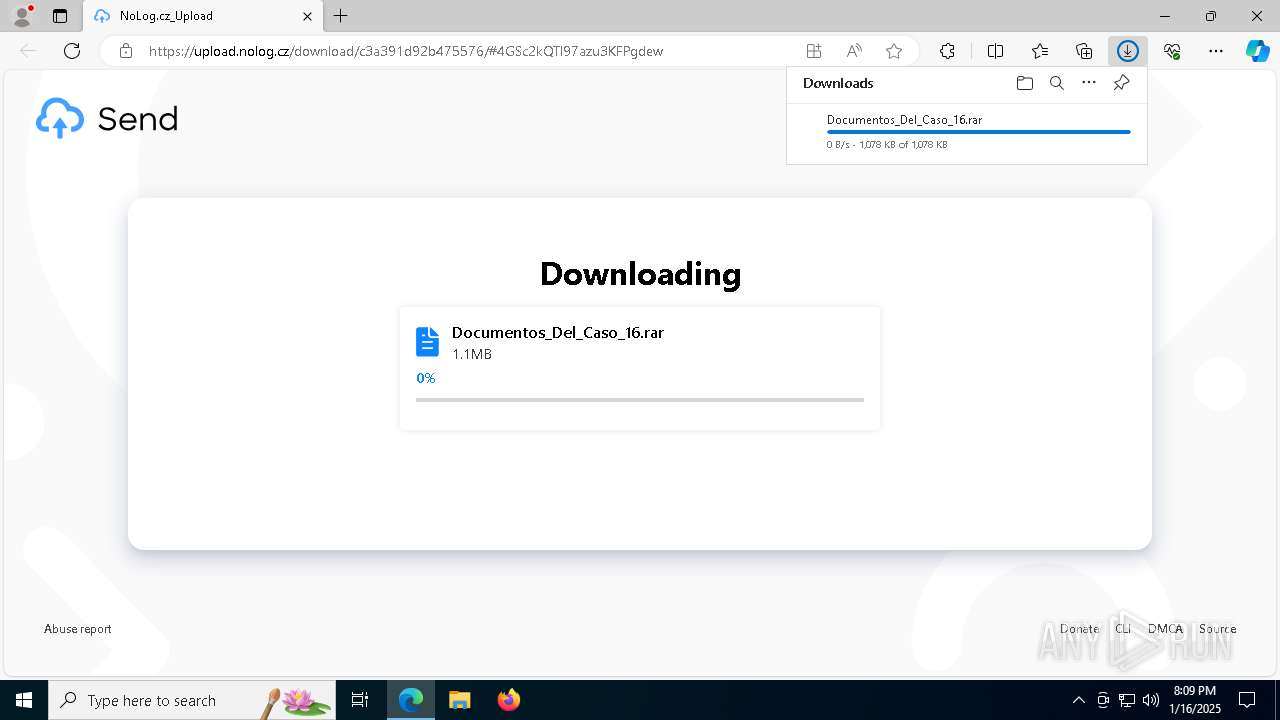
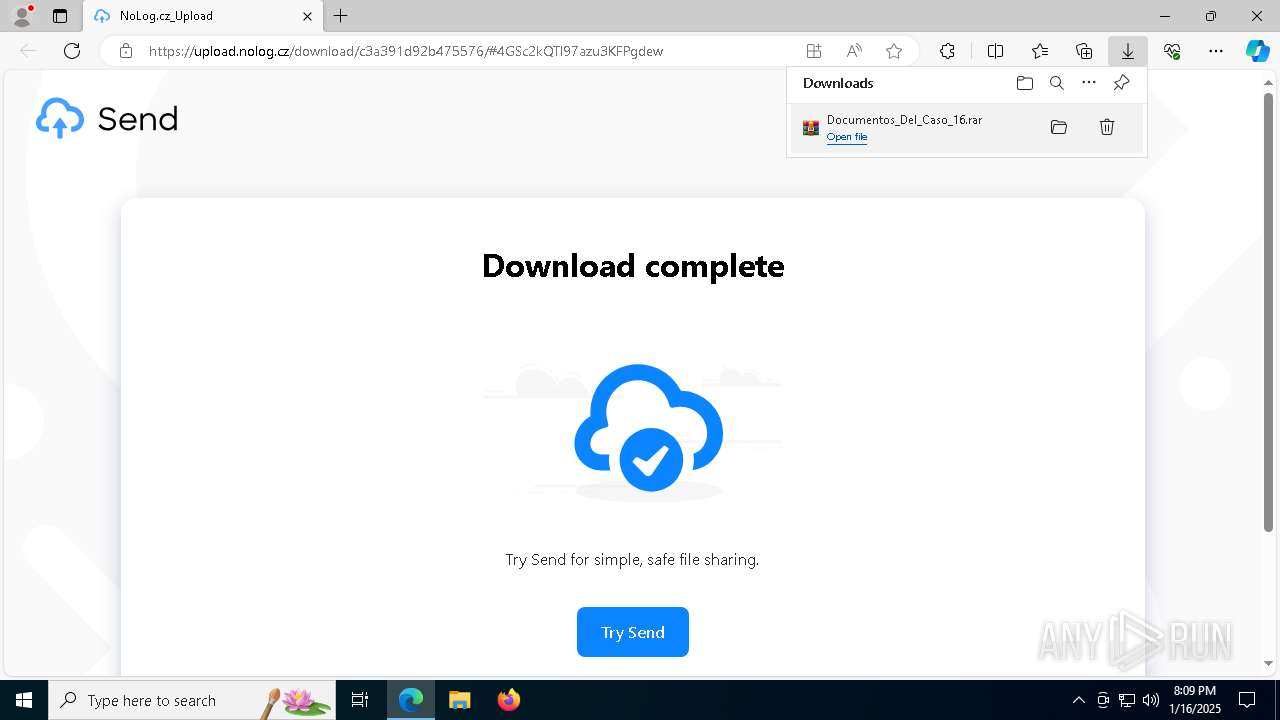
| URL: | https://upload.nolog.cz/download/c3a391d92b475576/#4GSc2kQTl97azu3KFPgdew |
| Full analysis: | https://app.any.run/tasks/1738be96-d556-4639-b6f6-d57506343997 |
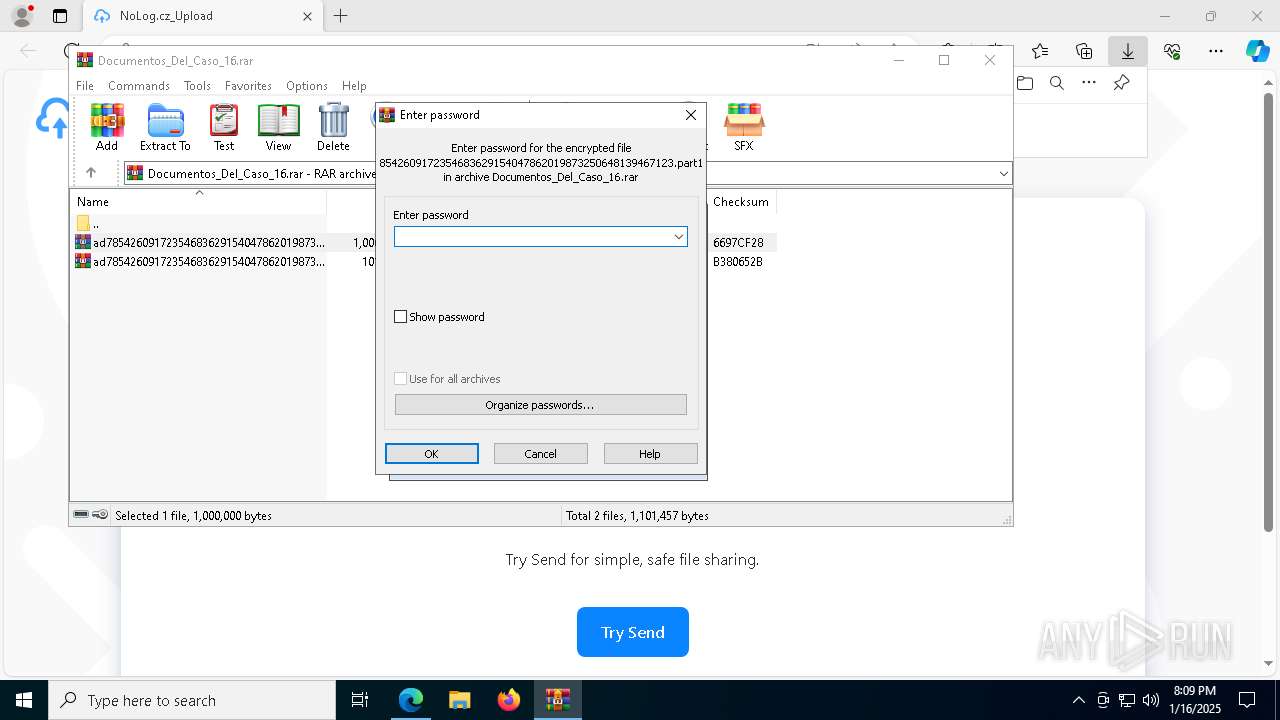
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | January 16, 2025, 20:09:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | ABE5DD8CF75E7DEA49068F27AC597B5F |
| SHA1: | 0B8071F58A59B417B8F5619F0392E2D91043EAB6 |
| SHA256: | D30383185340217D46B107F95A1ADF9EDAF2A3F45D0DB49647DF8284326310FE |
| SSDEEP: | 3:N8ZEkryi2B/cH/KGi2AOmN1O:2ZEayj/F12At1O |
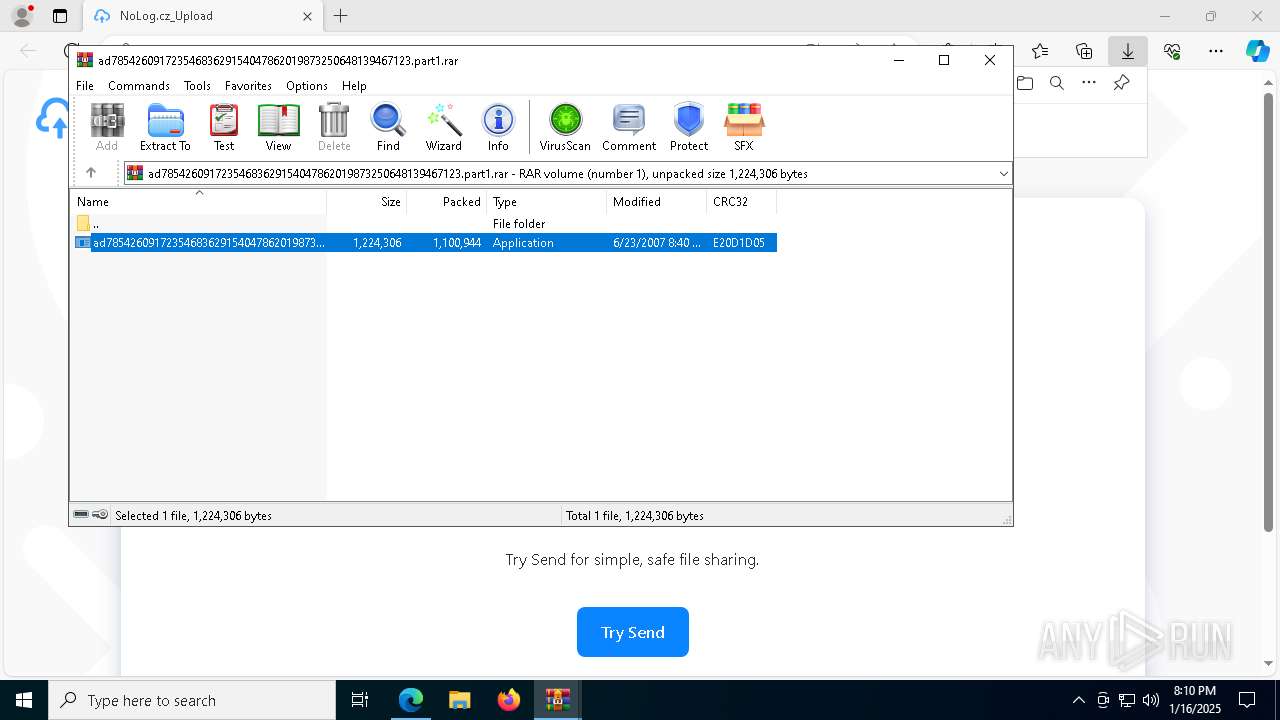
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7548)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7684)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 4980)
SUSPICIOUS
Application launched itself
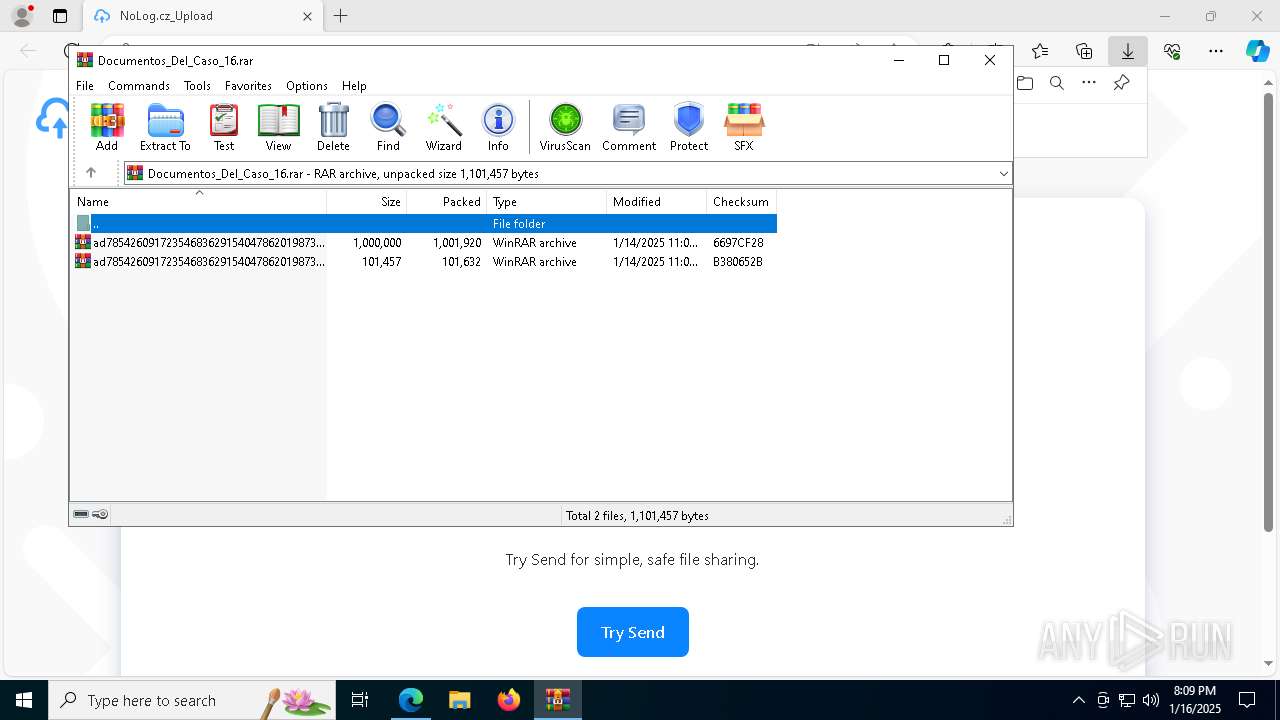
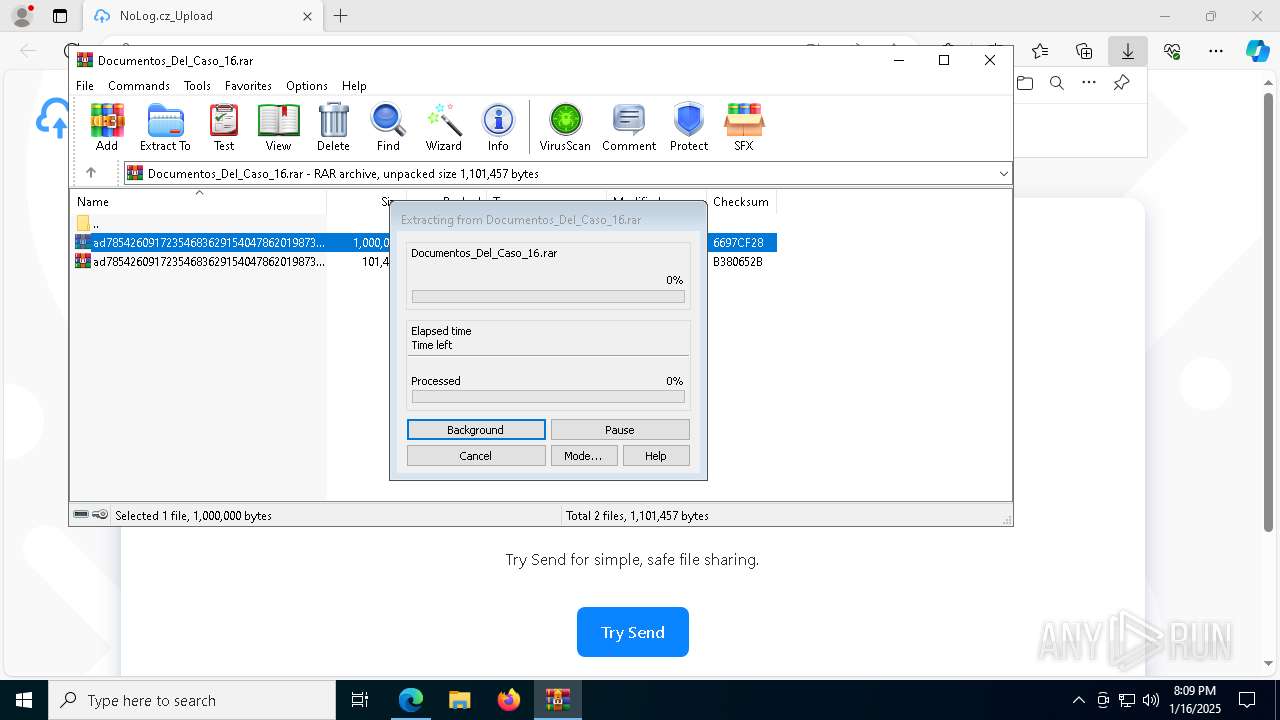
- WinRAR.exe (PID: 2548)
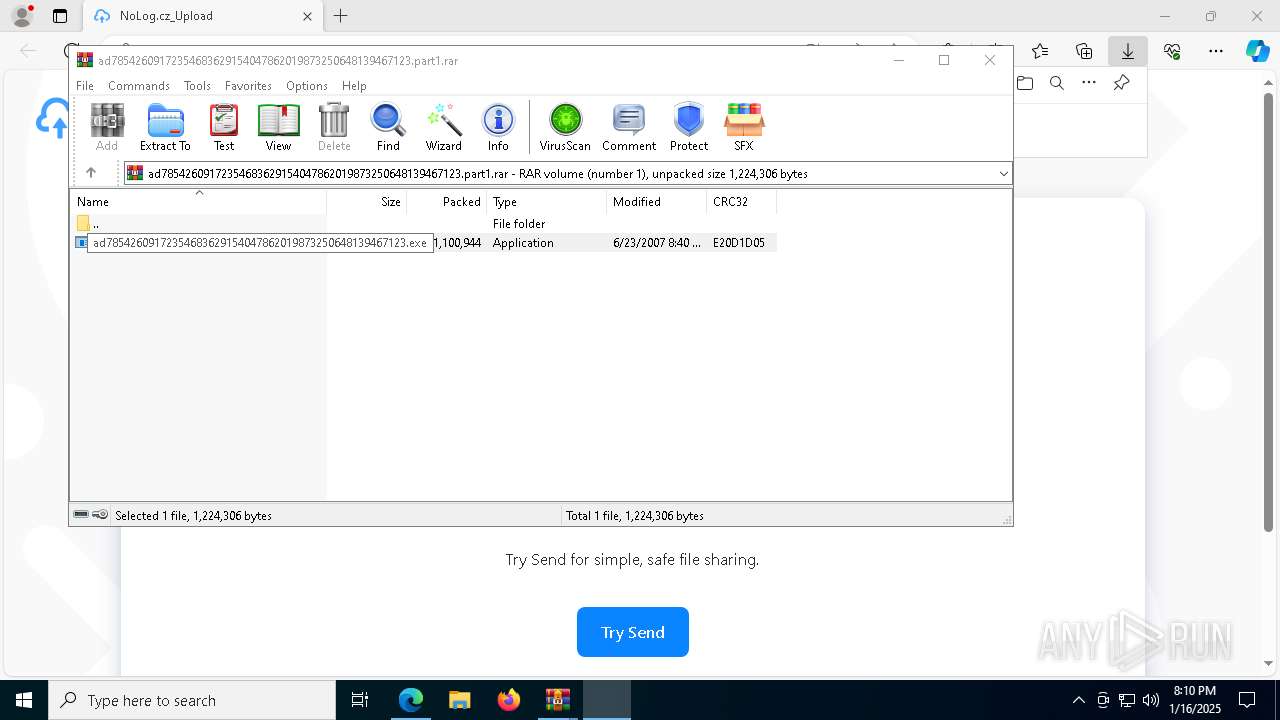
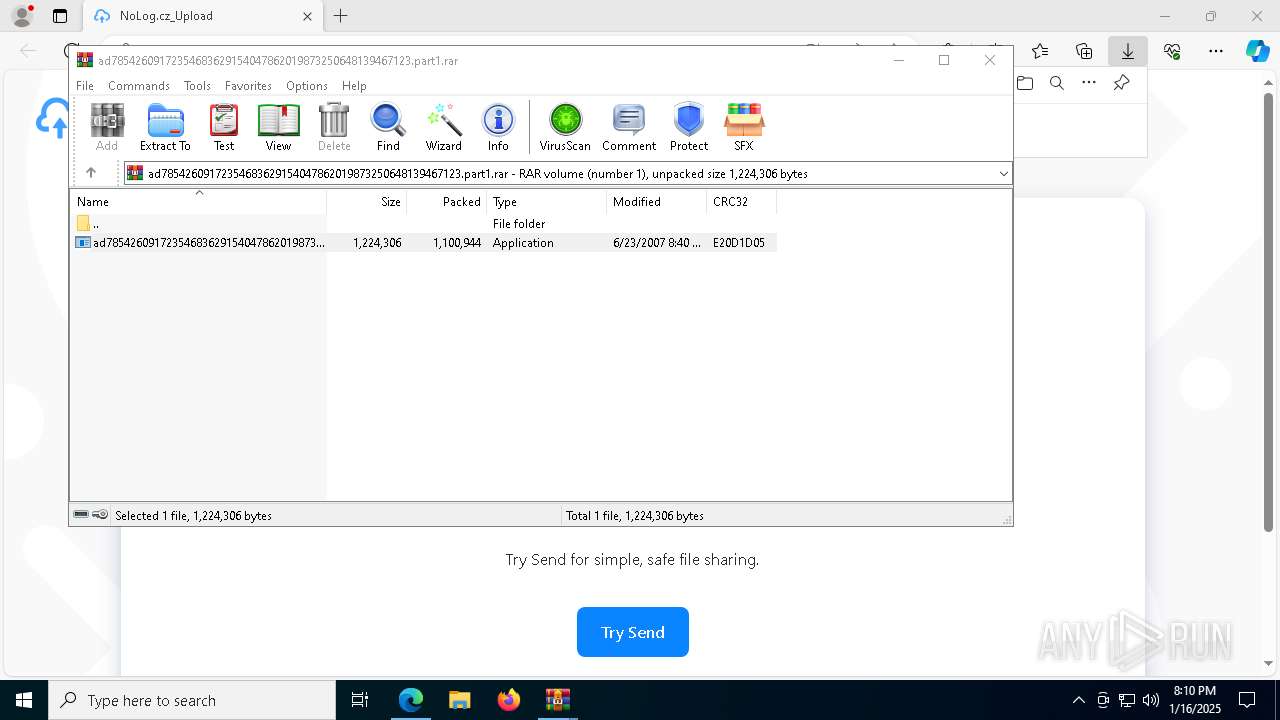
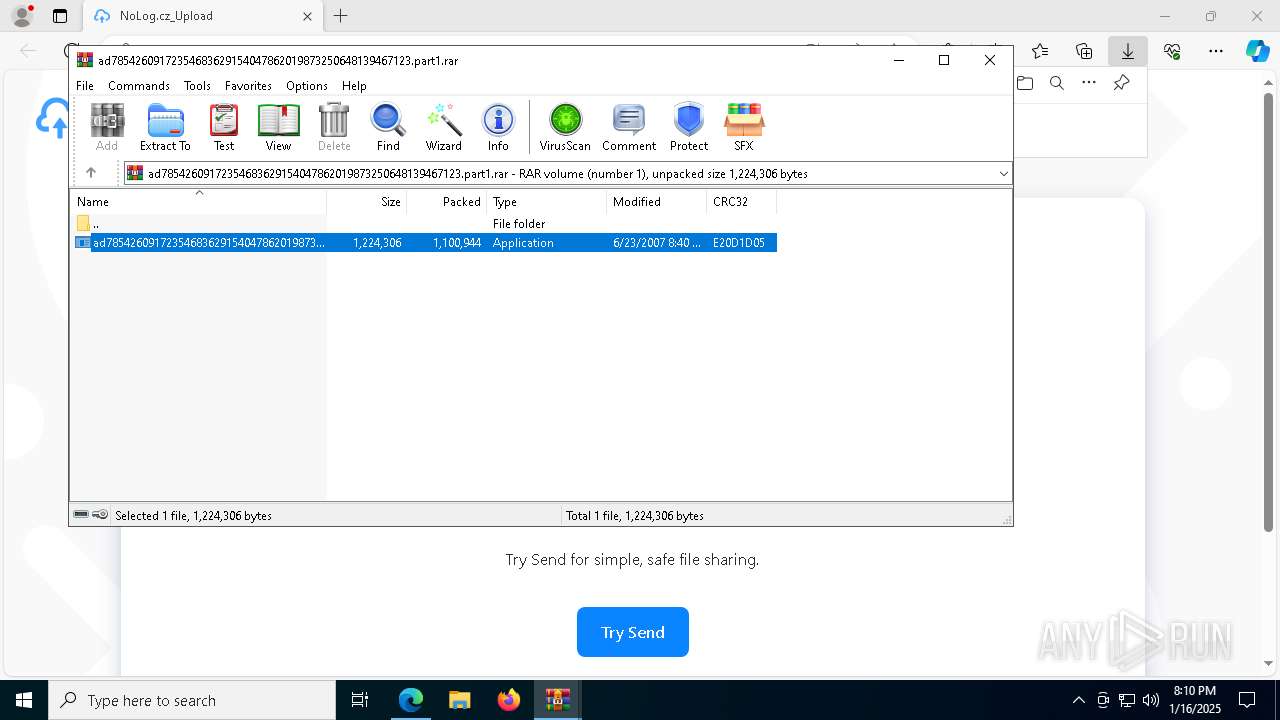
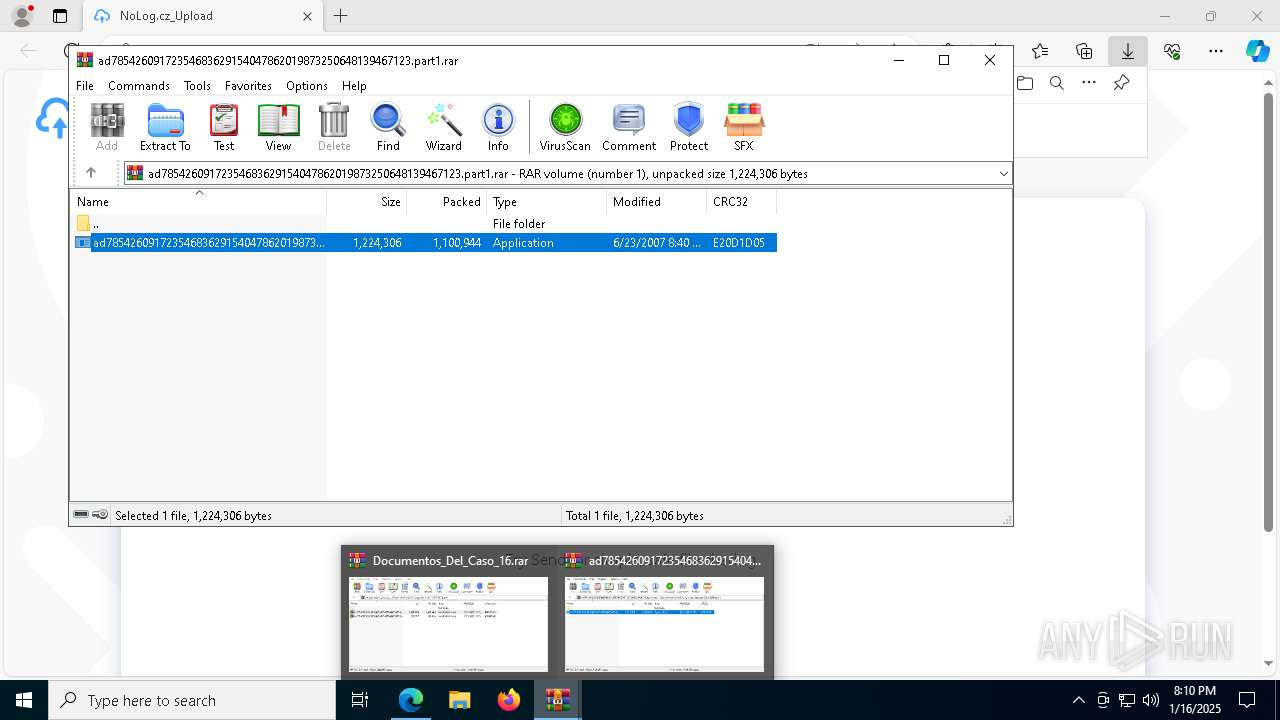
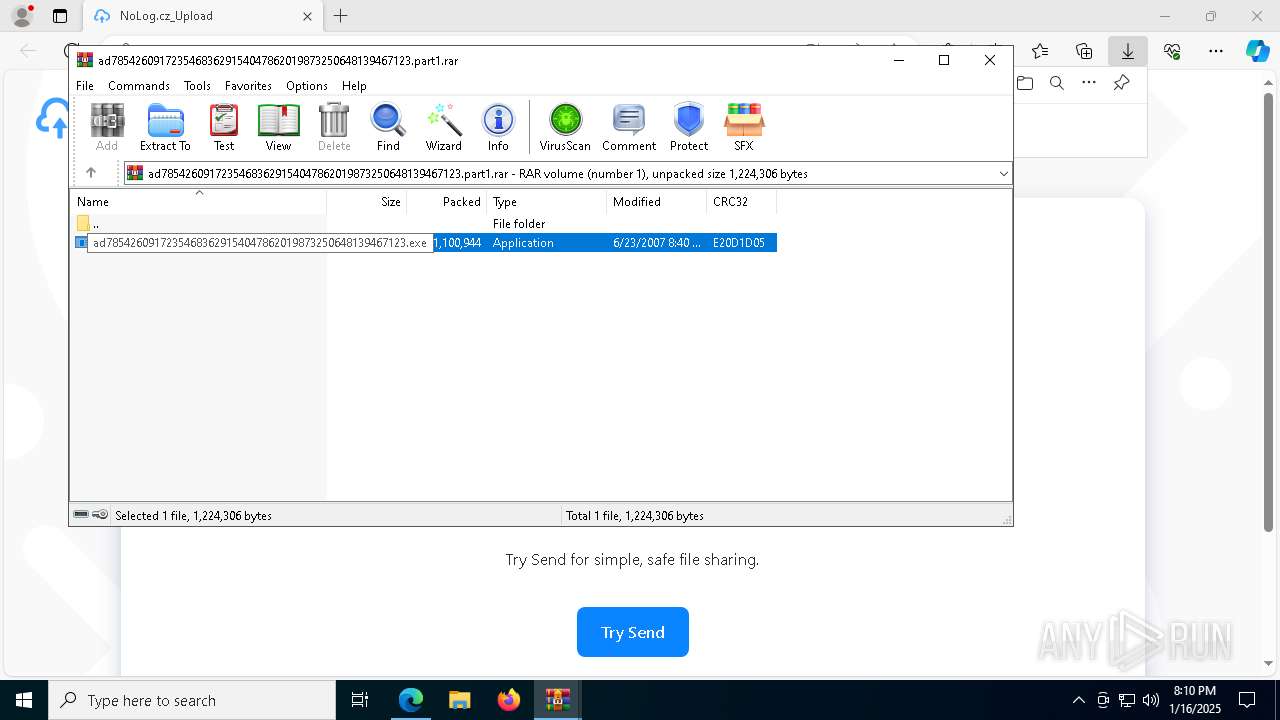
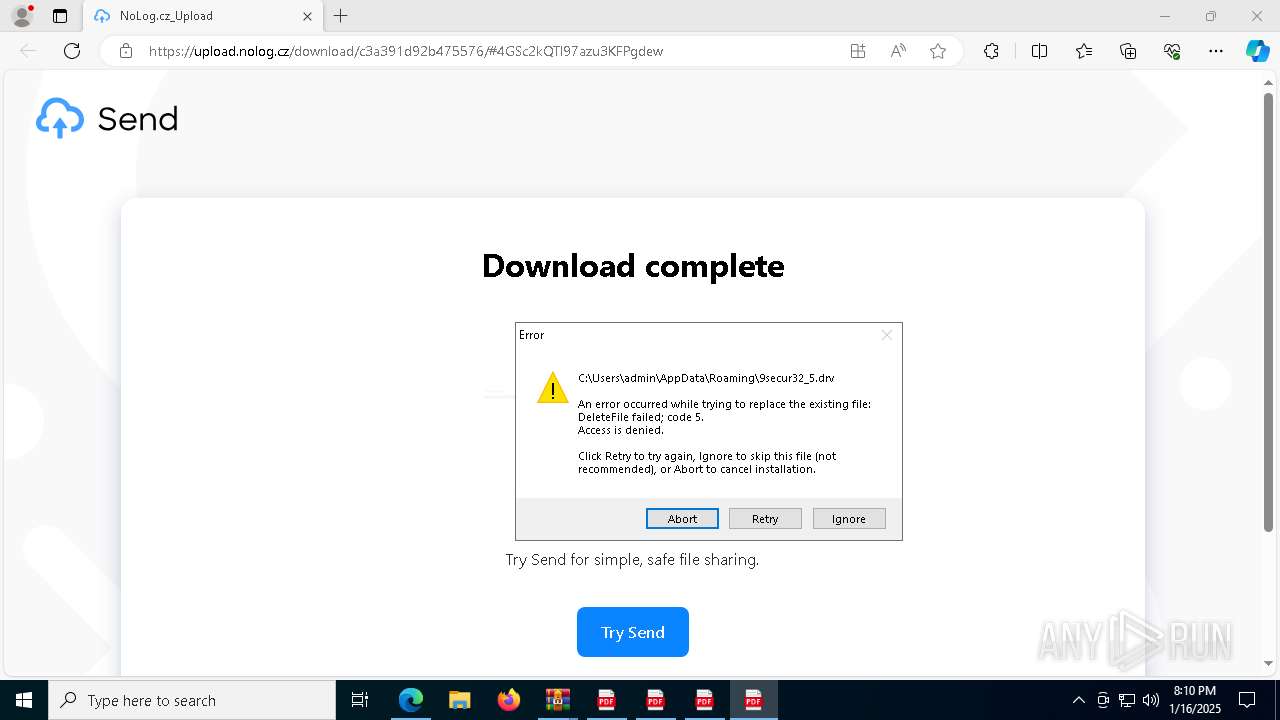
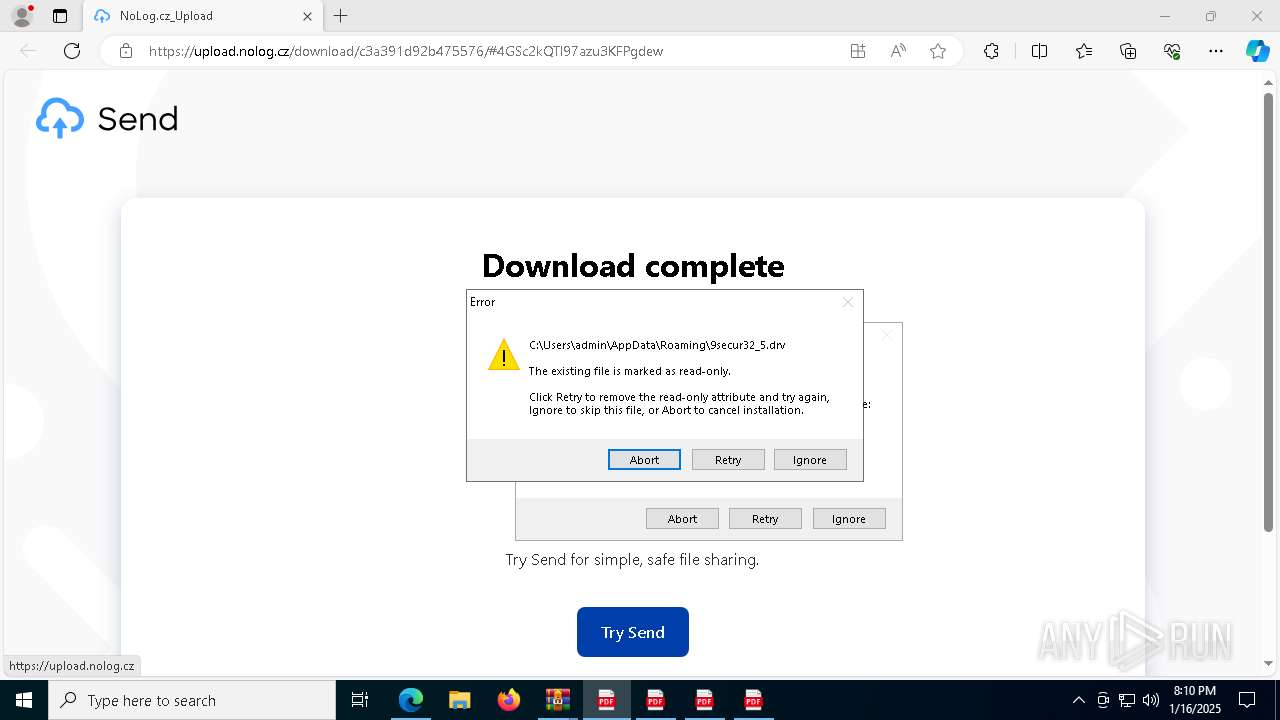
Executable content was dropped or overwritten
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7464)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7484)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7520)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7548)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7284)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 1576)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 2512)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 3836)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 5096)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7328)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7368)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 5888)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 4980)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7444)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7540)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7480)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 1468)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 3928)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7528)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7560)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7888)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 2280)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 6152)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7932)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7908)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7816)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7700)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 8016)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7852)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7792)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7684)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7960)
Process drops legitimate windows executable
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7484)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7548)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7284)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 2512)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 4980)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7444)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7328)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7528)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 6152)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7960)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 1468)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 3928)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 8016)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7792)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7684)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7908)
Reads the Windows owner or organization settings
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7484)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7548)
Starts POWERSHELL.EXE for commands execution
- regsvr32.exe (PID: 7628)
- regsvr32.exe (PID: 2728)
- regsvr32.exe (PID: 8156)
Searches for installed software
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 4980)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 1468)
INFO
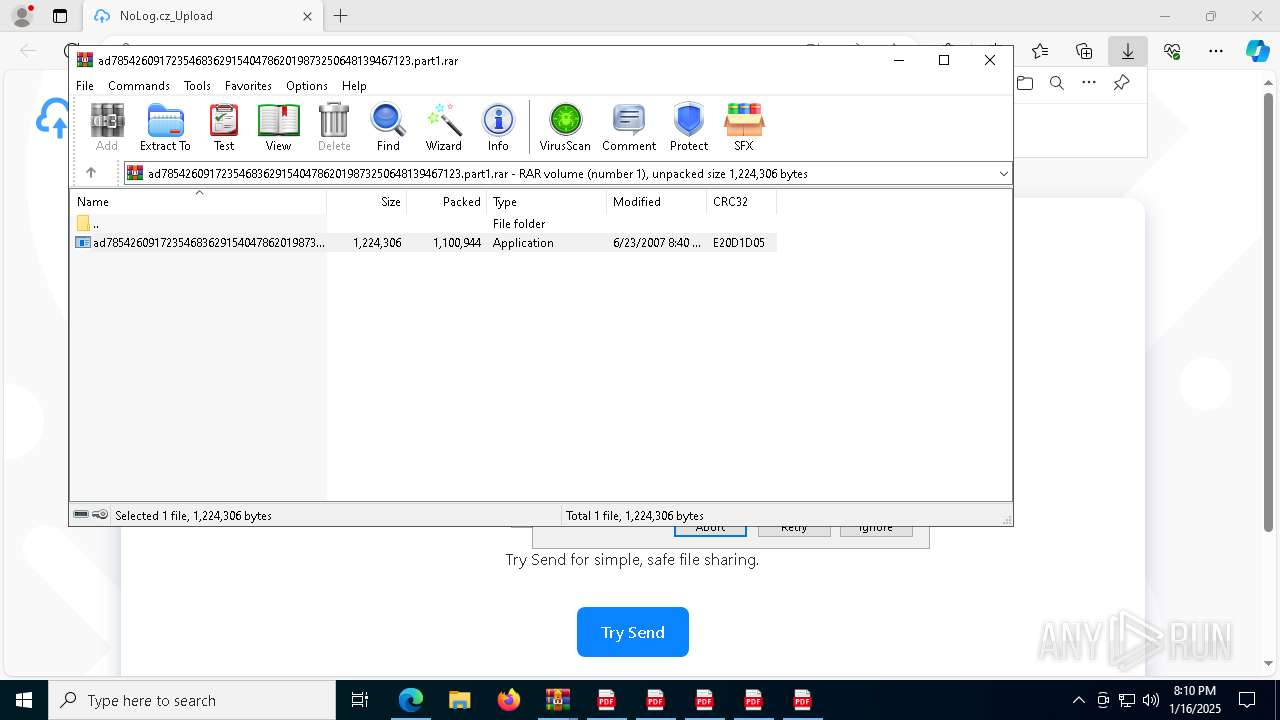
The process uses the downloaded file
- WinRAR.exe (PID: 2548)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7484)
Checks supported languages
- identity_helper.exe (PID: 836)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7464)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7520)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7548)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 1576)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7284)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7328)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7444)
- ad78542609172354683629154047862019873250648139467123.exe (PID: 7540)
Application launched itself
- msedge.exe (PID: 3612)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3612)
The sample compiled with english language support
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7484)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7548)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 2512)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7284)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7328)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7444)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 4980)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 1468)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 3928)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7528)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 6152)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7960)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7908)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 8016)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7792)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7684)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7388)
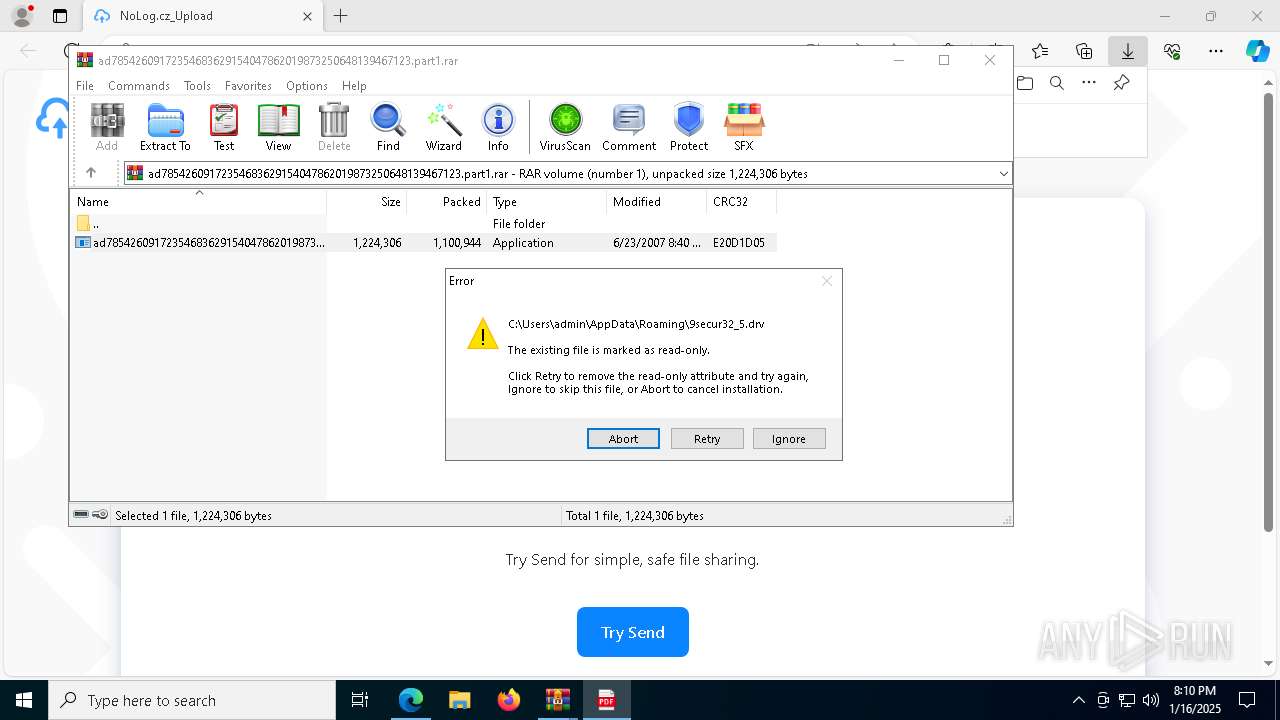
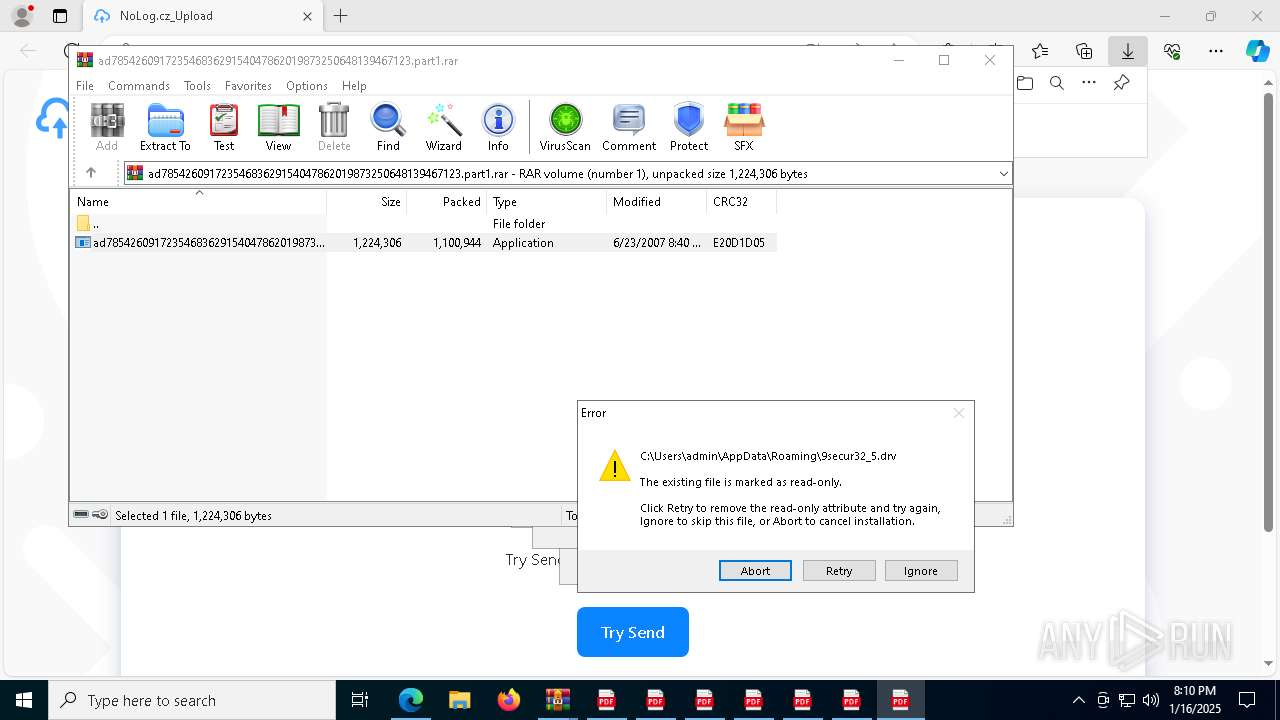
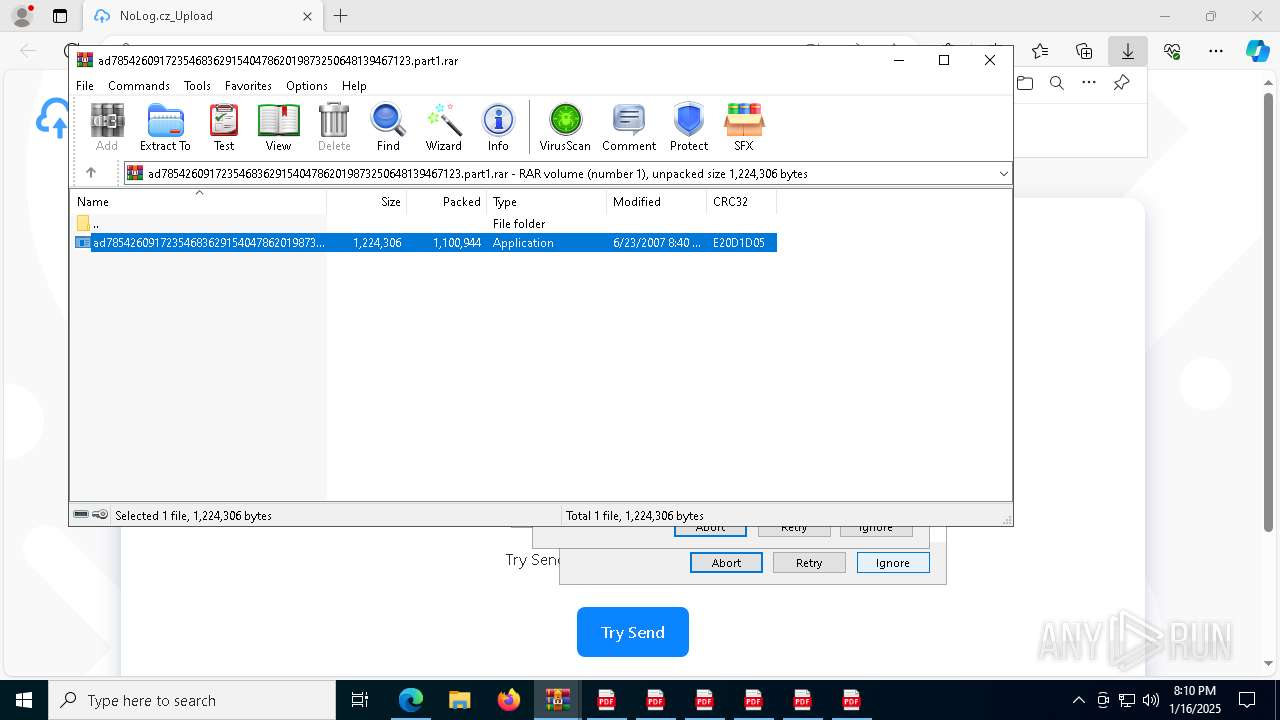
Create files in a temporary directory
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7548)
Creates files or folders in the user directory
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7548)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7656)
- powershell.exe (PID: 8076)
- powershell.exe (PID: 6872)
Process checks computer location settings
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7328)
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7444)
Reads the computer name
- ad78542609172354683629154047862019873250648139467123.tmp (PID: 7444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
216
Monitored processes
83
Malicious processes
3
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 836 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7064 --field-trial-handle=2388,i,9641861852151366078,5353340209743063011,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1468 | "C:\Users\admin\AppData\Local\Temp\is-LF0TL.tmp\ad78542609172354683629154047862019873250648139467123.tmp" /SL5="$7028A,829056,185856,C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.2439\ad78542609172354683629154047862019873250648139467123.exe" /VERYSILENT | C:\Users\admin\AppData\Local\Temp\is-LF0TL.tmp\ad78542609172354683629154047862019873250648139467123.tmp | ad78542609172354683629154047862019873250648139467123.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 5 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1576 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.2166\ad78542609172354683629154047862019873250648139467123.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.2166\ad78542609172354683629154047862019873250648139467123.exe | WinRAR.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Dangerous Square Setup Exit code: 1 Version: Modules
| |||||||||||||||
| 2164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=5340 --field-trial-handle=2388,i,9641861852151366078,5353340209743063011,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2280 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.2595\ad78542609172354683629154047862019873250648139467123.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.2595\ad78542609172354683629154047862019873250648139467123.exe | WinRAR.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Dangerous Square Setup Exit code: 1 Version: Modules
| |||||||||||||||
| 2512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7276 --field-trial-handle=2388,i,9641861852151366078,5353340209743063011,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2512 | "C:\Users\admin\AppData\Local\Temp\is-6TA2O.tmp\ad78542609172354683629154047862019873250648139467123.tmp" /SL5="$4022E,829056,185856,C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.2166\ad78542609172354683629154047862019873250648139467123.exe" | C:\Users\admin\AppData\Local\Temp\is-6TA2O.tmp\ad78542609172354683629154047862019873250648139467123.tmp | ad78542609172354683629154047862019873250648139467123.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2548 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Documentos_Del_Caso_16.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | msedge.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2676 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7268 --field-trial-handle=2388,i,9641861852151366078,5353340209743063011,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
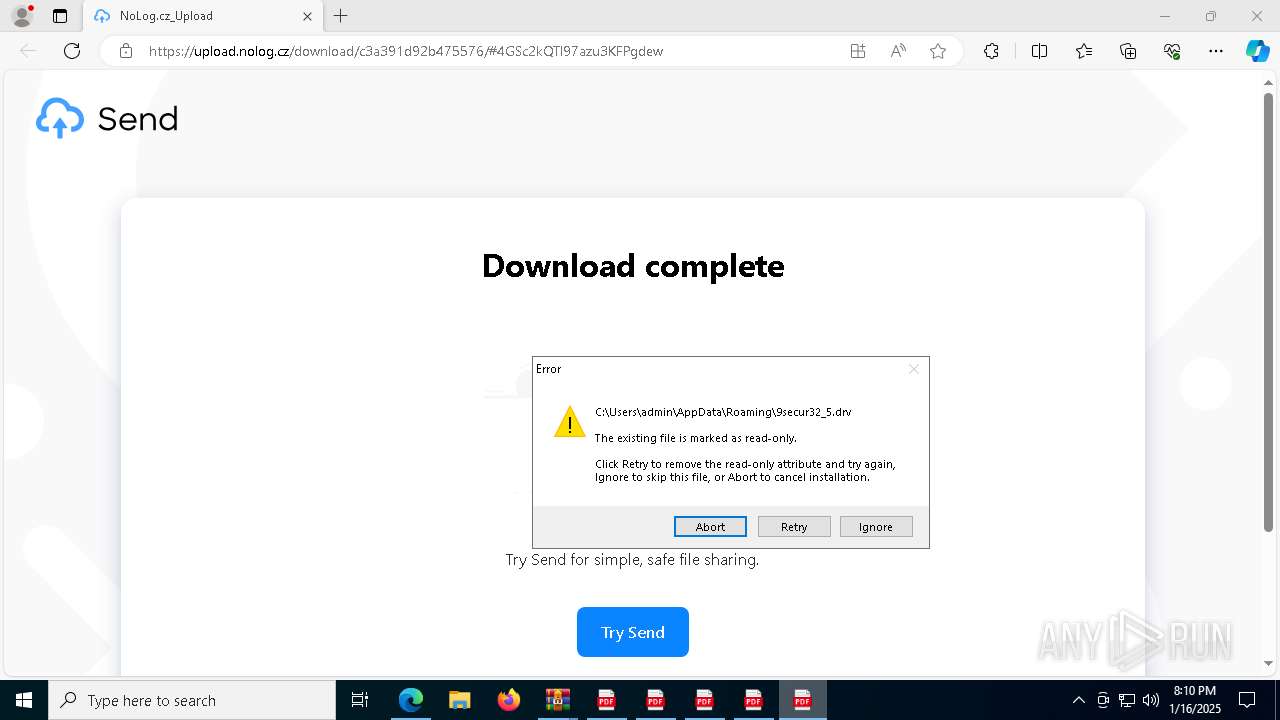
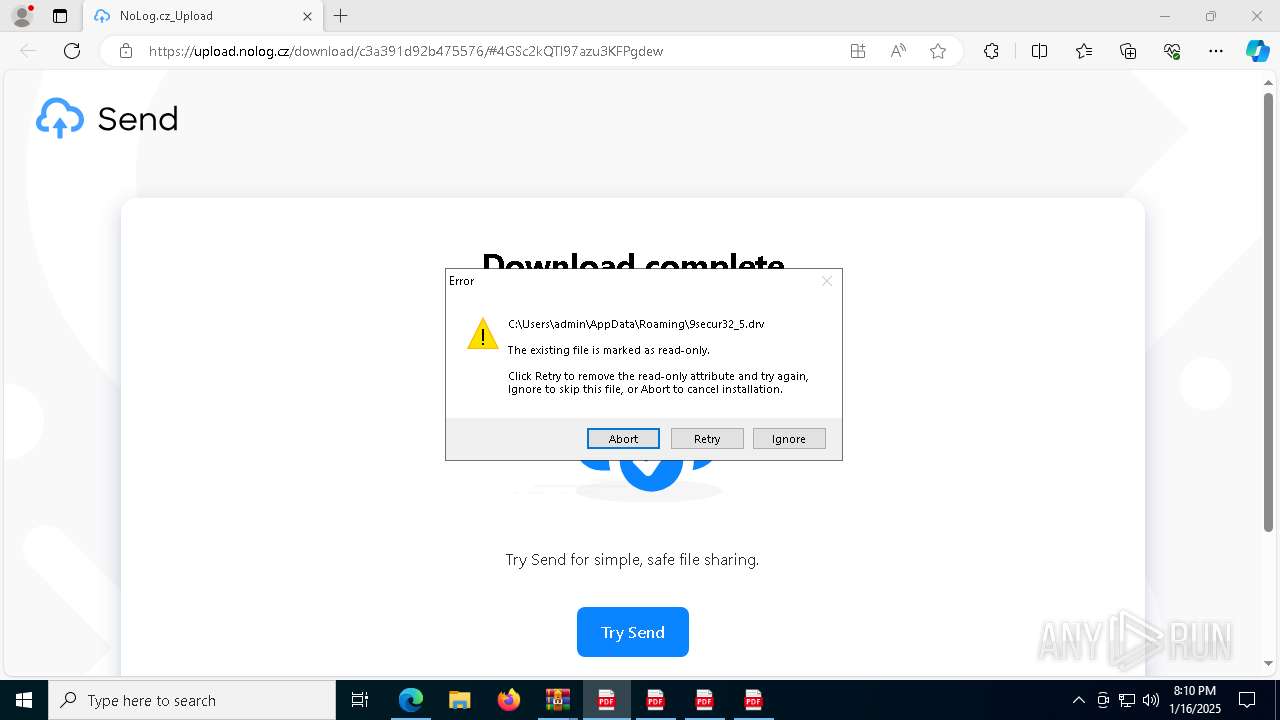
| 2728 | /s /i:SYNC "C:\Users\admin\AppData\Roaming\\9secur32_5.drv" | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
40 650
Read events
40 489
Write events
119
Delete events
42
Modification events
| (PID) Process: | (3612) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3612) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3612) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3612) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3612) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E89A3EA86E8A2F00 | |||
| (PID) Process: | (3612) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FAE74BA86E8A2F00 | |||
| (PID) Process: | (3612) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393968 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DDB42281-342E-455E-BAC2-08FC73185965} | |||
| (PID) Process: | (3612) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393968 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3B50DFF0-DA39-4216-9F59-EA36E0469EA2} | |||
| (PID) Process: | (3612) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393968 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {43573DBB-4B47-404A-A23C-C1FC0B952826} | |||
| (PID) Process: | (3612) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393968 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B2749751-0136-42EF-8080-5257438AE4ED} | |||
Executable files
91
Suspicious files
249
Text files
51
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\9e418121-d9a8-4b71-805f-c4bd524f3621.tmp | — | |
MD5:— | SHA256:— | |||
| 3612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF136361.TMP | — | |
MD5:— | SHA256:— | |||
| 3612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF136361.TMP | — | |
MD5:— | SHA256:— | |||
| 3612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF136361.TMP | — | |
MD5:— | SHA256:— | |||
| 3612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF136351.TMP | — | |
MD5:— | SHA256:— | |||
| 3612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF13639f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
54
DNS requests
51
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7568 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7568 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2676 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3612 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6344 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6344 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6344 | msedge.exe | 93.185.97.211:443 | upload.nolog.cz | VSHosting s.r.o. | CZ | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
upload.nolog.cz |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
— | — | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
1 ETPRO signatures available at the full report