| File name: | temp.exe |
| Full analysis: | https://app.any.run/tasks/ef3ad714-1f94-4c26-8419-ec0666528297 |
| Verdict: | Malicious activity |
| Threats: | TrickBot is an advanced banking trojan that attackers can use to steal payment credentials from the victims. It can redirect the victim to a fake banking cabinet and retrieve credentials typed in on the webpage. |
| Analysis date: | January 17, 2020, 21:47:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 714A0F6DA7E022584345A5A03567F899 |
| SHA1: | 66721C05CC337015E270C3FBCBD541E58C816D8C |
| SHA256: | D3B2AB3FC98E274D891908E6EDFE72545E7A03CD7E4E2D6BAF8367B0405CB782 |
| SSDEEP: | 768:A1StEpZnOoxjQJOoZVgiYfQ/sE5QZEYr8st5mcGQd6GrZPAWOGvEhY5txJsq9WQG:AUtIdnAVgAGalsOcGQPJshIJsq9Zts |
MALICIOUS
TRICKBOT was detected
- studio.exe (PID: 2548)
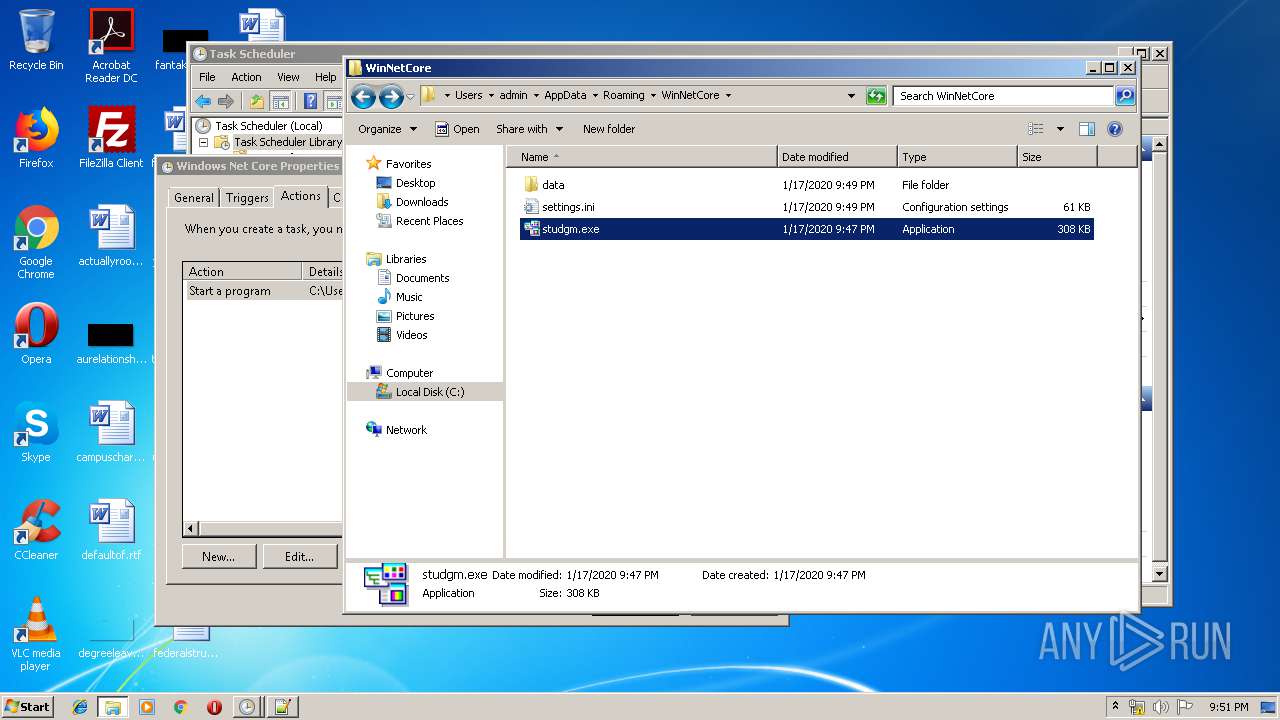
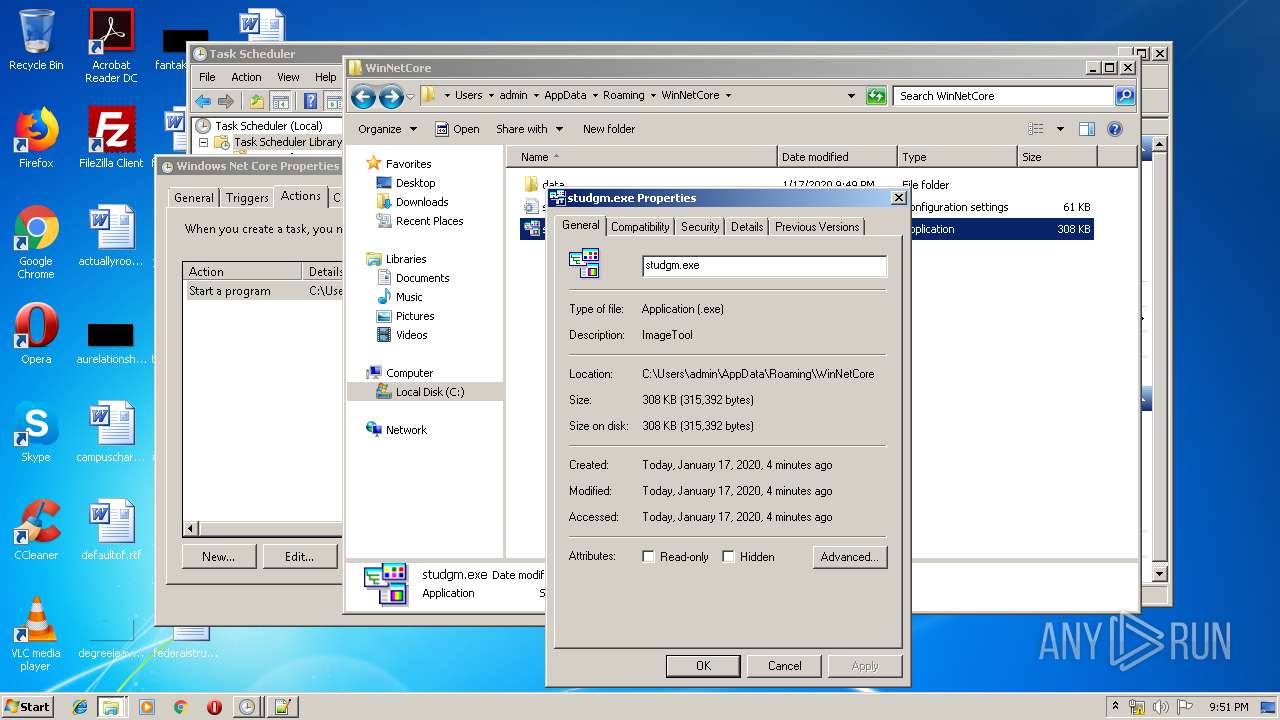
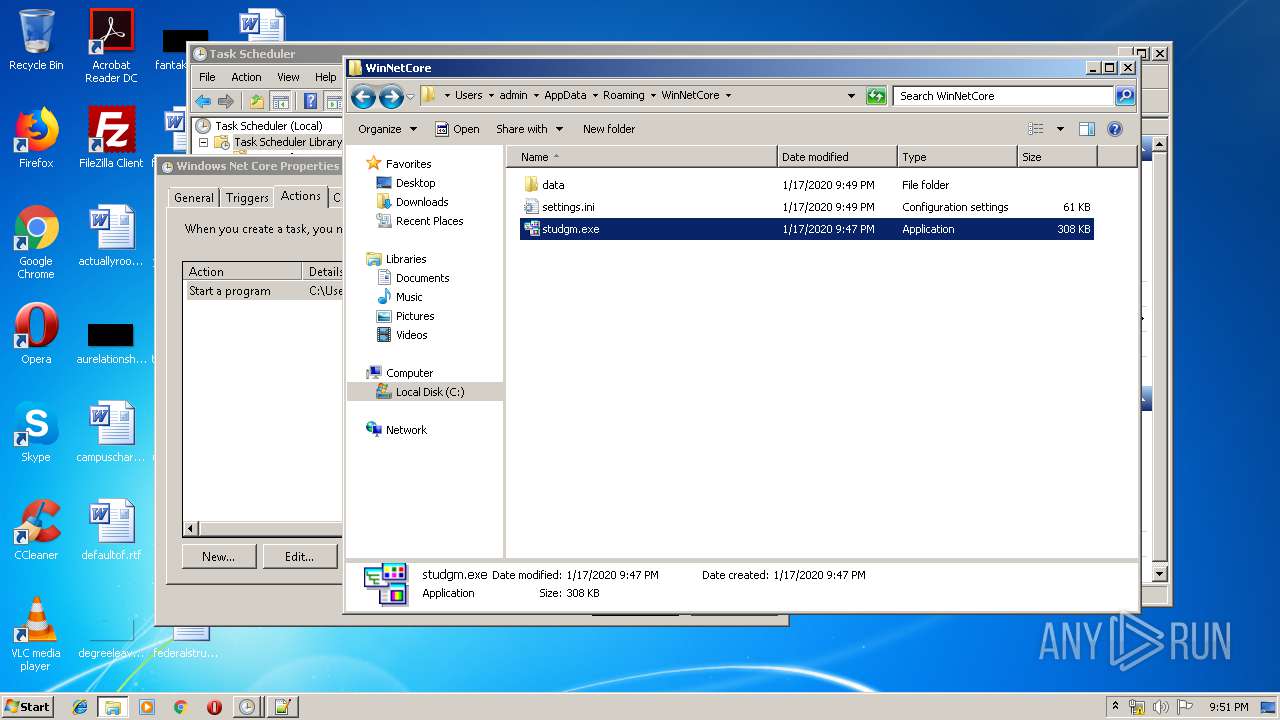
- studgm.exe (PID: 2424)
Application was dropped or rewritten from another process
- studio.exe (PID: 820)
- studio.exe (PID: 2548)
- studgm.exe (PID: 2424)
- studgm.exe (PID: 2252)
Known privilege escalation attack
- DllHost.exe (PID: 2772)
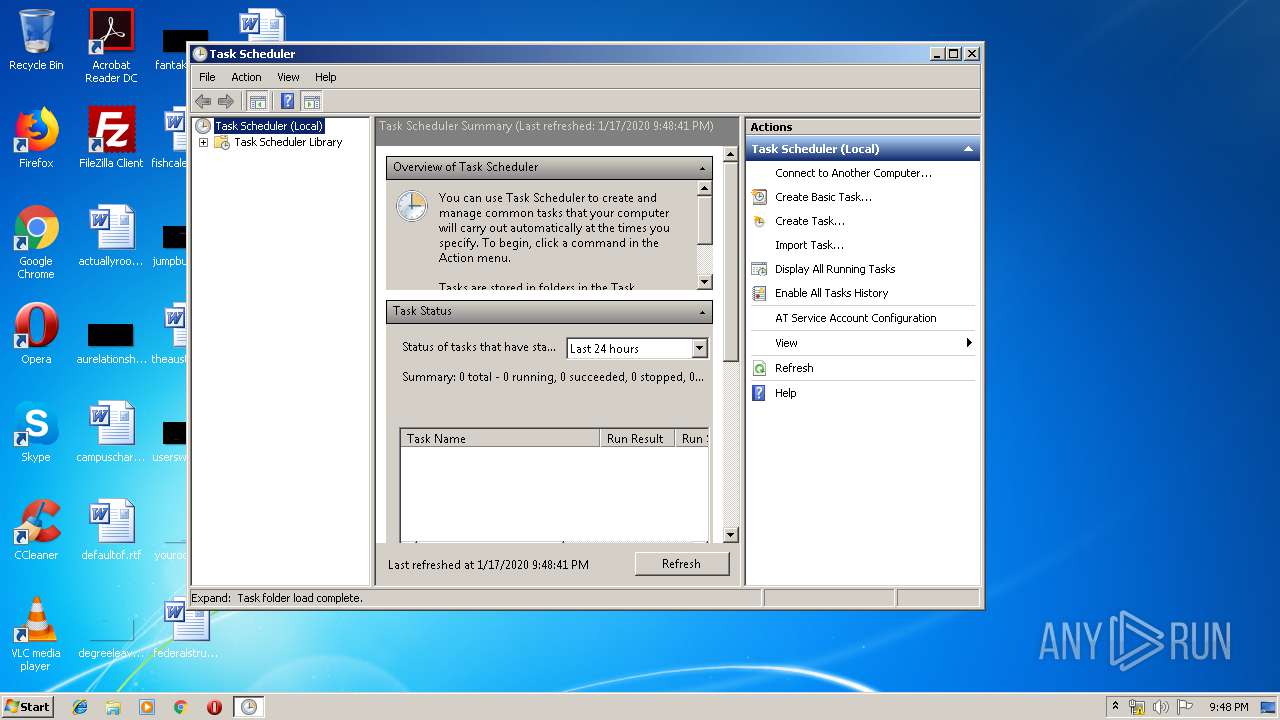
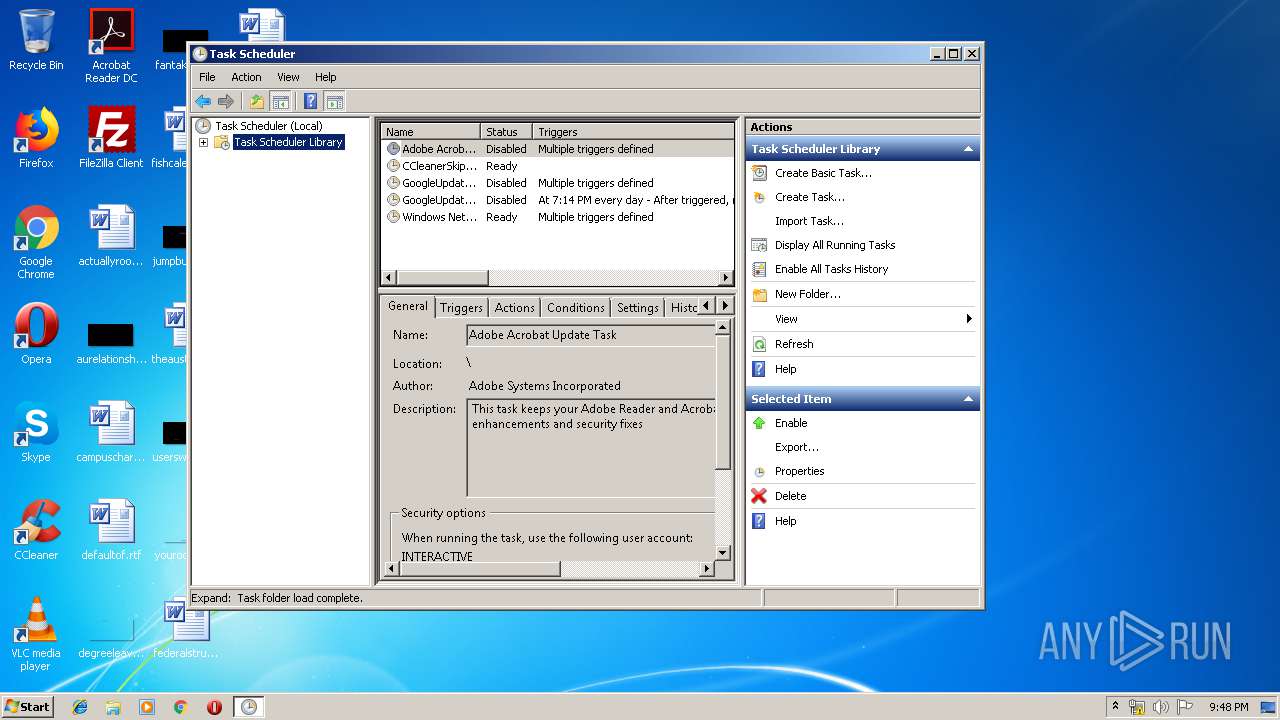
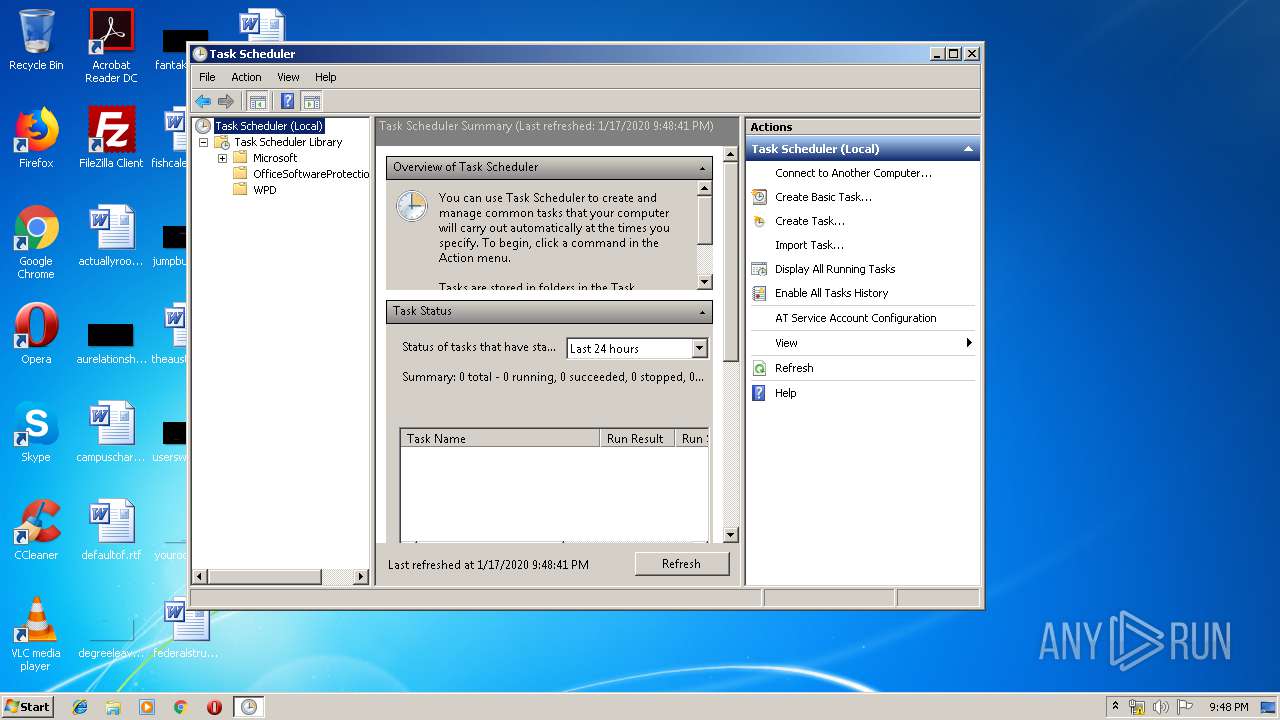
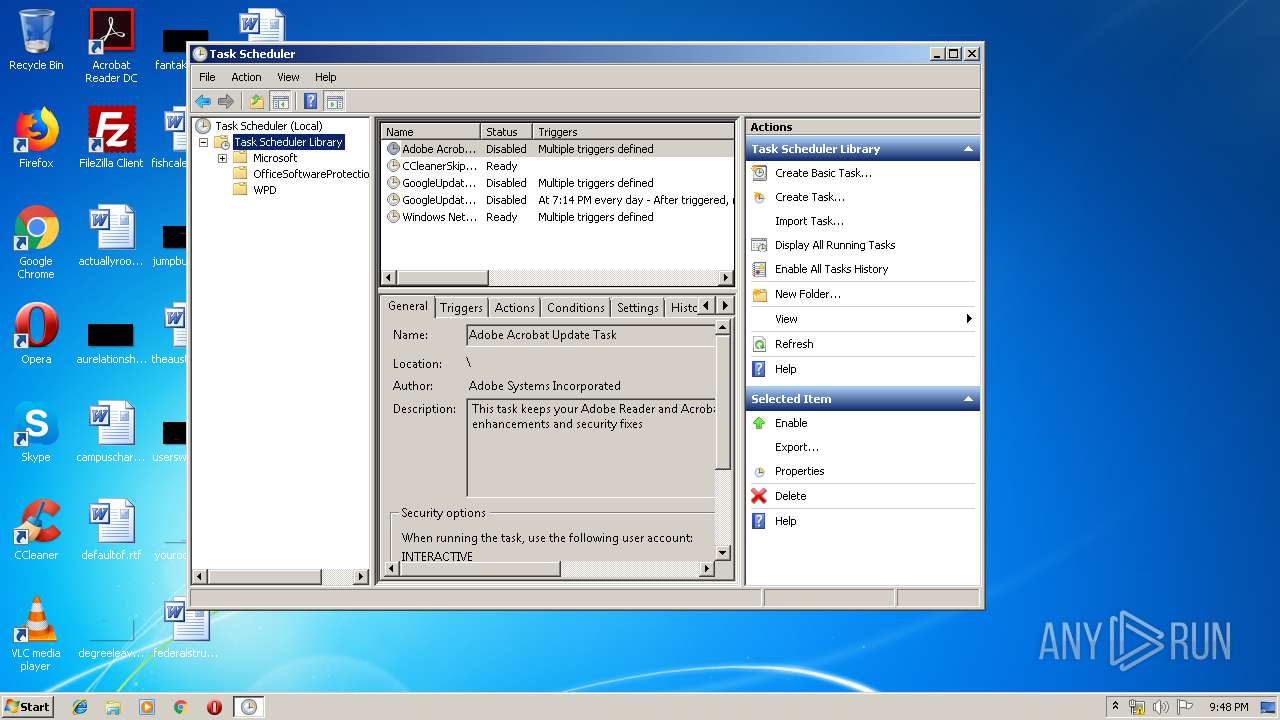
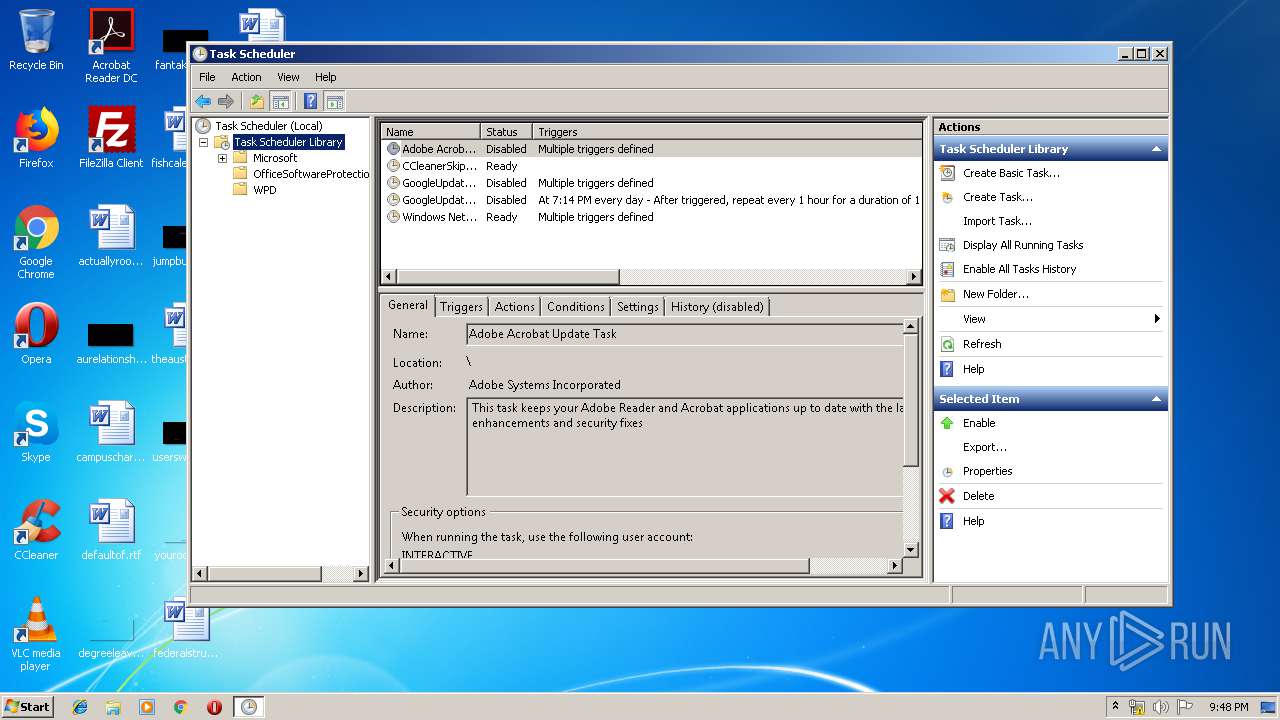
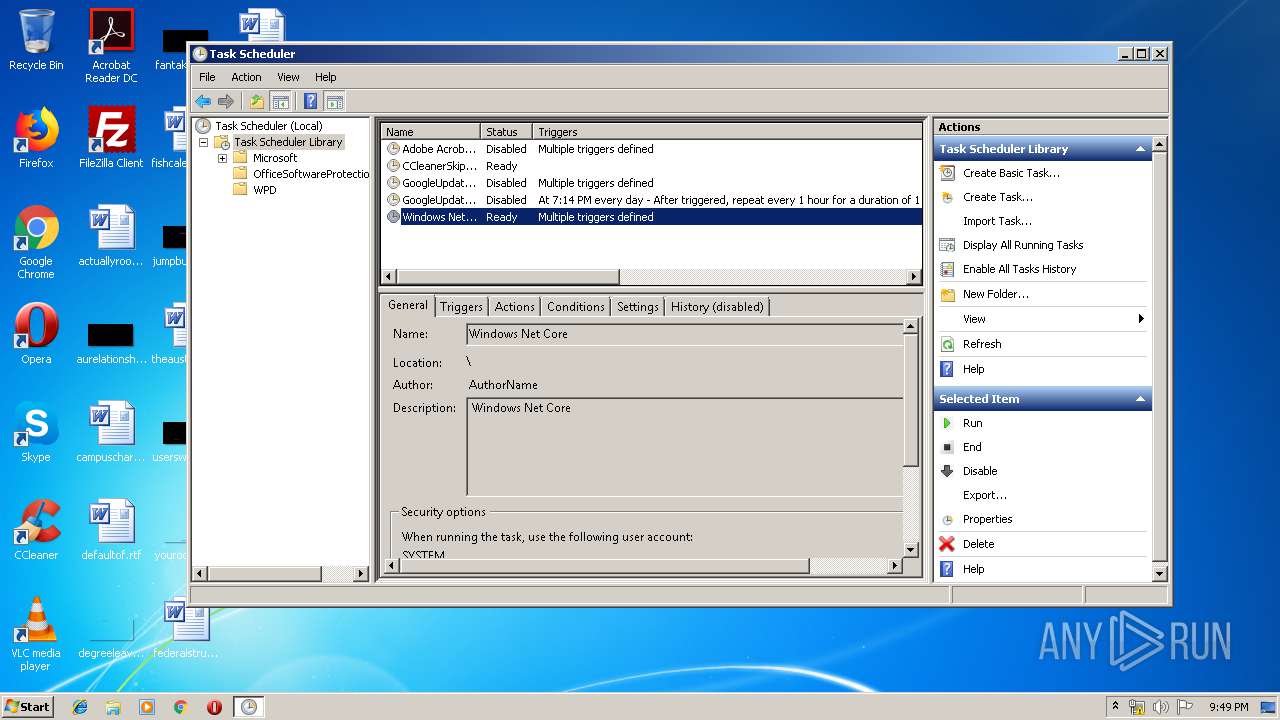
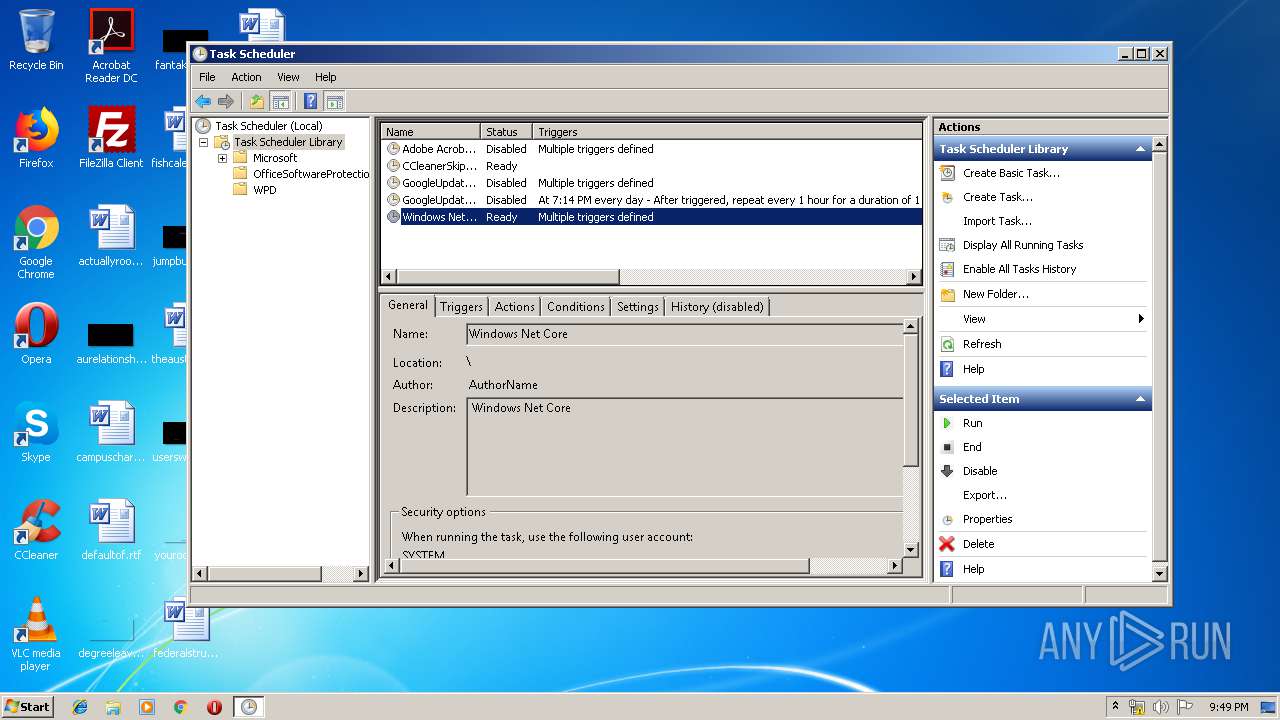
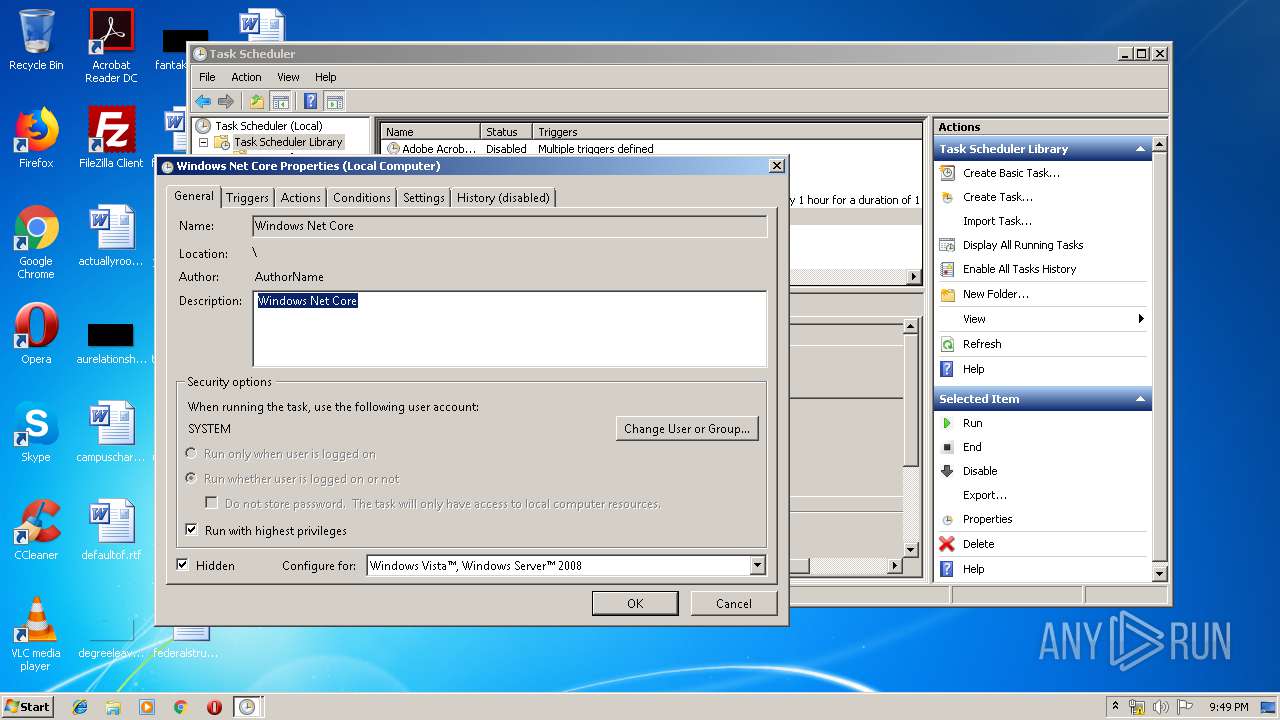
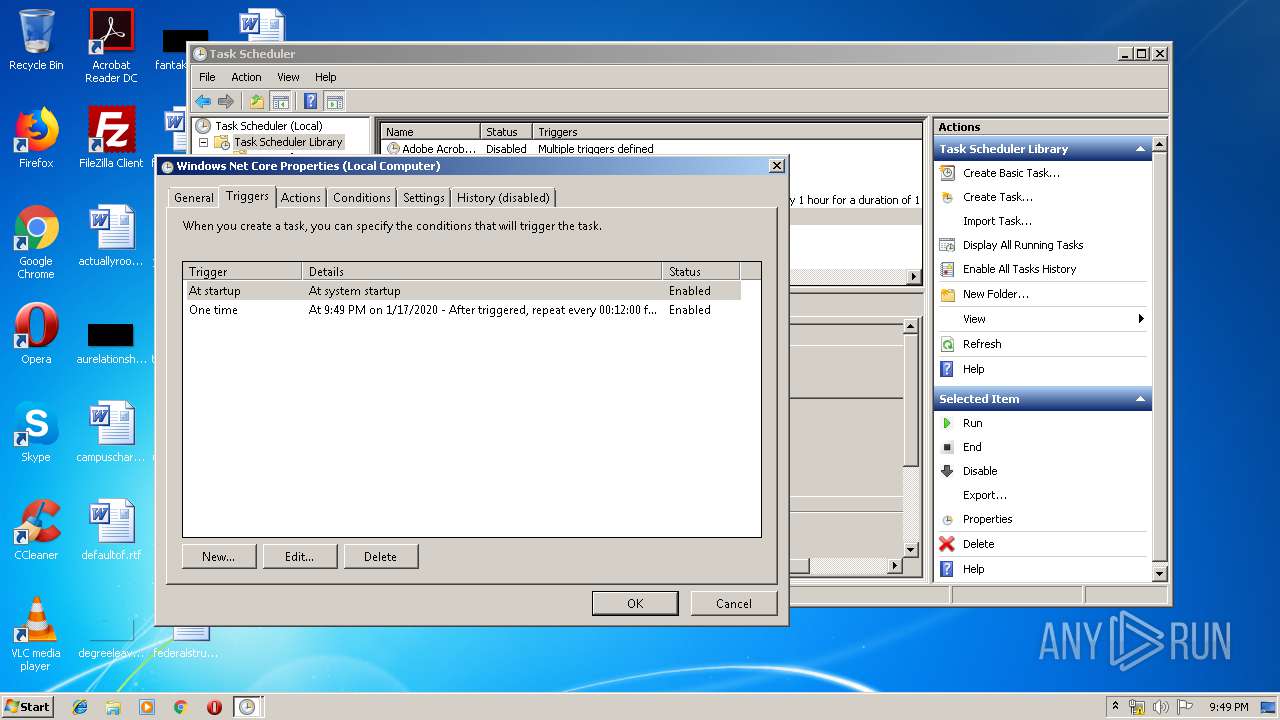
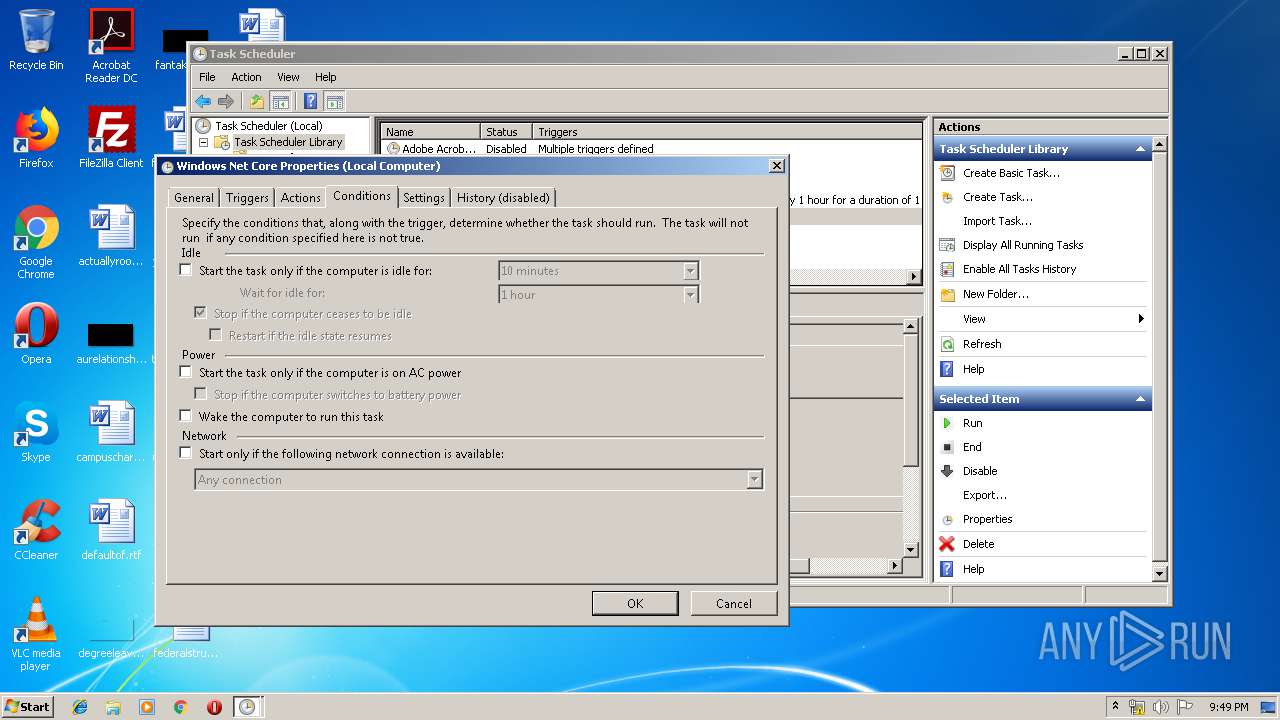
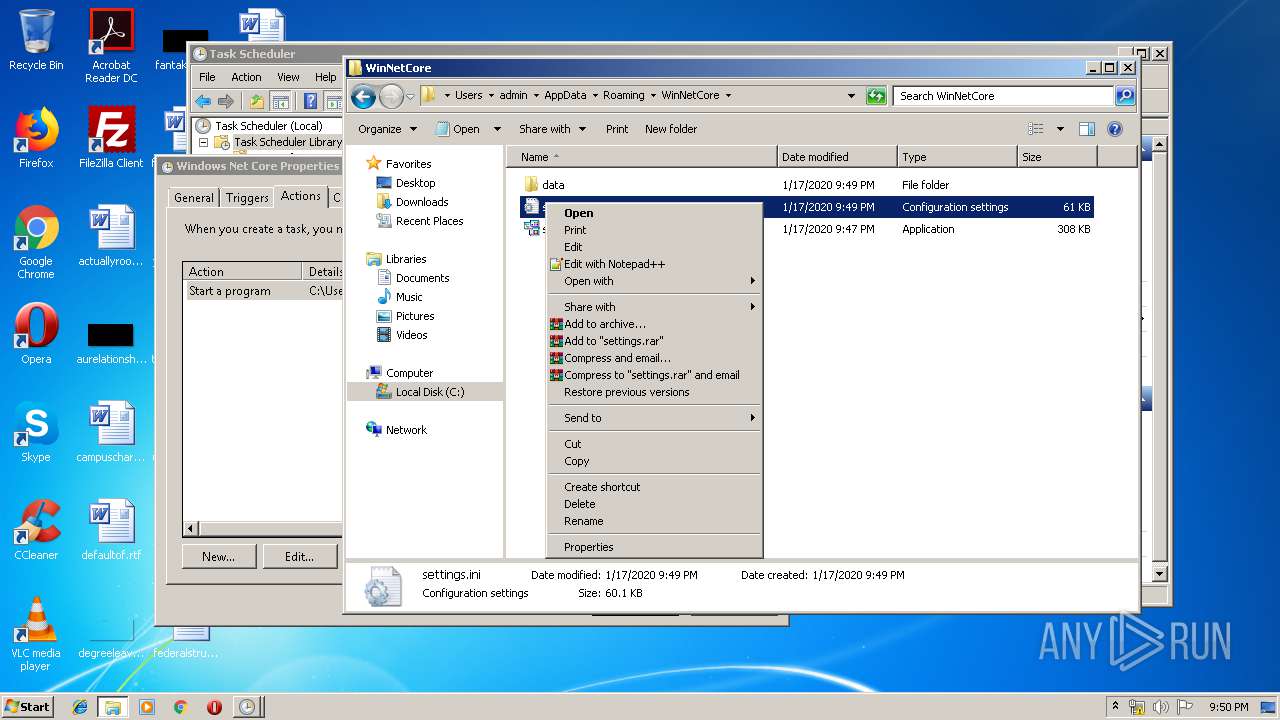
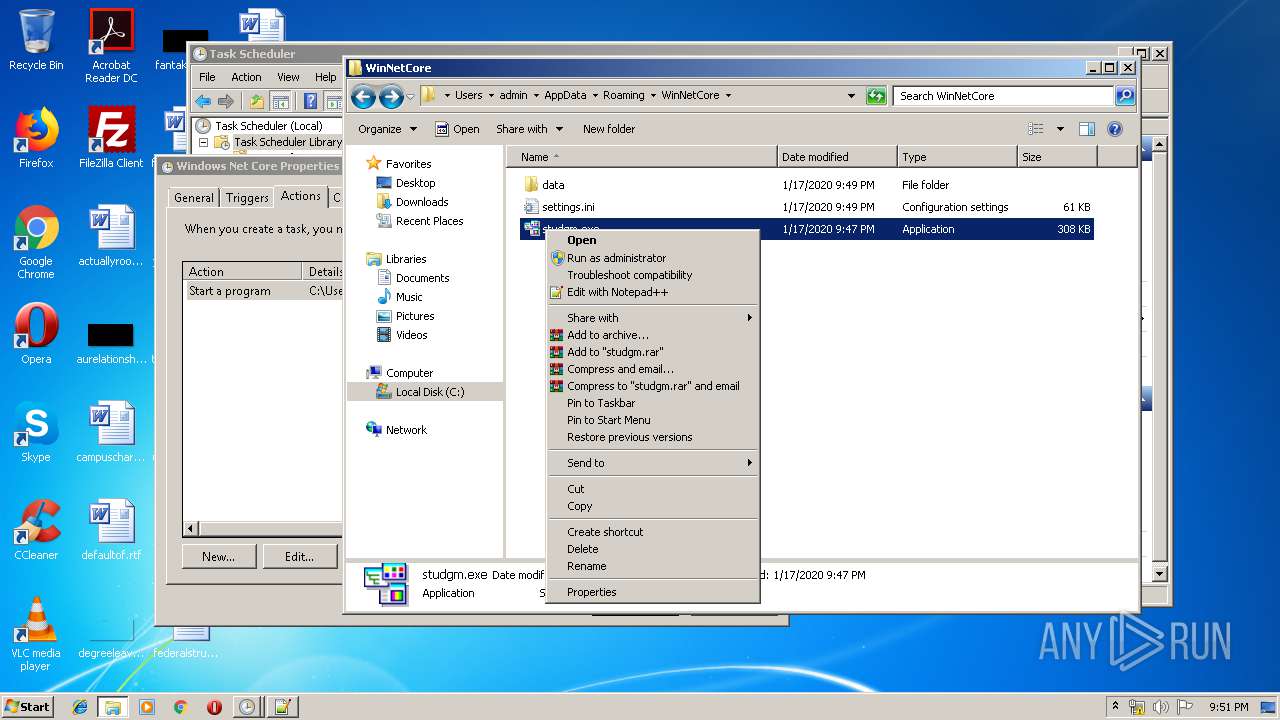
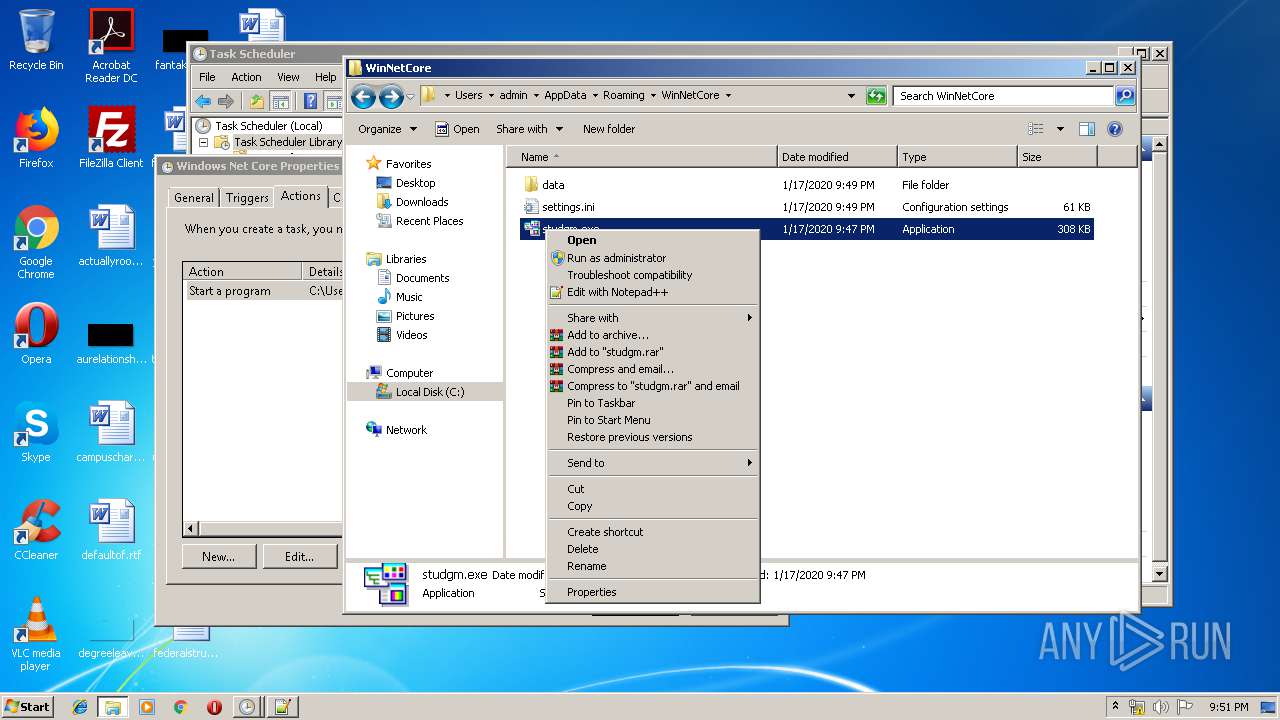
Loads the Task Scheduler COM API
- stsk.exe (PID: 3100)
- studio.exe (PID: 2548)
- mmc.exe (PID: 2736)
- studgm.exe (PID: 2424)
Connects to CnC server
- studgm.exe (PID: 2424)
SUSPICIOUS
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 1412)
- cmd.exe (PID: 2388)
Starts CMD.EXE for commands execution
- temp.exe (PID: 2768)
Executable content was dropped or overwritten
- winlogon.exe (PID: 3392)
- temp.exe (PID: 2768)
- studio.exe (PID: 2548)
Executed via COM
- DllHost.exe (PID: 2772)
- DllHost.exe (PID: 3972)
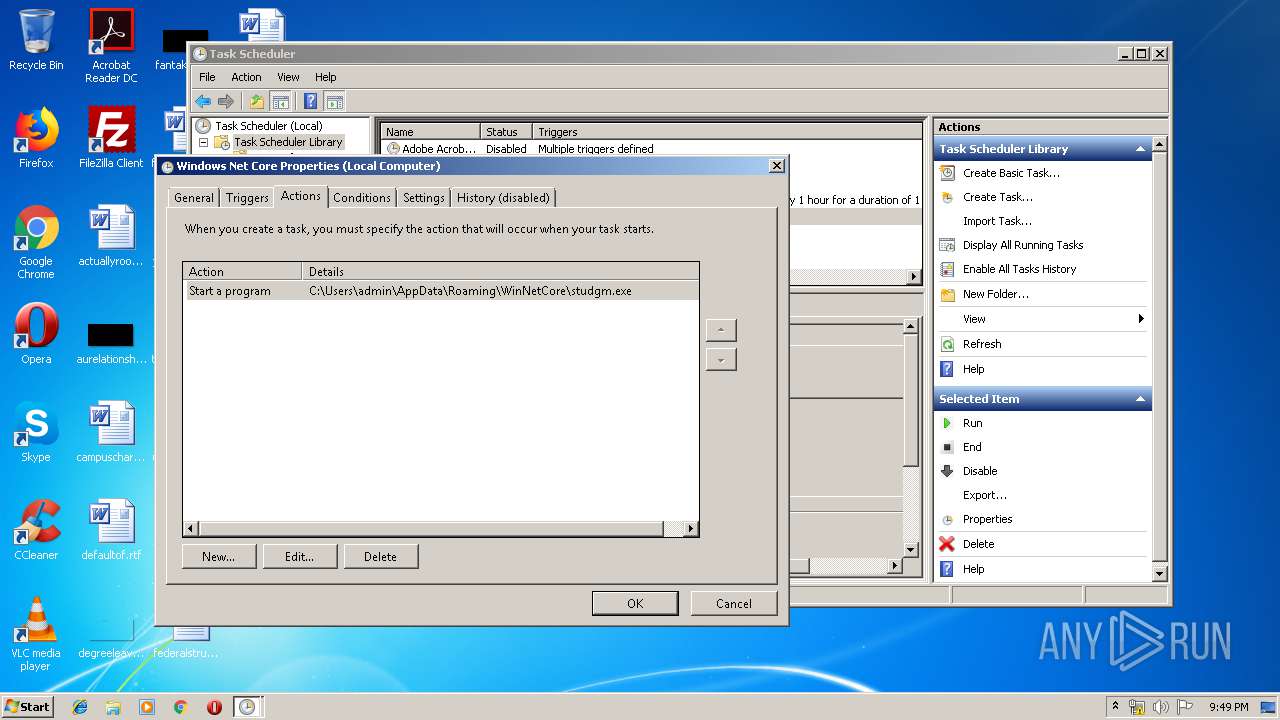
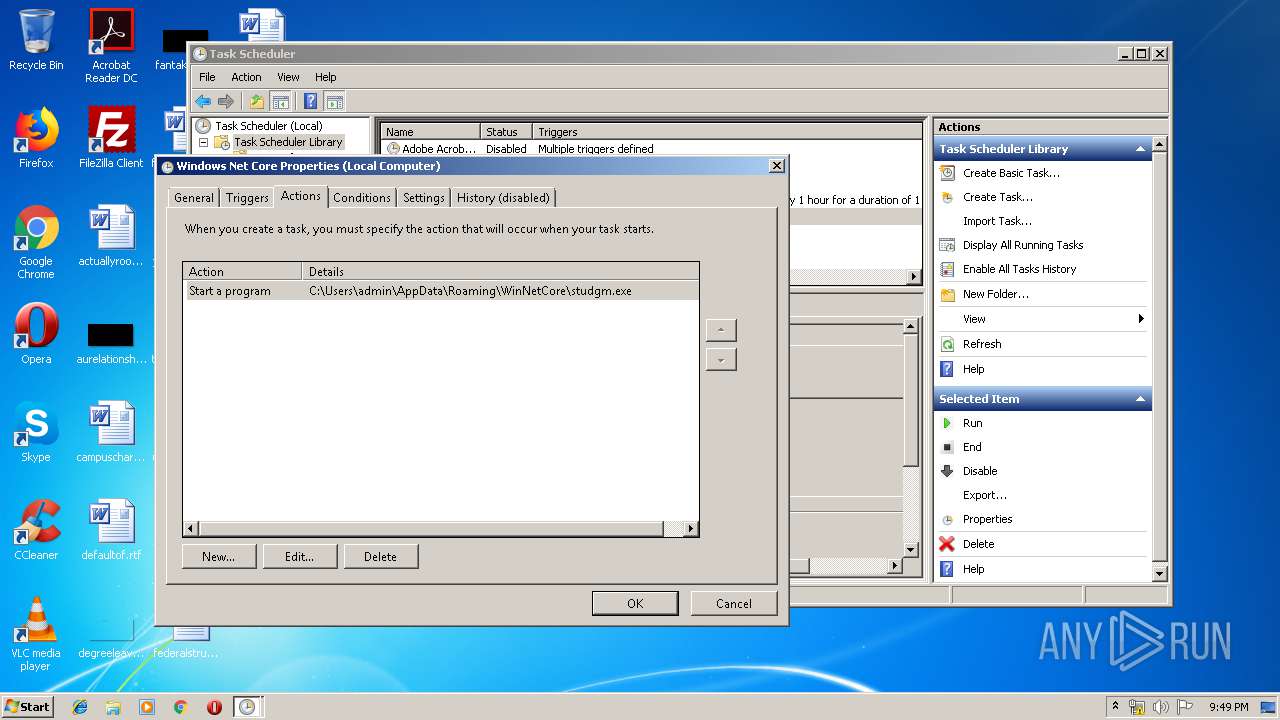
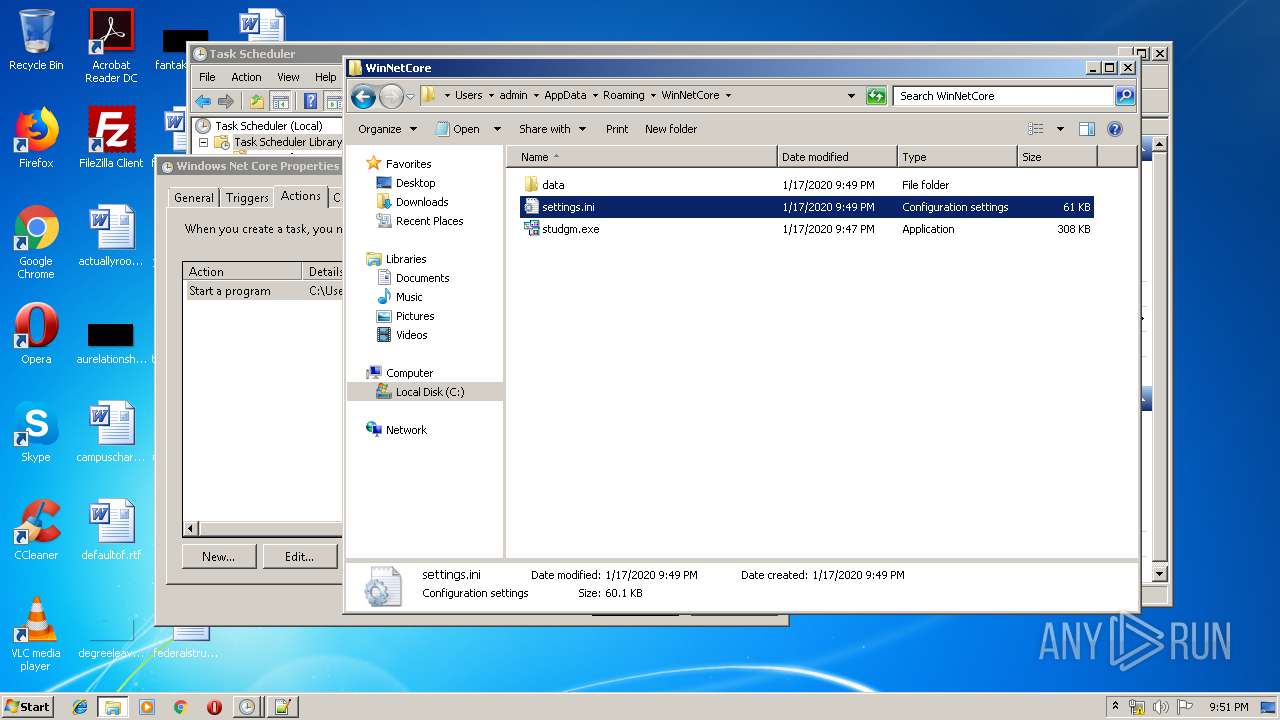
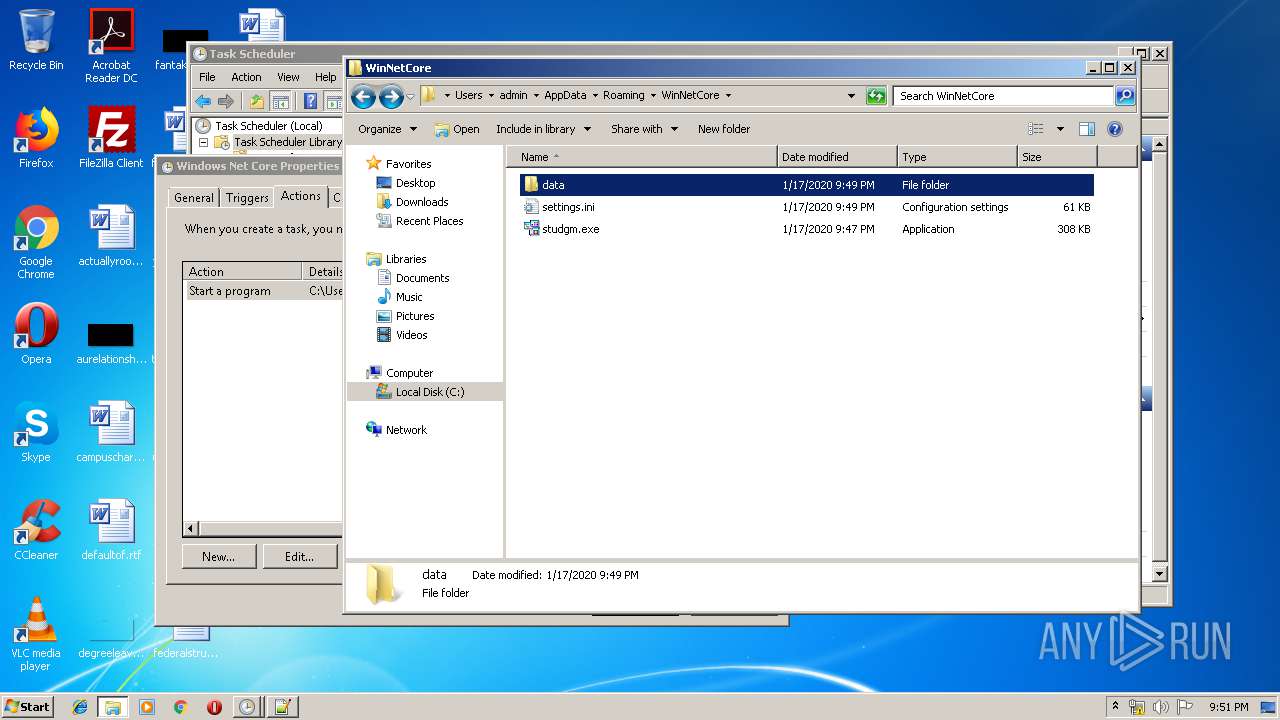
Executed via Task Scheduler
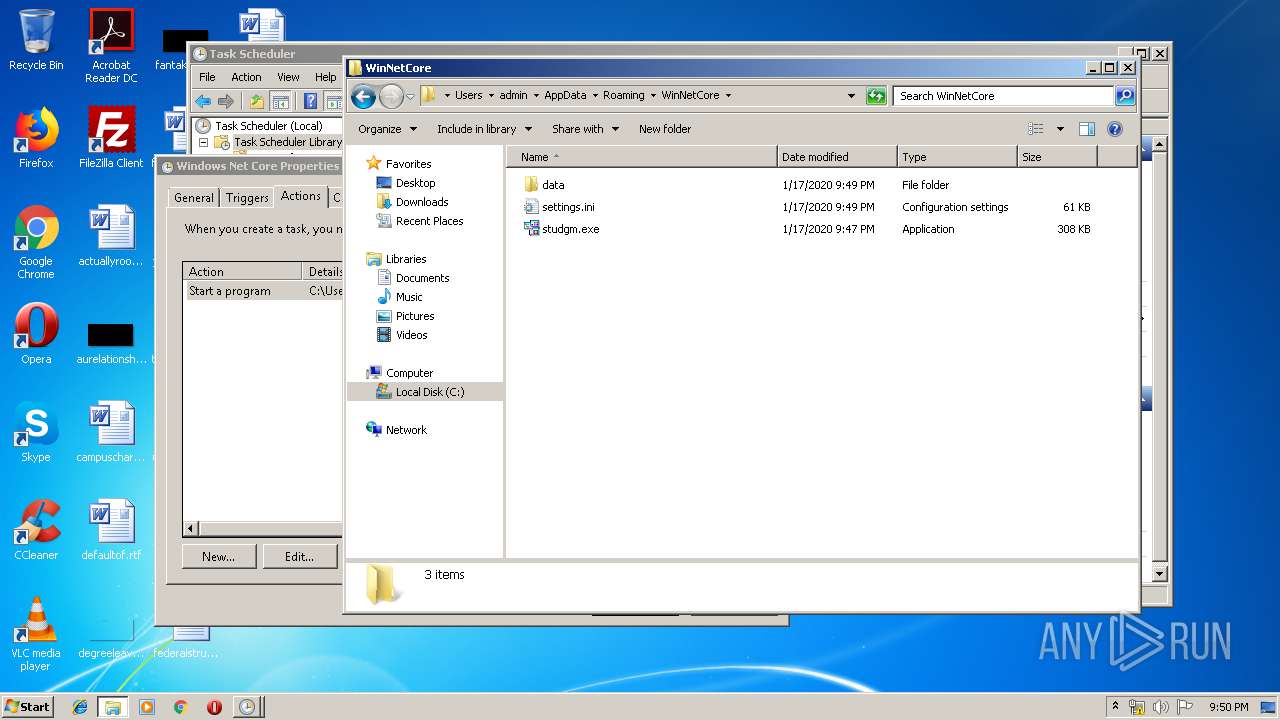
- studgm.exe (PID: 2424)
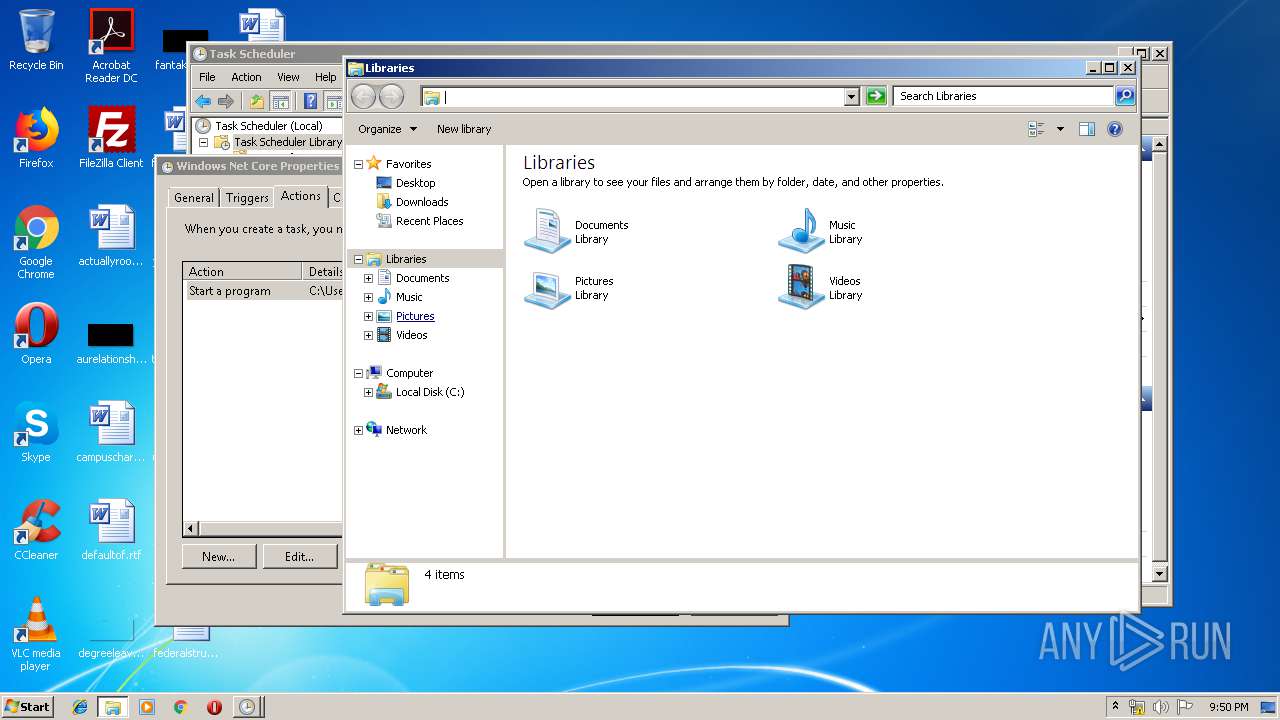
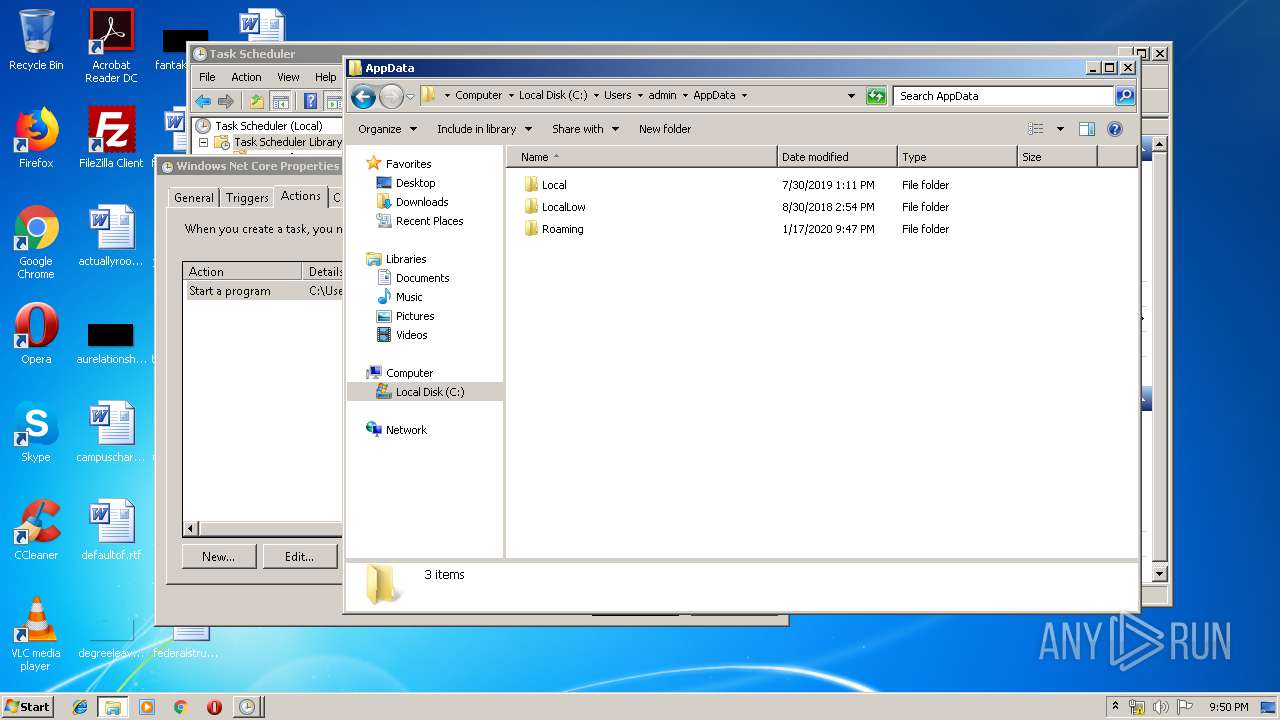
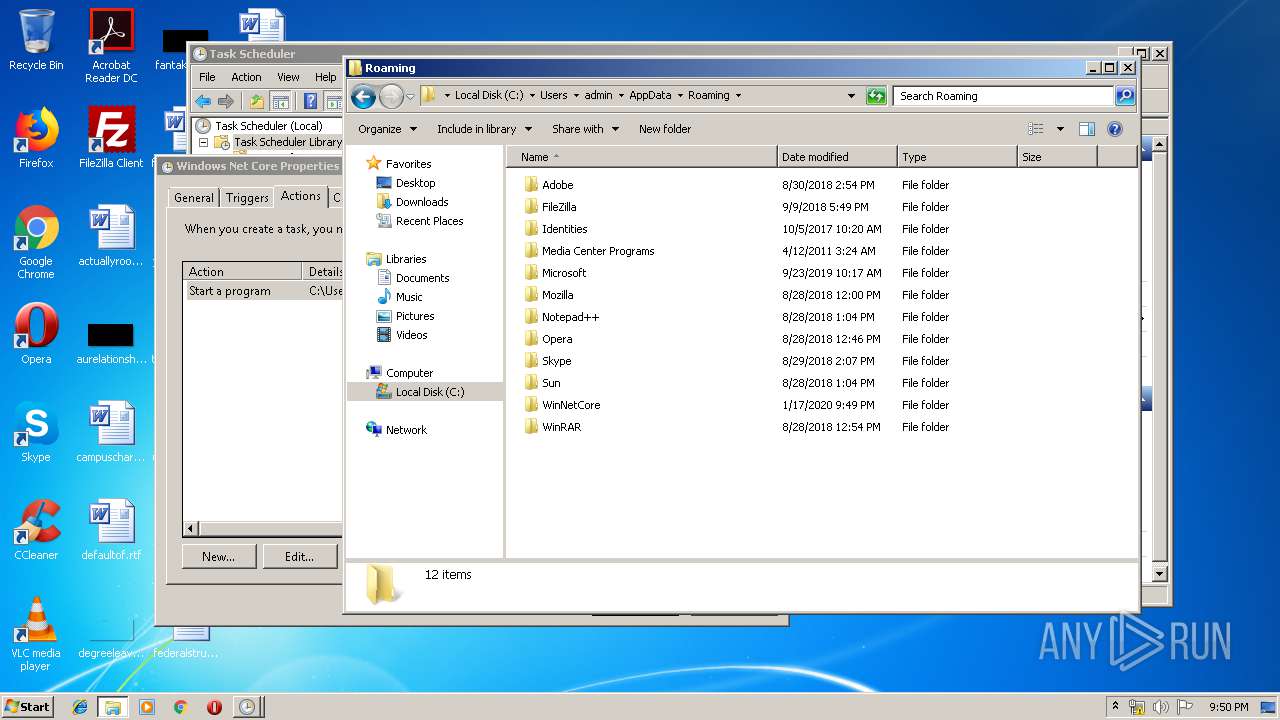
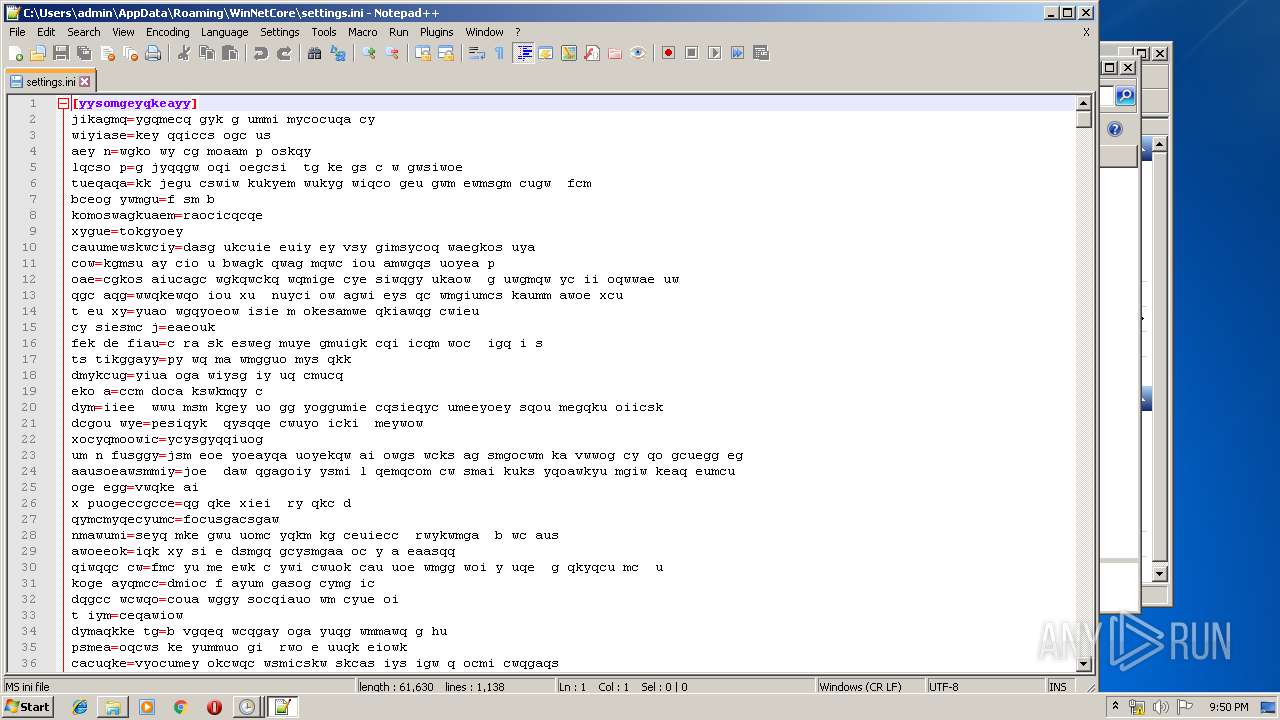
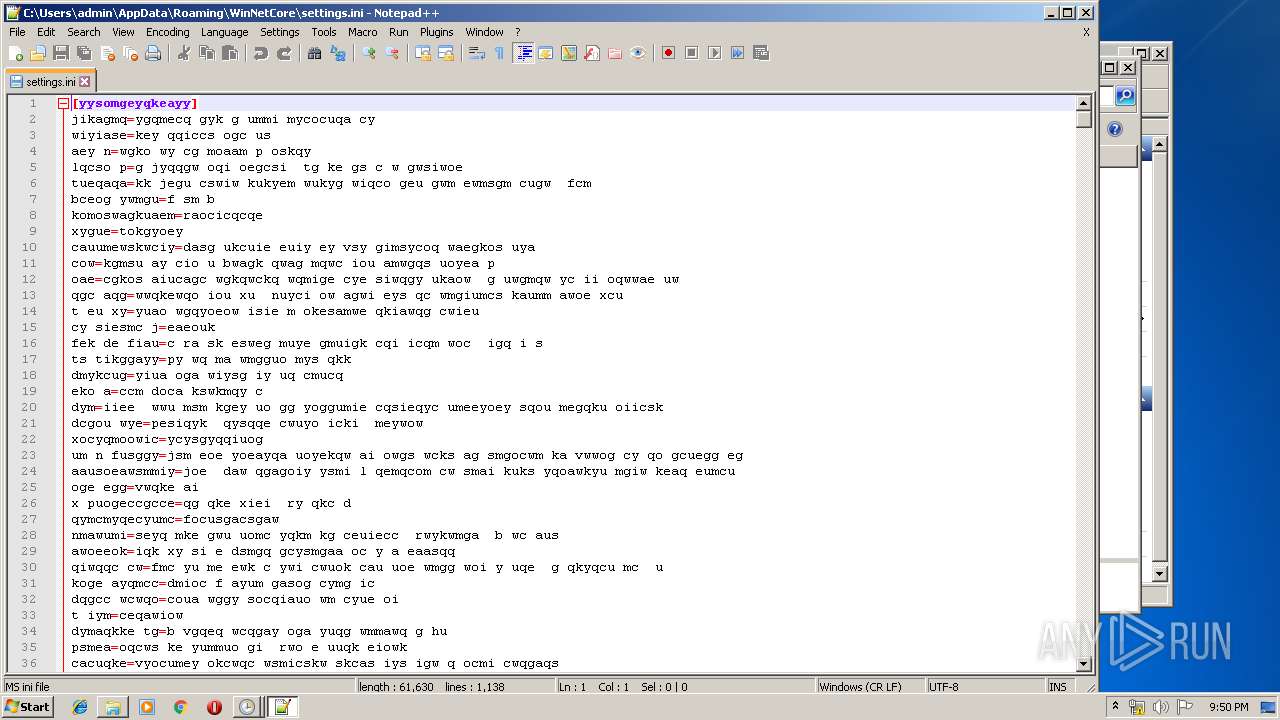
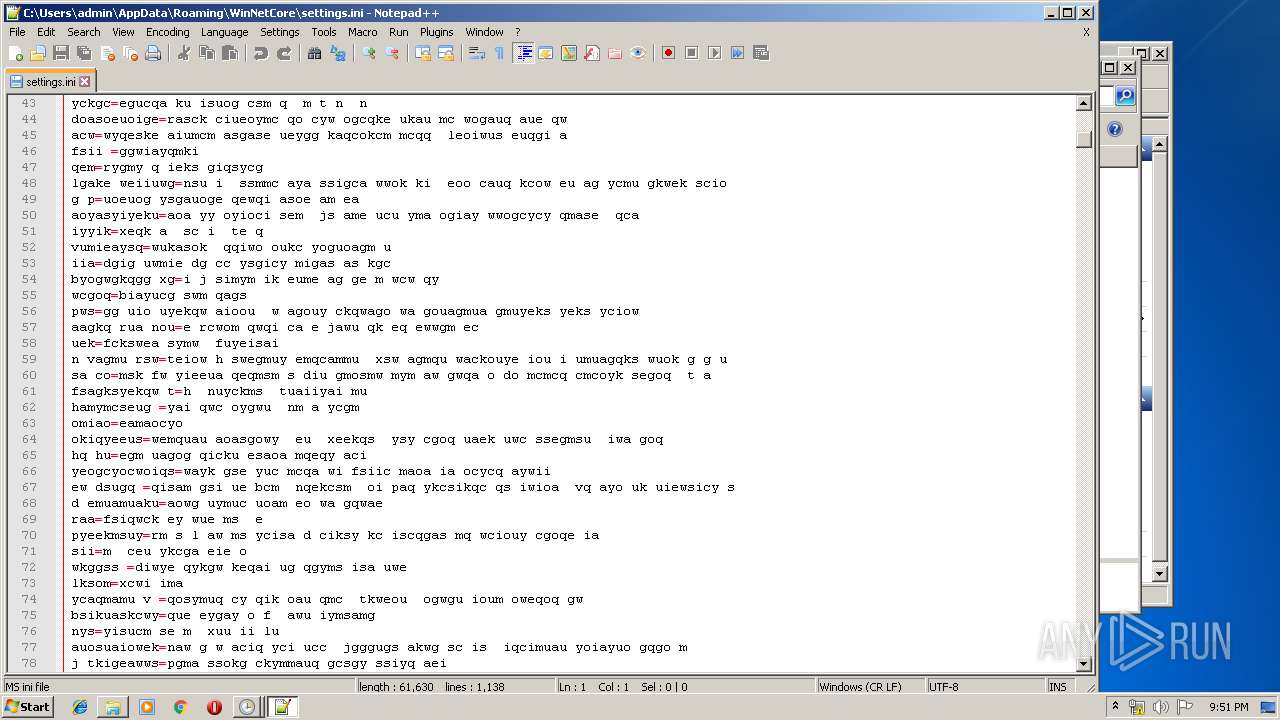
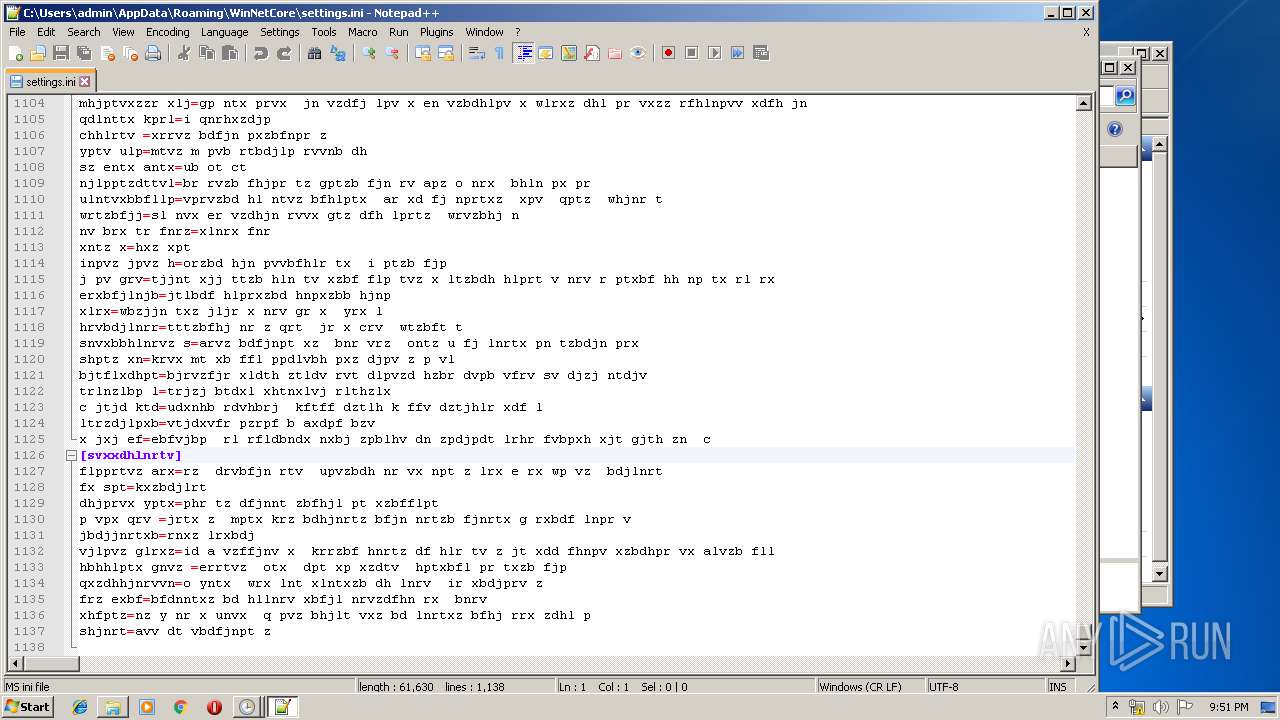
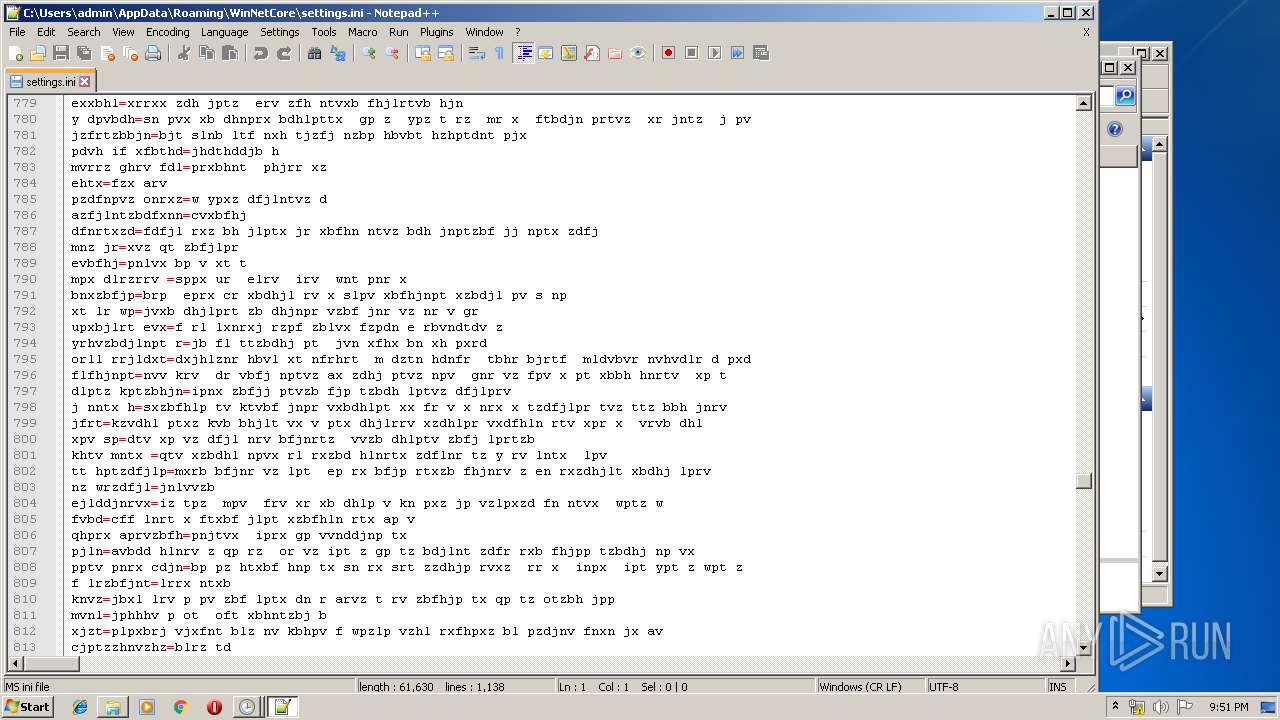
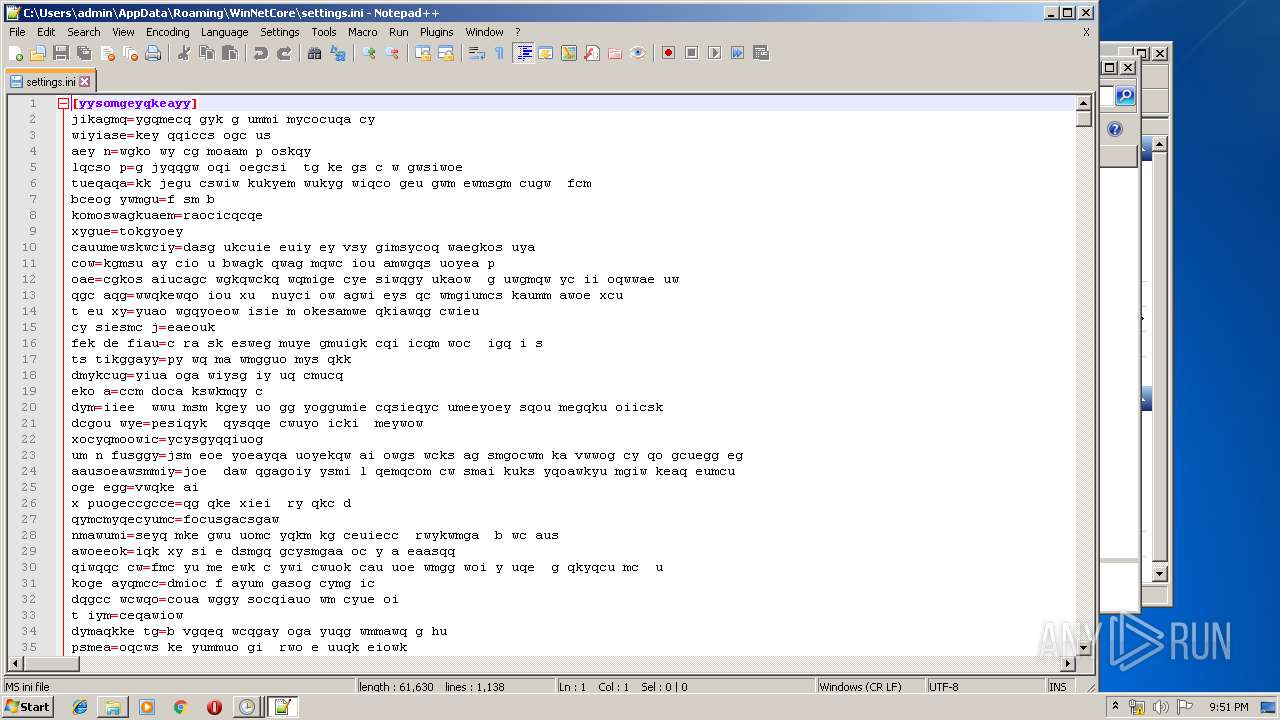
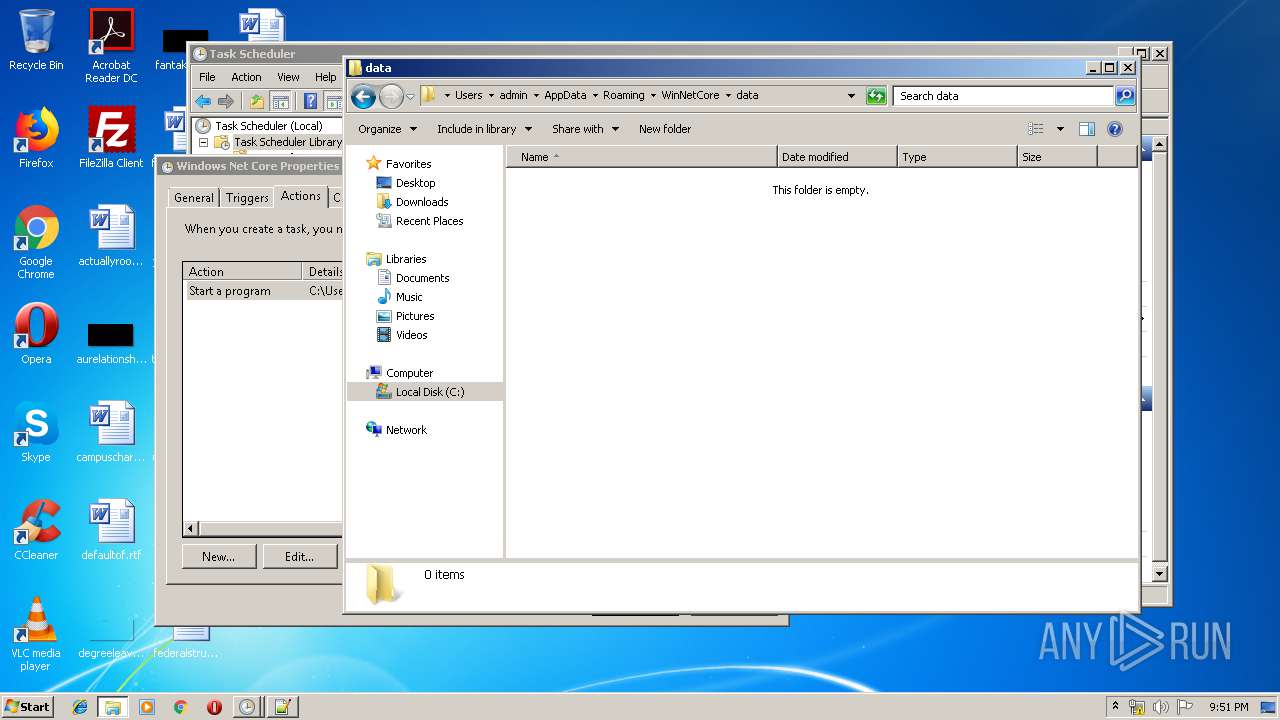
Creates files in the user directory
- studgm.exe (PID: 2424)
- notepad++.exe (PID: 3092)
- studio.exe (PID: 2548)
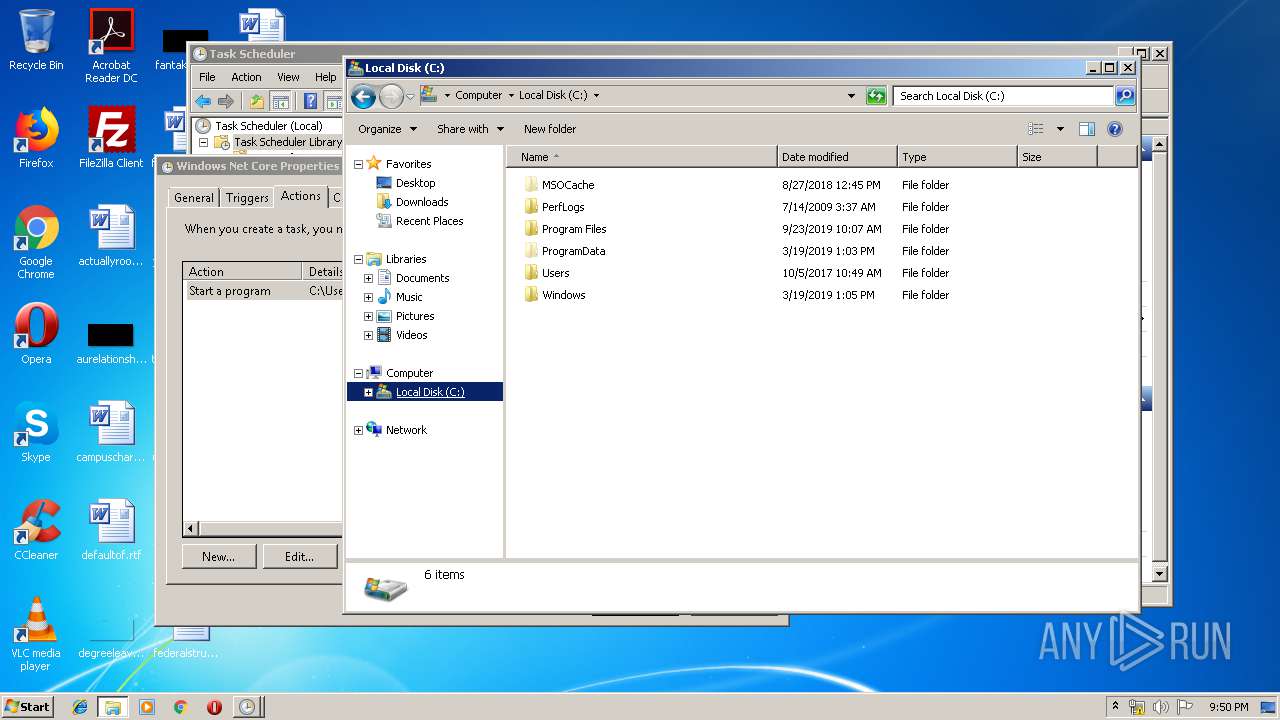
Creates files in the Windows directory
- studgm.exe (PID: 2424)
Removes files from Windows directory
- studgm.exe (PID: 2424)
INFO
Manual execution by user
- mmc.exe (PID: 2736)
- explorer.exe (PID: 1188)
- mmc.exe (PID: 944)
- studgm.exe (PID: 2252)
- notepad++.exe (PID: 3092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:16 15:09:55+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 29184 |
| InitializedDataSize: | 72704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x914e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | game |
| FileVersion: | 1.0.0.0 |
| InternalName: | temp.exe |
| LegalCopyright: | Copyright © 2009 |
| LegalTrademarks: | - |
| OriginalFileName: | temp.exe |
| ProductName: | game |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jan-2020 14:09:55 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | game |
| FileVersion: | 1.0.0.0 |
| InternalName: | temp.exe |
| LegalCopyright: | Copyright © 2009 |
| LegalTrademarks: | - |
| OriginalFilename: | temp.exe |
| ProductName: | game |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 16-Jan-2020 14:09:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00007154 | 0x00007200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.62939 |
.rsrc | 0x0000A000 | 0x000118C8 | 0x00011A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.58279 |
.reloc | 0x0001C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.44377 | 4217 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 2.08048 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
68
Monitored processes
18
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
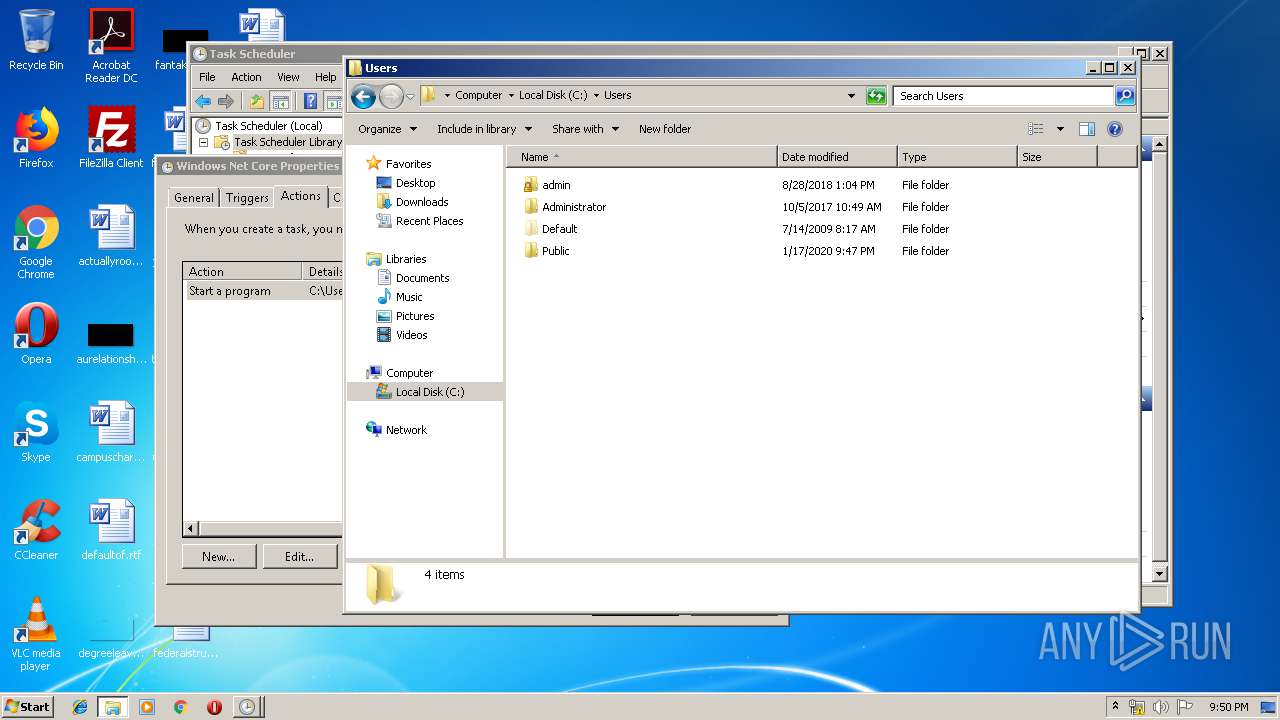
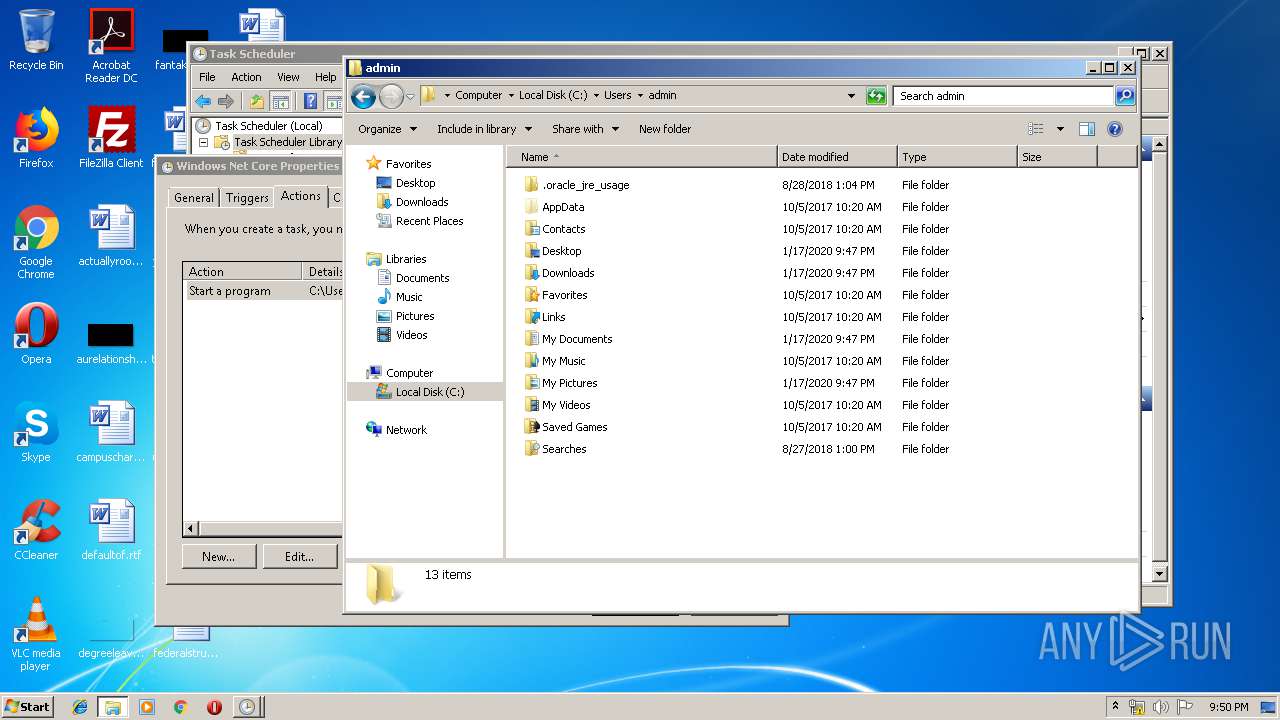
| 820 | C:\Users\Public\studio.exe | C:\Users\Public\studio.exe | — | winlogon.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ImageTool MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 944 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1188 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1412 | C:\Windows\System32\cmd.exe /C choice /C Y /N /D Y /T 10 & "C:\Users\Public\winlogon.exe" | C:\Windows\System32\cmd.exe | — | temp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2252 | "C:\Users\admin\AppData\Roaming\WinNetCore\studgm.exe" | C:\Users\admin\AppData\Roaming\WinNetCore\studgm.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ImageTool MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2388 | C:\Windows\System32\cmd.exe /C choice /C Y /N /D Y /T 5 & Del "C:\Users\admin\AppData\Local\Temp\temp.exe" & Del C:\Users\Public\tmp.bat & Del C:\Users\Public\tmpdir\tmpd.bat & Del C:\Users\Public\tmpdir\tmps.bat & rd C:\Users\Public\tmpdir | C:\Windows\System32\cmd.exe | — | temp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2424 | C:\Users\admin\AppData\Roaming\WinNetCore\studgm.exe | C:\Users\admin\AppData\Roaming\WinNetCore\studgm.exe | taskeng.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: ImageTool MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
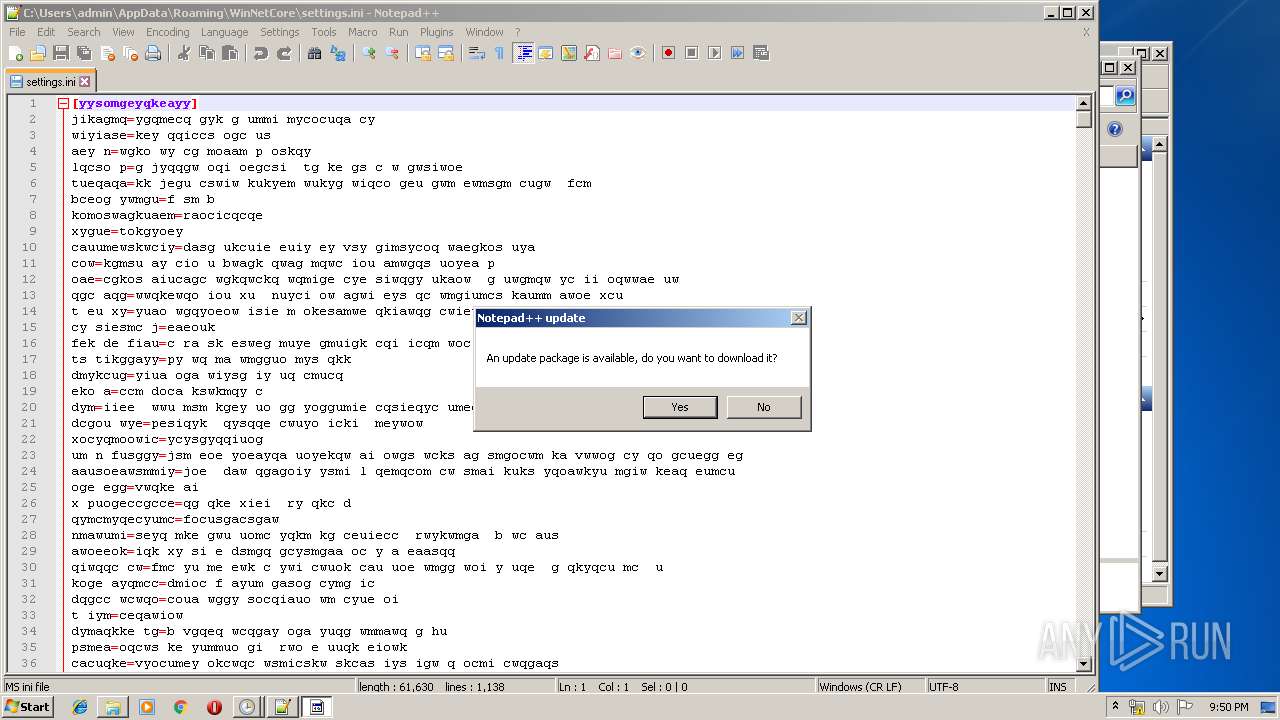
| 2428 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 2548 | "C:\Users\Public\studio.exe" | C:\Users\Public\studio.exe | DllHost.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: ImageTool MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2668 | choice /C Y /N /D Y /T 5 | C:\Windows\system32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
489
Read events
408
Write events
80
Delete events
1
Modification events
| (PID) Process: | (3392) winlogon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winlogon_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3392) winlogon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winlogon_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3392) winlogon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winlogon_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3392) winlogon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winlogon_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3392) winlogon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winlogon_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3392) winlogon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winlogon_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3392) winlogon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winlogon_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3392) winlogon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winlogon_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3392) winlogon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winlogon_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3392) winlogon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winlogon_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
3
Suspicious files
4
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | winlogon.exe | C:\Users\Public\stsk.exe | — | |
MD5:— | SHA256:— | |||
| 2424 | studgm.exe | C:\Windows\TEMP\Cab6B44.tmp | — | |
MD5:— | SHA256:— | |||
| 2424 | studgm.exe | C:\Windows\TEMP\Tar6B45.tmp | — | |
MD5:— | SHA256:— | |||
| 2424 | studgm.exe | C:\Windows\TEMP\Cab6B55.tmp | — | |
MD5:— | SHA256:— | |||
| 2424 | studgm.exe | C:\Windows\TEMP\Tar6B56.tmp | — | |
MD5:— | SHA256:— | |||
| 2424 | studgm.exe | C:\Windows\TEMP\Cab7FF9.tmp | — | |
MD5:— | SHA256:— | |||
| 2424 | studgm.exe | C:\Windows\TEMP\Tar7FFA.tmp | — | |
MD5:— | SHA256:— | |||
| 2548 | studio.exe | C:\Users\admin\AppData\Roaming\WinNetCore\studgm.exe | executable | |
MD5:— | SHA256:— | |||
| 2424 | studgm.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
| 3092 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:E792264BEC29005B9044A435FBA185AB | SHA256:5298FD2F119C43D04F6CF831F379EC25B4156192278E40E458EC356F9B49D624 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
11
DNS requests
10
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2424 | studgm.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3392 | winlogon.exe | GET | 302 | 104.168.99.30:80 | http://104.168.99.30/52Fc38FHeiWE3 | US | — | — | unknown |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAxHWpoyfQpCuYL7zNoKQA4%3D | US | der | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3392 | winlogon.exe | 104.168.99.30:80 | — | ColoCrossing | US | unknown |
3392 | winlogon.exe | 185.61.154.215:443 | analysprinter.online | Namecheap, Inc. | GB | suspicious |
2428 | gup.exe | 104.31.88.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
2424 | studgm.exe | 5.182.210.226:443 | — | — | — | malicious |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2424 | studgm.exe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2424 | studgm.exe | 185.255.55.29:443 | api.ip.sb | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
analysprinter.online |
| suspicious |
www.analysprinter.online |
| suspicious |
dns.msftncsi.com |
| shared |
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
api.ip.sb |
| whitelisted |
144.69.192.185.zen.spamhaus.org |
| unknown |
144.69.192.185.cbl.abuseat.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2424 | studgm.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 18 |
2424 | studgm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
2424 | studgm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
2424 | studgm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
2424 | studgm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
2424 | studgm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
2424 | studgm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
2424 | studgm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
2424 | studgm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
2424 | studgm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
16 ETPRO signatures available at the full report
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|