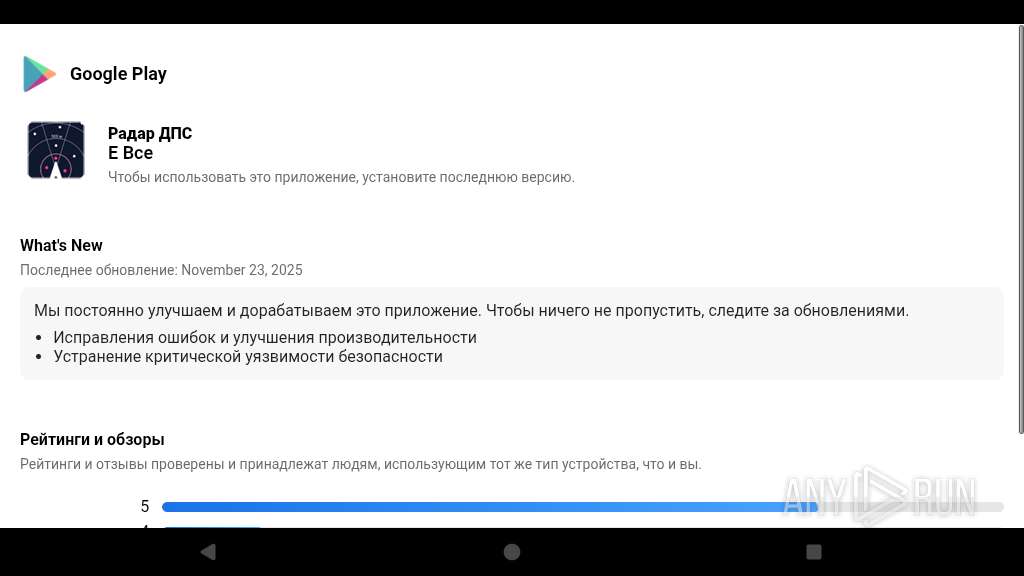
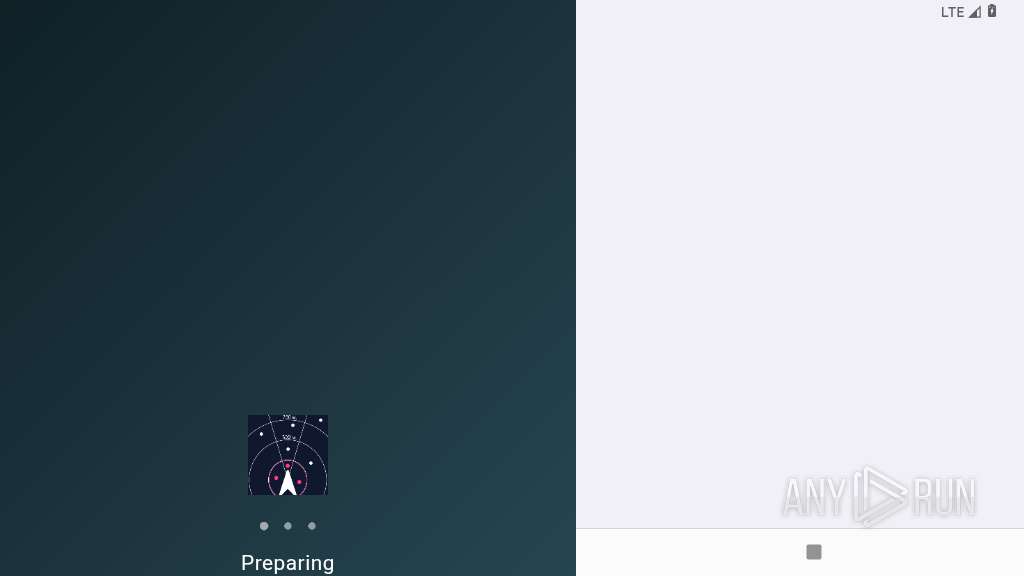
| File name: | Радар ДПС.apk |
| Full analysis: | https://app.any.run/tasks/0a0c9948-0d73-42d4-84da-1feabb3b8a84 |
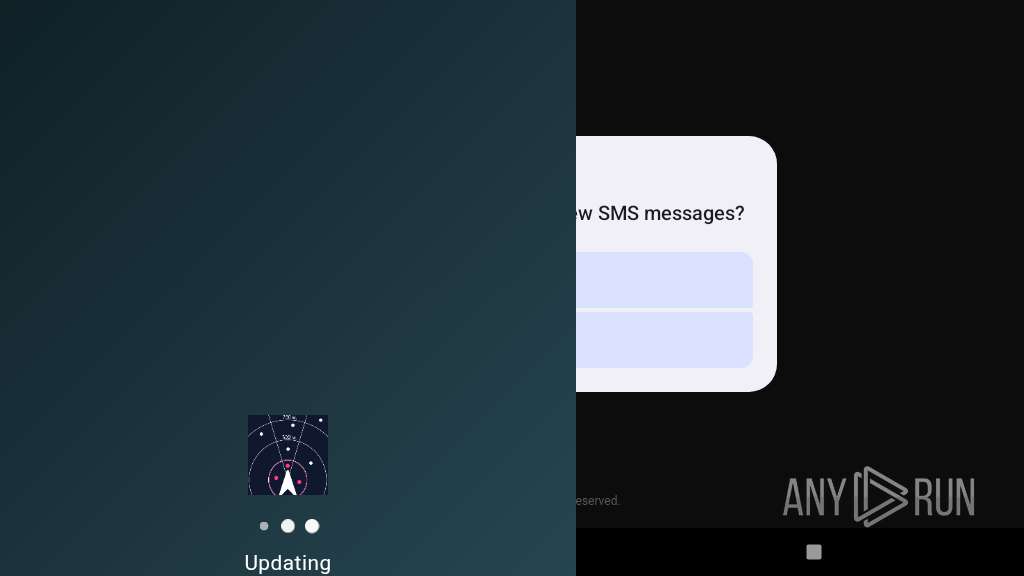
| Verdict: | Malicious activity |
| Threats: | BTMOB RAT is a remote access Trojan (RAT) designed to give attackers full control over infected devices. It targets Windows and Android endpoints. Its modular structure allows operators to tailor capabilities, making it suitable for espionage, credential theft, financial fraud, and establishing long-term footholds in corporate networks. |
| Analysis date: | January 05, 2026, 22:35:25 |
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v0.0 to extract, compression method=store |
| MD5: | 61C30BD7EB4914EB9419661AF821944C |
| SHA1: | 99D0BCE258388CCCE6EAD0E4A36D7986C9C431DB |
| SHA256: | D55057CD9110D12A192281356F06B94F342B9FEBB305CF0A5898A7E6AF40758F |
| SSDEEP: | 98304:rv3YbZRfnK0o+apE21ywNpaiqLguVlEX27AR2Mq/853AfQ+IOzaw2+9rVZ3998Ao:mo3fzODFrO1yJYp |
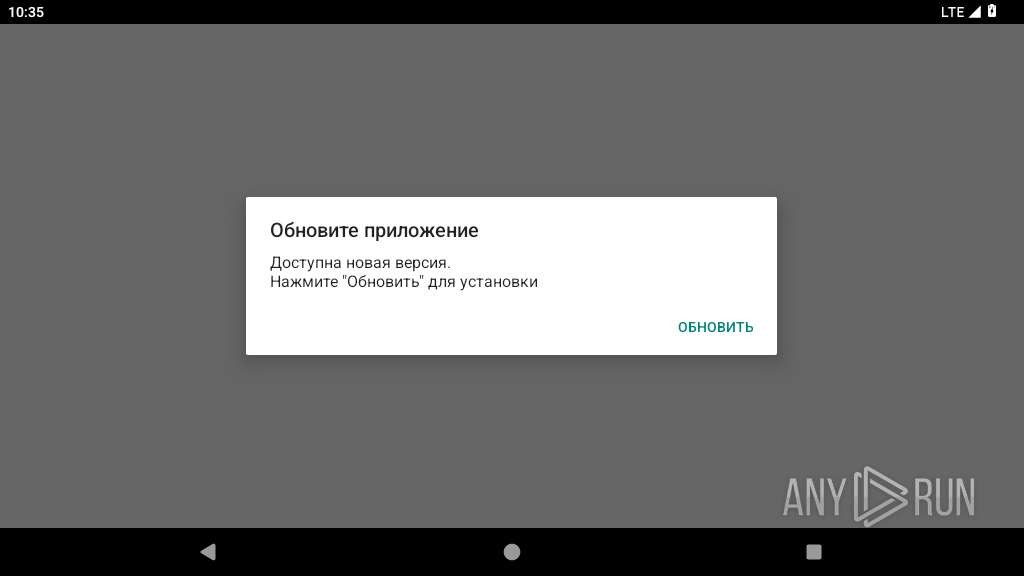
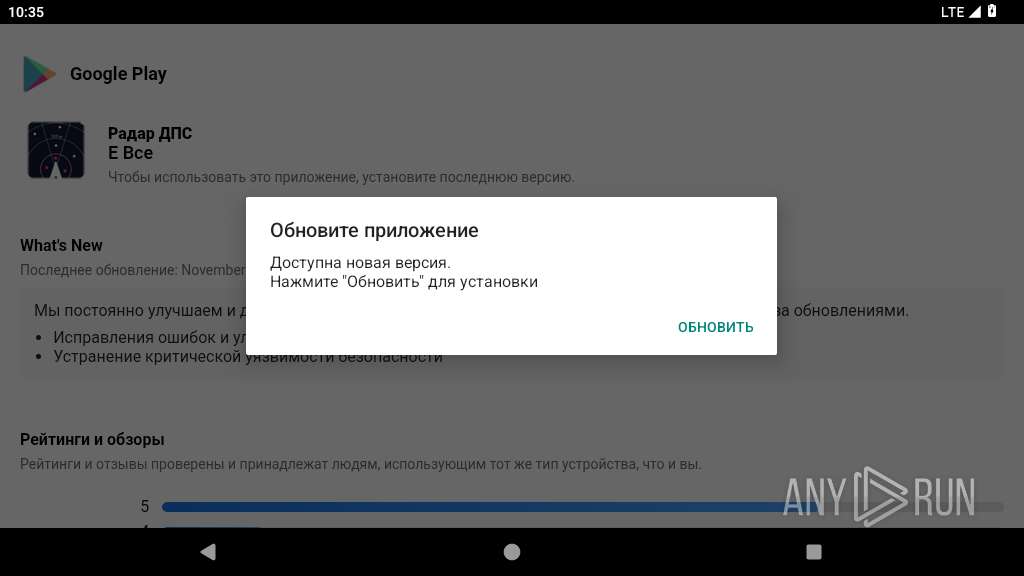
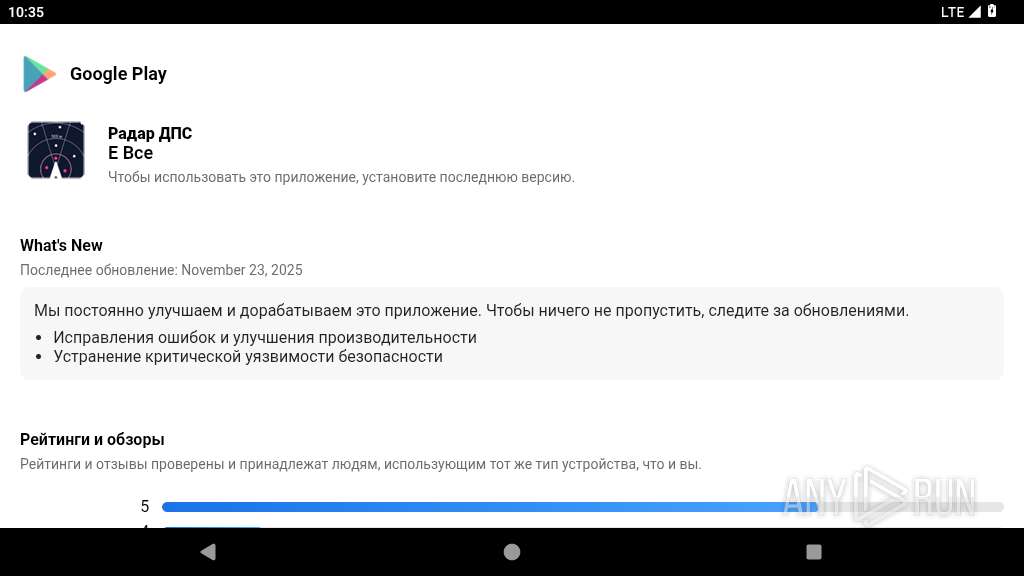
MALICIOUS
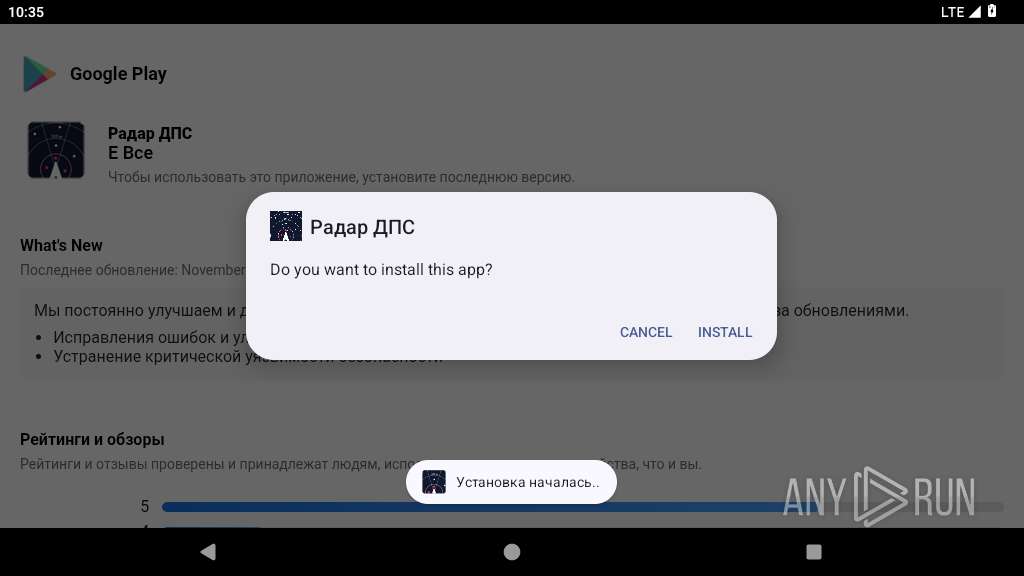
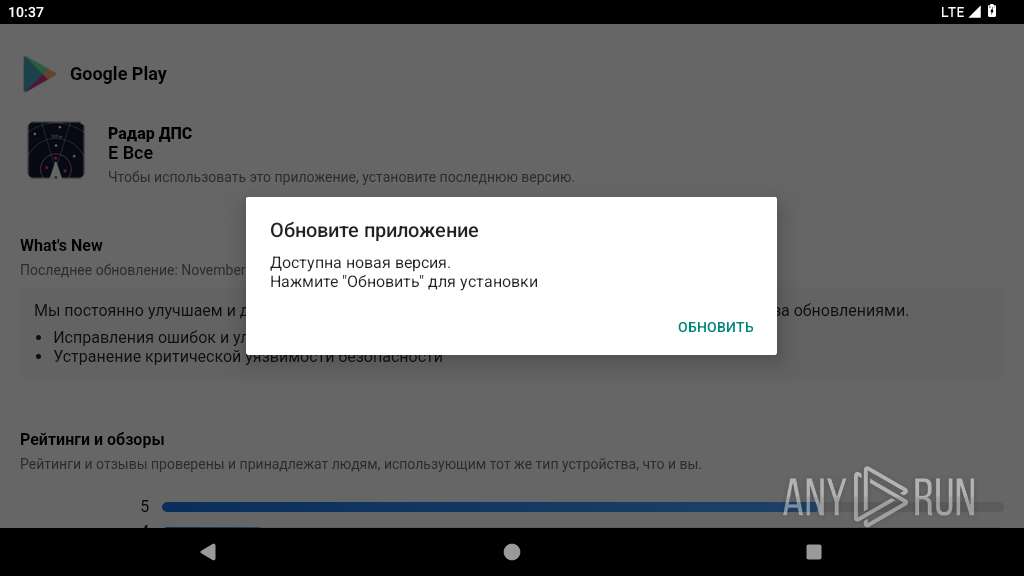
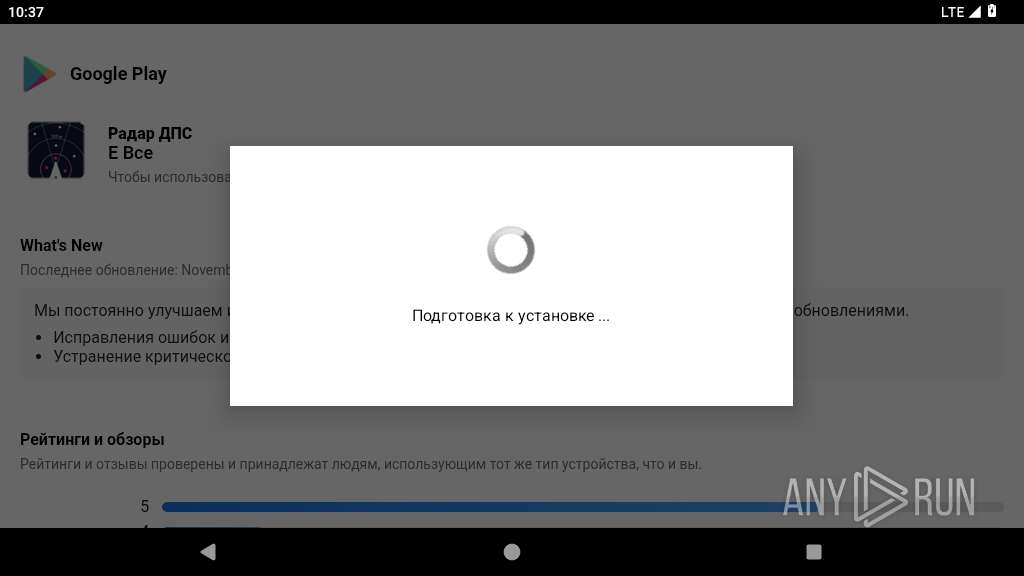
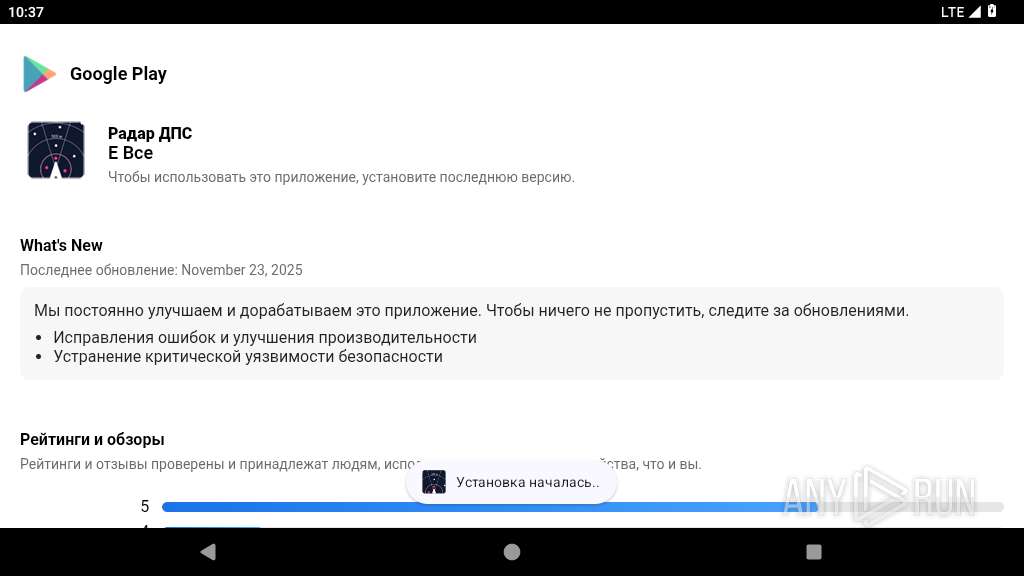
Initiates background APK installation
- app_process64 (PID: 2880)
Checks whether the screen is currently on
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
BTMOB has been detected
- app_process64 (PID: 3703)
- app_process64 (PID: 3127)
SUSPICIOUS
Uses encryption API functions
- app_process64 (PID: 2880)
- app_process64 (PID: 3703)
- app_process64 (PID: 3127)
Abuses foreground service for persistence
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Accesses system-level resources
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Launches a new activity
- app_process64 (PID: 2880)
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Retrieves a list of running services
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Creates a WakeLock to manage power state
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Acquires a wake lock to keep the device awake
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
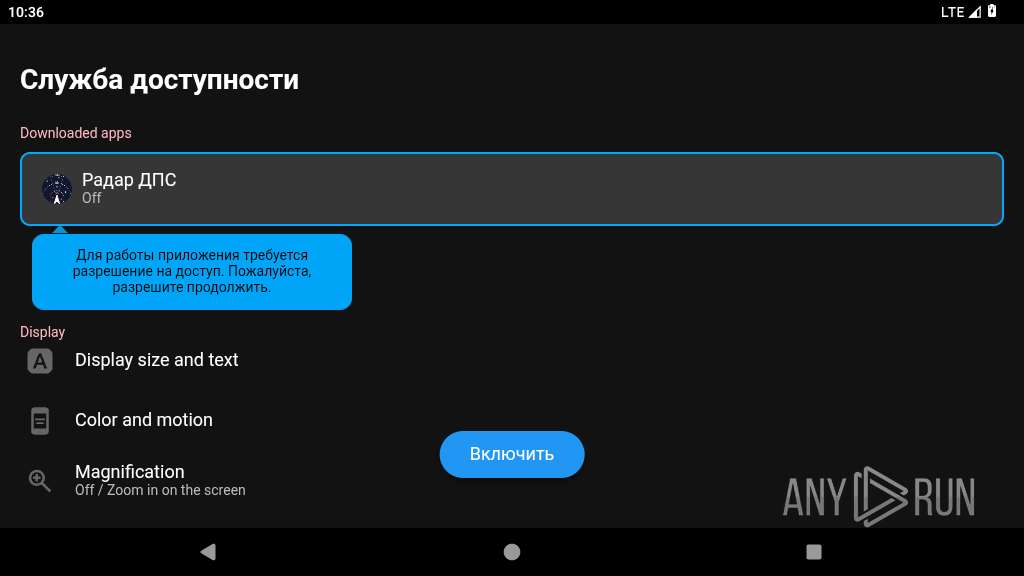
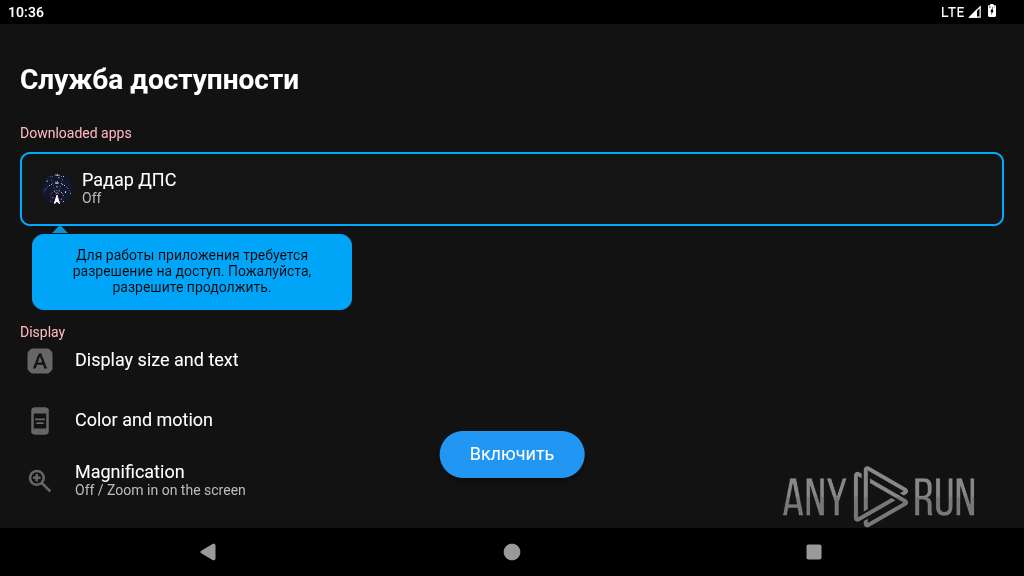
Intercepts events for accessibility services
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Overlays content on other applications
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Checks if the device's lock screen is showing
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Prevents its uninstallation by user
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
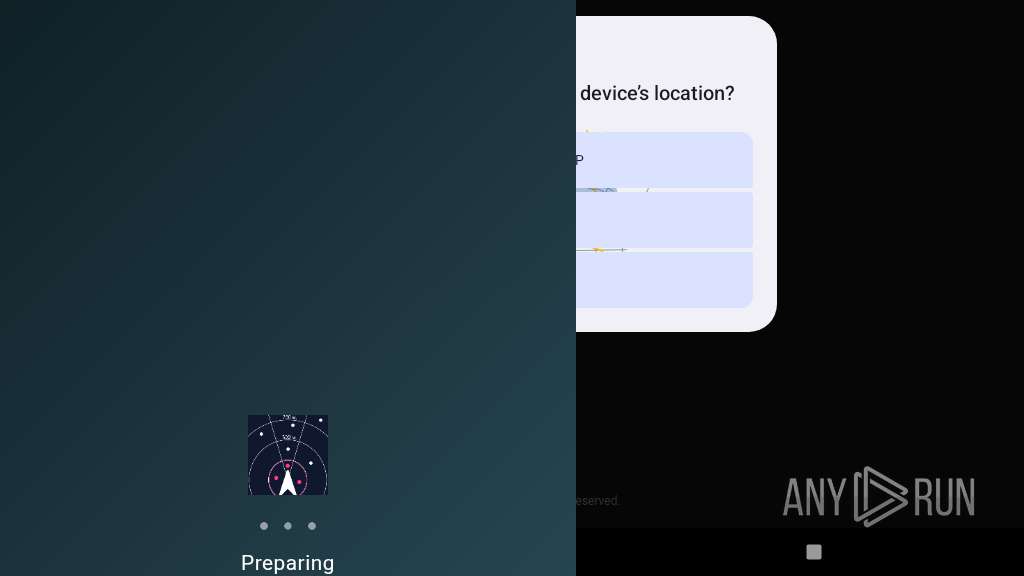
Checks for external IP
- netd (PID: 339)
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Establishing a connection
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Leverages accessibility to control apps
- app_process64 (PID: 3127)
Accesses external device storage files
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Returns the name of the current network operator
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Performs UI accessibility actions without user input
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Checks exemption from battery optimization
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Starts a service
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Retrieves installed applications on device
- app_process64 (PID: 3703)
- app_process64 (PID: 3127)
Detects presence of QEMU emulator
- app_process64 (PID: 3127)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 3703)
- app_process64 (PID: 3127)
Requests access to accessibility settings
- app_process64 (PID: 3127)
INFO
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2880)
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Stores data using SQLite database
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Dynamically registers broadcast event listeners
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Retrieves the value of a secure system setting
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Retrieves the value of a global system setting
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Verifies whether the device is connected to the internet
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Gets file name without full path
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Attempting to connect via WebSocket
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Detects device power status
- app_process64 (PID: 3127)
- app_process64 (PID: 3703)
Listens for changes in sensors
- app_process64 (PID: 3703)
- app_process64 (PID: 3127)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (73.9) |
|---|---|---|
| .jar | | | Java Archive (20.4) |
| .zip | | | ZIP compressed archive (5.6) |
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2026:01:05 18:09:06 |
| ZipCRC: | 0x918650cb |
| ZipCompressedSize: | 559052 |
| ZipUncompressedSize: | 559052 |
| ZipFileName: | resources.arsc |
Total processes
140
Monitored processes
15
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 339 | /system/bin/netd | /system/bin/netd | init | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2880 | JDUDJD.SJHSS.OIHSHZ.BXVXHSS.KSHSKSX.JSJJSKSKSKDH | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2916 | com.android.webview:webview_service | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2917 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2966 | com.android.webview:webview_apk | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3114 | /apex/com.android.art/bin/artd | /apex/com.android.art/bin/artd | — | init |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3117 | /apex/com.android.art/bin/dex2oat32 --zip-fd=6 --zip-location=/data/app/~~dzEE55GUFIpLjsci3aPaLg==/JDUJJDD.KDKDKD.SLKSKS.DNKDKD.DJDJDJDJJ-DLnLfma31SMmFf8s0hylEA==/base.apk --oat-fd=7 --oat-location=/data/app/~~dzEE55GUFIpLjsci3aPaLg==/JDUJJDD.KDKDKD.SLKSKS.DNKDKD.DJDJDJDJJ-DLnLfma31SMmFf8s0hylEA==/oat/arm64/base.odex --output-vdex-fd=8 --swap-fd=9 --class-loader-context-fds=10 --class-loader-context=PCL[]{PCL[/system/framework/org.apache.http.legacy.jar]} --classpath-dir=/data/app/~~dzEE55GUFIpLjsci3aPaLg==/JDUJJDD.KDKDKD.SLKSKS.DNKDKD.DJDJDJDJJ-DLnLfma31SMmFf8s0hylEA== --instruction-set=arm64 --instruction-set-features=default --instruction-set-variant=cortex-a53 --compiler-filter=verify --compilation-reason=install --compact-dex-level=none --max-image-block-size=524288 --resolve-startup-const-strings=true --generate-mini-debug-info --runtime-arg -Xtarget-sdk-version:34 --runtime-arg -Xhidden-api-policy:enabled --runtime-arg -Xms64m --runtime-arg -Xmx512m "--comments=app-version-name:7\.27\.43 modulator,app-version-code:72743,art-version:340090000" | /apex/com.android.art/bin/dex2oat32 | — | artd |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3127 | JDUJJDD.KDKDKD.SLKSKS.DNKDKD.DJDJDJDJJ | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 9 | ||||
| 3167 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3247 | com.android.systemui.accessibility.accessibilitymenu | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
268
Text files
78
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2880 | app_process64 | /data/data/JDUDJD.SJHSS.OIHSHZ.BXVXHSS.KSHSKSX.JSJJSKSKSKDH/app_webview/last-exit-info | text | |
MD5:— | SHA256:— | |||
| 2880 | app_process64 | /data/data/JDUDJD.SJHSS.OIHSHZ.BXVXHSS.KSHSKSX.JSJJSKSKSKDH/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2880 | app_process64 | /data/data/JDUDJD.SJHSS.OIHSHZ.BXVXHSS.KSHSKSX.JSJJSKSKSKDH/app_webview/Default/Shared Dictionary/cache/index | binary | |
MD5:— | SHA256:— | |||
| 2880 | app_process64 | /data/data/JDUDJD.SJHSS.OIHSHZ.BXVXHSS.KSHSKSX.JSJJSKSKSKDH/cache/WebView/Default/HTTP Cache/Code Cache/wasm/index | binary | |
MD5:— | SHA256:— | |||
| 2880 | app_process64 | /data/data/JDUDJD.SJHSS.OIHSHZ.BXVXHSS.KSHSKSX.JSJJSKSKSKDH/cache/WebView/Default/HTTP Cache/Code Cache/js/index | binary | |
MD5:— | SHA256:— | |||
| 2880 | app_process64 | /data/data/JDUDJD.SJHSS.OIHSHZ.BXVXHSS.KSHSKSX.JSJJSKSKSKDH/app_webview/Default/Local Storage/leveldb/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 2880 | app_process64 | /data/data/JDUDJD.SJHSS.OIHSHZ.BXVXHSS.KSHSKSX.JSJJSKSKSKDH/cache/WebView/Default/HTTP Cache/Code Cache/wasm/index-dir/temp-index | binary | |
MD5:— | SHA256:— | |||
| 2880 | app_process64 | /data/data/JDUDJD.SJHSS.OIHSHZ.BXVXHSS.KSHSKSX.JSJJSKSKSKDH/cache/WebView/Default/HTTP Cache/Code Cache/js/index-dir/temp-index | binary | |
MD5:— | SHA256:— | |||
| 2880 | app_process64 | /data/data/JDUDJD.SJHSS.OIHSHZ.BXVXHSS.KSHSKSX.JSJJSKSKSKDH/cache/WebView/font_unique_name_table.pb | binary | |
MD5:— | SHA256:— | |||
| 2880 | app_process64 | /data/data/JDUDJD.SJHSS.OIHSHZ.BXVXHSS.KSHSKSX.JSJJSKSKSKDH/app_webview/Default/Shared Dictionary/cache/index-dir/temp-index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
494
TCP/UDP connections
196
DNS requests
85
Threats
45
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
822 | app_process64 | GET | 204 | 142.250.184.228:443 | https://www.google.com/generate_204 | unknown | — | — | whitelisted |
— | — | GET | 204 | 142.250.184.228:80 | http://www.google.com/gen_204 | unknown | — | — | whitelisted |
822 | app_process64 | GET | 204 | 142.250.185.163:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
1756 | app_process64 | POST | 200 | 66.102.1.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:fetchEekChain | unknown | binary | 778 b | whitelisted |
3127 | app_process64 | HEAD | 200 | 193.108.170.41:80 | http://193.108.170.41/yaarsa/private/yarsap_80541.php | unknown | — | — | unknown |
1756 | app_process64 | POST | 200 | 66.102.1.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:signCertificates?challenge=AAABm5BNRL8BILStY9WnelL0lzc01Fcluh4f068=&request_id=0a483158-cf4d-4288-b86f-c835a54c8a2d | unknown | binary | 11.8 Kb | whitelisted |
2916 | app_process32 | GET | 200 | 142.250.186.131:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=android_webview&milestone=137 | unknown | compressed | 12.3 Kb | whitelisted |
3127 | app_process64 | POST | 200 | 193.108.170.41:80 | http://193.108.170.41/yaarsa/private/yarsap_80541.php | unknown | — | — | unknown |
2966 | app_process32 | POST | 200 | 142.251.141.67:443 | https://update.googleapis.com/service/update2/json?cup2key=15:hpZJldNkWhpu7vQf0EjK6y-INJp-pCR9-mHI2PP5nvQ&cup2hreq=16c07b18a36bb2f9ad569ab5bfe6cfd4fa13af67f77b4fd04ea064bb0570fcee | unknown | text | 482 b | whitelisted |
3127 | app_process64 | GET | 101 | 193.108.170.41:8080 | http://193.108.170.41:8080/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
443 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 142.250.184.228:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.184.228:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.185.163:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
822 | app_process64 | 142.250.184.228:443 | www.google.com | GOOGLE | US | whitelisted |
571 | app_process64 | 216.239.35.8:123 | time.android.com | GOOGLE | US | whitelisted |
822 | app_process64 | 142.250.185.163:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
1756 | app_process64 | 66.102.1.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
2916 | app_process32 | 142.250.186.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2966 | app_process32 | 142.251.141.67:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
checkip.amazonaws.com |
| whitelisted |
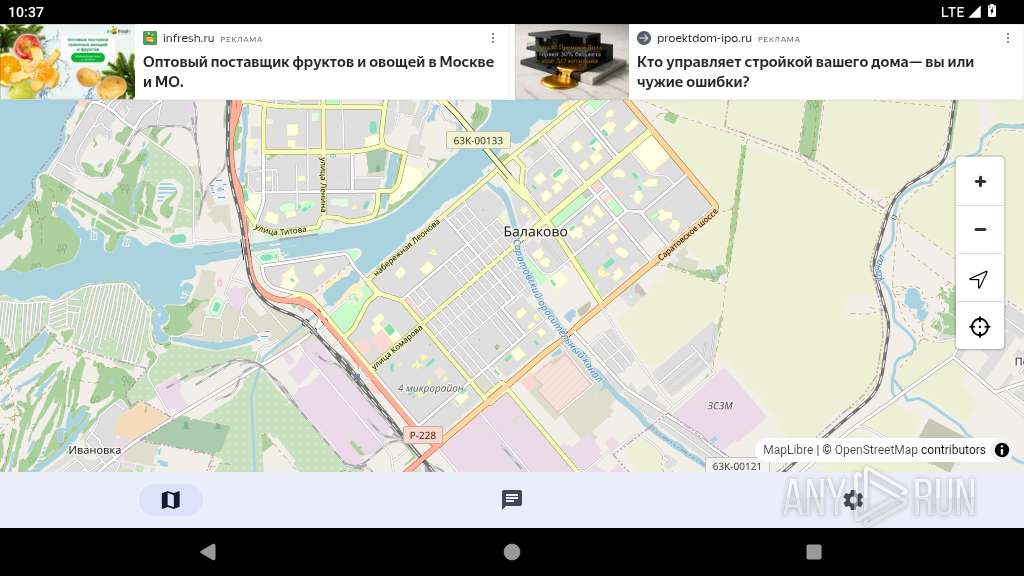
app.gdedps.com |
| unknown |
yandex.ru |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
822 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
339 | netd | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (checkip .amazonaws .com) |
3127 | app_process64 | Device Retrieving External IP Address Detected | ET INFO External IP Check (checkip .amazonaws .com) |
3127 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
3127 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
3127 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
3127 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
3127 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
3127 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
3127 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |