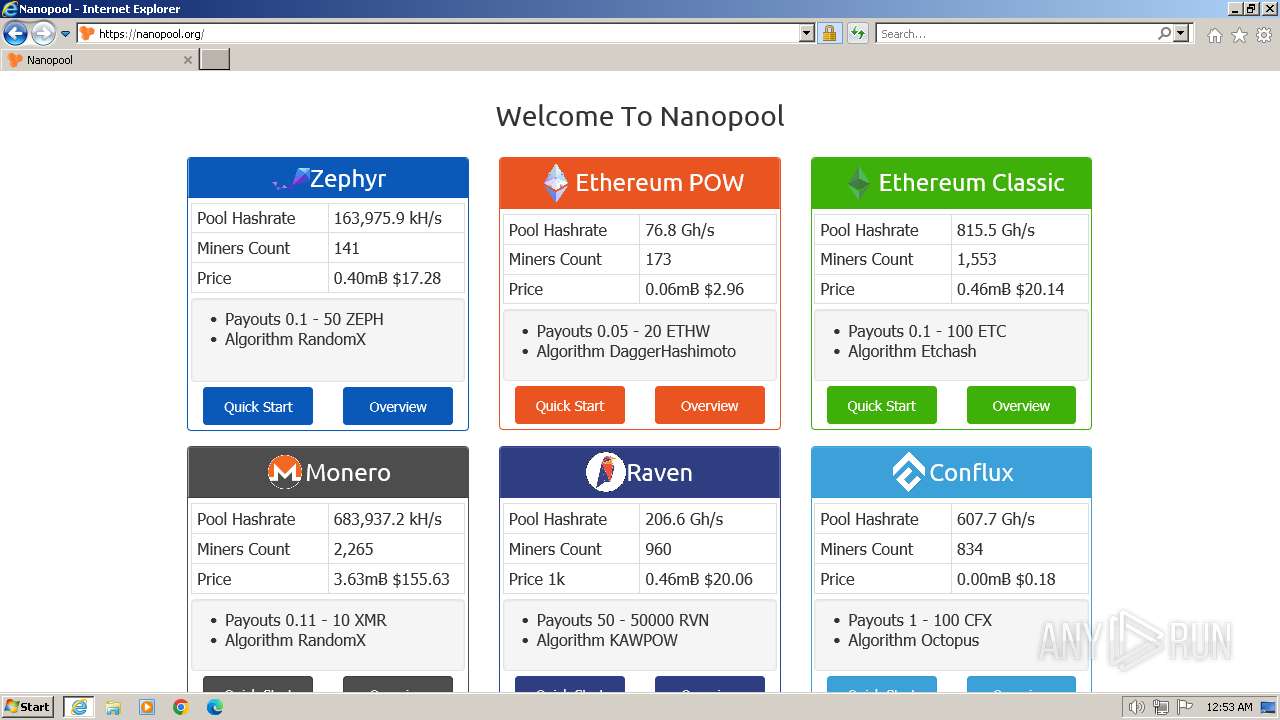
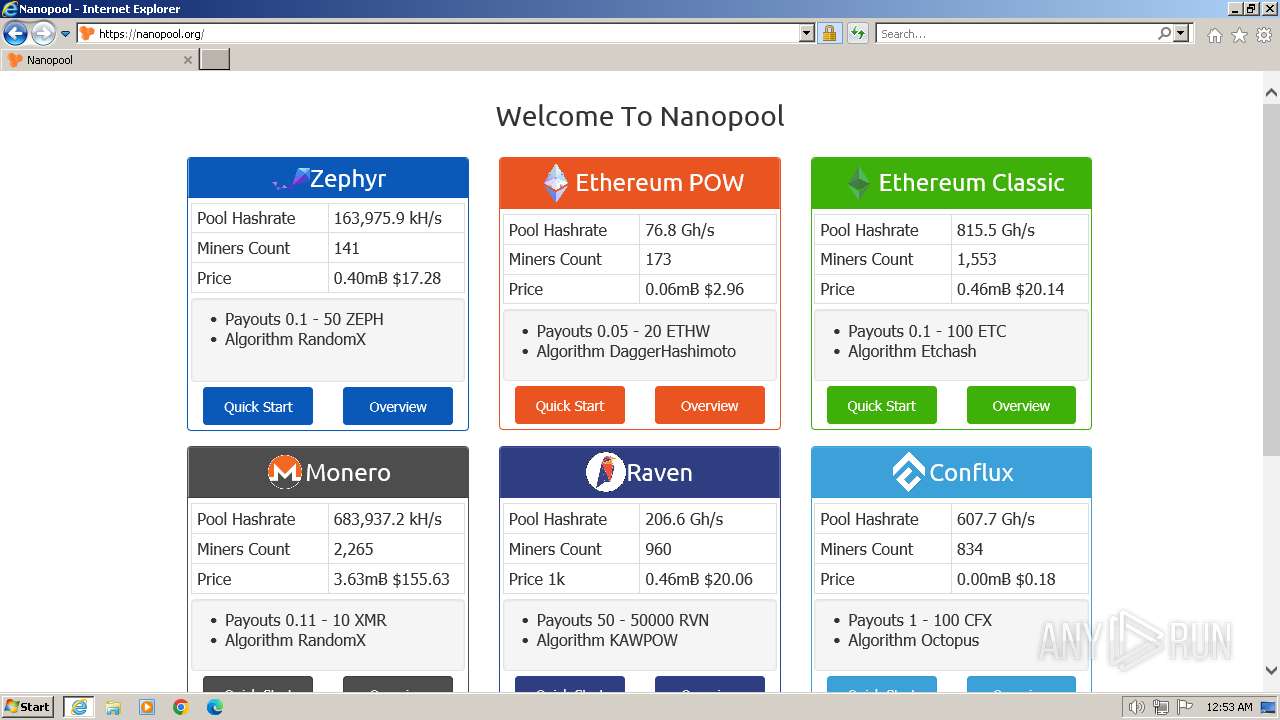
| URL: | xmr-eu1.nanopool.org |
| Full analysis: | https://app.any.run/tasks/0117f77c-5a80-48e9-a810-4c547b78b095 |
| Verdict: | Malicious activity |
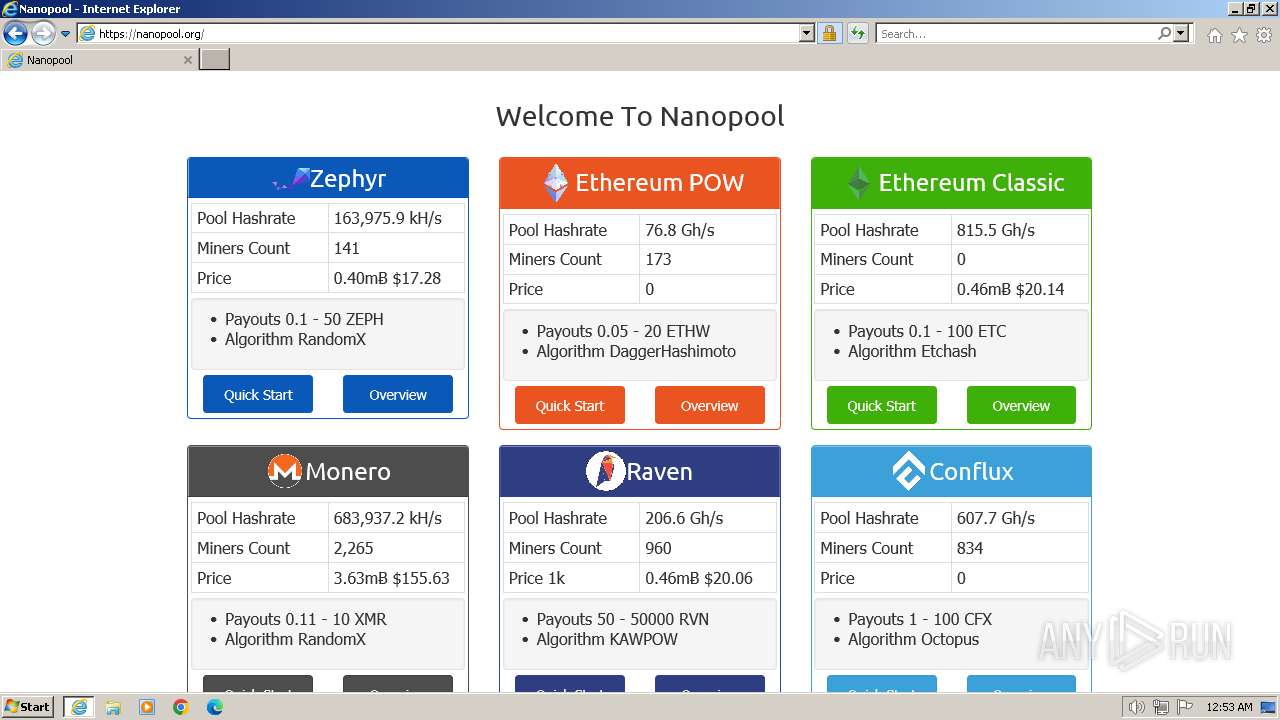
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | January 04, 2024, 00:52:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5E8B1DE2DBEE0E8CFE5C0E53824C2C3E |
| SHA1: | 7B877301280966EB93976B3C21C7C7312B91D27F |
| SHA256: | D197DCA9CB69AB16176FCECFC037E47E38CDE818A66D0CA3B3B18245DA7279CF |
| SSDEEP: | 3:MIAB/7K3C:MIAIy |
MALICIOUS
No malicious indicators.SUSPICIOUS
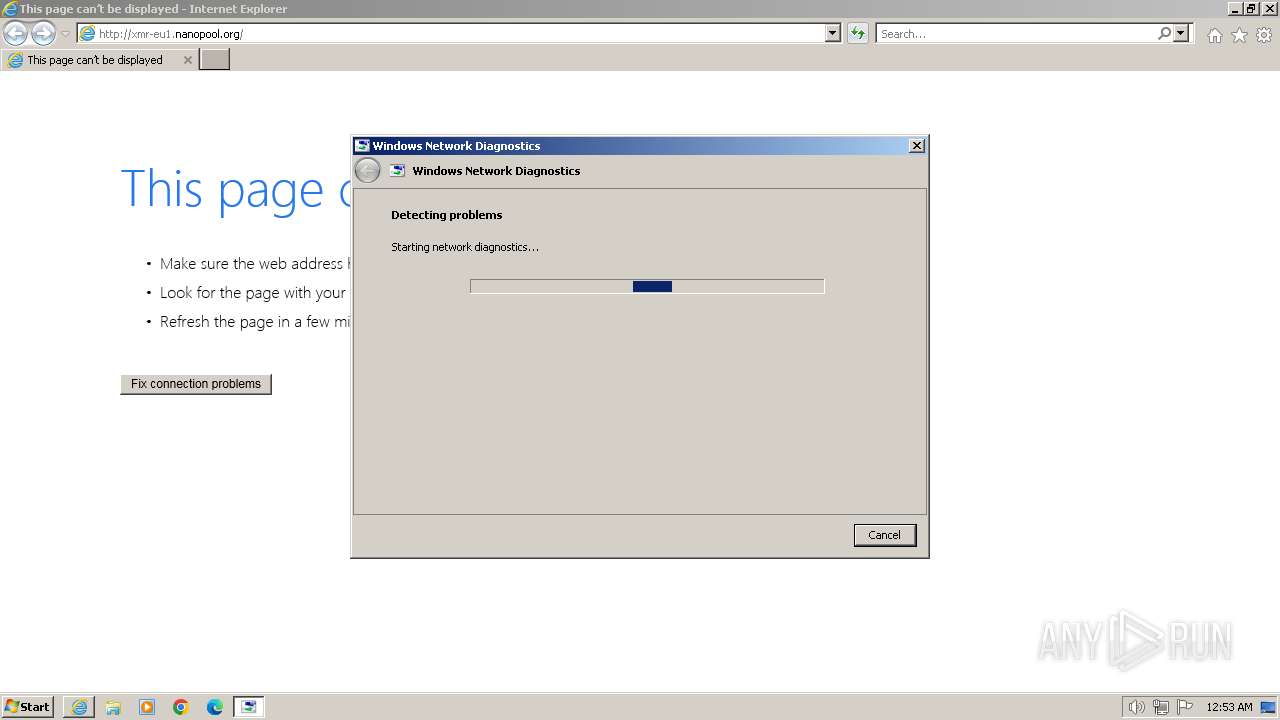
Reads the Internet Settings
- sdiagnhost.exe (PID: 848)
Reads settings of System Certificates
- msdt.exe (PID: 712)
INFO
Application launched itself
- iexplore.exe (PID: 116)
Process drops legitimate windows executable
- msdt.exe (PID: 712)
Create files in a temporary directory
- msdt.exe (PID: 712)
Reads security settings of Internet Explorer
- msdt.exe (PID: 712)
- sdiagnhost.exe (PID: 848)
Drops the executable file immediately after the start
- msdt.exe (PID: 712)
Creates files or folders in the user directory
- msdt.exe (PID: 712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" "xmr-eu1.nanopool.org" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 324 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:116 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 712 | -modal 196838 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDF4A14.tmp -ep NetworkDiagnosticsWeb | C:\Windows\System32\msdt.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 848 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
20 234
Read events
20 094
Write events
138
Delete events
2
Modification events
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
74
Text files
76
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 712 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_b1ec6541-79fd-4fbc-a868-3ea624e9460b\HTInteractiveRes.ps1 | text | |
MD5:C25ED2111C6EE9299E6D9BF51012F2F5 | SHA256:8E326EE0475208D4C943D885035058FAD7146BBA02B66305F7C9F31F6A57E81B | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:BFC4D4DBB6D0280E4BB502EC31314209 | SHA256:E032E41427EFEF9A16AF3D88BAF15061B006318EC270036CA4B241A570FCD88A | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | der | |
MD5:C63E26C4975910693E4E1DF165B50CC3 | SHA256:99AE0E949A82B867D1086B57D24298A11C60C38488CDCBC101D8567CA9D44545 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:7FD6F1A693DF408B91688059BDB3BB09 | SHA256:63BCC3639952E2DB32CC38A18F51A17885680A2D985FE156F94D817166506875 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 712 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_b1ec6541-79fd-4fbc-a868-3ea624e9460b\StartDPSService.ps1 | text | |
MD5:A660422059D953C6D681B53A6977100E | SHA256:D19677234127C38A52AEC23686775A8EB3F4E3A406F4A11804D97602D6C31813 | |||
| 712 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_b1ec6541-79fd-4fbc-a868-3ea624e9460b\NetworkDiagnosticsTroubleshoot.ps1 | text | |
MD5:1D192CE36953DBB7DC7EE0D04C57AD8D | SHA256:935A231924AE5D4A017B0C99D4A5F3904EF280CEA4B3F727D365283E26E8A756 | |||
| 712 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_b1ec6541-79fd-4fbc-a868-3ea624e9460b\DiagPackage.diagpkg | xml | |
MD5:C9FB87FA3460FAE6D5D599236CFD77E2 | SHA256:CDE728C08A4E50A02FCFF35C90EE2B3B33AB24C8B858F180B6A67BFA94DEF35F | |||
| 712 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_b1ec6541-79fd-4fbc-a868-3ea624e9460b\en-US\DiagPackage.dll.mui | executable | |
MD5:5D7936806E6855E2ECC2B095316D45D8 | SHA256:71A4559F9FD122914A95998E8685BE638B8F81E581987708497E8F8A7A2F4DCB | |||
| 712 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_b1ec6541-79fd-4fbc-a868-3ea624e9460b\NetworkDiagnosticsResolve.ps1 | text | |
MD5:A7B957F221C643580184665BE57E6AC8 | SHA256:8582EF50174CB74233F196F193E04C0CCBBEE2AED5CE50964CBB95822C218E7F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
162
DNS requests
33
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | iexplore.exe | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d8f761b8c0f86c21 | unknown | compressed | 4.66 Kb | unknown |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
— | — | GET | 200 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?111b88f027149bc7 | unknown | compressed | 4.66 Kb | unknown |
324 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
116 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
324 | iexplore.exe | GET | 301 | 104.20.82.127:80 | http://nanopool.org/ | unknown | — | — | unknown |
324 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
324 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
324 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
324 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQClj3zJOwEs2AlR6v%2BfUXog | unknown | binary | 472 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
324 | iexplore.exe | 51.15.193.130:80 | xmr-eu1.nanopool.org | Online S.a.s. | FR | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
324 | iexplore.exe | 141.94.23.83:80 | xmr-eu1.nanopool.org | OVH SAS | FR | unknown |
116 | iexplore.exe | 104.126.37.128:443 | www.bing.com | Akamai International B.V. | DE | unknown |
116 | iexplore.exe | 184.24.77.194:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
116 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
324 | iexplore.exe | 51.15.58.224:80 | xmr-eu1.nanopool.org | Online S.a.s. | NL | unknown |
324 | iexplore.exe | 146.59.154.106:80 | xmr-eu1.nanopool.org | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xmr-eu1.nanopool.org |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
nanopool.org |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |