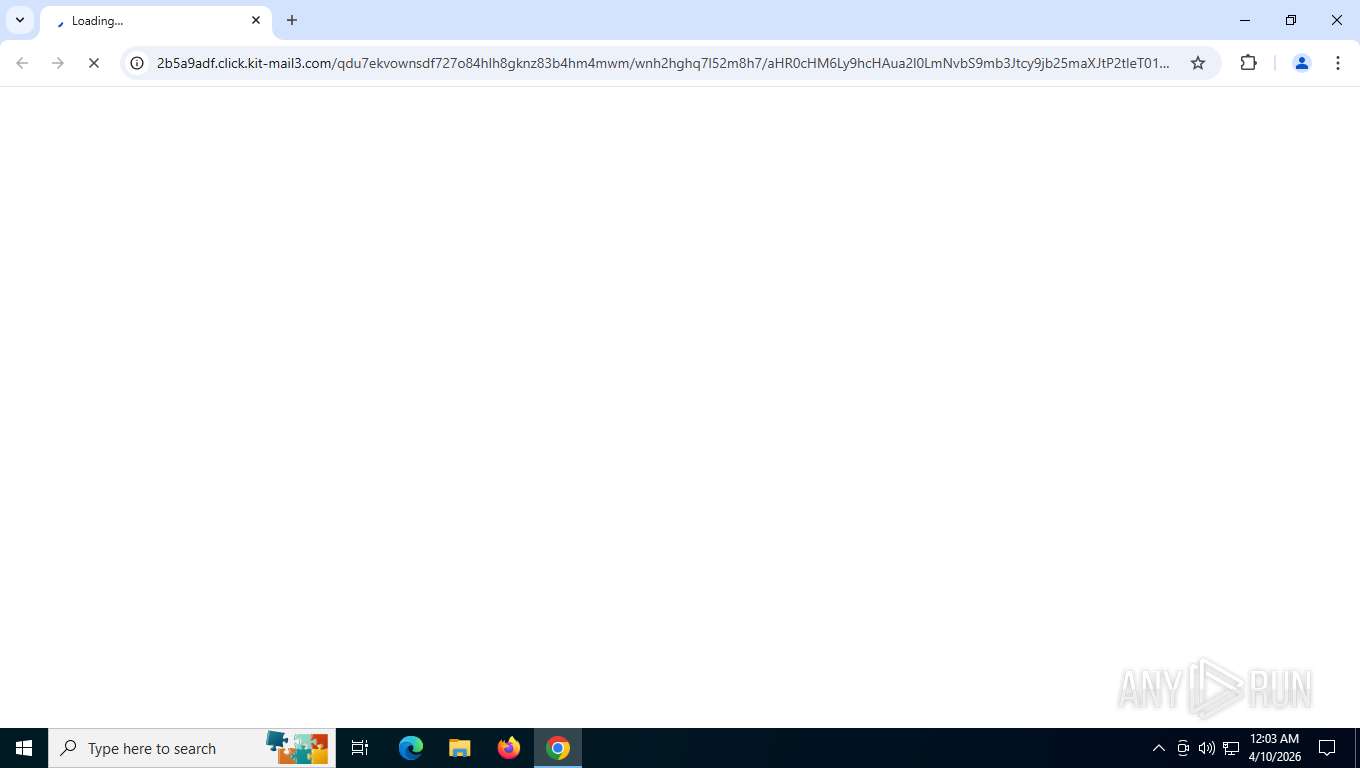
| URL: | https://2b5a9adf.click.kit-mail3.com/qdu7ekvownsdf727o84hlh8gknz83b4hm4mwm/wnh2hghq7l52m8h7/aHR0cHM6Ly9hcHAua2l0LmNvbS9mb3Jtcy9jb25maXJtP2tleT01YTgzZGQxYTA3YmM0MzFlYTRkOWU0NzA4N2Q5ZWRkNDY3YjU1MzE2JnNpZD0xMTIxODY3ODQ5NA== |
| Full analysis: | https://app.any.run/tasks/362c8f45-a8b8-4dde-a599-85105102f16c |
| Verdict: | Malicious activity |
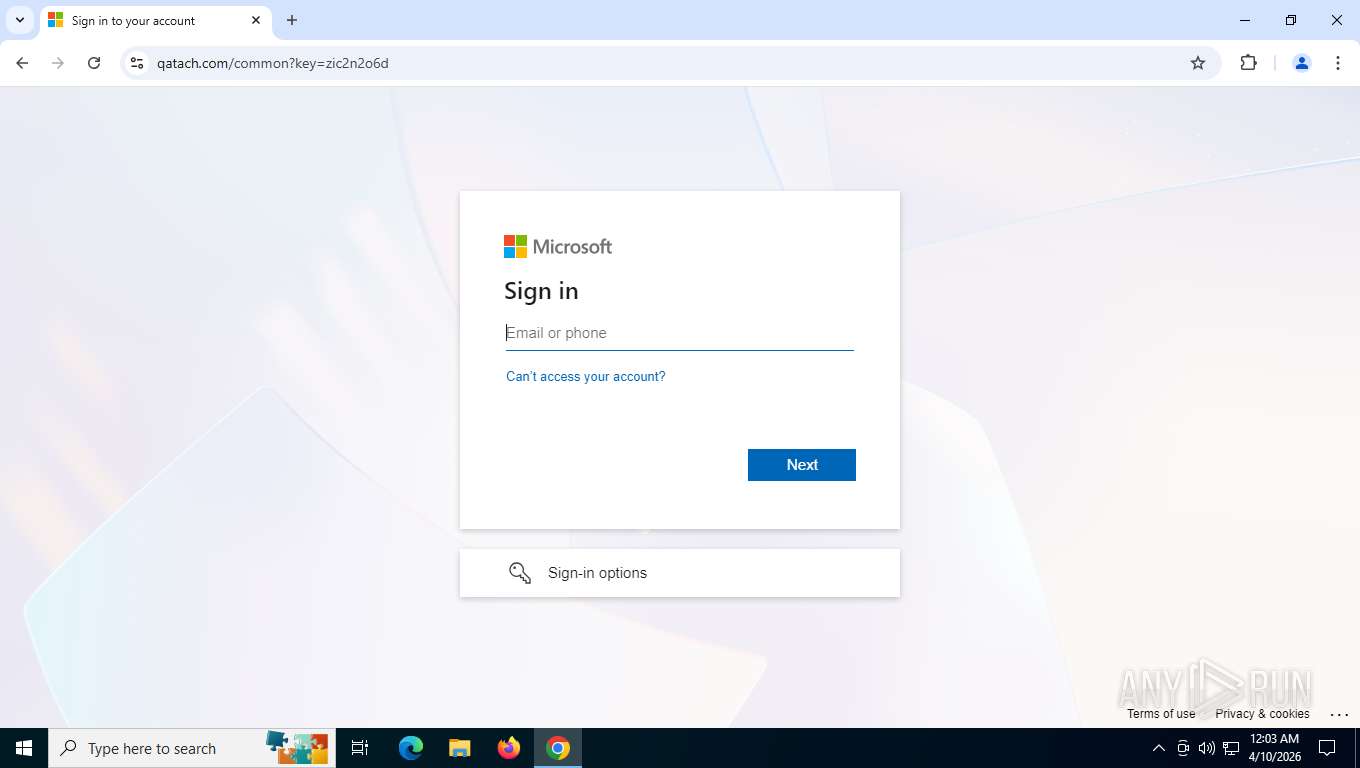
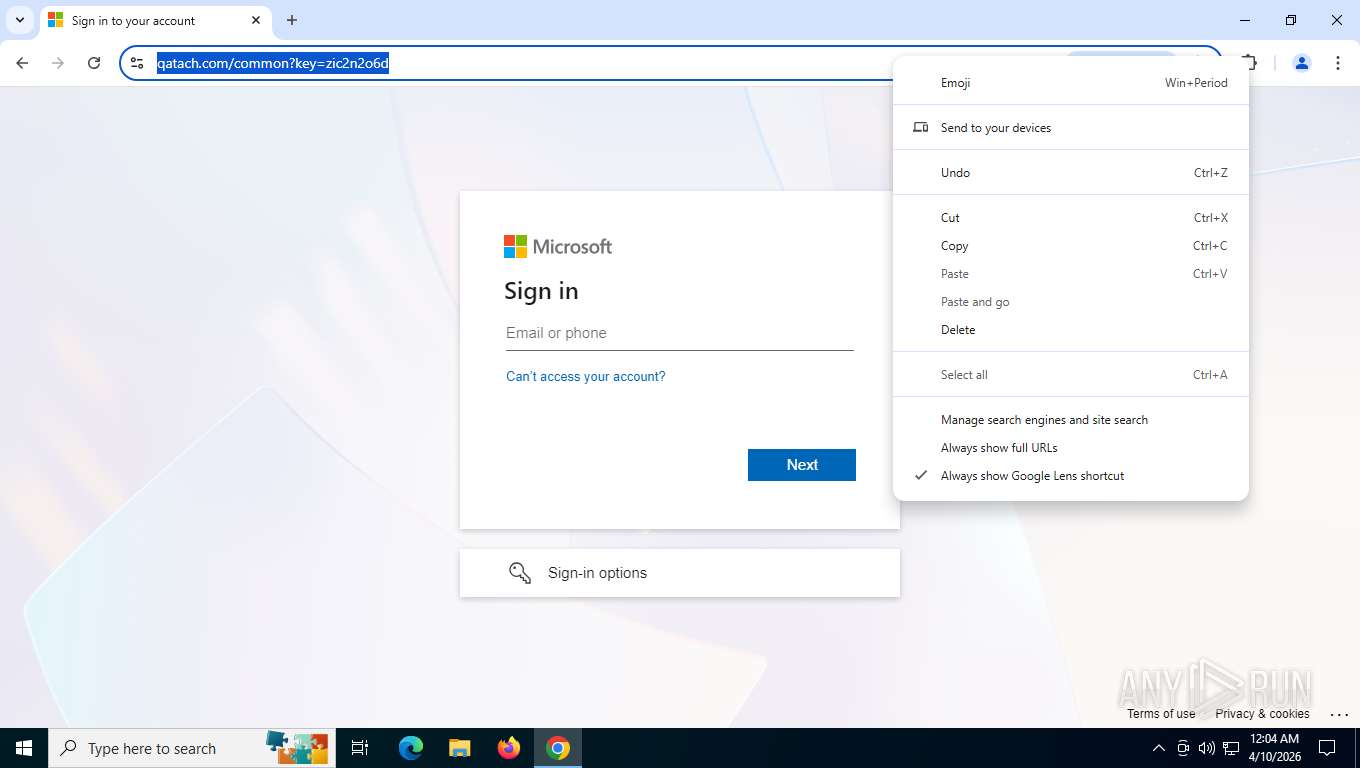
| Threats: | EvilProxy is a phishing-as-a-service (PhaaS) platform that enables cybercriminals to bypass multi-factor authentication (MFA) and hijack user sessions. It leverages reverse proxy techniques to harvest credentials and session cookies, posing a serious threat to both individuals and enterprises. |
| Analysis date: | April 10, 2026, 04:03:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2AD5A16F88D52590FEBEC5C8EB2DE33F |
| SHA1: | 23745C9622937BFB468260C4DE871D458F74D3A6 |
| SHA256: | D2FD0E4A57940CDAA42A2A77F3E3D759022DC7830187DD2F86BEBD6687D7F2A8 |
| SSDEEP: | 3:N8/WJMGHAHKIK9iFLW1kSOf9dGvKEt3MOP0ktpUb6WK/a7/V8xCX+OSyx3OqyxGS:27GDz1kbfOfFXyM/Yd9SyiUk8Te1 |
MALICIOUS
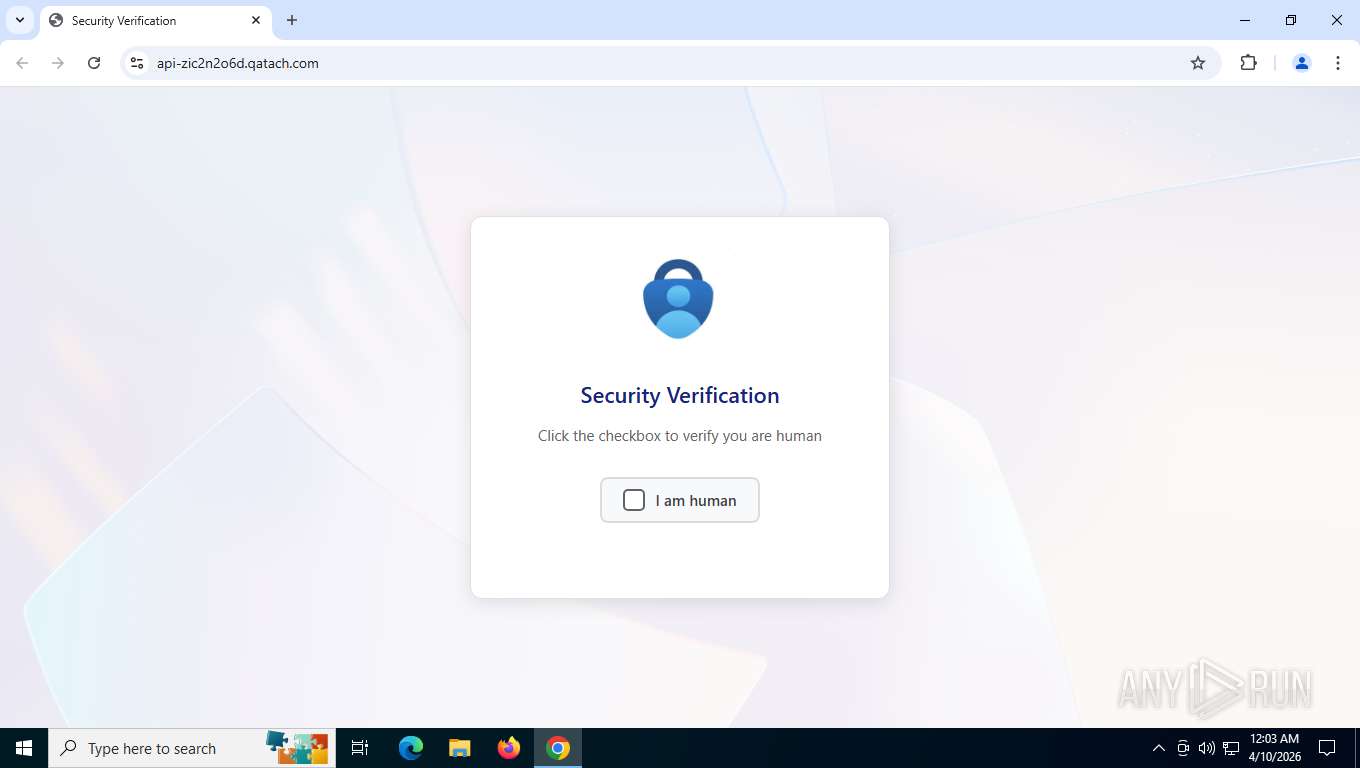
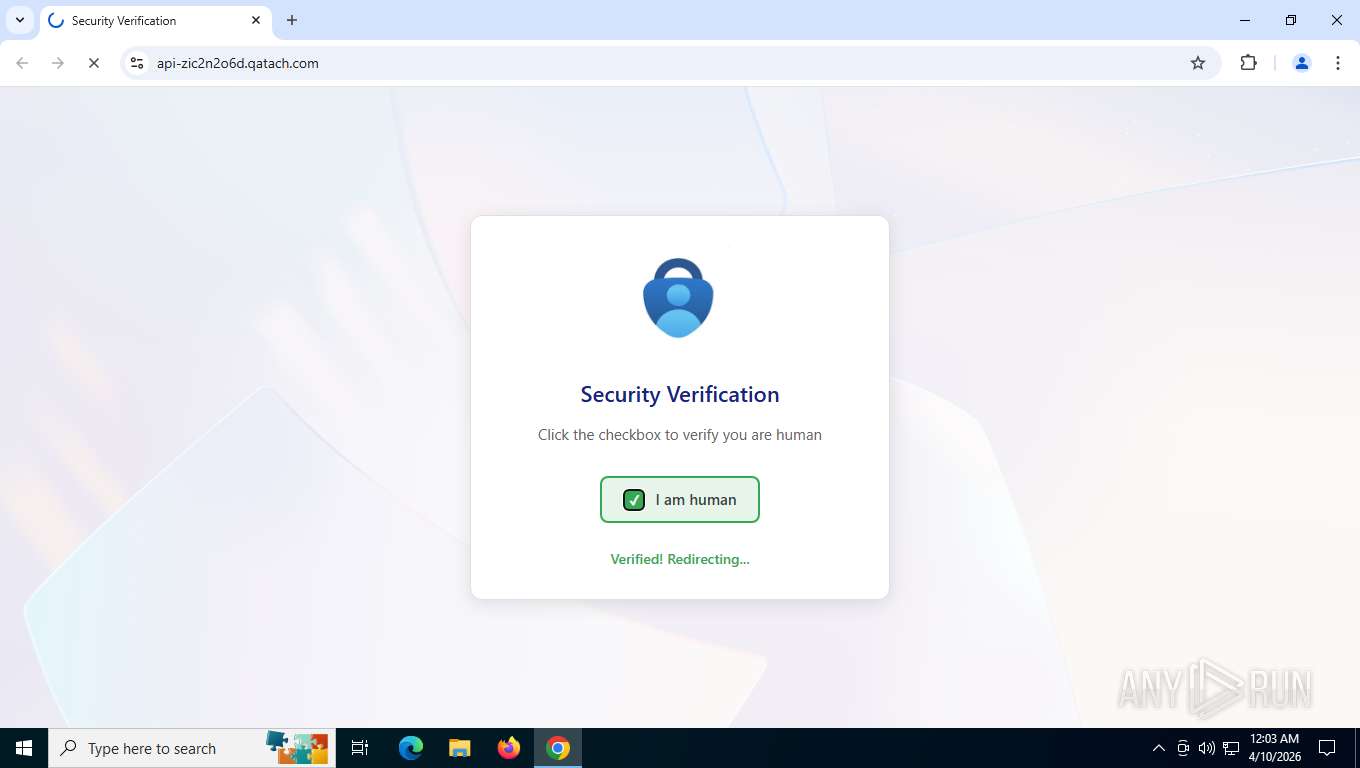
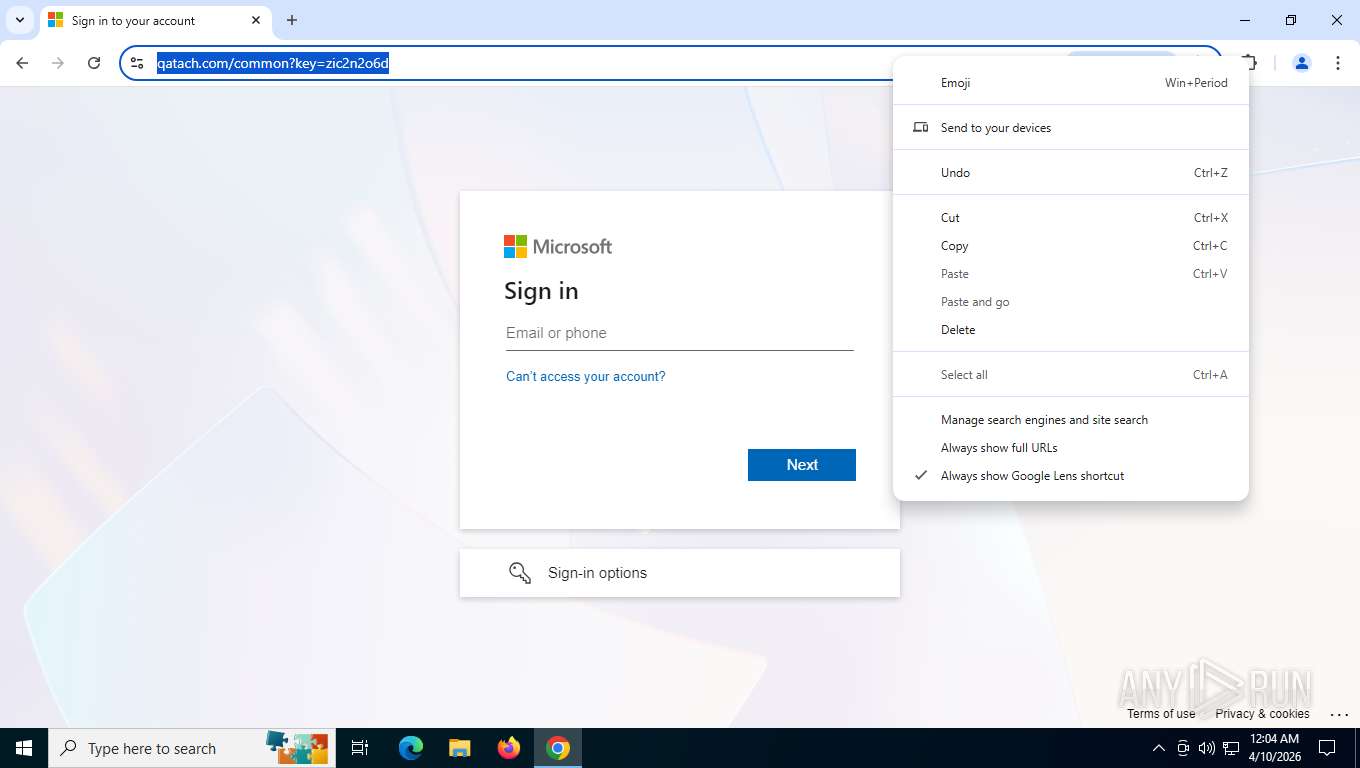
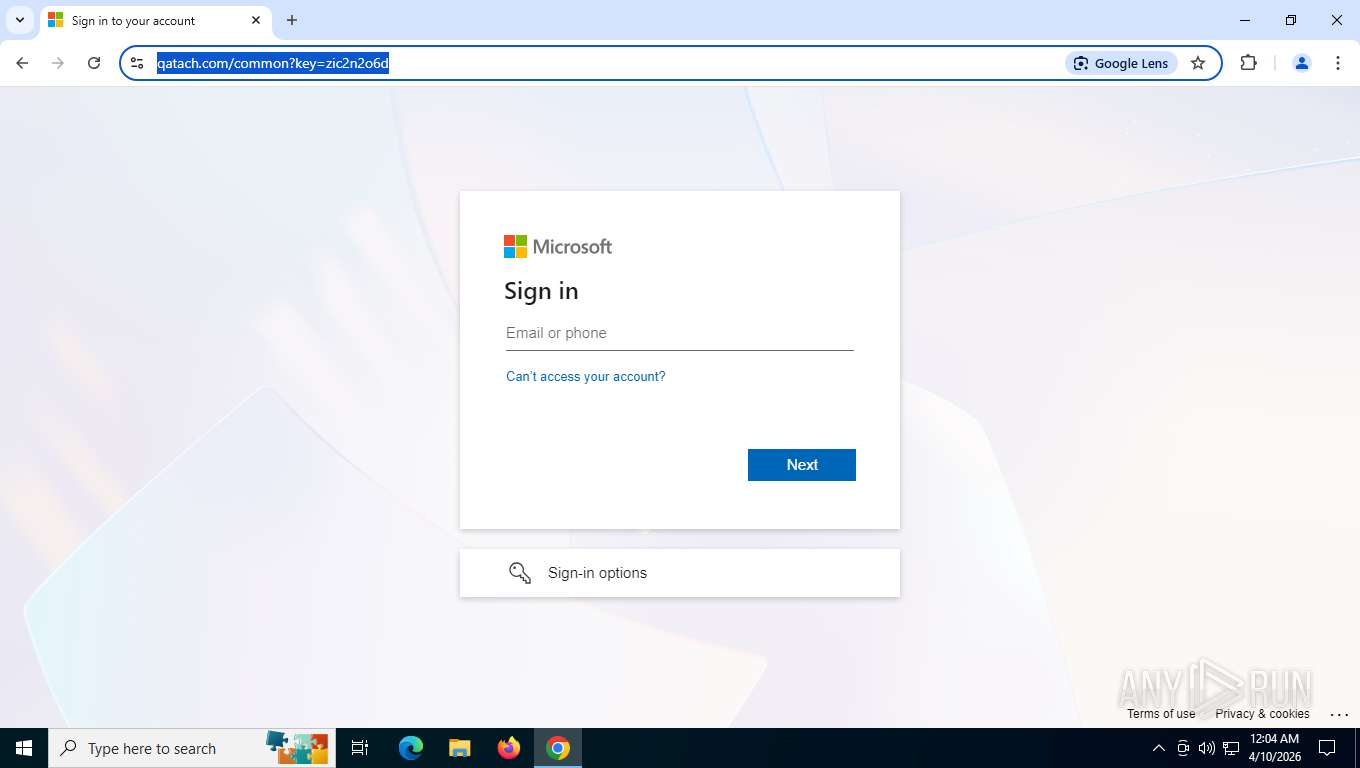
EvilProxy fake captcha has been detected
- chrome.exe (PID: 5384)
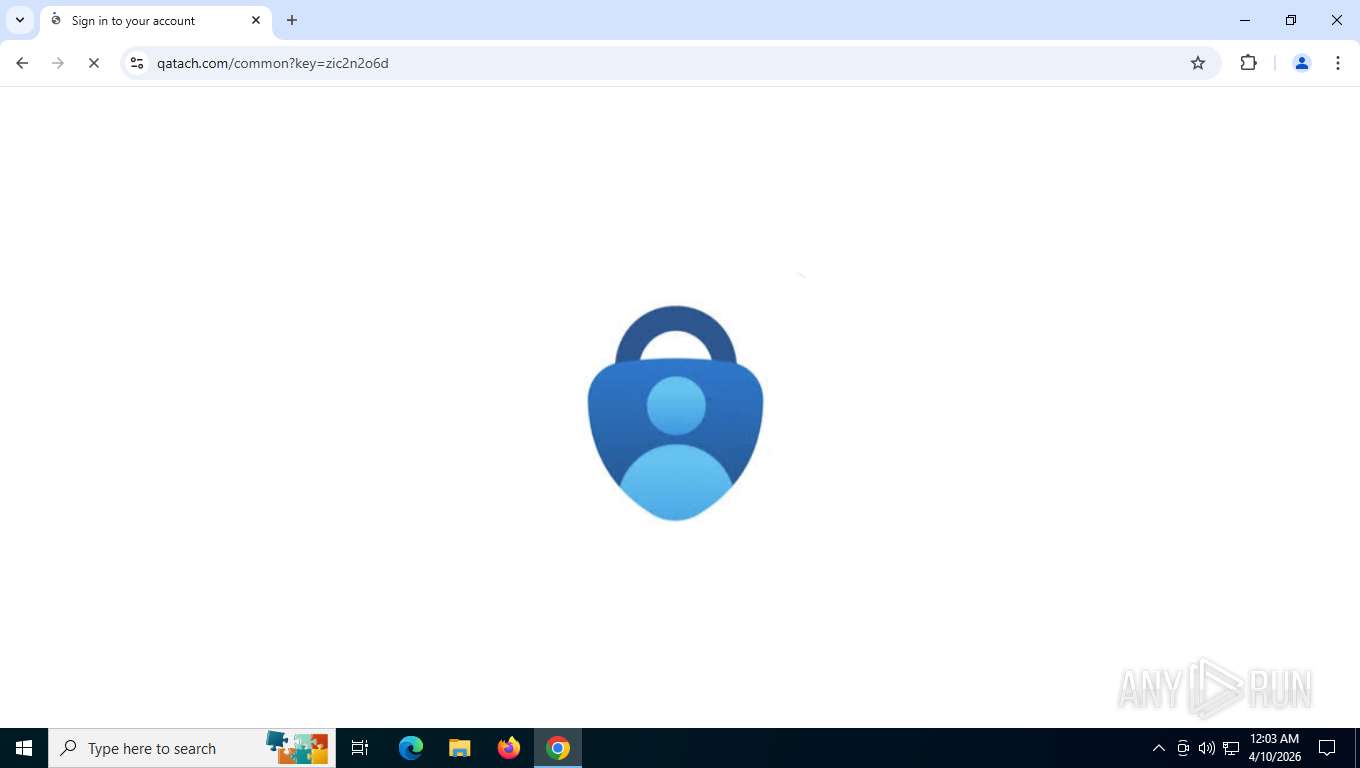
Fake Microsoft Authentication Page has been detected
- chrome.exe (PID: 5384)
MS auth config detected on a non-Microsoft site
- chrome.exe (PID: 5384)
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 7176)
SUSPICIOUS
No suspicious indicators.INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 7576)
Page contains obfuscated JavaScript
- chrome.exe (PID: 5384)
Application launched itself
- chrome.exe (PID: 5384)
The sample compiled with english language support
- chrome.exe (PID: 7576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
170
Monitored processes
34
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5496,i,6593168935585712670,613216543326514249,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5852 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=3540,i,6593168935585712670,613216543326514249,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=4740 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5824,i,6593168935585712670,613216543326514249,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5760 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5972,i,6593168935585712670,613216543326514249,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6092 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5524,i,6593168935585712670,613216543326514249,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5928 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5484,i,6593168935585712670,613216543326514249,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5832 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5604,i,6593168935585712670,613216543326514249,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5944 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffe234afff8,0x7ffe234b0004,0x7ffe234b0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5364,i,6593168935585712670,613216543326514249,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5920 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6052,i,6593168935585712670,613216543326514249,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5888 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
313
Text files
95
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFdff7f.TMP | — | |
MD5:— | SHA256:— | |||
| 5384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RFdff8e.TMP | — | |
MD5:— | SHA256:— | |||
| 5384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RFdff8e.TMP | — | |
MD5:— | SHA256:— | |||
| 5384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RFdff8e.TMP | — | |
MD5:— | SHA256:— | |||
| 5384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RFdff9e.TMP | — | |
MD5:— | SHA256:— | |||
| 5384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFdff9e.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
111
TCP/UDP connections
56
DNS requests
63
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7176 | chrome.exe | GET | 302 | 104.18.32.196:443 | https://2b5a9adf.click.kit-mail3.com/qdu7ekvownsdf727o84hlh8gknz83b4hm4mwm/wnh2hghq7l52m8h7/aHR0cHM6Ly9hcHAua2l0LmNvbS9mb3Jtcy9jb25maXJtP2tleT01YTgzZGQxYTA3YmM0MzFlYTRkOWU0NzA4N2Q5ZWRkNDY3YjU1MzE2JnNpZD0xMTIxODY3ODQ5NA== | US | — | — | unknown |
7176 | chrome.exe | GET | 302 | 172.64.149.80:443 | https://app.kit.com/forms/confirm?key=5a83dd1a07bc431ea4d9e47087d9edd467b55316&sid=11218678494 | US | — | — | unknown |
7176 | chrome.exe | GET | 200 | 172.67.219.37:443 | https://api-zic2n2o6d.qatach.com/favicon.ico | US | — | — | unknown |
7176 | chrome.exe | GET | 200 | 142.250.154.138:80 | http://clients2.google.com/time/1/current?cup2key=8:vuYuSt_KbhS_tWR11F9ZTGBJ02FCNKtfu3KkaGEXURc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 105 b | whitelisted |
7176 | chrome.exe | GET | 200 | 142.251.20.94:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=133 | US | compressed | 89.4 Kb | whitelisted |
7176 | chrome.exe | GET | 200 | 192.178.183.95:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | US | binary | 41 b | whitelisted |
7176 | chrome.exe | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | US | text | 17 b | whitelisted |
7176 | chrome.exe | GET | 200 | 172.67.219.37:443 | https://api-zic2n2o6d.qatach.com/ | US | html | 89.6 Kb | unknown |
7176 | chrome.exe | GET | 200 | 142.251.14.95:443 | https://content-autofill.googleapis.com/v1/pages/ChVDaHJvbWUvMTMzLjAuNjk0My4xMjcSGQkT6a3PSKhSshIFDfURvj0hrd6UcjwbYhQ=?alt=proto | US | text | 16 b | whitelisted |
7176 | chrome.exe | POST | 200 | 142.251.13.94:443 | https://update.googleapis.com/service/update2/json?cup2key=14:NRHfA8Mhuz0y5n3SqhrY9GhI-y7BycIb4BI6RHlfi9k&cup2hreq=6116ba49f5cae7afd9b0cc2fa72b931feaba408ec4d7b365eec948631e40b646 | US | text | 289 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4044 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7176 | chrome.exe | 142.251.20.94:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
7176 | chrome.exe | 104.18.32.196:443 | 2b5a9adf.click.kit-mail3.com | CLOUDFLARENET | US | whitelisted |
7176 | chrome.exe | 192.178.183.95:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7176 | chrome.exe | 142.250.154.138:80 | clients2.google.com | GOOGLE | US | whitelisted |
7176 | chrome.exe | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
2b5a9adf.click.kit-mail3.com |
| unknown |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| whitelisted |
app.kit.com |
| whitelisted |
api-zic2n2o6d.qatach.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4044 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7176 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
7176 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
7176 | chrome.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Fake Microsoft Sign-in domain chain (authisnotlogin) |
7176 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
7176 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
7176 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
7176 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
7176 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] EvilProxy related HTTP GET request observed |
7176 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |