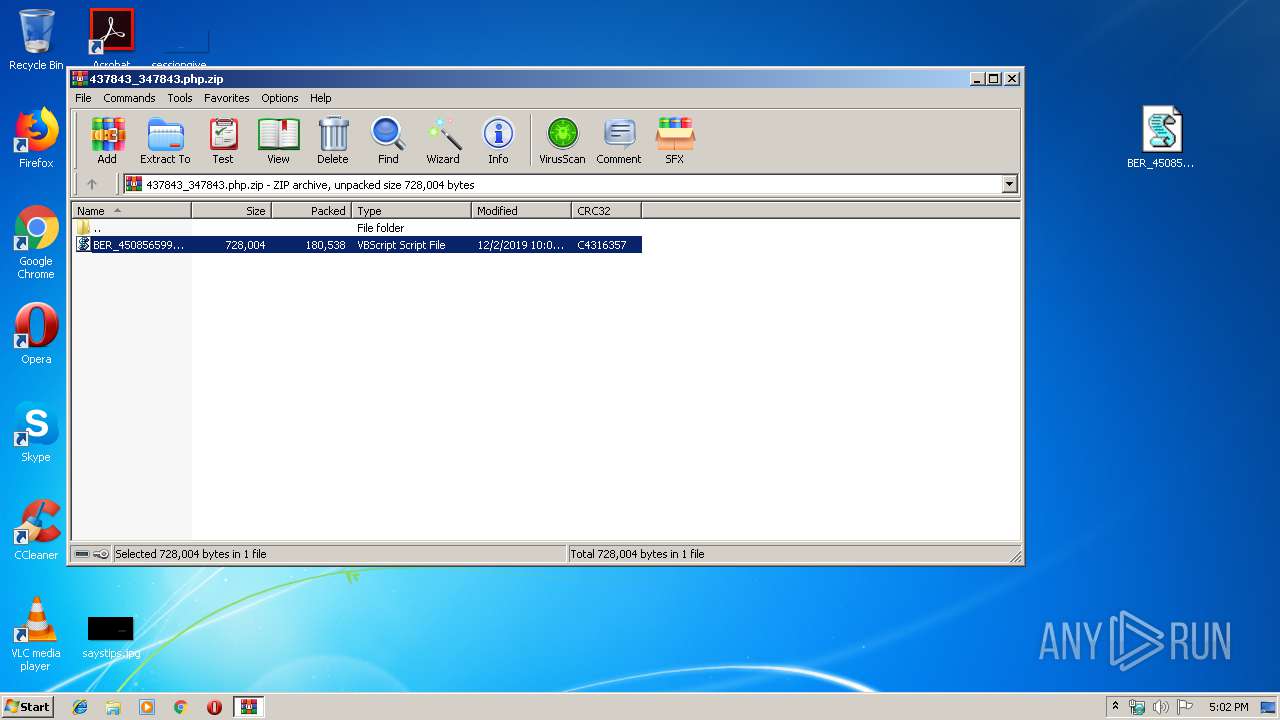
| download: | 437843_347843.php |
| Full analysis: | https://app.any.run/tasks/aaaadbb5-06a1-4002-9985-ff25cea25a59 |
| Verdict: | Malicious activity |
| Threats: | Hancitor was created in 2014 to drop other malware on infected machines. It is also known as Tordal and Chanitor. This malware is available as a service which makes it accessible tools to criminals and contributes to the popularity of this virus. |
| Analysis date: | December 02, 2019, 17:01:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
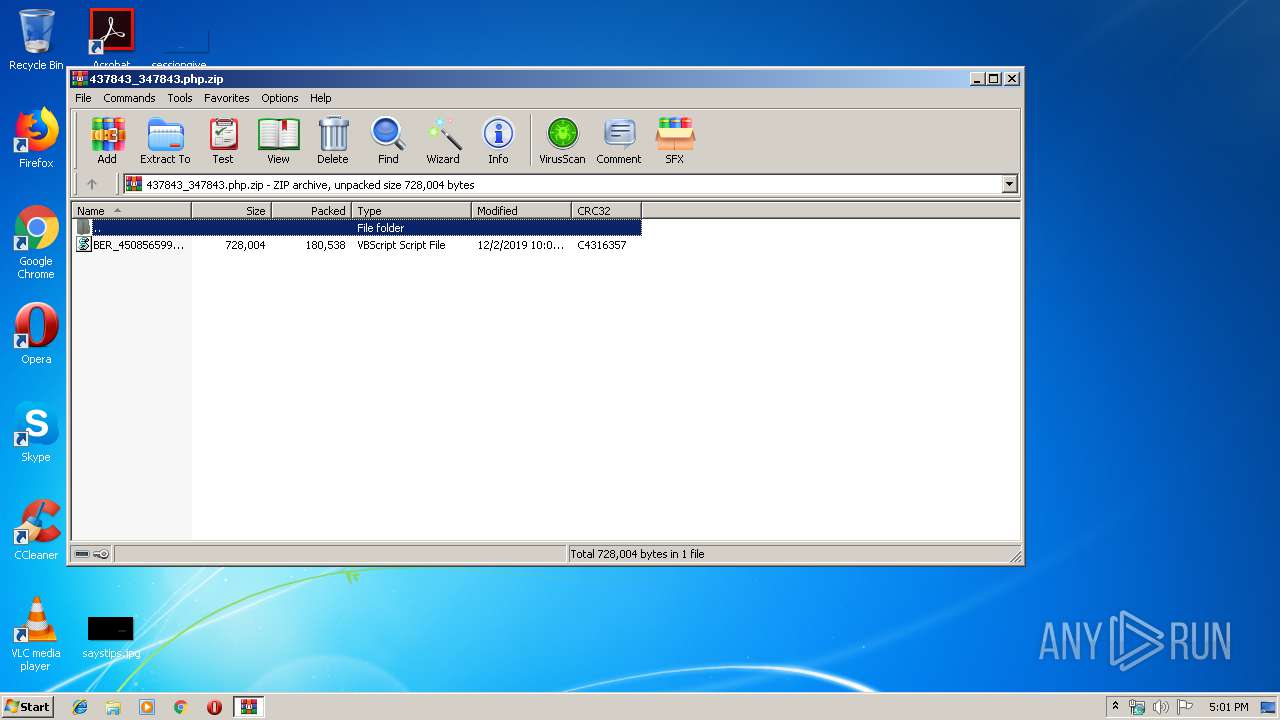
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7945D30F81563B898A6539CB3C3BE6B4 |
| SHA1: | B38F866458BBADCF4906AEEFFF78F619822F6686 |
| SHA256: | D43881293C066D49F69F313E66E3C94FB1EE52D2F6A5C0BEF072813DE8AFEE3A |
| SSDEEP: | 3072:YGocEW82aaREanMEp8xxpFzteaFTqxgDXIsoRxrb1KG5to2SQdLs748AwYq+cs5:YGocEdSRfMW8xx7zteaFOxgbIsorProW |
MALICIOUS
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3196)
Detected Pony/Fareit Trojan
- svchost.exe (PID: 4052)
Actions looks like stealing of personal data
- svchost.exe (PID: 4052)
- svchost.exe (PID: 2868)
Uses SVCHOST.EXE for hidden code execution
- regsvr32.exe (PID: 3196)
- svchost.exe (PID: 4052)
Connects to CnC server
- svchost.exe (PID: 2868)
- svchost.exe (PID: 4052)
PONY was detected
- svchost.exe (PID: 2868)
HANCITOR was detected
- svchost.exe (PID: 4052)
SUSPICIOUS
Checks for external IP
- svchost.exe (PID: 4052)
Executed via WMI
- regsvr32.exe (PID: 3196)
Application launched itself
- svchost.exe (PID: 4052)
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 4052)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 4052)
Searches for installed software
- svchost.exe (PID: 4052)
Executable content was dropped or overwritten
- WScript.exe (PID: 2584)
INFO
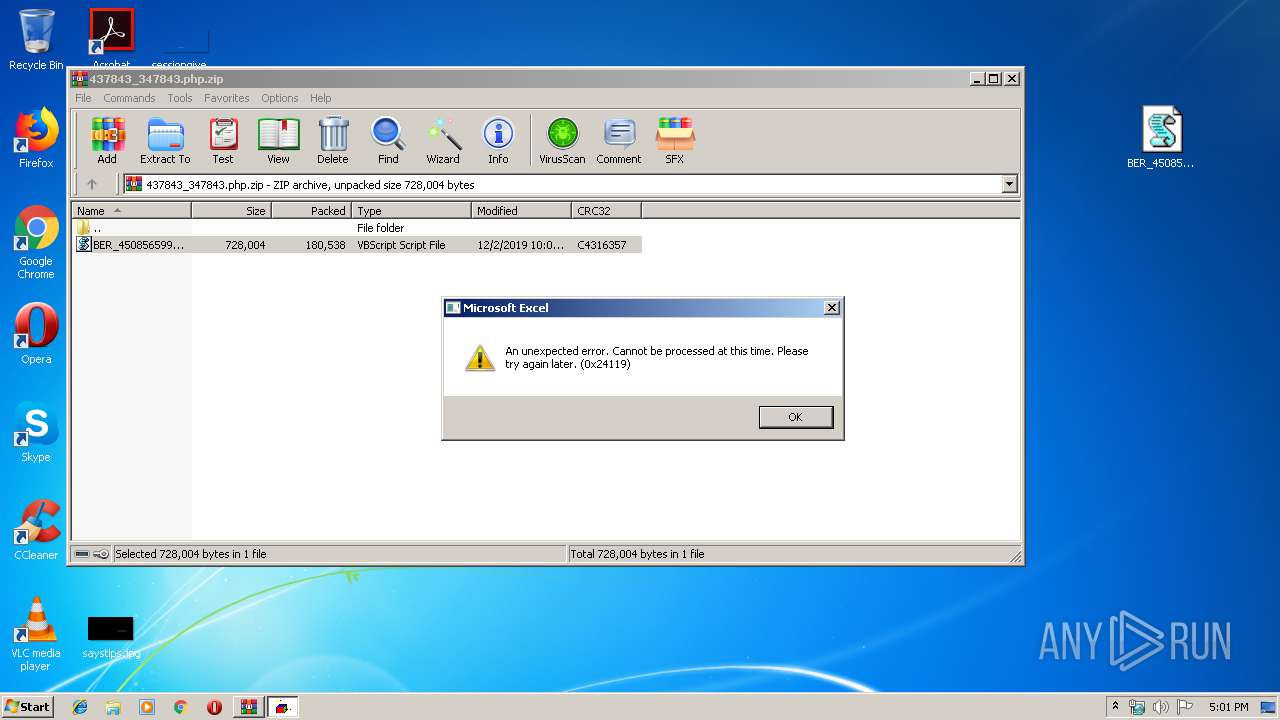
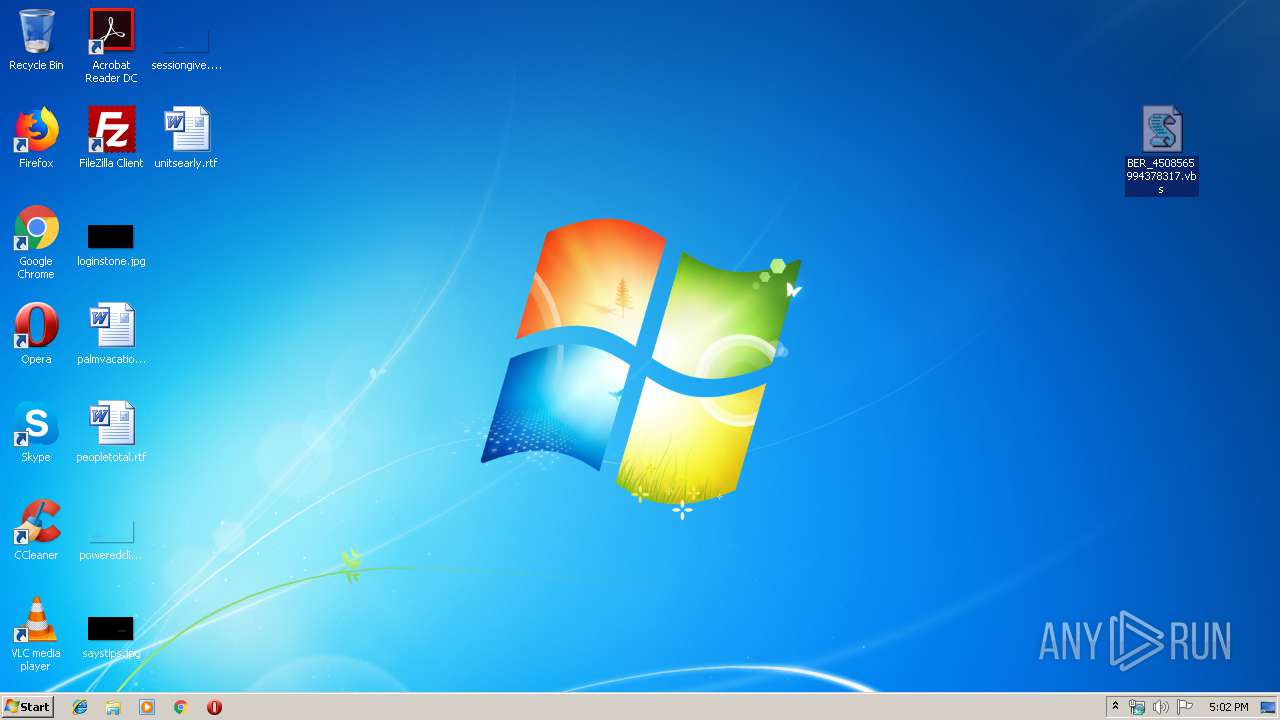
Manual execution by user
- WScript.exe (PID: 2584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:02 22:09:27 |
| ZipCRC: | 0xc4316357 |
| ZipCompressedSize: | 180538 |
| ZipUncompressedSize: | 728004 |
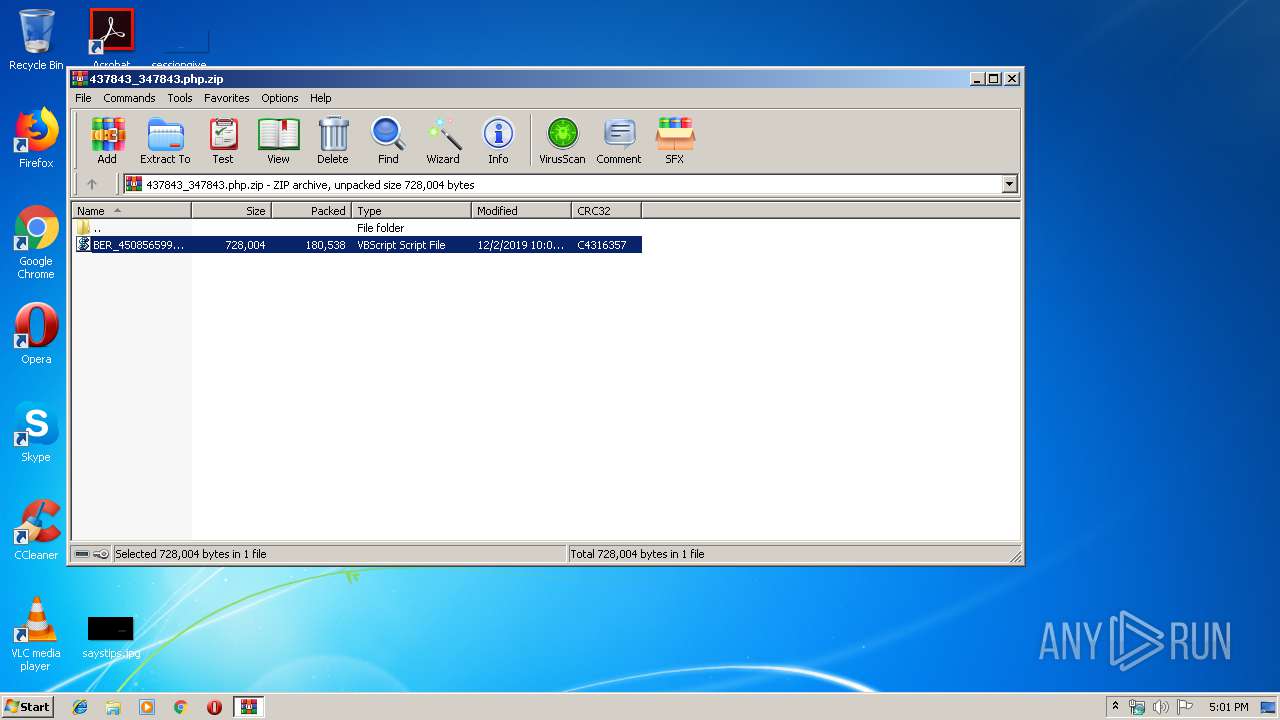
| ZipFileName: | BER_4508565994378317.vbs |
Total processes
41
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2584 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\BER_4508565994378317.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\437843_347843.php.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2868 | C:\Windows\System32\svchost.exe | C:\Windows\System32\svchost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3196 | regsvr32.exe -s C:\Users\admin\AppData\Local\Temp\gyMbJva.txt | C:\Windows\system32\regsvr32.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3584 | cmd /K | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4052 | C:\Windows\System32\svchost.exe | C:\Windows\System32\svchost.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
914
Read events
871
Write events
43
Delete events
0
Modification events
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\437843_347843.php.zip | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (2584) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2784 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2784.11696\BER_4508565994378317.vbs | — | |
MD5:— | SHA256:— | |||
| 2584 | WScript.exe | C:\Users\admin\AppData\Local\Temp\Rofrm.txt | — | |
MD5:— | SHA256:— | |||
| 2584 | WScript.exe | C:\Users\admin\AppData\Local\Temp\gyMbJva.txt | executable | |
MD5:— | SHA256:— | |||
| 2584 | WScript.exe | C:\Users\admin\AppData\Local\Temp\Rofrm.txt.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
4
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2868 | svchost.exe | POST | — | 178.170.248.82:80 | http://laticivue.com/d2/about.php | RU | — | — | malicious |
4052 | svchost.exe | GET | 200 | 2.57.89.115:80 | http://www.laadlifashionworld.com/1 | unknown | binary | 45.2 Kb | malicious |
4052 | svchost.exe | POST | 200 | 178.170.248.82:80 | http://laticivue.com/4/forum.php | RU | text | 420 b | malicious |
4052 | svchost.exe | POST | — | 178.170.248.82:80 | http://laticivue.com/mlu/forum.php | RU | — | — | malicious |
4052 | svchost.exe | GET | 200 | 2.57.89.115:80 | http://www.laadlifashionworld.com/2 | unknown | binary | 46.2 Kb | malicious |
4052 | svchost.exe | GET | 200 | 54.225.243.96:80 | http://api.ipify.org/ | US | text | 12 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4052 | svchost.exe | 178.170.248.82:80 | laticivue.com | Electrics Ltd | RU | malicious |
4052 | svchost.exe | 54.225.243.96:80 | api.ipify.org | Amazon.com, Inc. | US | suspicious |
2868 | svchost.exe | 178.170.248.82:80 | laticivue.com | Electrics Ltd | RU | malicious |
4052 | svchost.exe | 2.57.89.115:80 | www.laadlifashionworld.com | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
laticivue.com |
| malicious |
www.laadlifashionworld.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4052 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
4052 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony/Hancitor Payload (Zeus) |
4052 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
4052 | svchost.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
4052 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Pony encrypted POST Data Request |
4052 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony/Hancitor Payload (Zeus) |
2868 | svchost.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
2868 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Pony encrypted POST Data Request |
4052 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Pony encrypted C2 Response |
3 ETPRO signatures available at the full report