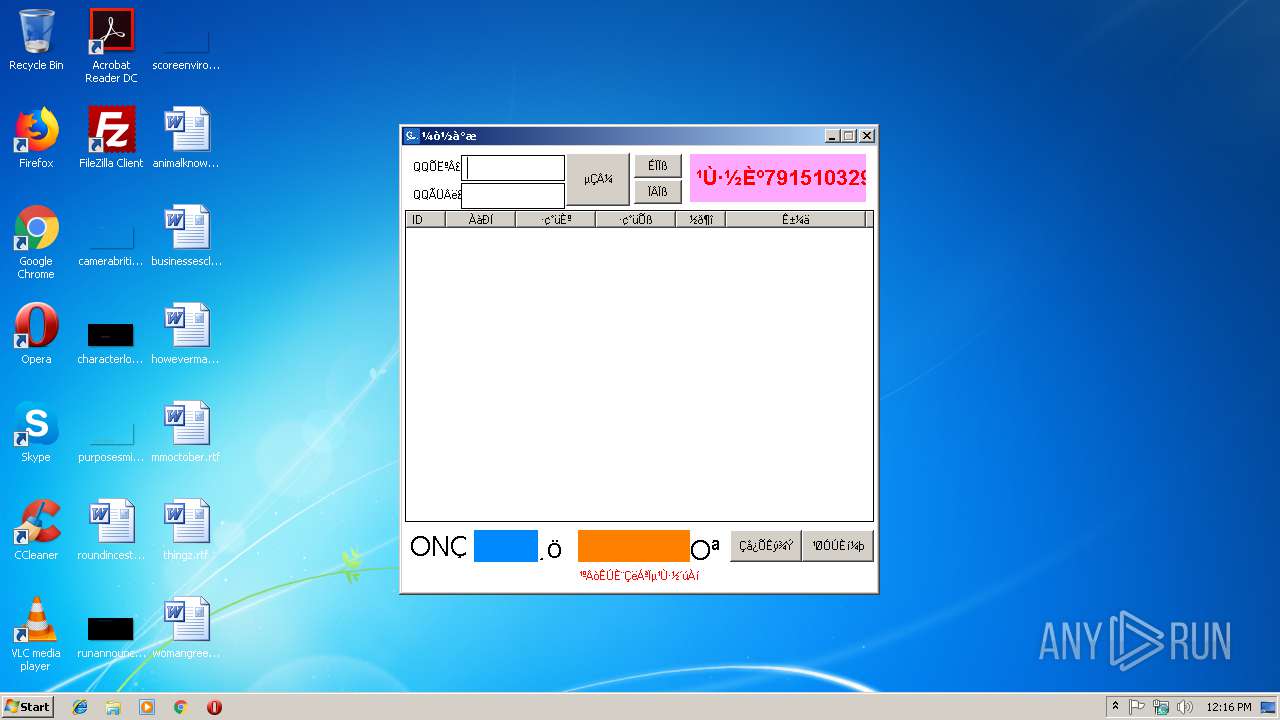
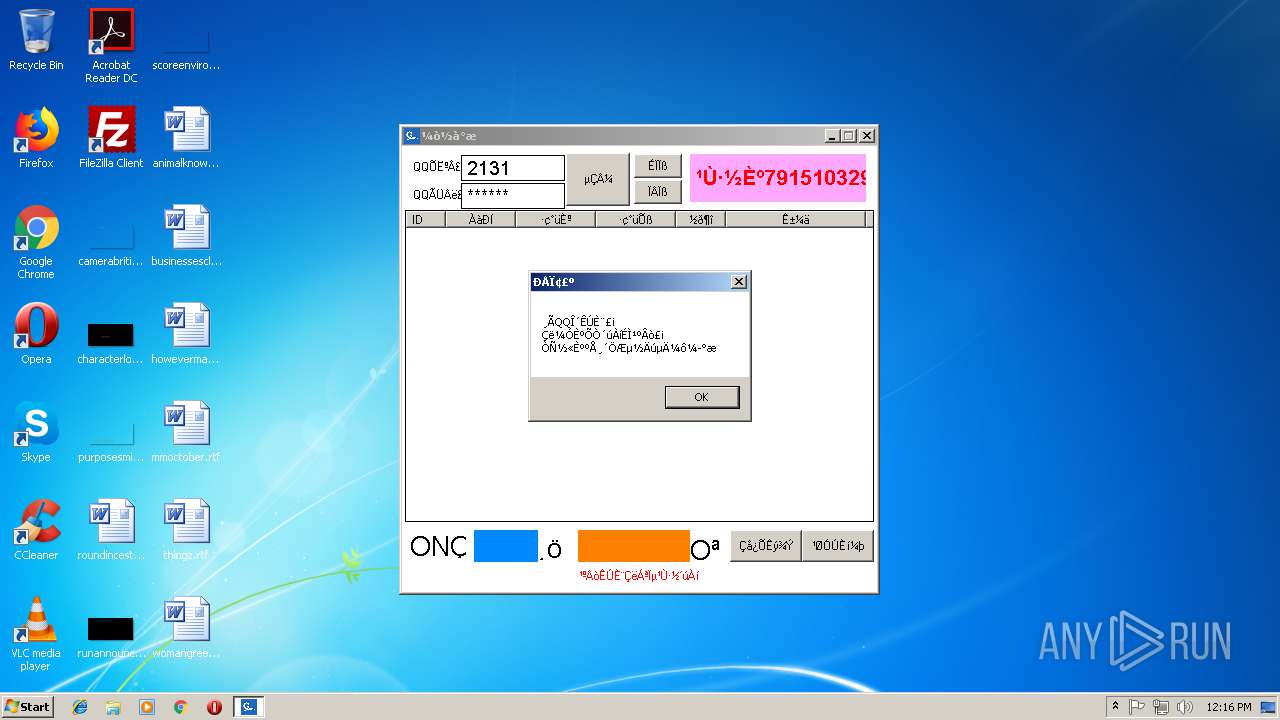
| File name: | j.exe |
| Full analysis: | https://app.any.run/tasks/e748f4cc-2431-4ecf-a2ff-b583cc6e4ae1 |
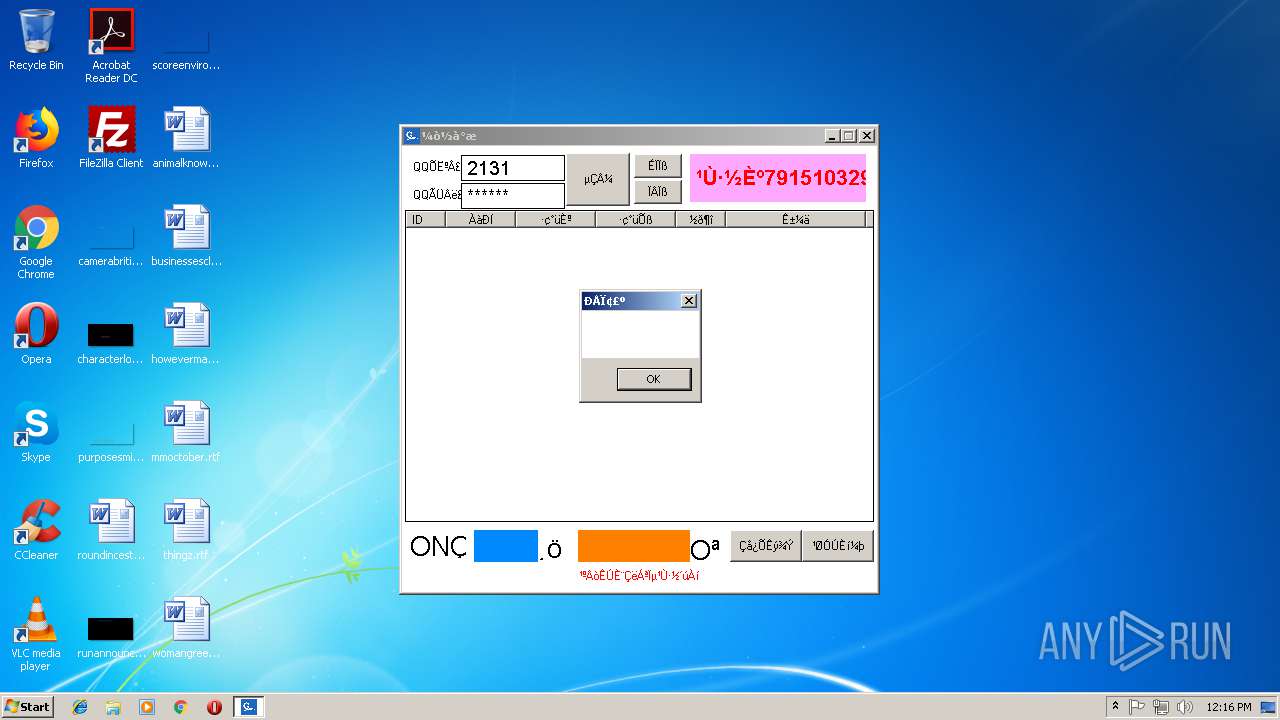
| Verdict: | Malicious activity |
| Threats: | Ramnit is a highly modular banking trojan and worm that evolved from a file-infecting virus into a powerful cybercrime tool. It specializes in financial fraud, credential theft, remote access, and malware delivery, being a serious threat to businesses and individuals. First spotted in 2010, Ramnit became popular after the 2014 takedown of the GameOver Zeus botnet, as cybercriminals sought alternatives for banking fraud. |
| Analysis date: | February 18, 2019, 12:15:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9ED7391B5C73FFB7559076B845ED17AC |
| SHA1: | 07FF5AD1F24C27D49D25B1D3B3365C2616F62929 |
| SHA256: | D40DD97E2B90E5C11F9F989B78F83A57BD9C0AEF1B88F49CD979157C8FE456E3 |
| SSDEEP: | 98304:OrBiBkFmpYJes4fJobqVsJgJBAUZL1za4:Oym/e2qVsWJVhzx |
MALICIOUS
Application was dropped or rewritten from another process
- jSrv.exe (PID: 2736)
- DesktopLayer.exe (PID: 3292)
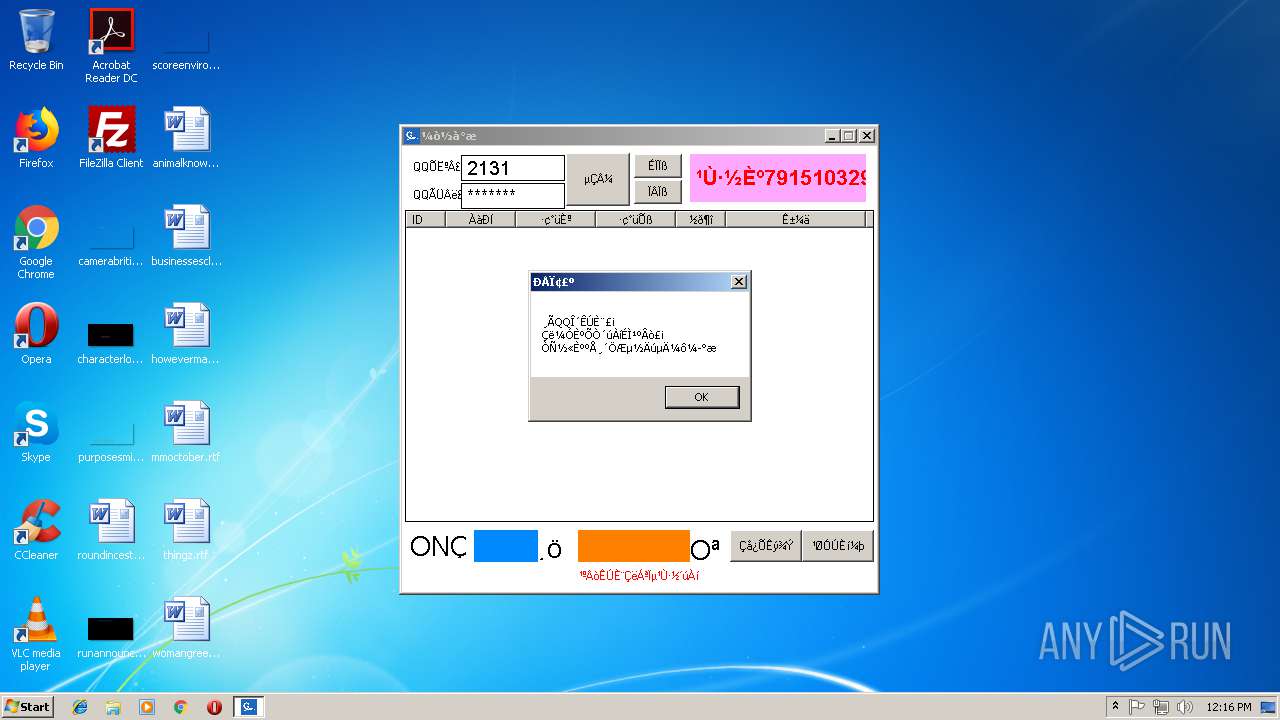
Changes the login/logoff helper path in the registry
- iexplore.exe (PID: 3808)
Loads dropped or rewritten executable
- j.exe (PID: 3248)
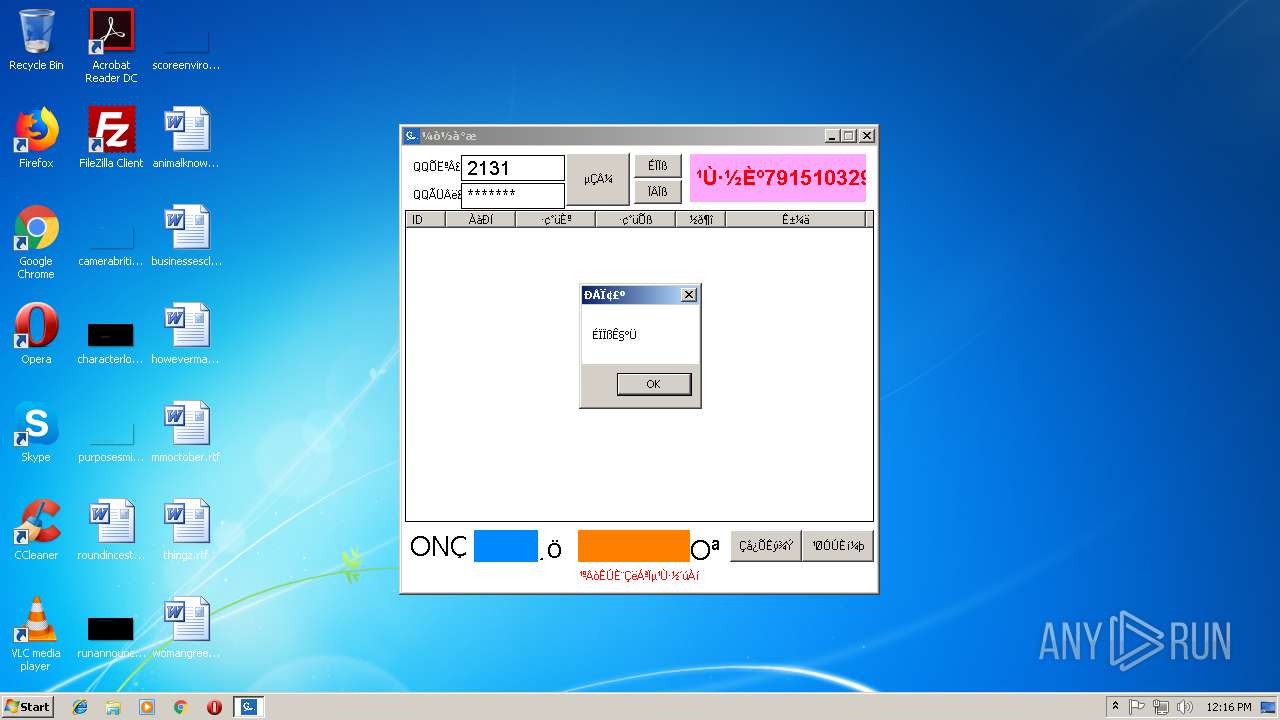
RAMNIT was detected
- iexplore.exe (PID: 3808)
Connects to CnC server
- iexplore.exe (PID: 3808)
SUSPICIOUS
Connects to unusual port
- j.exe (PID: 3248)
Executable content was dropped or overwritten
- j.exe (PID: 3248)
- jSrv.exe (PID: 2736)
Starts Internet Explorer
- DesktopLayer.exe (PID: 3292)
Creates files in the program directory
- iexplore.exe (PID: 3808)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (24.4) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.6) |
| .exe | | | UPX compressed Win32 Executable (21.2) |
| .exe | | | Win32 EXE Yoda's Crypter (20.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:18 02:12:35+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 1314816 |
| InitializedDataSize: | 3506176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11baf4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.0.0 |
| ProductVersionNumber: | 1.2.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.2.0.0 |
| FileDescription: | 易语言程序 |
| ProductName: | 简洁版 |
| ProductVersion: | 1.2.0.0 |
| CompanyName: | 欢喜 |
| LegalCopyright: | 本软件仅用于个人学习交流,禁止用于任何商业用途与一切违规用途,后果自负!最终解释权归作者所有! |
| Comments: | 简单版 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Feb-2019 01:12:35 |
| Detected languages: |
|
| FileVersion: | 1.2.0.0 |
| FileDescription: | 易语言程序 |
| ProductName: | 简洁版 |
| ProductVersion: | 1.2.0.0 |
| CompanyName: | 欢喜 |
| LegalCopyright: | 本软件仅用于个人学习交流,禁止用于任何商业用途与一切违规用途,后果自负!最终解释权归作者所有! |
| Comments: | 简单版 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 18-Feb-2019 01:12:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00140786 | 0x00141000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51939 |
.rdata | 0x00142000 | 0x00247CF0 | 0x00248000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.14739 |
.data | 0x0038A000 | 0x0011DC08 | 0x000C8000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.56802 |
.rsrc | 0x004A8000 | 0x00047078 | 0x00048000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.17356 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 2.73841 | 270376 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.74274 | 180 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
127 | 1.4183 | 12 | Latin 1 / Western European | Chinese - PRC | RT_MENU |
150 | 3.06278 | 152 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
286 | 3.5561 | 378 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
554 | 3.78697 | 250 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
1031 | 3.67246 | 584 | Latin 1 / Western European | Chinese - PRC | RT_BITMAP |
1032 | 1.91924 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RASAPI32.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
WINMM.dll |
Total processes
33
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2736 | C:\Users\admin\AppData\Local\Temp\jSrv.exe | C:\Users\admin\AppData\Local\Temp\jSrv.exe | j.exe | ||||||||||||
User: admin Company: SOFTWIN S.R.L. Integrity Level: MEDIUM Description: BitDefender Management Console Exit code: 0 Version: 106.42.73.61 Modules
| |||||||||||||||
| 3248 | "C:\Users\admin\AppData\Local\Temp\j.exe" | C:\Users\admin\AppData\Local\Temp\j.exe | explorer.exe | ||||||||||||
User: admin Company: 欢喜 Integrity Level: MEDIUM Description: 易语言程序 Exit code: 0 Version: 1.2.0.0 Modules
| |||||||||||||||
| 3292 | C:\Users\admin\Microsoft\DesktopLayer.exe | C:\Users\admin\Microsoft\DesktopLayer.exe | — | jSrv.exe | |||||||||||
User: admin Company: SOFTWIN S.R.L. Integrity Level: MEDIUM Description: BitDefender Management Console Exit code: 0 Version: 106.42.73.61 Modules
| |||||||||||||||
| 3808 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | DesktopLayer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
59
Read events
17
Write events
42
Delete events
0
Modification events
| (PID) Process: | (3808) iexplore.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: c:\windows\system32\userinit.exe,,c:\users\admin\microsoft\desktoplayer.exe | |||
Executable files
4
Suspicious files
0
Text files
77
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3808 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Leame.htm | html | |
MD5:— | SHA256:— | |||
| 3808 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Berime.htm | html | |
MD5:— | SHA256:— | |||
| 3808 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Benioku.htm | html | |
MD5:— | SHA256:— | |||
| 3808 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\LeesMij.htm | html | |
MD5:— | SHA256:— | |||
| 3808 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\IrakHau.htm | html | |
MD5:— | SHA256:— | |||
| 3808 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\LeiaMe.htm | html | |
MD5:— | SHA256:— | |||
| 3808 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Liesmich.htm | html | |
MD5:— | SHA256:— | |||
| 3808 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Lisezmoi.htm | html | |
MD5:— | SHA256:— | |||
| 3808 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Leggimi.htm | html | |
MD5:— | SHA256:— | |||
| 3808 | iexplore.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Reader\Legal\CAT\license.html | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
4
Threats
6
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3248 | j.exe | 47.111.55.132:3306 | rm-bp1uvj1d1oxcwhe8s8o.mysql.rds.aliyuncs.com | — | CN | unknown |
3248 | j.exe | 203.205.147.207:8080 | msfwifi.3g.qq.com | Tencent Building, Kejizhongyi Avenue | CN | unknown |
3808 | iexplore.exe | 172.217.18.174:80 | google.com | Google Inc. | US | whitelisted |
3808 | iexplore.exe | 89.185.44.100:443 | fget-career.com | Claranet Ltd | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rm-bp1uvj1d1oxcwhe8s8o.mysql.rds.aliyuncs.com |
| unknown |
msfwifi.3g.qq.com |
| unknown |
google.com |
| malicious |
fget-career.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3808 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
3808 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Ramnit Checkin |
3808 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
3808 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Ramnit Checkin |
3808 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Banker Ramnit CnC Connection |
1 ETPRO signatures available at the full report