| download: | /dobre/splwow64.exe |
| Full analysis: | https://app.any.run/tasks/d651d60e-5fd3-4592-b5ec-5dde7fa12433 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | September 22, 2024, 19:56:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2B01C9B0C69F13DA5EE7889A4B17C45E |
| SHA1: | 27F0C1AE0DDEDDC9EFAC38BC473476B103FEF043 |
| SHA256: | D5526528363CEEB718D30BC669038759C4CD80A1D3E9C8C661B12B261DCC9E29 |
| SSDEEP: | 49152:xbJ5NYRgPOau6akedLowwEoE62lde2gje64fzvlTgR/LLiWaBWoKpl7mXLLiA6+0:xbJ5MgdZakcA1E6Gc7jgfcZaLM7mHiTh |
MALICIOUS
Create files in the Startup directory
- cmd.exe (PID: 2960)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 6344)
- channel3.exe (PID: 3768)
CRYPTBOT has been detected (SURICATA)
- channel3.exe (PID: 3768)
Connects to the CnC server
- channel3.exe (PID: 3768)
- Waters.pif (PID: 5500)
- RegAsm.exe (PID: 6660)
CRYPTBOT has been detected (YARA)
- channel3.exe (PID: 3768)
AMADEY has been detected (SURICATA)
- Waters.pif (PID: 5500)
PRIVATELOADER has been detected (SURICATA)
- RegAsm.exe (PID: 6660)
VIDAR has been detected (YARA)
- RegAsm.exe (PID: 448)
VIDAR has been detected (SURICATA)
- RegAsm.exe (PID: 448)
Stealers network behavior
- RegAsm.exe (PID: 448)
SUSPICIOUS
Executing commands from a ".bat" file
- splwow64.exe (PID: 6592)
Reads security settings of Internet Explorer
- splwow64.exe (PID: 6592)
Starts CMD.EXE for commands execution
- splwow64.exe (PID: 6592)
- cmd.exe (PID: 1432)
Get information on the list of running processes
- cmd.exe (PID: 1432)
Application launched itself
- cmd.exe (PID: 1432)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1432)
Executable content was dropped or overwritten
- cmd.exe (PID: 1432)
- t6hkrxrh.exe (PID: 2064)
- Waters.pif (PID: 5500)
- RegAsm.exe (PID: 6660)
The executable file from the user directory is run by the CMD process
- Waters.pif (PID: 5500)
Starts application with an unusual extension
- cmd.exe (PID: 1432)
- wscript.exe (PID: 6668)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 1432)
Connects to the server without a host name
- RegAsm.exe (PID: 6660)
- Waters.pif (PID: 5500)
Potential Corporate Privacy Violation
- Waters.pif (PID: 5500)
- RegAsm.exe (PID: 6660)
Checks for external IP
- svchost.exe (PID: 2256)
- RegAsm.exe (PID: 6660)
Process requests binary or script from the Internet
- RegAsm.exe (PID: 6660)
Contacting a server suspected of hosting an CnC
- Waters.pif (PID: 5500)
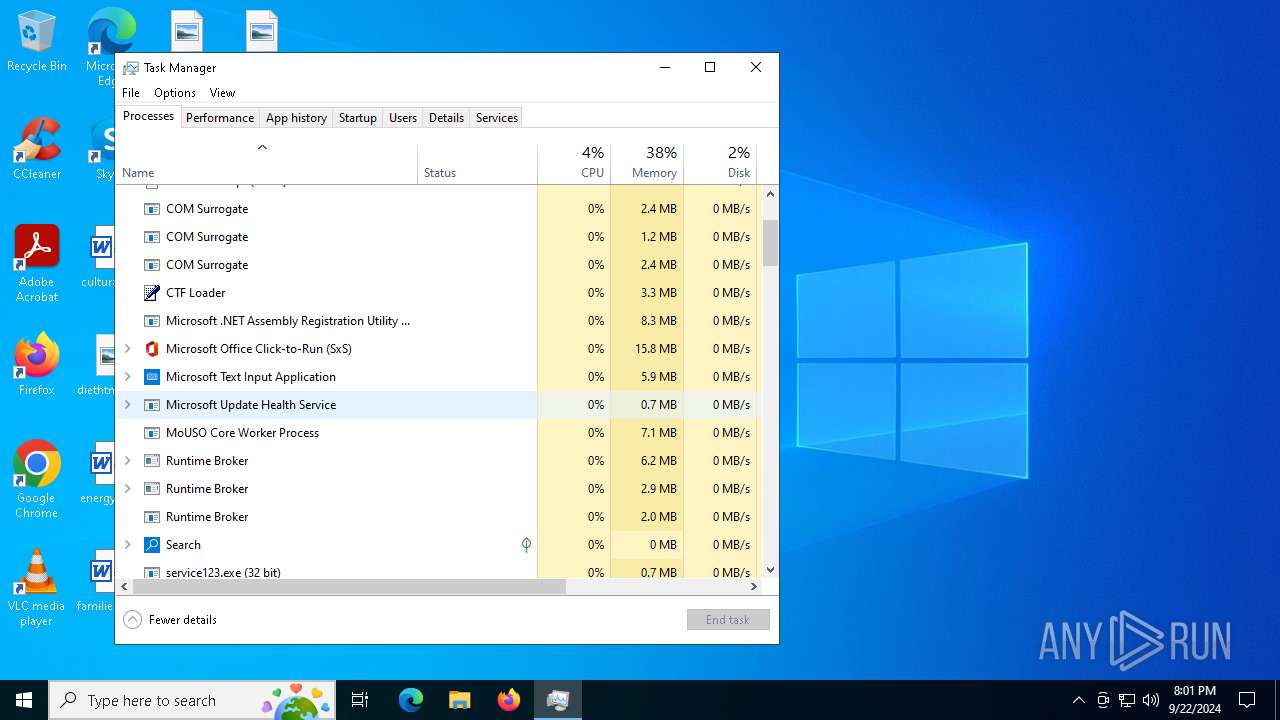
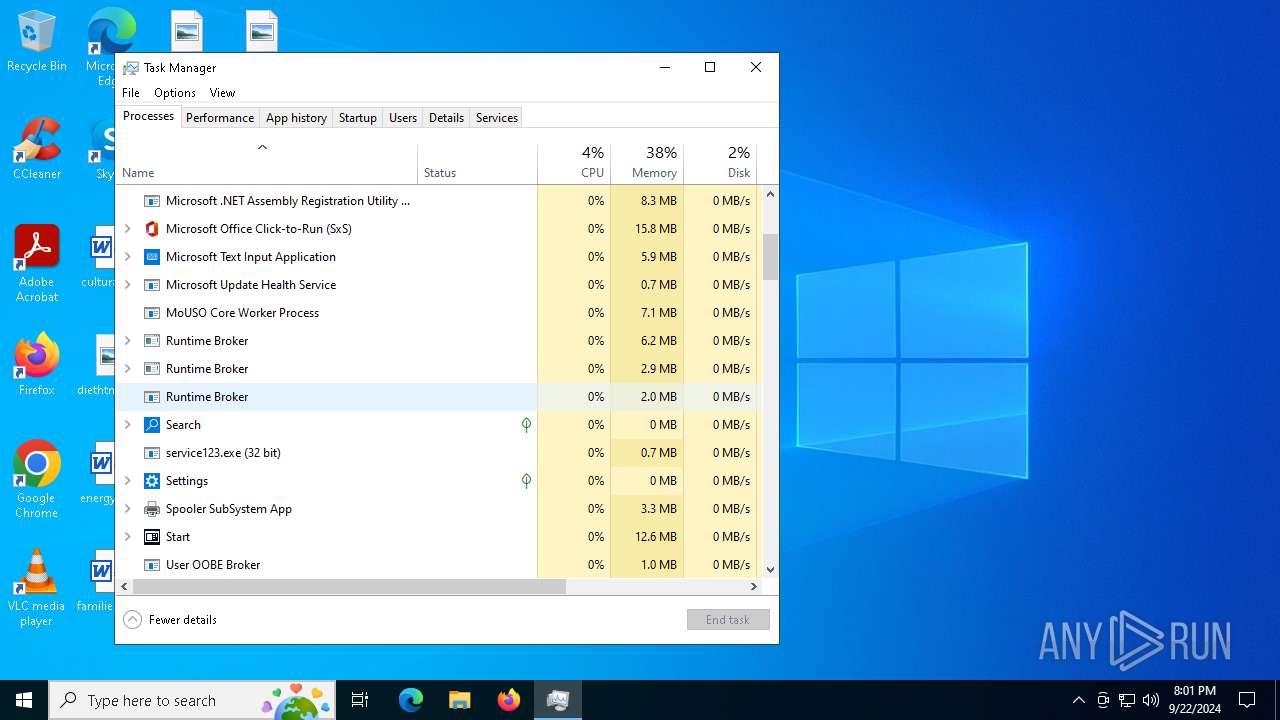
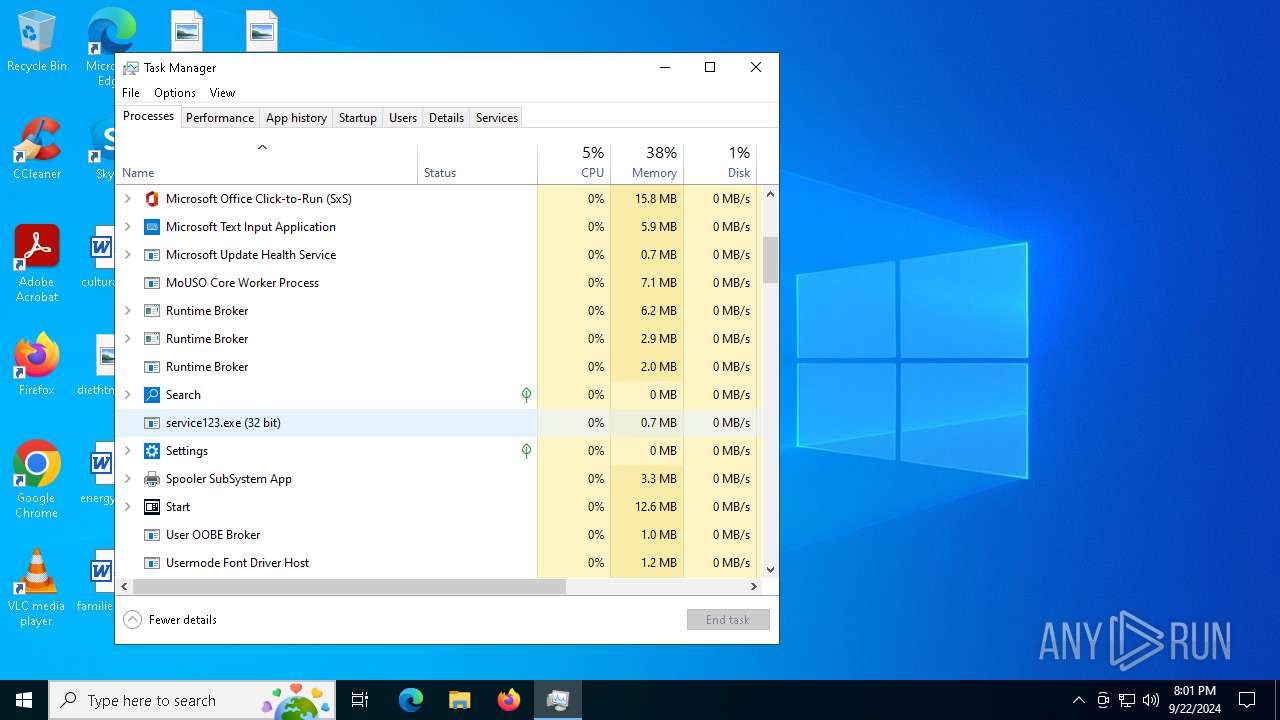
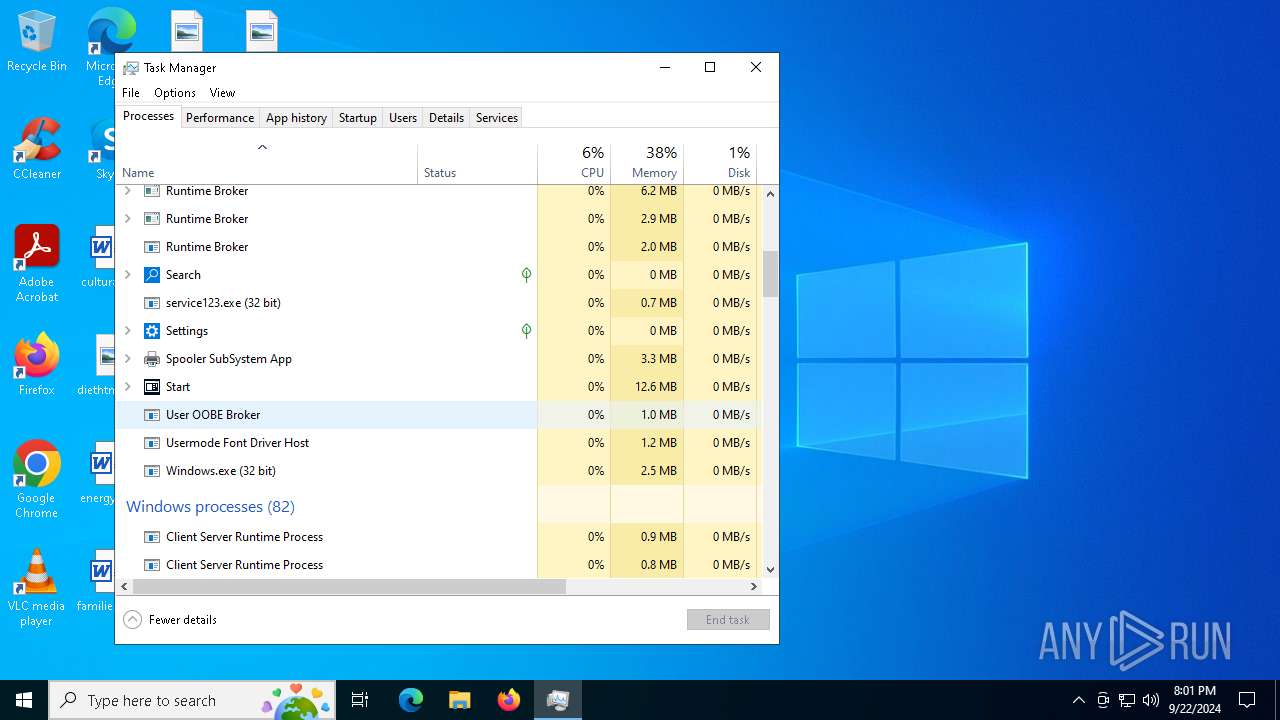
The process executes via Task Scheduler
- service123.exe (PID: 4060)
- service123.exe (PID: 7084)
- service123.exe (PID: 752)
- wscript.exe (PID: 6668)
Found regular expressions for crypto-addresses (YARA)
- service123.exe (PID: 6356)
INFO
Checks supported languages
- splwow64.exe (PID: 6592)
- Waters.pif (PID: 5500)
Process checks computer location settings
- splwow64.exe (PID: 6592)
Create files in a temporary directory
- splwow64.exe (PID: 6592)
The process uses the downloaded file
- splwow64.exe (PID: 6592)
Reads the computer name
- splwow64.exe (PID: 6592)
- Waters.pif (PID: 5500)
Reads mouse settings
- Waters.pif (PID: 5500)
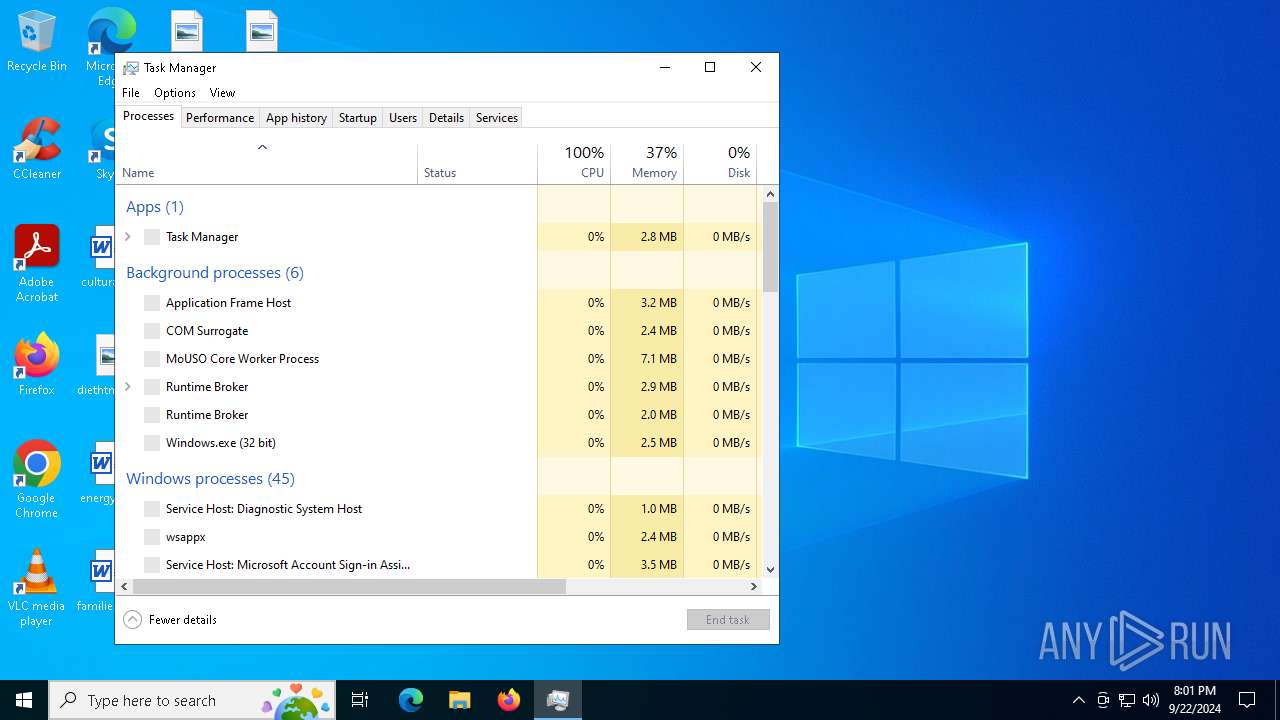
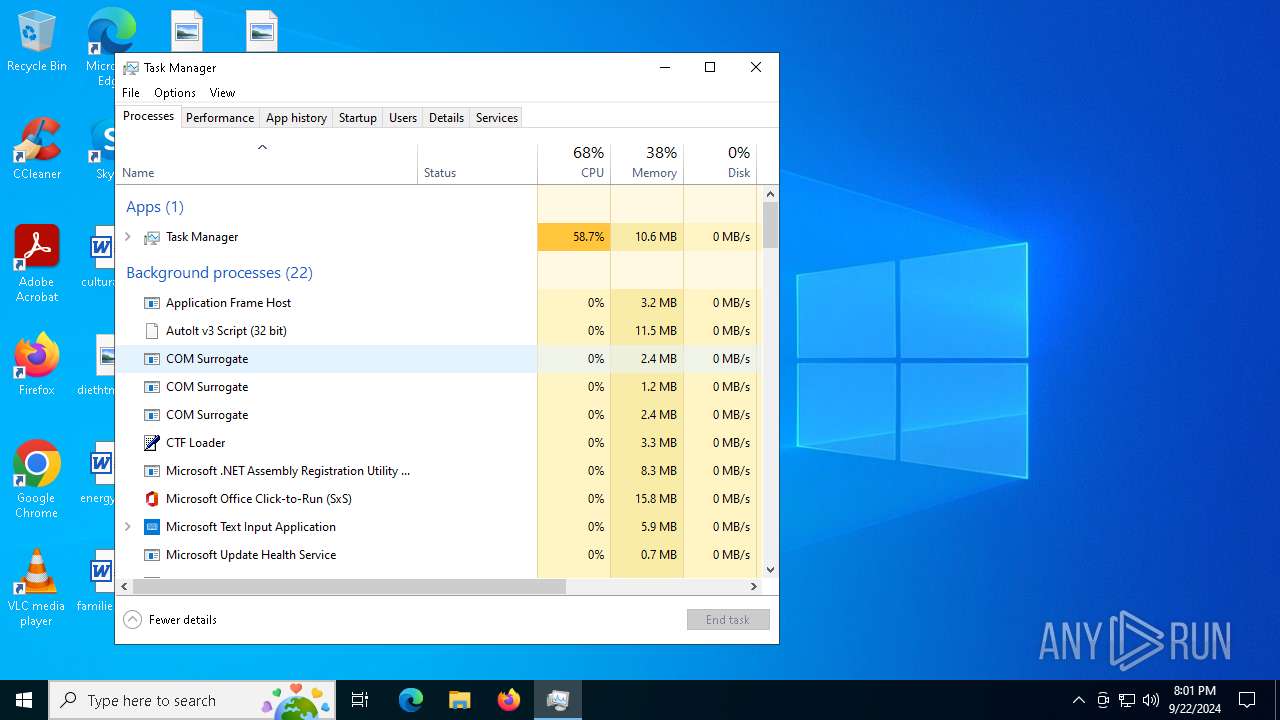
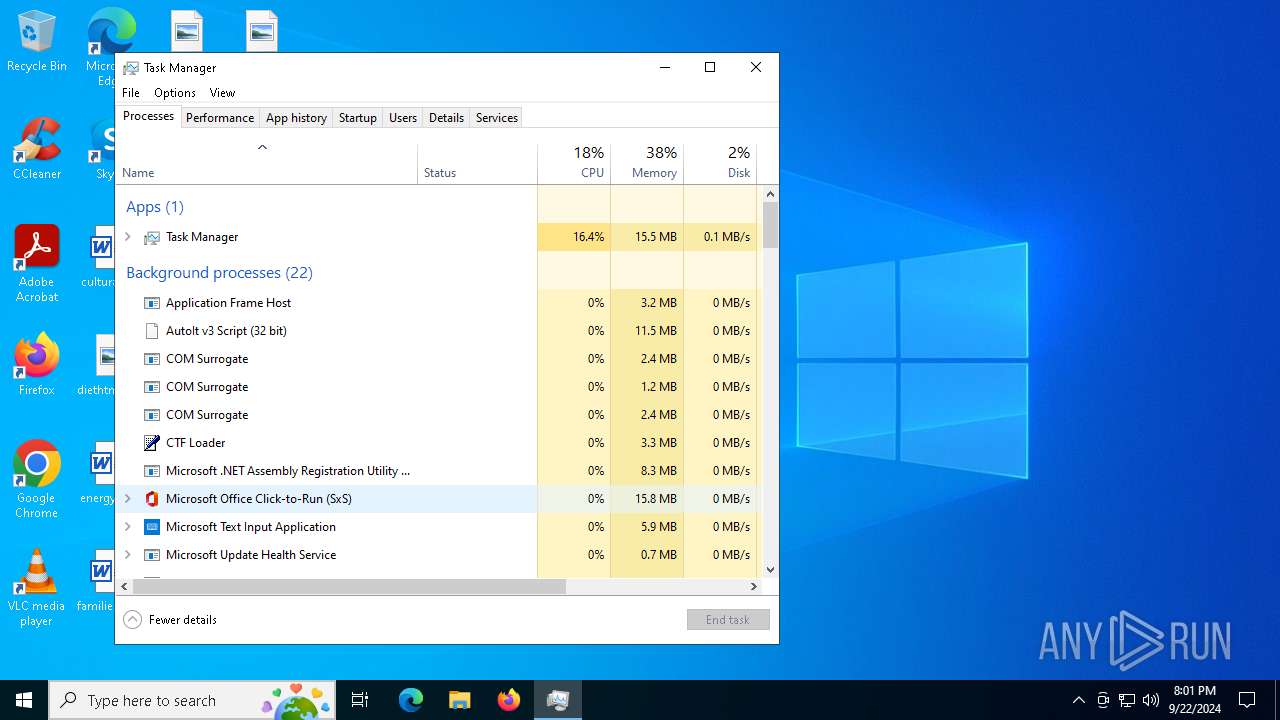
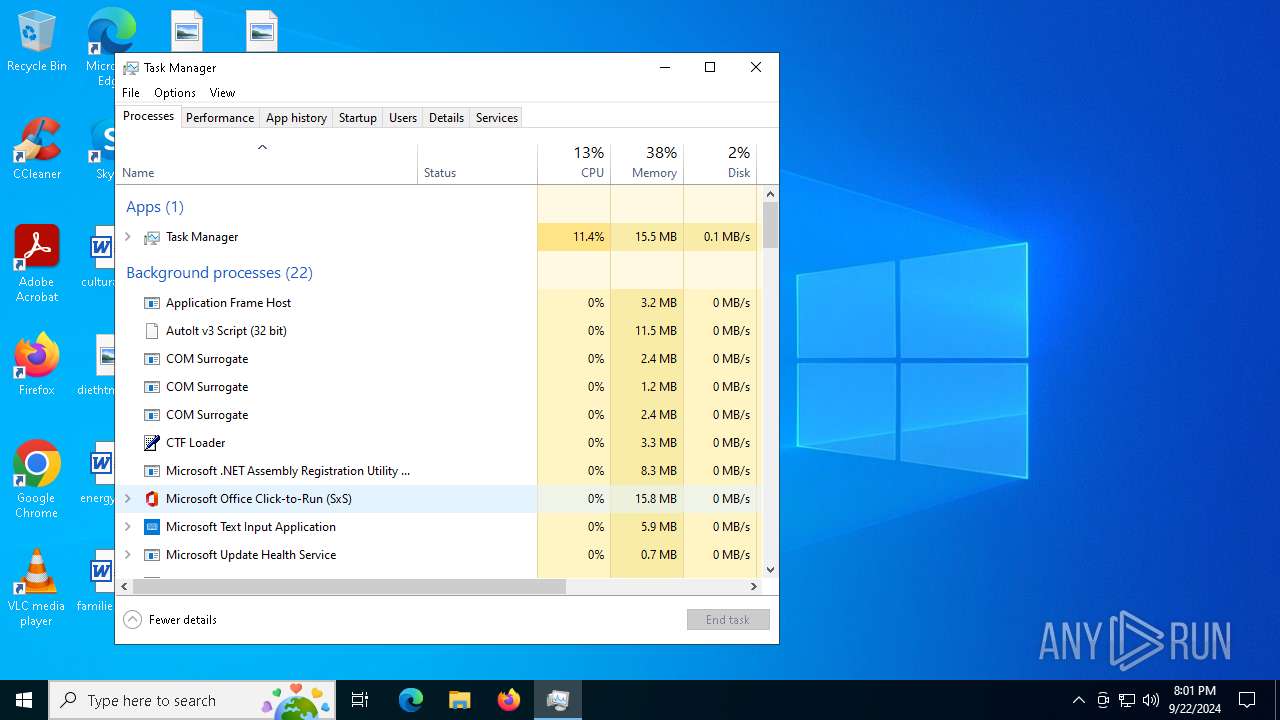
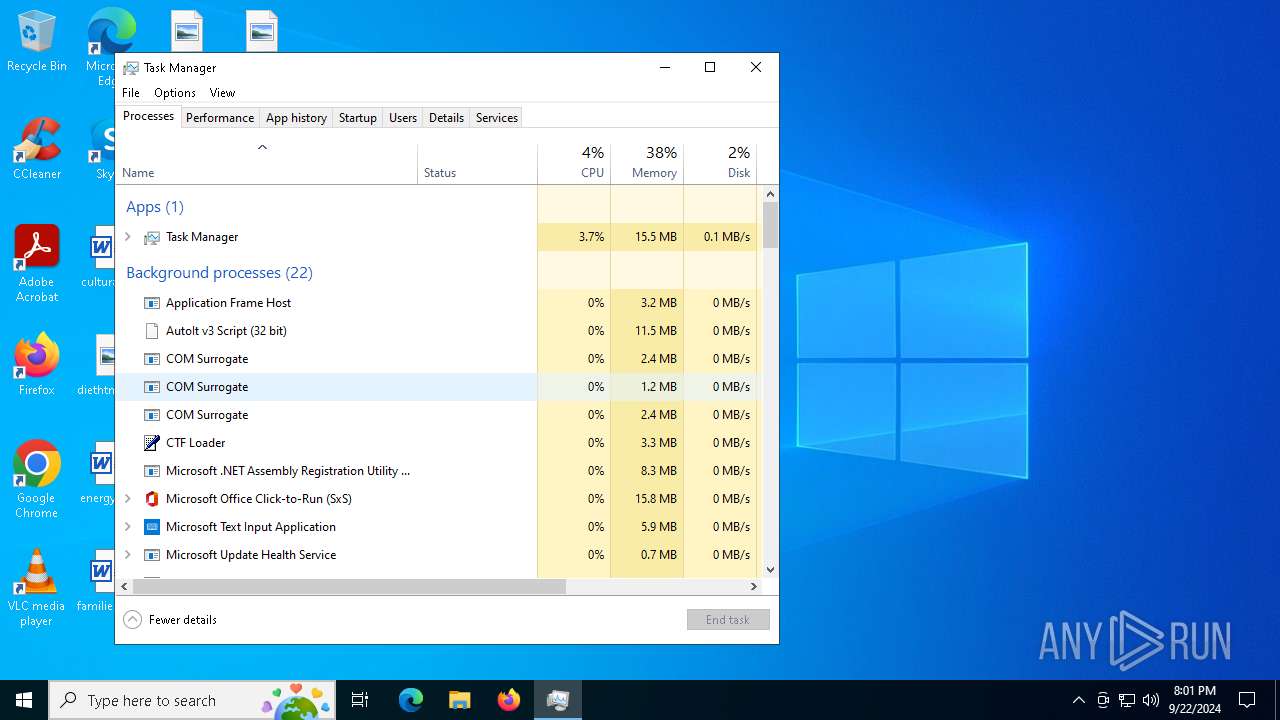
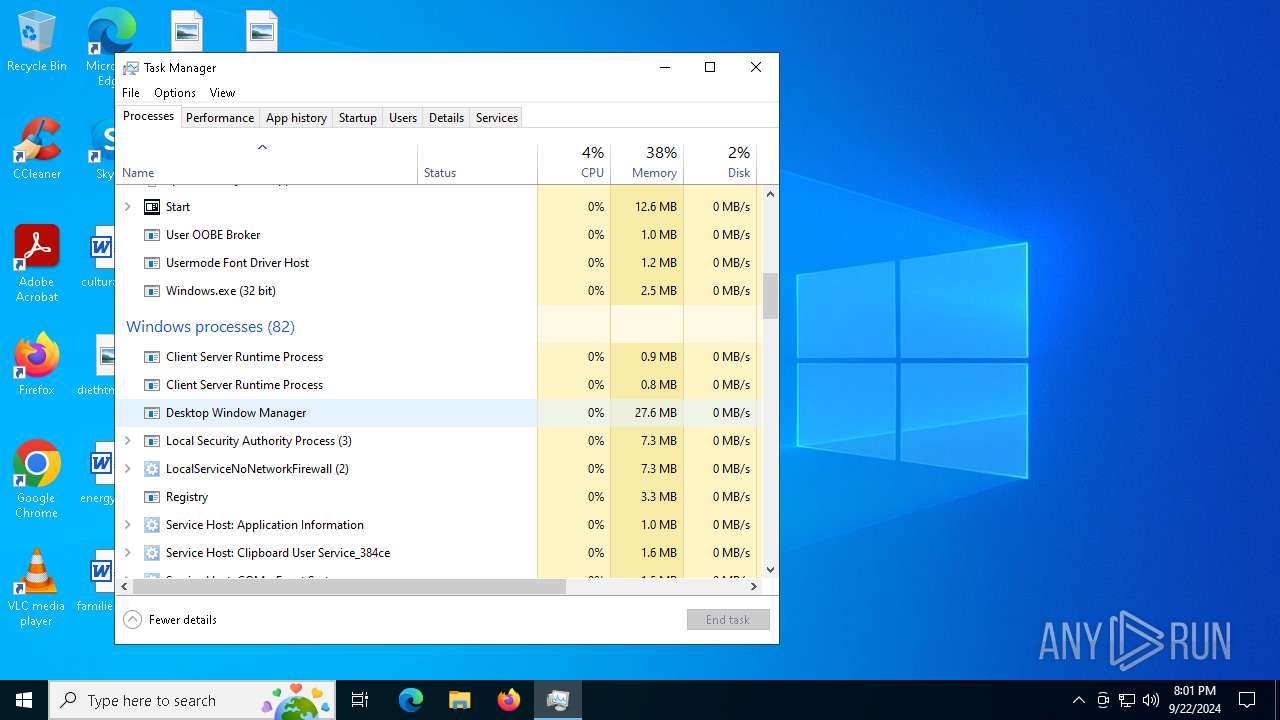
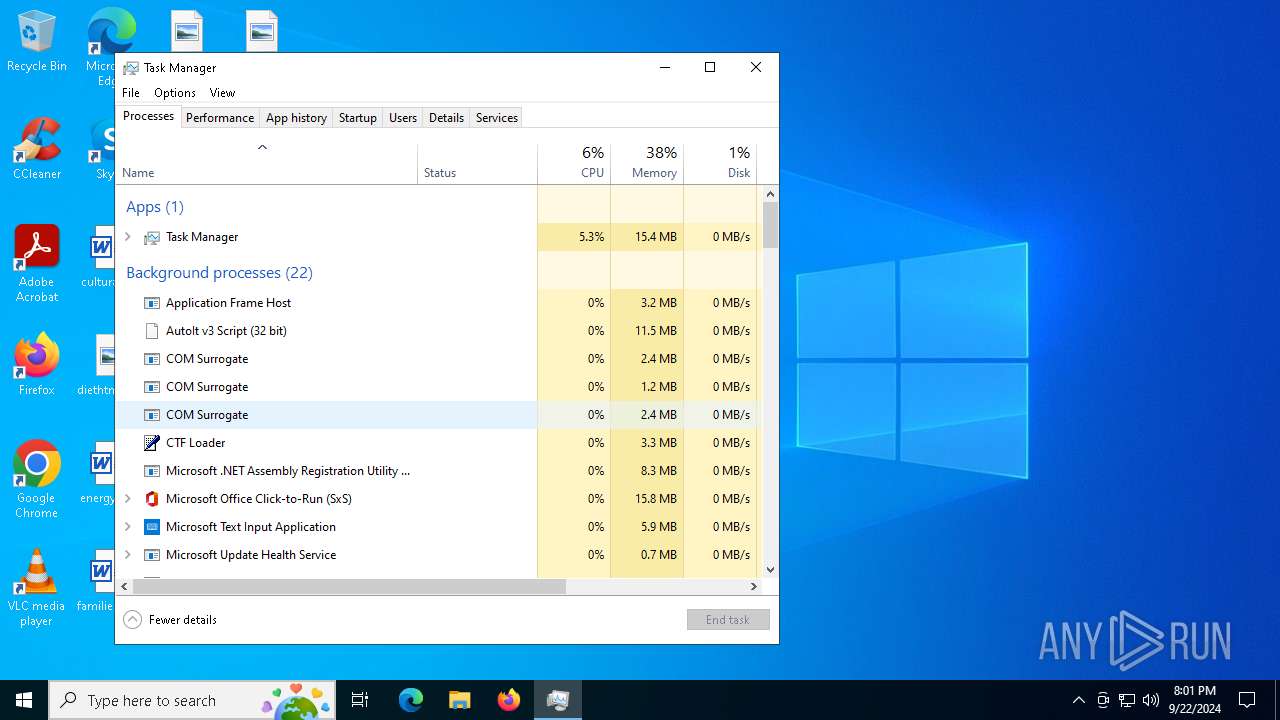
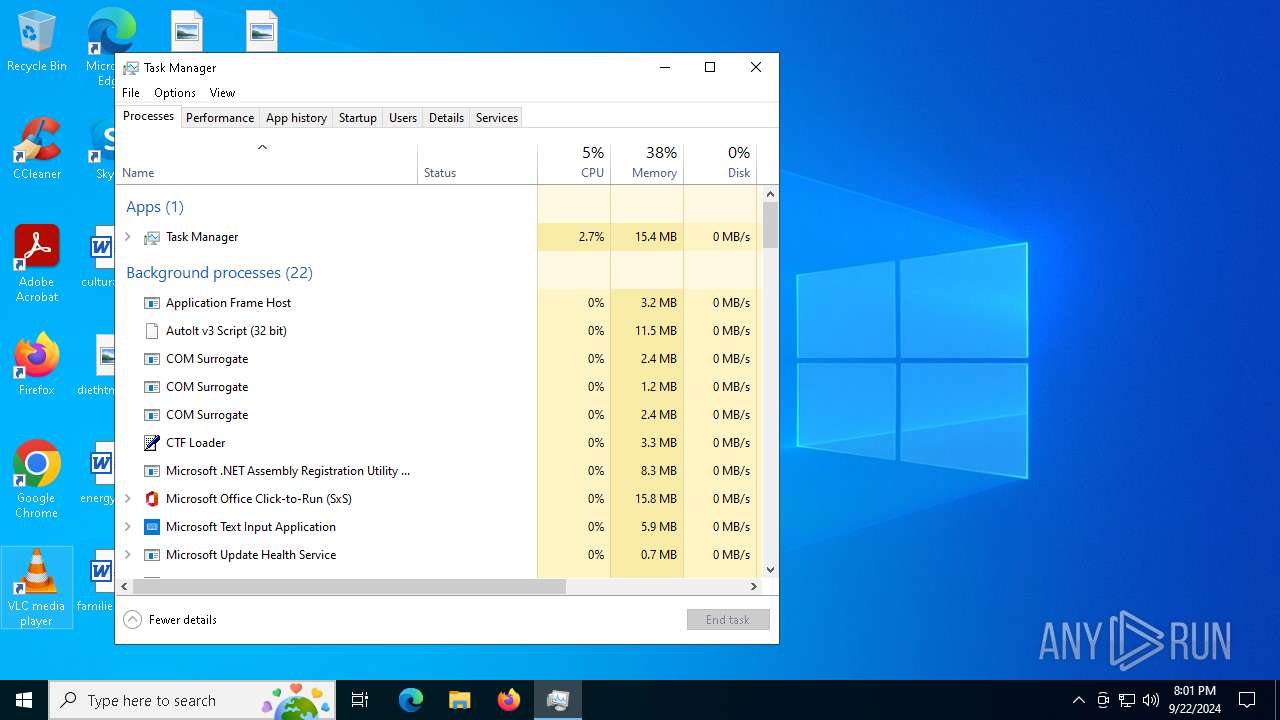
Manual execution by a user
- cmd.exe (PID: 6344)
- cmd.exe (PID: 2960)
- Taskmgr.exe (PID: 1480)
- Taskmgr.exe (PID: 7056)
Creates files or folders in the user directory
- Waters.pif (PID: 5500)
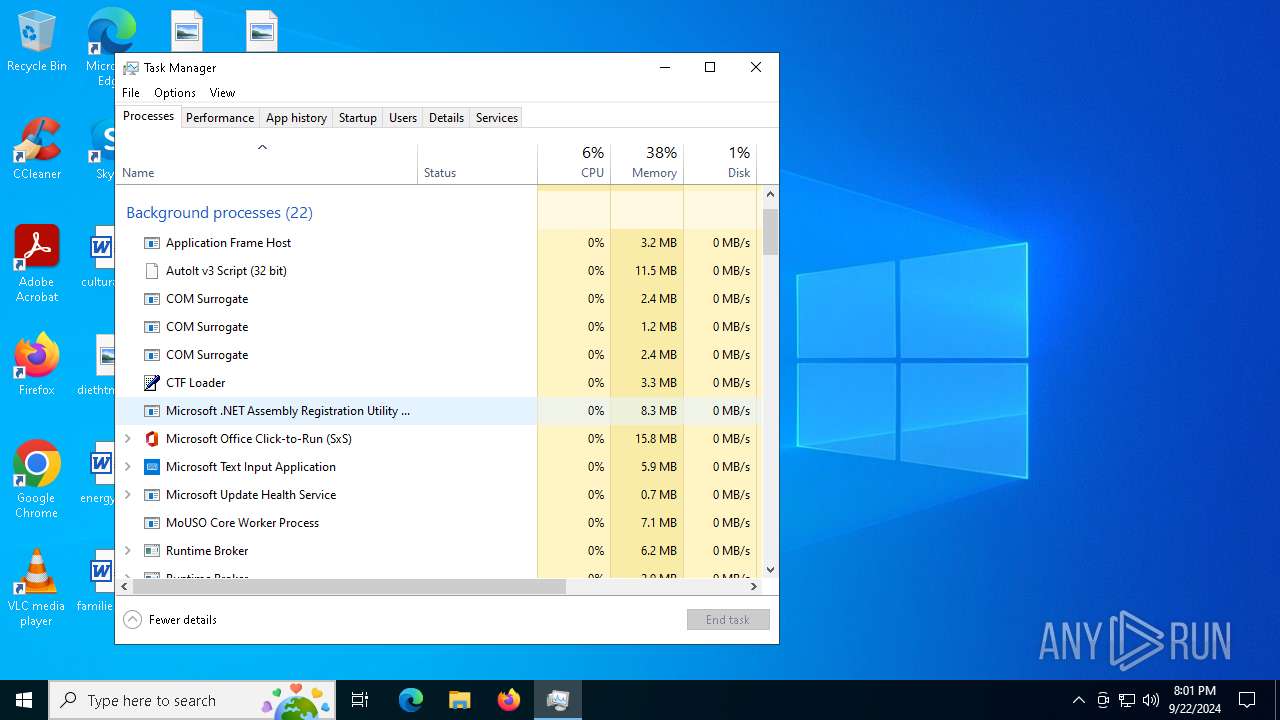
.NET Reactor protector has been detected
- 66f0297e9c3eb_15.exe (PID: 6736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 19:19:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 4120064 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3899 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.0.22621.3672 |
| ProductVersionNumber: | 10.0.22621.3672 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Mic rosoft Corporation |
| FileDescription: | Print driver host for applications |
| FileVersion: | 10.0.22621.3672 (WinBuild.160101.0800) |
| InternalName: | splwow64.exe |
| LegalCopyright: | © Mic rosoft Corporation. All rights reserved. |
| OriginalFileName: | splwow64.exe |
| ProductName: | Mic rosoft® Windows® Operating System |
| ProductVersion: | 10.0.22621.3672 |
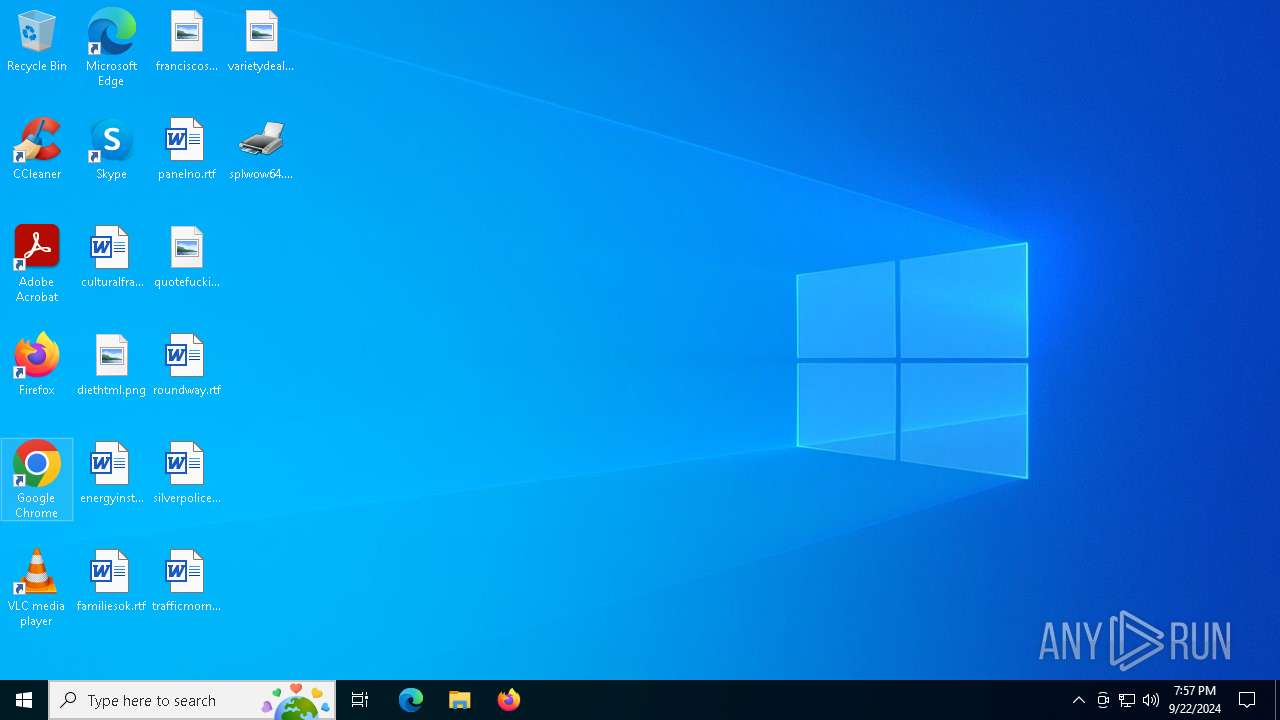
Total processes
164
Monitored processes
37
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | OA25D1nL7OtUPoAoRL0BaWNK.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 488 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | "C:\Users\admin\AppData\Local\Temp\/service123.exe" | C:\Users\admin\AppData\Local\Temp\service123.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1432 | "C:\Windows\System32\cmd.exe" /c move Emotions Emotions.bat & Emotions.bat | C:\Windows\SysWOW64\cmd.exe | splwow64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1480 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\AppData\Local\Temp\1000431001\t6hkrxrh.exe" | C:\Users\admin\AppData\Local\Temp\1000431001\t6hkrxrh.exe | Waters.pif | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Balls Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2128 | cmd /c md 607698 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2824 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2960 | cmd /k echo [InternetShortcut] > "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\QuantumFlow.url" & echo URL="C:\Users\admin\AppData\Local\QuantumDynamics Lab\QuantumFlow.js" >> "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\QuantumFlow.url" & exit | C:\Windows\SysWOW64\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 180
Read events
10 168
Write events
11
Delete events
1
Modification events
| (PID) Process: | (5500) Waters.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5500) Waters.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5500) Waters.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6660) RegAsm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6660) RegAsm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6660) RegAsm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (448) RegAsm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (448) RegAsm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (448) RegAsm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6668) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 85C8230000000000 | |||
Executable files
35
Suspicious files
45
Text files
108
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6592 | splwow64.exe | C:\Users\admin\AppData\Local\Temp\Streaming | binary | |
MD5:1501DE696D22F872DB44B548CBA0E4FA | SHA256:DCF4784EA71A3E1A42318C09183D4B5981009D296814D3679CA68EB0A7C9E2EF | |||
| 6592 | splwow64.exe | C:\Users\admin\AppData\Local\Temp\Participants | binary | |
MD5:F0E725ADDF4EC15A56AA0BDE5BD8B2A7 | SHA256:7CBD6810CB4DD516EEB75DF79D1DB55F74471C11594333AC225F24BFC0FCA7CA | |||
| 6592 | splwow64.exe | C:\Users\admin\AppData\Local\Temp\Asbestos | binary | |
MD5:19121D99734080F4FDD9CA3008168360 | SHA256:37576E4B3A1E0004B4CF7DA625B865A62D895411ED157C538F5F4CD3AA6FAB7A | |||
| 6592 | splwow64.exe | C:\Users\admin\AppData\Local\Temp\Rick | binary | |
MD5:E0D37E7B879F4B4E0DDE5006DA5009BD | SHA256:27014DAA44B8B92E1684970350C43BB1701D3A592572E650E1E00BE1470E5F77 | |||
| 6592 | splwow64.exe | C:\Users\admin\AppData\Local\Temp\Ashley | binary | |
MD5:E522956891659C41BD8550B8D5E16231 | SHA256:DDB7F60AB5F8957955DD20F2DC270E3EF833D3727F374A8C4C444634BD05609D | |||
| 6592 | splwow64.exe | C:\Users\admin\AppData\Local\Temp\Fla | binary | |
MD5:E139E52F93AE3E19AB47F437CBE8B3DE | SHA256:E0C1C46FA4582A3826F7AED2F7FB454D3EE42A425F214321910C25CC1D8879D5 | |||
| 6592 | splwow64.exe | C:\Users\admin\AppData\Local\Temp\Bet | binary | |
MD5:0F3F07B667E947C4DA38813D6D651E2A | SHA256:32B3D9D5BC58659EA524AA2CABD9CFC81B73E679E3D2CC899DFB00439612F5FF | |||
| 6592 | splwow64.exe | C:\Users\admin\AppData\Local\Temp\Viruses | binary | |
MD5:7C9DD6F9FA719321B72805DF762A82DA | SHA256:98232A6528BEB079D8FA9D77751722159D4974E6859DF867EFB3BA7A3EEC4BEC | |||
| 6592 | splwow64.exe | C:\Users\admin\AppData\Local\Temp\Navy | binary | |
MD5:D4EB107CFD9FC38ED7E7B253562E155A | SHA256:68E9A8D57BA2A484DD28A1AFED5262A86AFF4D81467B93B4072F329FAB984F4C | |||
| 6592 | splwow64.exe | C:\Users\admin\AppData\Local\Temp\Language | binary | |
MD5:5DE7106DF85E2F96F46F642D98433AD1 | SHA256:9201319C9C07E4312717845E59C9FE3A987F70575CD63E4C042DB778EBE4D5E9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
69
DNS requests
29
Threats
78
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3116 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1140 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1140 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5500 | Waters.pif | POST | 200 | 185.215.113.19:80 | http://185.215.113.19/CoreOPT/index.php | unknown | — | — | unknown |
5500 | Waters.pif | POST | 200 | 185.215.113.19:80 | http://185.215.113.19/CoreOPT/index.php | unknown | — | — | unknown |
5500 | Waters.pif | GET | 200 | 147.45.44.104:80 | http://147.45.44.104/yuop/66f0297e9c3eb_15.exe | unknown | — | — | suspicious |
5500 | Waters.pif | POST | 200 | 185.215.113.19:80 | http://185.215.113.19/CoreOPT/index.php?scr=1 | unknown | — | — | unknown |
5500 | Waters.pif | POST | 200 | 185.215.113.19:80 | http://185.215.113.19/CoreOPT/index.php | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 51.116.253.170:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | DE | unknown |
— | — | 104.126.37.171:443 | — | Akamai International B.V. | DE | unknown |
6176 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2976 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3116 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3116 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
HAYtAoQHDCIZfrnmkrkib.HAYtAoQHDCIZfrnmkrkib |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5500 | Waters.pif | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
5500 | Waters.pif | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5500 | Waters.pif | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
5500 | Waters.pif | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
5500 | Waters.pif | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
5500 | Waters.pif | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 23 |
5500 | Waters.pif | A Network Trojan was detected | ET MALWARE Amadey Bot Activity (POST) M1 |
5500 | Waters.pif | A Network Trojan was detected | ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M2 |
5500 | Waters.pif | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5500 | Waters.pif | Misc activity | ET INFO Packed Executable Download |
3 ETPRO signatures available at the full report