| File name: | bSee.exe |
| Full analysis: | https://app.any.run/tasks/c5e75813-d7f6-4b1f-aa06-4ee4b5f91a07 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | December 02, 2023, 15:09:51 |
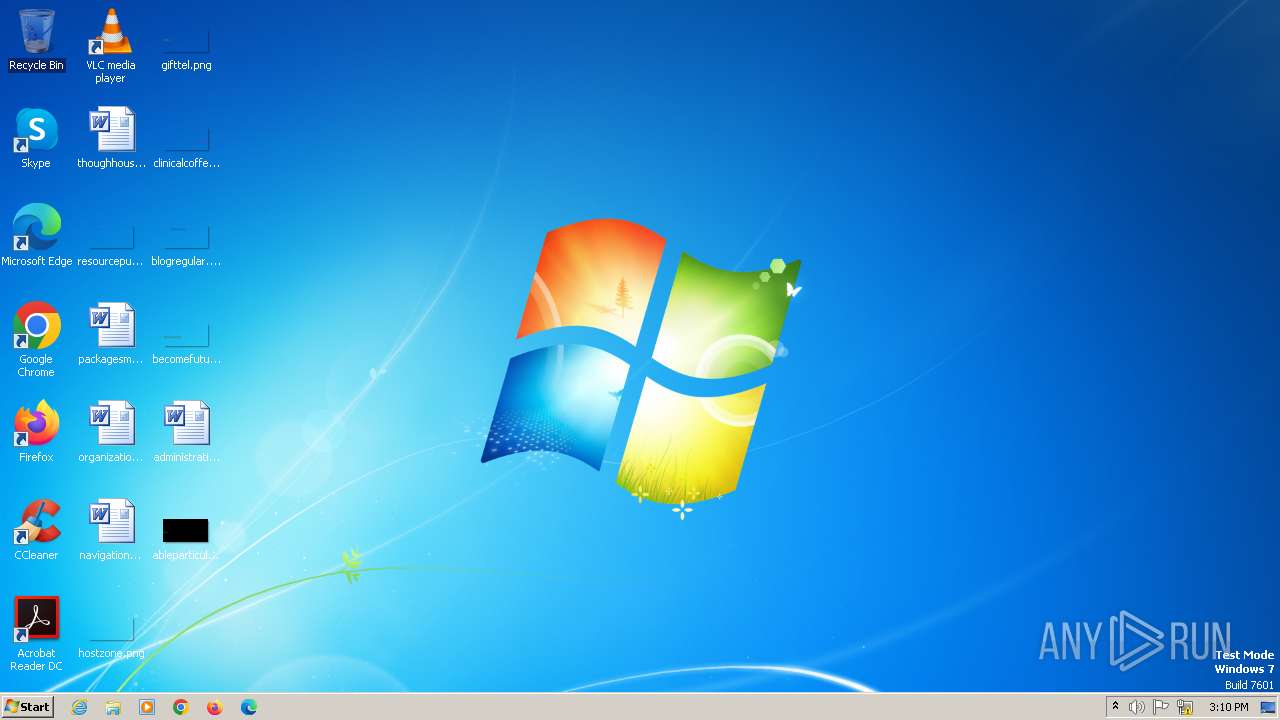
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 629CEFE795BE0F1FD1AE952CC1EB79DE |
| SHA1: | FAEDB770EFE20006272183A5F6E4C99E39754C12 |
| SHA256: | D47E620D1C305DA86A151AE4E615AEDCB53448C66808998251B407831D8F669B |
| SSDEEP: | 6144:zkjnf1OJNX5fRWdI4rDLJPq1DaMK/qbNX3OaHZ77T4RgG:zYtG9aMmY5XT4RP |
MALICIOUS
QUASAR has been detected (YARA)
- bSee.exe (PID: 2128)
SUSPICIOUS
Reads the Internet Settings
- bSee.exe (PID: 2128)
Connects to unusual port
- bSee.exe (PID: 2128)
INFO
Reads the computer name
- bSee.exe (PID: 2128)
Checks supported languages
- bSee.exe (PID: 2128)
Reads the machine GUID from the registry
- bSee.exe (PID: 2128)
Reads Environment values
- bSee.exe (PID: 2128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(2128) bSee.exe
Version1.3.0.0
C2 (2)nodetecton.ddns.net:5552
Sub_DirSubDir
Install_NameClient.exe
MutexQSR_MUTEX_PV7LCoiUmiwD1RBPCq
StartupQuasar Client Startup
TagOffice04
LogDirLogs
Signature
Certificate
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:02 14:46:48+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 352768 |
| InitializedDataSize: | 3072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5817e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.0.0 |
| ProductVersionNumber: | 1.3.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.3.0.0 |
| InternalName: | Client.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | Client.exe |
| ProductName: | - |
| ProductVersion: | 1.3.0.0 |
| AssemblyVersion: | 1.3.0.0 |
Total processes
33
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2128 | "C:\Users\admin\AppData\Local\Temp\bSee.exe" | C:\Users\admin\AppData\Local\Temp\bSee.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.3.0.0 Modules
Quasar(PID) Process(2128) bSee.exe Version1.3.0.0 C2 (2)nodetecton.ddns.net:5552 Sub_DirSubDir Install_NameClient.exe MutexQSR_MUTEX_PV7LCoiUmiwD1RBPCq StartupQuasar Client Startup TagOffice04 LogDirLogs Signature Certificate | |||||||||||||||
Total events
391
Read events
391
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
12
DNS requests
6
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2128 | bSee.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
2128 | bSee.exe | 172.67.75.176:80 | freegeoip.net | CLOUDFLARENET | US | unknown |
2128 | bSee.exe | 104.237.62.212:80 | api.ipify.org | WEBNX | US | unknown |
2128 | bSee.exe | 179.104.80.89:5552 | nodetecton.ddns.net | ALGAR TELECOM SA | BR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| shared |
freegeoip.net |
| shared |
api.ipify.org |
| shared |
nodetecton.ddns.net |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
324 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (freegeiop .net in DNS lookup) |
324 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
324 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
324 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |