| File name: | CLodop_Setup_for_Win32NT_4.102.exe |
| Full analysis: | https://app.any.run/tasks/063be197-637e-4240-a474-829426d2b410 |
| Verdict: | Malicious activity |
| Threats: | Metamorfo is a trojan malware family that has been active since 2018. It remains a top threat, focusing on stealing victims’ financial information, including banking credentials and other data. The malware is known for targeting users in Brazil. |
| Analysis date: | December 05, 2023, 15:24:37 |
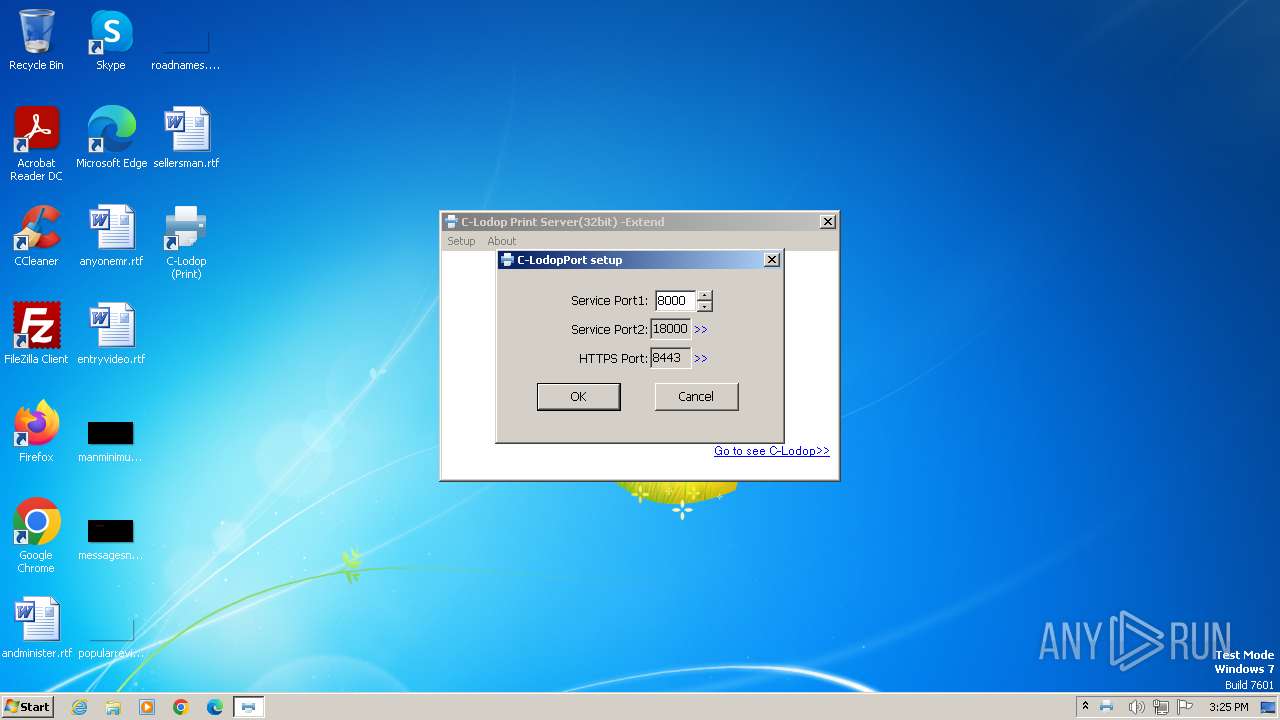
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A05746DDB5E9034297CDF60A093F5E60 |
| SHA1: | 531C8A60AF53249570925AC45BAA0D6B5B4BEC4D |
| SHA256: | D5C0CF0953687C85629E6451E00B0A0CC17549894B365795921301A44FC2FF76 |
| SSDEEP: | 98304:BCKHdWhqxR/sezSNh/aopjkZglcczIdMH4kGHGnYBTrYqPC:eEYe+NgoHlcc02Y/SMTVC |
MALICIOUS
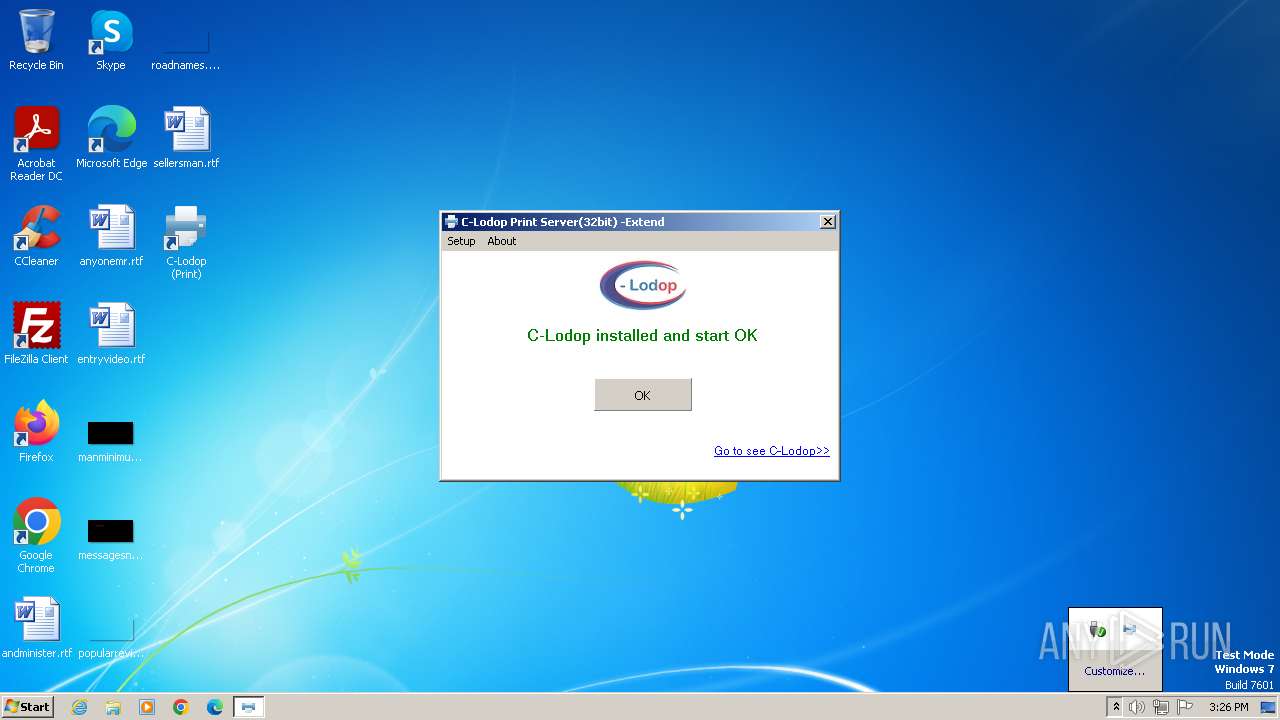
Drops the executable file immediately after the start
- CLodop_Setup_for_Win32NT_4.102.exe (PID: 1344)
- is-BEEOG.tmp (PID: 2600)
- CLodopPrint32.exe (PID: 1988)
METAMORFO has been detected (YARA)
- CLodopPrint32.exe (PID: 1988)
- CLodopPrint32_backup.exe (PID: 3528)
SUSPICIOUS
Process drops legitimate windows executable
- is-BEEOG.tmp (PID: 2600)
The process drops C-runtime libraries
- is-BEEOG.tmp (PID: 2600)
Reads the Windows owner or organization settings
- is-BEEOG.tmp (PID: 2600)
Reads the Internet Settings
- CLodopPrint32.exe (PID: 1988)
- mmc.exe (PID: 2168)
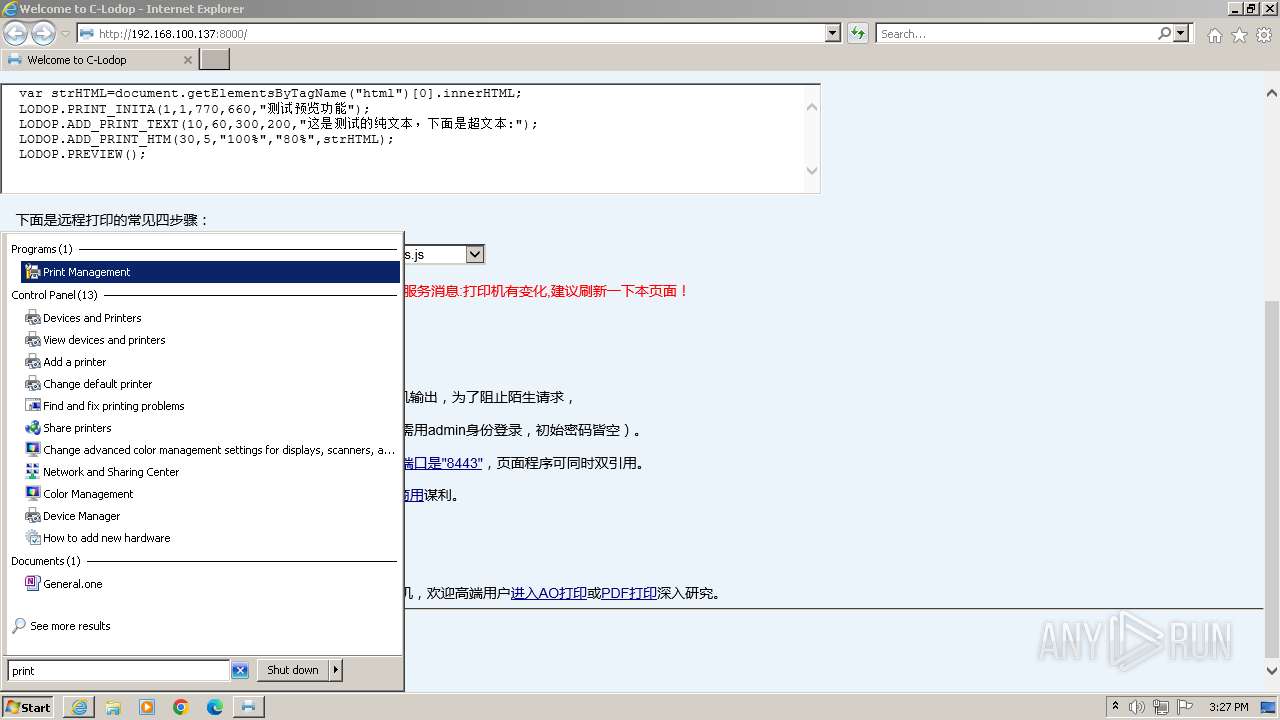
Executes as Windows Service
- CLodopService32.exe (PID: 3680)
Starts itself from another location
- CLodopPrint32.exe (PID: 1988)
Reads Microsoft Outlook installation path
- CLodopPrint32_backup.exe (PID: 3528)
- CLodopPrint32.exe (PID: 1988)
- mmc.exe (PID: 2168)
Reads Internet Explorer settings
- mmc.exe (PID: 2168)
INFO
Create files in a temporary directory
- CLodop_Setup_for_Win32NT_4.102.exe (PID: 1344)
- is-BEEOG.tmp (PID: 2600)
- CLodopPrint32.exe (PID: 1988)
Checks supported languages
- CLodop_Setup_for_Win32NT_4.102.exe (PID: 1344)
- is-BEEOG.tmp (PID: 2600)
- CLodopPrint32.exe (PID: 1988)
- CLodopService32.exe (PID: 1936)
- CLodopService32.exe (PID: 3680)
- CLodopPrint32_backup.exe (PID: 3528)
- wmpnscfg.exe (PID: 3632)
Reads the computer name
- is-BEEOG.tmp (PID: 2600)
- CLodopPrint32.exe (PID: 1988)
- CLodopService32.exe (PID: 1936)
- CLodopService32.exe (PID: 3680)
- CLodopPrint32_backup.exe (PID: 3528)
- wmpnscfg.exe (PID: 3632)
Creates files in the program directory
- is-BEEOG.tmp (PID: 2600)
- CLodopPrint32.exe (PID: 1988)
Reads the machine GUID from the registry
- CLodopPrint32.exe (PID: 1988)
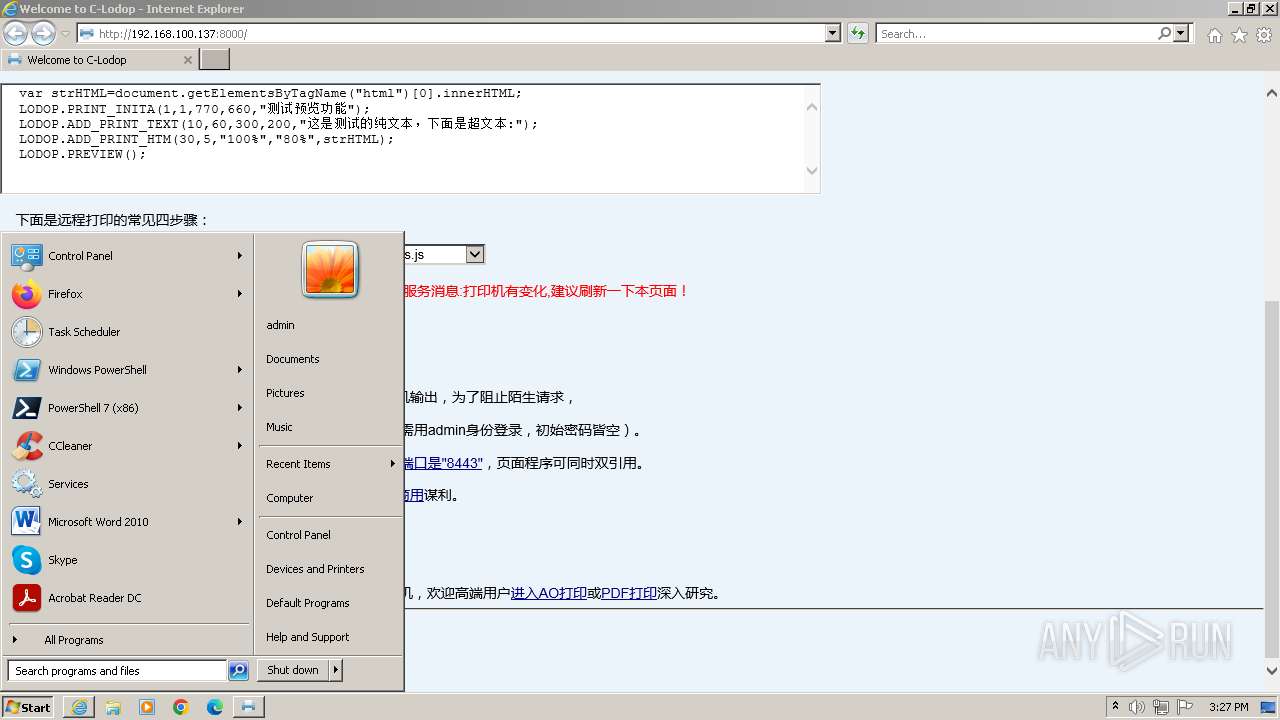
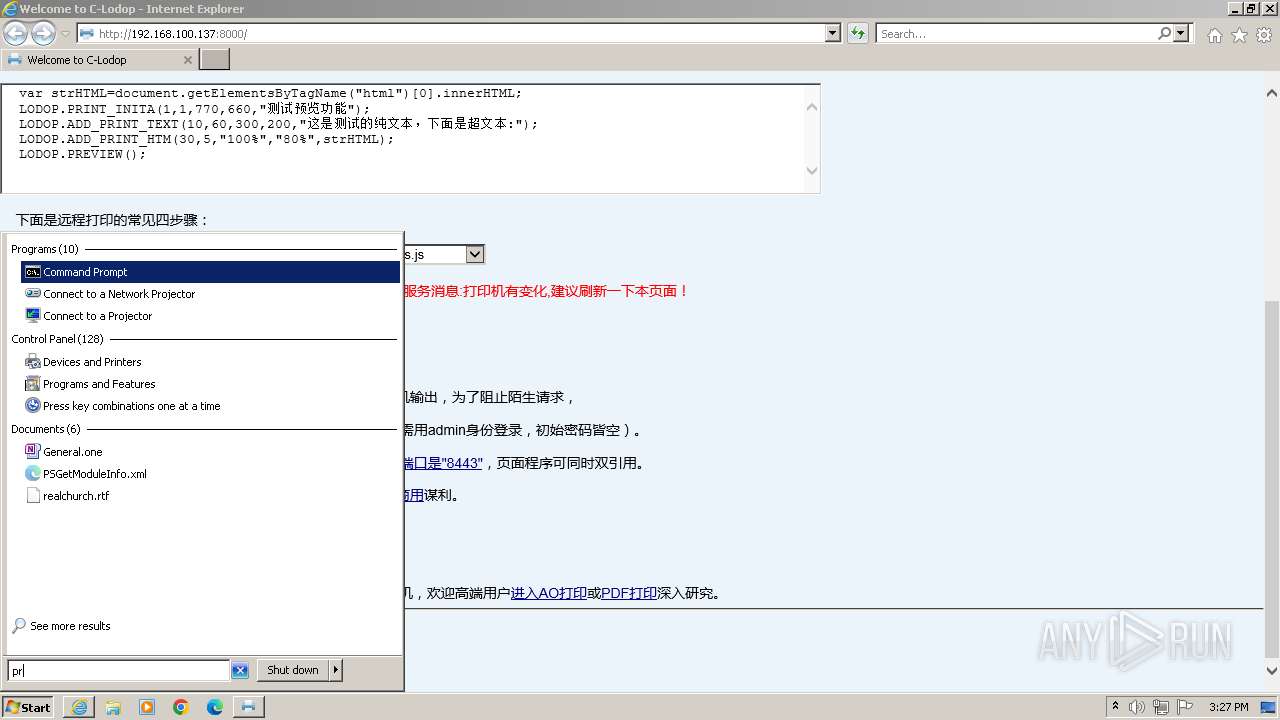
Manual execution by a user
- wmpnscfg.exe (PID: 3632)
- mmc.exe (PID: 2168)
- mmc.exe (PID: 3240)
Application launched itself
- iexplore.exe (PID: 3492)
Checks proxy server information
- mmc.exe (PID: 2168)
Creates files or folders in the user directory
- mmc.exe (PID: 2168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 36864 |
| InitializedDataSize: | 15872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x97f8 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.0.4 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | ASCII |
| Comments: | 此安装程序由 Inno Setup 构建。 |
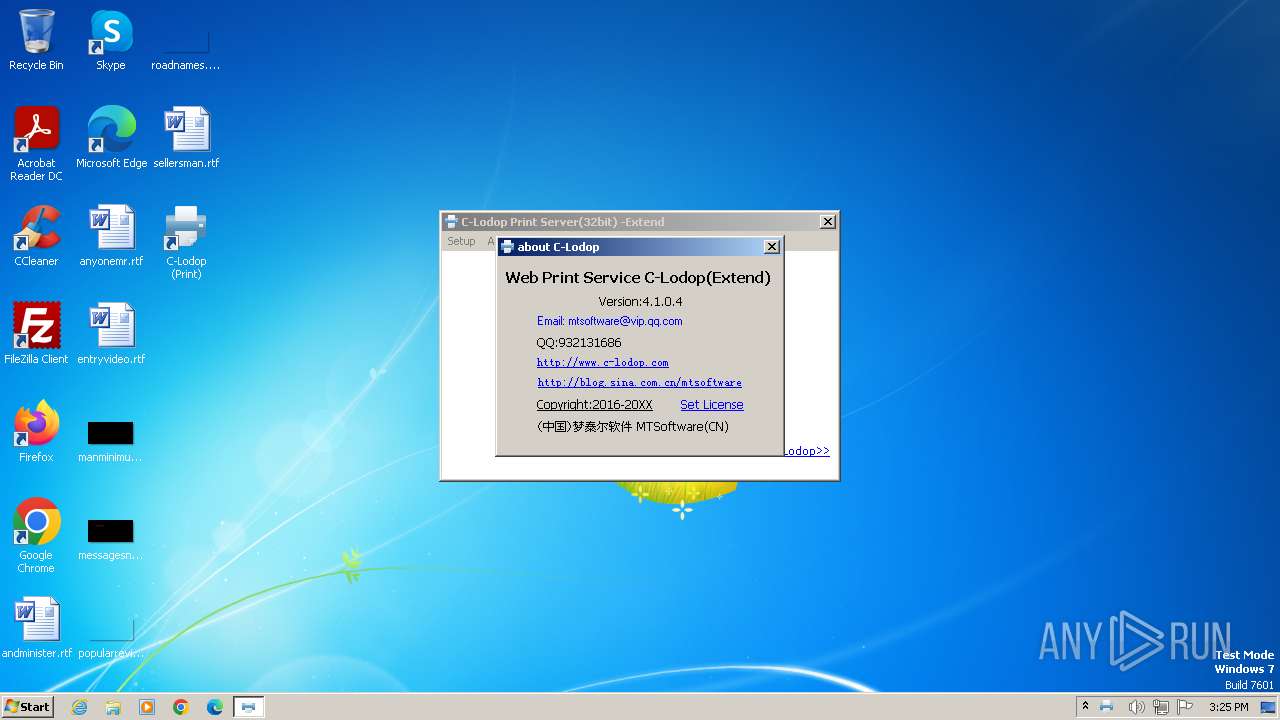
| CompanyName: | MTSoftware(CN) |
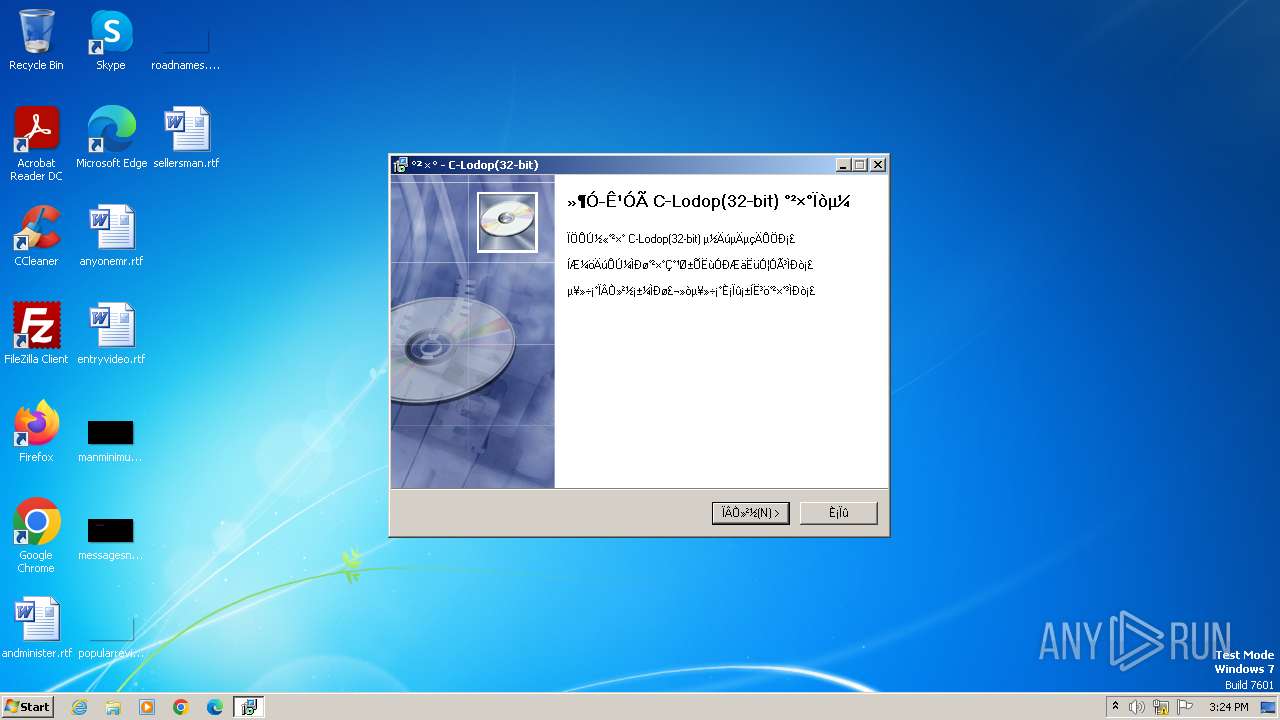
| FileDescription: | C-Lodop(32-bit) Setup |
| FileVersion: | 4.1.0.4 |
| LegalCopyright: |
Total processes
59
Monitored processes
13
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1344 | "C:\Users\admin\AppData\Local\Temp\CLodop_Setup_for_Win32NT_4.102.exe" | C:\Users\admin\AppData\Local\Temp\CLodop_Setup_for_Win32NT_4.102.exe | explorer.exe | ||||||||||||
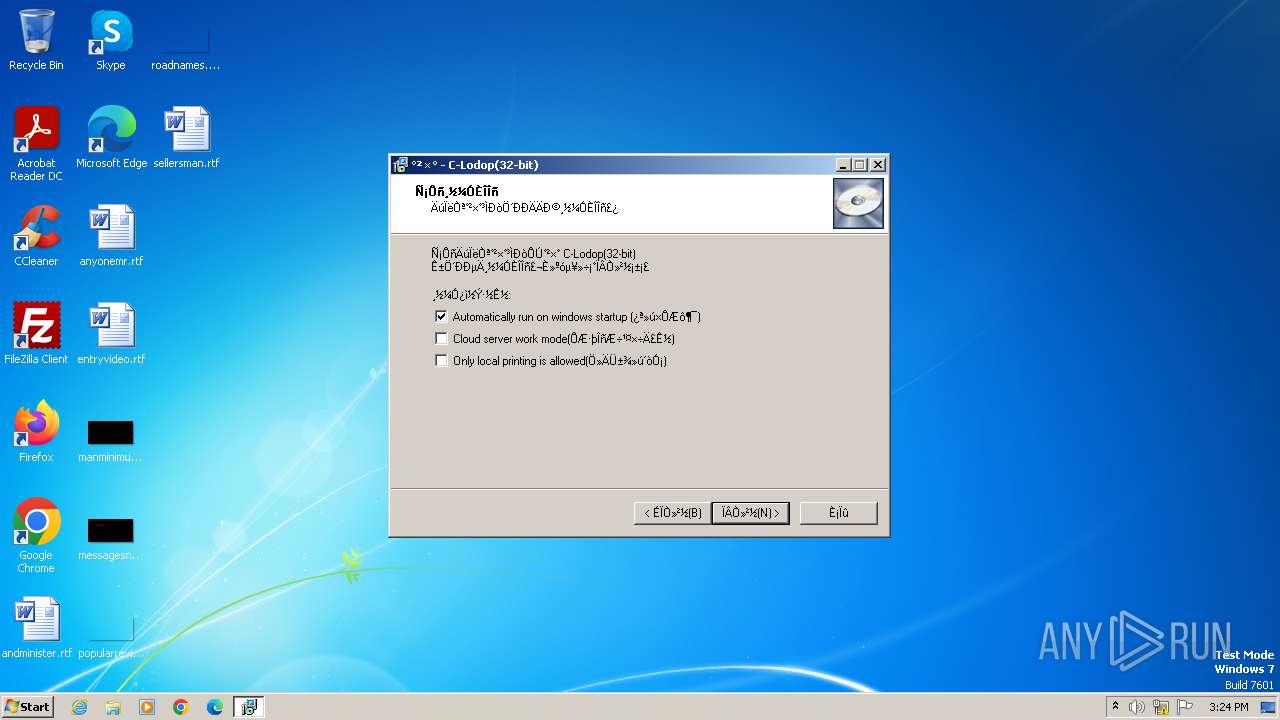
User: admin Company: MTSoftware(CN) Integrity Level: HIGH Description: C-Lodop(32-bit) Setup Exit code: 0 Version: 4.1.0.4 Modules
| |||||||||||||||
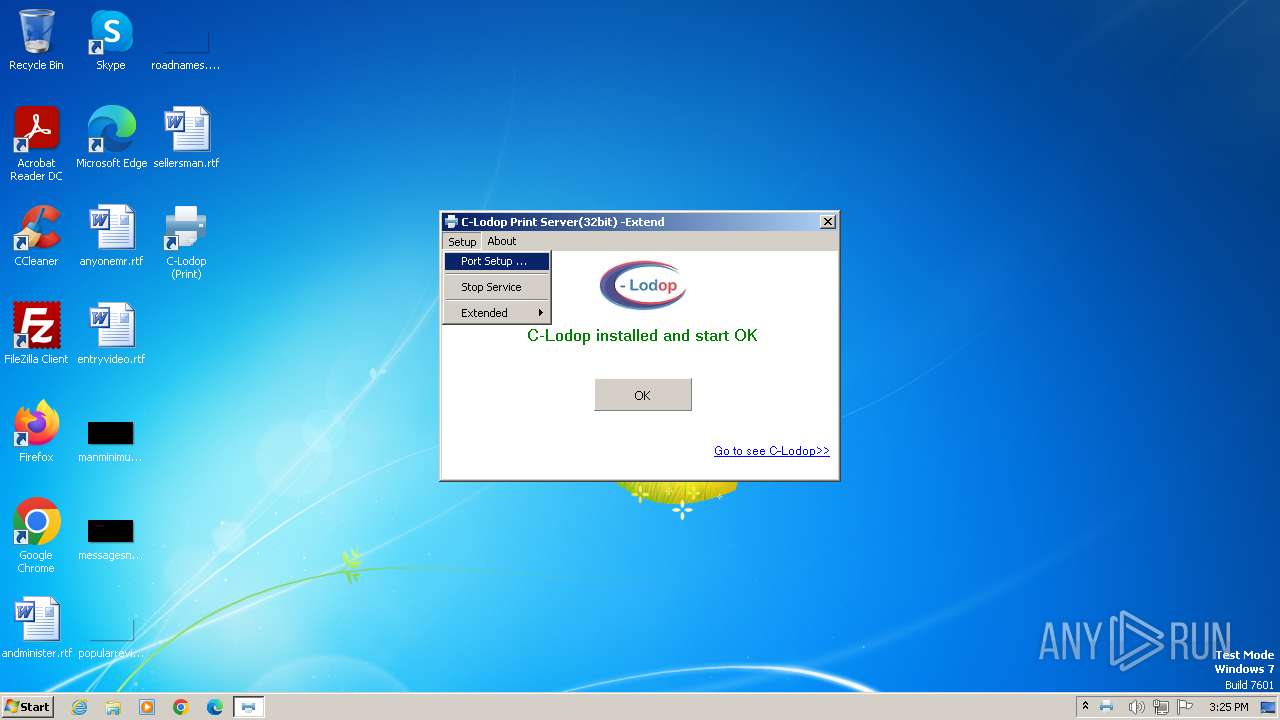
| 1936 | "C:\Program Files\MountTaiSoftware\CLodop32\CLodopService32.exe" -INSTALL -SILENT | C:\Program Files\MountTaiSoftware\CLodop32\CLodopService32.exe | — | CLodopPrint32.exe | |||||||||||
User: admin Company: (中国)梦泰尔软件 MTSoftware(CN) Integrity Level: HIGH Description: C-Lodop 云打印“免登录”启动服务 Exit code: 0 Version: 3.0.0.5 Modules
| |||||||||||||||
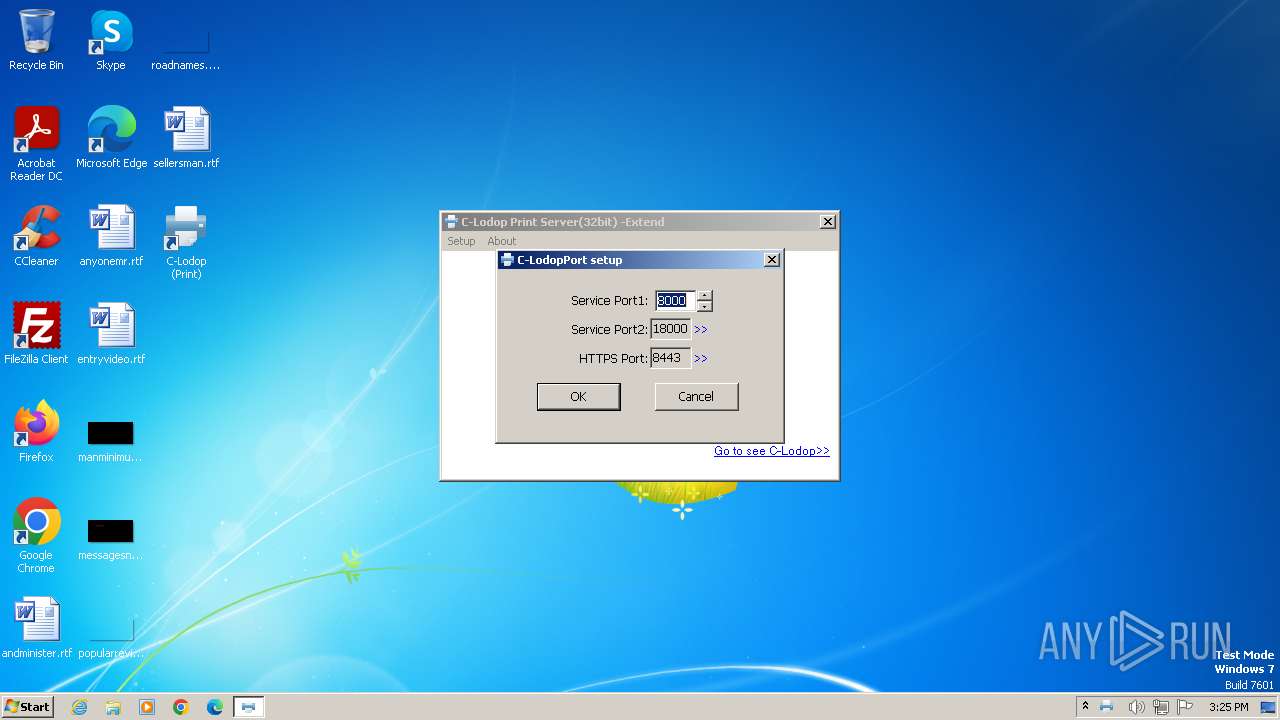
| 1988 | "C:\Program Files\MountTaiSoftware\CLodop32\CLodopPrint32.exe" setup_noauto | C:\Program Files\MountTaiSoftware\CLodop32\CLodopPrint32.exe | is-BEEOG.tmp | ||||||||||||
User: admin Company: (中国)梦泰尔软件 MTSoftware(CN) Integrity Level: HIGH Description: Web打印服务C-Lodop Exit code: 0 Version: 4.1.0.4 Modules
| |||||||||||||||
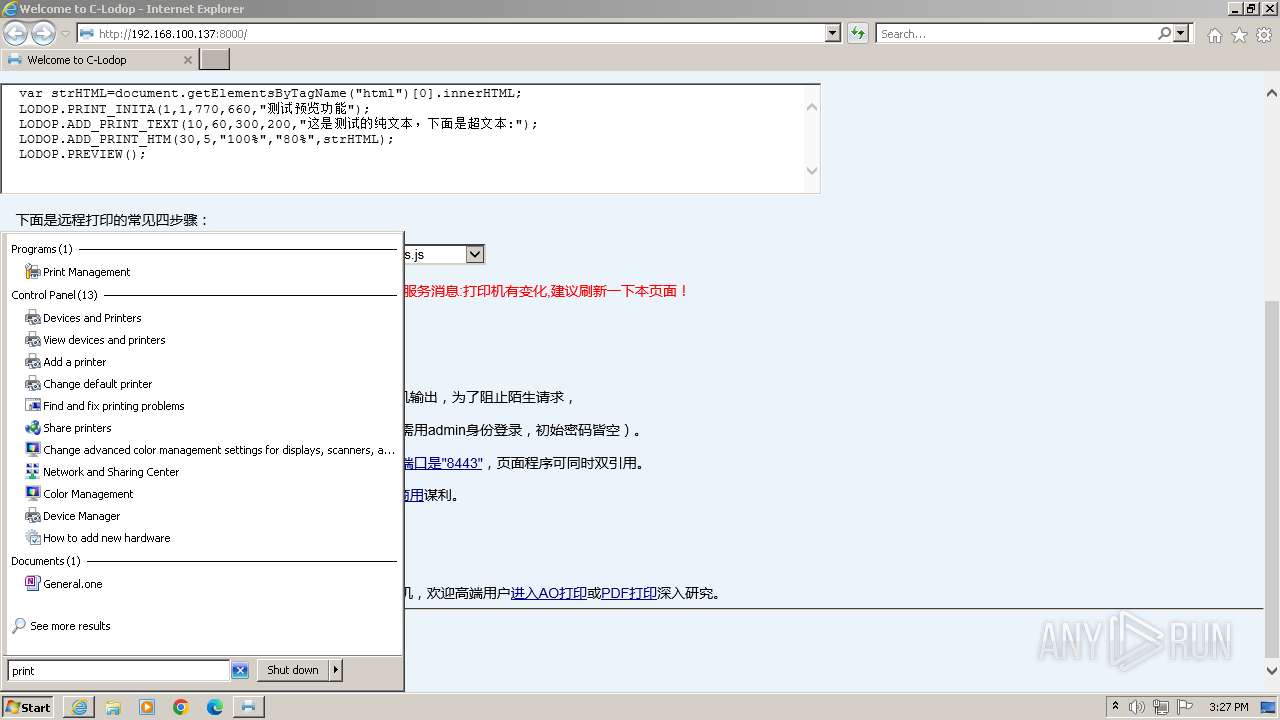
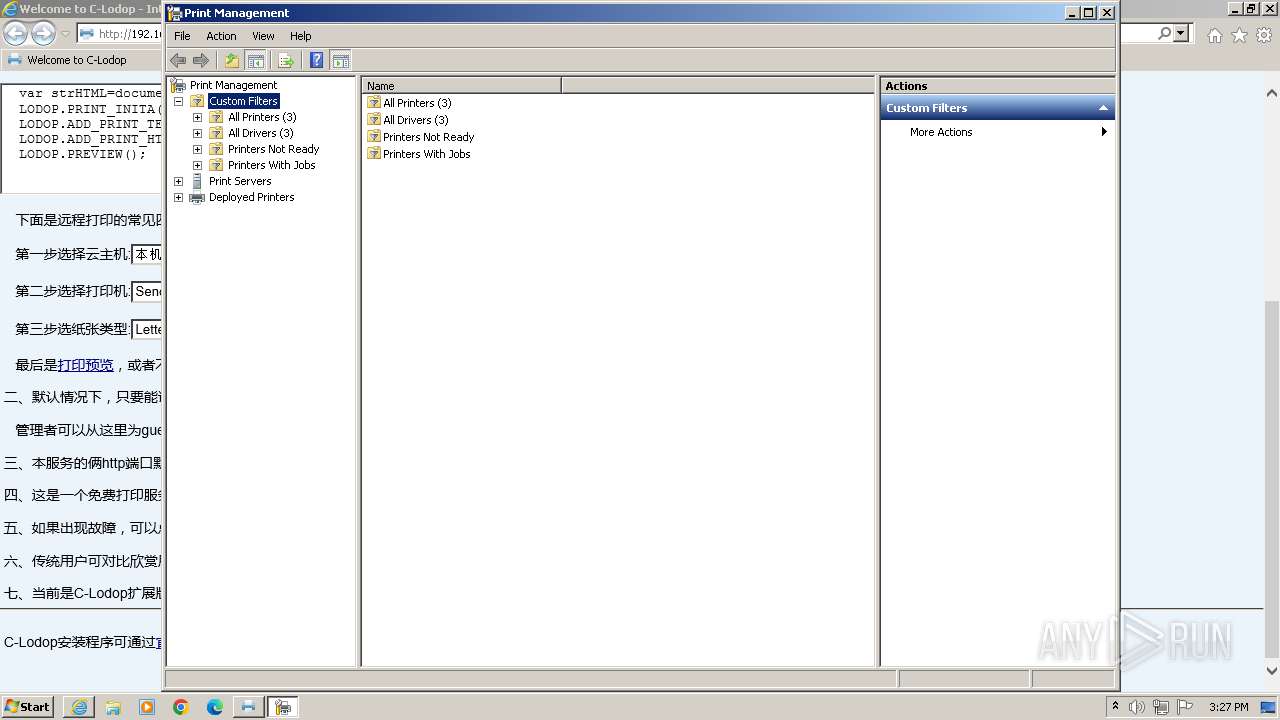
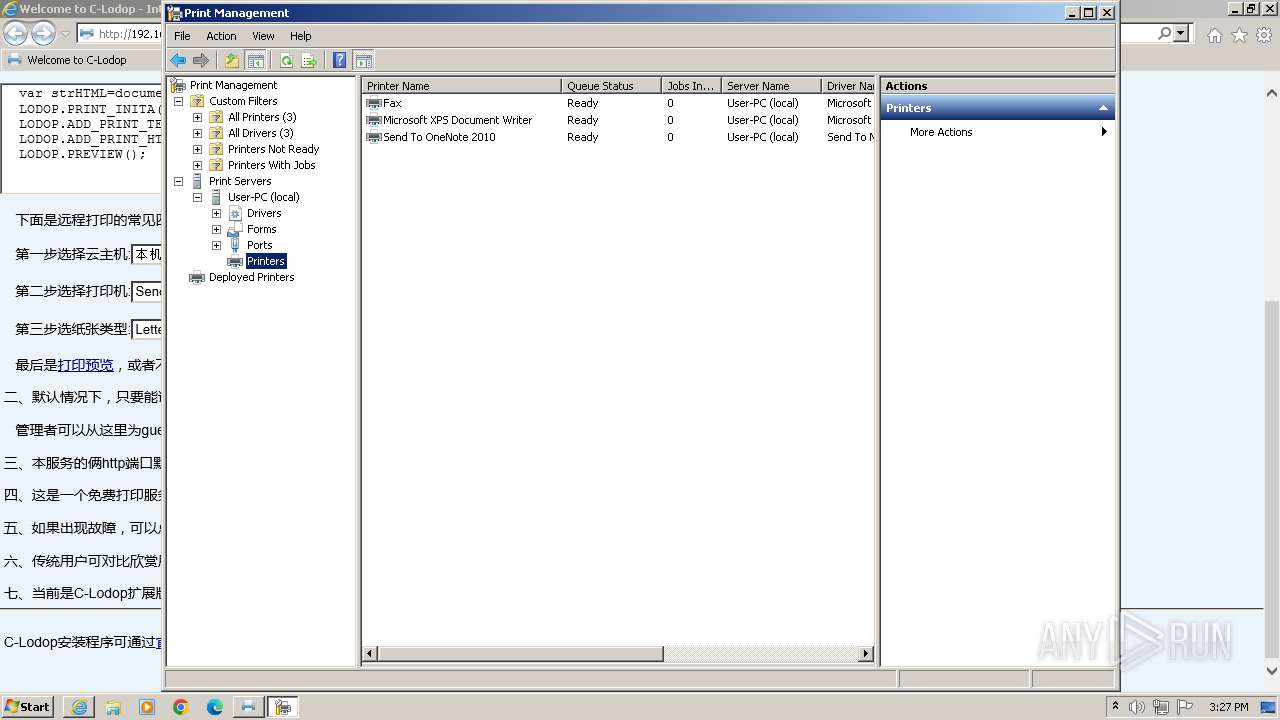
| 2168 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\printmanagement.msc" | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2600 | "C:\Users\admin\AppData\Local\Temp\is-R47CG.tmp\is-BEEOG.tmp" /SL4 $1C0142 "C:\Users\admin\AppData\Local\Temp\CLodop_Setup_for_Win32NT_4.102.exe" 4302233 51200 | C:\Users\admin\AppData\Local\Temp\is-R47CG.tmp\is-BEEOG.tmp | — | CLodop_Setup_for_Win32NT_4.102.exe | |||||||||||
User: admin Integrity Level: HIGH Description: 安装/卸载 Exit code: 0 Version: 51.46.0.0 Modules
| |||||||||||||||
| 2996 | "C:\Program Files\MountTaiSoftware\CLodop32\CLodopPrint32_backup.exe" | C:\Program Files\MountTaiSoftware\CLodop32\CLodopPrint32_backup.exe | — | CLodopPrint32.exe | |||||||||||
User: admin Company: (中国)梦泰尔软件 MTSoftware(CN) Integrity Level: HIGH Description: Web打印服务C-Lodop Exit code: 0 Version: 4.1.0.4 Modules
| |||||||||||||||
| 3240 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\printmanagement.msc" | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3264 | "C:\Users\admin\AppData\Local\Temp\CLodop_Setup_for_Win32NT_4.102.exe" | C:\Users\admin\AppData\Local\Temp\CLodop_Setup_for_Win32NT_4.102.exe | — | explorer.exe | |||||||||||
User: admin Company: MTSoftware(CN) Integrity Level: MEDIUM Description: C-Lodop(32-bit) Setup Exit code: 3221226540 Version: 4.1.0.4 Modules
| |||||||||||||||
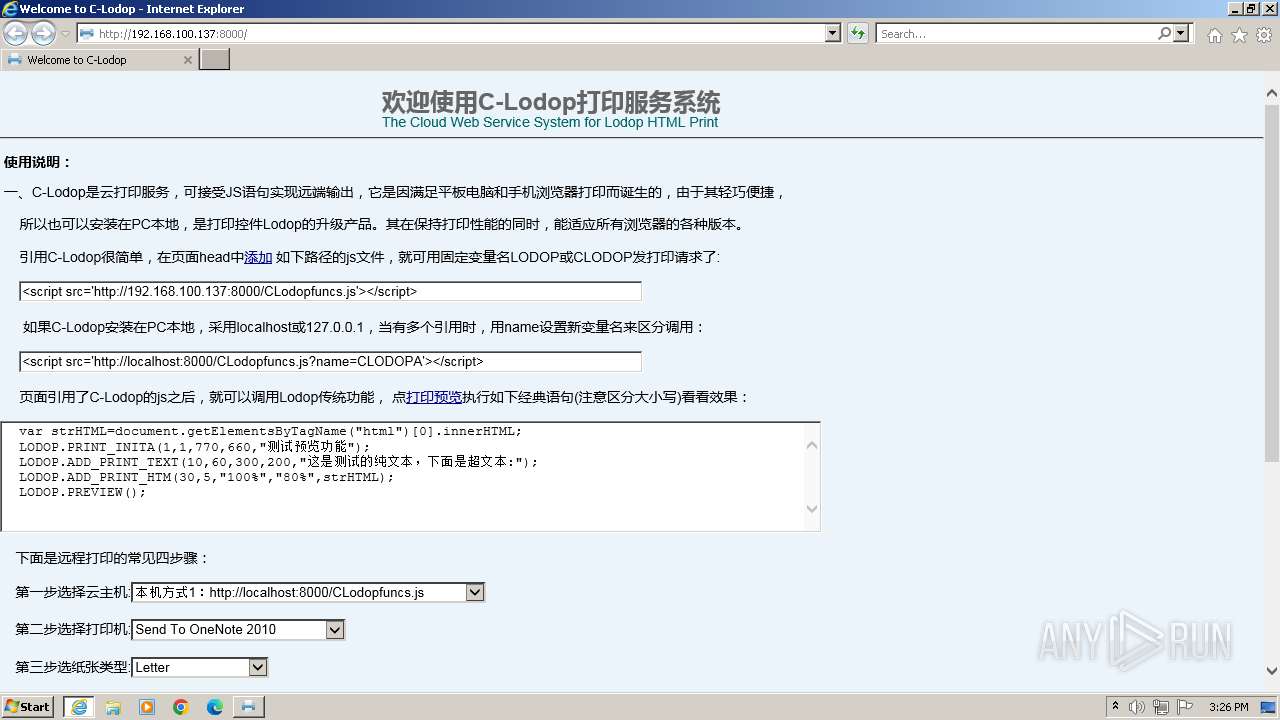
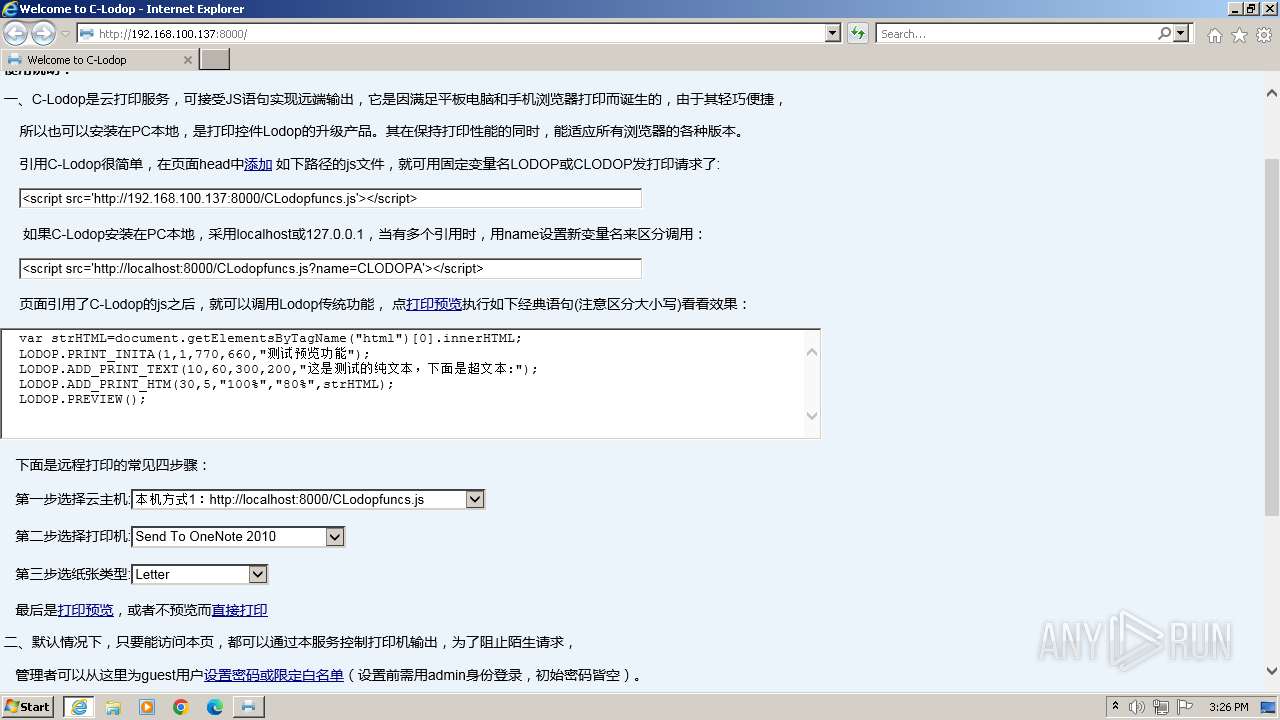
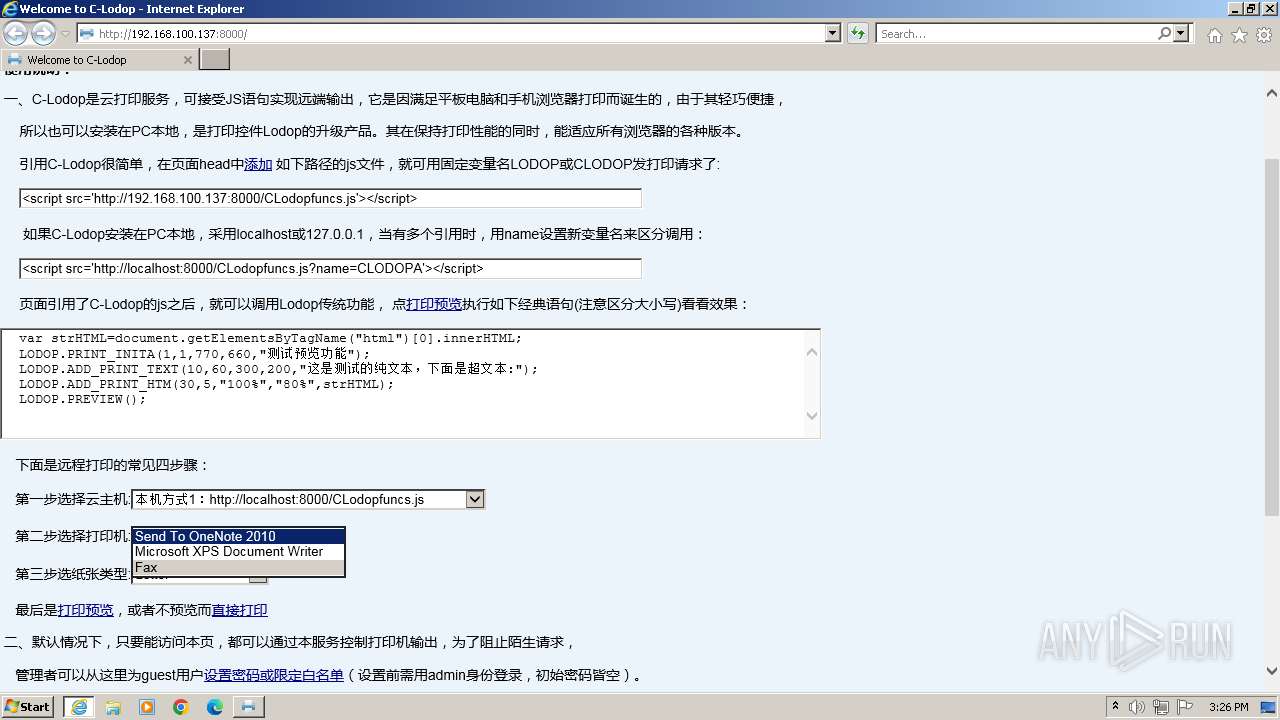
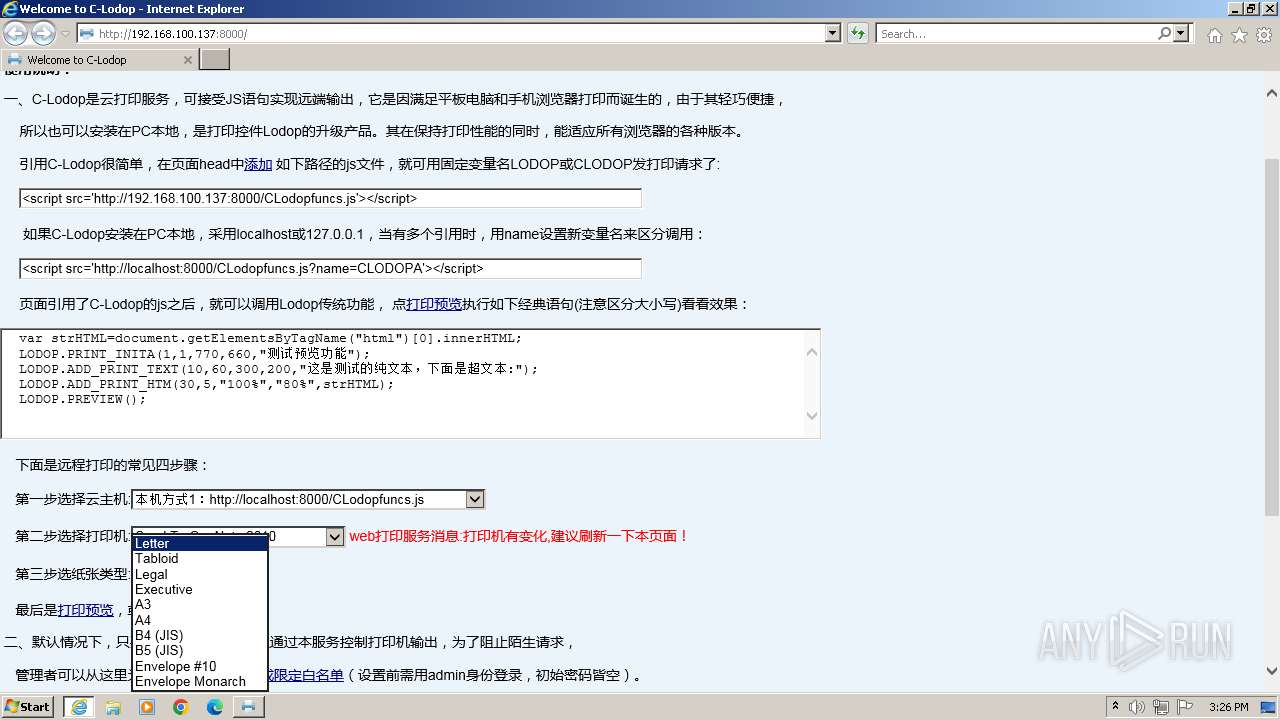
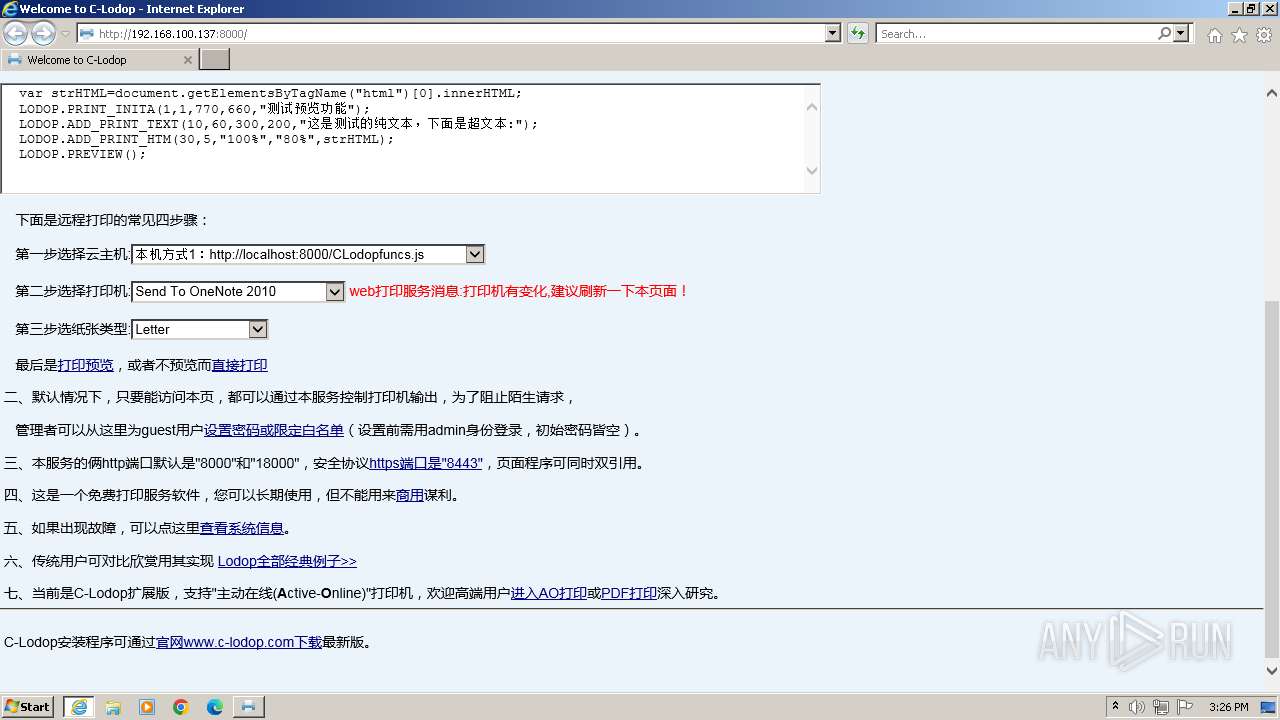
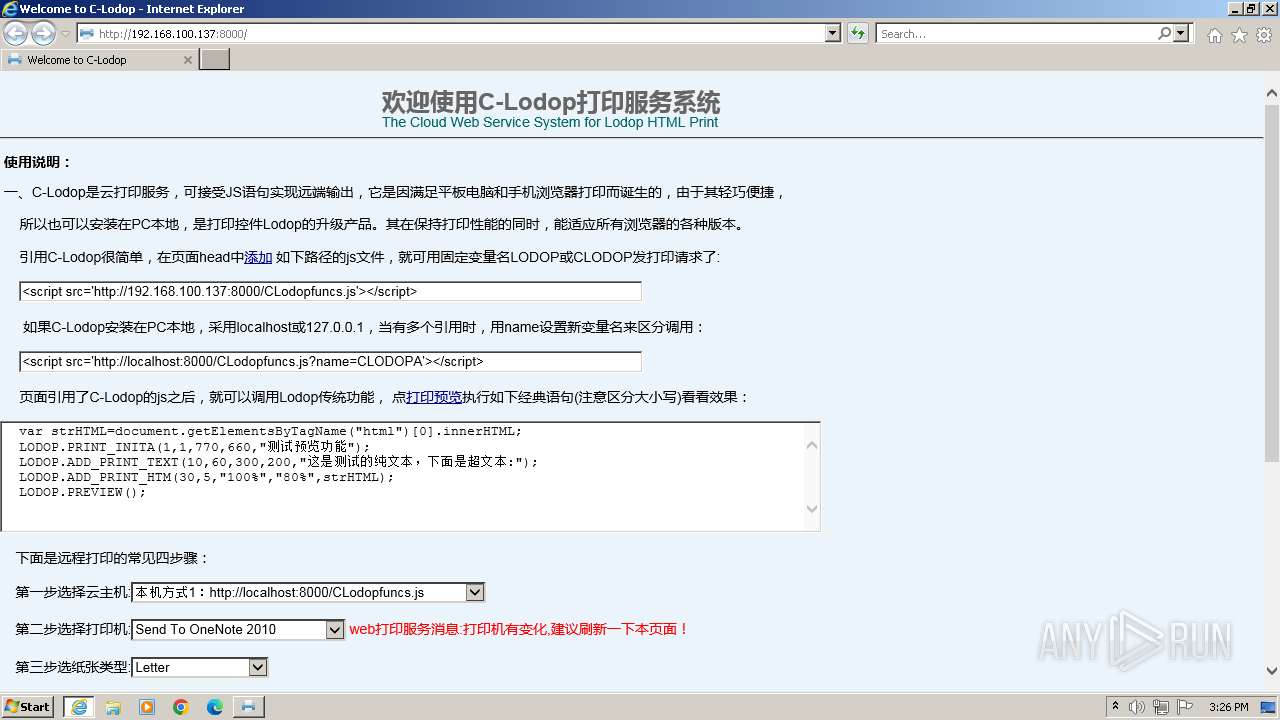
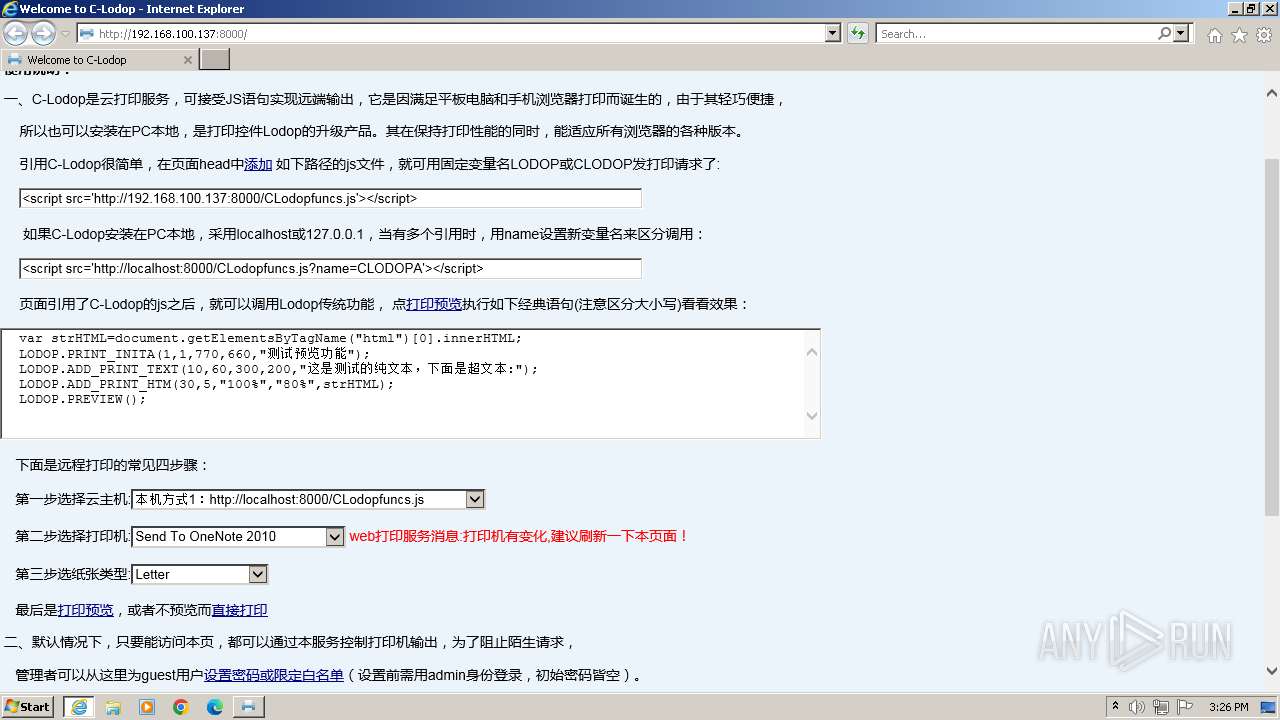
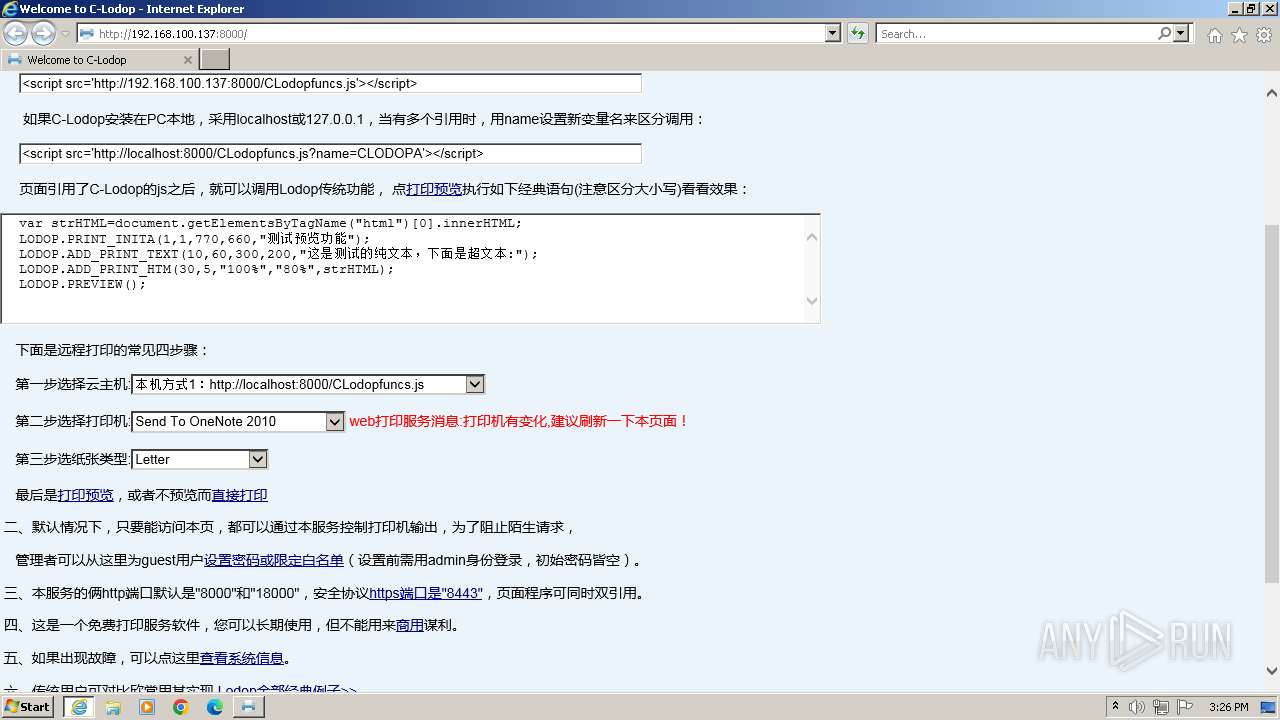
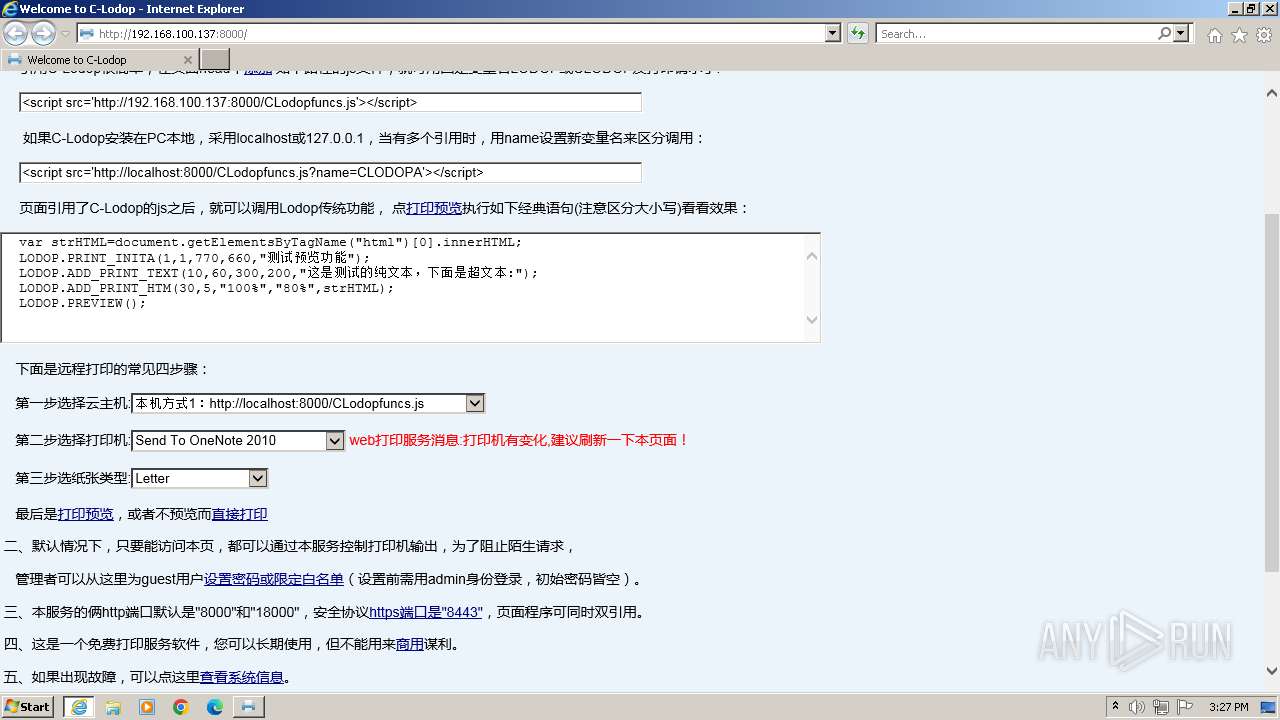
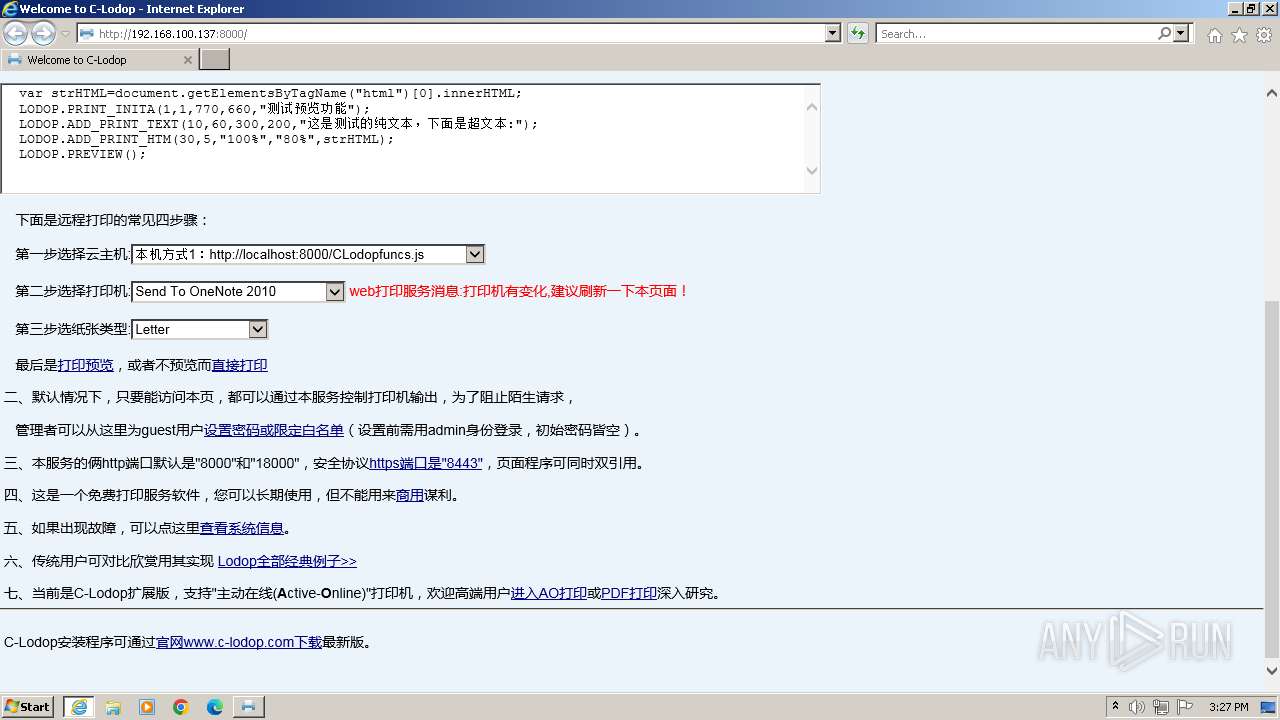
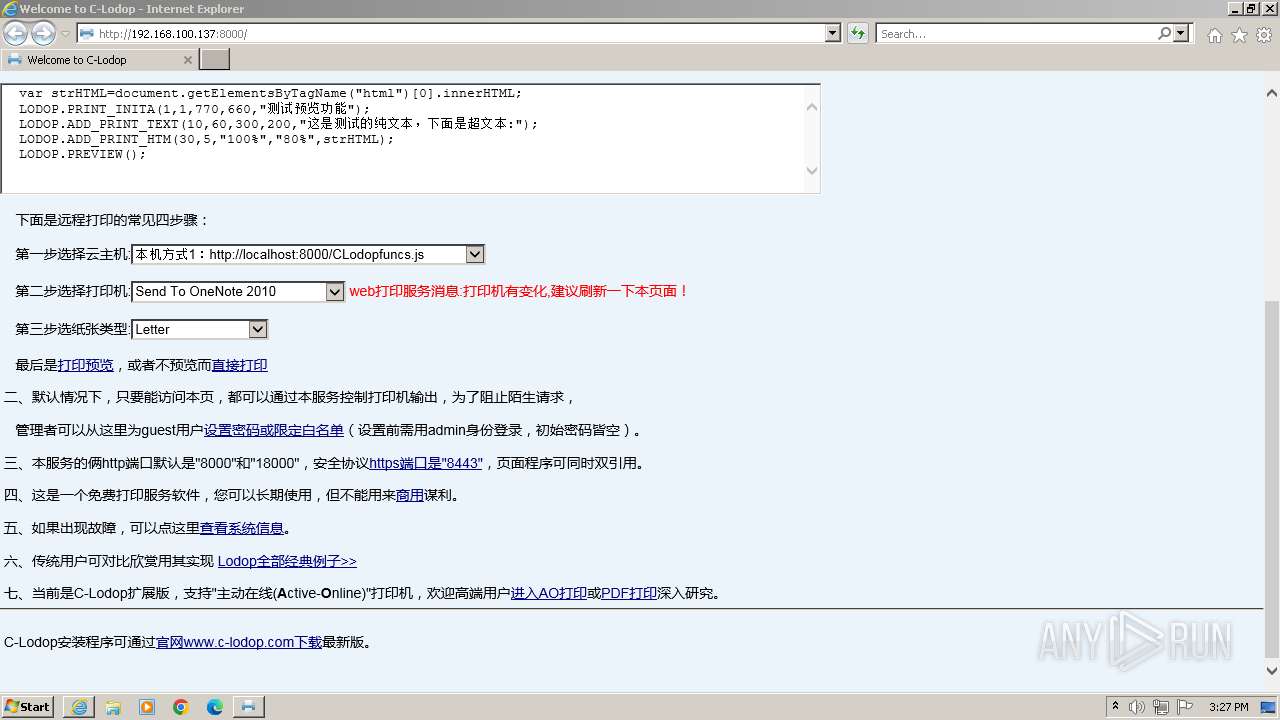
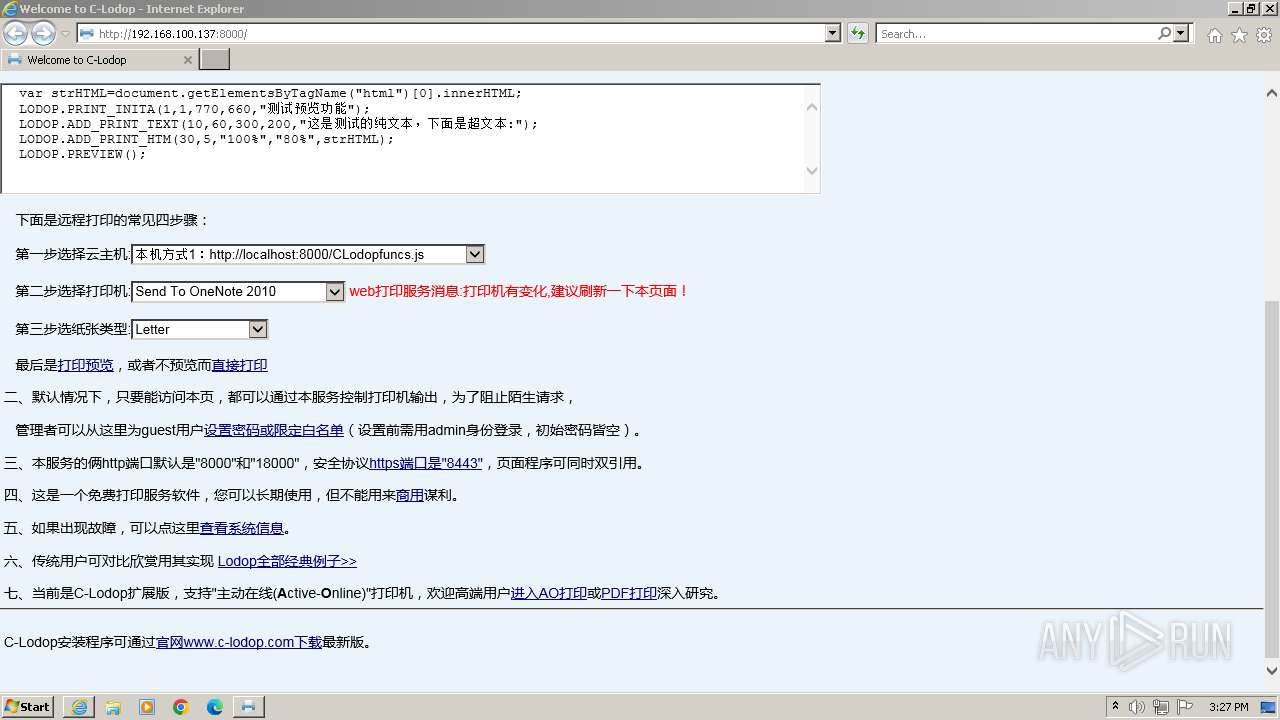
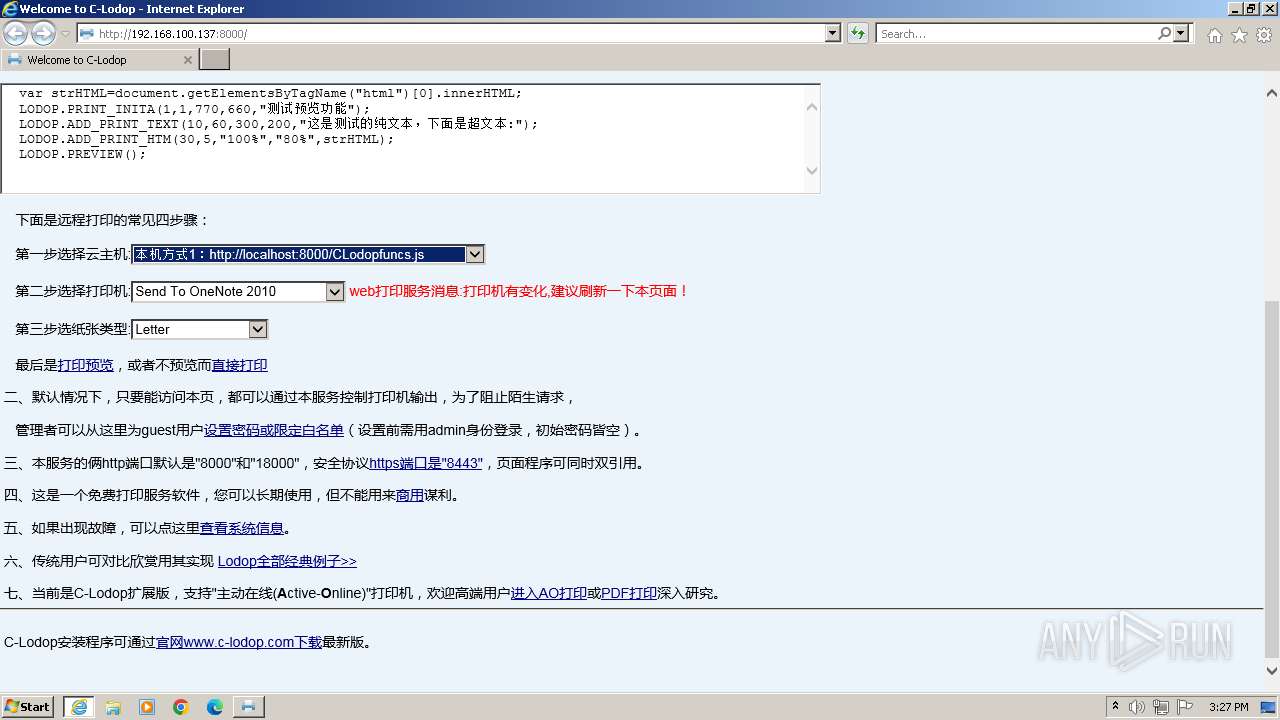
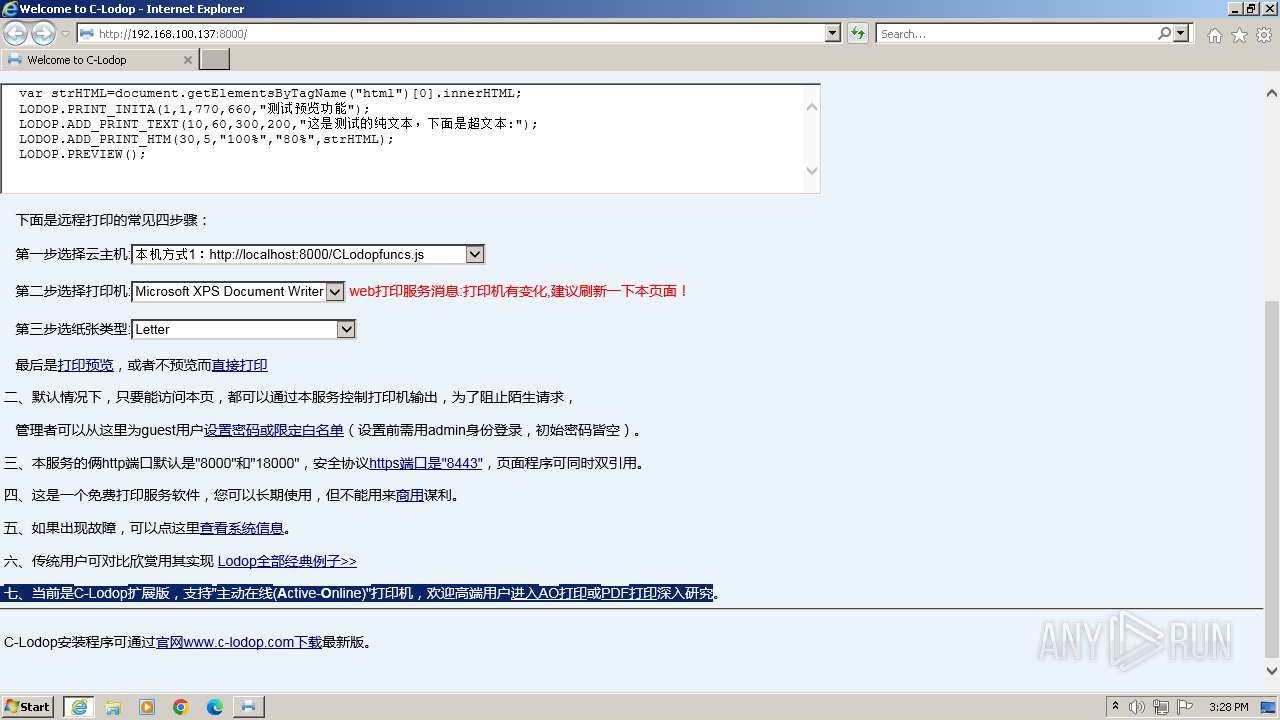
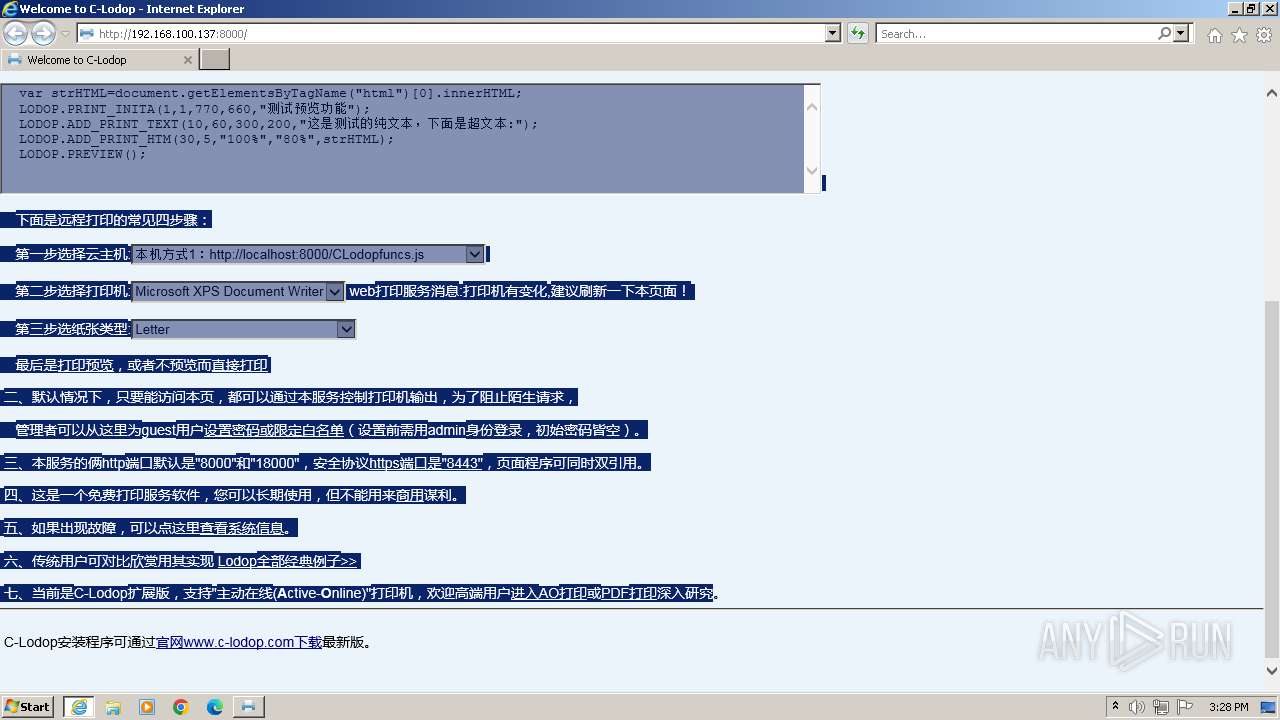
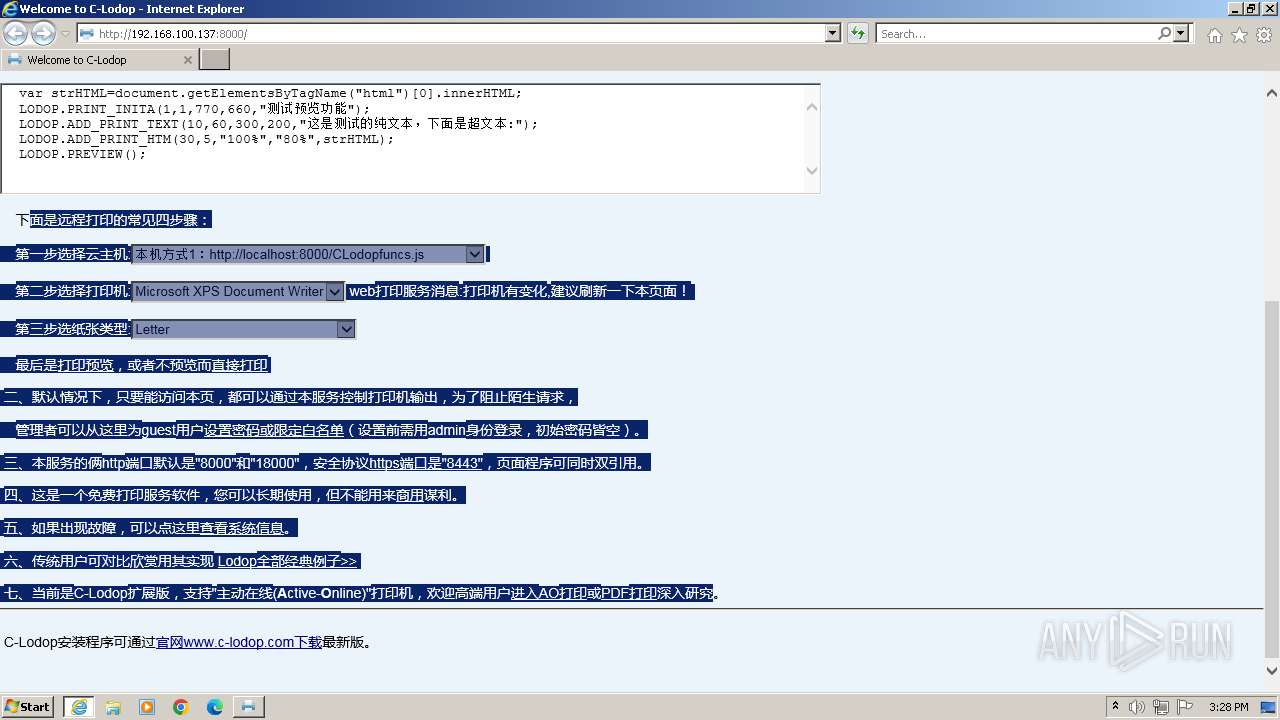
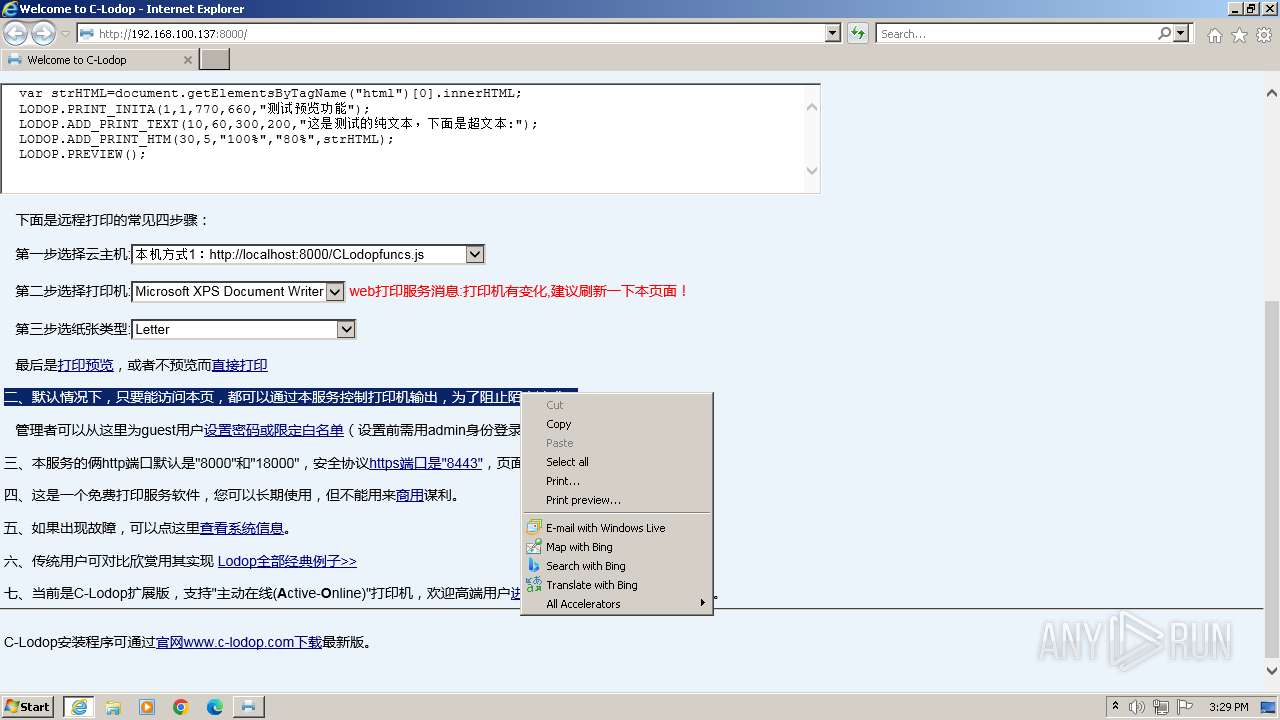
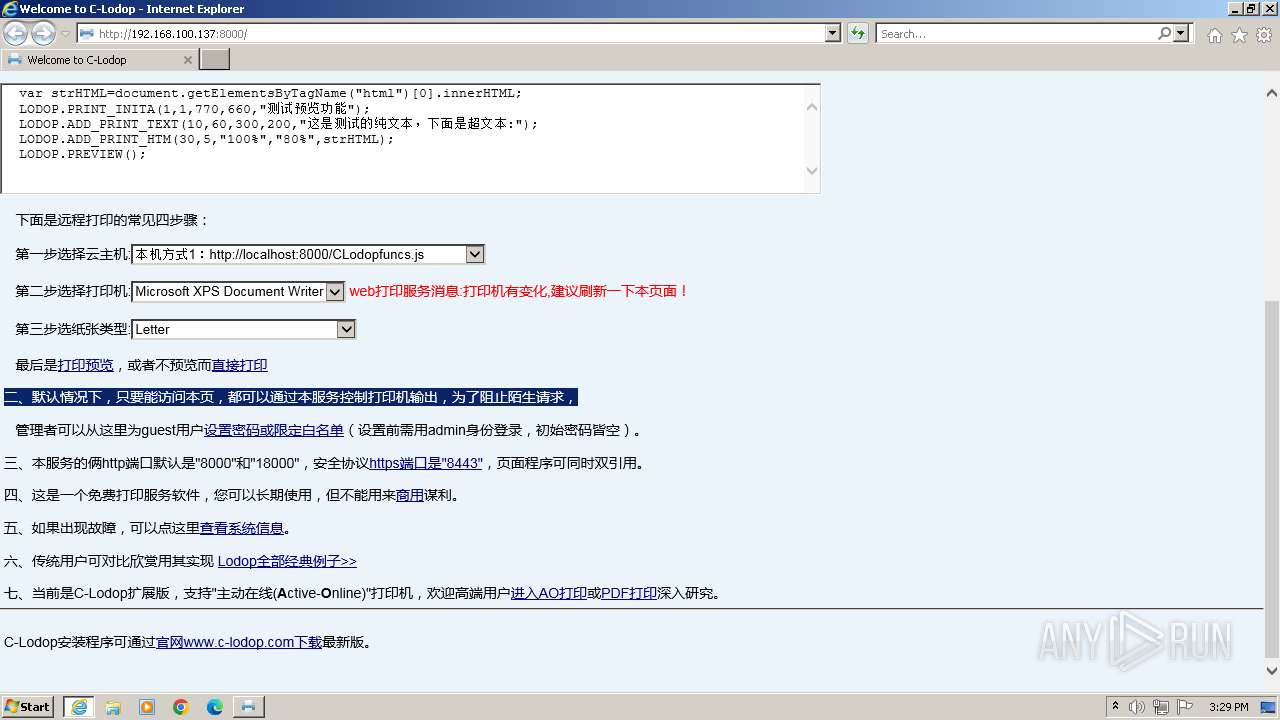
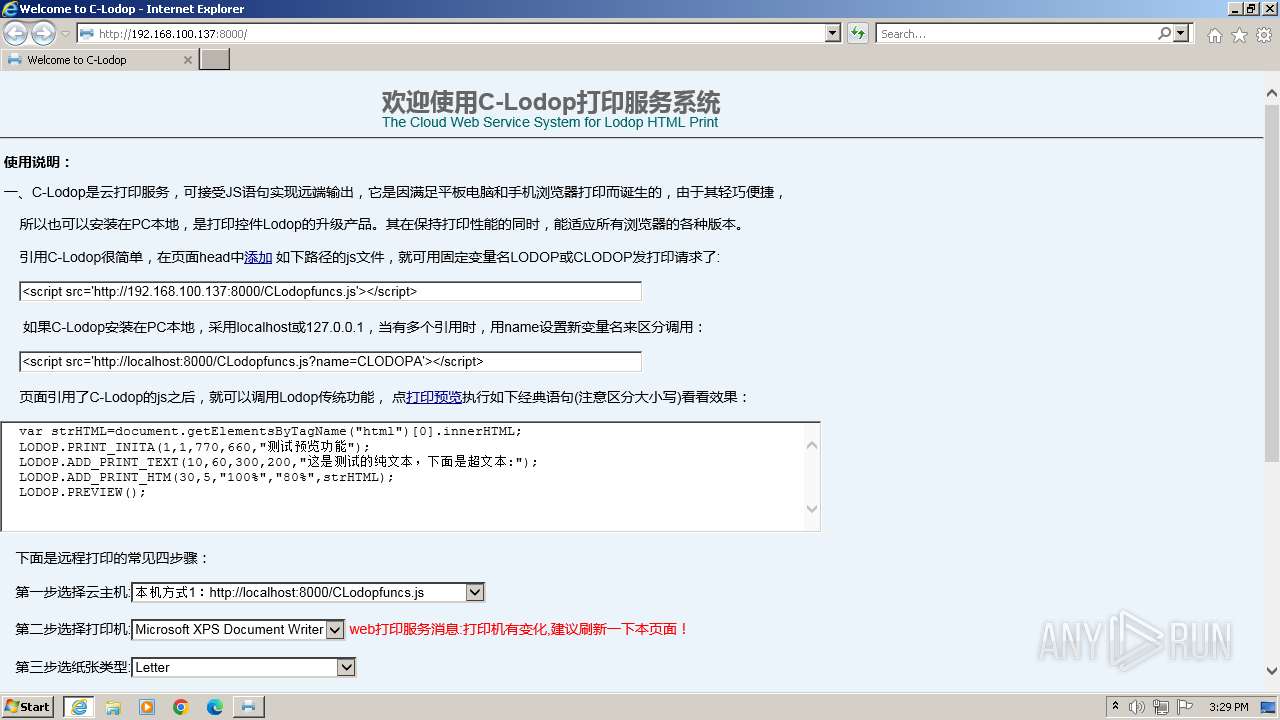
| 3492 | "C:\Program Files\Internet Explorer\iexplore.exe" http://192.168.100.137:8000 | C:\Program Files\Internet Explorer\iexplore.exe | CLodopPrint32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3528 | "C:\Program Files\MountTaiSoftware\CLodop32\CLodopPrint32_backup.exe" | C:\Program Files\MountTaiSoftware\CLodop32\CLodopPrint32_backup.exe | CLodopPrint32.exe | ||||||||||||
User: admin Company: (中国)梦泰尔软件 MTSoftware(CN) Integrity Level: HIGH Description: Web打印服务C-Lodop Exit code: 0 Version: 4.1.0.4 Modules
| |||||||||||||||
Total events
15 834
Read events
15 720
Write events
113
Delete events
1
Modification events
| (PID) Process: | (1988) CLodopPrint32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLodop.protocol |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (1988) CLodopPrint32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLodop.protocol\Application |
| Operation: | write | Name: | ApplicationName |
Value: Web打印服务C-Lodop | |||
| (PID) Process: | (1988) CLodopPrint32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLodop.protocol\Application |
| Operation: | write | Name: | ApplicationCompany |
Value: MTSoftware | |||
| (PID) Process: | (1988) CLodopPrint32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLodop.protocol\Application |
| Operation: | write | Name: | ApplicationDescription |
Value: Web打印服务C-Lodop | |||
| (PID) Process: | (1988) CLodopPrint32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLodop.protocol\Application |
| Operation: | write | Name: | ApplicationIcon |
Value: C:\Program Files\MountTaiSoftware\CLodop32\CLodopPrint32.exe,0 | |||
| (PID) Process: | (1988) CLodopPrint32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1988) CLodopPrint32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1988) CLodopPrint32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1988) CLodopPrint32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
Executable files
19
Suspicious files
22
Text files
151
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | is-BEEOG.tmp | C:\Users\admin\AppData\Local\Temp\is-PGNK4.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 2600 | is-BEEOG.tmp | C:\Program Files\MountTaiSoftware\CLodop32\SSL\is-FOST3.tmp | — | |
MD5:— | SHA256:— | |||
| 2600 | is-BEEOG.tmp | C:\Program Files\MountTaiSoftware\CLodop32\SSL\localhost_c_bak.pem | — | |
MD5:— | SHA256:— | |||
| 2600 | is-BEEOG.tmp | C:\Program Files\MountTaiSoftware\CLodop32\SSL\is-962T6.tmp | — | |
MD5:— | SHA256:— | |||
| 2600 | is-BEEOG.tmp | C:\Program Files\MountTaiSoftware\CLodop32\SSL\localhost_c_bak.key | — | |
MD5:— | SHA256:— | |||
| 1344 | CLodop_Setup_for_Win32NT_4.102.exe | C:\Users\admin\AppData\Local\Temp\is-R47CG.tmp\is-BEEOG.tmp | executable | |
MD5:79551E7F460CE4A92B6C9C0F0B714108 | SHA256:06AE7ABCEC424F92569CD67E55E27C7E91F84F6108F91876CD3F135262341BEF | |||
| 2600 | is-BEEOG.tmp | C:\Program Files\MountTaiSoftware\CLodop32\is-R5K0F.tmp | executable | |
MD5:2976C5EBBFD55691CCE2527B7E6C8308 | SHA256:6630790AF959021AF2C50405DD40FBF6BF283DD04E0622A8BFE5A69CA5BAB496 | |||
| 2600 | is-BEEOG.tmp | C:\Program Files\MountTaiSoftware\CLodop32\is-MPI3J.tmp | executable | |
MD5:E479394A699363D869DB4B12E135FA4B | SHA256:36C6757A0277A98E1E07E52065A67CF8B06C75E109EAB509533290D79C929DF5 | |||
| 2600 | is-BEEOG.tmp | C:\Program Files\MountTaiSoftware\CLodop32\MSVCR100.DLL | executable | |
MD5:67EC459E42D3081DD8FD34356F7CAFC1 | SHA256:1221A09484964A6F38AF5E34EE292B9AFEFCCB3DC6E55435FD3AAF7C235D9067 | |||
| 2600 | is-BEEOG.tmp | C:\Program Files\MountTaiSoftware\CLodop32\CLodopPrint32.exe | executable | |
MD5:D2FB89B2FF3316182A5AF04C2AD79115 | SHA256:C5990D0C4FFB1DA0EF5916A629D3F12730703F8468E60CF203712A0C4EE4D47B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
21
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3492 | iexplore.exe | GET | 200 | 184.24.77.184:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a5c05099bb80df53 | unknown | compressed | 4.66 Kb | unknown |
3492 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
1988 | CLodopPrint32.exe | GET | 200 | 121.196.197.102:80 | http://ssl.lodop.net/localhost_c_date | unknown | text | 10 b | unknown |
3492 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e0032a321da2bdc4 | unknown | compressed | 65.2 Kb | unknown |
3492 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
3492 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
3492 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1988 | CLodopPrint32.exe | 121.196.197.102:80 | ssl.lodop.net | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3492 | iexplore.exe | 23.212.110.160:443 | www.bing.com | Akamai International B.V. | CZ | unknown |
3492 | iexplore.exe | 184.24.77.184:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3492 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3492 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
4016 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ssl.lodop.net |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |