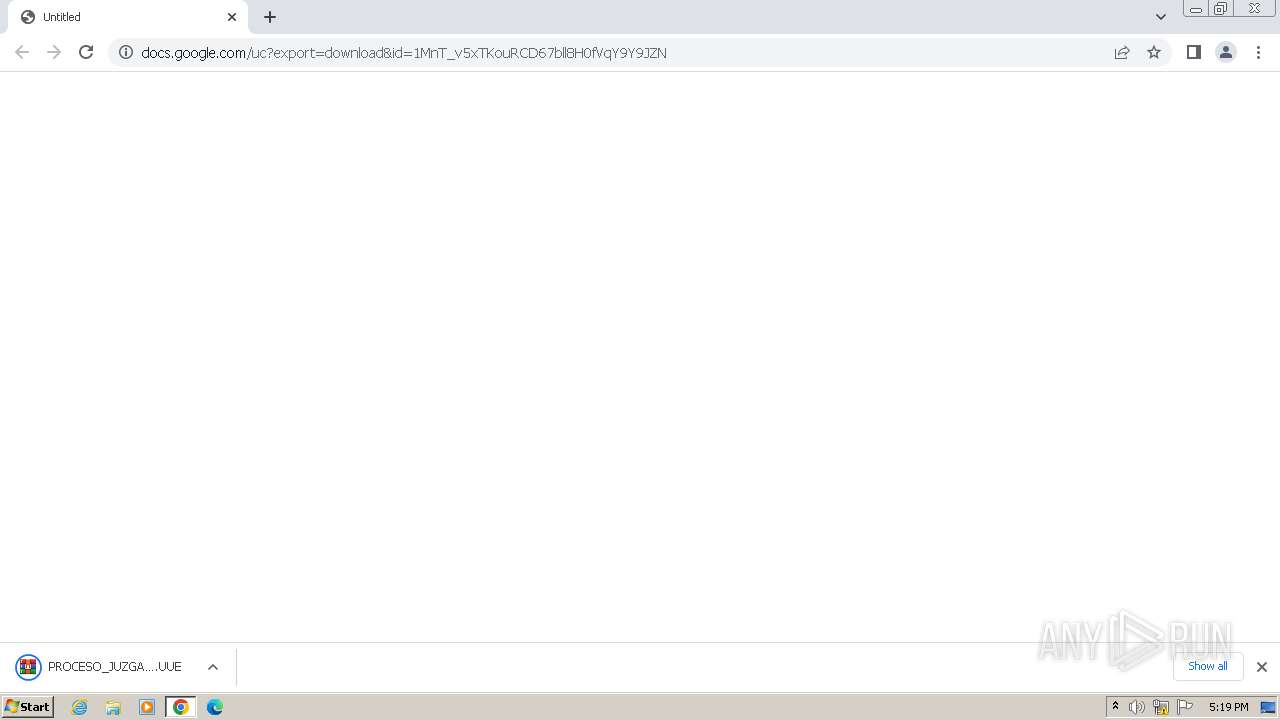
| URL: | https://docs.google.com/uc?export=download&id=1MnT_v5xTKouRCD67bll8H0fVqY9Y9JZN |
| Full analysis: | https://app.any.run/tasks/7a4d0c7b-7846-4569-8eca-33abc0dc326c |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | June 06, 2024, 16:18:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2FD9BB390000F93488F76454E8D24F11 |
| SHA1: | 8715F851D703B47C8972844CBFB31BE803934704 |
| SHA256: | D17E47D3E4F75EA648CF1C205196A272C21E8F4694E6712C512D94669AB45756 |
| SSDEEP: | 3:N8SP3u2NAaBrC2o2QJ3SVSj:2Sm2BB+2+SMj |
MALICIOUS
Changes the autorun value in the registry
- PROCESO_JUZGADO_PENAL_N° 4528-2932-22.exe (PID: 664)
- PROCESO_JUZGADO_PENAL_N° 4528-2932-22.exe (PID: 1612)
Starts Visual C# compiler
- PROCESO_JUZGADO_PENAL_N° 4528-2932-22.exe (PID: 664)
- PROCESO_JUZGADO_PENAL_N° 4528-2932-22.exe (PID: 1612)
ASYNCRAT has been detected (SURICATA)
- csc.exe (PID: 2188)
ASYNCRAT has been detected (YARA)
- csc.exe (PID: 2188)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2020)
Connects to unusual port
- csc.exe (PID: 2188)
Reads settings of System Certificates
- csc.exe (PID: 2188)
Contacting a server suspected of hosting an CnC
- csc.exe (PID: 2188)
Reads the Internet Settings
- csc.exe (PID: 2188)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 1980)
- PROCESO_JUZGADO_PENAL_N° 4528-2932-22.exe (PID: 664)
- PROCESO_JUZGADO_PENAL_N° 4528-2932-22.exe (PID: 1612)
- csc.exe (PID: 2188)
- csc.exe (PID: 2588)
Application launched itself
- chrome.exe (PID: 3972)
Reads the computer name
- wmpnscfg.exe (PID: 1980)
- csc.exe (PID: 2188)
- csc.exe (PID: 2588)
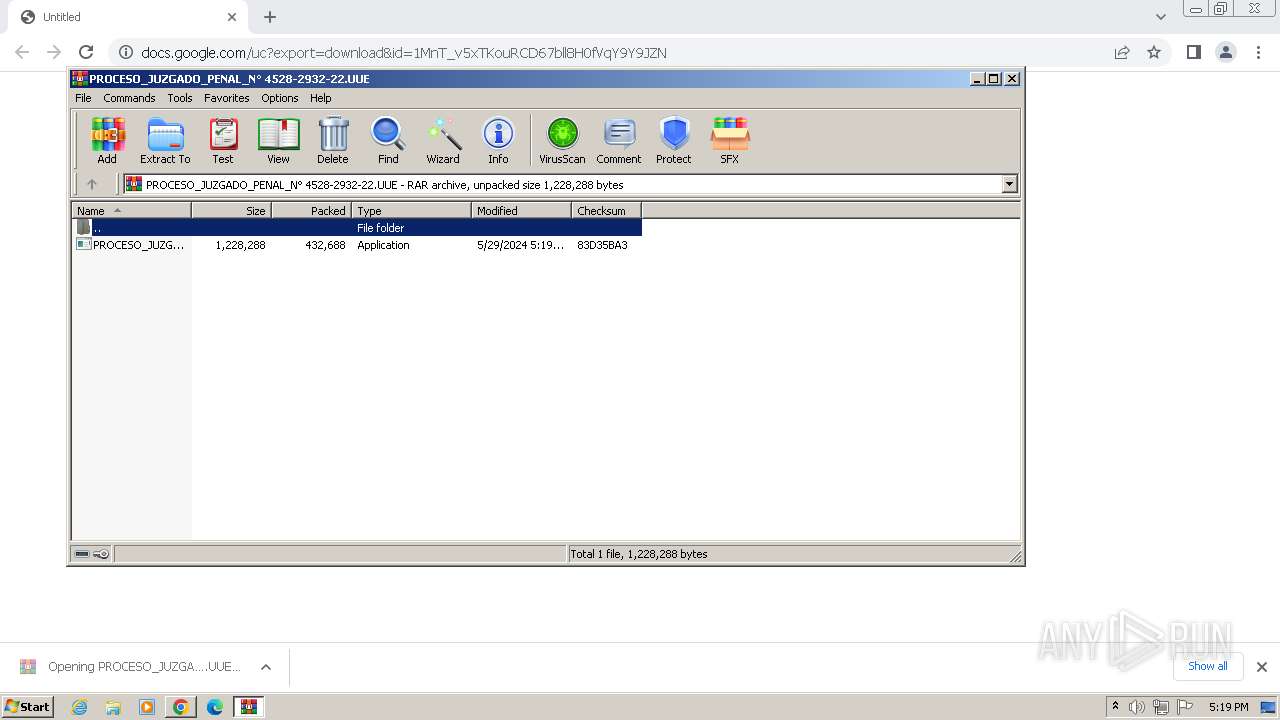
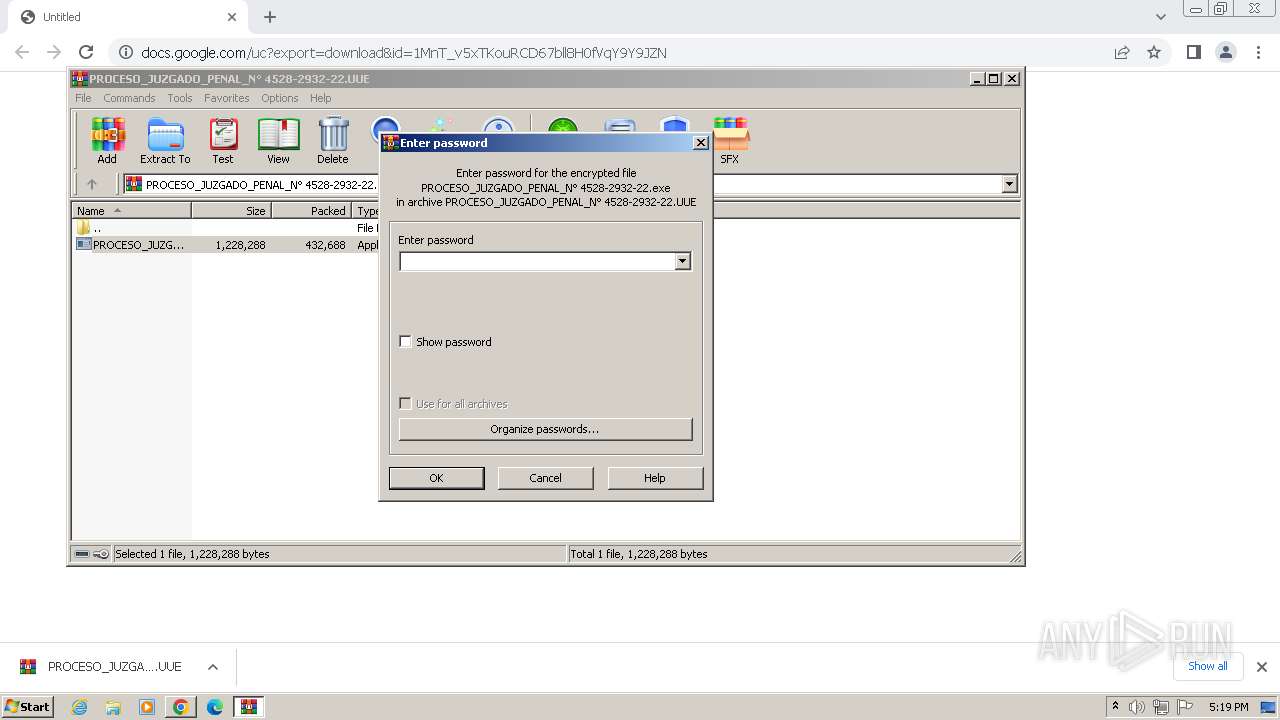
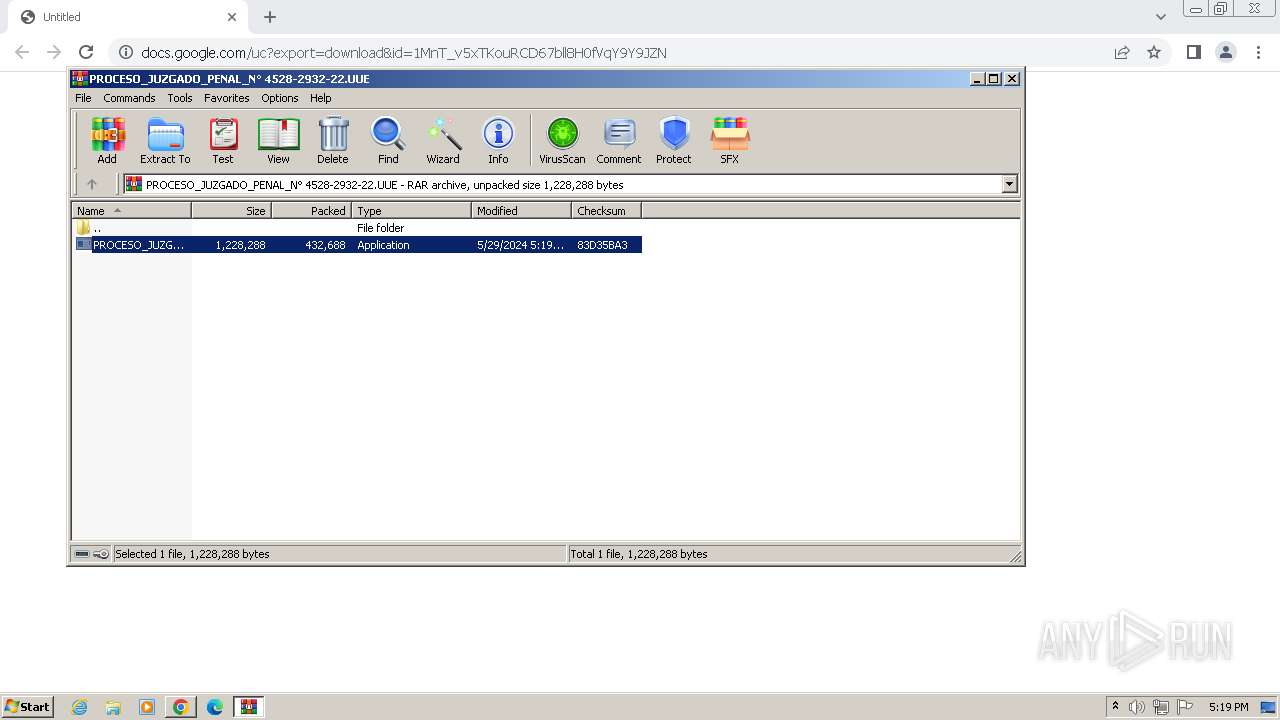
