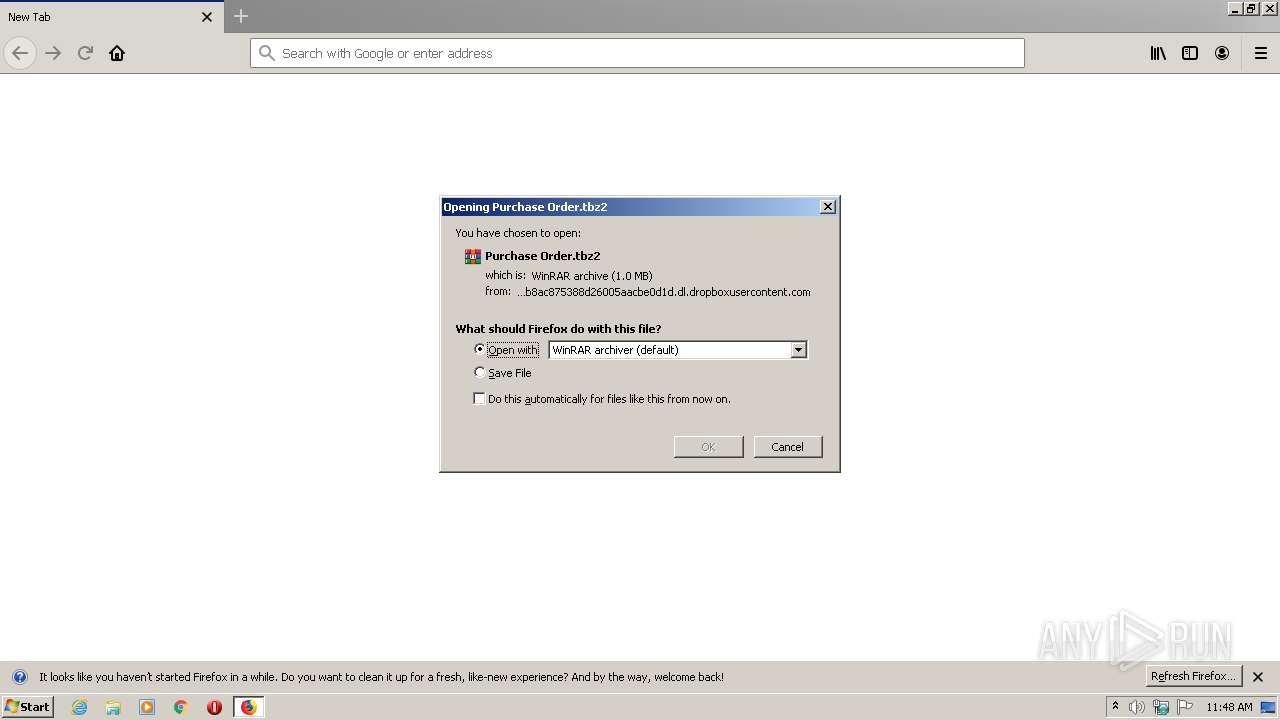
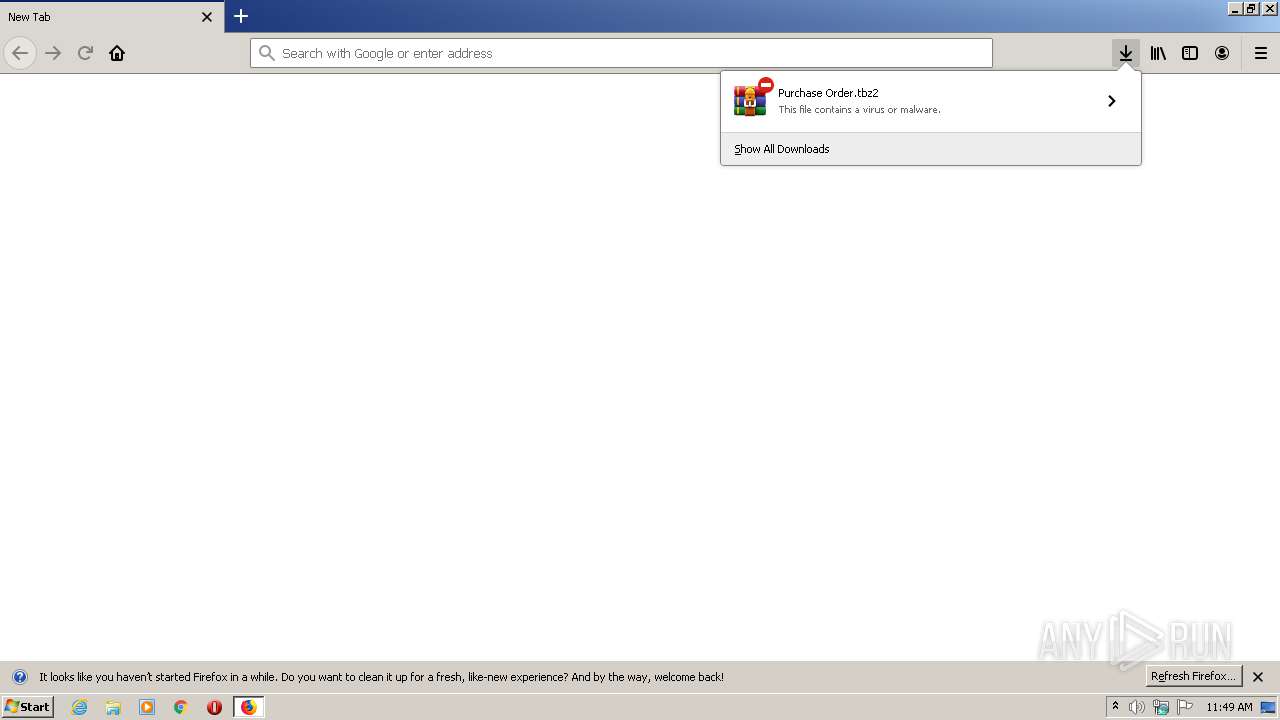
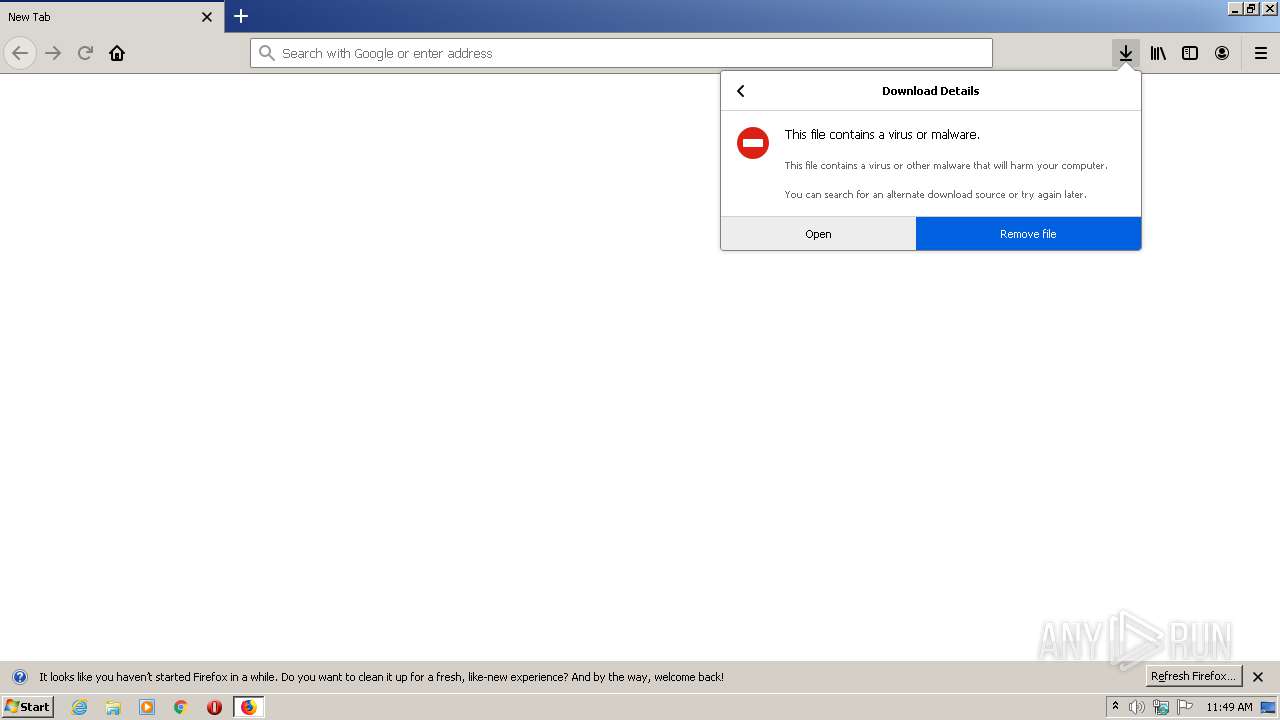
| URL: | https://www.dropbox.com/s/3qx86k2oabnwnq4/?dl=1 |
| Full analysis: | https://app.any.run/tasks/9a8d0b46-883a-403d-bb78-db051121913b |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
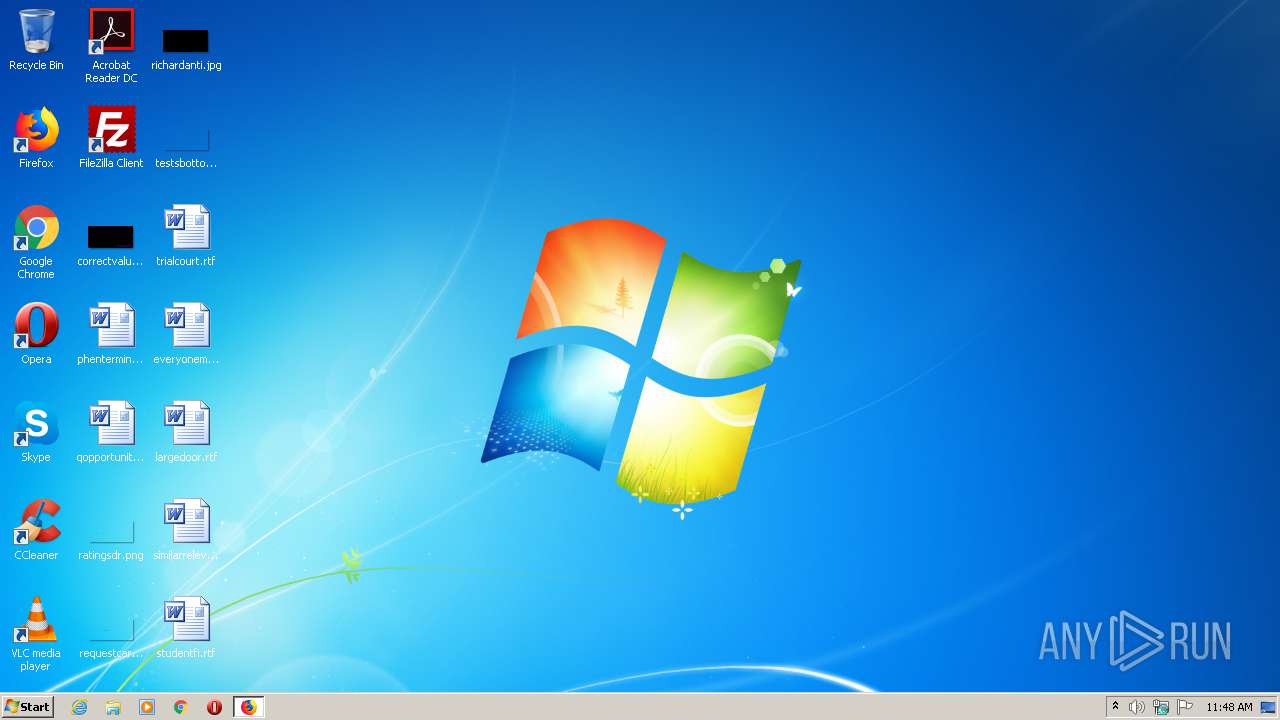
| Analysis date: | August 08, 2020, 10:48:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D989FF97FFBF14EFD3DF4025AD98C86D |
| SHA1: | 417C7981AEFF52D09A39543625E1D986AEBD9E65 |
| SHA256: | D1593D4C18A8EEB69DBA9A703DA63A463EC18D2FD7D34CC60A4B07CAA3EEE086 |
| SSDEEP: | 3:N8DSLcVHGkGdiLKSYUn:2OLHkKi+An |
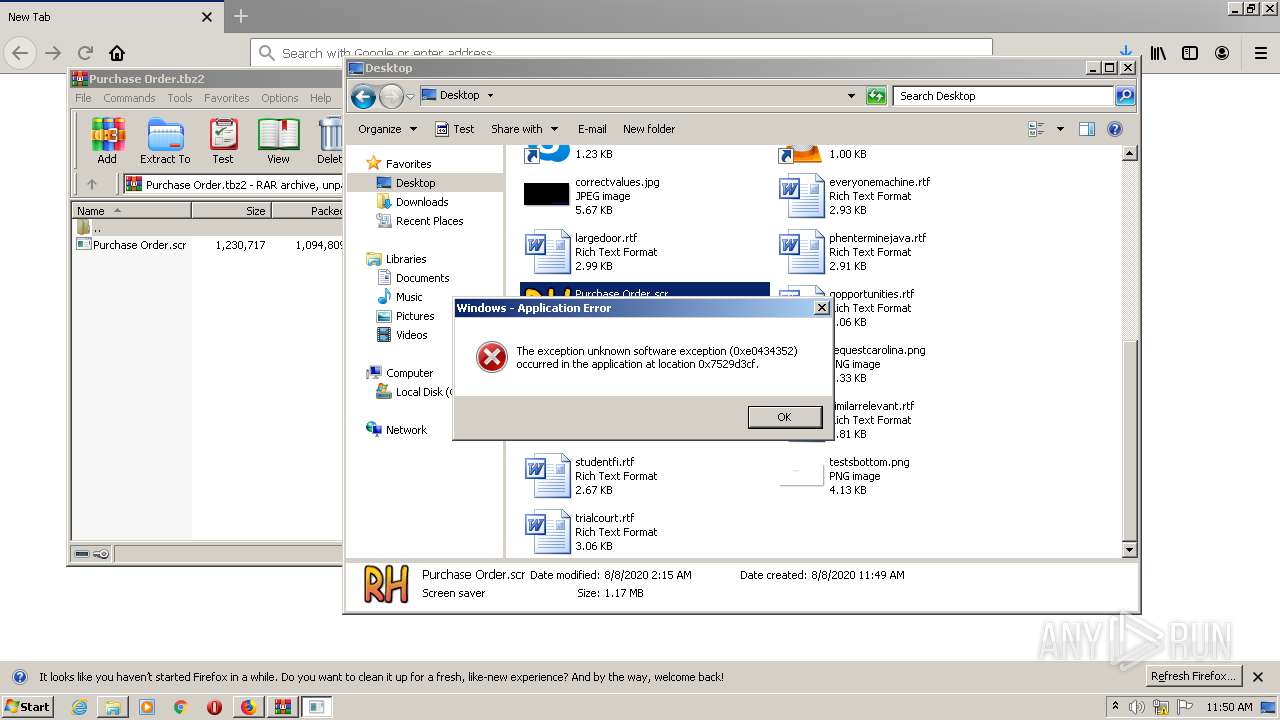
MALICIOUS
Application was dropped or rewritten from another process
- Purchase Order.scr (PID: 1484)
- qcpdpja.pif (PID: 564)
- RegSvcs.exe (PID: 2248)
- qcpdpja.pif (PID: 2760)
- RegSvcs.exe (PID: 3632)
- RegSvcs.exe (PID: 968)
- RegSvcs.exe (PID: 2488)
Changes the autorun value in the registry
- RegSvcs.exe (PID: 2248)
- qcpdpja.pif (PID: 564)
- qcpdpja.pif (PID: 2760)
- RegSvcs.exe (PID: 968)
Writes to a start menu file
- qcpdpja.pif (PID: 564)
- qcpdpja.pif (PID: 2760)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 1680)
- cmd.exe (PID: 2384)
QUASAR was detected
- RegSvcs.exe (PID: 2248)
- RegSvcs.exe (PID: 968)
SUSPICIOUS
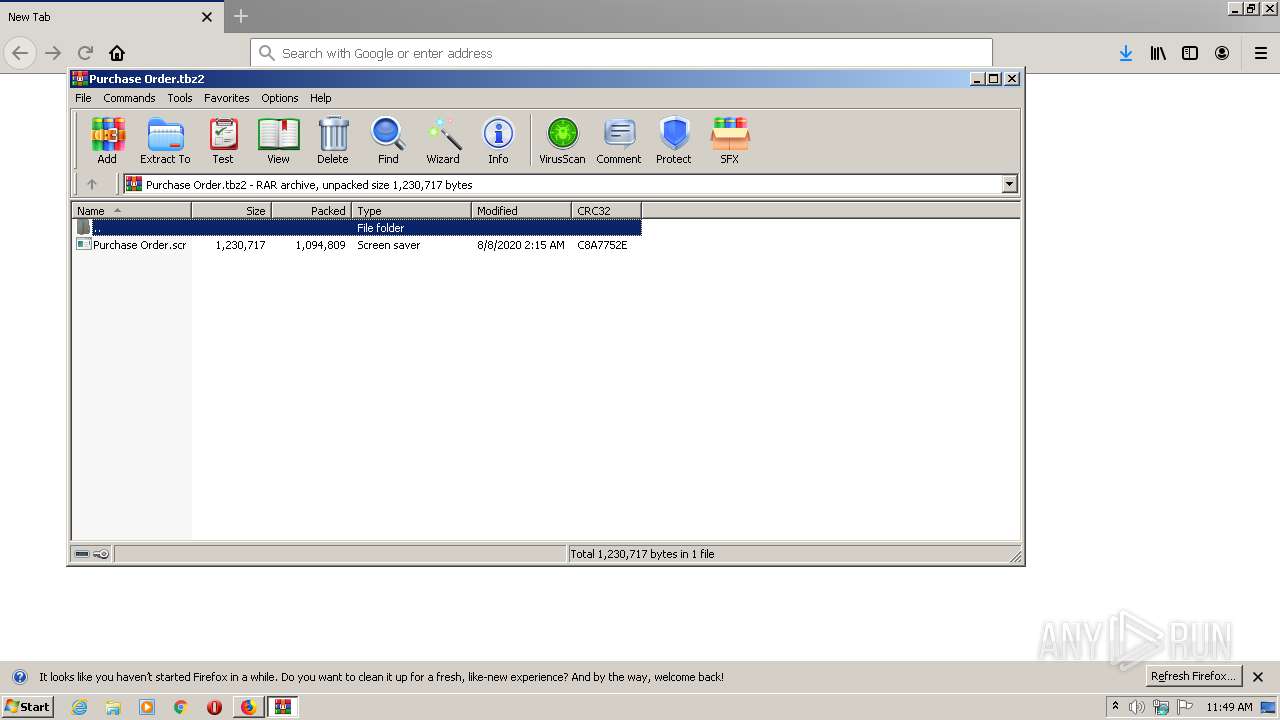
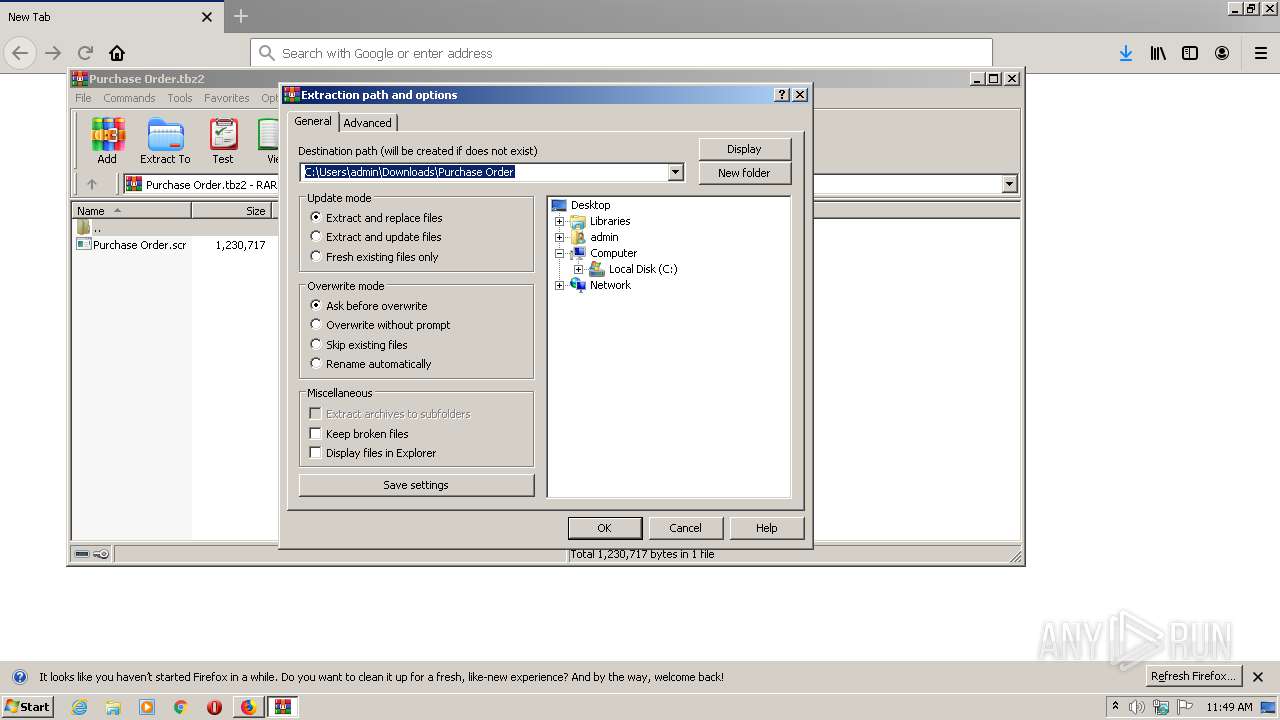
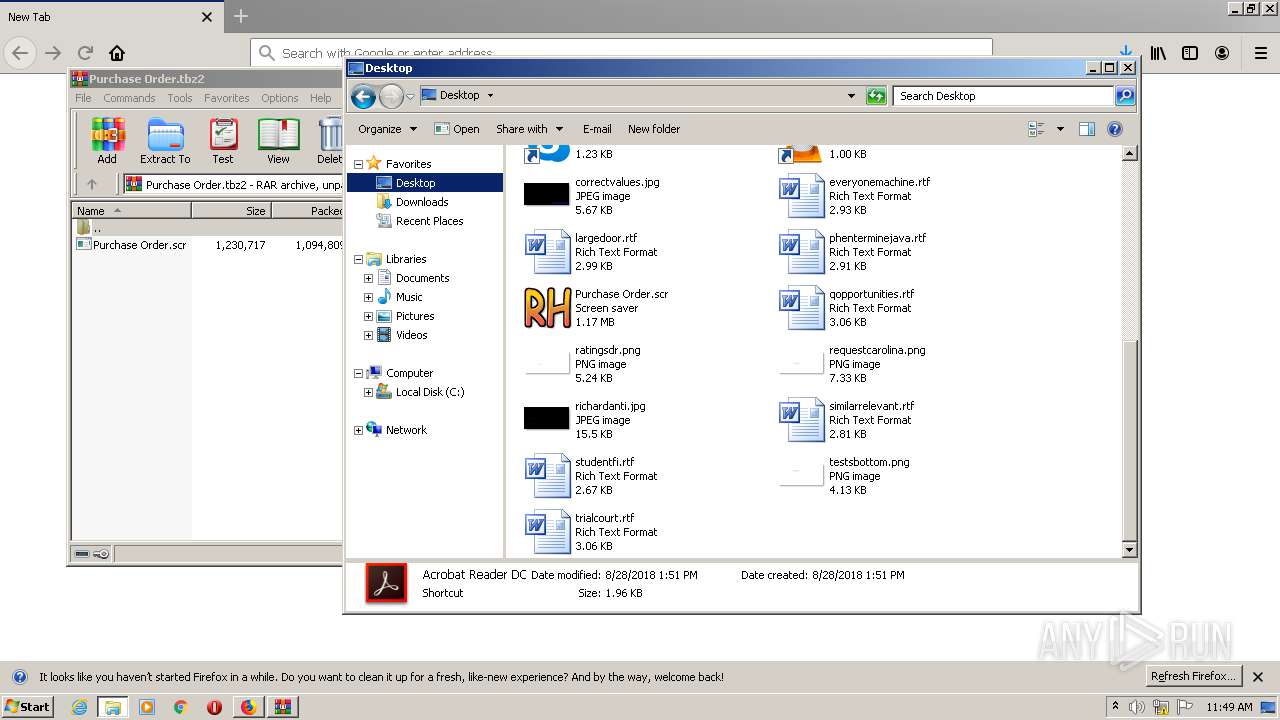
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2664)
- Purchase Order.scr (PID: 1484)
- qcpdpja.pif (PID: 564)
- qcpdpja.pif (PID: 2760)
Creates files in the program directory
- firefox.exe (PID: 1492)
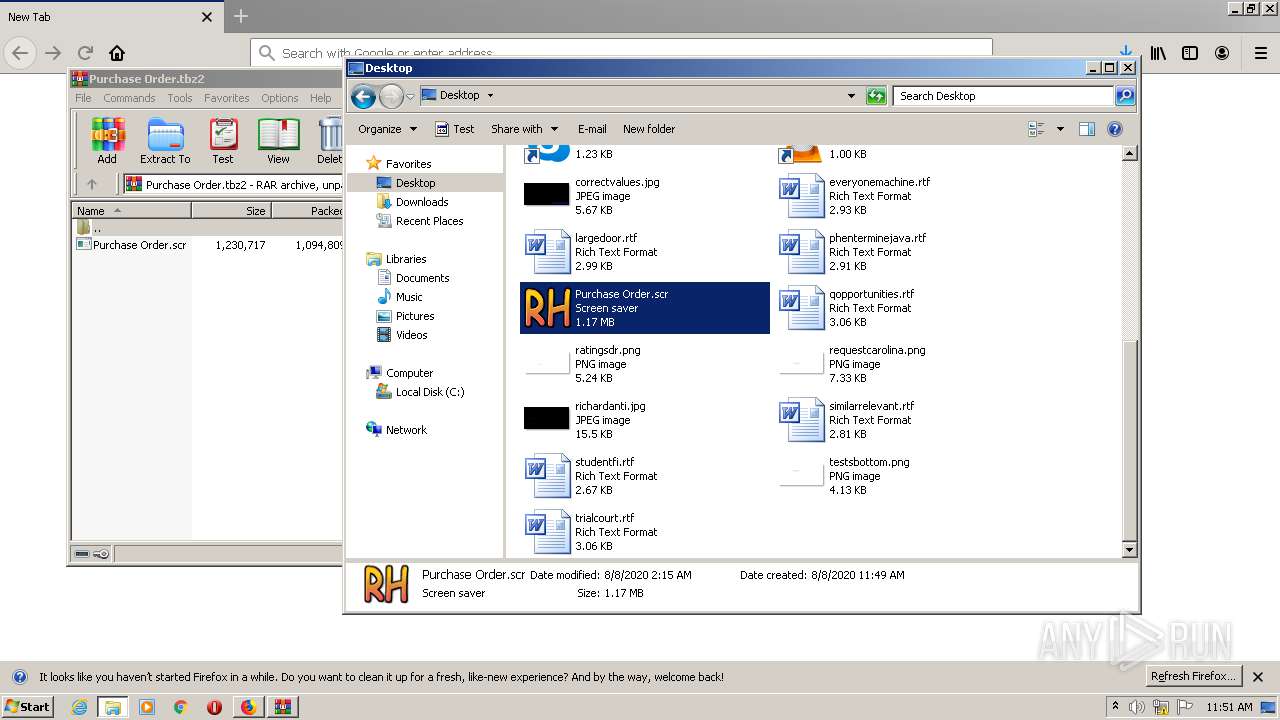
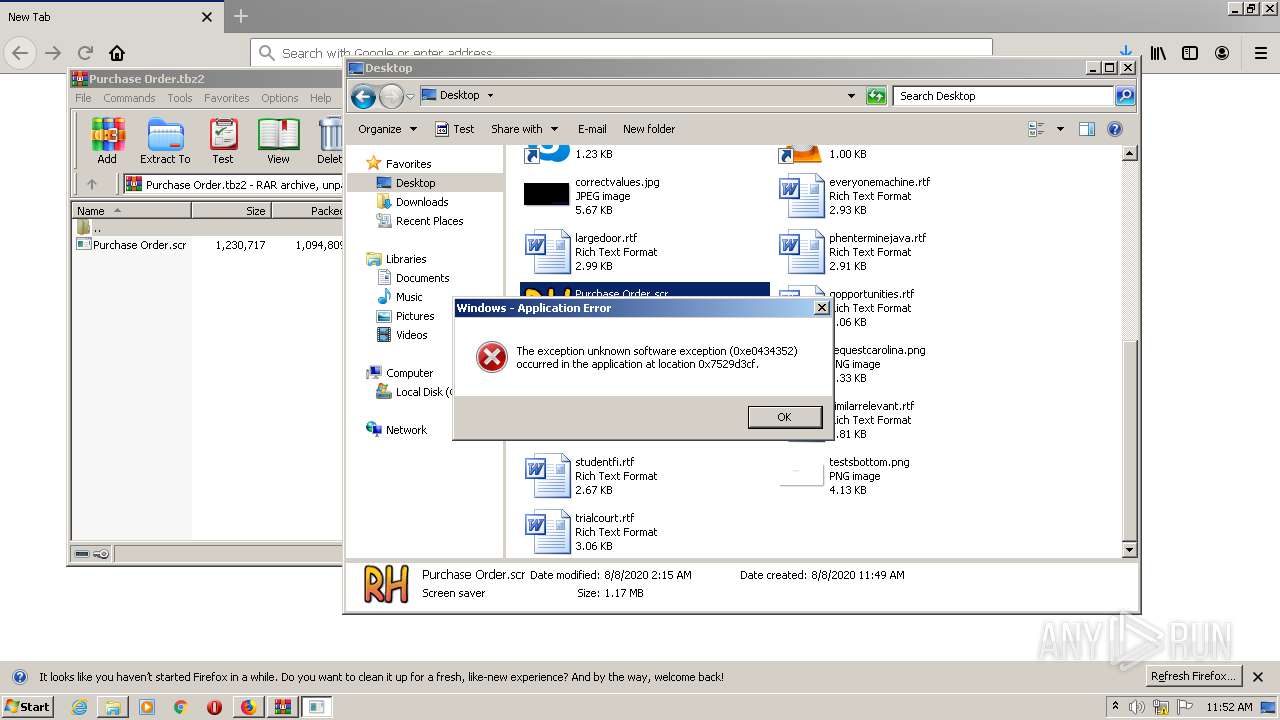
Starts application with an unusual extension
- Purchase Order.scr (PID: 1484)
- cmd.exe (PID: 1680)
- WScript.exe (PID: 1728)
- cmd.exe (PID: 2384)
Starts MSHTA.EXE for opening HTA or HTMLS files
- qcpdpja.pif (PID: 564)
- qcpdpja.pif (PID: 2760)
Checks for external IP
- RegSvcs.exe (PID: 2248)
- RegSvcs.exe (PID: 968)
Creates files in the user directory
- qcpdpja.pif (PID: 564)
Starts CMD.EXE for commands execution
- RegSvcs.exe (PID: 2248)
- RegSvcs.exe (PID: 968)
Executes scripts
- qcpdpja.pif (PID: 564)
INFO
Application launched itself
- firefox.exe (PID: 1492)
- firefox.exe (PID: 2744)
Reads CPU info
- firefox.exe (PID: 1492)
Reads Internet Cache Settings
- firefox.exe (PID: 1492)
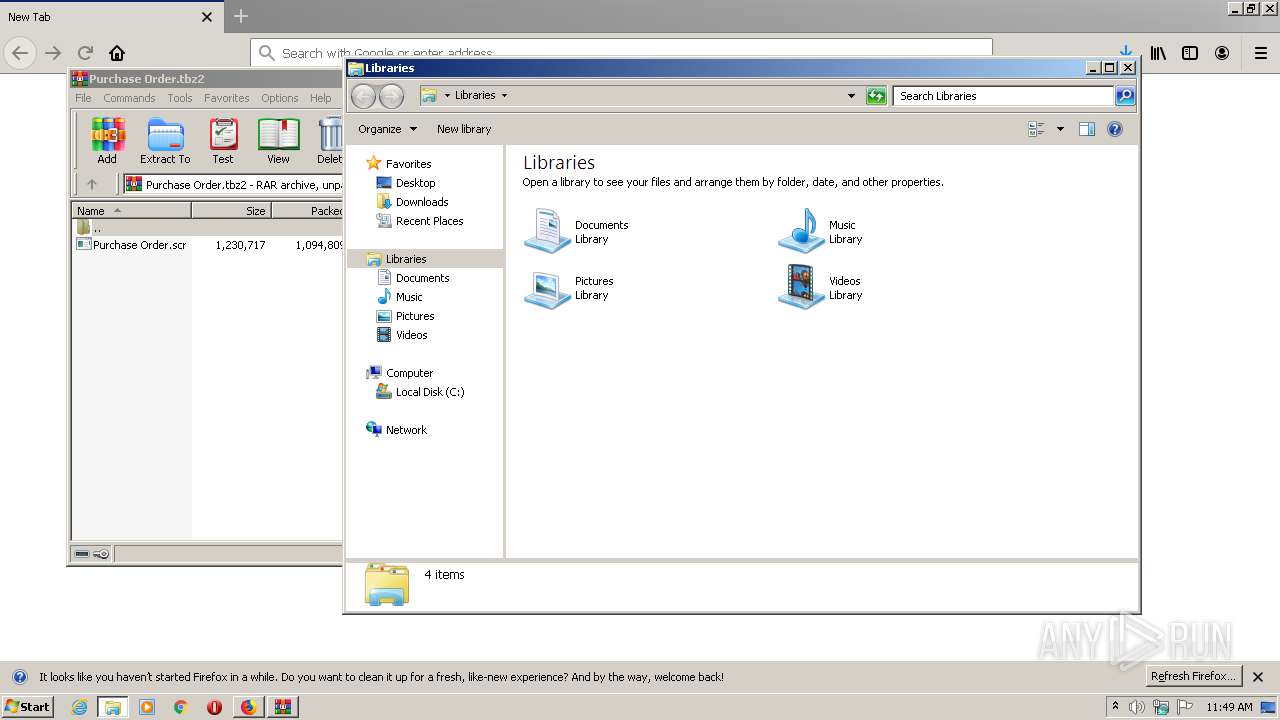
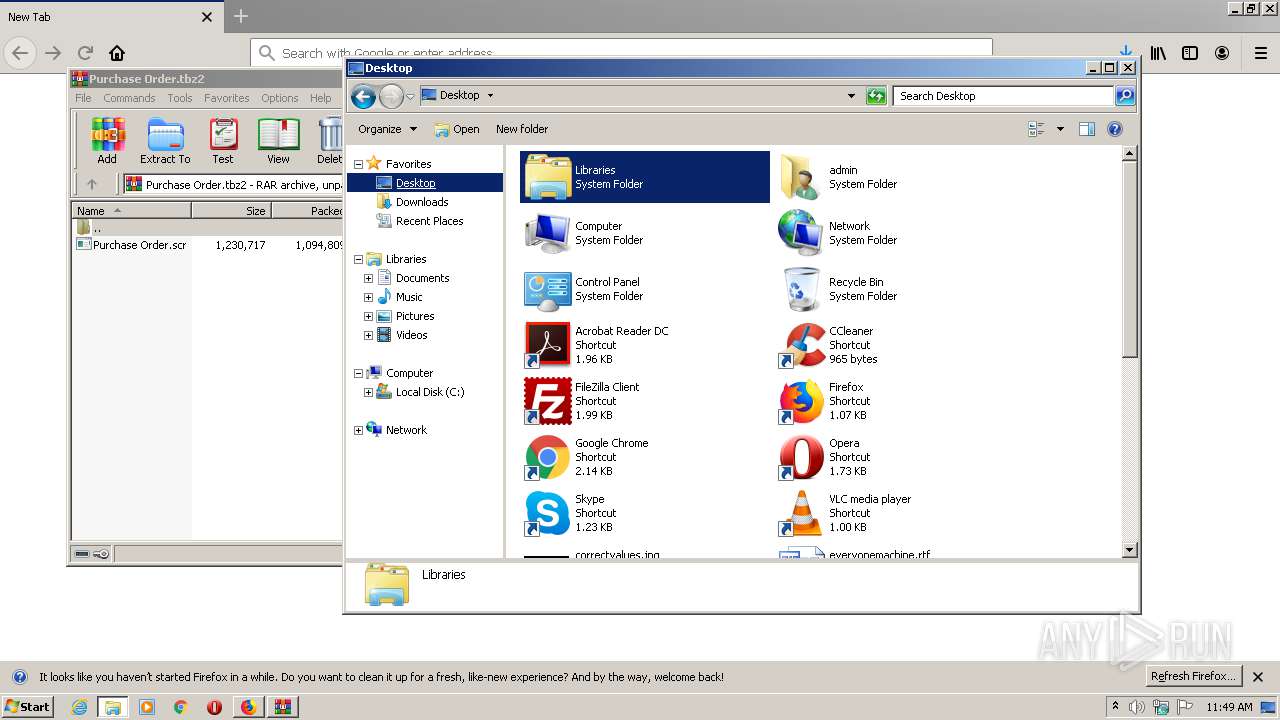
Manual execution by user
- explorer.exe (PID: 2372)
- Purchase Order.scr (PID: 1484)
Creates files in the user directory
- firefox.exe (PID: 1492)
Dropped object may contain Bitcoin addresses
- Purchase Order.scr (PID: 1484)
Reads internet explorer settings
- mshta.exe (PID: 3120)
- mshta.exe (PID: 2488)
- mshta.exe (PID: 4028)
- mshta.exe (PID: 2188)
- mshta.exe (PID: 848)
- mshta.exe (PID: 3740)
- mshta.exe (PID: 3372)
- mshta.exe (PID: 1172)
- mshta.exe (PID: 3332)
- mshta.exe (PID: 2640)
- mshta.exe (PID: 3188)
- mshta.exe (PID: 3344)
- mshta.exe (PID: 2504)
- mshta.exe (PID: 3688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
84
Monitored processes
36
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Users\admin\45564445\qcpdpja.pif" tibblhklv.dog | C:\Users\admin\45564445\qcpdpja.pif | Purchase Order.scr | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Write Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 848 | "C:\Windows\system32\mshta.exe" | C:\Windows\system32\mshta.exe | — | qcpdpja.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 968 | "C:\Users\admin\AppData\Local\Temp\RegSvcs.exe" | C:\Users\admin\AppData\Local\Temp\RegSvcs.exe | qcpdpja.pif | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 1172 | "C:\Windows\system32\mshta.exe" | C:\Windows\system32\mshta.exe | — | qcpdpja.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1196 | chcp 65001 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | "C:\Users\admin\Desktop\Purchase Order.scr" /S | C:\Users\admin\Desktop\Purchase Order.scr | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://www.dropbox.com/s/3qx86k2oabnwnq4/?dl=1 | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1680 | cmd /c ""C:\Users\admin\AppData\Local\Temp\vgAEZQvX1vxi.bat" " | C:\Windows\system32\cmd.exe | — | RegSvcs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1728 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\45564445\run.vbs" | C:\Windows\System32\WScript.exe | — | qcpdpja.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2188 | "C:\Windows\system32\mshta.exe" | C:\Windows\system32\mshta.exe | — | qcpdpja.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
4 166
Read events
3 742
Write events
424
Delete events
0
Modification events
| (PID) Process: | (1492) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 4816F02600000000 | |||
| (PID) Process: | (2744) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 3E16F02600000000 | |||
| (PID) Process: | (1492) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (1492) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1492) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1492) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1492) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1492) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.tbz2\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (2664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
4
Suspicious files
66
Text files
67
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1492 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1492 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 1492 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 1492 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 1492 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\allow-flashallow-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 1492 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\allow-flashallow-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 1492 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 1492 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 1492 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 1492 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
37
DNS requests
80
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1492 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1492 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1492 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1492 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1492 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1492 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1492 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1492 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1492 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1492 | firefox.exe | GET | 200 | 2.16.177.18:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1492 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1492 | firefox.exe | 52.25.145.219:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1492 | firefox.exe | 162.125.66.1:443 | www.dropbox.com | Dropbox, Inc. | DE | shared |
1492 | firefox.exe | 143.204.201.78:443 | snippets.cdn.mozilla.net | — | US | malicious |
1492 | firefox.exe | 143.204.201.119:443 | snippets.cdn.mozilla.net | — | US | suspicious |
1492 | firefox.exe | 162.125.66.15:443 | uc6b8ac875388d26005aacbe0d1d.dl.dropboxusercontent.com | Dropbox, Inc. | DE | malicious |
1492 | firefox.exe | 216.58.207.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1492 | firefox.exe | 172.217.16.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1492 | firefox.exe | 143.204.201.113:443 | tracking-protection.cdn.mozilla.net | — | US | suspicious |
1492 | firefox.exe | 2.16.177.64:443 | shavar.services.mozilla.com | Akamai International B.V. | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dropbox.com |
| shared |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
www.dropbox-dns.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
2248 | RegSvcs.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2248 | RegSvcs.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2248 | RegSvcs.exe | A Network Trojan was detected | REMOTE [PTsecurity] Quasar.RAT IP Lookup |
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
968 | RegSvcs.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
968 | RegSvcs.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
968 | RegSvcs.exe | A Network Trojan was detected | REMOTE [PTsecurity] Quasar.RAT IP Lookup |
2 ETPRO signatures available at the full report