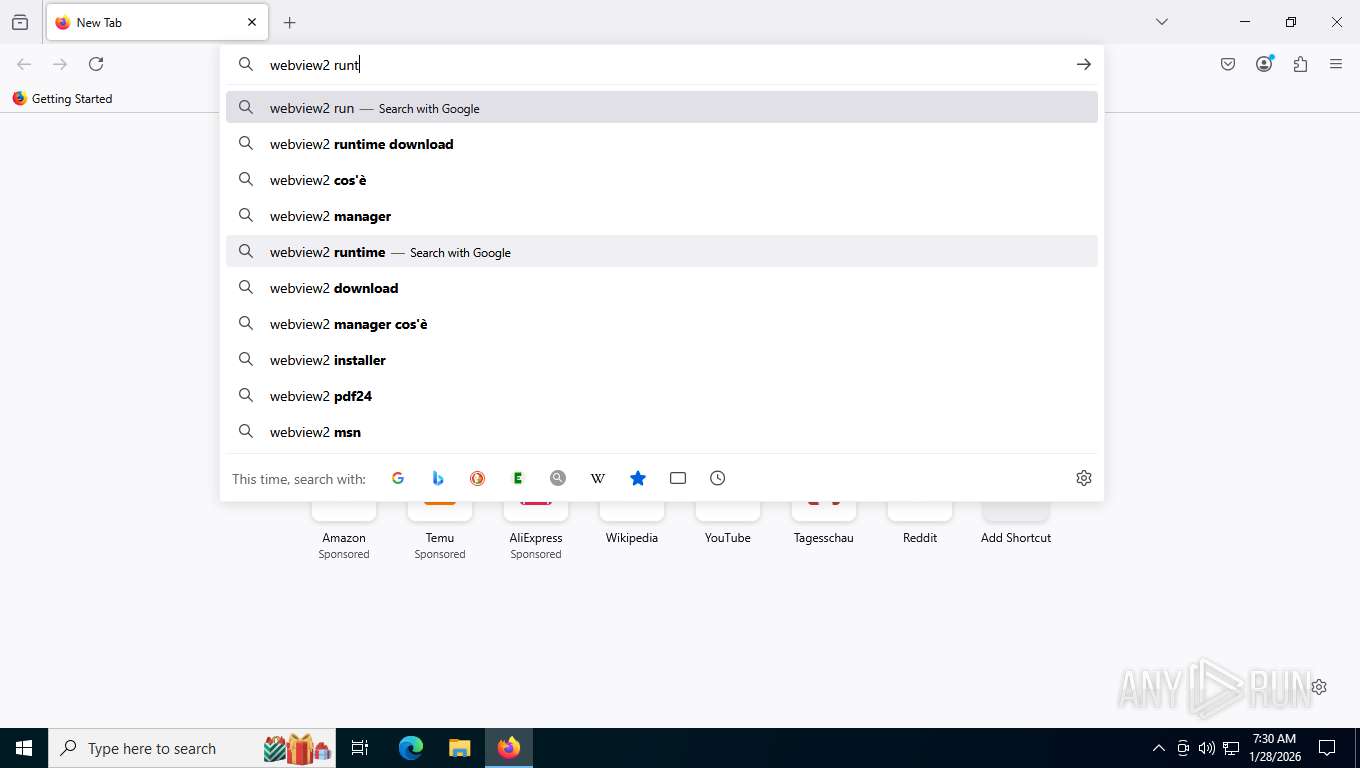
Process | Message |
|---|---|
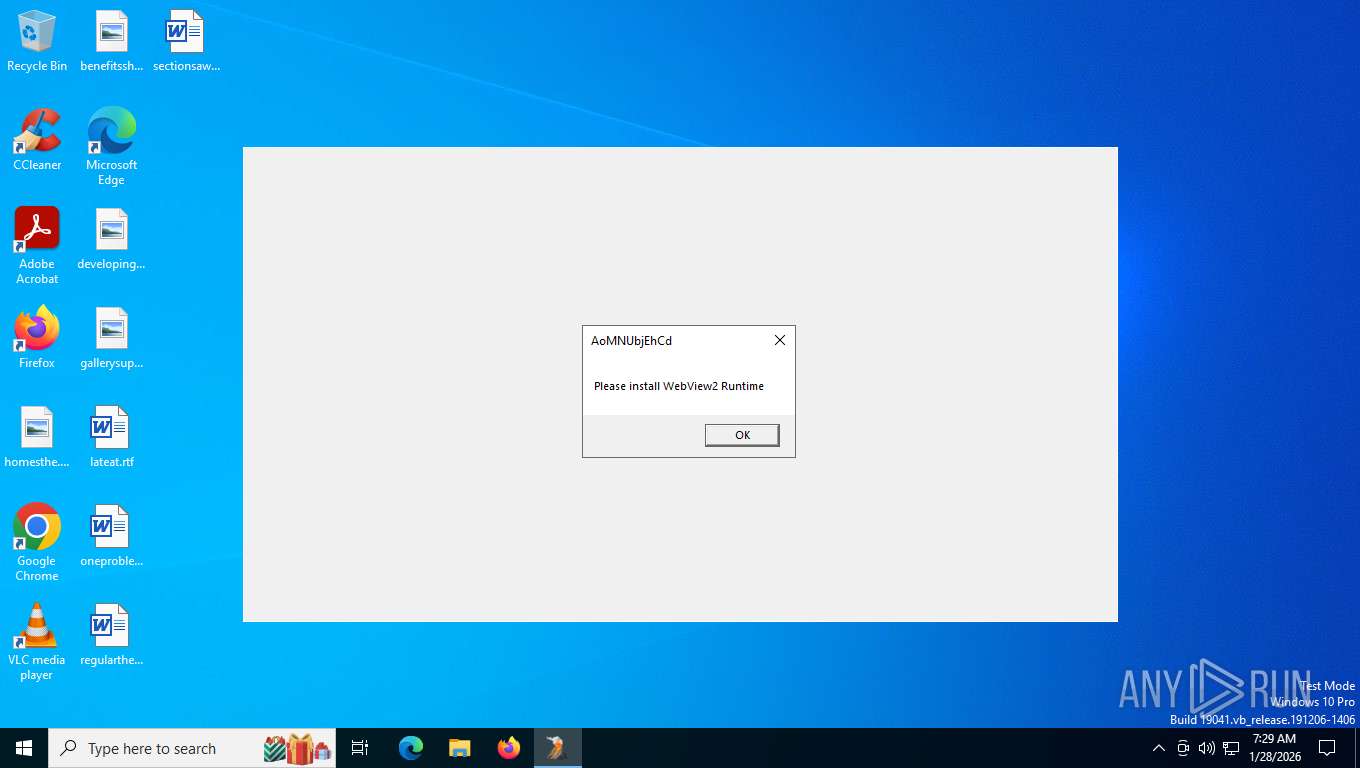
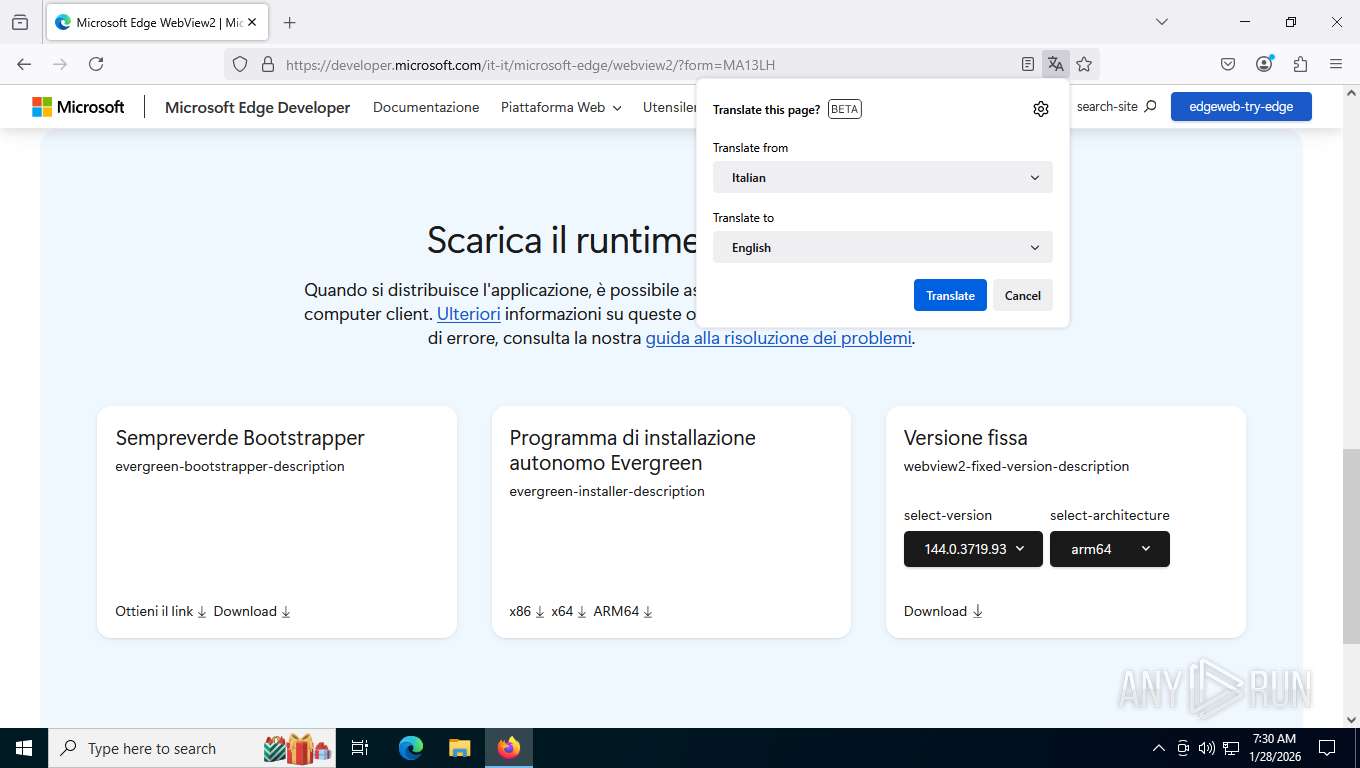
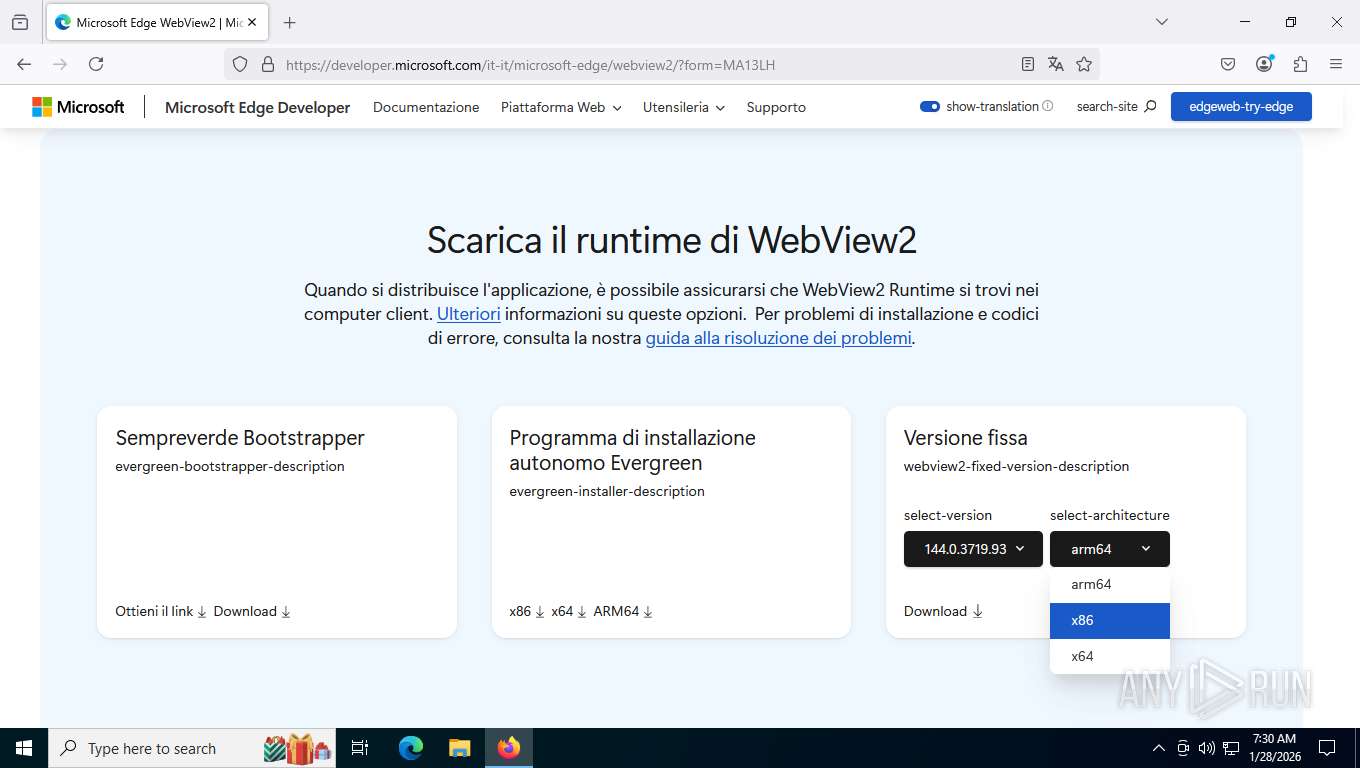
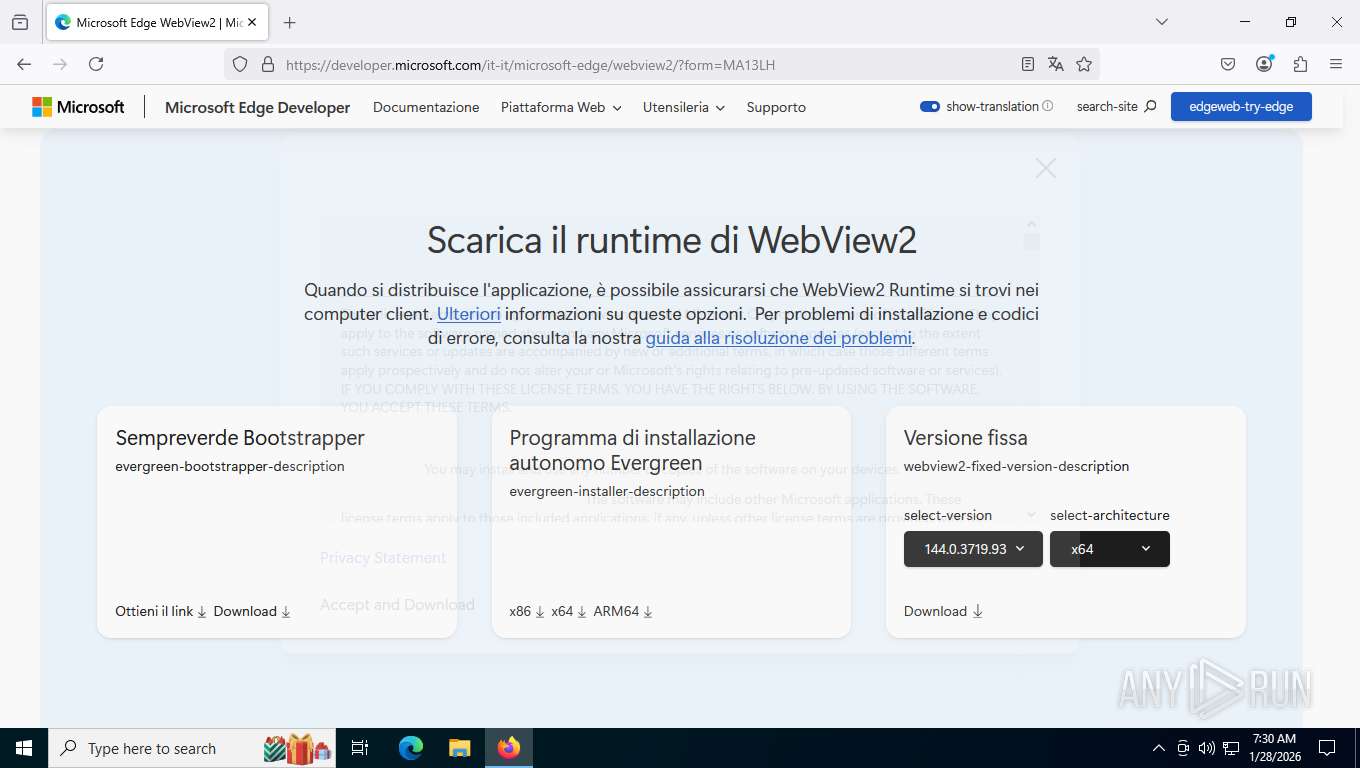
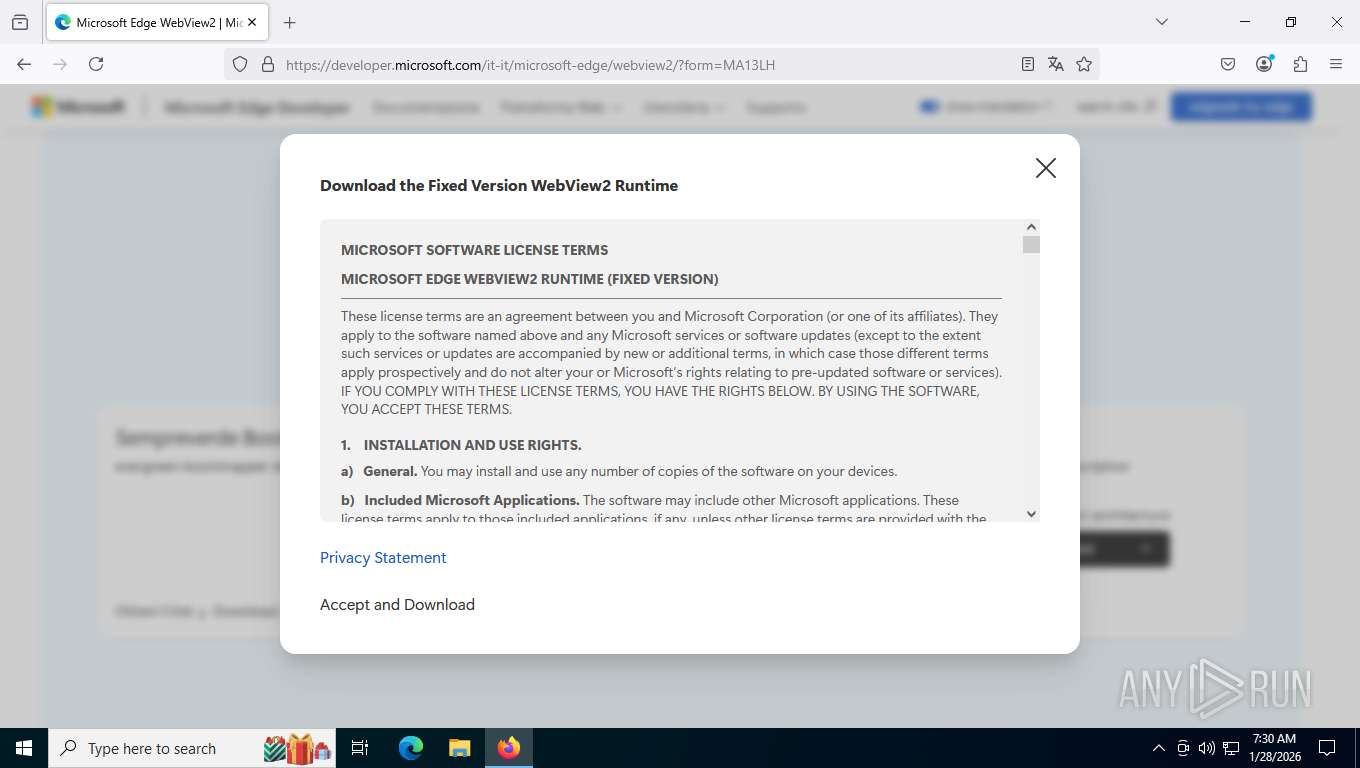
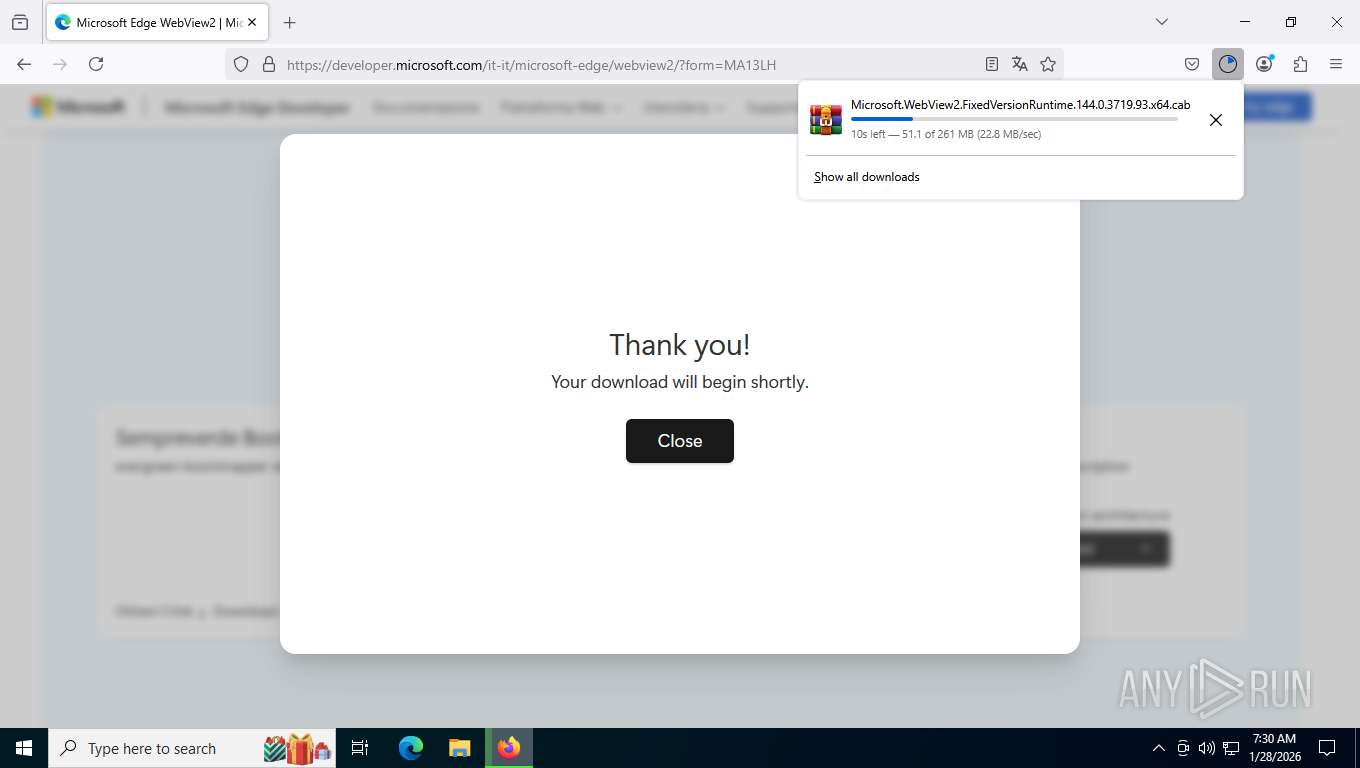
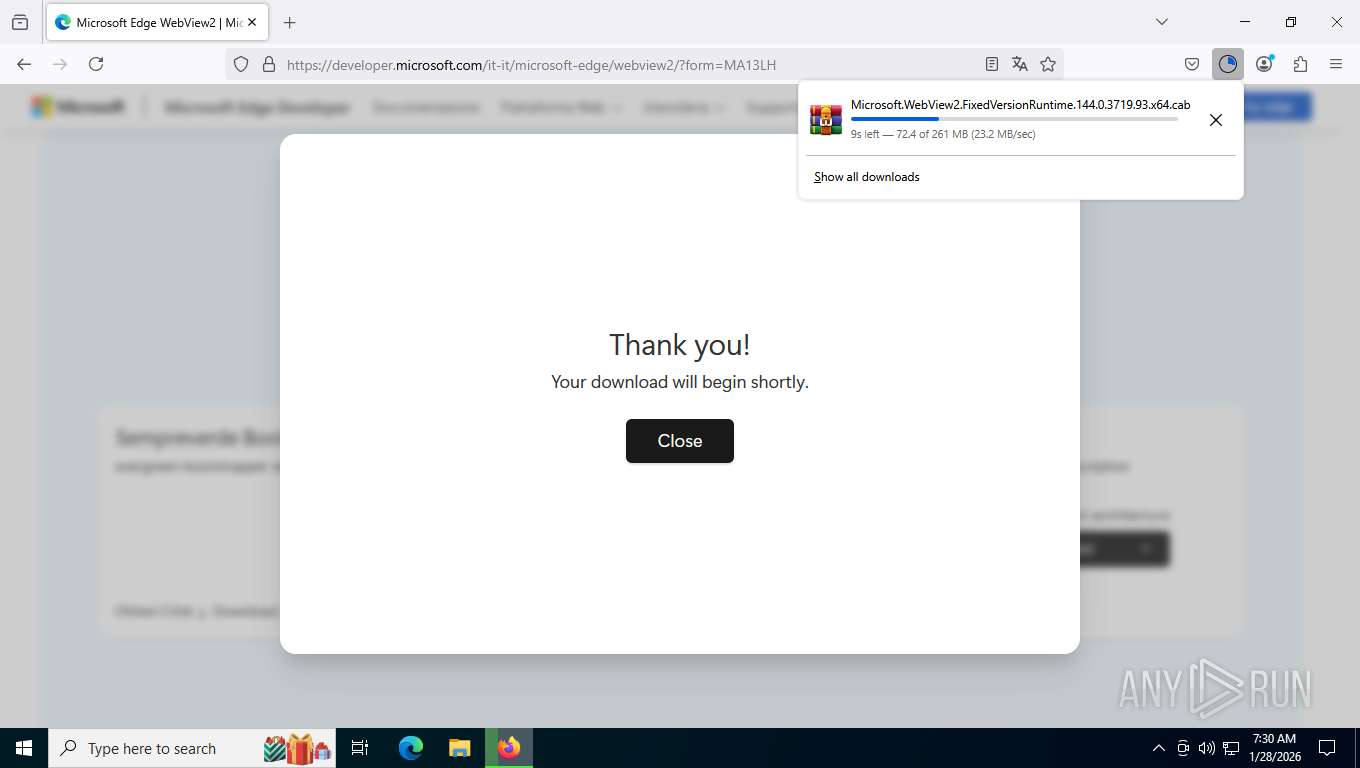
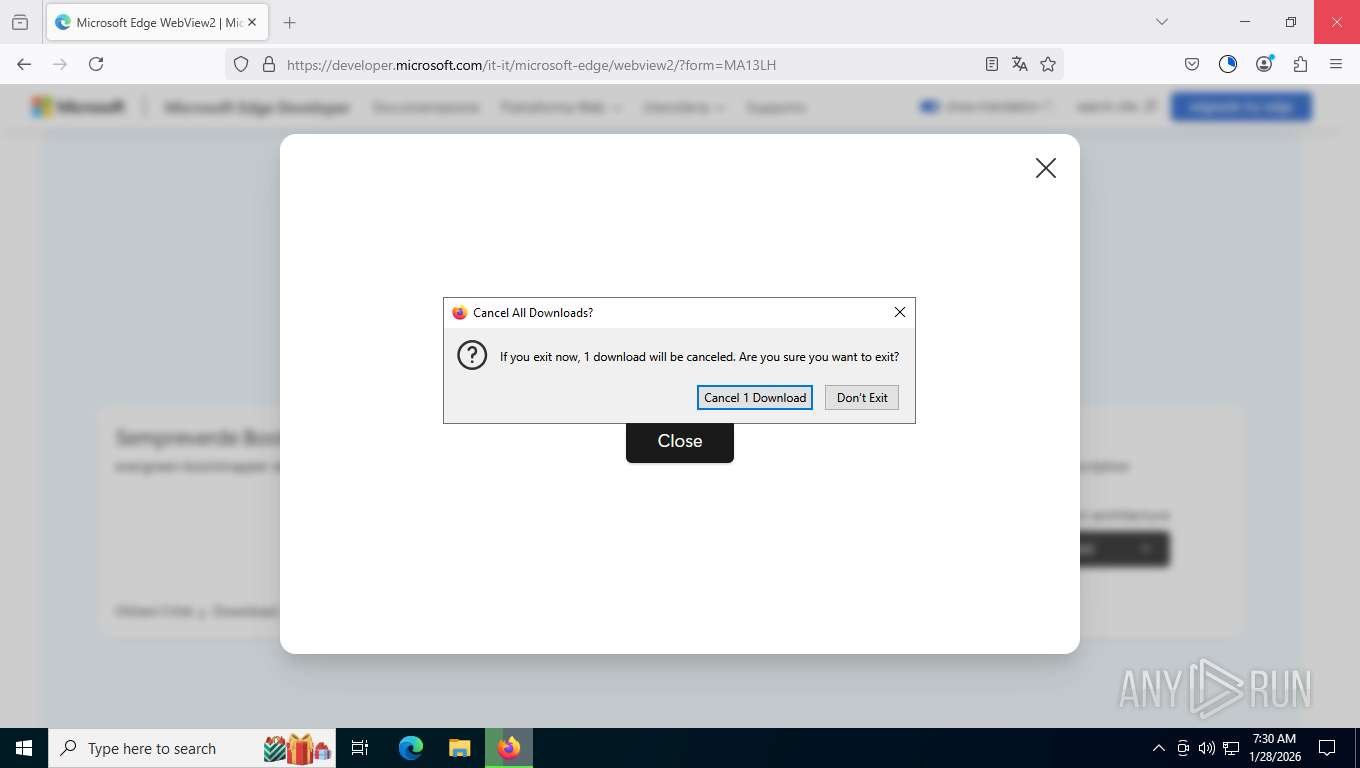
VolcanoUI.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
VolcanoUI.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|