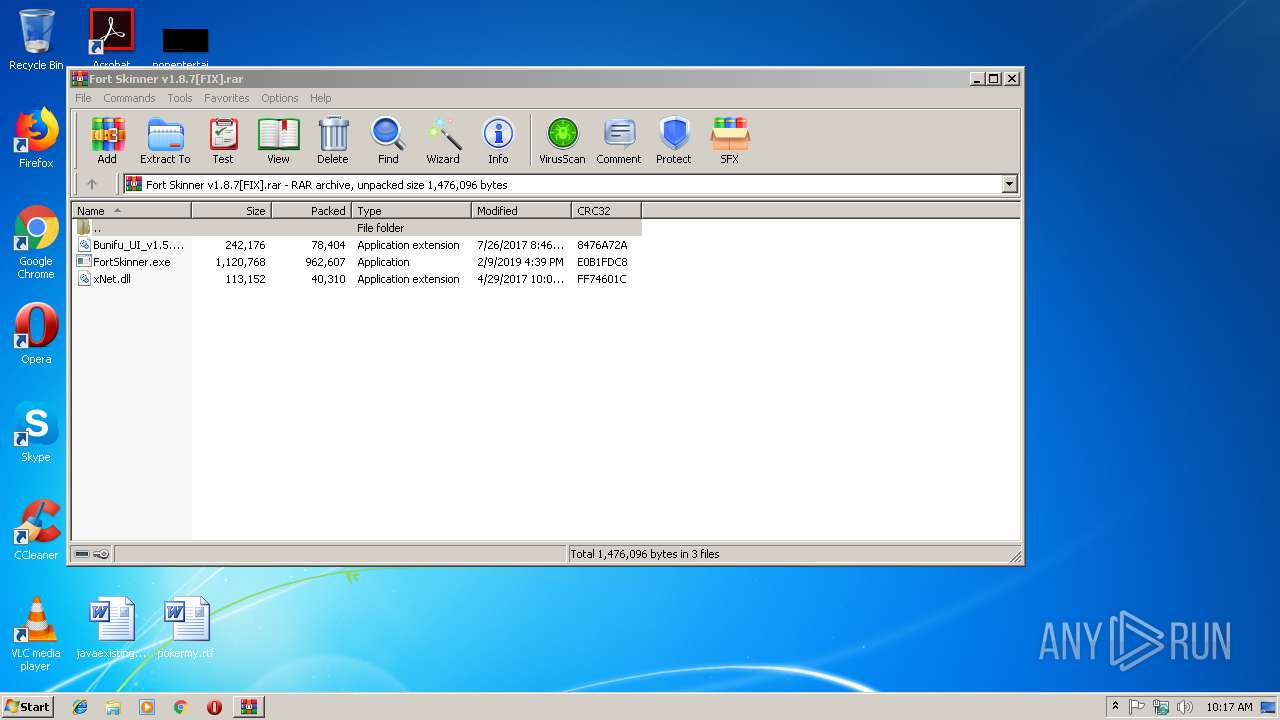
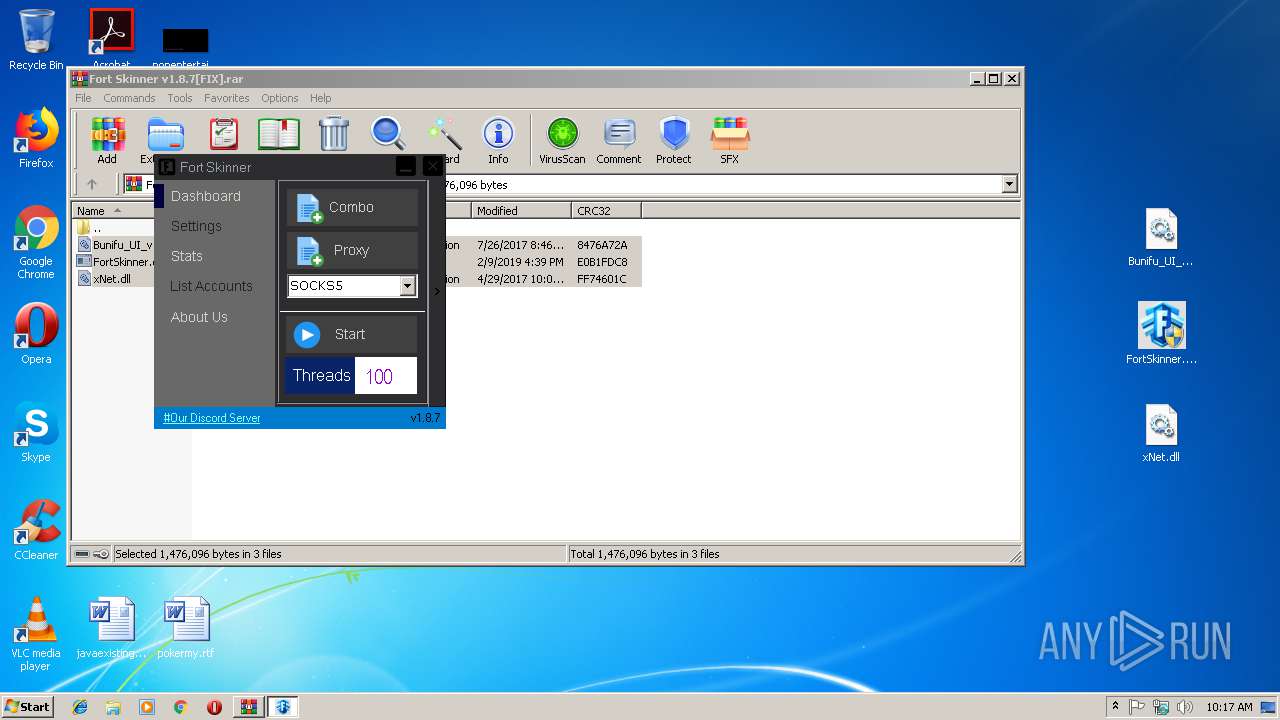
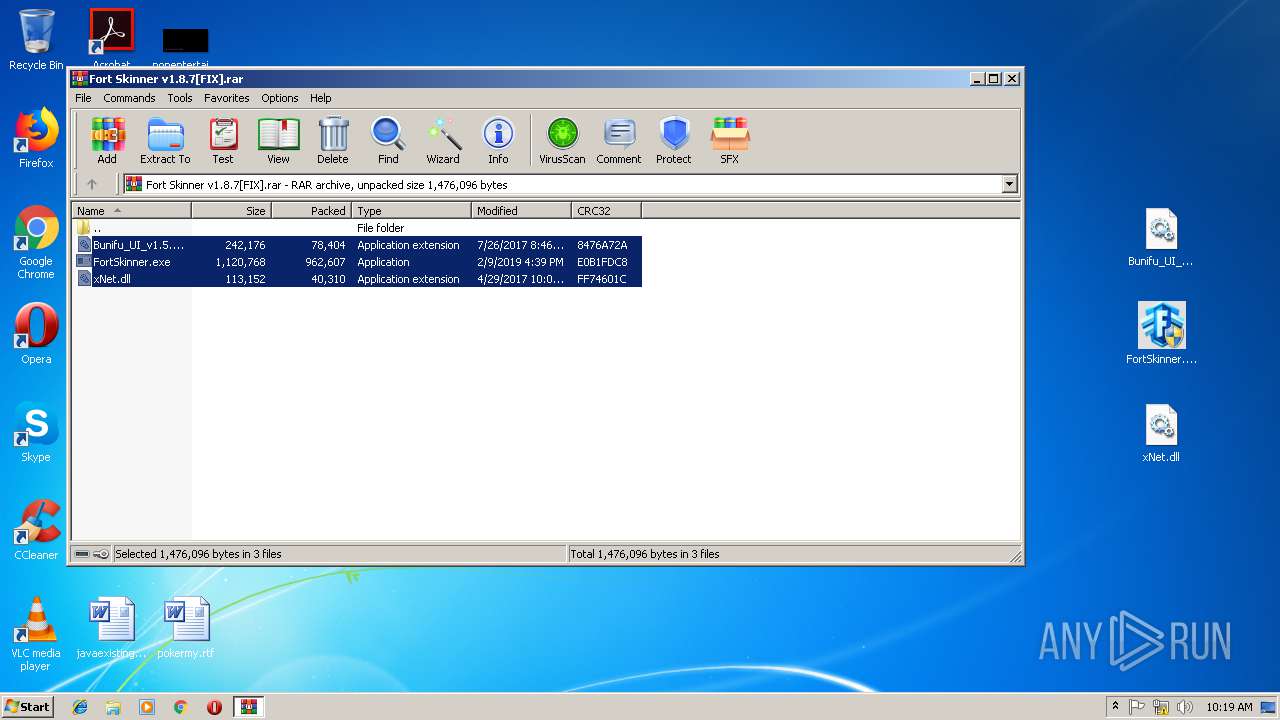
| File name: | Fort Skinner v1.8.7[FIX].rar |
| Full analysis: | https://app.any.run/tasks/65968dc0-e92c-4948-8e1f-e92b0193ab6a |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | February 11, 2019, 10:17:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2E1E57BA708E87CBE7E0B21A3F3DFE7B |
| SHA1: | 44EC5615B2E6ACEF4468C40C0D76D05777134035 |
| SHA256: | D6FC9258A50C602F0232A538EE4AC012AC554DAD9B8343928554C9336CE4E271 |
| SSDEEP: | 24576:+4MUNH9PzxYuKm32XmE15mvUpg8FBTgsm5kWCHHfX/EzLk:HMabx8m32WE15mw/FqkWqPik |
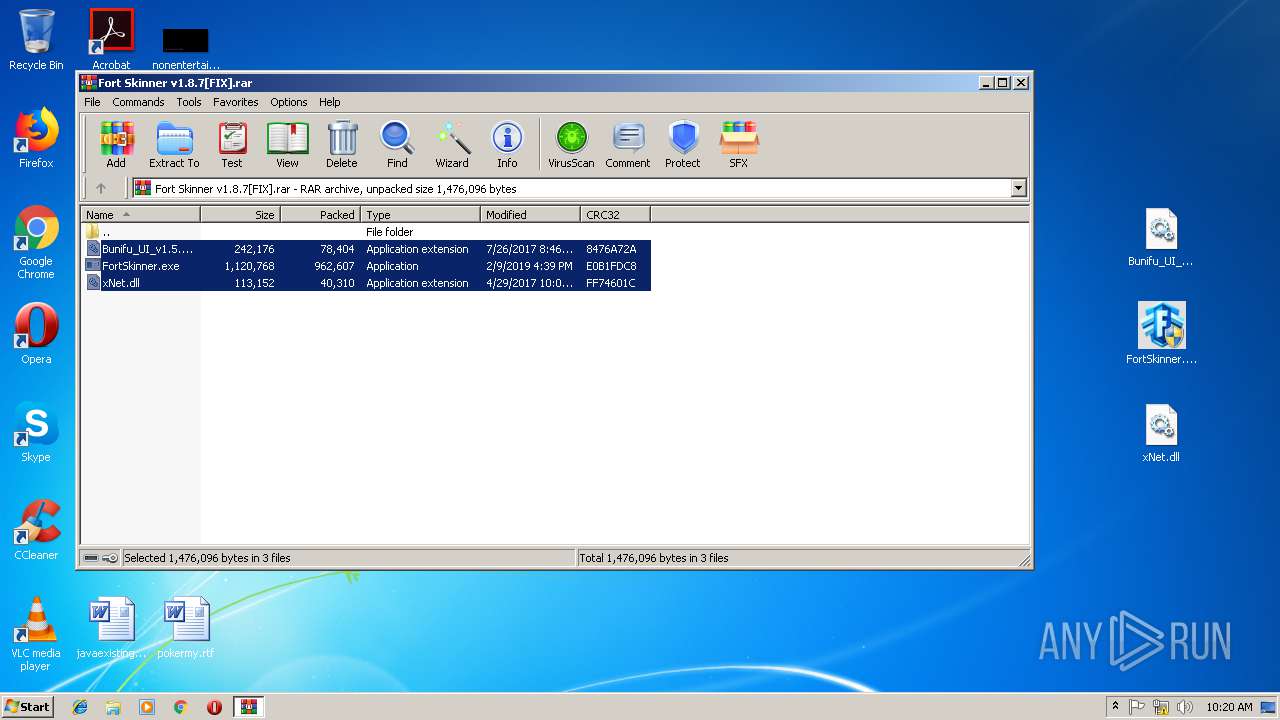
MALICIOUS
Application was dropped or rewritten from another process
- FortSkinner.exe (PID: 3828)
- FortSkinner.exe (PID: 3676)
- FortSkinner.exe (PID: 2996)
- FortSkinner.exe (PID: 3608)
- FortSkinner.exe (PID: 552)
- FortSkinner.exe (PID: 3412)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 364)
- FortSkinner.exe (PID: 3828)
- FortSkinner.exe (PID: 3412)
- FortSkinner.exe (PID: 552)
QUASAR was detected
- Regasm.exe (PID: 4000)
SUSPICIOUS
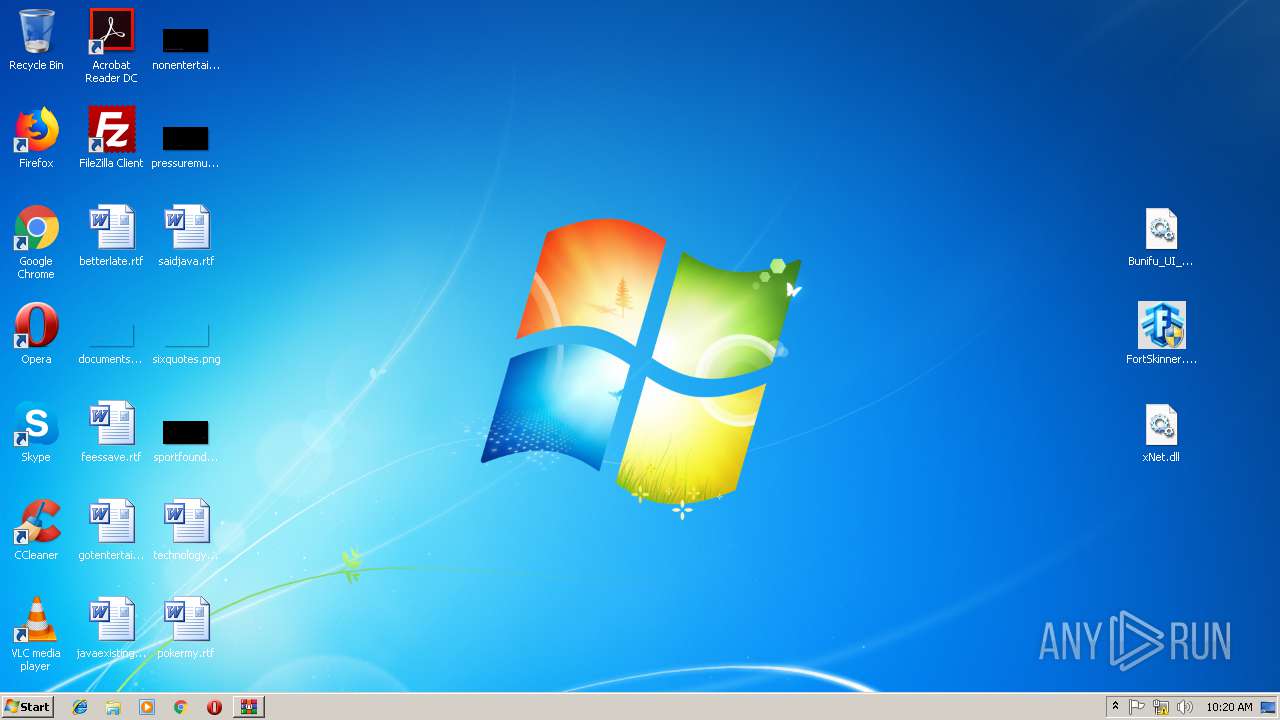
Creates files in the user directory
- FortSkinner.exe (PID: 552)
Checks for external IP
- Regasm.exe (PID: 4000)
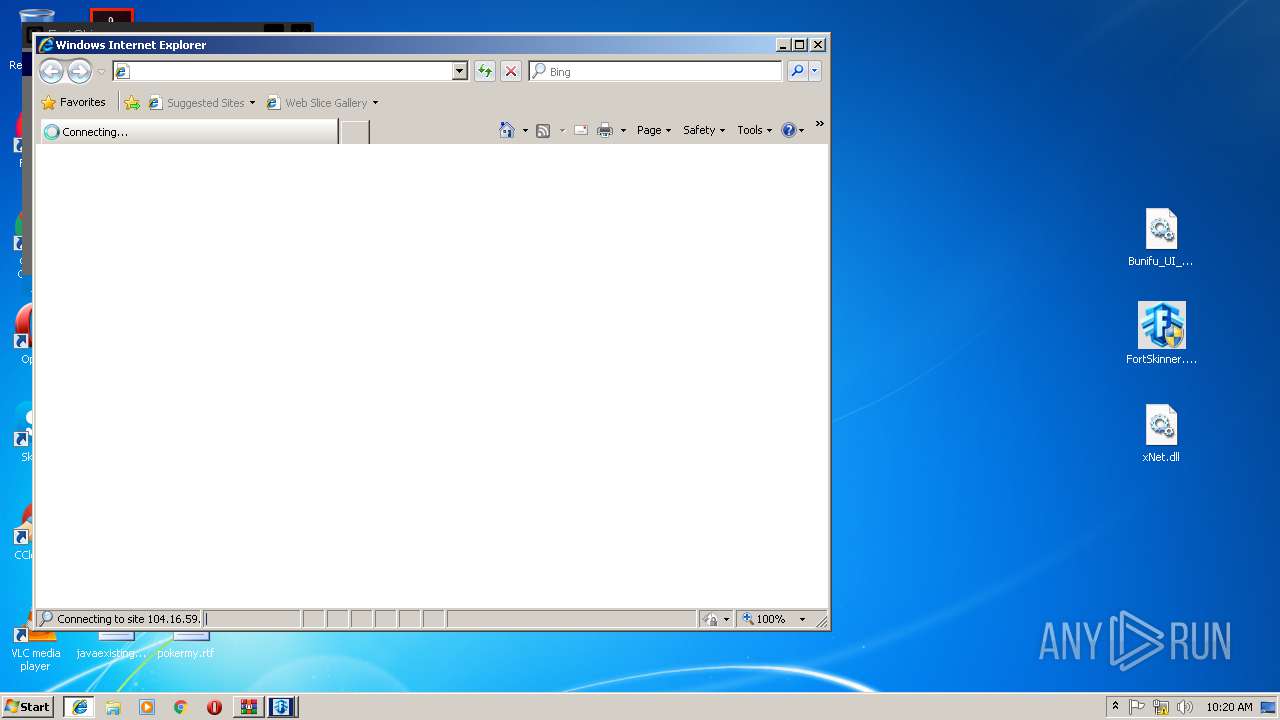
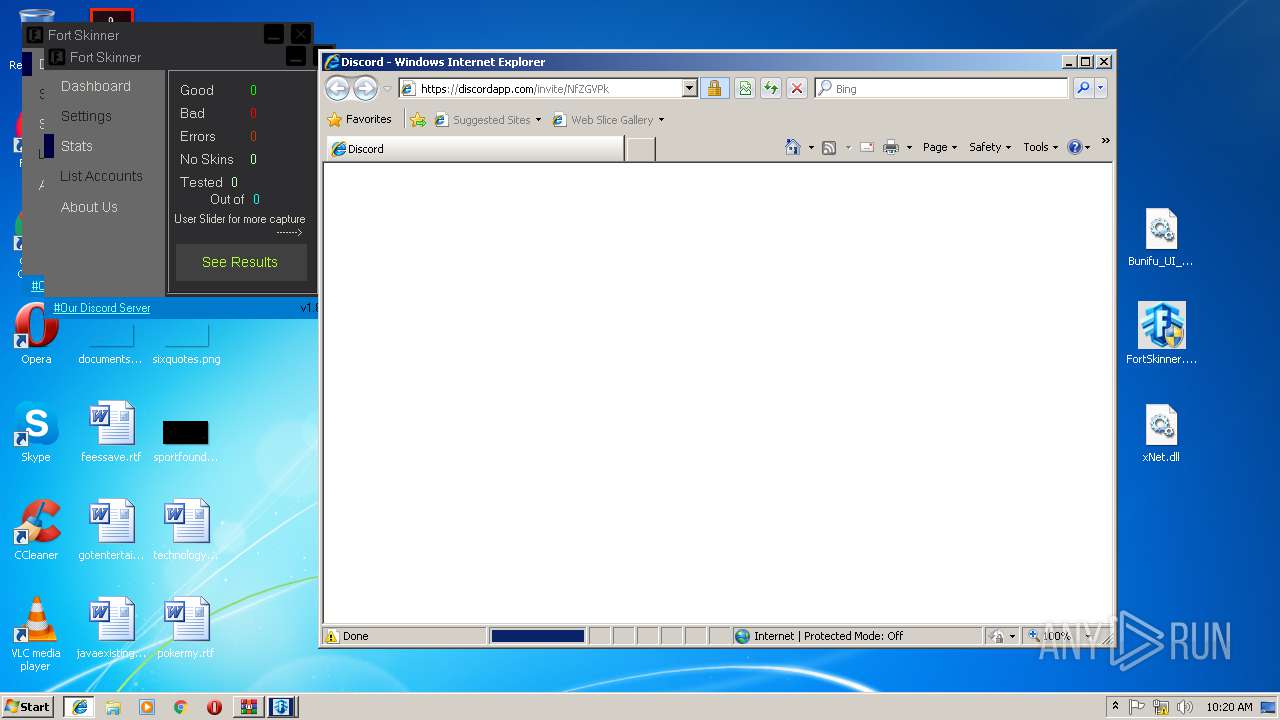
Starts Internet Explorer
- FortSkinner.exe (PID: 552)
Connects to unusual port
- Regasm.exe (PID: 4000)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3252)
Creates files in the user directory
- iexplore.exe (PID: 3908)
- iexplore.exe (PID: 3252)
Reads internet explorer settings
- iexplore.exe (PID: 3908)
Reads Internet Cache Settings
- iexplore.exe (PID: 3908)
- iexplore.exe (PID: 3252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
52
Monitored processes
11
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
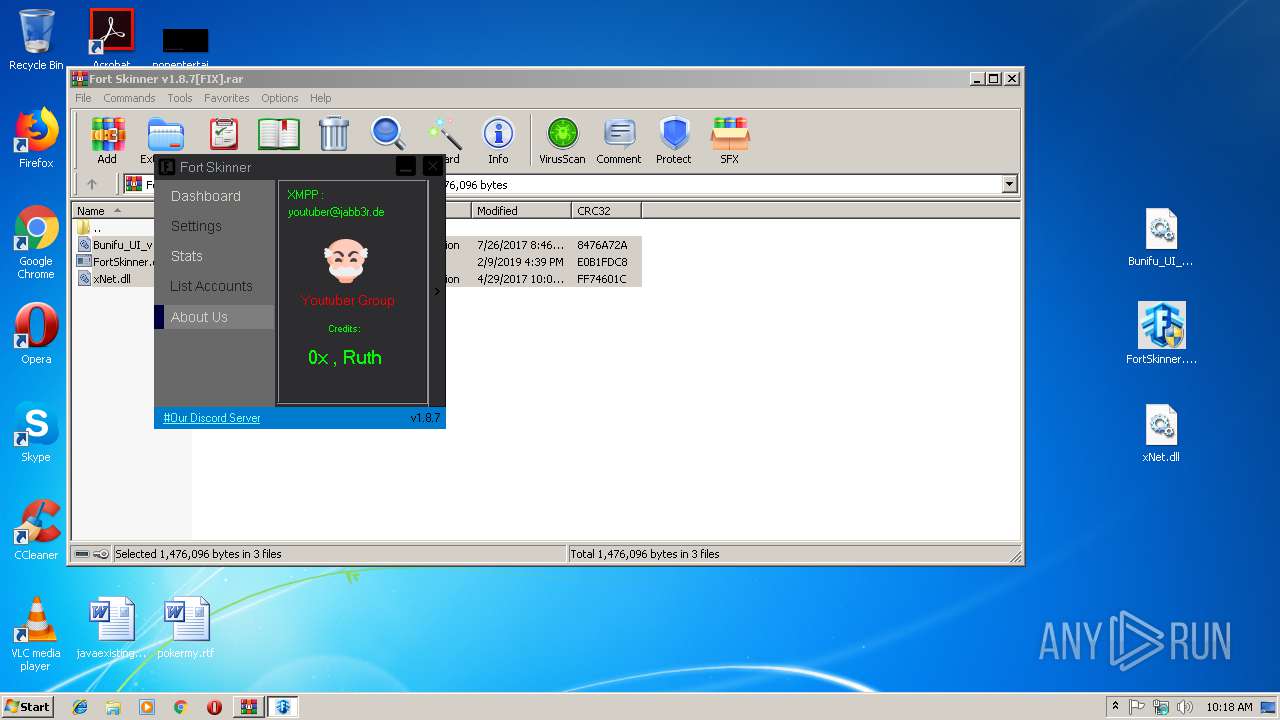
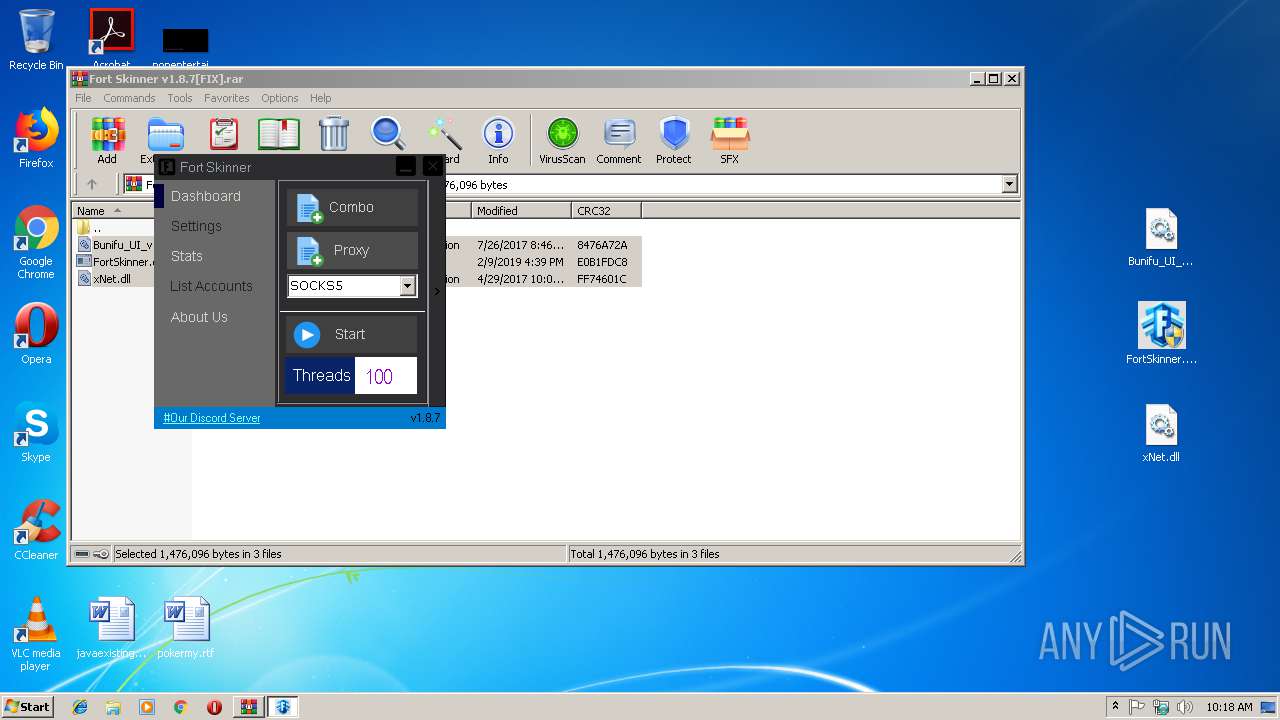
| 552 | "C:\Users\admin\Desktop\FortSkinner.exe" | C:\Users\admin\Desktop\FortSkinner.exe | explorer.exe | ||||||||||||
User: admin Company: Youtuber Group Integrity Level: HIGH Description: Fort Skinner Exit code: 0 Version: 1.5.4.0 Modules
| |||||||||||||||
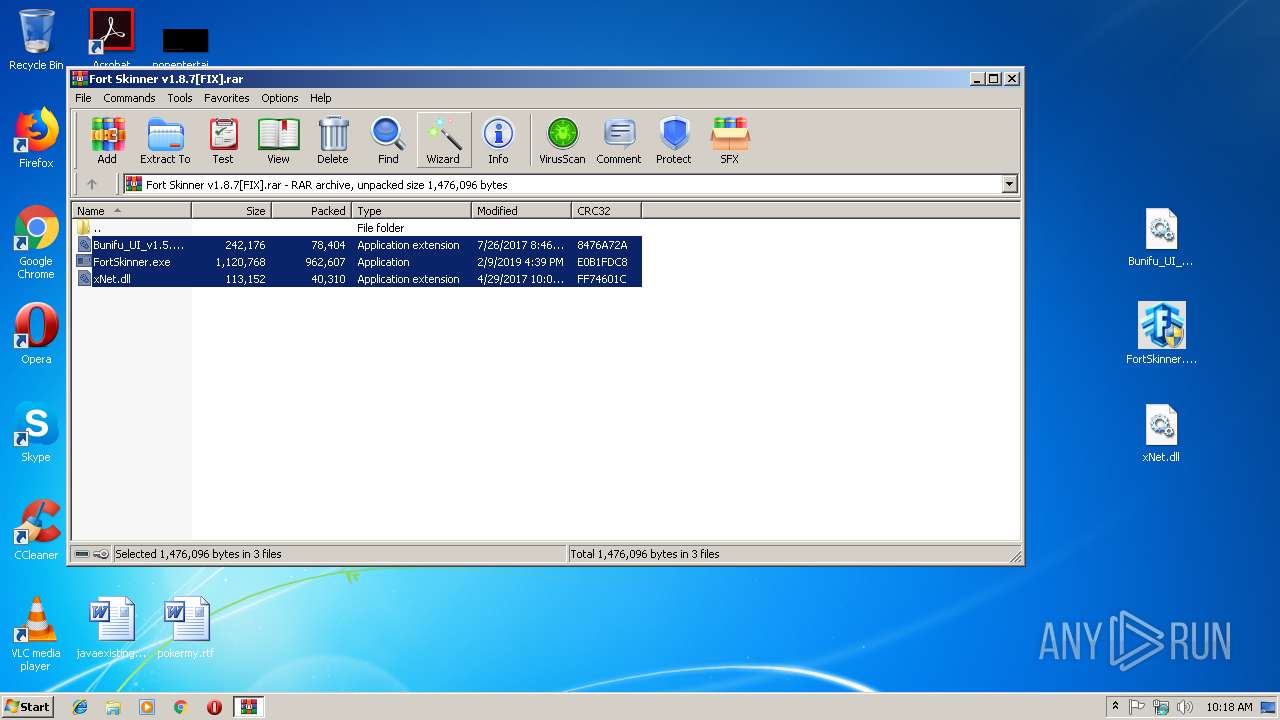
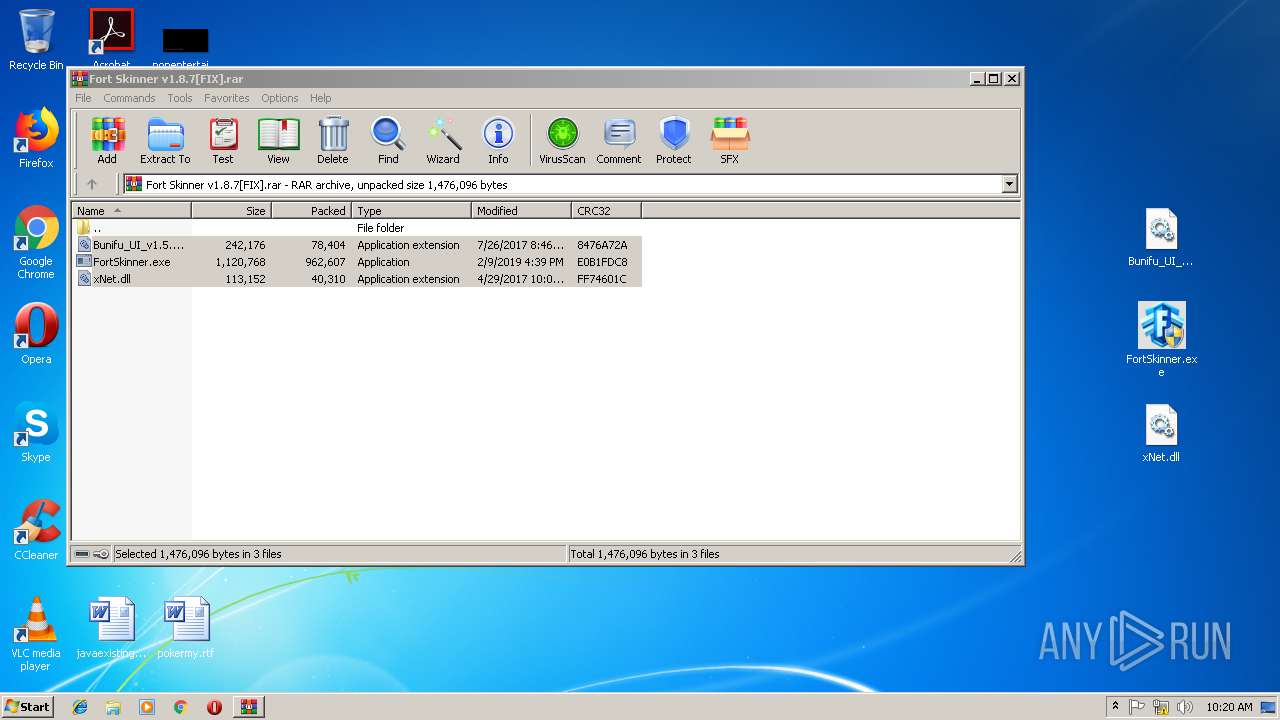
| 2976 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Fort Skinner v1.8.7[FIX].rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\Desktop\FortSkinner.exe" | C:\Users\admin\Desktop\FortSkinner.exe | — | explorer.exe | |||||||||||
User: admin Company: Youtuber Group Integrity Level: MEDIUM Description: Fort Skinner Exit code: 3221226540 Version: 1.5.4.0 Modules
| |||||||||||||||
| 3252 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | FortSkinner.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3412 | "C:\Users\admin\Desktop\FortSkinner.exe" | C:\Users\admin\Desktop\FortSkinner.exe | explorer.exe | ||||||||||||
User: admin Company: Youtuber Group Integrity Level: HIGH Description: Fort Skinner Exit code: 0 Version: 1.5.4.0 Modules
| |||||||||||||||
| 3608 | "C:\Users\admin\Desktop\FortSkinner.exe" | C:\Users\admin\Desktop\FortSkinner.exe | — | explorer.exe | |||||||||||
User: admin Company: Youtuber Group Integrity Level: MEDIUM Description: Fort Skinner Exit code: 3221226540 Version: 1.5.4.0 Modules
| |||||||||||||||
| 3676 | "C:\Users\admin\Desktop\FortSkinner.exe" | C:\Users\admin\Desktop\FortSkinner.exe | — | explorer.exe | |||||||||||
User: admin Company: Youtuber Group Integrity Level: MEDIUM Description: Fort Skinner Exit code: 3221226540 Version: 1.5.4.0 Modules
| |||||||||||||||
| 3828 | "C:\Users\admin\Desktop\FortSkinner.exe" | C:\Users\admin\Desktop\FortSkinner.exe | explorer.exe | ||||||||||||
User: admin Company: Youtuber Group Integrity Level: HIGH Description: Fort Skinner Exit code: 0 Version: 1.5.4.0 Modules
| |||||||||||||||
| 3908 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3252 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
992
Read events
854
Write events
135
Delete events
3
Modification events
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Fort Skinner v1.8.7[FIX].rar | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3828) FortSkinner.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FortSkinner_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3828) FortSkinner.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FortSkinner_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
4
Text files
8
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
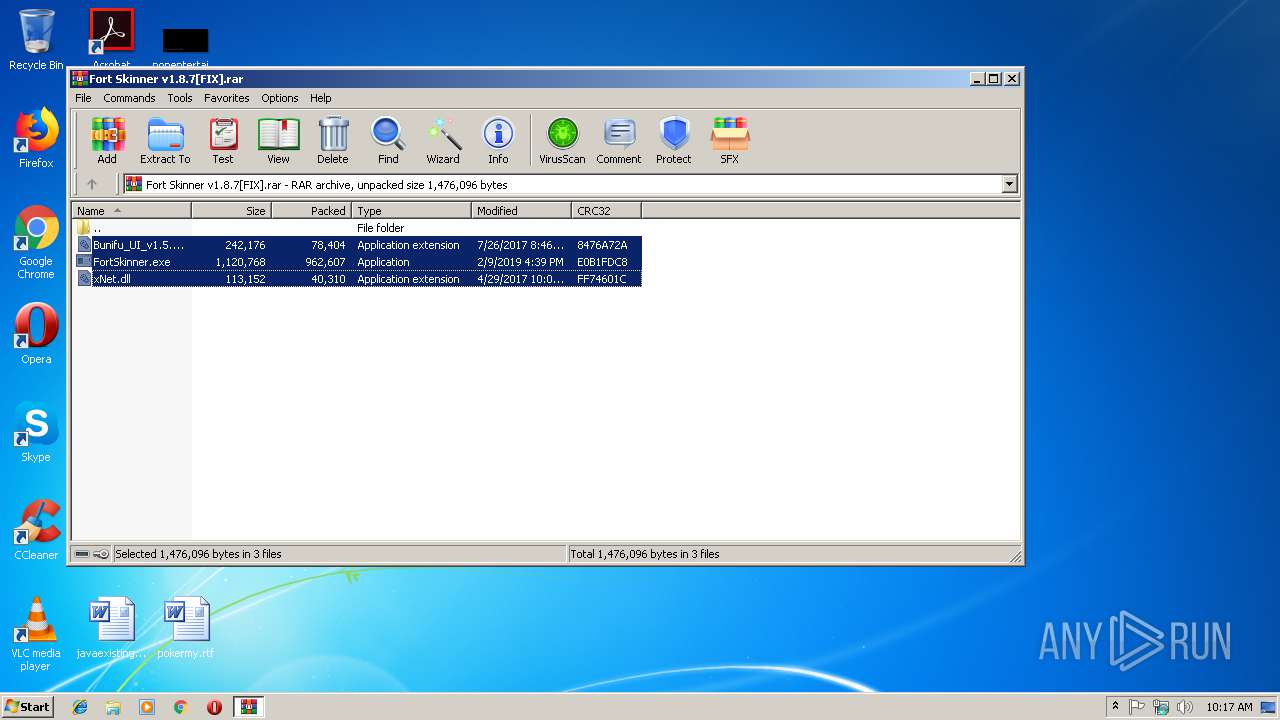
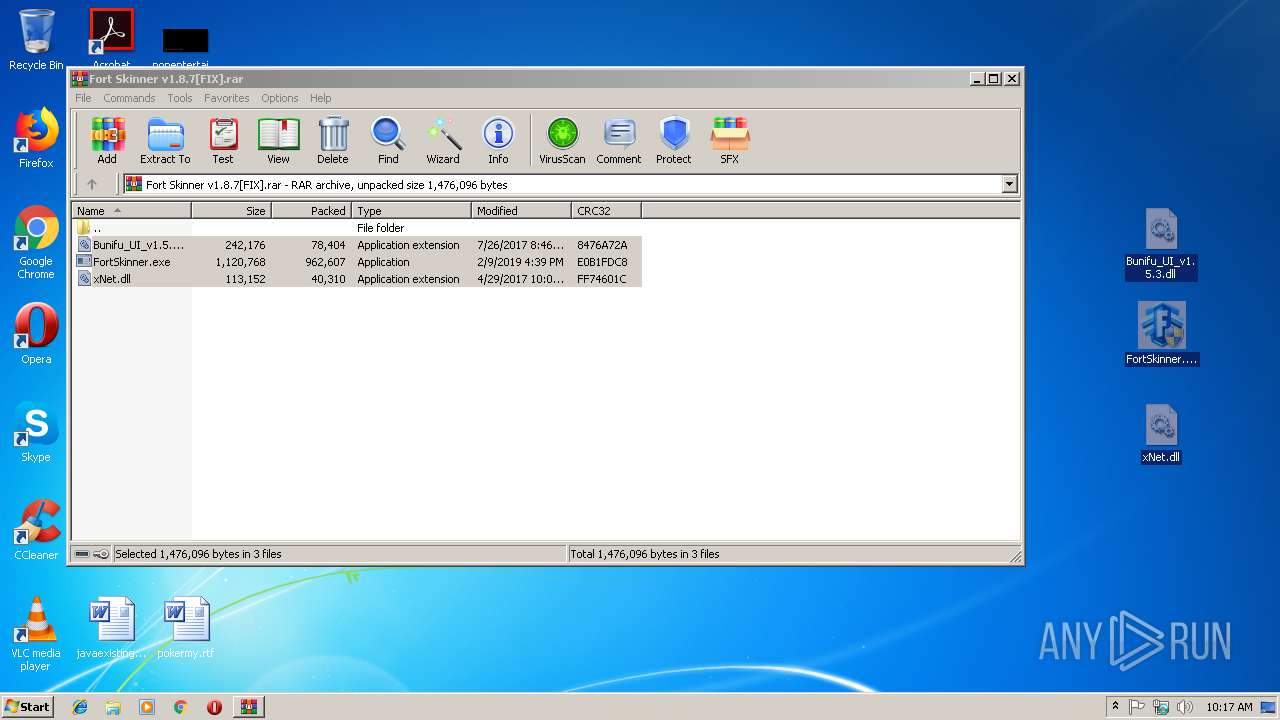
| 2976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2976.27600\FortSkinner.exe | — | |
MD5:— | SHA256:— | |||
| 2976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2976.27600\xNet.dll | — | |
MD5:— | SHA256:— | |||
| 2976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2976.27600\Bunifu_UI_v1.5.3.dll | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3908 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\c73d229b094bb39f0686[1].js | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2AEB74FD81252FE1.TMP | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF96F6475EFC4B2785.TMP | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3F26E1F42026231E.TMP | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\{A452AB44-2DE6-11E9-91D7-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
21
DNS requests
11
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4000 | Regasm.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 256 b | malicious |
3252 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3828 | FortSkinner.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
3908 | iexplore.exe | 104.16.59.37:443 | discord.gg | Cloudflare Inc | US | shared |
3252 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3908 | iexplore.exe | 104.16.58.5:443 | discordapp.com | Cloudflare Inc | US | shared |
4000 | Regasm.exe | 69.61.84.233:3364 | ilikemoo.mooo.com | Cyber Wurx LLC | US | malicious |
— | — | 69.61.84.233:3364 | ilikemoo.mooo.com | Cyber Wurx LLC | US | malicious |
552 | FortSkinner.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
3412 | FortSkinner.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
4000 | Regasm.exe | 185.17.26.75:3363 | — | UK Dedicated Servers Limited | GB | unknown |
4000 | Regasm.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.telegram.org |
| shared |
ip-api.com |
| malicious |
discord.gg |
| whitelisted |
www.bing.com |
| whitelisted |
discordapp.com |
| whitelisted |
dns.msftncsi.com |
| shared |
ilikemoo.mooo.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4000 | Regasm.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
4000 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar 1.3 RAT IP Lookup ip-api.com (HTTP headeer) |
1060 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to Abused Domain *.mooo.com |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] Quasar RAT |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] Quasar RAT |
1 ETPRO signatures available at the full report