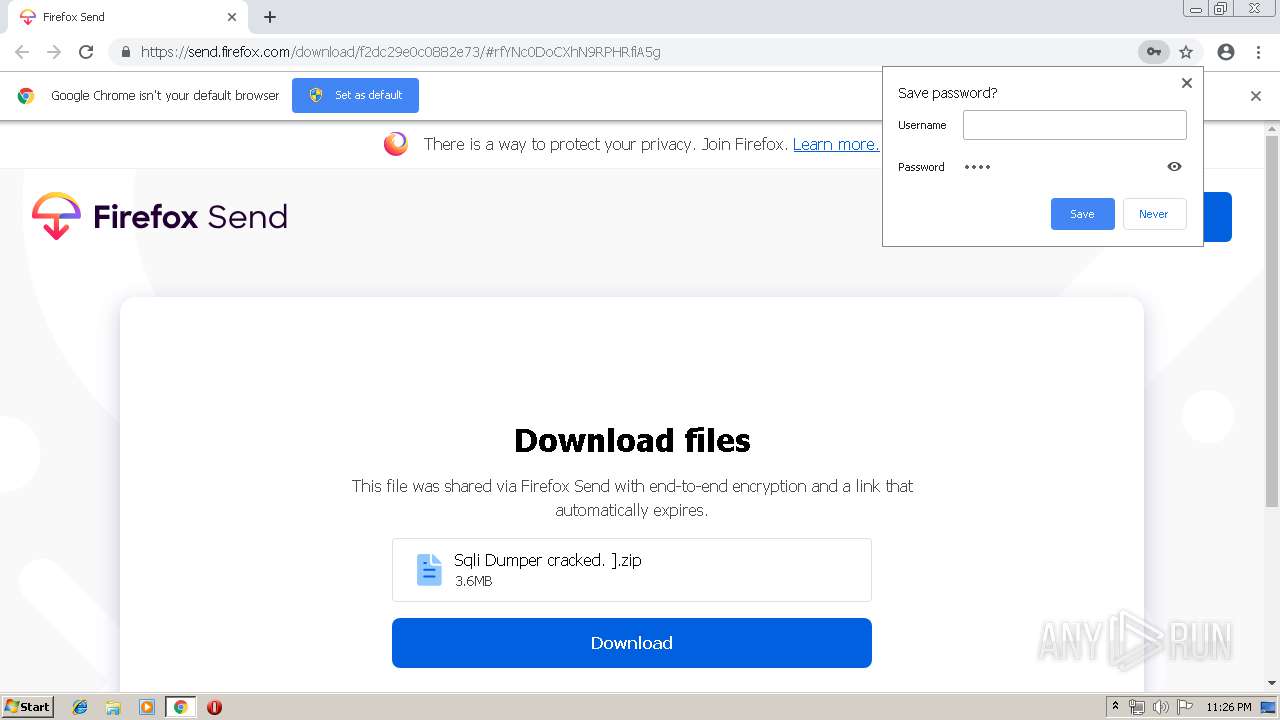
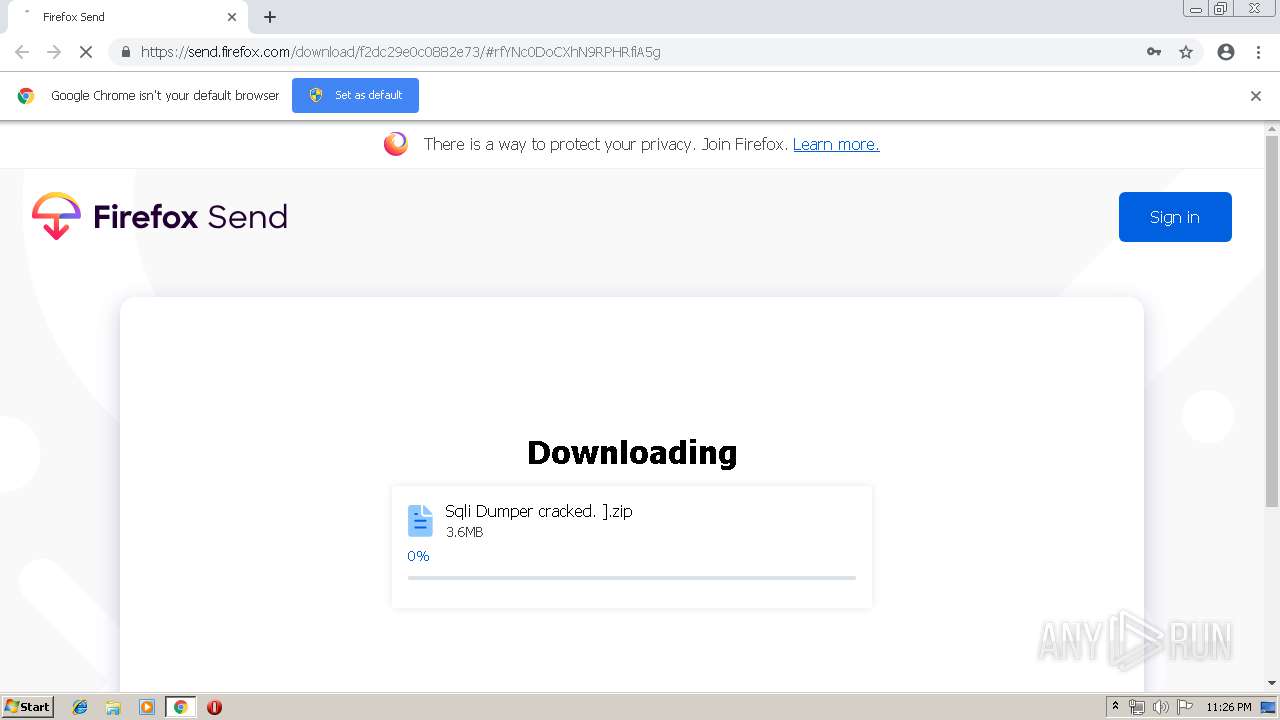
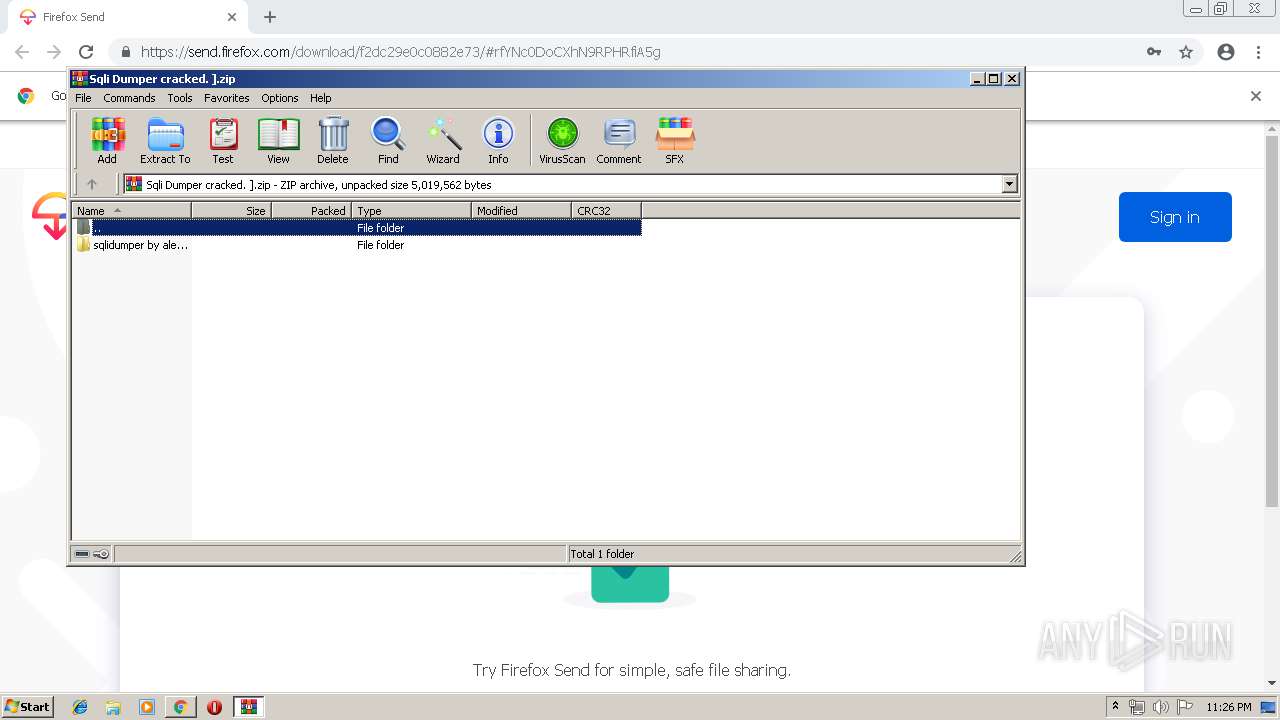
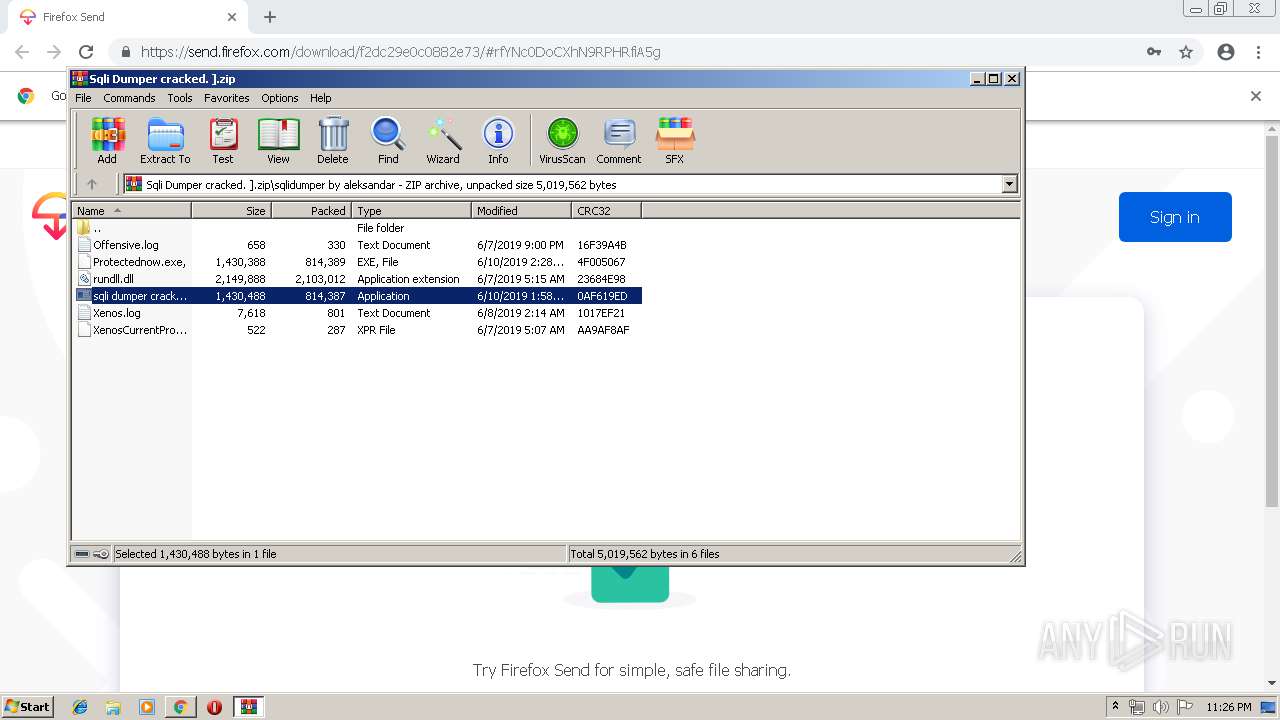
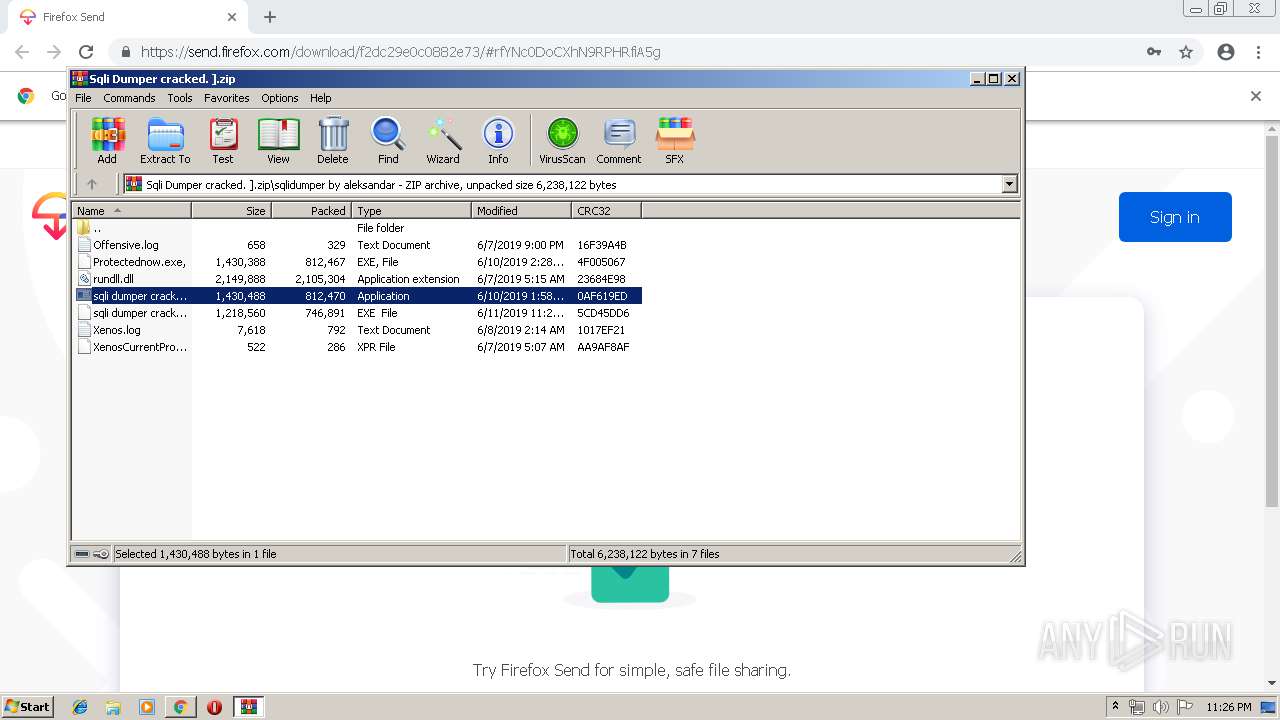
| URL: | https://send.firefox.com/download/f2dc29e0c0882e73/#rfYNc0DoCXhN9RPHRfiA5g |
| Full analysis: | https://app.any.run/tasks/fe7ff920-7519-4fc8-9b59-12be69ba83ce |
| Verdict: | Malicious activity |
| Threats: | NanoCore is a Remote Access Trojan or RAT. This malware is highly customizable with plugins which allow attackers to tailor its functionality to their needs. Nanocore is created with the .NET framework and it’s available for purchase for just $25 from its “official” website. |
| Analysis date: | June 11, 2019, 22:25:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E20F4B51E2E1E5B10AEC196F2A9B527F |
| SHA1: | 68A2F82DF042E286EDC4FD31DC3776C405C997D2 |
| SHA256: | D2E8C87CD8D6F7F18C7CE85B3780076D0F3EB6A7C41B28BE3F2326740B32226B |
| SSDEEP: | 3:N8NlazKLMimeifMFxQC:2famwim4 |
MALICIOUS
Changes the autorun value in the registry
- sqli dumper cracked.exe (PID: 876)
- l7EkgSQJSvyC.exe (PID: 1804)
Application was dropped or rewritten from another process
- sqli dumper cracked.exe (PID: 3204)
- icsys.icn.exe (PID: 3172)
- sqli dumper cracked.exe (PID: 876)
- l7EkgSQJSvyC.exe (PID: 1804)
Connects to CnC server
- RegAsm.exe (PID: 644)
QUASAR was detected
- RegAsm.exe (PID: 644)
- l7EkgSQJSvyC.exe (PID: 1804)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 644)
Drops/Copies Quasar RAT executable
- RegAsm.exe (PID: 644)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2152)
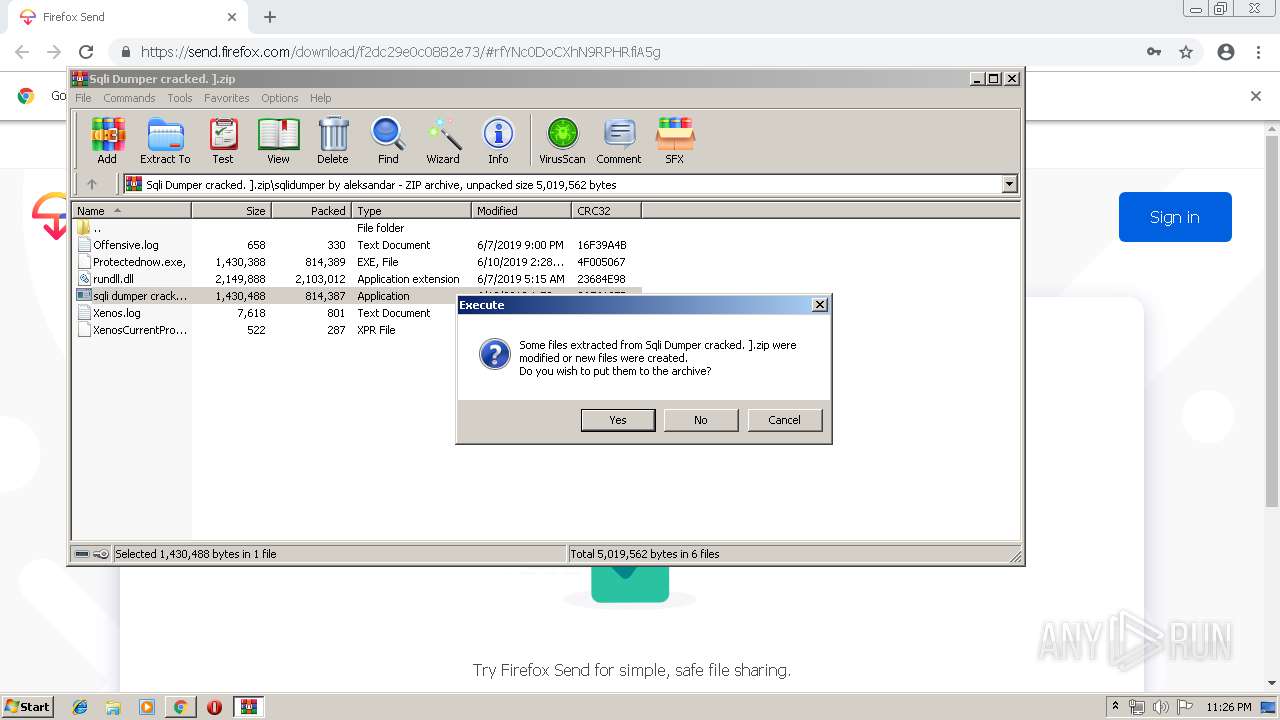
Executable content was dropped or overwritten
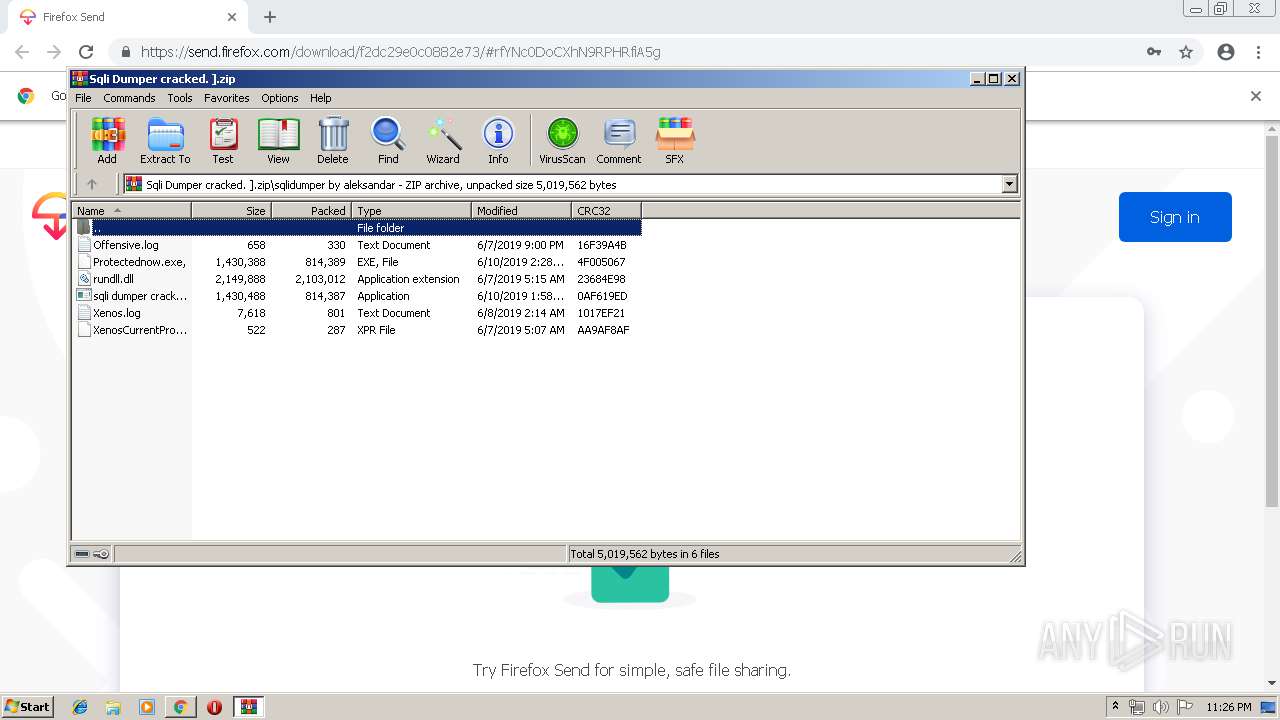
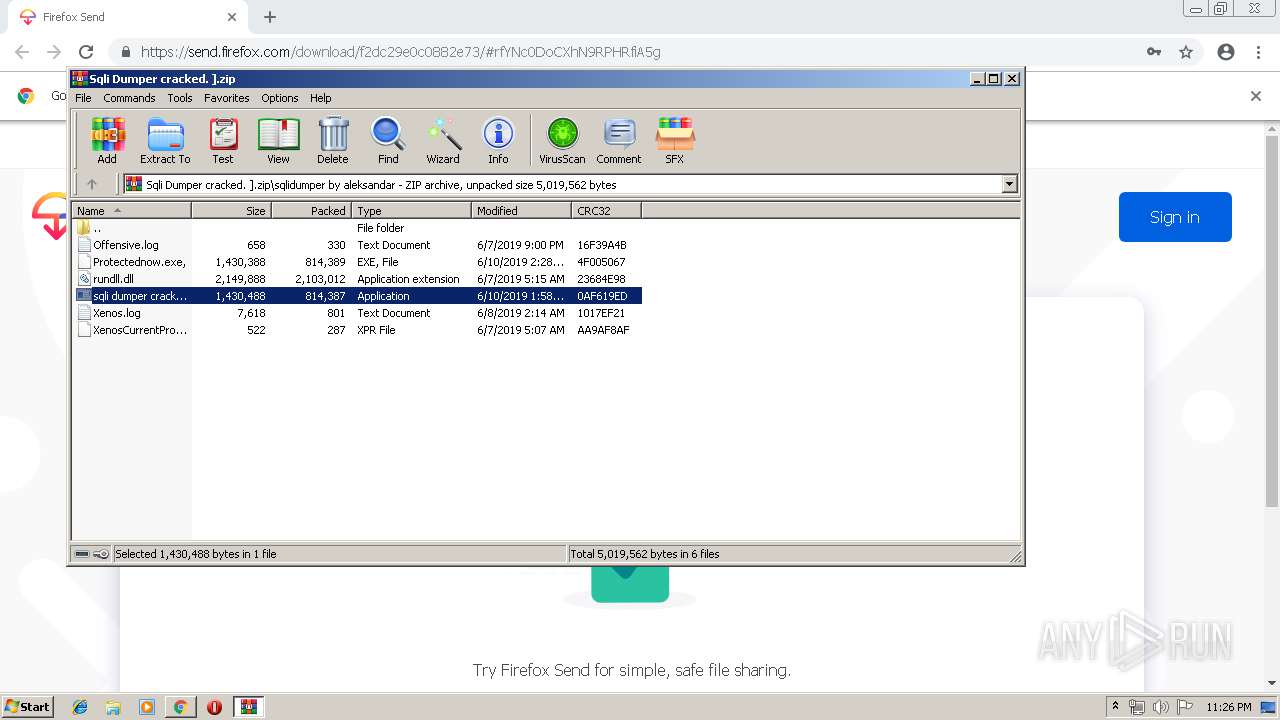
- WinRAR.exe (PID: 2776)
- sqli dumper cracked.exe (PID: 3204)
- sqli dumper cracked.exe (PID: 876)
- RegAsm.exe (PID: 644)
Starts itself from another location
- sqli dumper cracked.exe (PID: 3204)
Starts application with an unusual extension
- sqli dumper cracked.exe (PID: 3204)
Creates files in the user directory
- sqli dumper cracked.exe (PID: 876)
- l7EkgSQJSvyC.exe (PID: 1804)
Checks for external IP
- RegAsm.exe (PID: 644)
- l7EkgSQJSvyC.exe (PID: 1804)
Loads DLL from Mozilla Firefox
- RegAsm.exe (PID: 644)
INFO
Application launched itself
- chrome.exe (PID: 2152)
Reads settings of System Certificates
- chrome.exe (PID: 2152)
Reads Internet Cache Settings
- chrome.exe (PID: 2152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
27
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5627207915868008733 --mojo-platform-channel-handle=4300 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 644 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | sqli dumper cracked.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13328800731491488575 --mojo-platform-channel-handle=3848 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 876 | "c:\users\admin\appdata\local\temp\rar$exa2776.47755\sqlidumper by aleksandar\sqli dumper cracked.exe " | c:\users\admin\appdata\local\temp\rar$exa2776.47755\sqlidumper by aleksandar\sqli dumper cracked.exe | sqli dumper cracked.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11459077567841807805 --mojo-platform-channel-handle=4000 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1804 | "C:\Users\admin\AppData\Local\Temp\l7EkgSQJSvyC.exe" | C:\Users\admin\AppData\Local\Temp\l7EkgSQJSvyC.exe | RegAsm.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.3.0.0 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2160 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://send.firefox.com/download/f2dc29e0c0882e73/#rfYNc0DoCXhN9RPHRfiA5g | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=15540309883557182829 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15540309883557182829 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1956 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=66203899630775436 --mojo-platform-channel-handle=968 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 609
Read events
1 452
Write events
152
Delete events
5
Modification events
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2152-13204765532261750 |
Value: 259 | |||
Executable files
7
Suspicious files
77
Text files
190
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f1e9678e-3650-4a78-a7ee-38a5bc9caa9c.tmp | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
22
DNS requests
15
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
644 | RegAsm.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 323 b | malicious |
2152 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 506 b | whitelisted |
2152 | chrome.exe | GET | 200 | 173.194.5.40:80 | http://r3---sn-aigzrn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=130.185.144.231&mm=28&mn=sn-aigzrn7e&ms=nvh&mt=1560290658&mv=u&pl=22&shardbypass=yes | US | crx | 842 Kb | whitelisted |
1804 | l7EkgSQJSvyC.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 323 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2152 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 35.186.224.242:443 | send.firefox.com | Google Inc. | US | suspicious |
2152 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 172.217.21.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 172.217.22.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 216.58.207.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2152 | chrome.exe | 172.217.21.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
644 | RegAsm.exe | 162.159.135.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
— | — | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
send.firefox.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-aigzrn7e.gvt1.com |
| whitelisted |
www.google.com |
| malicious |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
644 | RegAsm.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
644 | RegAsm.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
644 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar 1.3 RAT IP Lookup ip-api.com (HTTP headeer) |
644 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar RAT |
644 | RegAsm.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 64B |
1804 | l7EkgSQJSvyC.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
1804 | l7EkgSQJSvyC.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
1804 | l7EkgSQJSvyC.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar 1.3 RAT IP Lookup ip-api.com (HTTP headeer) |
1804 | l7EkgSQJSvyC.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar RAT |
2 ETPRO signatures available at the full report