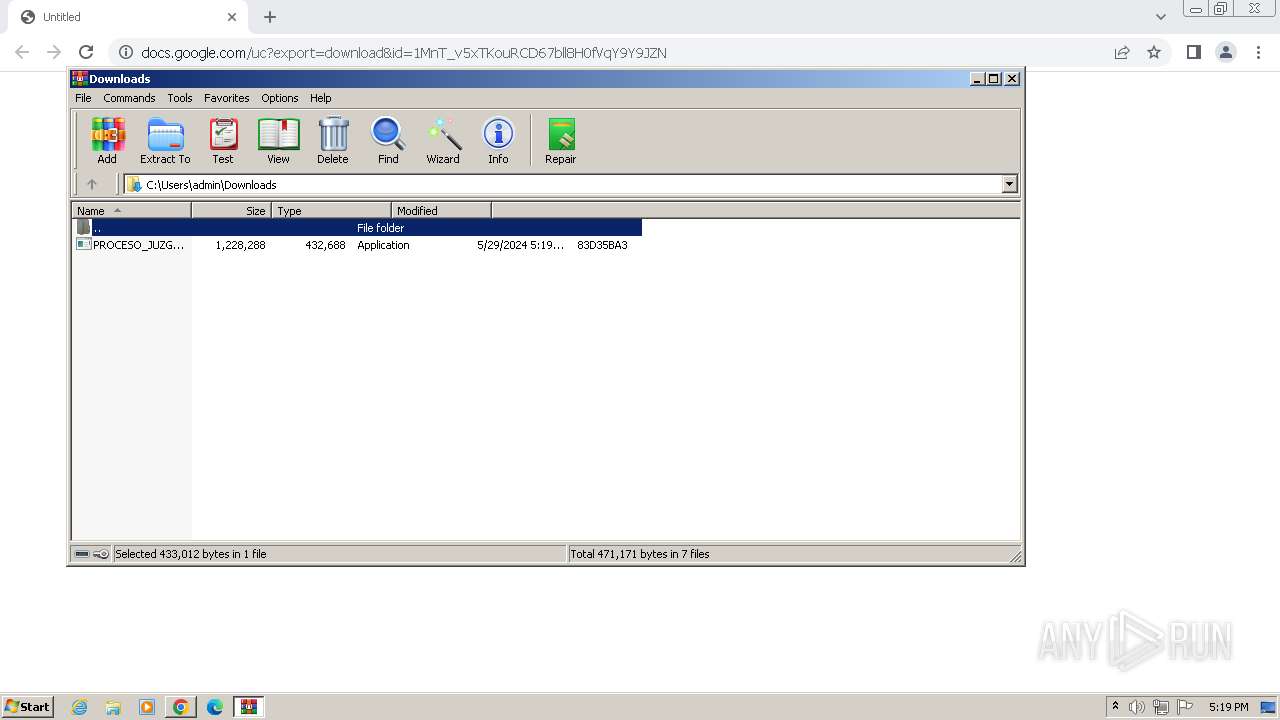
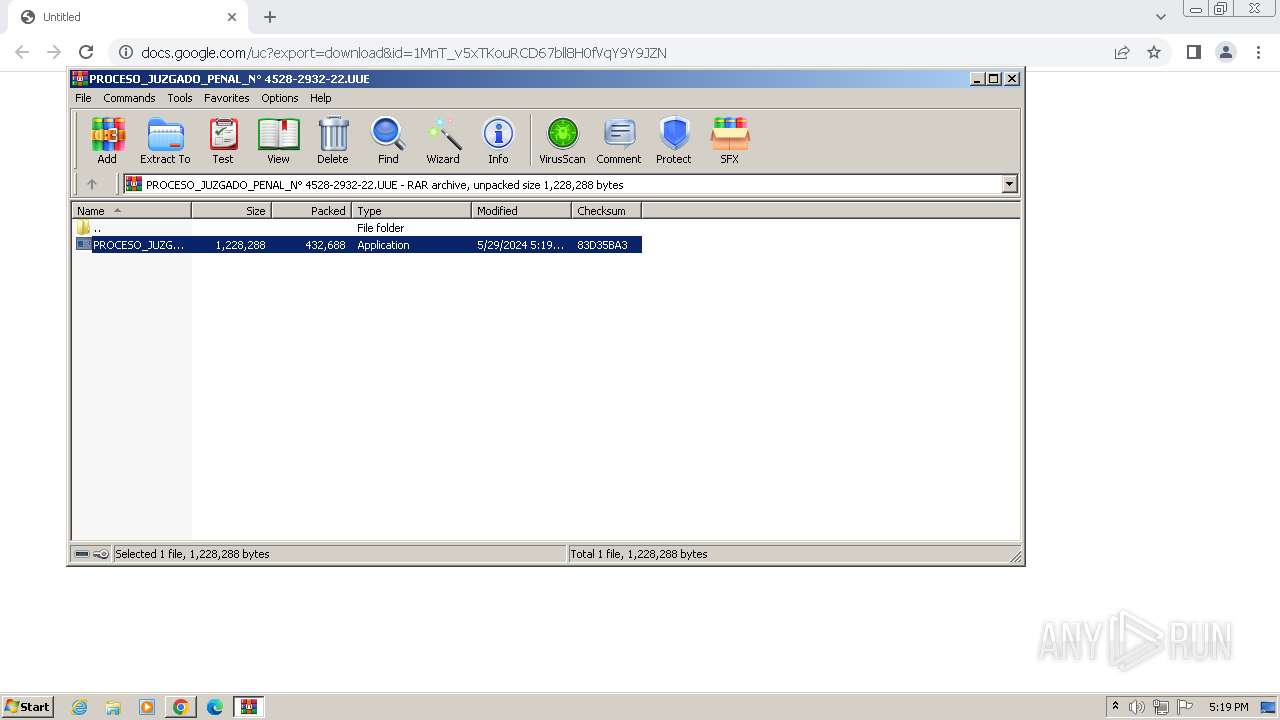
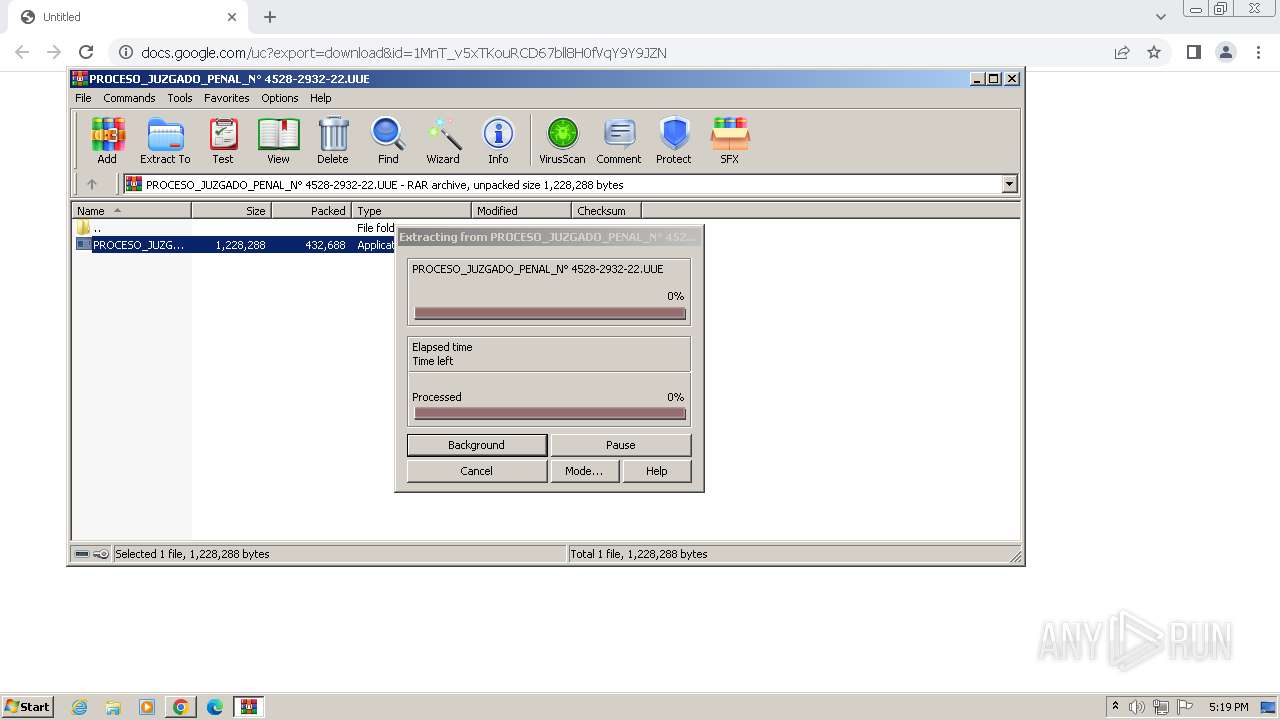
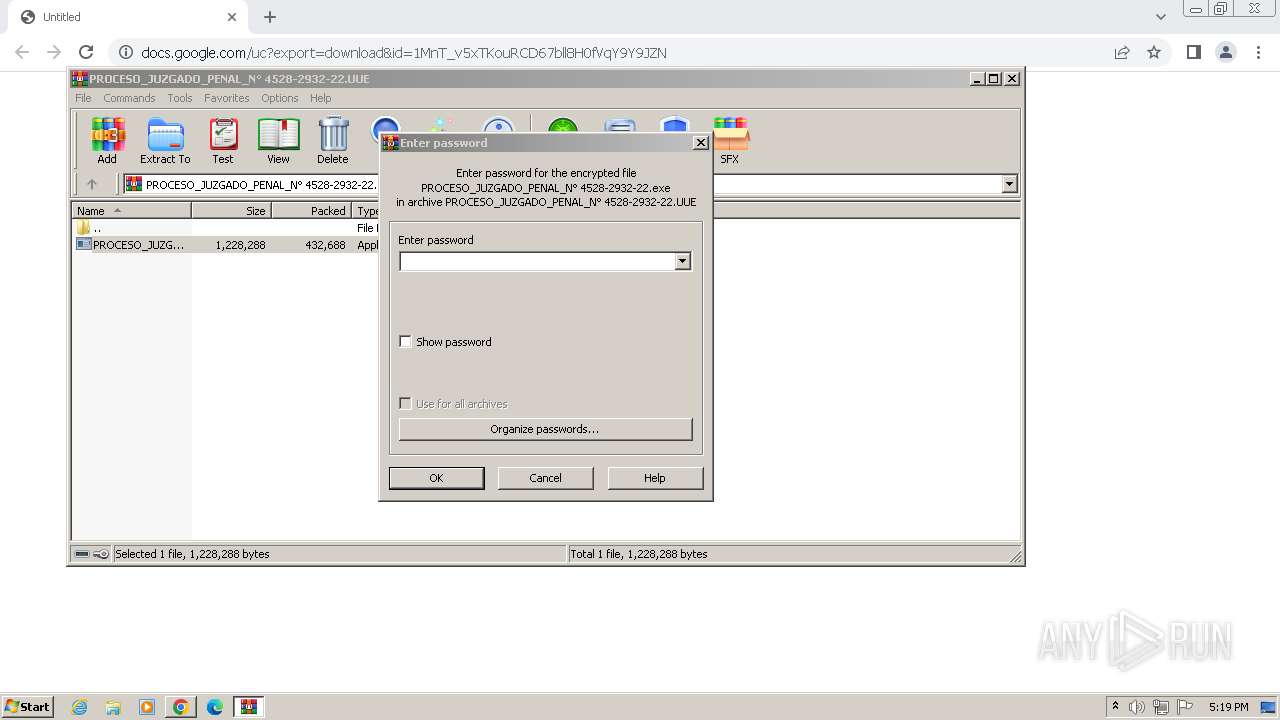
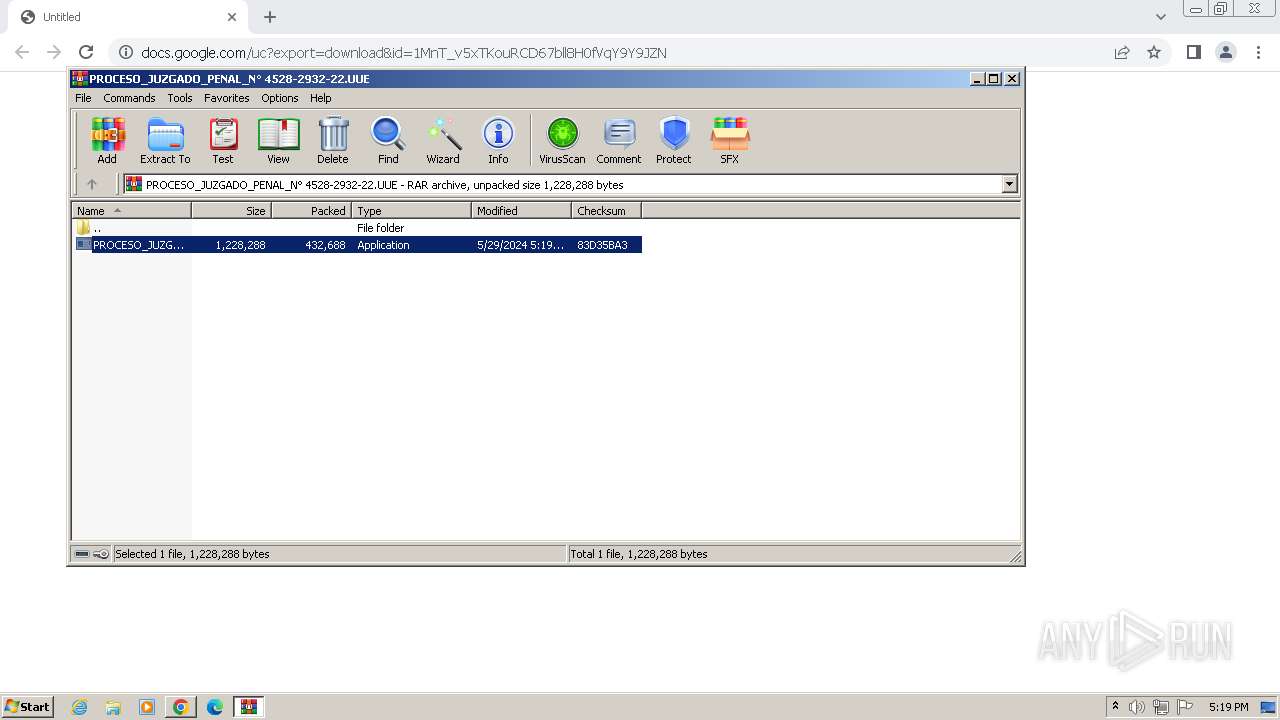
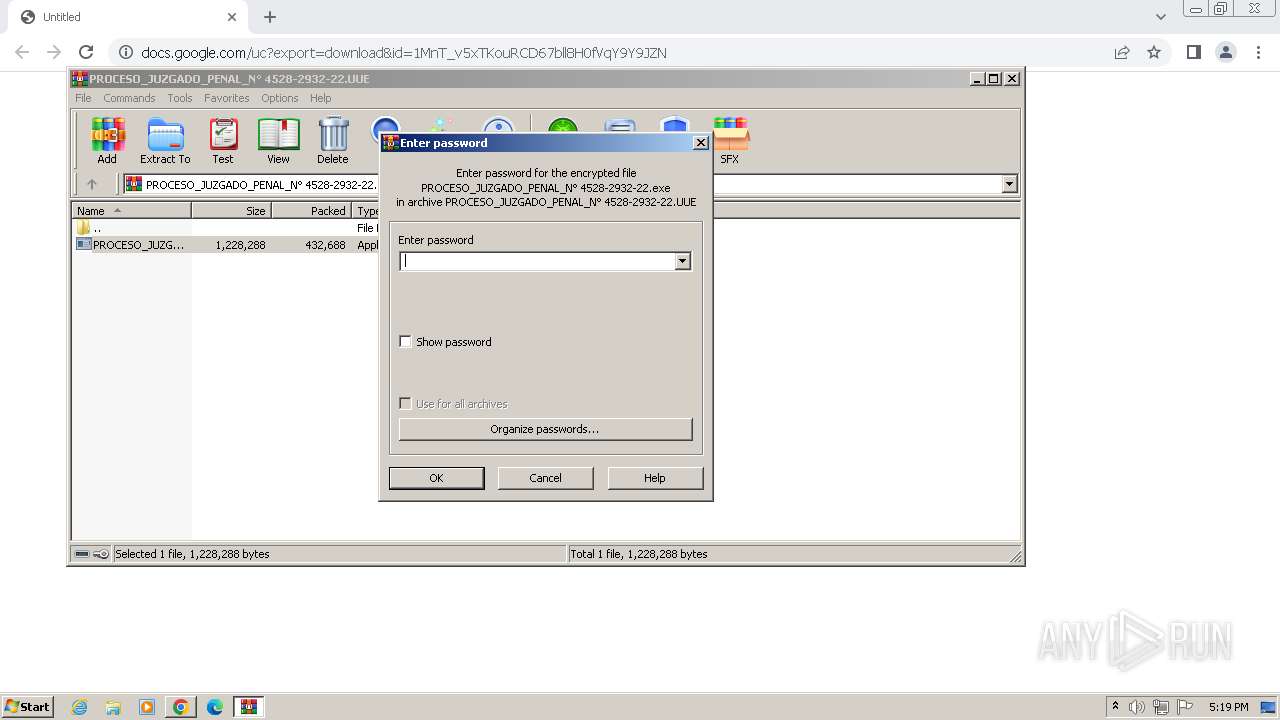
The process uses the downloaded file
- chrome.exe (PID: 2280)
- WinRAR.exe (PID: 2020)
Manual execution by a user
- wmpnscfg.exe (PID: 1980)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2020)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2020)
Reads the machine GUID from the registry
- csc.exe (PID: 2188)
- csc.exe (PID: 2588)
Reads Environment values
- csc.exe (PID: 2188)
Reads the software policy settings
- csc.exe (PID: 2188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(2188) csc.exe
C2 (1)diazmane14.duckdns.org
Ports (1)9000
Version1.0.7
Options
AutoRunfalse
Mutexpowershellmcgdtrseawqyudisokfdpx
InstallFolder%Temp%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVALHnIPqvO0ejsIiXRAS4cjBZw0S5MA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIyMTAxMzE2NDExOFoXDTMzMDcyMjE2NDExOFowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignaturePVDvL4eTwhleDuHXgkrk3IJAOe9mzn4Ih9iO4YLG7bX7L42SbED+tQS0OqJXKY0ajHSzPoV125sUl84R/6tpsK2PWHSWEQAAZm1teYOg7+YRESVuBq7uwGr5ZIrj2cYz8FrXY8oXqSuyQnBA0bh4Qrt061iRUlfO27gQ2VeeSPo=
Keys
AESa1ef5a4c021ebf903d0411f79e4bc5bfe0ceba39201d386ec59b790c1e448a5b
SaltDcRatByqwqdanchun
Total processes
48
Monitored processes
16
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2032 --field-trial-handle=1148,i,17191758660113037130,833455565531662565,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 664 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2020.5895\PROCESO_JUZGADO_PENAL_N° 4528-2932-22.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2020.5895\PROCESO_JUZGADO_PENAL_N° 4528-2932-22.exe | WinRAR.exe | ||||||||||||
User: admin Company: uTorrent Software Inc. Integrity Level: MEDIUM Description: uTorrent Launcher Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1284 --field-trial-handle=1148,i,17191758660113037130,833455565531662565,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1516 --field-trial-handle=1148,i,17191758660113037130,833455565531662565,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1612 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2020.6992\PROCESO_JUZGADO_PENAL_N° 4528-2932-22.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2020.6992\PROCESO_JUZGADO_PENAL_N° 4528-2932-22.exe | WinRAR.exe | ||||||||||||
User: admin Company: uTorrent Software Inc. Integrity Level: MEDIUM Description: uTorrent Launcher Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2012 --field-trial-handle=1148,i,17191758660113037130,833455565531662565,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1224 --field-trial-handle=1148,i,17191758660113037130,833455565531662565,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3468 --field-trial-handle=1148,i,17191758660113037130,833455565531662565,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1980 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2020 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\PROCESO_JUZGADO_PENAL_N° 4528-2932-22.UUE" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
14 056
Read events
13 952
Write events
98
Delete events
6
Modification events
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
3
Suspicious files
22
Text files
20
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF103dc6.TMP | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF103ed0.TMP | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF104567.TMP | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF103ff9.TMP | text | |
MD5:BF244CDEBD39A0D20444C1578C0200BE | SHA256:CC7E247D7764DA50D4137E894838F918281D4915FE0823B4FC0CB763BF582F4D | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\eef566f1-ccf4-4188-895d-4bbd44579139.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
13
DNS requests
14
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2188 | csc.exe | GET | — | 2.19.126.137:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f2bc360093877209 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1036 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
3972 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1036 | chrome.exe | 216.58.212.174:443 | docs.google.com | GOOGLE | US | whitelisted |
1036 | chrome.exe | 142.250.186.65:443 | drive.usercontent.google.com | GOOGLE | US | whitelisted |
3972 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
1036 | chrome.exe | 172.217.18.4:443 | www.google.com | GOOGLE | US | whitelisted |
1036 | chrome.exe | 216.58.212.170:443 | www.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
docs.google.com |
| shared |
drive.usercontent.google.com |
| unknown |
www.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
diazmane14.duckdns.org |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1088 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
1088 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
1088 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2188 | csc.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
2188 | csc.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |