| File name: | d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8 |
| Full analysis: | https://app.any.run/tasks/149247a0-a766-499e-8444-0c88450278be |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | January 10, 2025, 18:59:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 13DCCF3D94C8435353A3BF886CA19E7E |
| SHA1: | 52474B83A6EA7CF75D1D4986B32E26D87B7074EB |
| SHA256: | D15433CCA1E4B6695379317EF0650E4CF9F07FCD5317B8D84343465F3D9186D8 |
| SSDEEP: | 49152:aqC3b2CQOnBQBsaVCmbxIZDSYaKySmMMROFVPAEqG3yfaPJ87bMsoX+OLNtGQEtw:aqHlq0VCmbSAVSK8FZjsCJYMs5OPtGGn |
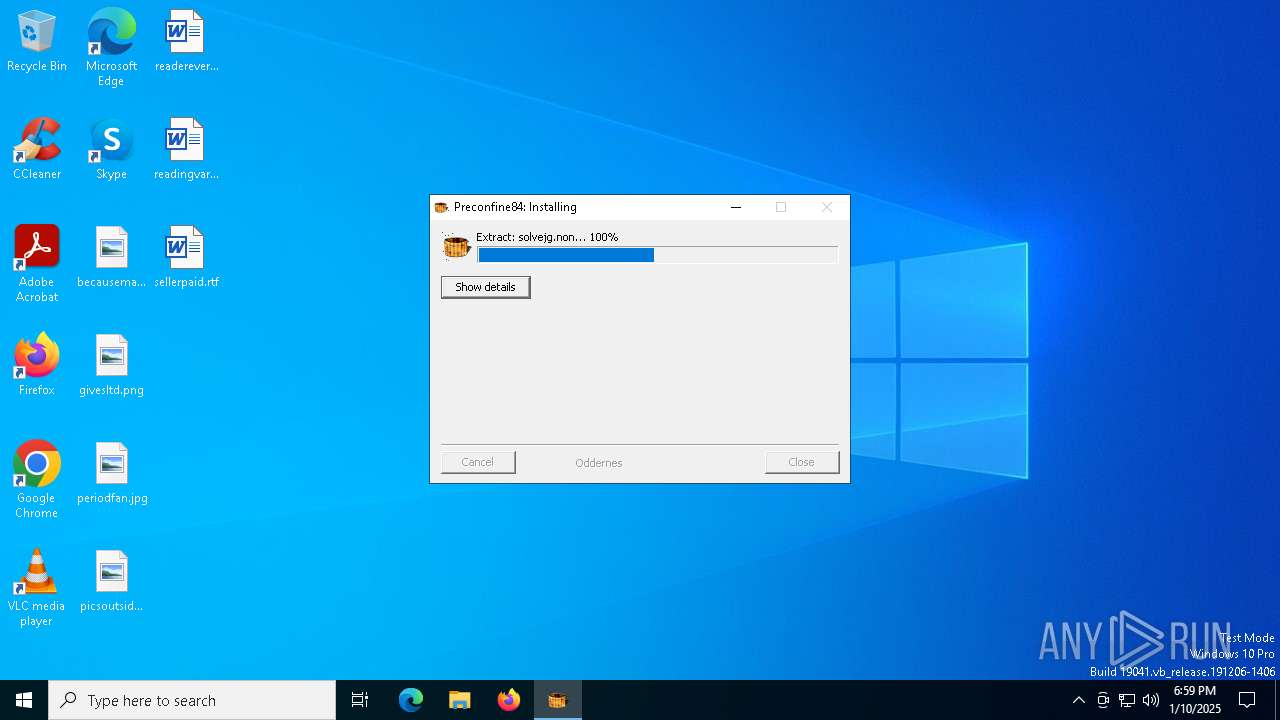
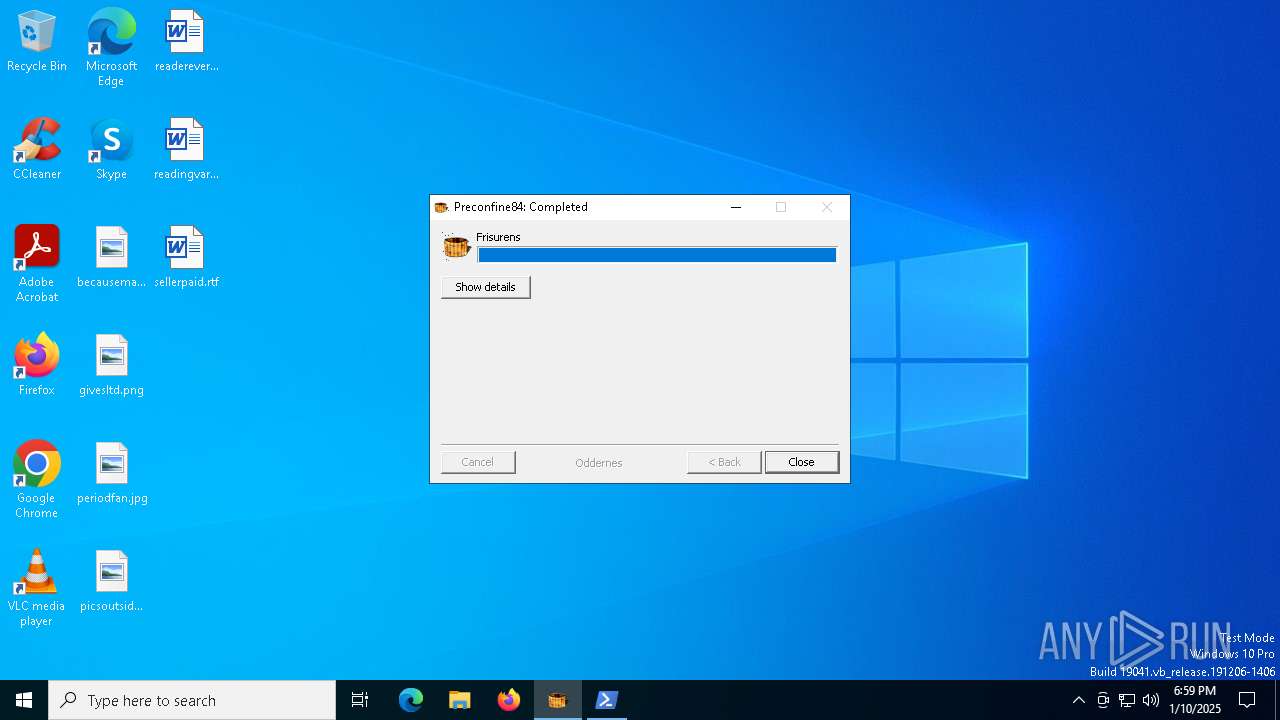
MALICIOUS
GULOADER has been detected
- d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe (PID: 644)
SUSPICIOUS
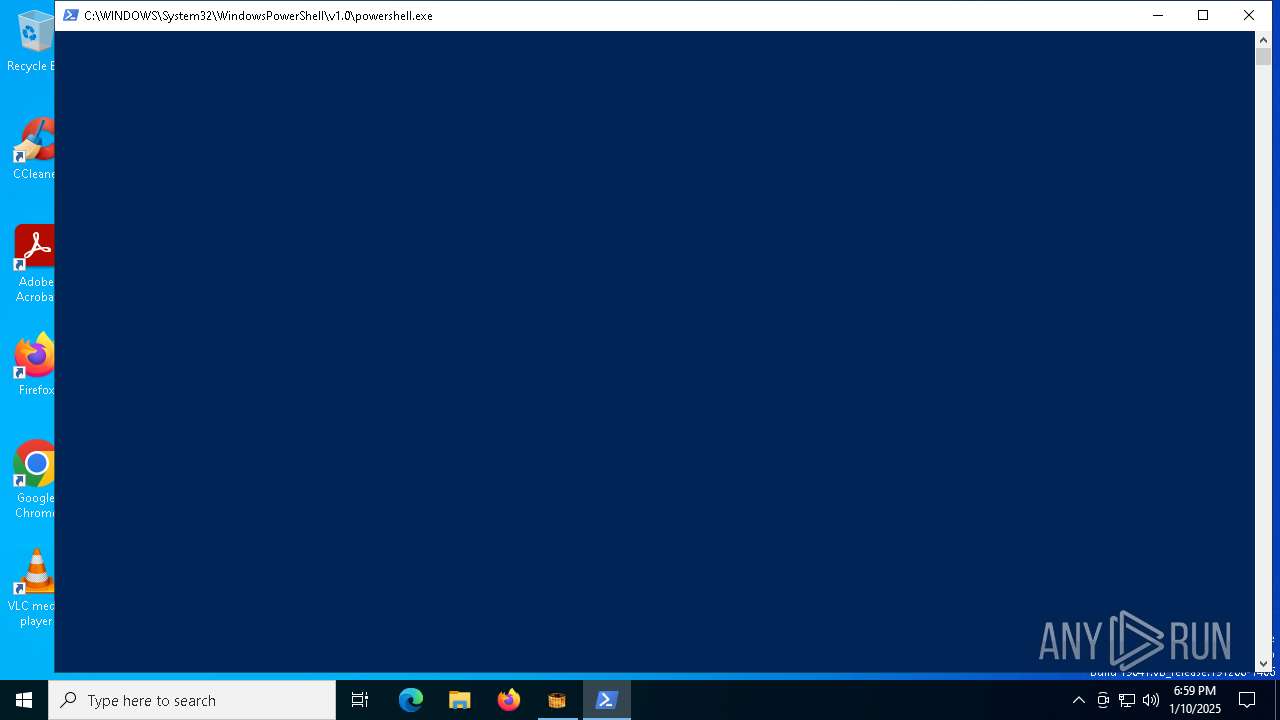
Starts POWERSHELL.EXE for commands execution
- d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe (PID: 644)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 6796)
INFO
Checks supported languages
- d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe (PID: 644)
The sample compiled with english language support
- d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe (PID: 644)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6796)
Reads the computer name
- d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe (PID: 644)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6796)
Creates files or folders in the user directory
- msiexec.exe (PID: 7164)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6796)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6796)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6796)
The process uses the downloaded file
- powershell.exe (PID: 6796)
Checks proxy server information
- msiexec.exe (PID: 7164)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7164)
Reads the software policy settings
- msiexec.exe (PID: 7164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:05:19 23:53:05+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x31dd |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.5.0.0 |
| ProductVersionNumber: | 2.5.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | nonrustic |
| FileDescription: | distruster fejlreaktion |
| InternalName: | hampert.exe |
| OriginalFileName: | hampert.exe |
Total processes
128
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | "C:\Users\admin\AppData\Local\Temp\d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe" | C:\Users\admin\AppData\Local\Temp\d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: distruster fejlreaktion Exit code: 0 Modules
| |||||||||||||||
| 6796 | "powershell.exe" -windowstyle minimized "$Willock=Get-Content -Raw 'C:\Users\admin\AppData\Roaming\Polysulfonate\sangersken\Hjtryks.Tog';$Fysiologen=$Willock.SubString(2860,3);.$Fysiologen($Willock)" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7164 | "C:\WINDOWS\SysWOW64\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 452
Read events
8 449
Write events
3
Delete events
0
Modification events
| (PID) Process: | (7164) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7164) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7164) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
10
Text files
5
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 644 | d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe | C:\Users\admin\AppData\Roaming\Polysulfonate\sangersken\Skolevsens\cloner.hol | binary | |
MD5:E4AC954ED484155B2A165BF00B1E8A4F | SHA256:3078C30C80C29C473A796C4E1FE5F89A175D9B23FC88DBCD0262D93B0C67BEED | |||
| 644 | d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe | C:\Users\admin\AppData\Roaming\Polysulfonate\sangersken\Vara183.Bib | abr | |
MD5:F62EAE8CE9F6C249DC71B48D0D0719B9 | SHA256:BEFC15D7D141B2D2193D73DA595FC799FE704617C134C50F744F666ED24F76AB | |||
| 644 | d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe | C:\Users\admin\AppData\Roaming\Polysulfonate\sangersken\brugerinstallation.cry | abr | |
MD5:77218C2134D28A666F2FDEAA5E452489 | SHA256:A901A3525DC18A4A9E6EF655931252D8258D954D419FCE81668F251C8EF54EE5 | |||
| 644 | d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe | C:\Users\admin\AppData\Roaming\Polysulfonate\sangersken\Hjtryks.Tog | text | |
MD5:A075DC6E560DD3AD9464CC1BB85F9E37 | SHA256:3655D8F8ACA4048B5935D4DE1D1FEA8B89AF57F4B317B4EF9681DCFC5AEF9170 | |||
| 644 | d15433cca1e4b6695379317ef0650e4cf9f07fcd5317b8d84343465f3d9186d8.exe | C:\Users\admin\AppData\Roaming\Polysulfonate\sangersken\Skolevsens\hogni.opd | abr | |
MD5:7586252625434A405256063977B84D0D | SHA256:5AFA5BC29281632F196999E16D8F4B26F2C14EC6A8A5F589DC5932B6DE78A2A7 | |||
| 6796 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_umhoq3ak.ive.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7164 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:D5180223BA059161E0790D5039DD69F1 | SHA256:ECA7748104FD92A153DEAE707860D19EA0F1B6E90FB8D9A1DE0F1C9C421D4C20 | |||
| 7164 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\DDE8B1B7E253A9758EC380BD648952AF_8C0D12F01B5D981AACF8BFC375CA0F2B | binary | |
MD5:CE271484F84D7DBAD46BA8244F2AE216 | SHA256:A6B1D553FFBBEFD66C266B7AB788A6A37201896E8CF77E0D4BD4746CB5482BFF | |||
| 6796 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_libydvml.mnv.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7164 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\05DDC6AA91765AACACDB0A5F96DF8199 | binary | |
MD5:E935BC5762068CAF3E24A2683B1B8A88 | SHA256:A8ACCFCFEB51BD73DF23B91F4D89FF1A9EB7438EF5B12E8AFDA1A6FF1769E89D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
37
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2356 | svchost.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2356 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7088 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7088 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6212 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7164 | msiexec.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2356 | svchost.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2356 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |