| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/844f89a4-ca81-426f-8aa3-0be7ede695a2 |
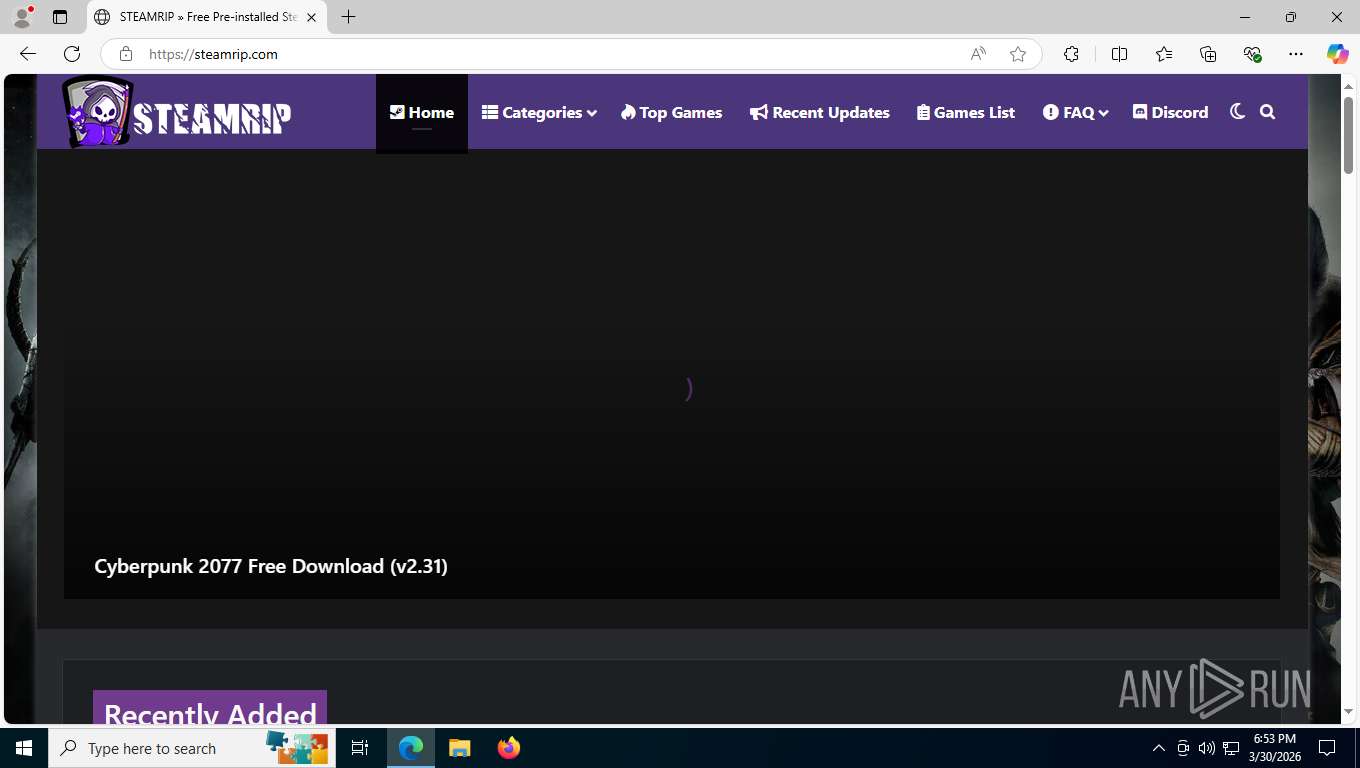
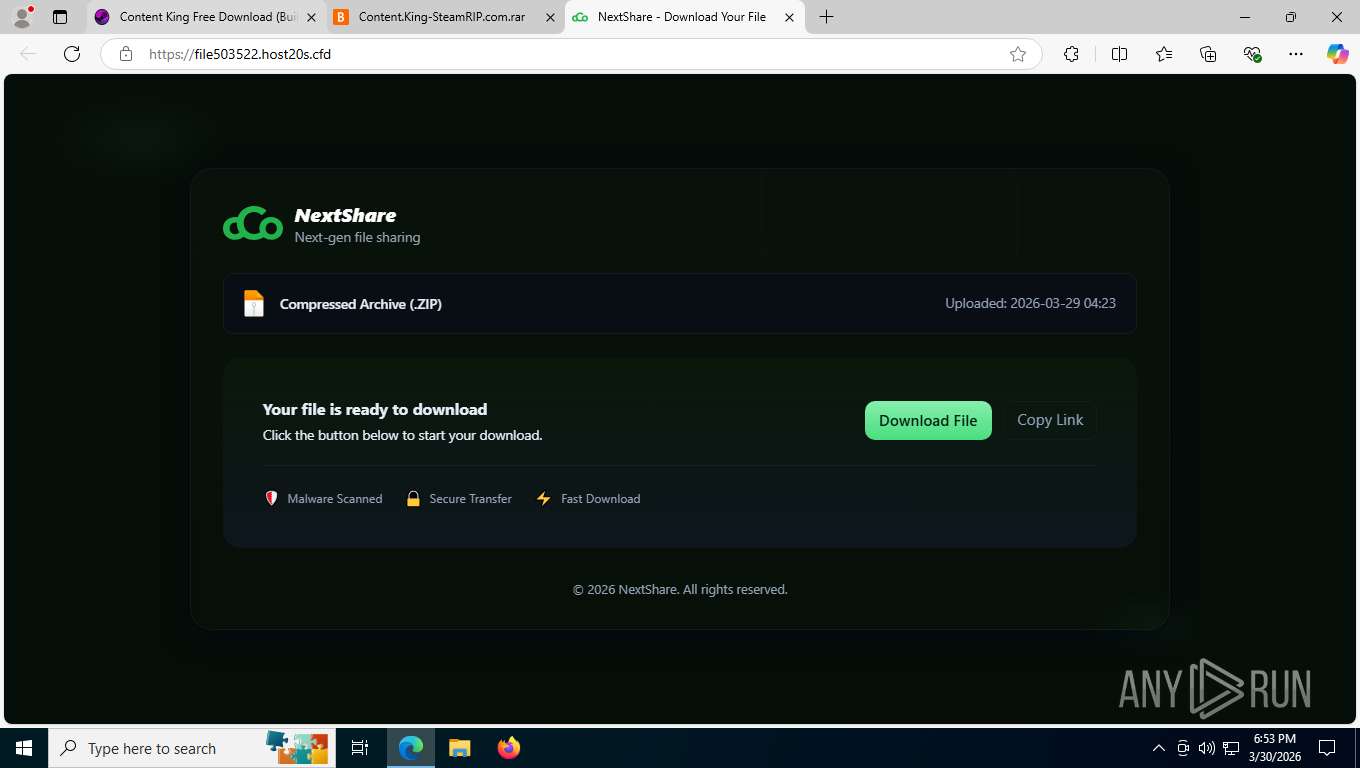
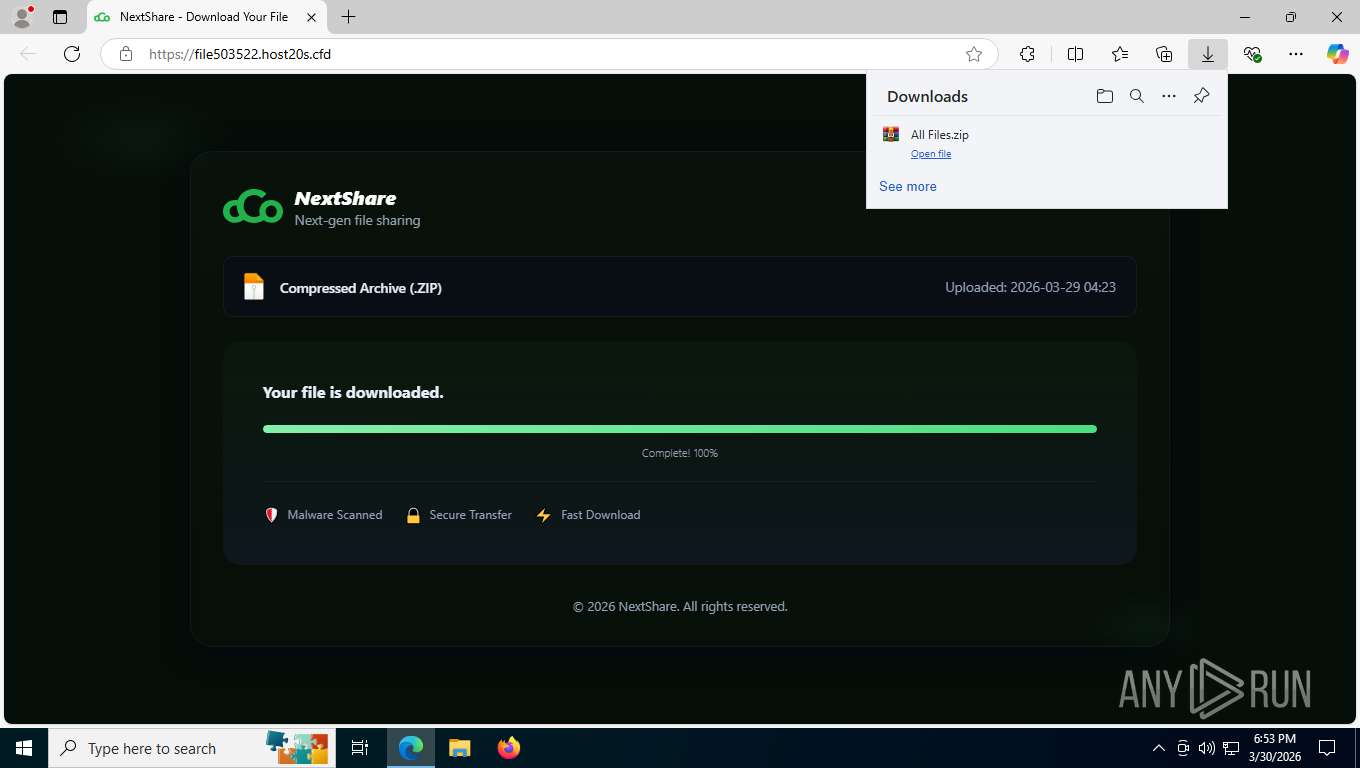
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | March 30, 2026, 22:52:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
MALICIOUS
LUMMA has been detected (SURICATA)
- msedge.exe (PID: 7160)
Executing a file with an untrusted certificate
- update.exe (PID: 7288)
- update.exe (PID: 7500)
Actions looks like stealing of personal data
- update.exe (PID: 7288)
- update.exe (PID: 7500)
Steals credentials from Web Browsers
- update.exe (PID: 7288)
- update.exe (PID: 7500)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Changes the autorun value in the registry
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Creates scheduled task from XML file
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Run PowerShell with an invisible window
- powershell.exe (PID: 2988)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 5988)
Changes powershell execution policy (Bypass)
- conhost.exe (PID: 6448)
- conhost.exe (PID: 2956)
Execute application with conhost.exe as parent process
- powershell.exe (PID: 2988)
- powershell.exe (PID: 3100)
ETHERHIDING has been detected (SURICATA)
- PresentationSettings.exe (PID: 5716)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 964)
- cmd.exe (PID: 3996)
- cmd.exe (PID: 4960)
- cmd.exe (PID: 9132)
- cmd.exe (PID: 9192)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 4684)
- cmd.exe (PID: 684)
- cmd.exe (PID: 4680)
- cmd.exe (PID: 5412)
- cmd.exe (PID: 2880)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 2660)
- cmd.exe (PID: 664)
- cmd.exe (PID: 5988)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 9132)
- cmd.exe (PID: 5412)
- cmd.exe (PID: 9192)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 2880)
- cmd.exe (PID: 5780)
- update.exe (PID: 7288)
- cmd.exe (PID: 2660)
- cmd.exe (PID: 664)
- cmd.exe (PID: 4680)
- cmd.exe (PID: 5988)
- conhost.exe (PID: 6448)
- update.exe (PID: 7500)
- powershell.exe (PID: 684)
- conhost.exe (PID: 2956)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 7764)
Accesses local storage devices (Win32_LogicalDisk) (SCRIPT)
- powershell.exe (PID: 8728)
- powershell.exe (PID: 6748)
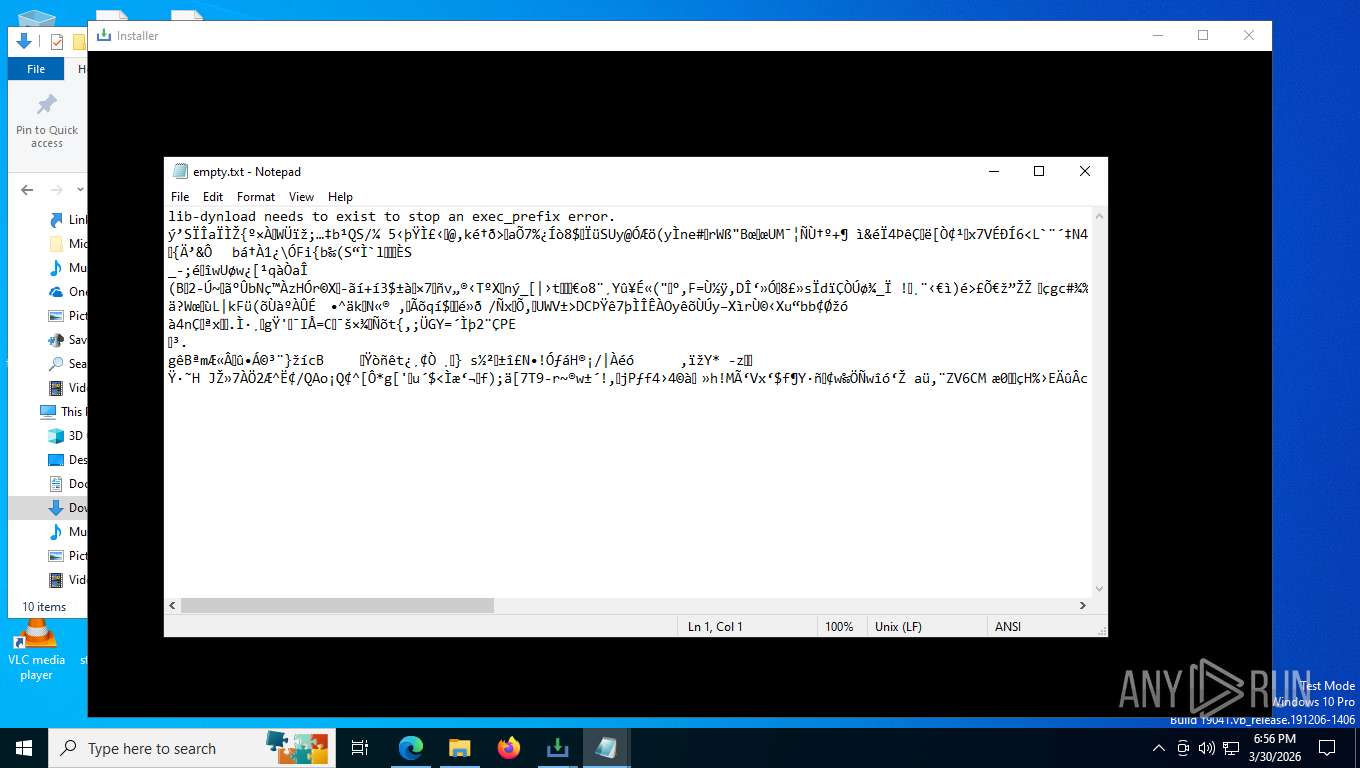
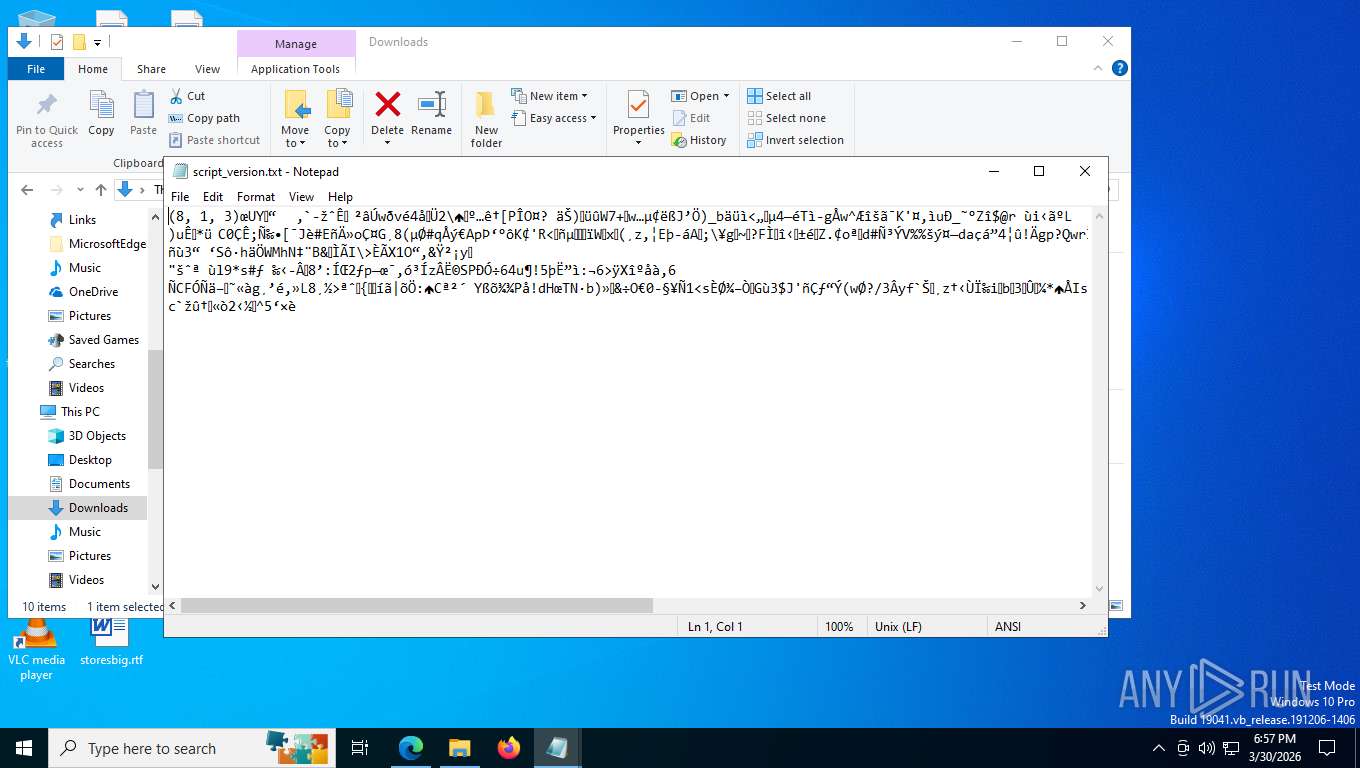
Executable content was dropped or overwritten
- lnstaIer.exe (PID: 4336)
- lnstaIer.exe (PID: 4916)
- csc.exe (PID: 8644)
Contacting a server suspected of hosting an CnC
- msedge.exe (PID: 7160)
Checks for external IP
- lnstaIer.exe (PID: 4336)
- lnstaIer.exe (PID: 4916)
Possible stealing from crypto wallets
- update.exe (PID: 7288)
- update.exe (PID: 7500)
Possible stealing of email data
- update.exe (PID: 7288)
- update.exe (PID: 7500)
Searches for installed software
- update.exe (PID: 7288)
- update.exe (PID: 7500)
Possible stealing from password managers
- update.exe (PID: 7288)
- update.exe (PID: 7500)
Multiple wallet extension IDs have been found
- update.exe (PID: 7288)
The process bypasses the loading of PowerShell profile settings
- update.exe (PID: 7288)
- conhost.exe (PID: 6448)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 684)
- update.exe (PID: 7500)
- conhost.exe (PID: 2956)
- powershell.exe (PID: 1868)
The process hide an interactive prompt from the user
- update.exe (PID: 7288)
- update.exe (PID: 7500)
Possible stealing from browsers
- update.exe (PID: 7288)
- update.exe (PID: 7500)
The process hides Powershell's copyright startup banner
- update.exe (PID: 7288)
- powershell.exe (PID: 684)
- update.exe (PID: 7500)
Executes script without checking the security policy
- powershell.exe (PID: 7764)
- powershell.exe (PID: 2988)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 3100)
Receives information about network interfaces and IP addresses (POWERSHELL)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
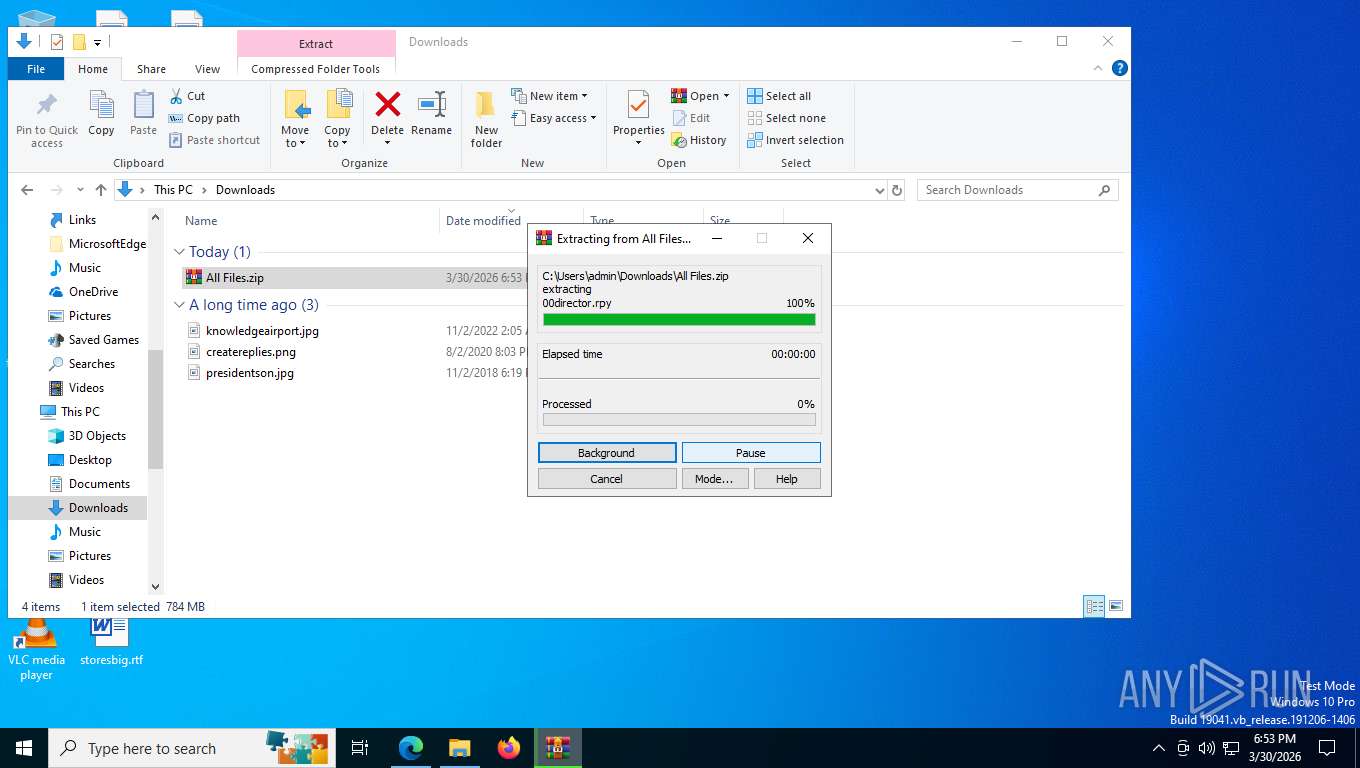
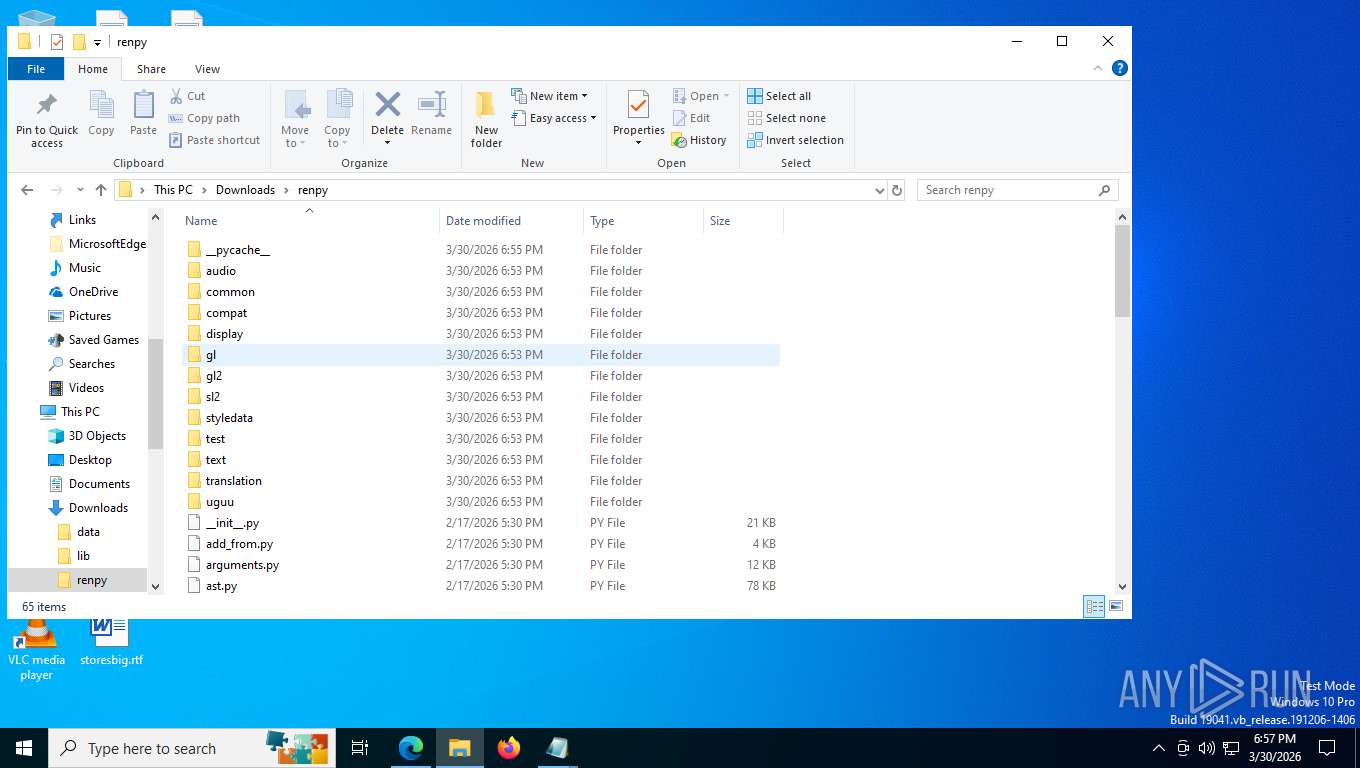
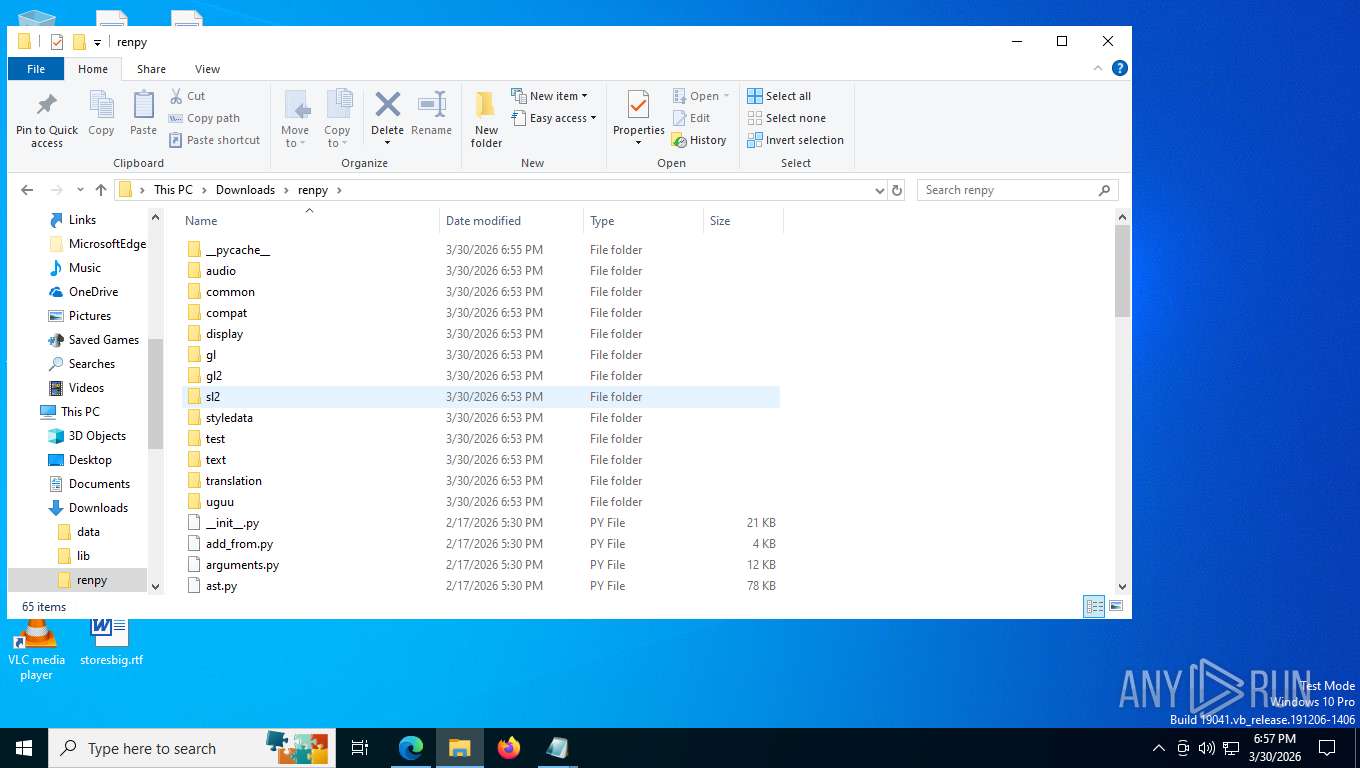
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Enumerate domain group members
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Enumerate domain controller
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Enumerate organizational units
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Enumerate domain users
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Enumerate domain groups
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Enumerate current domain
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 684)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 5988)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 684)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 5988)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 684)
- powershell.exe (PID: 1868)
The process executes via Task Scheduler
- conhost.exe (PID: 6448)
- conhost.exe (PID: 2956)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 6228)
- schtasks.exe (PID: 1504)
Probably obfuscated PowerShell command line is found
- conhost.exe (PID: 6448)
- powershell.exe (PID: 7764)
- conhost.exe (PID: 2956)
- powershell.exe (PID: 1868)
Application launched itself
- powershell.exe (PID: 7764)
- powershell.exe (PID: 684)
- powershell.exe (PID: 1868)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 684)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8644)
Bypass execution policy to execute commands
- powershell.exe (PID: 3100)
- powershell.exe (PID: 2988)
- powershell.exe (PID: 5988)
Potential Corporate Privacy Violation
- PresentationSettings.exe (PID: 5716)
Executes as Windows Service
- WmiApSrv.exe (PID: 6748)
INFO
Application launched itself
- msedge.exe (PID: 7096)
Context menu (right-click) prevention is present
- msedge.exe (PID: 7096)
Reads Environment values
- identity_helper.exe (PID: 5160)
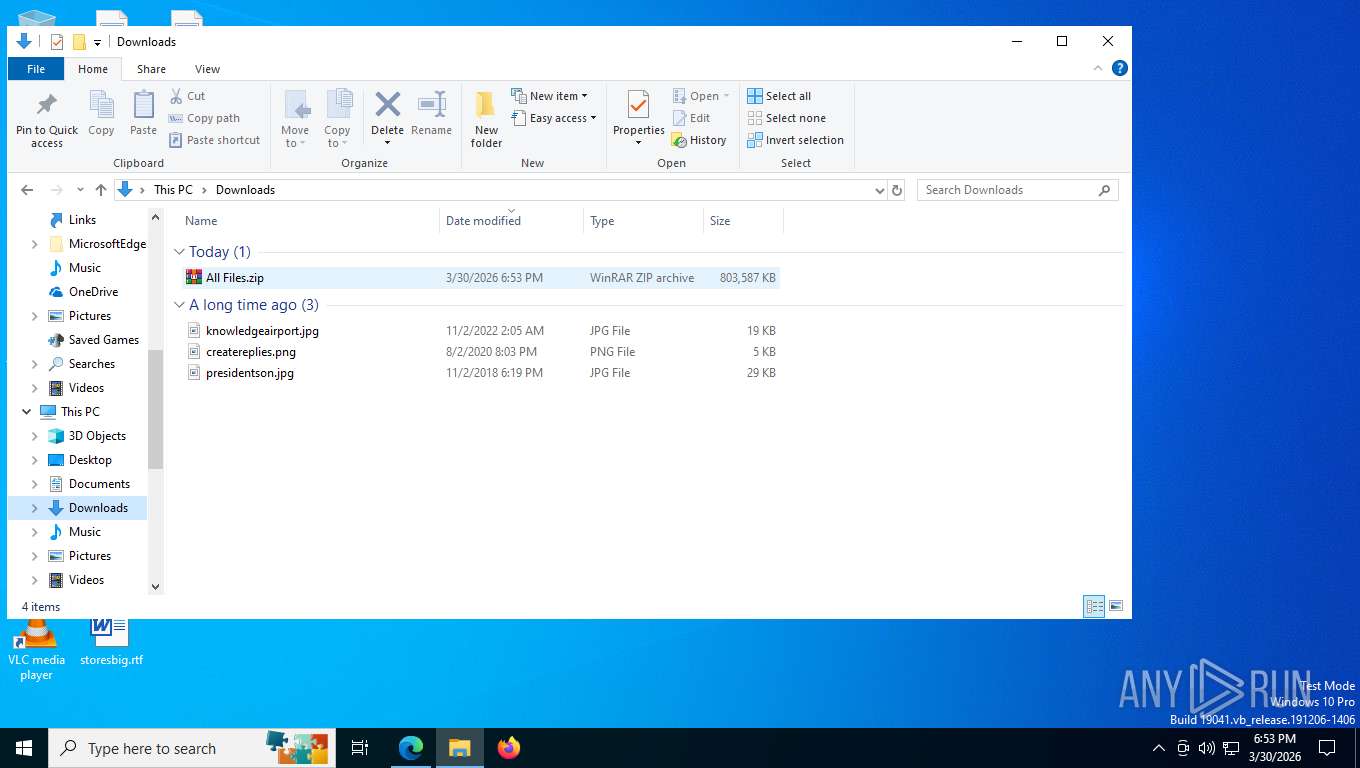
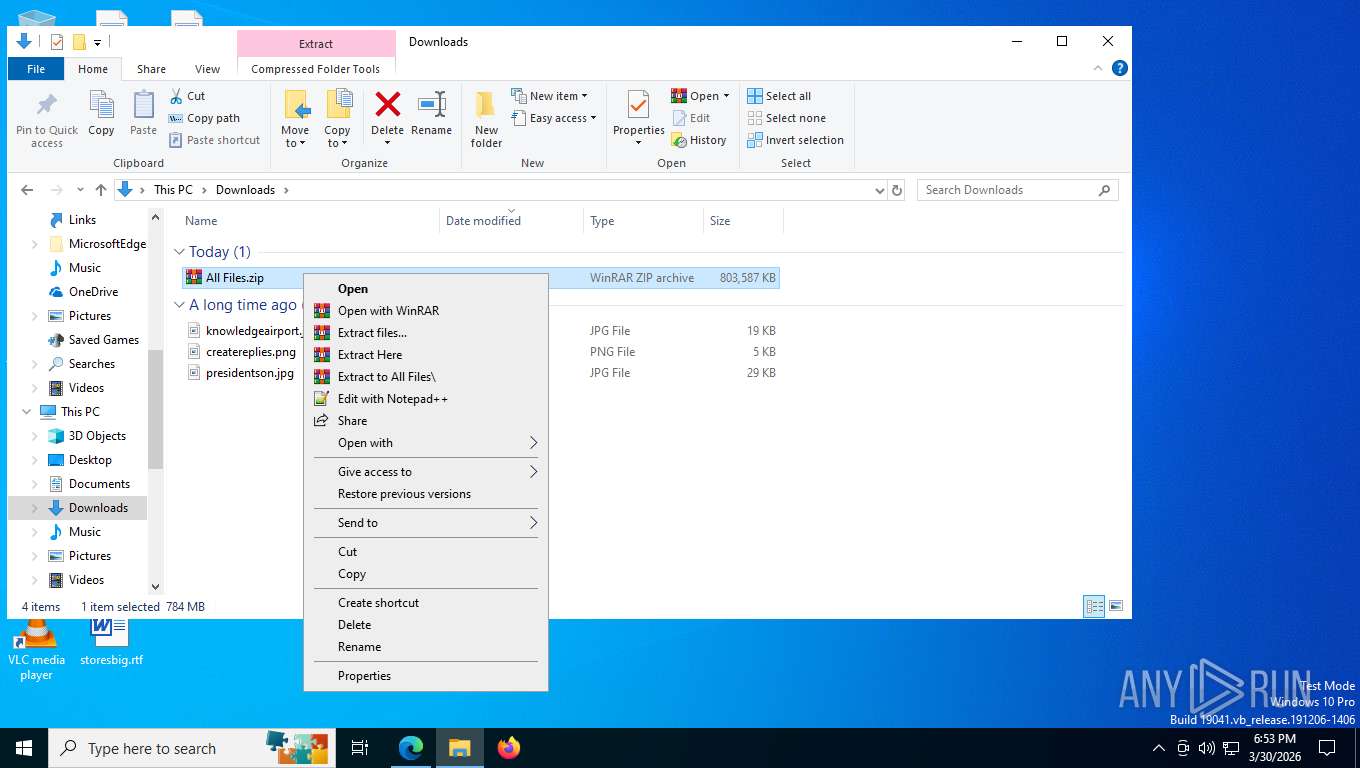
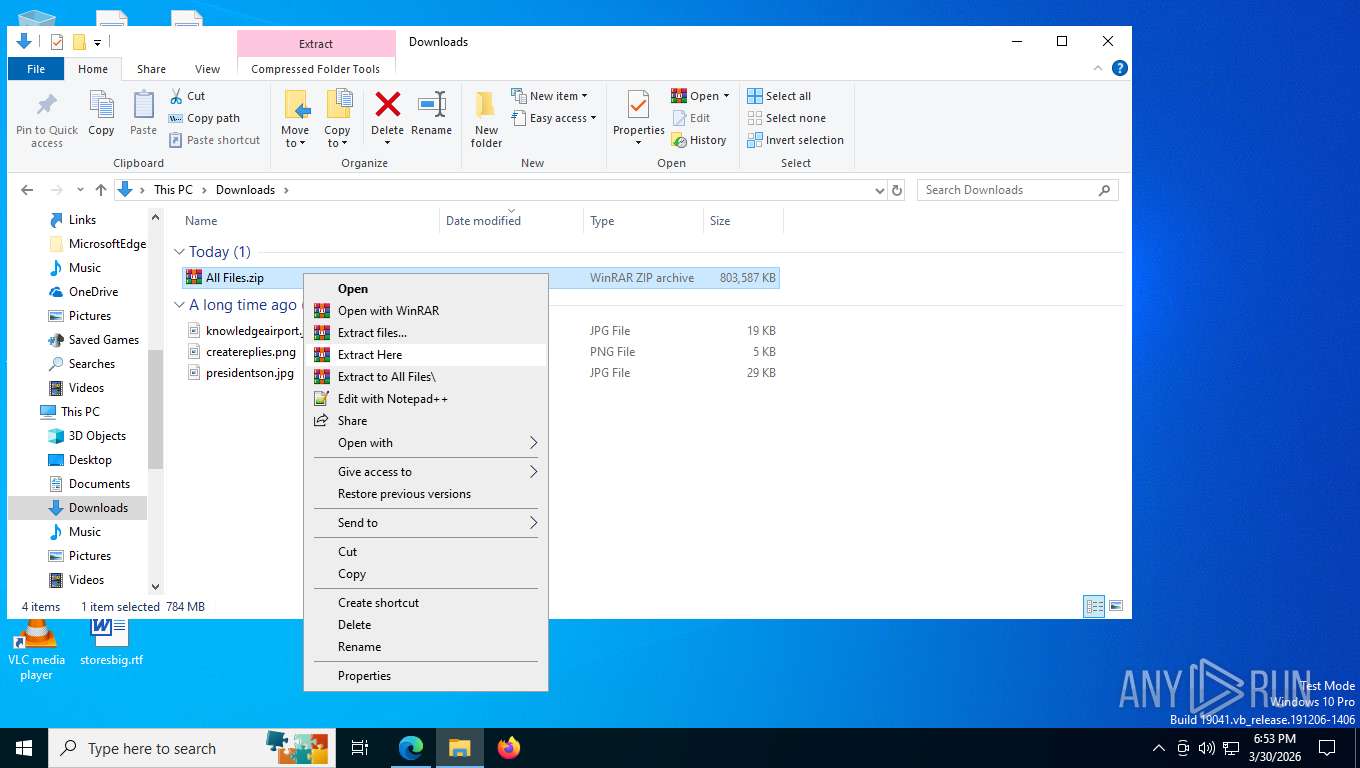
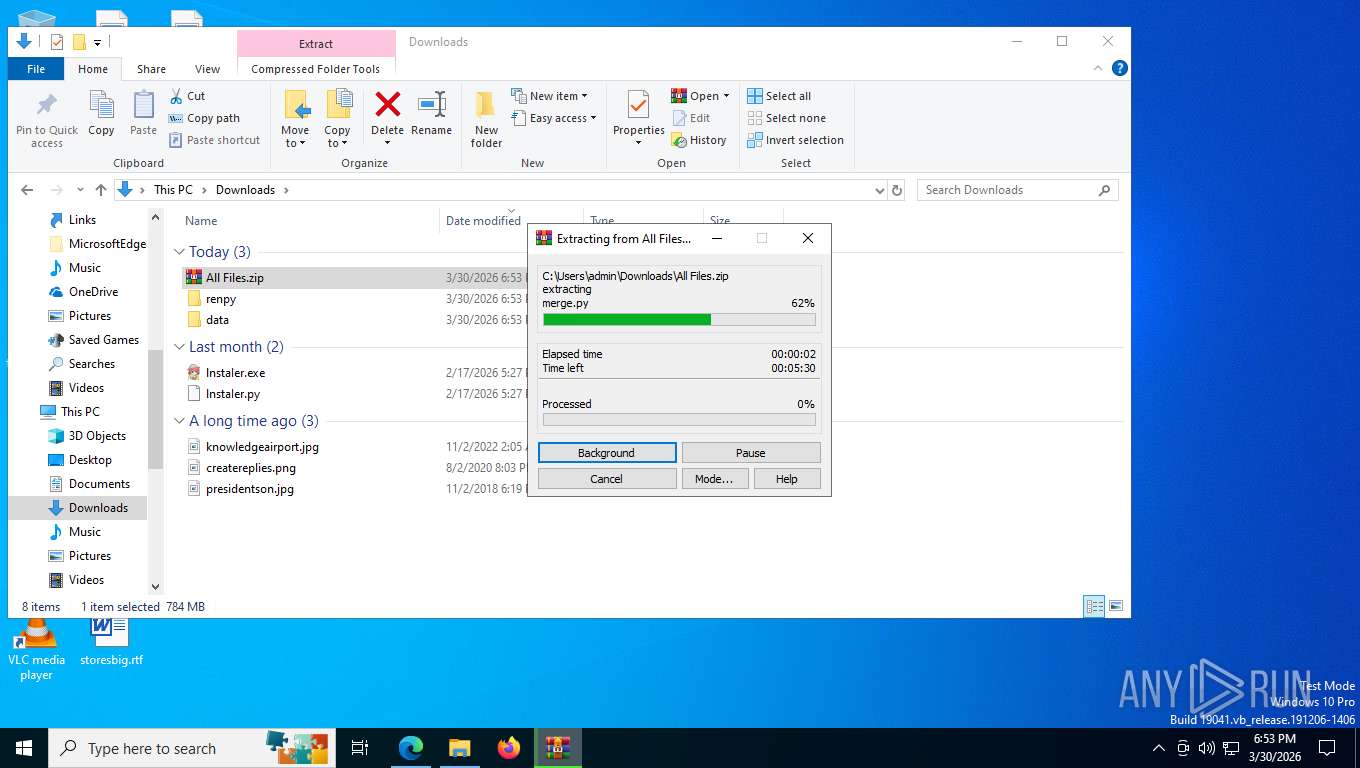
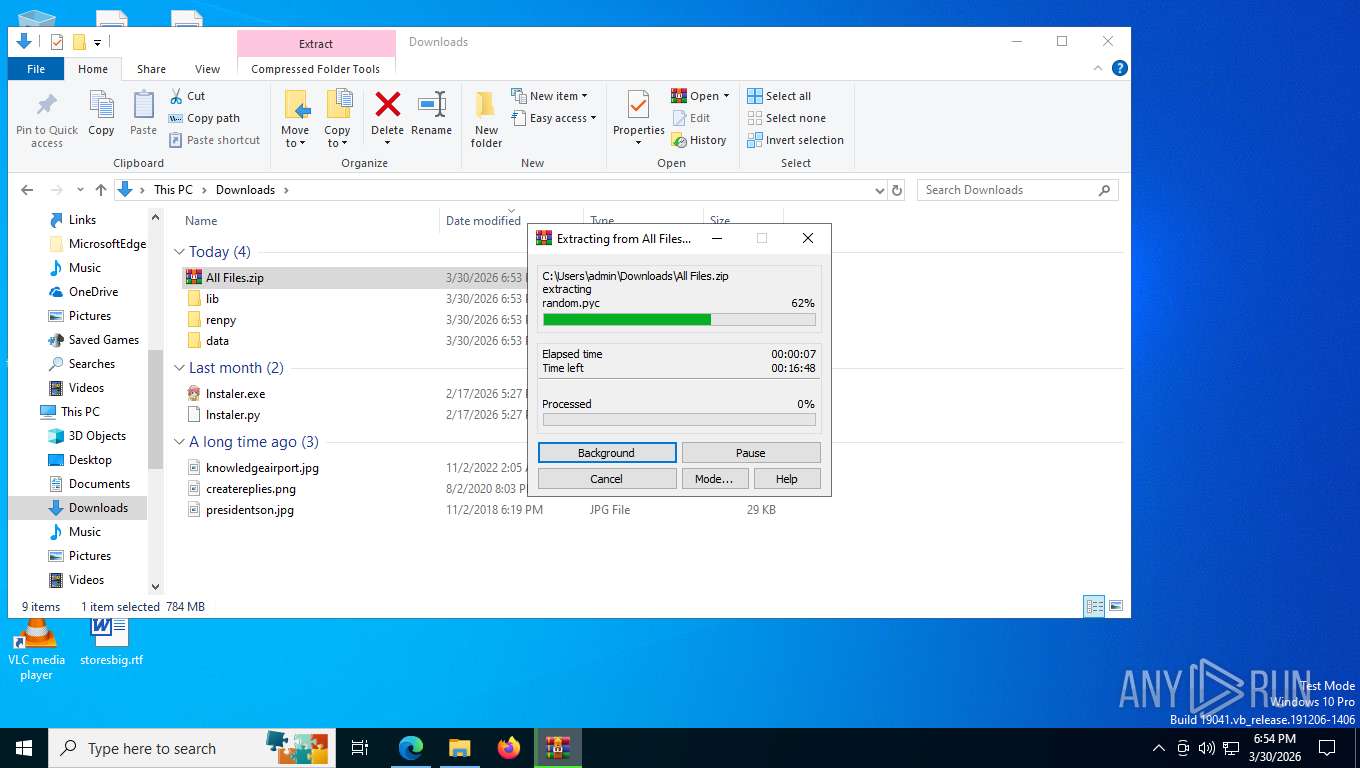
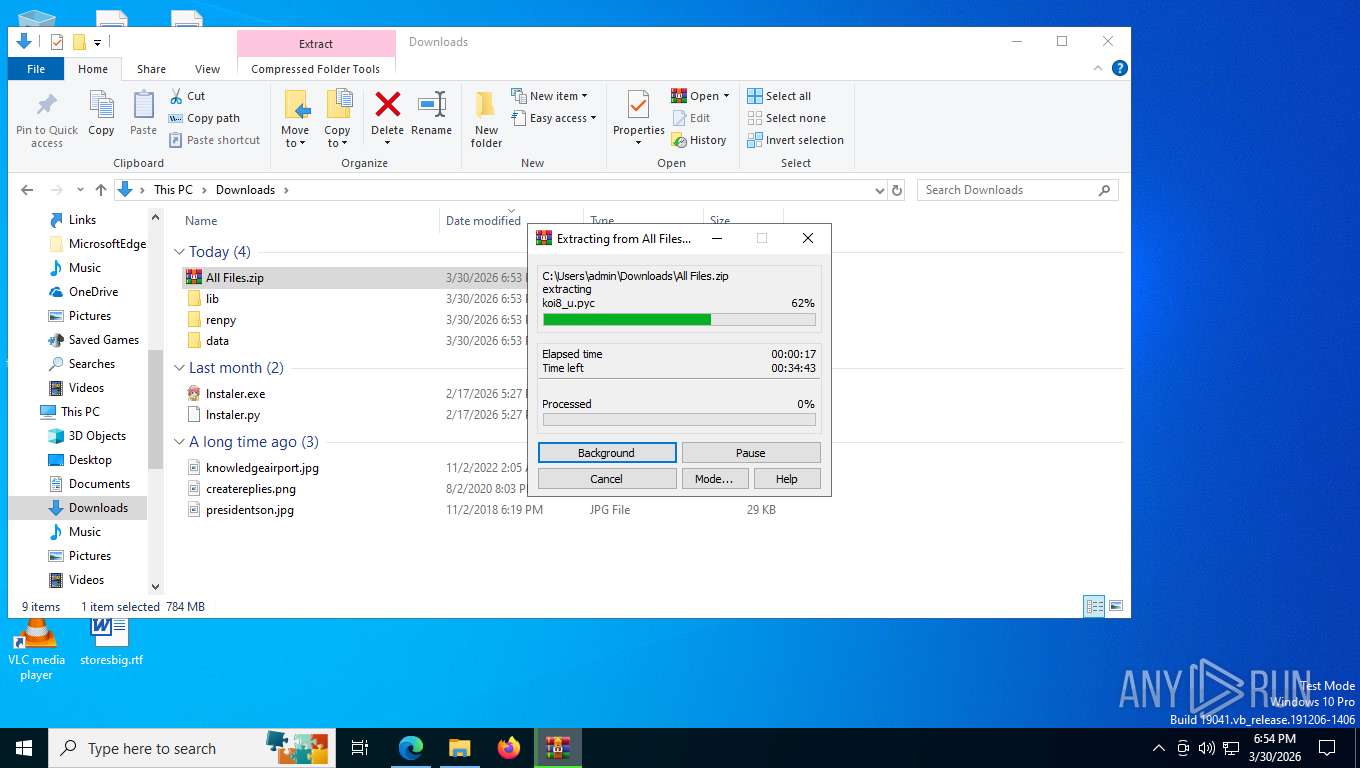
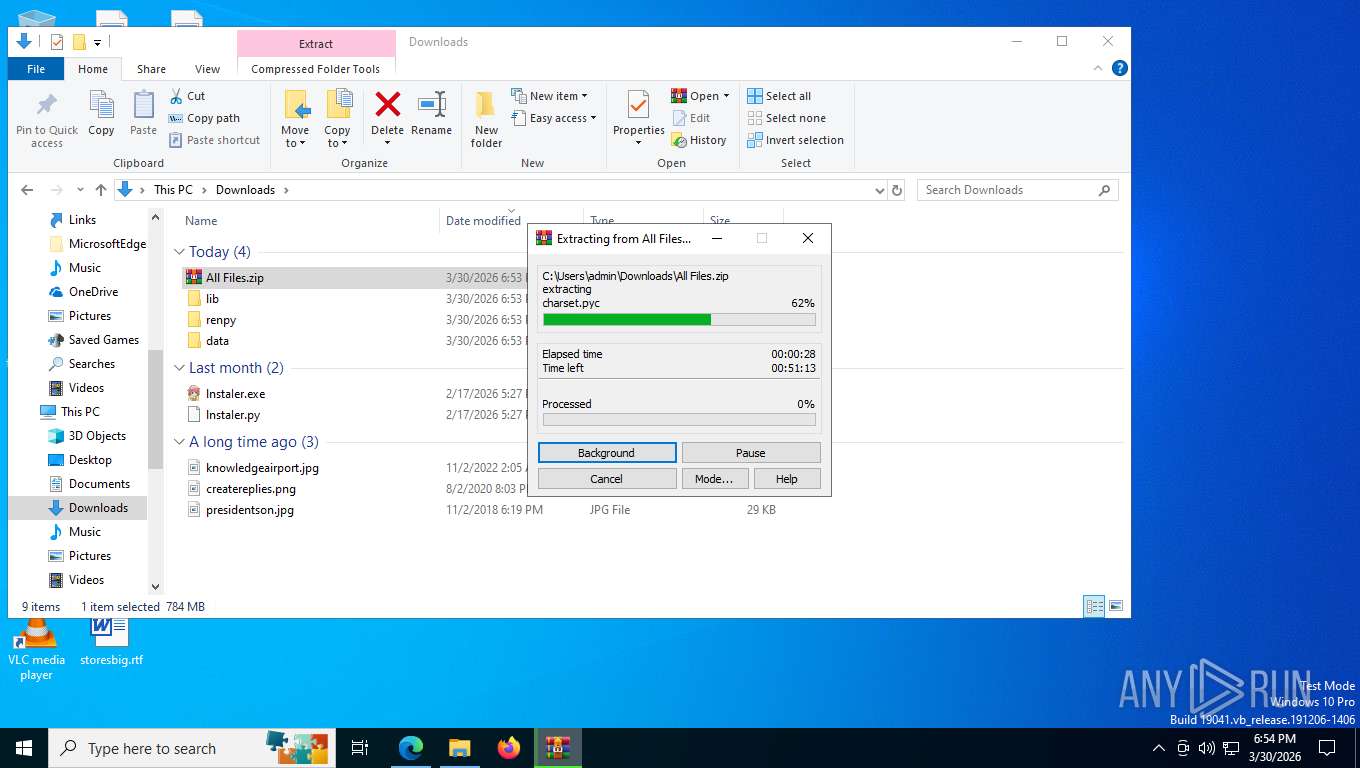
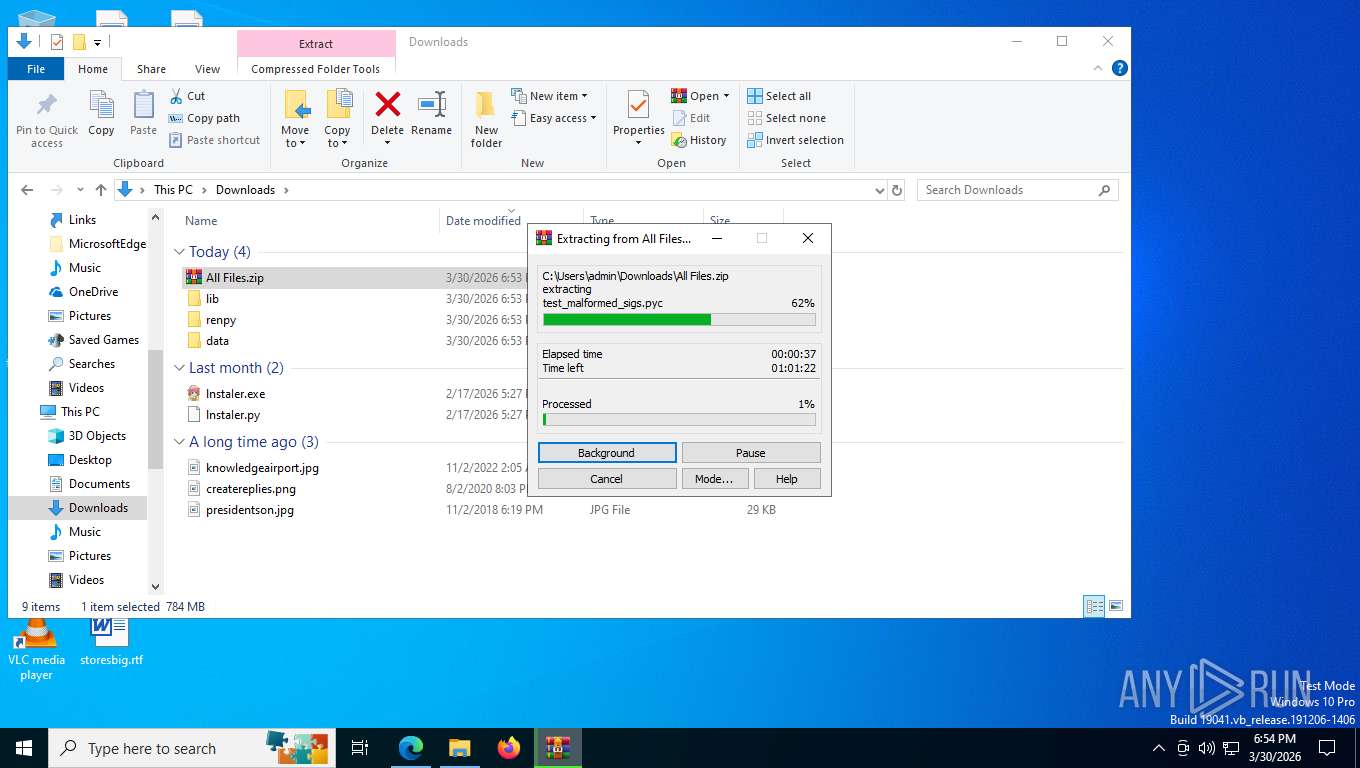
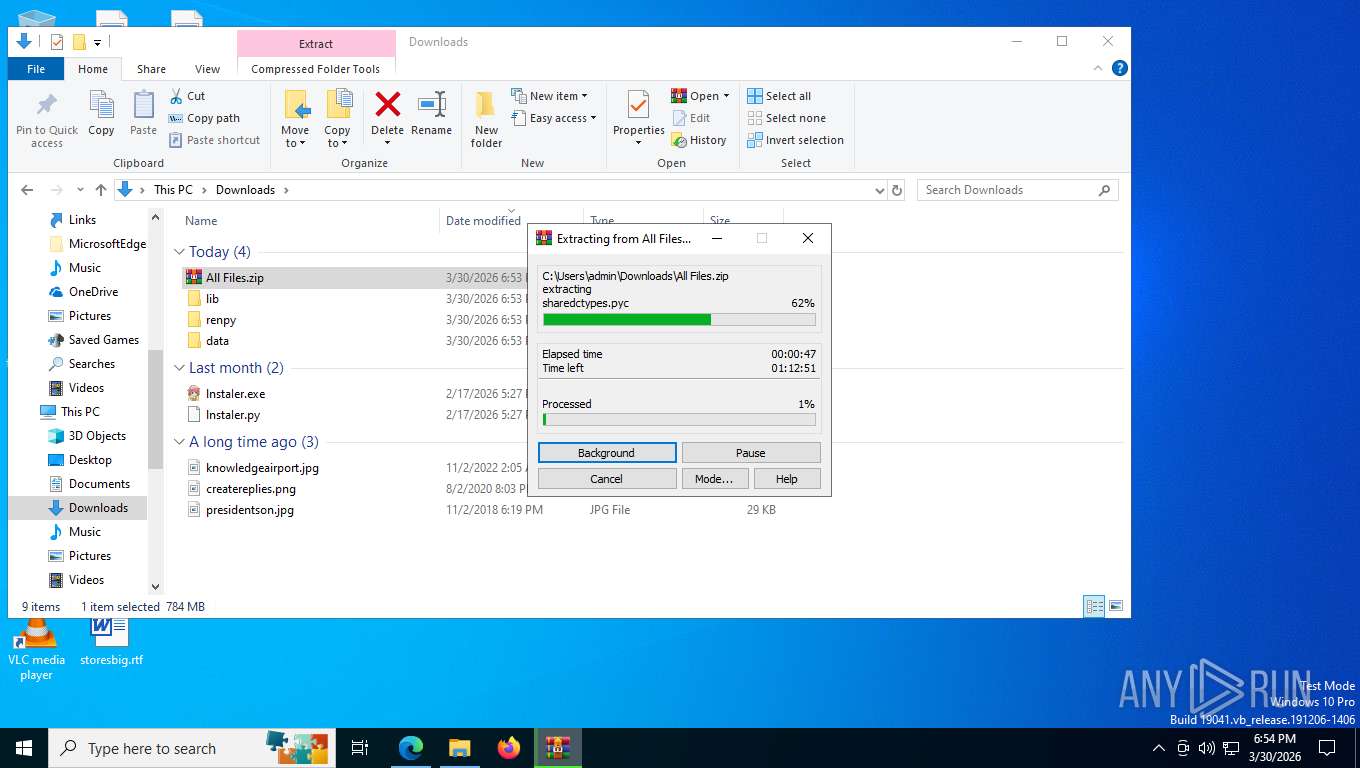
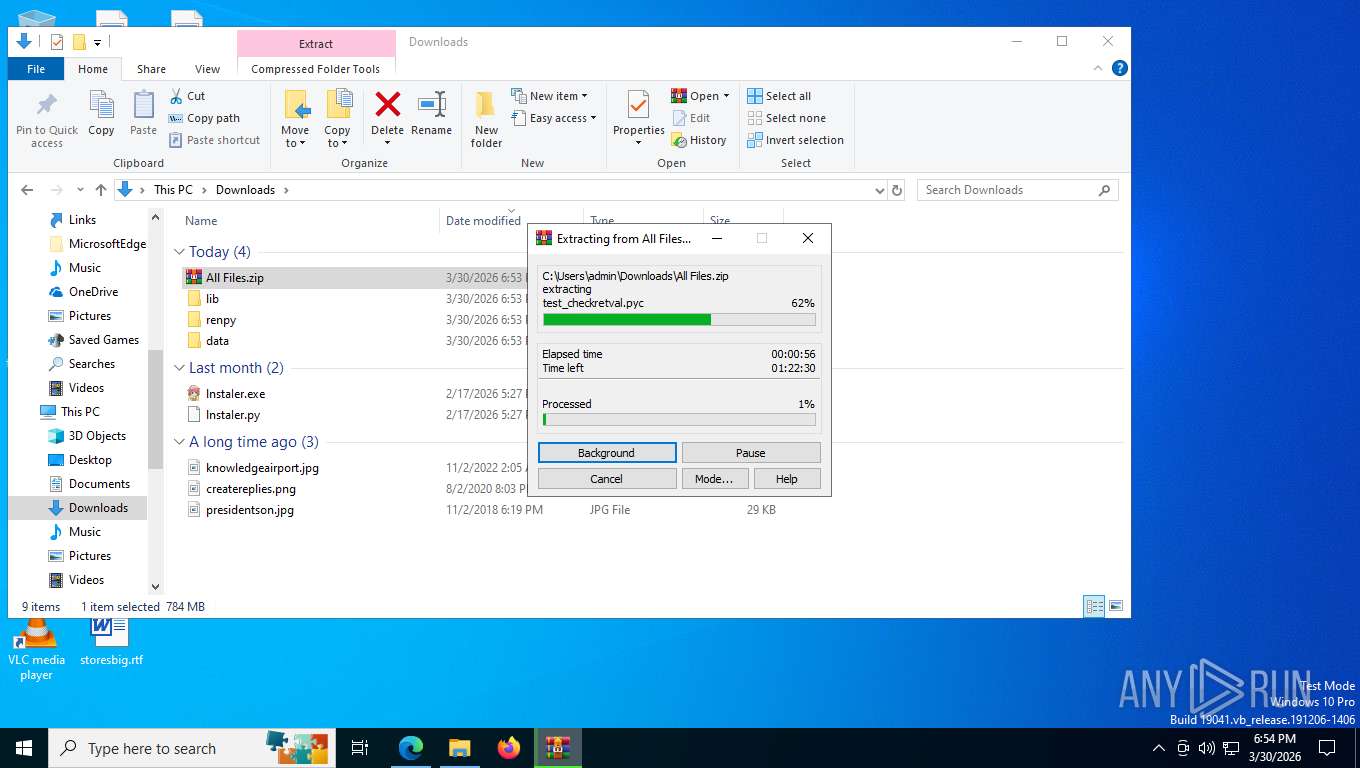
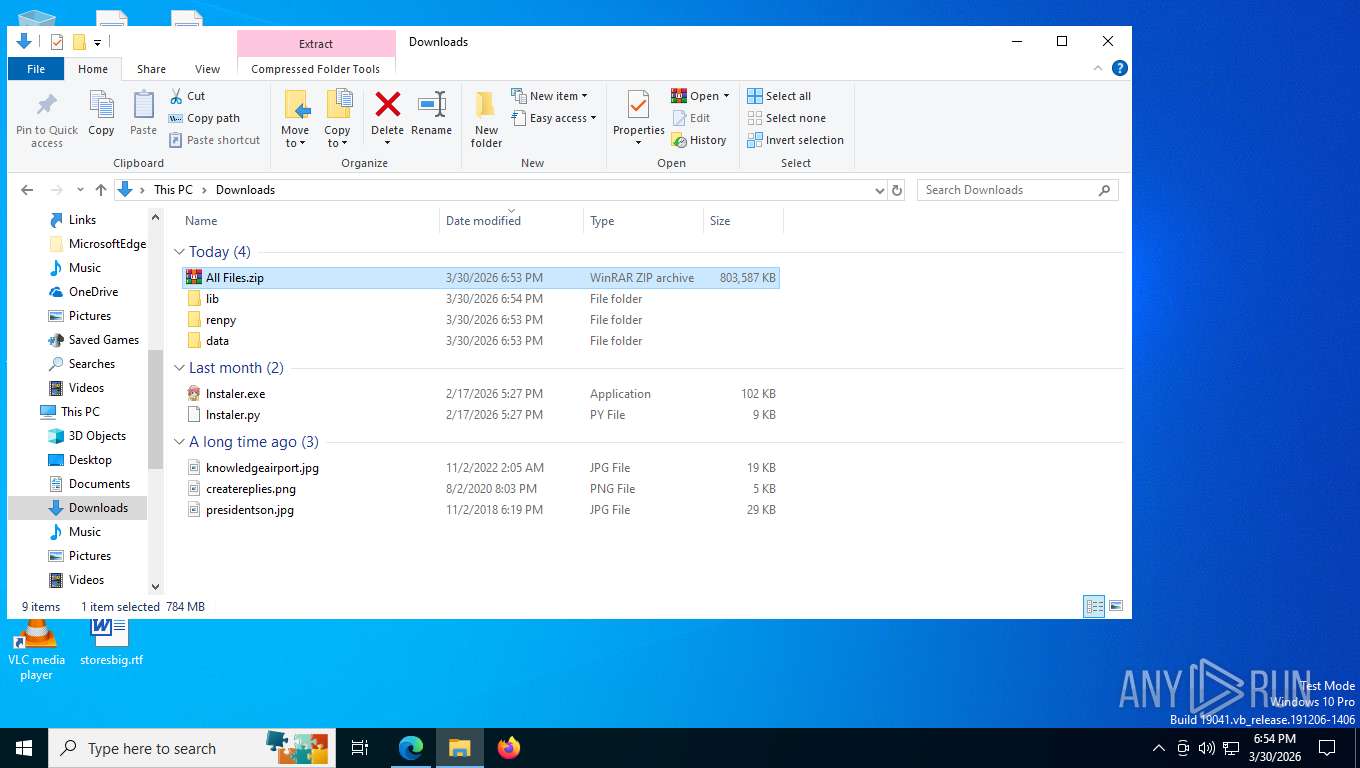
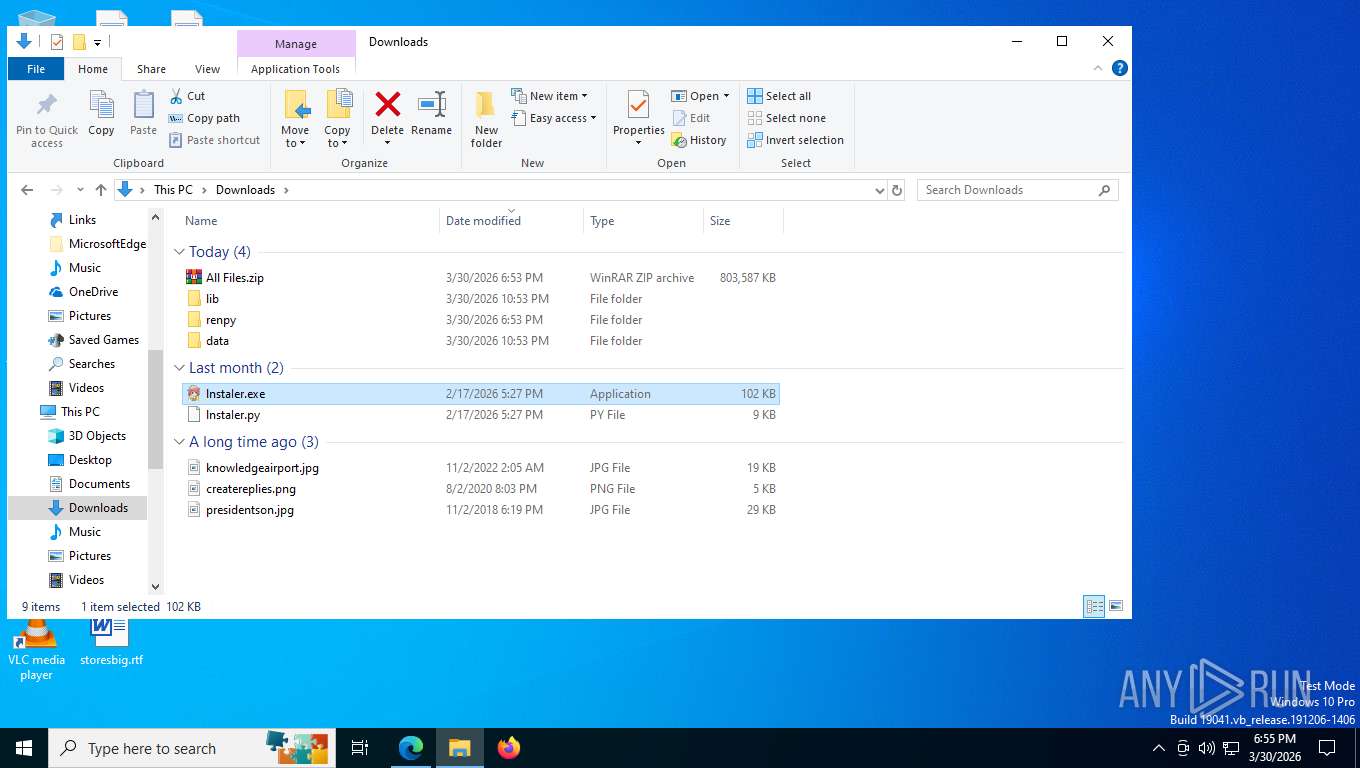
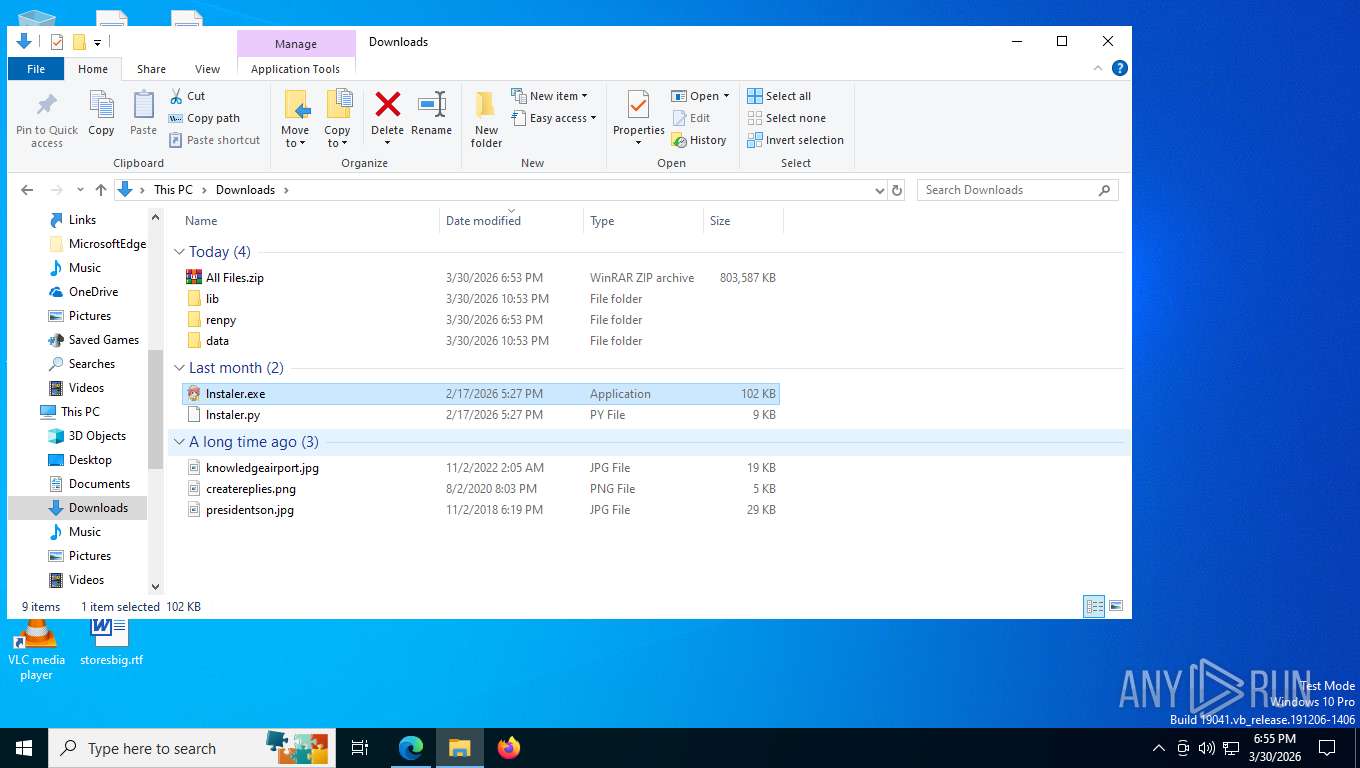
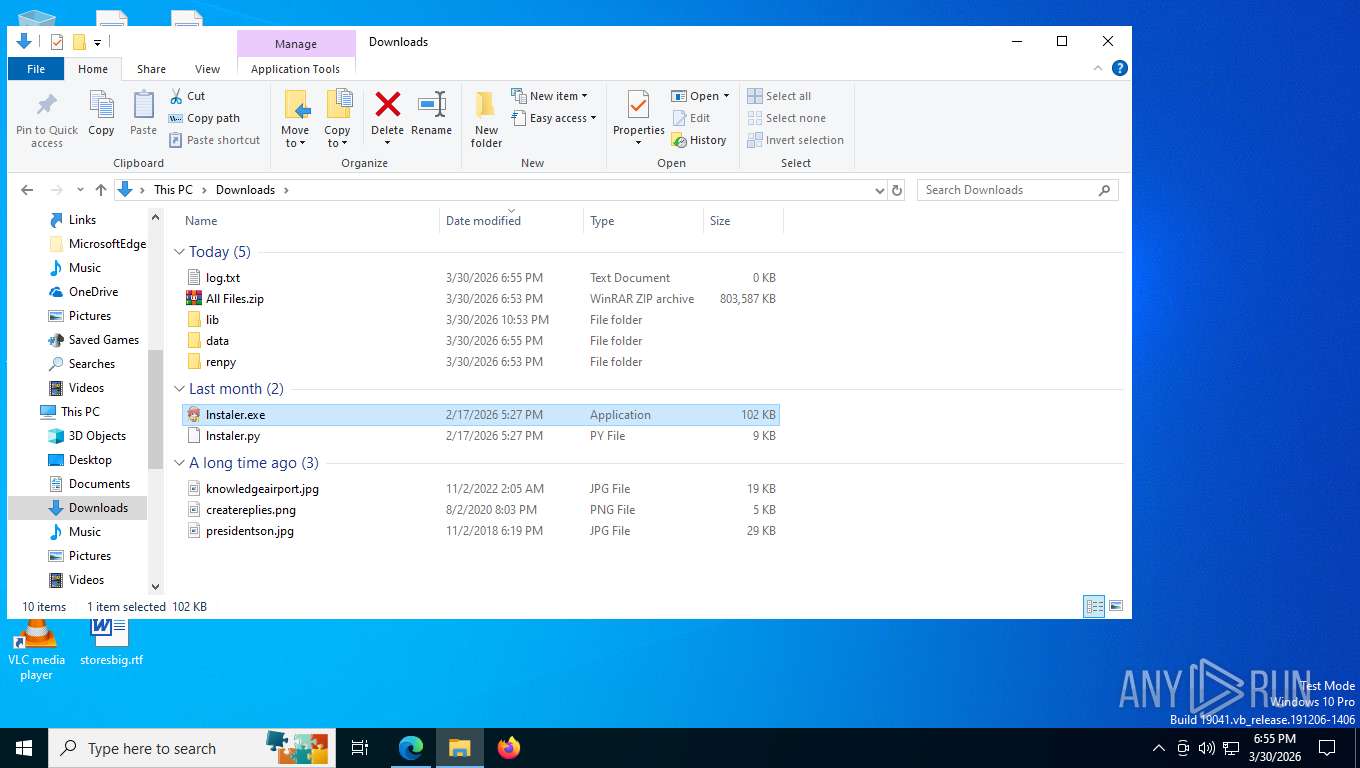
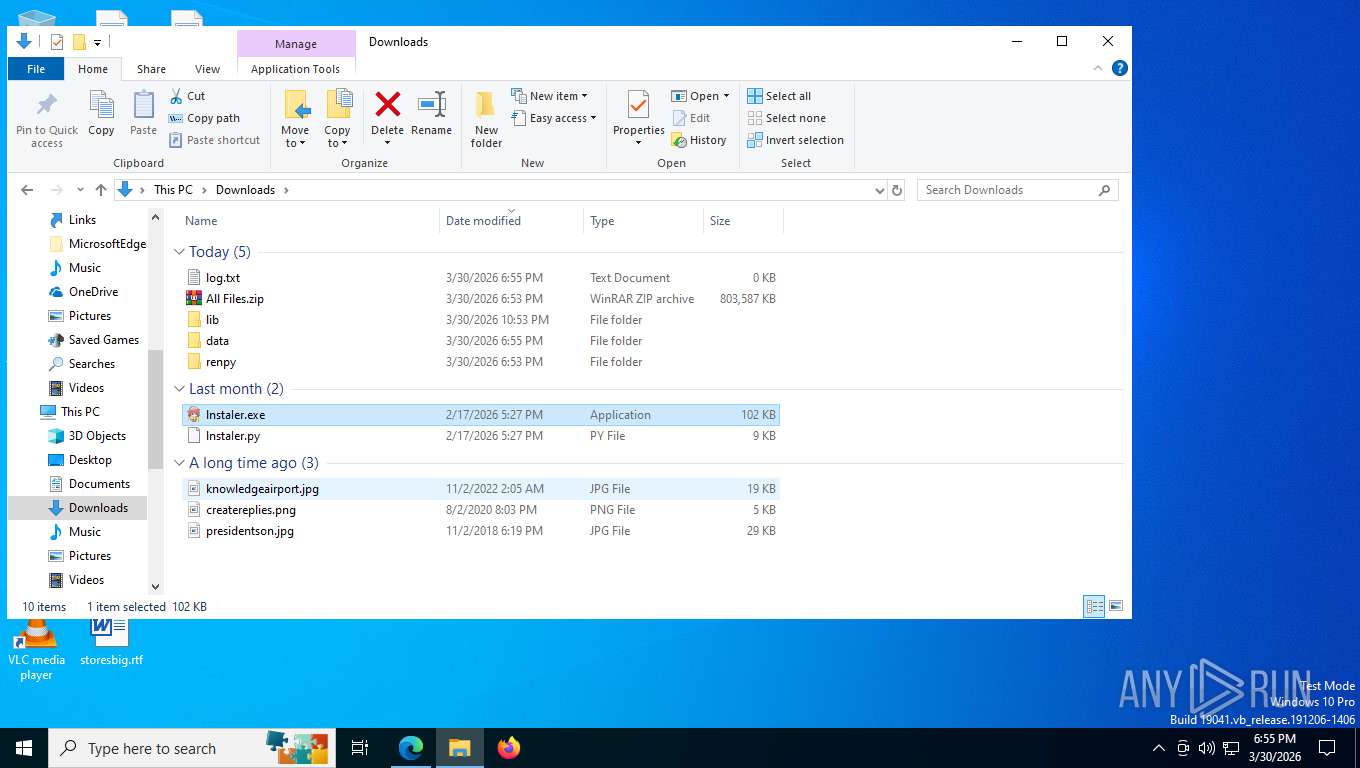
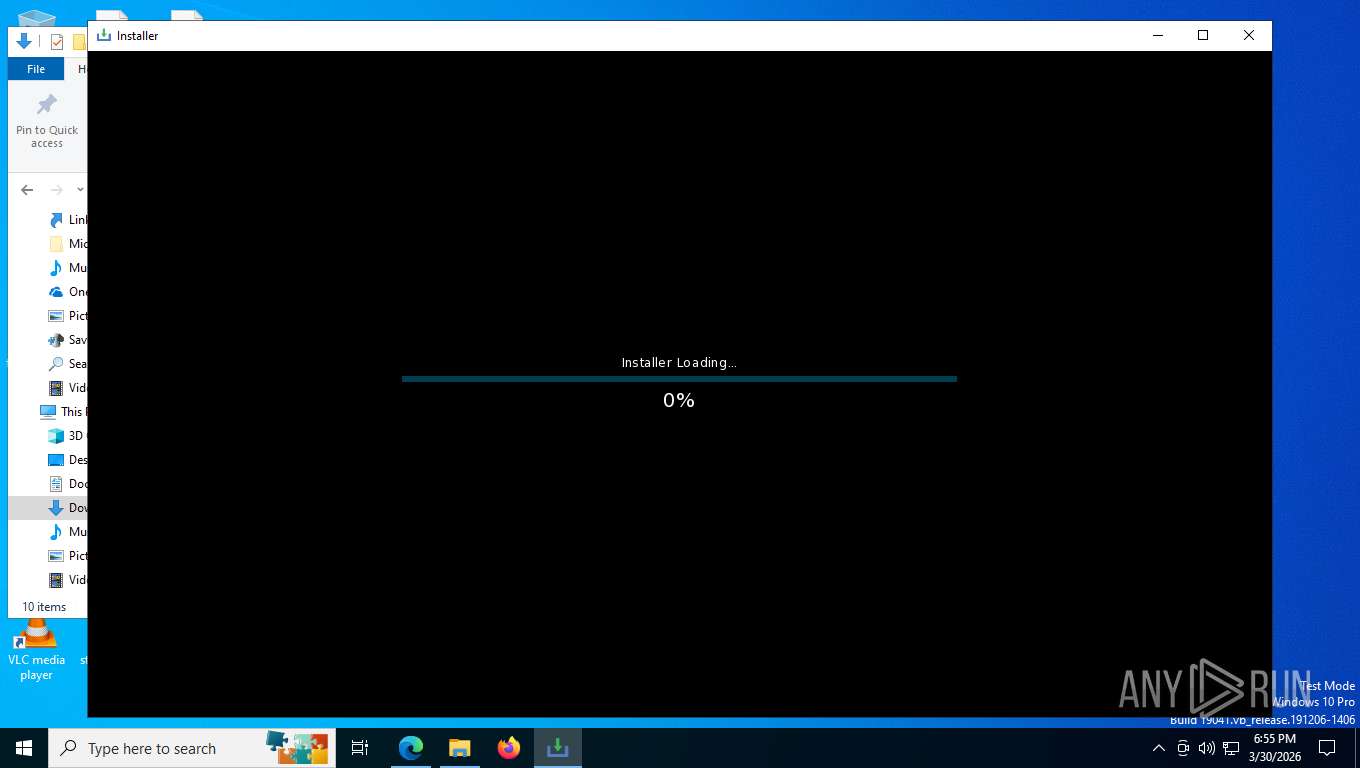
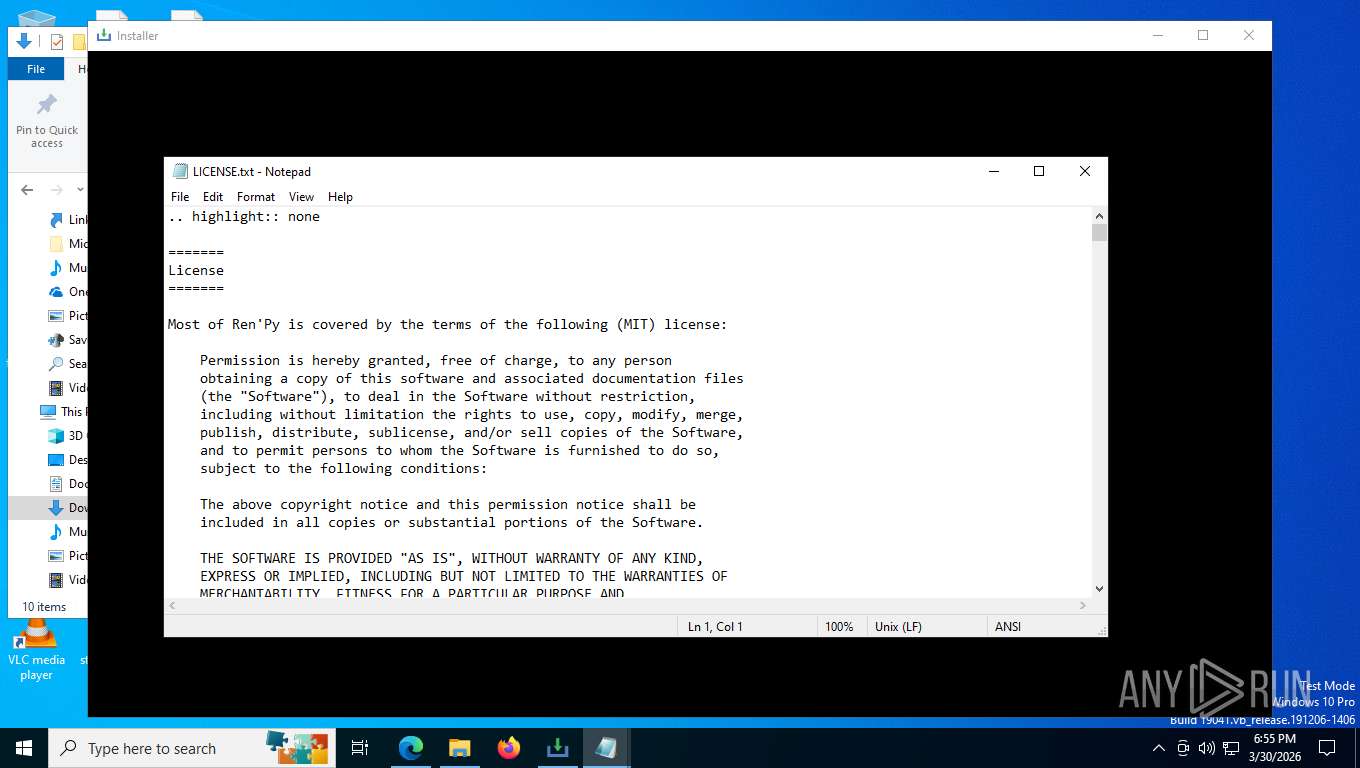
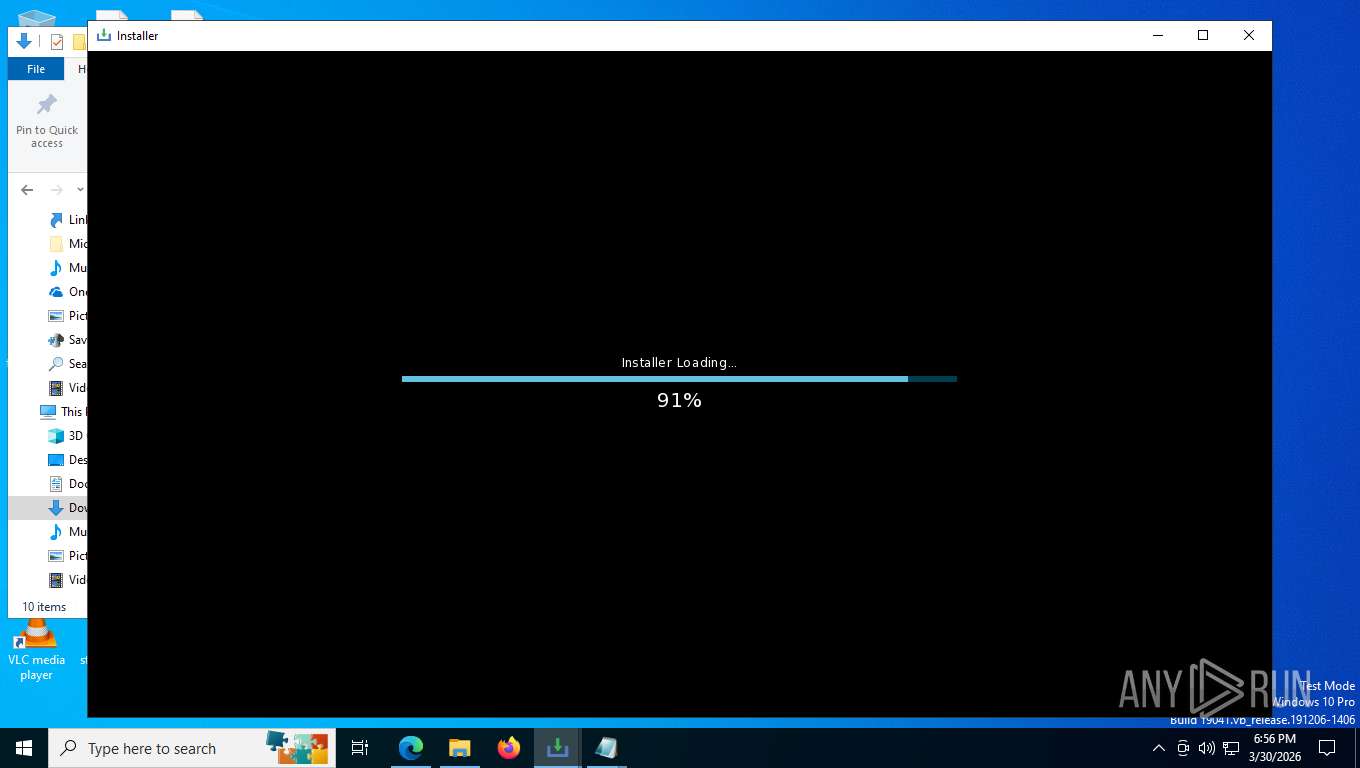
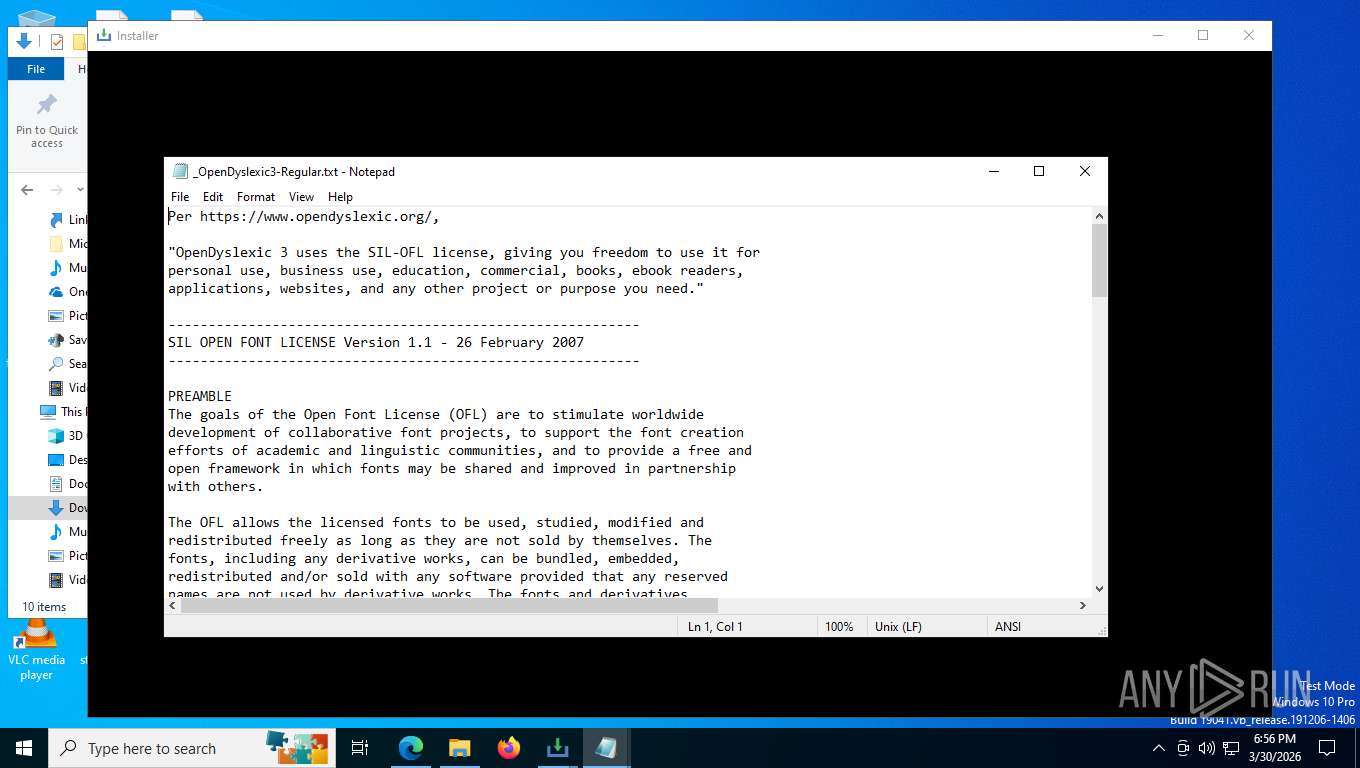
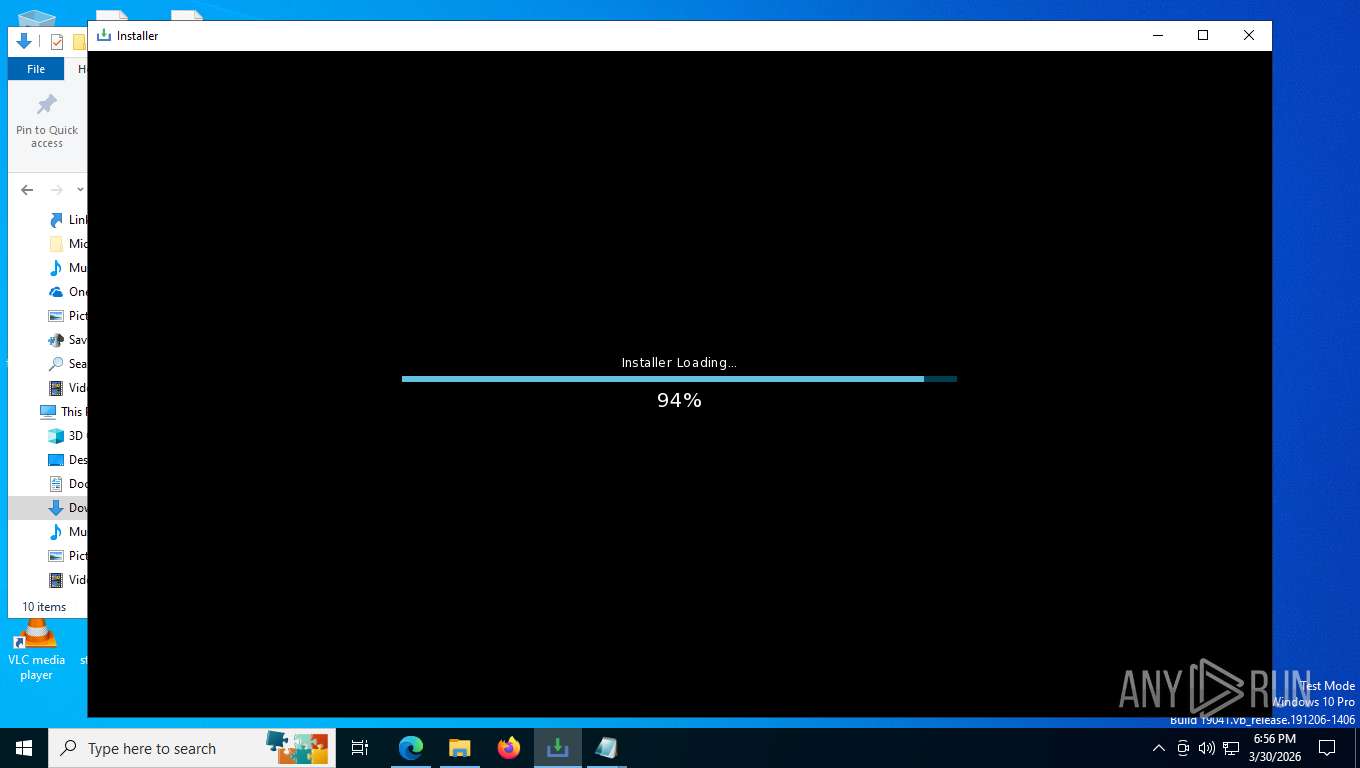
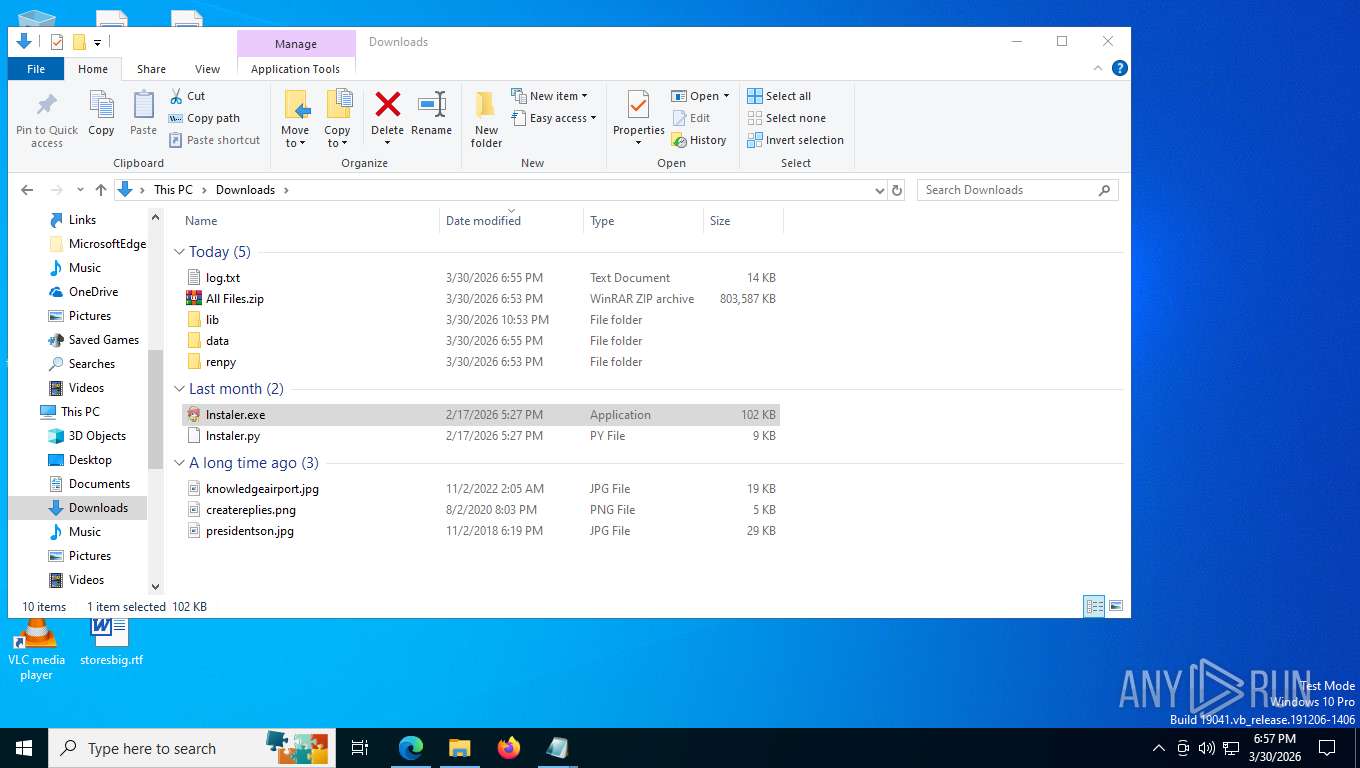
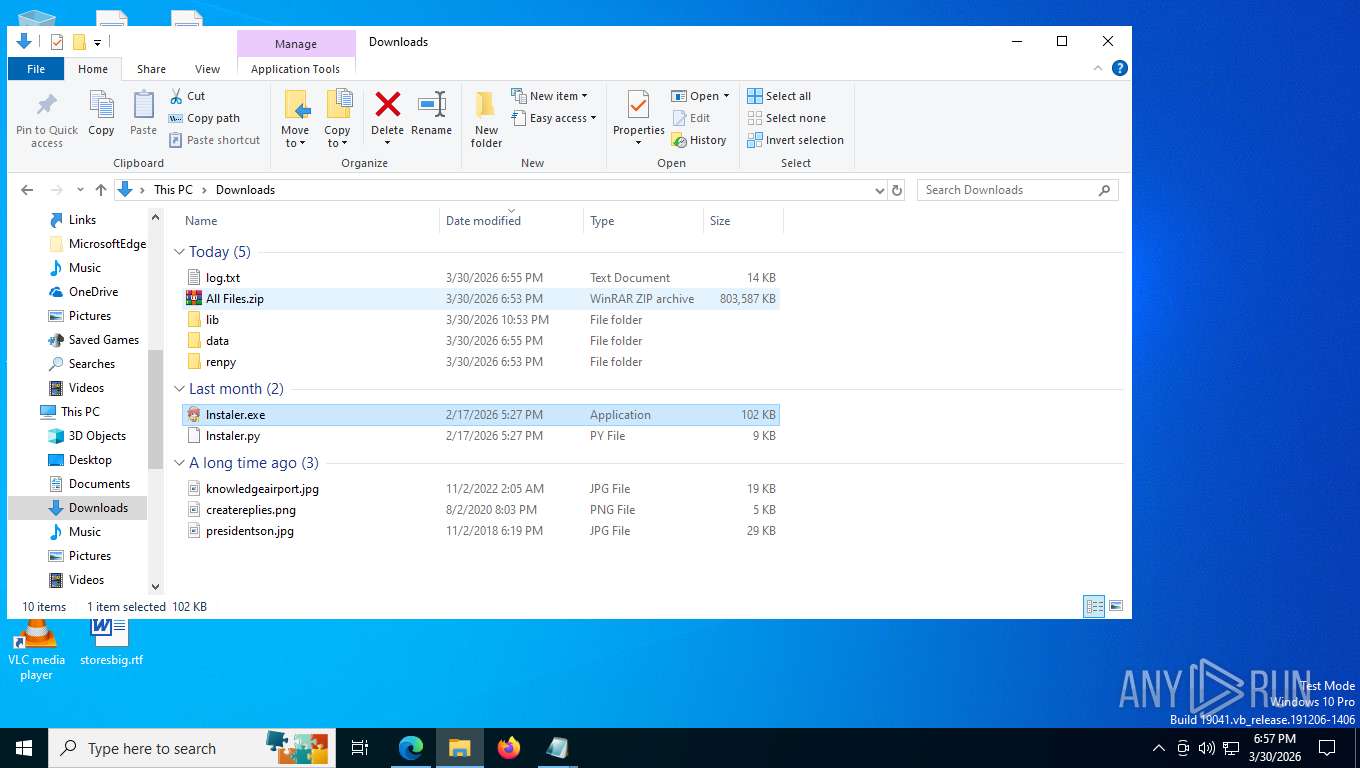
Manual execution by a user
- WinRAR.exe (PID: 8412)
- lnstaIer.exe (PID: 4336)
- notepad.exe (PID: 5568)
- notepad.exe (PID: 2728)
- lnstaIer.exe (PID: 4916)
- powershell.exe (PID: 5988)
- notepad.exe (PID: 5704)
- notepad.exe (PID: 1032)
- notepad.exe (PID: 9120)
- notepad.exe (PID: 4276)
- notepad.exe (PID: 6404)
- mspaint.exe (PID: 8664)
Checks supported languages
- lnstaIer.exe (PID: 4336)
- identity_helper.exe (PID: 5160)
- update.exe (PID: 7288)
- lnstaIer.exe (PID: 4916)
- update.exe (PID: 7500)
- csc.exe (PID: 8644)
- cvtres.exe (PID: 7276)
Checks operating system version
- lnstaIer.exe (PID: 4336)
- lnstaIer.exe (PID: 4916)
Reads the machine GUID from the registry
- lnstaIer.exe (PID: 4336)
- update.exe (PID: 7288)
- lnstaIer.exe (PID: 4916)
- update.exe (PID: 7500)
- csc.exe (PID: 8644)
Creates files or folders in the user directory
- lnstaIer.exe (PID: 4336)
- lnstaIer.exe (PID: 4916)
- PresentationSettings.exe (PID: 5716)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 8728)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 684)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 5988)
Reads the computer name
- identity_helper.exe (PID: 5160)
- lnstaIer.exe (PID: 4336)
- update.exe (PID: 7288)
- lnstaIer.exe (PID: 4916)
- update.exe (PID: 7500)
The sample compiled with english language support
- WinRAR.exe (PID: 8412)
- lnstaIer.exe (PID: 4336)
- lnstaIer.exe (PID: 4916)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8412)
There is functionality for taking screenshot (YARA)
- lnstaIer.exe (PID: 4336)
- lnstaIer.exe (PID: 4916)
Create files in a temporary directory
- lnstaIer.exe (PID: 4336)
- lnstaIer.exe (PID: 4916)
- powershell.exe (PID: 7764)
- cvtres.exe (PID: 7276)
- powershell.exe (PID: 1868)
- csc.exe (PID: 8644)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5568)
- notepad.exe (PID: 2728)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
- PresentationSettings.exe (PID: 5716)
- notepad.exe (PID: 1032)
- notepad.exe (PID: 5704)
- notepad.exe (PID: 4276)
- notepad.exe (PID: 9120)
- notepad.exe (PID: 6404)
Application based on Golang
- update.exe (PID: 7288)
Disables trace logs
- powershell.exe (PID: 7764)
- powershell.exe (PID: 684)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 5988)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 684)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 5988)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 684)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 5988)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 684)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 5988)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 684)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 5988)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 2988)
- powershell.exe (PID: 684)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 5988)
Launching a file from a Registry key
- powershell.exe (PID: 7764)
- powershell.exe (PID: 1868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
278
Monitored processes
132
Malicious processes
15
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5816,i,6994264002753618243,17103570870083388014,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7352 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 664 | C:\WINDOWS\system32\cmd.exe /c "powershell -Command "Get-CimInstance Win32_ComputerSystem | Select-Object Model"" | C:\Windows\System32\cmd.exe | — | lnstaIer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | lnstaIer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -Command ".(gal ?rm) 79.8141710/task | .('ROGieROGx'.Replace('ROG', ''))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | lnstaIer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1032 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\lib\python3.9\lib-dynload\empty.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1504 | "C:\WINDOWS\system32\schtasks.exe" /delete /tn \GoogleSystem\GoogleUpdater\GoogleUpdaterTaskSystem47.0.7703.3{47263A17-2D66-43B9-9692-30514D0C1AEC} /f | C:\Windows\System32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1824 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2288,i,6994264002753618243,17103570870083388014,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2280 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1868 | C:\WINDOWS\Sysnative\WindowsPowerShell\v1.0\powershell.exe -NoP -NoLogo -NonI -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | update.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
108 256
Read events
108 216
Write events
39
Delete events
1
Modification events
| (PID) Process: | (8412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4336) lnstaIer.exe | Key: | HKEY_CURRENT_USER\System\CurrentControlSet\Control\MediaProperties\PrivateProperties\DirectInput\VID_0627&PID_0001\Calibration\0 |
| Operation: | write | Name: | GUID |
Value: F010F3046A2CF1118001444553540000 | |||
| (PID) Process: | (7764) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows PowerShell v1.0 |
Value: C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -ExecutionPolicy Bypass -WindowStyle Hidden -Command "sal psv1 C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe; .(gal ?rm) 79.8141710/task | .('ROGieROGx'.Replace('ROG', ''))" | |||
| (PID) Process: | (1868) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows PowerShell v1.0 |
Value: C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -ExecutionPolicy Bypass -WindowStyle Hidden -Command "sal psv1 C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe; .(gal ?rm) 79.8141710/task | .('ROGieROGx'.Replace('ROG', ''))" | |||
| (PID) Process: | (5716) PresentationSettings.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5716) PresentationSettings.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5716) PresentationSettings.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
17
Suspicious files
1 502
Text files
932
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFe00f6.TMP | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe00f6.TMP | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe00f6.TMP | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe0105.TMP | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe0105.TMP | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
595
TCP/UDP connections
186
DNS requests
213
Threats
55
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7160 | msedge.exe | POST | 204 | 142.251.152.119:443 | https://www.google.com/gen_204?ei=xv7KafHAD7yPwPAPoq-18AM&vet=10ahUKEwjxu7Kw28iTAxW8BxAIHaJXDT4QhJAHCDE..s&bl=Dxyv&s=webhp&gl=no&pc=SEARCH_HOMEPAGE&isMobile=false | unknown | — | — | whitelisted |
7160 | msedge.exe | GET | 204 | 142.251.152.119:443 | https://www.google.com/gen_204?atyp=i&ct=bxjs&cad=&b=0&ei=xv7KafHAD7yPwPAPoq-18AM&zx=1774911174350&opi=89978449 | unknown | — | — | whitelisted |
7160 | msedge.exe | POST | 204 | 142.251.152.119:443 | https://www.google.com/gen_204?s=async&astyp=hpba&t=all&atyp=csi&ei=xv7Kafm2H-jGi-gP8YyEWA&rt=ipf.13,ipfr.155,ttfb.155,st.155,ipfrl.155,acrt.155,aaft.155,art.155,ns.-890&imn=0&ima=0&cb=111&ucb=101&folid=_xv7KafHAD7yPwPAPoq-18AM_7 | unknown | — | — | whitelisted |
7160 | msedge.exe | POST | 204 | 142.251.152.119:443 | https://www.google.com/gen_204?s=webhp&t=aft&atyp=csi&ei=xv7KafHAD7yPwPAPoq-18AM&rt=wsrt.771,hst.62,prt.168,afti.301,aft.301&folr=_xv7KafHAD7yPwPAPoq-18AM_7&imn=13&dtc=192&stc=43&ima=1&imad=0&imac=1&wh=650&wih=650&dch=650&nt=navigate&dt=&ts=72440&nhp=h2&ant=replace&opi=89978449 | unknown | — | — | whitelisted |
7160 | msedge.exe | GET | 204 | 142.251.152.119:443 | https://www.google.com/client_204?atyp=i&biw=1352&bih=650&ei=xv7KafHAD7yPwPAPoq-18AM&opi=89978449 | unknown | — | — | whitelisted |
7160 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 314 b | whitelisted |
7160 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1774911173&lafgdate=0 | unknown | text | 4.42 Kb | whitelisted |
7160 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
7160 | msedge.exe | POST | 204 | 142.251.152.119:443 | https://www.google.com/gen_204?atyp=csi&ei=xv7KafHAD7yPwPAPoq-18AM&s=webhp&t=all&folr=_xv7KafHAD7yPwPAPoq-18AM_7&imn=13&dtc=192&stc=43&ima=1&imad=0&imac=1&wh=650&wih=650&dch=650&nt=navigate&dt=&ts=72440&nhp=h2&ant=replace&tbdba=0&tbdaa=66&thdba=0&thdaa=0&ime=1&imeh=1&imeha=0&imehb=0&imea=0&imeb=0&imel=0&imed=0&imeeb=0&imexb=0&scp=0&cb=72140&ucb=238776<s=72440&adh=&mem=ujhs.9,tjhs.12,jhsl.2248,dm.4&nv=ne.1,feid.fff55399-fb61-4464-8e3b-6296b6886cd6&net=dl.10000,ect.4g,rtt.50,sd.0&hp=&p=bs.true&rt=hst.62,prt.168,afti.301,aft.301,xjses.309,xjsee.357,dcl.371,xjs2ls.391,xjs2es.499,xjs.503,fcp.277,lcp.277,wsrt.771,cst.0,dnst.0,rqst.212,rspt.95,sslt.0,rqstt.654,unt.541,cstt.654,dit.942&zx=1774911174717&opi=89978449 | unknown | — | — | whitelisted |
7160 | msedge.exe | GET | 301 | 142.251.110.101:443 | https://google.com/ | unknown | html | 220 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5484 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7160 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7160 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7160 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7160 | msedge.exe | 142.251.110.101:443 | google.com | GOOGLE | US | whitelisted |
7160 | msedge.exe | 13.107.253.45:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7160 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7160 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7160 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7160 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7160 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7160 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
5484 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7160 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7160 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7160 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |