| URL: | https://url.au.m.mimecastprotect.com/s/swX8CNLJA6T9gzG5Imf5Syobf7?domain=linkprotect.cudasvc.com#fe4f4121ad64cfa8ddaa6f261e39c8eb=YWJhcmthbkBhYXJwLm9yZw0= |
| Full analysis: | https://app.any.run/tasks/48b83a1b-1459-4d23-ace2-09c3928973cf |
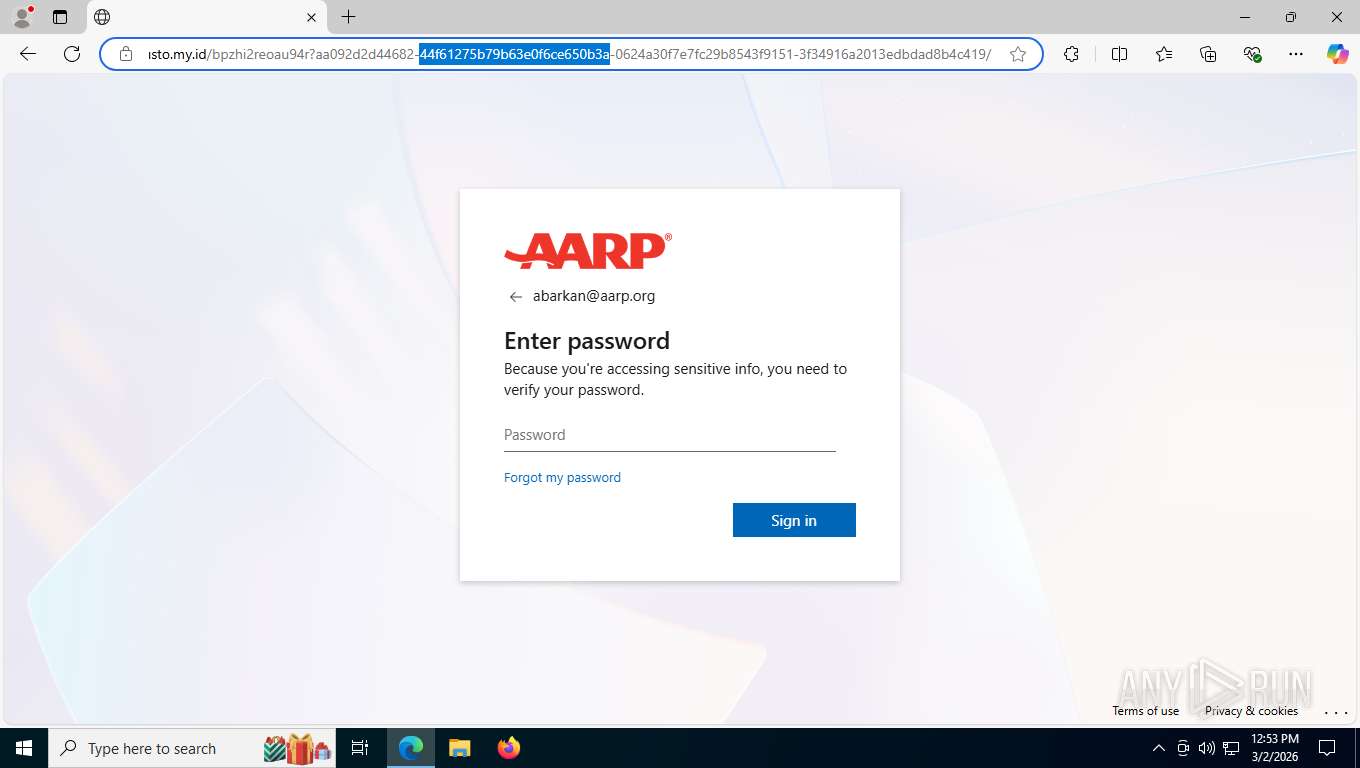
| Verdict: | Malicious activity |
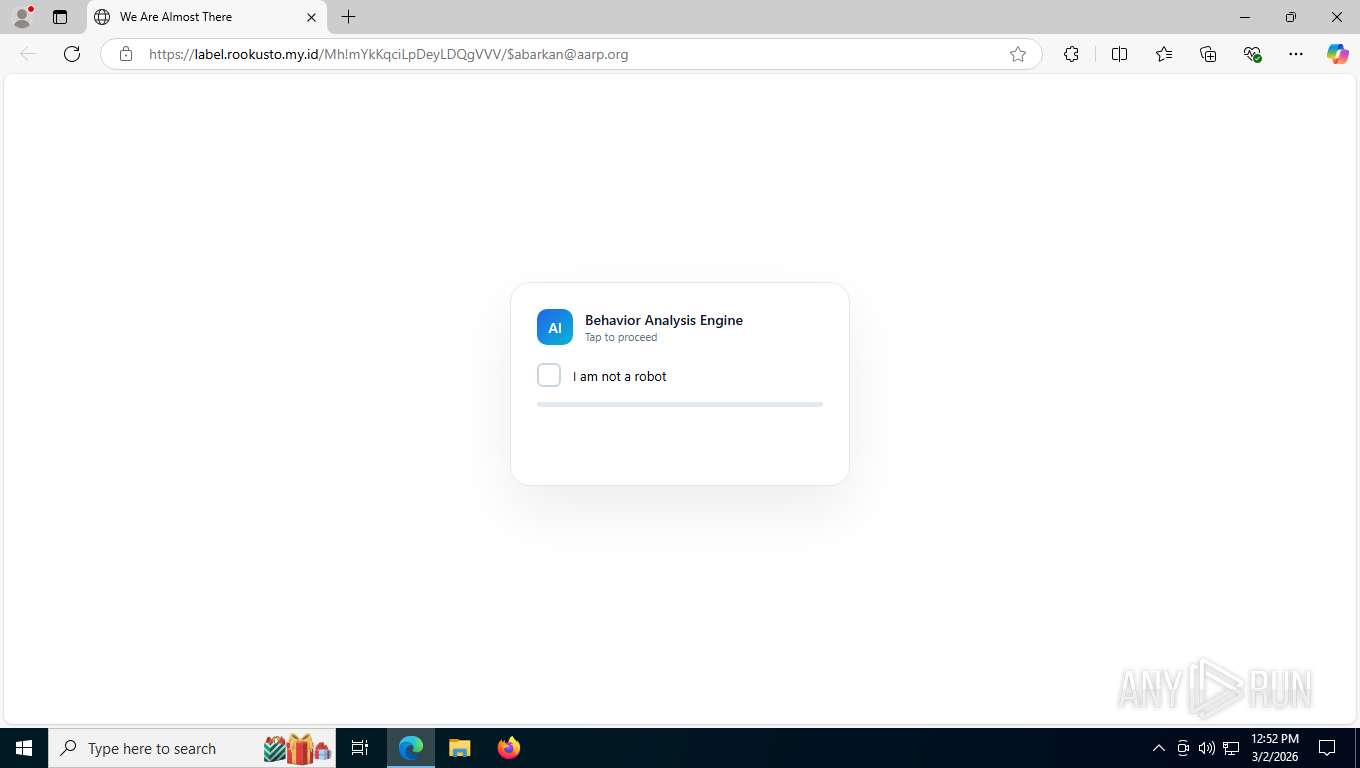
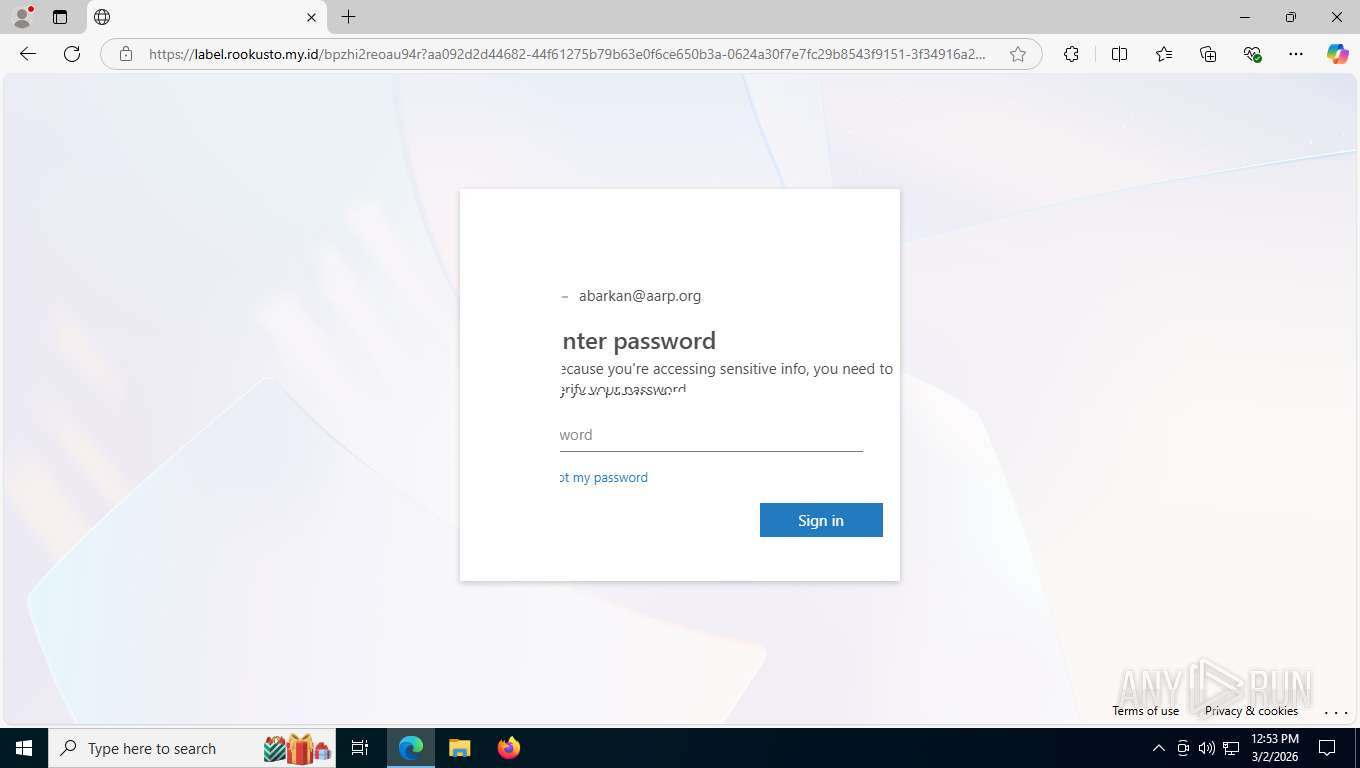
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | March 02, 2026, 17:52:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7387BD45A4CD77073F15ED9681E92481 |
| SHA1: | 93E5E29FE562C7A958955083EFCDA0F87E9FBCF5 |
| SHA256: | D60C0C4A5B726393D02DCC2888E19604CB54E7E1AC308F3675E56EC3C1DBCE3A |
| SSDEEP: | 3:N8UDATSCx9zi57KjSxMtdHGDEEyDEdFlbxcGITw8t:2U2+7JMt0EERrlbKGITF |
MALICIOUS
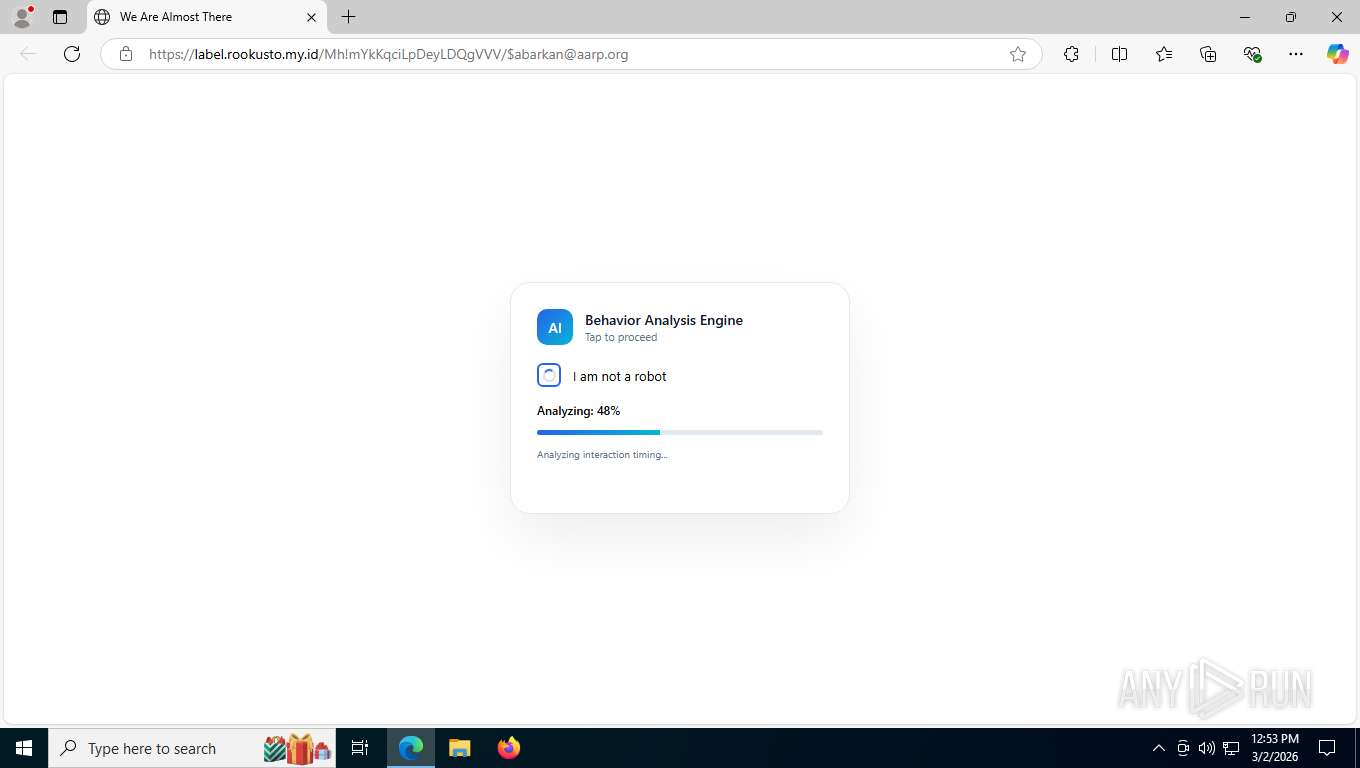
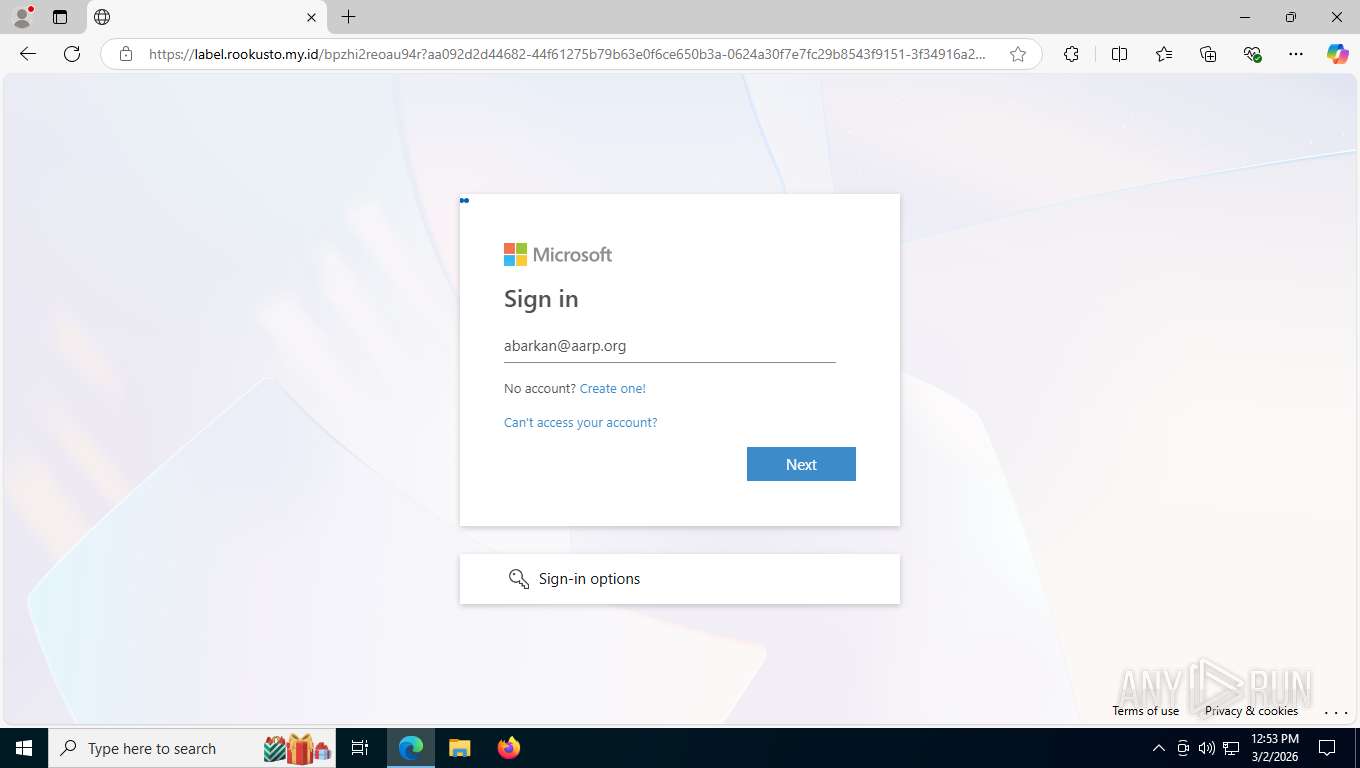
Tycoon 2FA phishing kit has been detected
- msedge.exe (PID: 4712)
PHISHING has been detected (ML)
- msedge.exe (PID: 4712)
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7164)
Fake Microsoft Authentication Page has been detected
- msedge.exe (PID: 4712)
SUSPICIOUS
Page with zero-length space title
- msedge.exe (PID: 4712)
INFO
Checks supported languages
- identity_helper.exe (PID: 3644)
Drops script file
- msedge.exe (PID: 8780)
- msedge.exe (PID: 4712)
Application launched itself
- msedge.exe (PID: 4712)
Checks proxy server information
- slui.exe (PID: 1568)
Reads the computer name
- identity_helper.exe (PID: 3644)
Reads Environment values
- identity_helper.exe (PID: 3644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
183
Monitored processes
34
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=6136,i,16500357932624631990,14071783502226702516,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5896 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 848 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6892,i,16500357932624631990,14071783502226702516,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6924 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1400 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6912,i,16500357932624631990,14071783502226702516,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6940 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1568 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6320,i,16500357932624631990,14071783502226702516,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5784 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5624,i,16500357932624631990,14071783502226702516,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3584 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3616,i,16500357932624631990,14071783502226702516,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3648 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3588 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6360,i,16500357932624631990,14071783502226702516,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6388 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3644 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6360,i,16500357932624631990,14071783502226702516,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6388 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6688,i,16500357932624631990,14071783502226702516,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5828 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
3 859
Read events
3 859
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
25
Text files
235
Unknown types
131
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e5419.TMP | — | |
MD5:— | SHA256:— | |||
| 4712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e5438.TMP | — | |
MD5:— | SHA256:— | |||
| 4712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e5438.TMP | — | |
MD5:— | SHA256:— | |||
| 4712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e5438.TMP | — | |
MD5:— | SHA256:— | |||
| 4712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e5457.TMP | — | |
MD5:— | SHA256:— | |||
| 4712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
132
TCP/UDP connections
78
DNS requests
94
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7164 | msedge.exe | GET | 307 | 124.47.150.19:443 | https://url.au.m.mimecastprotect.com/s/swX8CNLJA6T9gzG5Imf5Syobf7?domain=linkprotect.cudasvc.com | unknown | — | — | unknown |
7164 | msedge.exe | GET | 307 | 124.47.150.19:443 | https://url.au.m.mimecastprotect.com/r/mU1QRyRHm-qbYYcfcrz8ZKWry4ixoH0CJ0OdxXIl9UYExQAp1trm5HfCzO9EKs6AJUdWCi0qlrtz0iu3LDoYXexRDhRpIxZu6kjsQXvQcPoYTOFTIH9DGBUIxhcBwKfxK0Tq3edxVq0-cp1GKLkOW_3Uj5-LdwIzb7F2fM-XrZa5qvmeWsZ2FF2KsSVXrGfPD7viRkEuTZzTFeuDrnlmkVeV79S2EddWrfzZfEkh8g-hfFn6YeiB-bE-7_8DuFiuMNUQXRq0Fom7cSiIIgqdhv5PT3O6g1e6rb5Ad9d9PE3qauruTN66Qdzuar7JrAiAZWylm-Rk3J4JikK8laEdxB-xM2RSxa8wITZs5LMp0p0pCO9I3cWhWk3Jdnz3HKYG3pP-BJ_3gasZi5HB_Dy808xDjLhnAIElfT_ENZVIxO154T70uEgp54WsR5_Vhj2J1czsdgUDh04PsywcOJ1qnXmIdBTHjgfEbjyMm1PdKJ4vT5sKutt6zpVyr3iedws0Bj7r_q_9ifj4_pCBWN8dNQPdGmU8QPC6XYxTk-z908lC7kaUoVRuFMuDAvN9JDW2Z-j4GW8ssRq6m_0NrH5EclCIlRKo1B828fVycBBLjyYuKXwdTxyVX3xcrAuaXD-XlKAAp4fk1PRCklXaO2jpiixHTccUmD779J7vI_Vrzl-VBiXdxkTl03NJvURrhfLFIYjP5p4f_sbVKt_YPh9bRANvJRaZt5P95KtYlwxKz10hDjE7WpNz0-dV7EQGQX5C49BTMIcWAh-qfcn6x39QzJf9XvCNAVlwbpZr5nkF1KQPG9g9DyS8b9lTeJTG7eVbcypcMlDpEgyBjsKujnvqdu9HG2wGxyNHB8JVY4B0oszVrxZo1rgL63_84pQ9ys57qO5Qc3w7zzqlTlMAKipdMXOYJtXCiULgZYOwR6HMxWj5II9EsCT4MF31M_jIFXMFIqU1fMhDU-LFEOgYGrdYmPakyQOB6dSUTl5D66WIhK7dolDRdRIvro8Qi75Wibu43VtUfraKXlwu72pOs1-9nuYUBxRjR2L3Sd3BGu4yDAt1v-yxQL-F00DVjfhnl90lY1yDP8lTaJJc6OZngK-0DeR-3m_lK8yKO5ai1rmiox5KXSokdj3NIbzkLcrd2dSCsGeAk1hGliVgB-mGKQNDQS5M_UdWitJtI-Tf8LNtDL_mTE5Upi4JswYKkNUiberFz1_VHyGKkxjAhO6F2RxznTt-CgWOXSLVrsy6crUlbi1E5TFhq1WnSG-bqrT_FyjLHvB2kvjQ_mx0QaHhSGYWsz3hfXM_xsZyyZ1LFWTQPAXdsW8Ijz8H5cJg9MNCiUrEa5YCbUBfBjYc23euHDGfXyZR8tgX1Ya9CWVZOCwx80-rA_3Zhac_Zjtzb2V1ixTbdWcexuBA4TgSKtZZtgYUawAKR5XIkN_Ro_VAzjIH4yIo2a4q25n1mxuJnShn49BFfx0QRAUPcBedxMOV3N9zNK1Ys3XUx2b_IUNiwBLTNbxdBzUWz40OYSAub1GjrK5NmvFgqEKqVVGzs6jC2sjKmKoTHq6m5J18RaDa4v2FWDOysH1KLxVIV-hCp8aoQnd7CKsol7UK7QoeHx7zXzGs7hC2L72QC4xnZu-fTGb7rNAFbH6hC0YLlRrobDSkUEZ56jYsyY_lJB-cBXGZkXC3WcuaeARp9vYDqmcyiuXuuDR9Cdol8-Cxb8Q5KJEP7B7t1jV_7RZvbWHFLKjft2vEkPZ-iZkQzk0lVrU0hjekcslHRVO2YASnl9d_DQXqISksvDcXGsF9EjIvDy8zqqALRPqW8wnEpDPcKwoi3eHCJp5E5NOfE_n_QexO8LMGEptyOnqU75naQKfbhimLmBytHAm_u4_UFLUnYJp0T08hCwnNp_ciNJAui7F1o7oenM8hV4diNrCuRWTiyrKVXKrtEE9_6Es1AP8LH8kXZQxUGWp5RVDEOSwMoBFqmXXaxFpKCWmbxc18DoiYFOg8fP8OCmuc4lcTj5AJPMqfKgAMGRFqauj93aLWyPAIpWt1Y3BTNMYO9Opuio3x5ztqcKR6iCTrGsCqPA6Id2SZruwD8iLk4vOHvknA3kWIQFm_LRbURQcUtdqM7SxkDwJhbDMVkfLkY26n9DEFg-IKV40tWh_h-qtXC8xmvDPhml52Eu4DnClRvHz3L7nCK9G26CBWw3DM0WJEIyU4v_fTIOaNqDHTgrgU58RgQIa7ftPK58npIkD2VfFNmhbtJDchzAsEIEhCH2JVCru3A-3pH8vUkG3nXuwE7vmjZDhcKg7v32GPEPS3YOv7m6KT99h43U76gx5lwUErCF0L_GiR5cH-b5Pms3Y3oQPIdq3gXUYBmGOz-h5Bc6lkCpr1A_n4DWTwAyIg8IJBcrWP_ddjxzL-7kNjh79P_wvrM201P6yX4jo04HRMGbC7pDlIeVX1We_rS_muiuLKZjr3m71h1cLVpxA7bbcoamYnuJ4pzGFfZi6LoJcKRGHd4BCBXcYxWjJdzozLfHfzVD3WZe8J8EJEPKDLms8R-nZTEWbs4mZdR9Es6aAVprMtoLEEfyztdnNYdMymDugaojyDOujqk_qQNYDKbd7AvTOptQYdGyjbreUbtk-rQHqrj6zkqfFdZRpihp3C1WdzM1p48x3hF9O6EIYfDpWDViyT9in9R60VGojA79nV9E9qj4pWqCz2seMM3wEGqjWdpA-EJUArU4AiqVyijn3vFVCprVd4o5aG7l288RZx05B1o40GpshLHznCv937oa9-BIRPJL_CwA-yC7akEDi4pqPlv6rUeaEnTFN4VTFLYp_wIpDaK0ICwbPJiqfRiwKtfQMQCANF7Qq2z4DGNPVyh2T9S8iv2pPgBddAcMWXRxCAyj1DyTwaB0PyP37biCXS--3W-CSvaNuBYmFWh7TzZLikoLMGZ-KG_ROzTRF-u0E5bg4WzfCw_jnUPs9z1HAgqWf95dJeKRpxERdEi1IgFnQNv-Lm8utx3KiQ9vxFwoB7yKP_y7_fCEFFgr-BG3dFGragA2DBFCX7cpRQrxqw8CAt5mgOA-tOd_gtzRQ3sYxZ4BtbBCC_ZmyQQ3rN8FveiXCooFmmoIDE5tyrv_Q4qEC_ifTu2CV4jFGrCXnk6HkMNaGWrkECPNhyjQwIwx6CMLqaGpaMwIXxFz5w0rsvB2dr50rJ6aZk1n-SxeFxfwYyfd1MrDa3Vm_cj4SGPZJRddnbzgymnkYOwGybVzuxyakqbx2BJ2dRnEIlA1kkIUmKKcZGLx3VxYHXXogCuvGpAUVkFX3CtdcSCwk | unknown | — | — | unknown |
7164 | msedge.exe | GET | 301 | 91.92.41.47:443 | https://qa.yeniegekoc.com.tr/ | unknown | — | — | unknown |
7164 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1772473946&lafgdate=0 | unknown | binary | 4.30 Kb | whitelisted |
7164 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 295 b | whitelisted |
7164 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:o7k-KgGHQa7w0WNxAdUi4WxrvFQ0OpjQ4Qxp-kwFT00&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7164 | msedge.exe | GET | 304 | 150.171.28.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | unknown | — | — | whitelisted |
7164 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
7164 | msedge.exe | GET | 200 | 13.107.246.45:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | unknown | binary | 82 b | whitelisted |
7164 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeRuntime%2CEdgeRuntimeConfig%2CEdgeDomainActions&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1772473946&lafgdate=0 | unknown | binary | 41.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
8124 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5512 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7164 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7164 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7164 | msedge.exe | 124.47.150.19:443 | url.au.m.mimecastprotect.com | MCT-SYDNEY Macquarie Technology Operations Pty Limited | AU | whitelisted |
7164 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7164 | msedge.exe | 104.18.22.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
url.au.m.mimecastprotect.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
linkprotect.cudasvc.com |
| whitelisted |
qa.yeniegekoc.com.tr |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7164 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Web apps custom Builder (.my .id) |
7164 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Web apps custom Builder (.my .id) |
7164 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as Tycoon (rookusto .my .id) |
7164 | msedge.exe | Generic Protocol Command Decode | SURICATA HTTP invalid response field folding |
7164 | msedge.exe | Generic Protocol Command Decode | SURICATA HTTP response header invalid |
8124 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7164 | msedge.exe | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
7164 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Tycoon2FA related URL pattern observed (tilda-variant) |
7164 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7164 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |