| File name: | 322d183f55d629ffaad41fdb10ec48b9.doc |
| Full analysis: | https://app.any.run/tasks/3a1a715d-2028-4df7-897e-8f4f32688f06 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | April 25, 2019, 08:20:43 |
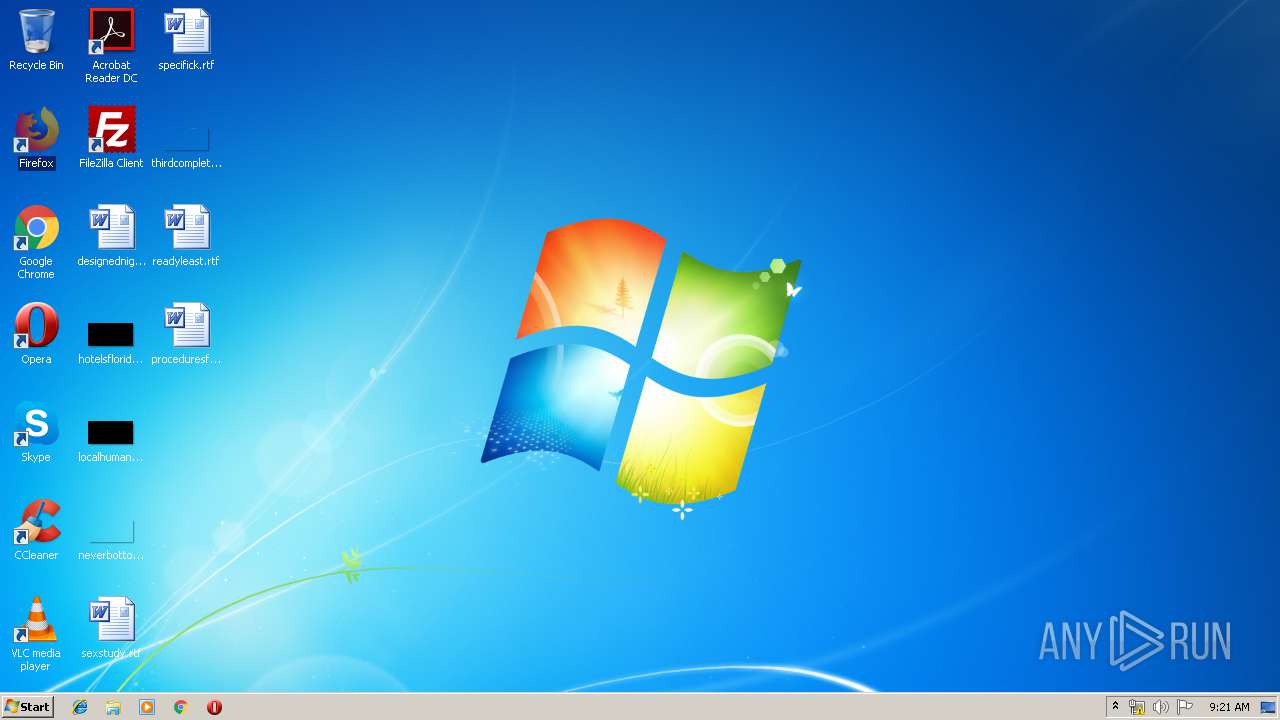
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
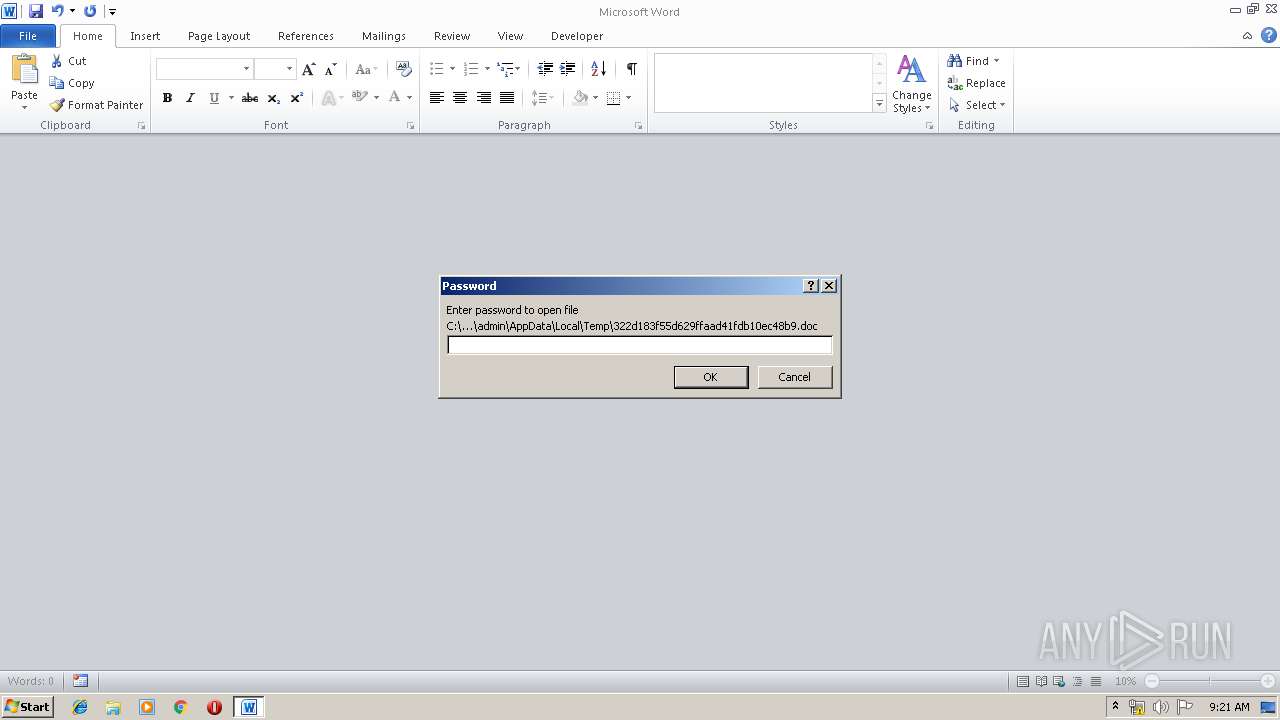
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | 322D183F55D629FFAAD41FDB10EC48B9 |
| SHA1: | 92EBAB7A11247622EA63B572F0D409292576ACE2 |
| SHA256: | D590B0F0F349C759FCBA252474EADFA401677C2D214B7E3572C3964B6D890FA1 |
| SSDEEP: | 3072:AB4IgEY12E1k4hDu5pbRNIC06xHDTHaOkayR+hzCOZxNJhotB8pD8:A5gEWDu5BRNV0W/HaOkeXVoTQ |
MALICIOUS
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2188)
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 2188)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2188)
Changes the Startup folder
- REG.exe (PID: 2616)
Application was dropped or rewritten from another process
- vuyj43.tmp (PID: 3116)
- cmualrc.exe (PID: 2580)
Connects to CnC server
- cmualrc.exe (PID: 2580)
AMADEY was detected
- cmualrc.exe (PID: 2580)
SUSPICIOUS
Starts application with an unusual extension
- WINWORD.EXE (PID: 2188)
Starts itself from another location
- vuyj43.tmp (PID: 3116)
Connects to server without host name
- cmualrc.exe (PID: 2580)
Creates files in the program directory
- vuyj43.tmp (PID: 3116)
Uses REG.EXE to modify Windows registry
- cmualrc.exe (PID: 2580)
Executable content was dropped or overwritten
- vuyj43.tmp (PID: 3116)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2188)
Creates files in the user directory
- WINWORD.EXE (PID: 2188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2188 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\322d183f55d629ffaad41fdb10ec48b9.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2580 | c:\programdata\189fecf19f\cmualrc.exe | c:\programdata\189fecf19f\cmualrc.exe | vuyj43.tmp | ||||||||||||
User: admin Company: Wargaming.net Integrity Level: MEDIUM Description: Pendedit Didntw Flex Ice Recrdsets Attained Exit code: 0 Version: 5.4.22.5 Modules
| |||||||||||||||
| 2616 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /f /v Startup /t REG_SZ /d C:\ProgramData\189fecf19f | C:\Windows\system32\REG.exe | cmualrc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3116 | C:\Users\admin\AppData\Local\Temp\vuyj43.tmp | C:\Users\admin\AppData\Local\Temp\vuyj43.tmp | WINWORD.EXE | ||||||||||||
User: admin Company: Wargaming.net Integrity Level: MEDIUM Description: Pendedit Didntw Flex Ice Recrdsets Attained Exit code: 0 Version: 5.4.22.5 Modules
| |||||||||||||||
Total events
1 137
Read events
803
Write events
329
Delete events
5
Modification events
| (PID) Process: | (2188) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | t68 |
Value: 743638008C080000010000000000000000000000 | |||
| (PID) Process: | (2188) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2188) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2188) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318649886 | |||
| (PID) Process: | (2188) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318650000 | |||
| (PID) Process: | (2188) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318650001 | |||
| (PID) Process: | (2188) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 8C080000A2891CD33FFBD40100000000 | |||
| (PID) Process: | (2188) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | x88 |
Value: 783838008C08000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2188) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | x88 |
Value: 783838008C08000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2188) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5EF4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFB2E9EACC76FBDB7E.TMP | — | |
MD5:— | SHA256:— | |||
| 2188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFCCBA8F649568E324.TMP | — | |
MD5:— | SHA256:— | |||
| 2188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF222B272C38E70211.TMP | — | |
MD5:— | SHA256:— | |||
| 2188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF1D35CFF4A202107E.TMP | — | |
MD5:— | SHA256:— | |||
| 2188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF91E4B65ADEABA51.TMP | — | |
MD5:— | SHA256:— | |||
| 2188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF1416DE074DAD05C6.TMP | — | |
MD5:— | SHA256:— | |||
| 3116 | vuyj43.tmp | C:\ProgramData\0 | — | |
MD5:— | SHA256:— | |||
| 3116 | vuyj43.tmp | C:\programdata\189fecf19f\cmualrc.exe:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2580 | cmualrc.exe | C:\ProgramData\0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
1
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2580 | cmualrc.exe | POST | 200 | 142.93.231.106:80 | http://142.93.231.106/ppk/index.php | CA | text | 6 b | malicious |
2580 | cmualrc.exe | POST | 200 | 142.93.231.106:80 | http://142.93.231.106/ppk/index.php | CA | text | 6 b | malicious |
2580 | cmualrc.exe | POST | 200 | 142.93.231.106:80 | http://142.93.231.106/ppk/index.php | CA | text | 6 b | malicious |
2188 | WINWORD.EXE | GET | 200 | 87.98.158.248:80 | http://achmannatgagamico.info/word77.tmp | FR | executable | 588 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2580 | cmualrc.exe | 142.93.231.106:80 | — | — | CA | malicious |
2188 | WINWORD.EXE | 87.98.158.248:80 | achmannatgagamico.info | OVH SAS | FR | suspicious |
— | — | 142.93.231.106:80 | — | — | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
achmannatgagamico.info |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2188 | WINWORD.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2188 | WINWORD.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
2580 | cmualrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2580 | cmualrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2580 | cmualrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2580 | cmualrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2580 | cmualrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2580 | cmualrc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
3 ETPRO signatures available at the full report