| File name: | Dropper.exe |
| Full analysis: | https://app.any.run/tasks/0c4d972d-eb64-4a12-b31d-5a7a2d7df570 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | July 30, 2018, 12:24:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 95CD5029E310569A2730C863127B22E5 |
| SHA1: | 2929219D4F0725A78D560AD3351DE3FEFED5D9A2 |
| SHA256: | D58E07A9C3F5EE3DDBF2D4C5B657B67E6DB7722000EDCDC8D5CD92CB9A37845A |
| SSDEEP: | 12288:j/uLxn3yJ6DxKhsx5pAaldBqKPNIIRuVdQTZEFut5ZRZAemB92qN/3J9oOx/pUQO:t4OTUxV2K |
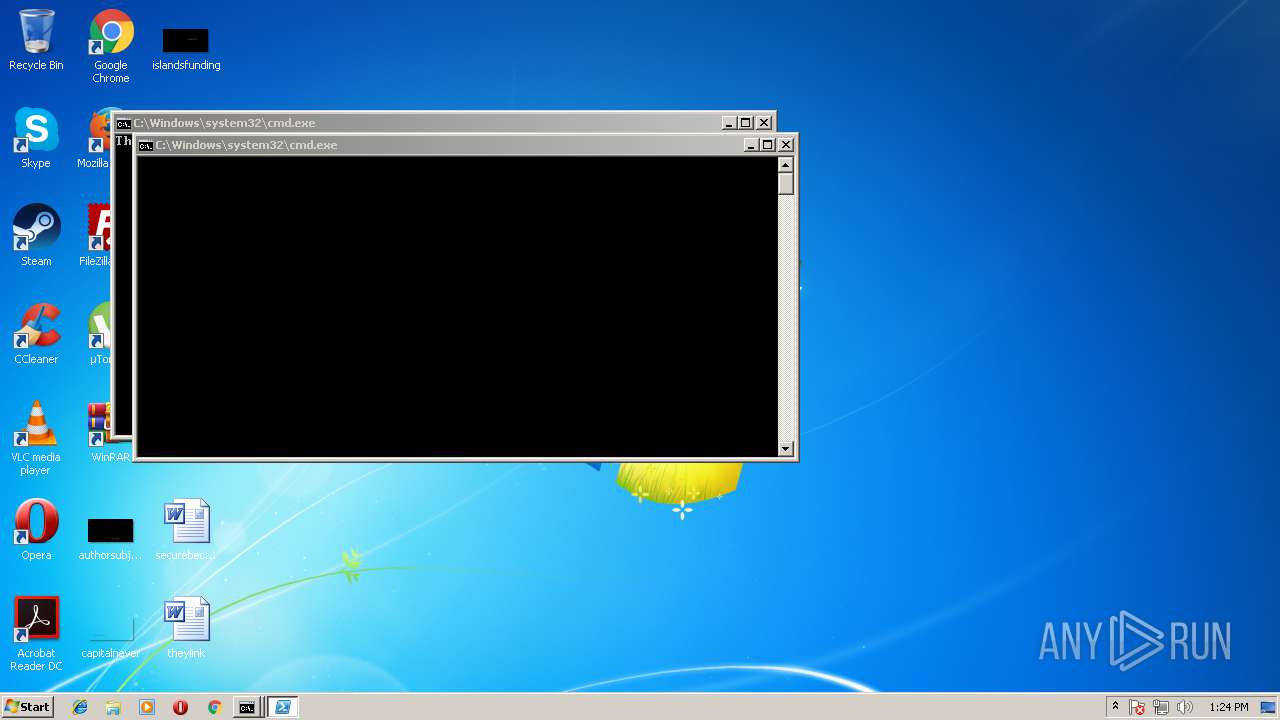
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2200)
Changes the autorun value in the registry
- reg.exe (PID: 1544)
- reg.exe (PID: 3780)
- reg.exe (PID: 2520)
- Windows Update.exe (PID: 2248)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3776)
- schtasks.exe (PID: 3876)
- schtasks.exe (PID: 3136)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3752)
- cmd.exe (PID: 3512)
- cmd.exe (PID: 2200)
Application was dropped or rewritten from another process
- rundll32.exe (PID: 616)
- Windows Update.exe (PID: 2248)
- MoneroMinerBuild.exe (PID: 2596)
Detected Hawkeye Keylogger
- Windows Update.exe (PID: 2248)
SUSPICIOUS
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3752)
- cmd.exe (PID: 3512)
- cmd.exe (PID: 2200)
Executes scripts
- Dropper.exe (PID: 1792)
- Windows Update.exe (PID: 2248)
Executable content was dropped or overwritten
- Dropper.exe (PID: 1792)
- MoneroMinerBuild.exe (PID: 2596)
- rundll32.exe (PID: 616)
- Windows Update.exe (PID: 2248)
Creates files in the user directory
- Dropper.exe (PID: 1792)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 2848)
- rundll32.exe (PID: 616)
- Windows Update.exe (PID: 2248)
Starts CMD.EXE for commands execution
- Dropper.exe (PID: 1792)
- WScript.exe (PID: 2672)
Executes PowerShell scripts
- MoneroMinerBuild.exe (PID: 2596)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2200)
Starts itself from another location
- rundll32.exe (PID: 616)
Checks for external IP
- Windows Update.exe (PID: 2248)
INFO
Dropped object may contain URL's
- MoneroMinerBuild.exe (PID: 2596)
- Dropper.exe (PID: 1792)
- rundll32.exe (PID: 616)
- Windows Update.exe (PID: 2248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (84.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
| .exe | | | Generic Win/DOS Executable (2) |
| .exe | | | DOS Executable Generic (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:01:16 01:01:02+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 4096 |
| InitializedDataSize: | 1560576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x104c |
| OSVersion: | 4 |
| ImageVersion: | 1.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.0.1 |
| ProductVersionNumber: | 1.1.0.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | BreakingSecurity.net |
| ProductName: | ViottoBinder_Stub |
| FileVersion: | 1.01.0001 |
| ProductVersion: | 1.01.0001 |
| InternalName: | ViottoBinder_Stub |
| OriginalFileName: | ViottoBinder_Stub.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jan-2016 00:01:02 |
| Detected languages: |
|
| CompanyName: | BreakingSecurity.net |
| ProductName: | ViottoBinder_Stub |
| FileVersion: | 1.01.0001 |
| ProductVersion: | 1.01.0001 |
| InternalName: | ViottoBinder_Stub |
| OriginalFilename: | ViottoBinder_Stub.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 16-Jan-2016 00:01:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000F24 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.37413 |
.data | 0x00002000 | 0x0000032C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00003000 | 0x0017CE90 | 0x0017D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.03999 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.25029 | 624 | Latin 1 / Western European | English - United States | RT_VERSION |
101 | 4.03791 | 1557766 | Latin 1 / Western European | UNKNOWN | CUSTOM |
30001 | 2.57965 | 304 | Latin 1 / Western European | UNKNOWN | RT_ICON |
30002 | 1.76987 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
30003 | 2.07177 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
58
Monitored processes
21
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Users\admin\AppData\Local\Temp\rundll32.exe" | C:\Users\admin\AppData\Local\Temp\rundll32.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Phulli Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1540 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /V "Avast" /t REG_SZ /F /D "C:\Users\admin\AppData\Roaming\chekin.bat" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1544 | reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run" /V "Avast" /t REG_SZ /F /D "C:\Users\admin\AppData\Roaming\checkin.bat" | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1792 | "C:\Users\admin\AppData\Local\Temp\Dropper.exe" | C:\Users\admin\AppData\Local\Temp\Dropper.exe | explorer.exe | ||||||||||||
User: admin Company: BreakingSecurity.net Integrity Level: MEDIUM Exit code: 0 Version: 1.01.0001 Modules
| |||||||||||||||
| 2200 | cmd /c ""C:\Users\admin\AppData\Roaming\chekin.bat" 0" | C:\Windows\system32\cmd.exe | — | Dropper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2232 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /V "Avast" /t REG_SZ /F /D "C:\Users\admin\AppData\Roaming\chekin.bat" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2248 | "C:\Users\admin\AppData\Roaming\Windows Update.exe" | C:\Users\admin\AppData\Roaming\Windows Update.exe | rundll32.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Phulli Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2520 | reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run" /V "Avast" /t REG_SZ /F /D "C:\Users\admin\AppData\Roaming\chekin.bat" | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2588 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holdermail.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | — | Windows Update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2596 | "C:\Users\admin\AppData\Local\Temp\MoneroMinerBuild.exe" 0 | C:\Users\admin\AppData\Local\Temp\MoneroMinerBuild.exe | Dropper.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
2 078
Read events
1 935
Write events
143
Delete events
0
Modification events
| (PID) Process: | (1792) Dropper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1792) Dropper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1544) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Avast |
Value: C:\Users\admin\AppData\Roaming\checkin.bat | |||
| (PID) Process: | (2672) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2672) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3332) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2848) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3780) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Avast |
Value: C:\Users\admin\AppData\Roaming\checkin.bat | |||
| (PID) Process: | (2520) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Avast |
Value: C:\Users\admin\AppData\Roaming\chekin.bat | |||
| (PID) Process: | (2848) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
4
Suspicious files
4
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\U11K24RYOT2L1DXUA0XI.temp | — | |
MD5:— | SHA256:— | |||
| 2848 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NQRI4ID6AKUCDIOXASYK.temp | — | |
MD5:— | SHA256:— | |||
| 1792 | Dropper.exe | C:\Users\admin\AppData\Roaming\chekin.bat | text | |
MD5:— | SHA256:— | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF4456b0.TMP | binary | |
MD5:— | SHA256:— | |||
| 1792 | Dropper.exe | C:\Users\admin\AppData\Roaming\regadd.bat | text | |
MD5:— | SHA256:— | |||
| 2596 | MoneroMinerBuild.exe | C:\Users\admin\AppData\Local\Temp\rundll32.exe | executable | |
MD5:— | SHA256:— | |||
| 2848 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2848 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF4456cf.TMP | binary | |
MD5:— | SHA256:— | |||
| 616 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\SysInfo.txt | text | |
MD5:— | SHA256:— | |||
| 616 | rundll32.exe | C:\Users\admin\AppData\Roaming\Windows Update.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2248 | Windows Update.exe | GET | 403 | 104.16.16.96:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2248 | Windows Update.exe | 104.16.16.96:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
whatismyipaddress.com |
| shared |