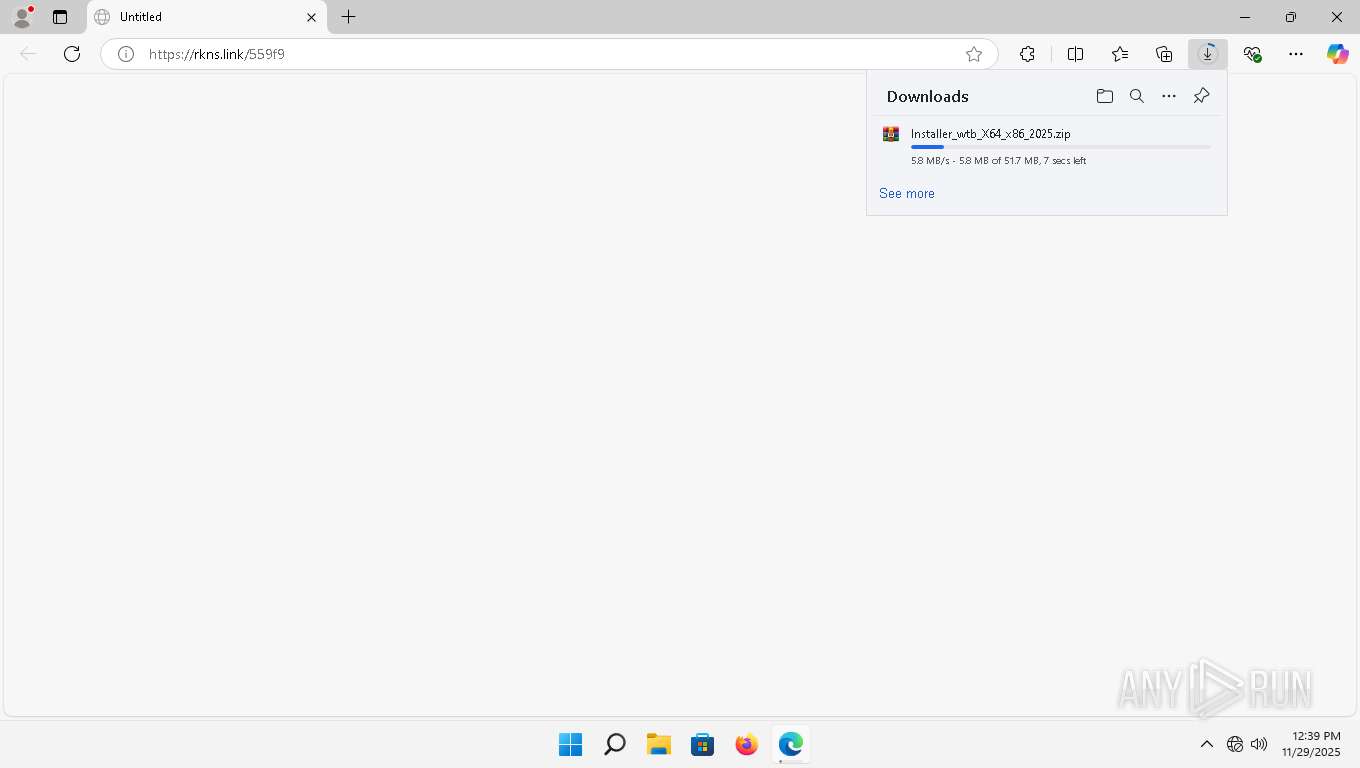
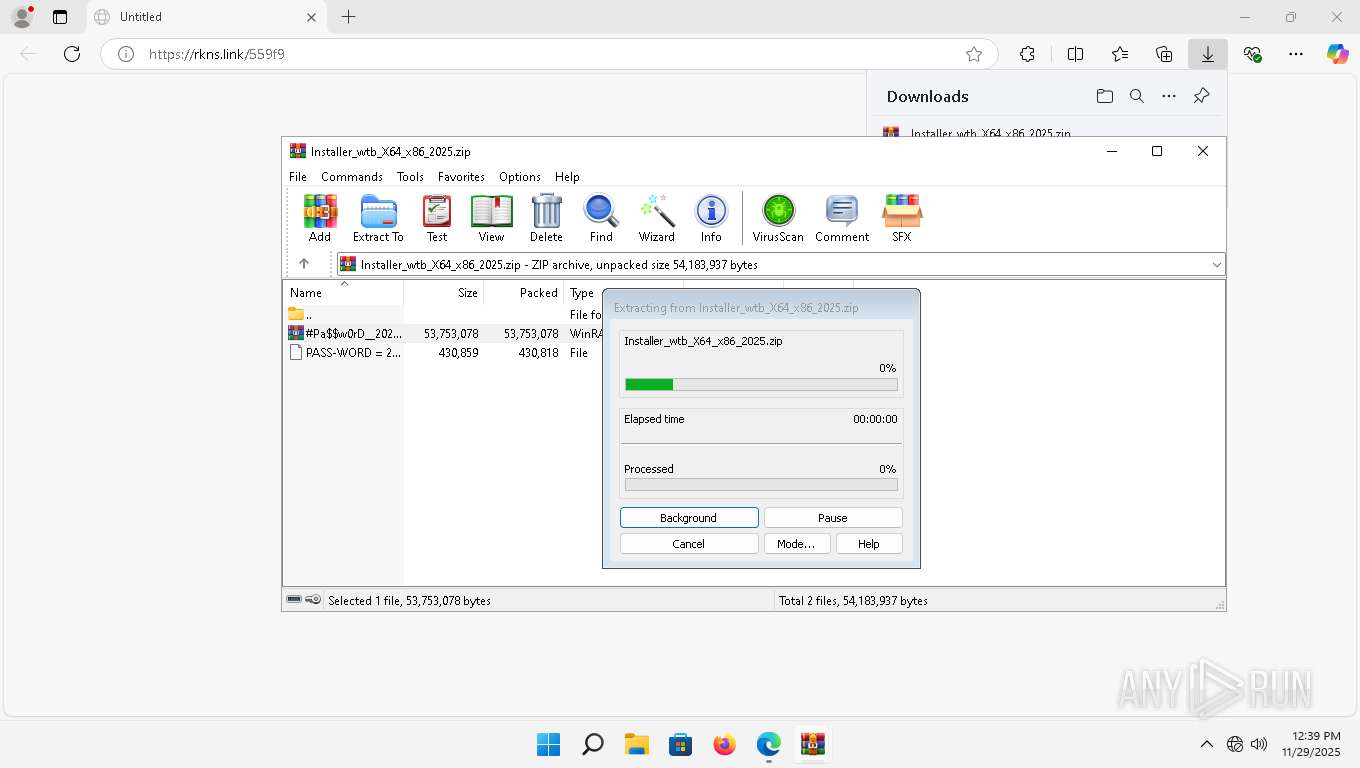
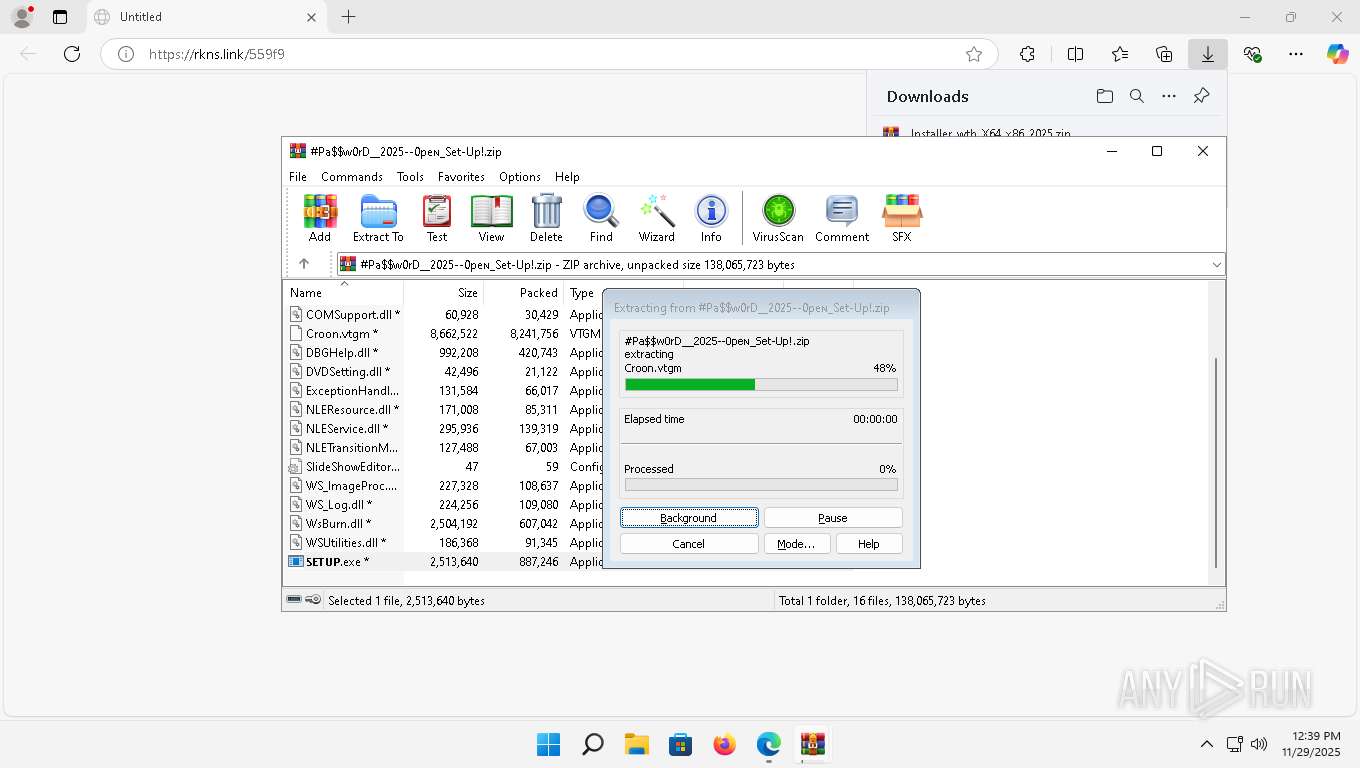
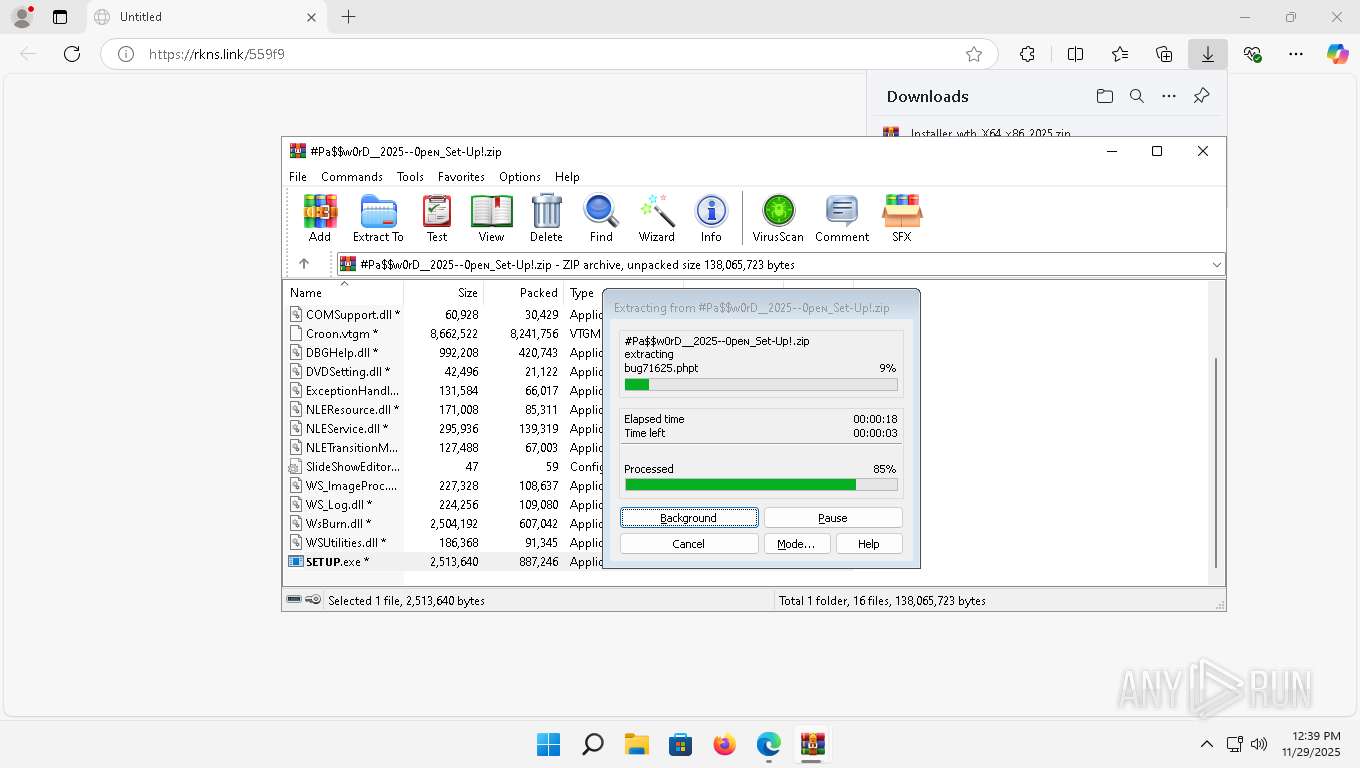
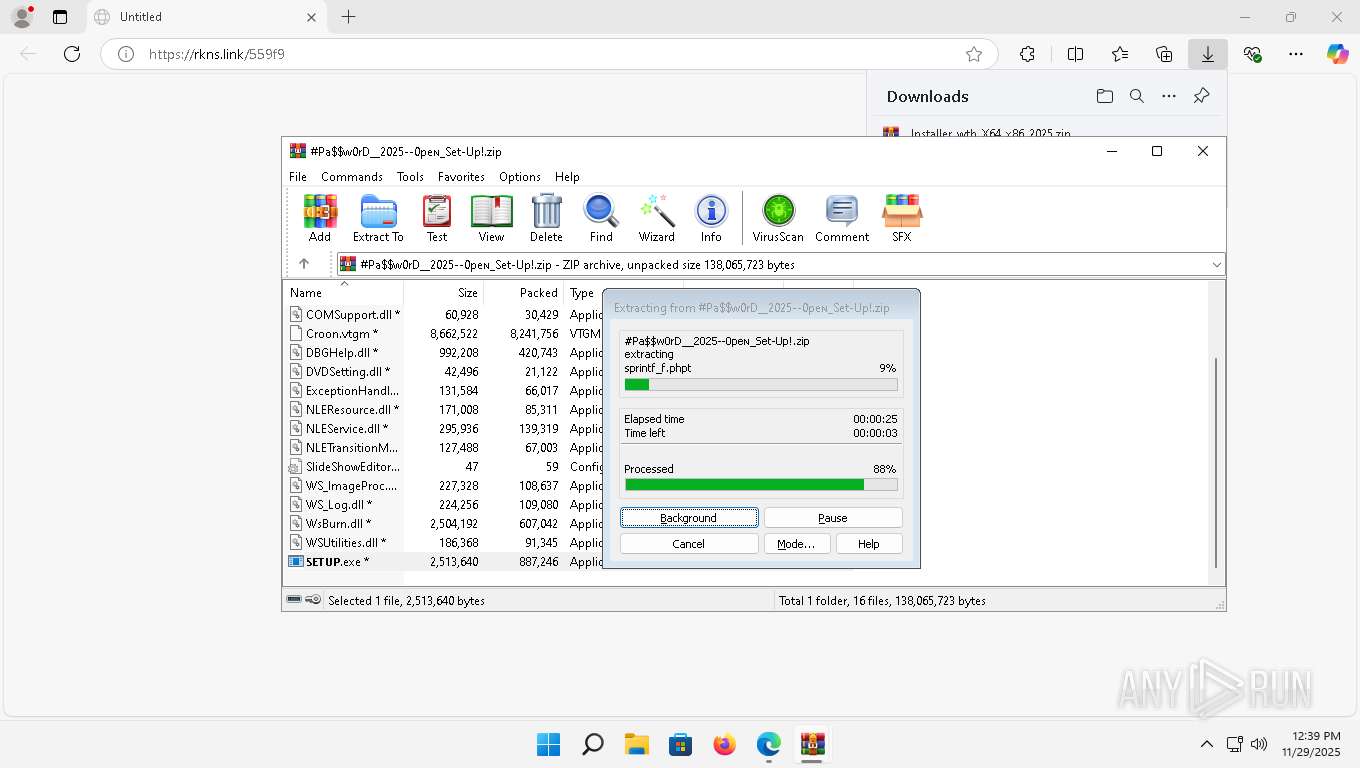
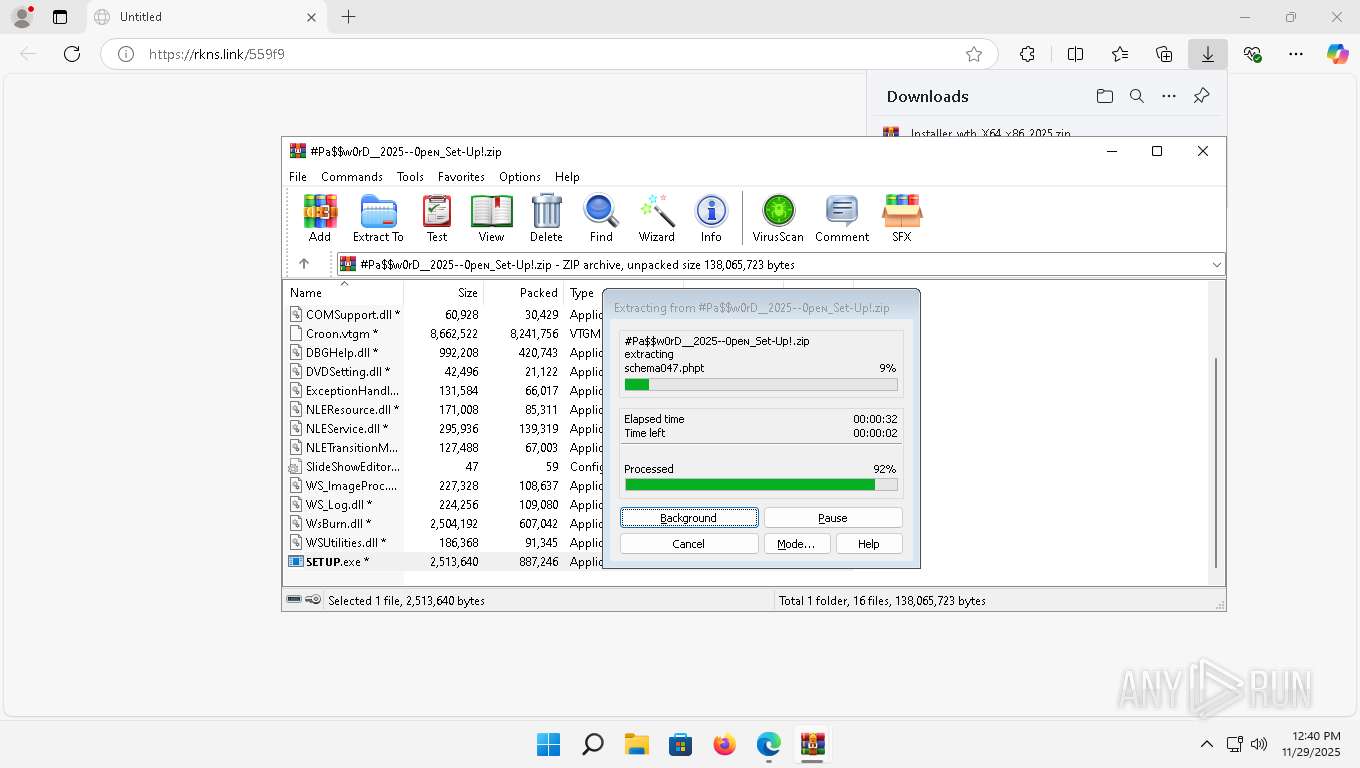
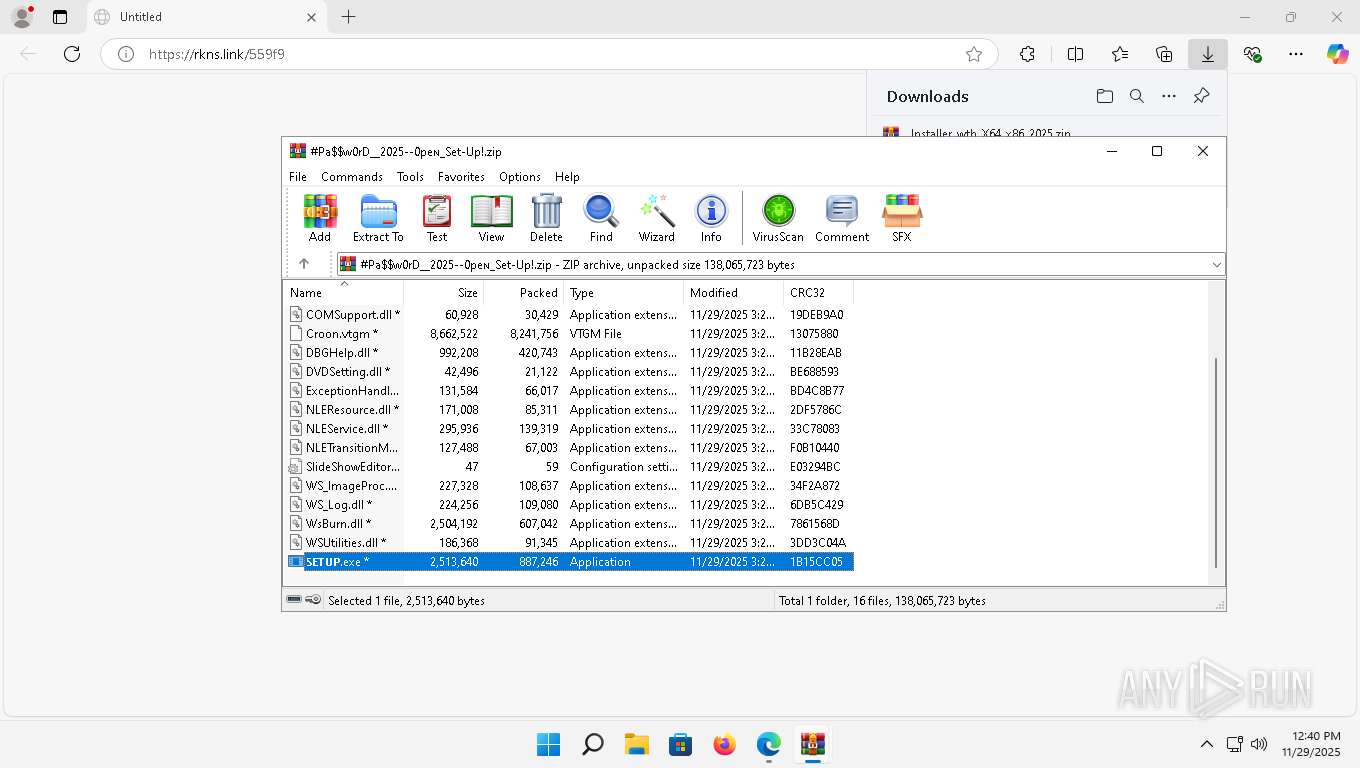
| URL: | https://rkns.link/559f9 |
| Full analysis: | https://app.any.run/tasks/84a917e6-2c6f-40f2-8f9e-fded0d4c174f |
| Verdict: | Malicious activity |
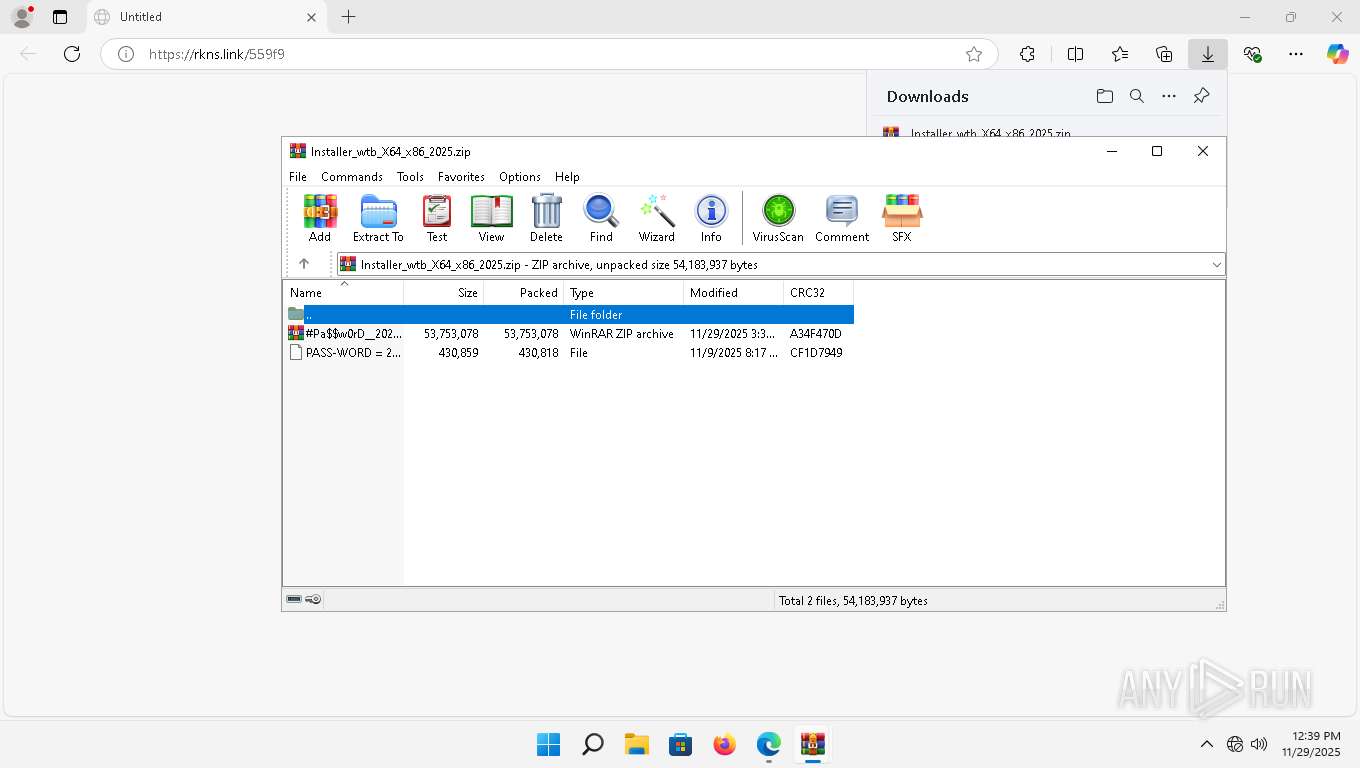
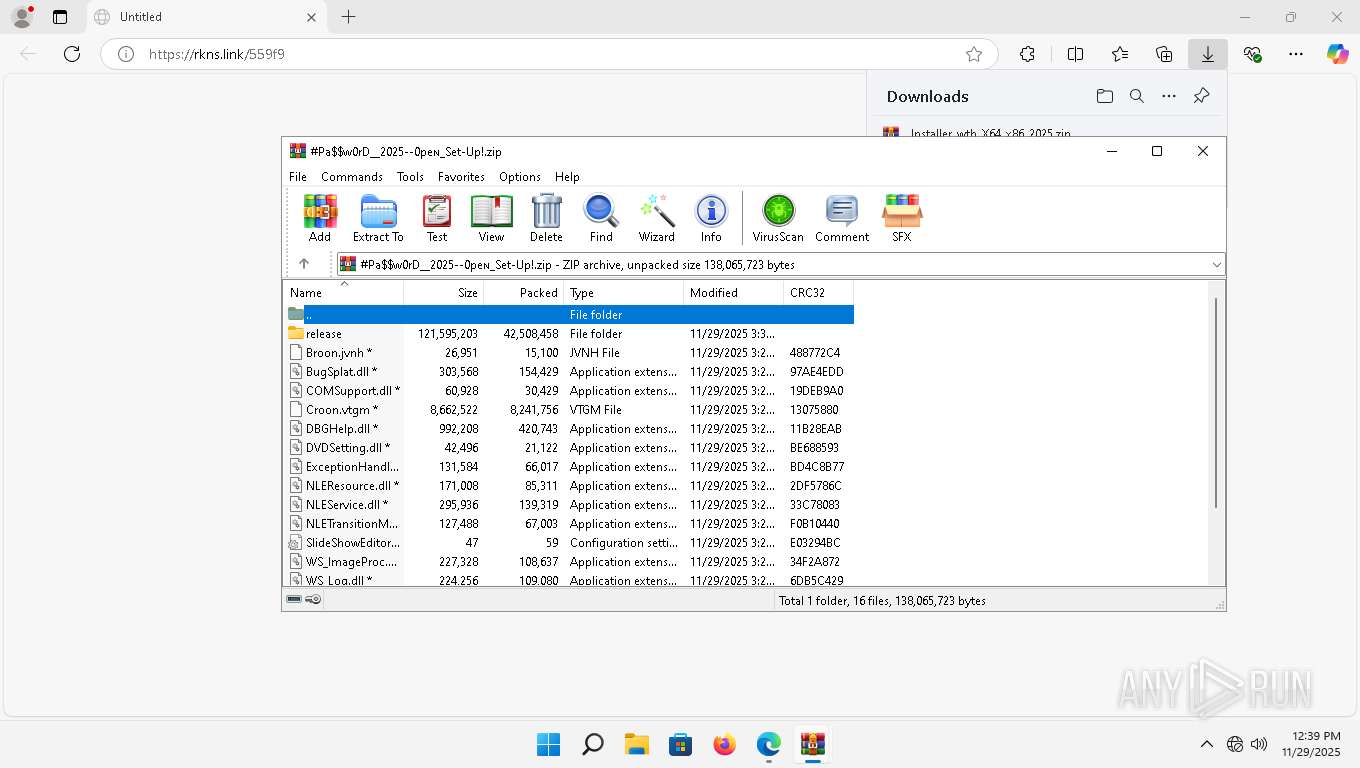
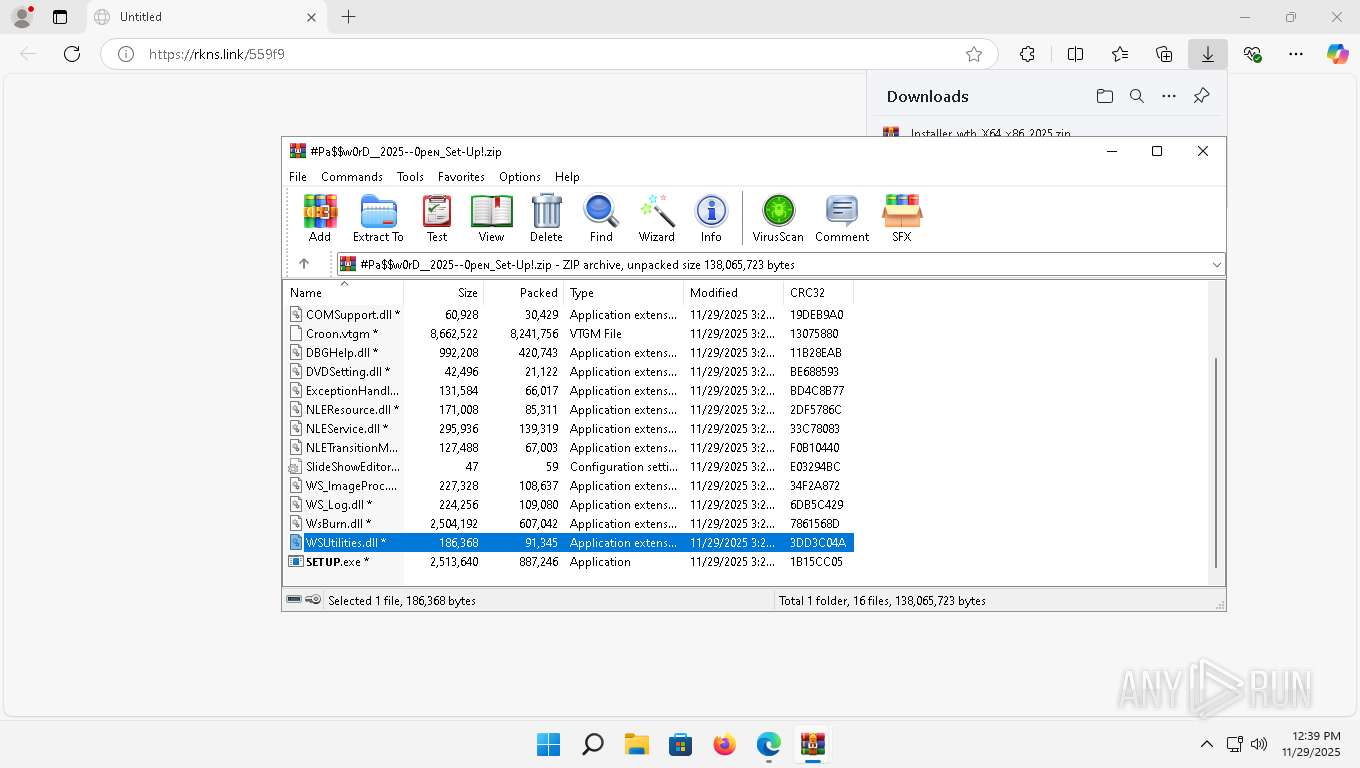
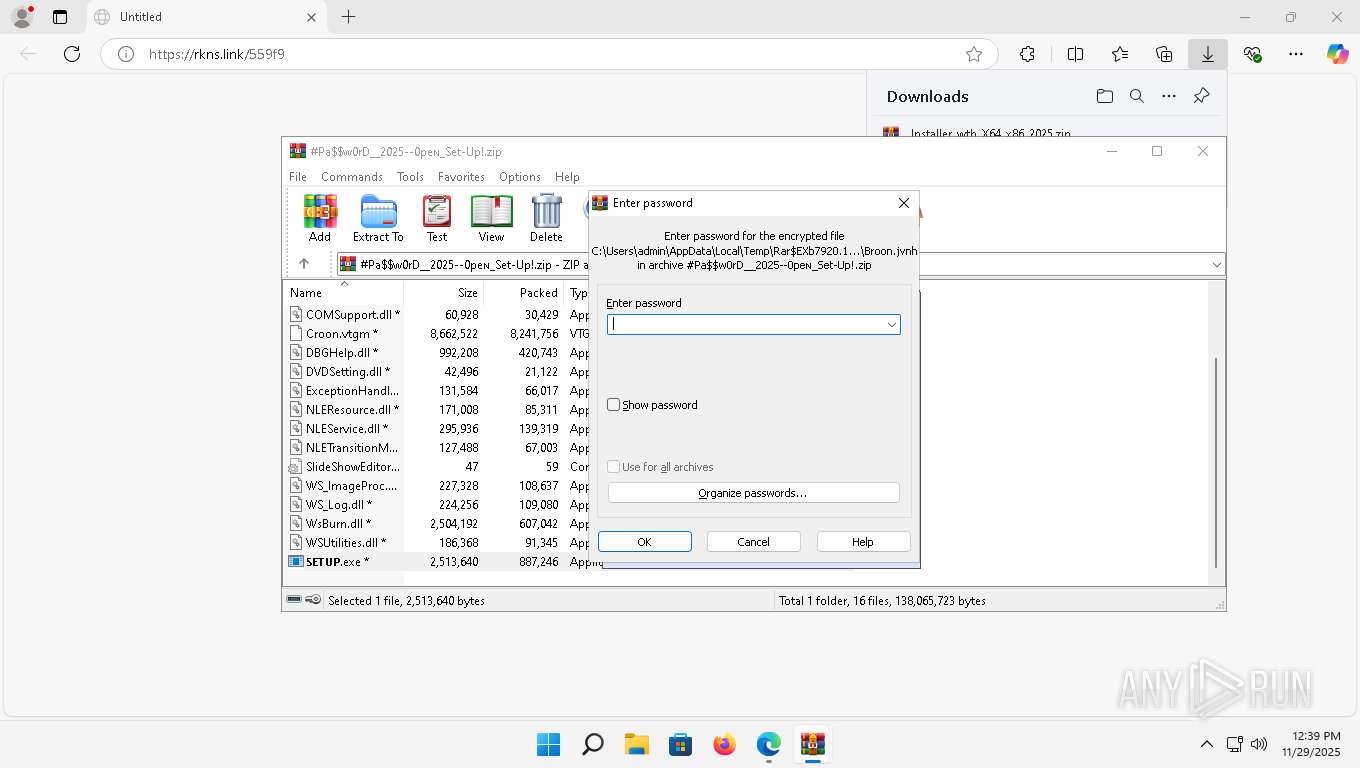
| Threats: | HijackLoader is a modular malware acting as a vehicle for distributing different types of malicious software on compromised systems. It gained prominence during the summer of 2023 and has since been used in multiple attacks against organizations from various sectors, including hospitality businesses. |
| Analysis date: | November 29, 2025, 12:39:08 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FA2029EDA49E3110F955860B22A73C09 |
| SHA1: | 06299A368636D6F29665F47A645A7C364B5292E9 |
| SHA256: | D21AFDCA72149BF625A2F433A4EC70FA50A86DF003C386DABAB483C37F0F0D13 |
| SSDEEP: | 3:N8exhFP:2ghl |
MALICIOUS
HIJACKLOADER has been detected (YARA)
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
- Injector_Advanc16.exe (PID: 648)
- PhotEngine86.exe (PID: 508)
- MForge32.exe (PID: 7708)
XORed URL has been found (YARA)
- PhotEngine86.exe (PID: 508)
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 8140)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 6080)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 2560)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7928)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8140)
- WinRAR.exe (PID: 7920)
- PhotEngine86.exe (PID: 508)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7920)
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
The process drops Mozilla's DLL files
- WinRAR.exe (PID: 7920)
Starts itself from another location
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
There is functionality for taking screenshot (YARA)
- Injector_Advanc16.exe (PID: 648)
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
Executable content was dropped or overwritten
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
- Injector_Advanc16.exe (PID: 648)
Executing commands from a ".bat" file
- Injector_Advanc16.exe (PID: 648)
- cmd.exe (PID: 6080)
- cmd.exe (PID: 708)
- cmd.exe (PID: 7700)
- powershell.exe (PID: 740)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 7360)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6080)
- cmd.exe (PID: 708)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 7700)
- Injector_Advanc16.exe (PID: 648)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 2560)
- powershell.exe (PID: 740)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7928)
Starts SC.EXE for service management
- cmd.exe (PID: 7700)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 7360)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7700)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 7360)
Windows service management via SC.EXE
- sc.exe (PID: 8000)
- sc.exe (PID: 8048)
- sc.exe (PID: 2988)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7700)
- cmd.exe (PID: 8108)
- cmd.exe (PID: 5484)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7700)
- cmd.exe (PID: 8108)
- cmd.exe (PID: 5484)
Reads the Internet Settings
- powershell.exe (PID: 740)
- PhotEngine86.exe (PID: 508)
Hides command output
- cmd.exe (PID: 8108)
- cmd.exe (PID: 5484)
Executes script without checking the security policy
- powershell.exe (PID: 8148)
- powershell.exe (PID: 740)
- powershell.exe (PID: 740)
Converts TXT file into a string
- powershell.exe (PID: 8148)
- powershell.exe (PID: 740)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2568)
Queries Computer System Information (Win32_ComputerSystem) (SCRIPT)
- powershell.exe (PID: 8148)
- powershell.exe (PID: 740)
Reads settings of System Certificates
- PhotEngine86.exe (PID: 508)
INFO
Checks supported languages
- identity_helper.exe (PID: 7648)
- Injector_Advanc16.exe (PID: 648)
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
- mode.com (PID: 6524)
- mode.com (PID: 1108)
- PhotEngine86.exe (PID: 508)
- Chime.exe (PID: 2624)
- MForge32.exe (PID: 7708)
- Chime.exe (PID: 1688)
Application launched itself
- msedge.exe (PID: 5348)
Reads the computer name
- identity_helper.exe (PID: 7648)
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
- Injector_Advanc16.exe (PID: 648)
- PhotEngine86.exe (PID: 508)
- Chime.exe (PID: 2624)
- MForge32.exe (PID: 7708)
- Chime.exe (PID: 1688)
Reads Environment values
- identity_helper.exe (PID: 7648)
The sample compiled with chinese language support
- WinRAR.exe (PID: 7920)
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7920)
The sample compiled with english language support
- WinRAR.exe (PID: 7920)
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
- Injector_Advanc16.exe (PID: 648)
The sample compiled with russian language support
- WinRAR.exe (PID: 7920)
Compiled with Borland Delphi (YARA)
- Injector_Advanc16.exe (PID: 648)
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
- PhotEngine86.exe (PID: 508)
Create files in a temporary directory
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
- Injector_Advanc16.exe (PID: 648)
- Chime.exe (PID: 1688)
Creates files in the program directory
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
- PhotEngine86.exe (PID: 508)
- Injector_Advanc16.exe (PID: 648)
Creates files or folders in the user directory
- 𝗦𝗘𝗧𝗨𝗣.exe (PID: 5248)
- Injector_Advanc16.exe (PID: 648)
- PhotEngine86.exe (PID: 508)
Checks operating system version
- cmd.exe (PID: 7700)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 7360)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 8148)
- powershell.exe (PID: 740)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8148)
- powershell.exe (PID: 740)
Starts MODE.COM to configure console settings
- mode.com (PID: 6524)
- mode.com (PID: 1108)
Checks proxy server information
- PhotEngine86.exe (PID: 508)
Reads the machine GUID from the registry
- PhotEngine86.exe (PID: 508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
249
Monitored processes
123
Malicious processes
12
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | reg add HKCU\Console /v QuickEdit /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 508 | C:\Users\admin\AppData\Local\Temp\PhotEngine86.exe | C:\Users\admin\AppData\Local\Temp\PhotEngine86.exe | 𝗦𝗘𝗧𝗨𝗣.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 360 Total Security Version: 2, 0, 0, 1123 Modules
| |||||||||||||||
| 648 | C:\Users\admin\AppData\Roaming\ms_orchestrator_net45_lts%APPDATA%\FZWDTYQIIMYHXEZMTFC\Injector_Advanc16.exe | C:\Users\admin\AppData\Roaming\ms_orchestrator_net45_lts%APPDATA%\FZWDTYQIIMYHXEZMTFC\Injector_Advanc16.exe | 𝗦𝗘𝗧𝗨𝗣.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.11 Modules
| |||||||||||||||
| 656 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 708 | C:\Windows\system32\cmd.exe /K "C:\Users\admin\AppData\Roaming\SAZlogger_gateway_rel\OOPWRBYQGAYASEAPOVD\123.bat" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3532,i,11141704448108961246,3391352342051060953,262144 --variations-seed-version --mojo-platform-channel-handle=3336 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 740 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c "start cmd.exe -arg '/c \""""C:\Users\admin\AppData\Roaming\SAZlogger_gateway_rel\OOPWRBYQGAYASEAPOVD\123.bat""" -el \"' -verb runas" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 740 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c "if ($PSVersionTable.PSEdition -ne 'Core') {$f=[System.IO.File]::ReadAllText('C:\Users\admin\AppData\Roaming\SAZlogger_gateway_rel\OOPWRBYQGAYASEAPOVD\123.bat') -split ':pstst';. ([scriptblock]::Create($f[1]))}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 756 | ping -n 1 updatecheck38.activated.win | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 846
Read events
25 773
Write events
73
Delete events
0
Modification events
| (PID) Process: | (8140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (8140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (8096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Installer_wtb_X64_x86_2025.zip | |||
| (PID) Process: | (8140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Installer_wtb_X64_x86_2025.zip | |||
| (PID) Process: | (8140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
228
Suspicious files
329
Text files
872
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\ClientCertificates\LOG.old~RF1a6591.TMP | — | |
MD5:— | SHA256:— | |||
| 5348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\parcel_tracking_db\LOG.old~RF1a65a1.TMP | — | |
MD5:— | SHA256:— | |||
| 5348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\LOG.old~RF1a65b0.TMP | — | |
MD5:— | SHA256:— | |||
| 5348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\discounts_db\LOG.old~RF1a65a1.TMP | — | |
MD5:— | SHA256:— | |||
| 5348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\PersistentOriginTrials\LOG.old~RF1a65b0.TMP | — | |
MD5:— | SHA256:— | |||
| 5348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
127
DNS requests
73
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7336 | MoUsoCoreWorker.exe | GET | 304 | 185.160.60.100:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c9c0bf2d4e35d72e | unknown | — | — | whitelisted |
7052 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5528 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:xFENBiZwULllLr4cvZmUNFPU2qdK3mKIbcVDV9ZjTZc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2424 | firefox.exe | POST | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
7052 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6508 | svchost.exe | POST | 403 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
6508 | svchost.exe | POST | 403 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
6508 | svchost.exe | POST | 403 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
6508 | svchost.exe | POST | 403 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
6508 | svchost.exe | POST | 403 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5264 | rundll32.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
3740 | SDXHelper.exe | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1000 | SDXHelper.exe | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
508 | OfficeC2RClient.exe | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3152 | pingsender.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
2424 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
2424 | firefox.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1420 | svchost.exe | 2.23.154.26:80 | — | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
e3913.cd.akamaiedge.net |
| whitelisted |
google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
rkns.link |
| malicious |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1420 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |