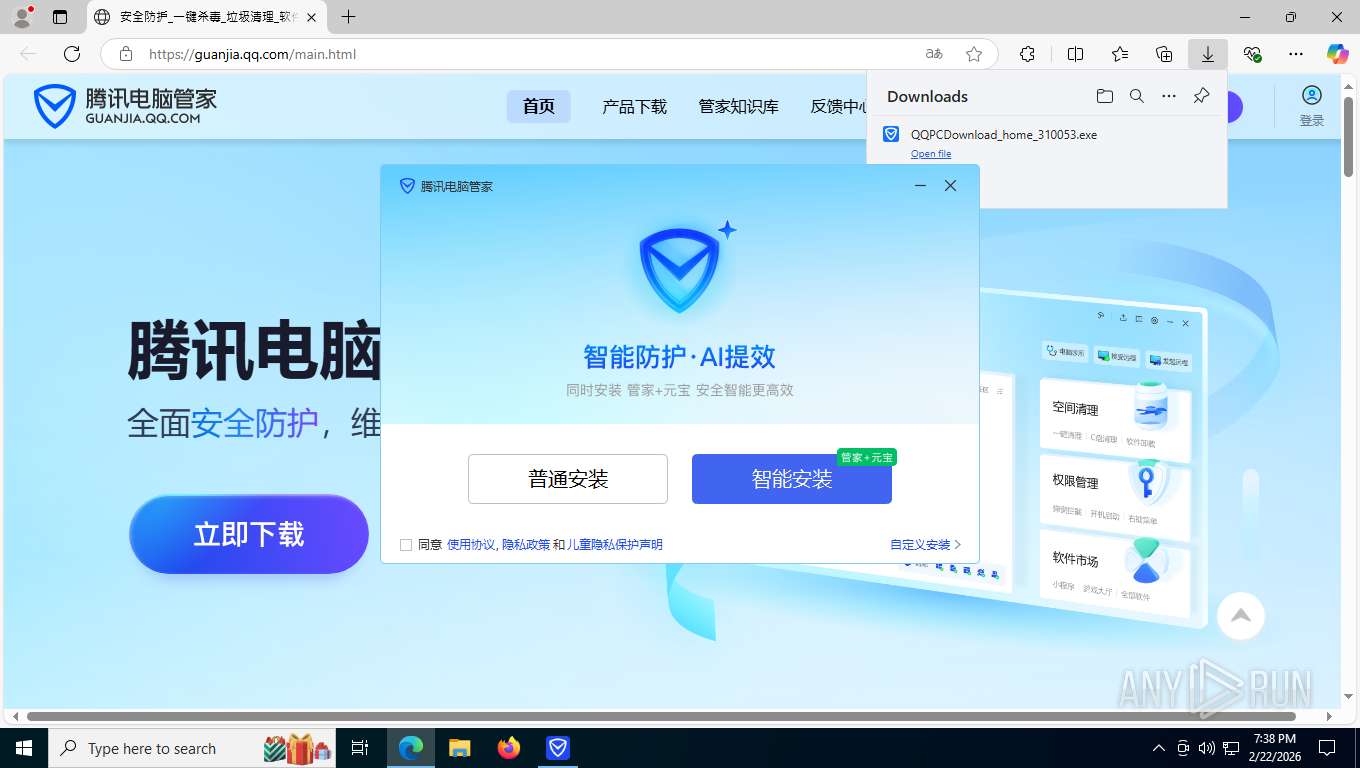
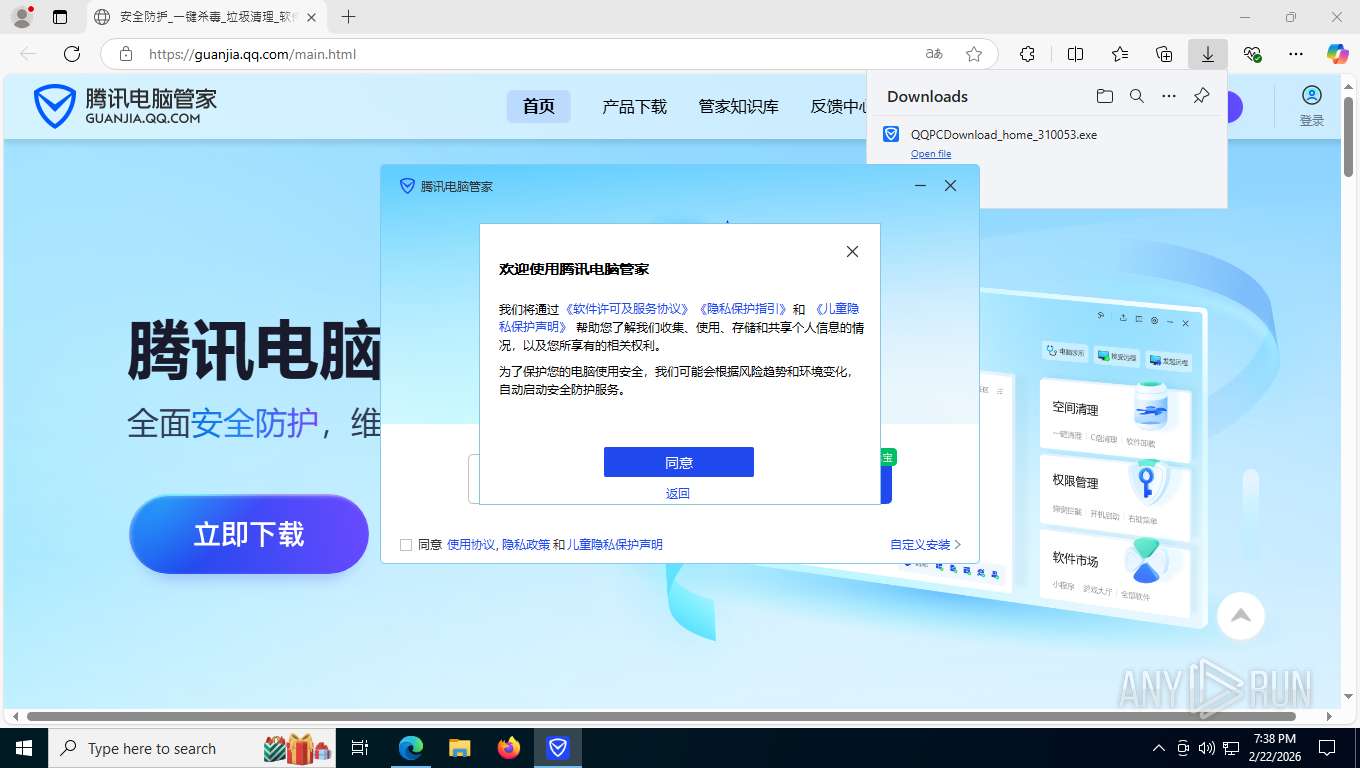
| URL: | https://guanjia.qq.com/main.html |
| Full analysis: | https://app.any.run/tasks/053b844c-75a2-49b6-af50-ffa27169e43d |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | February 23, 2026, 00:38:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BB41AC1106D4F63AF977808F7D585C4C |
| SHA1: | 7A2302E50E7C8D5AE031EAEDBB0B356DDFC3EFF0 |
| SHA256: | D0E662CF7132286023F4FF534608D77DE6BD01A3B24D84F1934850707A3BECC6 |
| SSDEEP: | 3:N8xsN6ZIJ:2M6Z0 |
MALICIOUS
Changes the autorun value in the registry
- QQPCMgr_Setup.exe (PID: 8536)
- QQPCRTP.exe (PID: 8828)
Registers / Runs the DLL via REGSVR32.EXE
- QQPCMgr_Setup.exe (PID: 8536)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
Application was injected by another process
- explorer.exe (PID: 4972)
Runs injected code in another process
- InjectHostExe64.exe (PID: 1368)
- InjectHostExe64.exe (PID: 6000)
- TrayRocketInjectHelper64.exe (PID: 8344)
Loads dropped or rewritten executable
- conhost.exe (PID: 3004)
- conhost.exe (PID: 9508)
- WmiPrvSE.exe (PID: 9896)
- WeChatOCR.exe (PID: 9976)
- WeChatOCR.exe (PID: 10072)
- WeChatOCR.exe (PID: 10100)
- WeChatOCR.exe (PID: 10092)
- TSVulFixInc64.exe (PID: 10196)
- consent.exe (PID: 10648)
- Taskmgr.exe (PID: 10704)
- regsvr32.exe (PID: 6600)
- conhost.exe (PID: 10416)
- CompatTelRunner.exe (PID: 10352)
- TSVulFixInc64.exe (PID: 9688)
- TSVulFixInc64.exe (PID: 9312)
Actions looks like stealing of personal data
- QQPCTray.exe (PID: 4948)
- QMGarbageAutoClean.exe (PID: 10544)
XORed URL has been found (YARA)
- QQPCRTP.exe (PID: 8828)
- QMDL.exe (PID: 6020)
DCRAT has been detected (YARA)
- QQPCRTP.exe (PID: 8828)
GCLEANER has been detected (YARA)
- QQPCRTP.exe (PID: 8828)
COBALTSTRIKE has been detected (YARA)
- QQPCRTP.exe (PID: 8828)
AHK has been detected (YARA)
- QQPCRTP.exe (PID: 8828)
CVE-2022-30190 detected
- QQPCRTP.exe (PID: 8828)
Steals credentials from Web Browsers
- QMGarbageAutoClean.exe (PID: 10544)
Changes settings of System certificates
- QMSignScan.exe (PID: 9304)
SUSPICIOUS
Executable content was dropped or overwritten
- QQPCDownload_home_310053.exe (PID: 1984)
- QQPCDownload_home_310053.exe (PID: 1944)
- yuanbao_10072_x64.exe (PID: 7408)
- QQPCMgr_Setup.exe (PID: 8536)
- svchost.exe (PID: 7092)
- QQPCTray.exe (PID: 4948)
- QQPCRTP.exe (PID: 8828)
- qmbinsx64.exe (PID: 5516)
- TpkUpdate.exe (PID: 9352)
- QMDL.exe (PID: 6020)
- QMDynamicPackageSetup_17.11.28973.206__1764299558601.exe (PID: 11032)
- QMSoftMgrSetup_17.12.29269.301__1770301803198.exe (PID: 11144)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
- 25814.exe (PID: 3700)
The process verifies whether the antivirus software is installed
- QQPCDownload_home_310053.exe (PID: 1944)
- QQPCMgr_Setup.exe (PID: 8536)
- cacls.exe (PID: 8312)
- QQPCSoftCmd.exe (PID: 8504)
- QQPCRTP.exe (PID: 4544)
- 25814.exe (PID: 6304)
- 25814.exe (PID: 3700)
- regsvr32.exe (PID: 8052)
- regsvr32.exe (PID: 8140)
- regsvr32.exe (PID: 8892)
- explorer.exe (PID: 4972)
- QQPCRTP.exe (PID: 8408)
- QQPCRTP.exe (PID: 7976)
- QQPCRTP.exe (PID: 8828)
- QQPCSoftCmd.exe (PID: 1176)
- QQPCTray.exe (PID: 4948)
- QQPCTray.exe (PID: 8864)
- UpdateTrayIcon.exe (PID: 8916)
- InjectHostExe64.exe (PID: 1368)
- InjectHostExe64.exe (PID: 6000)
- QMDL.exe (PID: 6020)
- VolSnapshotX64.exe (PID: 3716)
- QMHwDrX64.exe (PID: 8264)
- TrayRocketInjectHelper64.exe (PID: 8344)
- qmbinsx64.exe (PID: 5516)
- qmbsrv.exe (PID: 5888)
- QQPCMgrUpdate.exe (PID: 7340)
- QQPCPatch.exe (PID: 4728)
- QQPCUpdateAVLib.exe (PID: 9956)
- QQPCSoftCmd.exe (PID: 10008)
- WeChatOCR.exe (PID: 9976)
- WeChatOCR.exe (PID: 10072)
- WeChatOCR.exe (PID: 10092)
- WeChatOCR.exe (PID: 10100)
- QMCheckNetwork.exe (PID: 10156)
- TSVulFixInc64.exe (PID: 10196)
- TpkUpdate.exe (PID: 9352)
- QMCheckNetwork.exe (PID: 10220)
- QQPCMgrUpdate.exe (PID: 9584)
- QQPCMgrUpdate.exe (PID: 10252)
- QQPCMgrUpdate.exe (PID: 10464)
- QMDynamicPackageSetup_17.11.28973.206__1764299558601.exe (PID: 11032)
- QQPCTray.exe (PID: 10864)
- Taskmgr.exe (PID: 10704)
- QMSoftMgrSetup_17.12.29269.301__1770301803198.exe (PID: 11144)
- QQPCPatch.exe (PID: 2392)
- QMGarbageAutoClean.exe (PID: 10544)
- QQPCPatch.exe (PID: 9284)
- QMLspPing.exe (PID: 9560)
- QMSignScan.exe (PID: 9304)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
- regsvr32.exe (PID: 10520)
- regsvr32.exe (PID: 10096)
- regsvr32.exe (PID: 6600)
- FileSmashPro.exe (PID: 10136)
- QQPCLeakScan.exe (PID: 11172)
- TSVulFixInc64.exe (PID: 9688)
- TSVulFixInc64.exe (PID: 9312)
The process creates files with name similar to system file names
- yuanbao_10072_x64.exe (PID: 7408)
- QQPCMgr_Setup.exe (PID: 8536)
- QMDynamicPackageSetup_17.11.28973.206__1764299558601.exe (PID: 11032)
- QMSoftMgrSetup_17.12.29269.301__1770301803198.exe (PID: 11144)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
Malware-specific behavior (creating "System.dll" in Temp)
- yuanbao_10072_x64.exe (PID: 7408)
- QMDynamicPackageSetup_17.11.28973.206__1764299558601.exe (PID: 11032)
- QMSoftMgrSetup_17.12.29269.301__1770301803198.exe (PID: 11144)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 7940)
- cmd.exe (PID: 8404)
- cmd.exe (PID: 2096)
- QQPCMgr_Setup.exe (PID: 8536)
- QMDL.exe (PID: 6020)
The process drops C-runtime libraries
- QQPCMgr_Setup.exe (PID: 8536)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
Searches for installed software
- QQPCMgr_Setup.exe (PID: 8536)
- svchost.exe (PID: 7092)
- QQPCRTP.exe (PID: 8828)
- QQPCTray.exe (PID: 4948)
- QMGarbageAutoClean.exe (PID: 10544)
- CompatTelRunner.exe (PID: 10352)
Starts CMD.EXE for commands execution
- QQPCMgr_Setup.exe (PID: 8536)
Drops 7-zip archiver for unpacking
- QQPCMgr_Setup.exe (PID: 8536)
Drops a system driver (possible attempt to evade defenses)
- QQPCMgr_Setup.exe (PID: 8536)
- QQPCTray.exe (PID: 4948)
- qmbinsx64.exe (PID: 5516)
Creates or modifies Windows services
- QQPCMgr_Setup.exe (PID: 8536)
- QQPCRTP.exe (PID: 8828)
- QQPCTray.exe (PID: 4948)
Creates files in the driver directory
- QQPCMgr_Setup.exe (PID: 8536)
- QQPCTray.exe (PID: 4948)
- qmbinsx64.exe (PID: 5516)
Starts application with an unusual extension
- cmd.exe (PID: 7412)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 7412)
Executes as Windows Service
- 25814.exe (PID: 3700)
- QQPCRTP.exe (PID: 8828)
- VSSVC.exe (PID: 5588)
- qmbsrv.exe (PID: 5888)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 8052)
- regsvr32.exe (PID: 8140)
- regsvr32.exe (PID: 8892)
- regsvr32.exe (PID: 10520)
- regsvr32.exe (PID: 6600)
Creates file in the systems drive root
- QQPCSoftCmd.exe (PID: 1176)
- QQPCSoftCmd.exe (PID: 10008)
Reads the date of Windows installation
- QQPCSoftCmd.exe (PID: 1176)
- QQPCSoftCmd.exe (PID: 10008)
- QQPCTray.exe (PID: 4948)
Reads the BIOS version
- QQPCSoftCmd.exe (PID: 1176)
Possible stealing of FTP data
- QQPCRTP.exe (PID: 8828)
- QQPCTray.exe (PID: 4948)
Reads Microsoft Outlook installation path
- QQPCTray.exe (PID: 4948)
The process checks if it is being run in the virtual environment
- QQPCSoftCmd.exe (PID: 1176)
- QQPCSoftCmd.exe (PID: 10008)
Application launched itself
- QMCheckNetwork.exe (PID: 10156)
- QQPCMgrUpdate.exe (PID: 7340)
- QQPCMgrUpdate.exe (PID: 9584)
- QQPCTray.exe (PID: 4948)
There is functionality for communication over UDP network (YARA)
- QQPCRTP.exe (PID: 8828)
Possible stealing of messenger data
- QMGarbageAutoClean.exe (PID: 10544)
Possible stealing of email data
- QMGarbageAutoClean.exe (PID: 10544)
Adds/modifies Windows certificates
- QMSignScan.exe (PID: 9304)
INFO
Application launched itself
- msedge.exe (PID: 8108)
Drops script file
- msedge.exe (PID: 8108)
- QQPCMgr_Setup.exe (PID: 8536)
- QQPCTray.exe (PID: 4948)
- WmiPrvSE.exe (PID: 9896)
- QMGarbageAutoClean.exe (PID: 10544)
- QMSignScan.exe (PID: 9304)
Reads the computer name
- identity_helper.exe (PID: 3212)
- QQPCDownload_home_310053.exe (PID: 1944)
- report_helper.exe (PID: 2872)
- report_helper.exe (PID: 8360)
- report_helper.exe (PID: 524)
- yuanbao_10072_x64.exe (PID: 7408)
- report_helper.exe (PID: 8180)
- QQPCMgr_Setup.exe (PID: 8536)
- report_helper.exe (PID: 7376)
- QQPCSoftCmd.exe (PID: 8504)
- QQPCRTP.exe (PID: 4544)
- 25814.exe (PID: 6304)
- 25814.exe (PID: 3700)
- QQPCRTP.exe (PID: 8408)
- QQPCRTP.exe (PID: 7976)
- QQPCRTP.exe (PID: 8828)
- QQPCSoftCmd.exe (PID: 1176)
- UpdateTrayIcon64.exe (PID: 5588)
- QQPCTray.exe (PID: 8864)
- QQPCTray.exe (PID: 4948)
- QMDL.exe (PID: 6020)
- QMHwDrX64.exe (PID: 8264)
- VolSnapshotX64.exe (PID: 3716)
- TrayRocketInjectHelper64.exe (PID: 8344)
- qmbinsx64.exe (PID: 5516)
- qmbsrv.exe (PID: 5888)
- QQPCMgrUpdate.exe (PID: 7340)
- QQPCPatch.exe (PID: 4728)
- QQPCUpdateAVLib.exe (PID: 9956)
- QQPCSoftCmd.exe (PID: 10008)
- QMCheckNetwork.exe (PID: 10156)
- QMCheckNetwork.exe (PID: 10220)
- TSVulFixInc64.exe (PID: 10196)
- QQPCMgrUpdate.exe (PID: 9584)
- TpkUpdate.exe (PID: 9352)
- QQPCMgrUpdate.exe (PID: 10252)
- QQPCMgrUpdate.exe (PID: 10464)
- QQPCTray.exe (PID: 10864)
- QQPCPatch.exe (PID: 2392)
- QQPCPatch.exe (PID: 9284)
- QMGarbageAutoClean.exe (PID: 10544)
- QMLspPing.exe (PID: 9560)
- QMSignScan.exe (PID: 9304)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
- FileSmashPro.exe (PID: 10136)
- QQPCLeakScan.exe (PID: 11172)
- TSVulFixInc64.exe (PID: 9688)
- TSVulFixInc64.exe (PID: 9312)
Reads Environment values
- identity_helper.exe (PID: 3212)
- QQPCSoftCmd.exe (PID: 1176)
- QQPCSoftCmd.exe (PID: 10008)
- TSVulFixInc64.exe (PID: 9688)
- TSVulFixInc64.exe (PID: 9312)
Checks supported languages
- identity_helper.exe (PID: 3212)
- yuanbao_10072_x64.exe (PID: 7408)
- QQPCDownload_home_310053.exe (PID: 1944)
- QQPCDownload_home_310053.exe (PID: 1984)
- report_helper.exe (PID: 8360)
- report_helper.exe (PID: 8180)
- report_helper.exe (PID: 2872)
- report_helper.exe (PID: 524)
- report_helper.exe (PID: 7376)
- QQPCMgr_Setup.exe (PID: 8536)
- QQPCSoftCmd.exe (PID: 8504)
- QQPCRTP.exe (PID: 4544)
- chcp.com (PID: 4284)
- 25814.exe (PID: 6304)
- 25814.exe (PID: 3700)
- QQPCRTP.exe (PID: 8408)
- QQPCRTP.exe (PID: 7976)
- QQPCRTP.exe (PID: 8828)
- QQPCSoftCmd.exe (PID: 1176)
- QQPCTray.exe (PID: 4948)
- QQPCTray.exe (PID: 8864)
- UpdateTrayIcon.exe (PID: 8916)
- UpdateTrayIcon64.exe (PID: 5588)
- InjectHostExe64.exe (PID: 6000)
- InjectHostExe64.exe (PID: 1368)
- QMDL.exe (PID: 6020)
- VolSnapshotX64.exe (PID: 3716)
- QMHwDrX64.exe (PID: 8264)
- TrayRocketInjectHelper64.exe (PID: 8344)
- qmbinsx64.exe (PID: 5516)
- qmbsrv.exe (PID: 5888)
- QQPCMgrUpdate.exe (PID: 7340)
- QQPCPatch.exe (PID: 4728)
- QQPCUpdateAVLib.exe (PID: 9956)
- QQPCSoftCmd.exe (PID: 10008)
- WeChatOCR.exe (PID: 9976)
- QMCheckNetwork.exe (PID: 10220)
- TSVulFixInc64.exe (PID: 10196)
- QMCheckNetwork.exe (PID: 10156)
- TpkUpdate.exe (PID: 9352)
- QQPCMgrUpdate.exe (PID: 9584)
- QQPCMgrUpdate.exe (PID: 10252)
- QQPCMgrUpdate.exe (PID: 10464)
- QQPCTray.exe (PID: 10864)
- QMDynamicPackageSetup_17.11.28973.206__1764299558601.exe (PID: 11032)
- QMSoftMgrSetup_17.12.29269.301__1770301803198.exe (PID: 11144)
- QQPCPatch.exe (PID: 2392)
- QQPCPatch.exe (PID: 9284)
- QMGarbageAutoClean.exe (PID: 10544)
- QMLspPing.exe (PID: 9560)
- QMSignScan.exe (PID: 9304)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
- FileSmashPro.exe (PID: 10136)
- QQPCLeakScan.exe (PID: 11172)
- TSVulFixInc64.exe (PID: 9688)
- TSVulFixInc64.exe (PID: 9312)
The sample compiled with chinese language support
- msedge.exe (PID: 3352)
- msedge.exe (PID: 8108)
- QQPCDownload_home_310053.exe (PID: 1944)
- QQPCDownload_home_310053.exe (PID: 1984)
- yuanbao_10072_x64.exe (PID: 7408)
- QQPCMgr_Setup.exe (PID: 8536)
- svchost.exe (PID: 7092)
- QQPCTray.exe (PID: 4948)
- qmbinsx64.exe (PID: 5516)
- QMDL.exe (PID: 6020)
- TpkUpdate.exe (PID: 9352)
- QMDynamicPackageSetup_17.11.28973.206__1764299558601.exe (PID: 11032)
- QMSoftMgrSetup_17.12.29269.301__1770301803198.exe (PID: 11144)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
Launching a file from the Downloads directory
- msedge.exe (PID: 8108)
Create files in a temporary directory
- QQPCDownload_home_310053.exe (PID: 1944)
- QQPCDownload_home_310053.exe (PID: 1984)
- yuanbao_10072_x64.exe (PID: 7408)
- QQPCMgr_Setup.exe (PID: 8536)
- UpdateTrayIcon.exe (PID: 8916)
- UpdateTrayIcon64.exe (PID: 5588)
- QQPCRTP.exe (PID: 8828)
- QMDL.exe (PID: 6020)
- QQPCTray.exe (PID: 4948)
- QMDynamicPackageSetup_17.11.28973.206__1764299558601.exe (PID: 11032)
- QMSoftMgrSetup_17.12.29269.301__1770301803198.exe (PID: 11144)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
Executable content was dropped or overwritten
- msedge.exe (PID: 8108)
- msedge.exe (PID: 3352)
Creates files or folders in the user directory
- QQPCDownload_home_310053.exe (PID: 1944)
- yuanbao_10072_x64.exe (PID: 7408)
- QQPCMgr_Setup.exe (PID: 8536)
- 25814.exe (PID: 6304)
- explorer.exe (PID: 4972)
- QQPCTray.exe (PID: 4948)
- QMDL.exe (PID: 6020)
- QQPCSoftCmd.exe (PID: 10008)
- QQPCMgrUpdate.exe (PID: 10252)
- QMSignScan.exe (PID: 9304)
Creates files in the program directory
- QQPCDownload_home_310053.exe (PID: 1944)
- MoUsoCoreWorker.exe (PID: 6768)
- QQPCMgr_Setup.exe (PID: 8536)
- QQPCSoftCmd.exe (PID: 8504)
- 25814.exe (PID: 3700)
- QQPCRTP.exe (PID: 8828)
- QQPCSoftCmd.exe (PID: 1176)
- QQPCTray.exe (PID: 4948)
- QMDL.exe (PID: 6020)
- qmbinsx64.exe (PID: 5516)
- QQPCMgrUpdate.exe (PID: 7340)
- QQPCUpdateAVLib.exe (PID: 9956)
- TpkUpdate.exe (PID: 9352)
- QQPCMgrUpdate.exe (PID: 10252)
- QMDynamicPackageSetup_17.11.28973.206__1764299558601.exe (PID: 11032)
- QMSoftMgrSetup_17.12.29269.301__1770301803198.exe (PID: 11144)
- QMGarbageAutoClean.exe (PID: 10544)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
- QQPCLeakScan.exe (PID: 11172)
Reads the machine GUID from the registry
- QQPCDownload_home_310053.exe (PID: 1944)
- yuanbao_10072_x64.exe (PID: 7408)
- QQPCMgr_Setup.exe (PID: 8536)
- 25814.exe (PID: 6304)
- 25814.exe (PID: 3700)
- QQPCSoftCmd.exe (PID: 1176)
- QQPCTray.exe (PID: 4948)
- QQPCRTP.exe (PID: 8828)
- QMDL.exe (PID: 6020)
- QQPCMgrUpdate.exe (PID: 7340)
- QQPCSoftCmd.exe (PID: 10008)
- QMCheckNetwork.exe (PID: 10220)
- TpkUpdate.exe (PID: 9352)
- QQPCMgrUpdate.exe (PID: 9584)
- QQPCMgrUpdate.exe (PID: 10252)
- QQPCTray.exe (PID: 10864)
- QMGarbageAutoClean.exe (PID: 10544)
- QMSignScan.exe (PID: 9304)
- QQPCLeakScan.exe (PID: 11172)
Checks proxy server information
- yuanbao_10072_x64.exe (PID: 7408)
- slui.exe (PID: 3004)
- QQPCMgr_Setup.exe (PID: 8536)
- QMDL.exe (PID: 6020)
- QQPCTray.exe (PID: 4948)
- QQPCSoftCmd.exe (PID: 10008)
- QQPCMgrUpdate.exe (PID: 10252)
- QMSignScan.exe (PID: 9304)
Reads security settings of Internet Explorer
- yuanbao_10072_x64.exe (PID: 7408)
- QQPCMgr_Setup.exe (PID: 8536)
- QQPCSoftCmd.exe (PID: 1176)
- QQPCTray.exe (PID: 4948)
- QMDL.exe (PID: 6020)
- WmiPrvSE.exe (PID: 9896)
- QQPCSoftCmd.exe (PID: 10008)
- QQPCMgrUpdate.exe (PID: 9584)
- QQPCMgrUpdate.exe (PID: 10252)
- explorer.exe (PID: 4972)
- Taskmgr.exe (PID: 10704)
- QMSignScan.exe (PID: 9304)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
The sample compiled with english language support
- yuanbao_10072_x64.exe (PID: 7408)
- QQPCMgr_Setup.exe (PID: 8536)
- QQPCTray.exe (PID: 4948)
- QQPCRTP.exe (PID: 8828)
- svchost.exe (PID: 7092)
- QMDynamicPackageSetup_17.11.28973.206__1764299558601.exe (PID: 11032)
- QMSoftMgrSetup_17.12.29269.301__1770301803198.exe (PID: 11144)
- QMFileSmashProSetup_17.11.28973.206__1764299558601.exe (PID: 10584)
- 25814.exe (PID: 3700)
Creating file in SysWOW64
- QQPCMgr_Setup.exe (PID: 8536)
There is functionality for taking screenshot (YARA)
- QQPCDownload_home_310053.exe (PID: 1944)
- 25814.exe (PID: 3700)
- QQPCRTP.exe (PID: 8828)
- QQPCSoftCmd.exe (PID: 1176)
- QQPCTray.exe (PID: 4948)
Creates a software uninstall entry
- QQPCMgr_Setup.exe (PID: 8536)
Launching a file from a Registry key
- QQPCMgr_Setup.exe (PID: 8536)
- QQPCRTP.exe (PID: 8828)
Changes the display of characters in the console
- cmd.exe (PID: 7412)
Reads product name
- QQPCSoftCmd.exe (PID: 1176)
- QQPCSoftCmd.exe (PID: 10008)
Reads Windows Product ID
- QQPCSoftCmd.exe (PID: 1176)
Process checks whether UAC notifications are on
- QQPCTray.exe (PID: 4948)
Reads CPU info
- QMHwDrX64.exe (PID: 8264)
- QQPCTray.exe (PID: 4948)
- qmbsrv.exe (PID: 5888)
Reads the time zone
- QQPCTray.exe (PID: 4948)
- qmbsrv.exe (PID: 5888)
- WmiPrvSE.exe (PID: 9896)
SMARTFTP has been detected
- QQPCRTP.exe (PID: 8828)
- QQPCTray.exe (PID: 4948)
TeamViewer related mutex has been found
- QQPCSoftCmd.exe (PID: 1176)
- QQPCSoftCmd.exe (PID: 10008)
ANYVIEWER has been detected
- QQPCRTP.exe (PID: 8828)
- QQPCTray.exe (PID: 4948)
TODESK has been detected
- QQPCRTP.exe (PID: 8828)
- QQPCTray.exe (PID: 4948)
Disables trace logs
- QQPCTray.exe (PID: 4948)
Process checks computer location settings
- QMDL.exe (PID: 6020)
- QQPCMgrUpdate.exe (PID: 9584)
- QQPCTray.exe (PID: 4948)
Loads dropped or rewritten executable
- msedge.exe (PID: 10276)
- msedge.exe (PID: 5260)
- msedge.exe (PID: 5680)
- msedge.exe (PID: 10204)
- msedge.exe (PID: 1904)
- msedge.exe (PID: 10056)
- msedge.exe (PID: 10232)
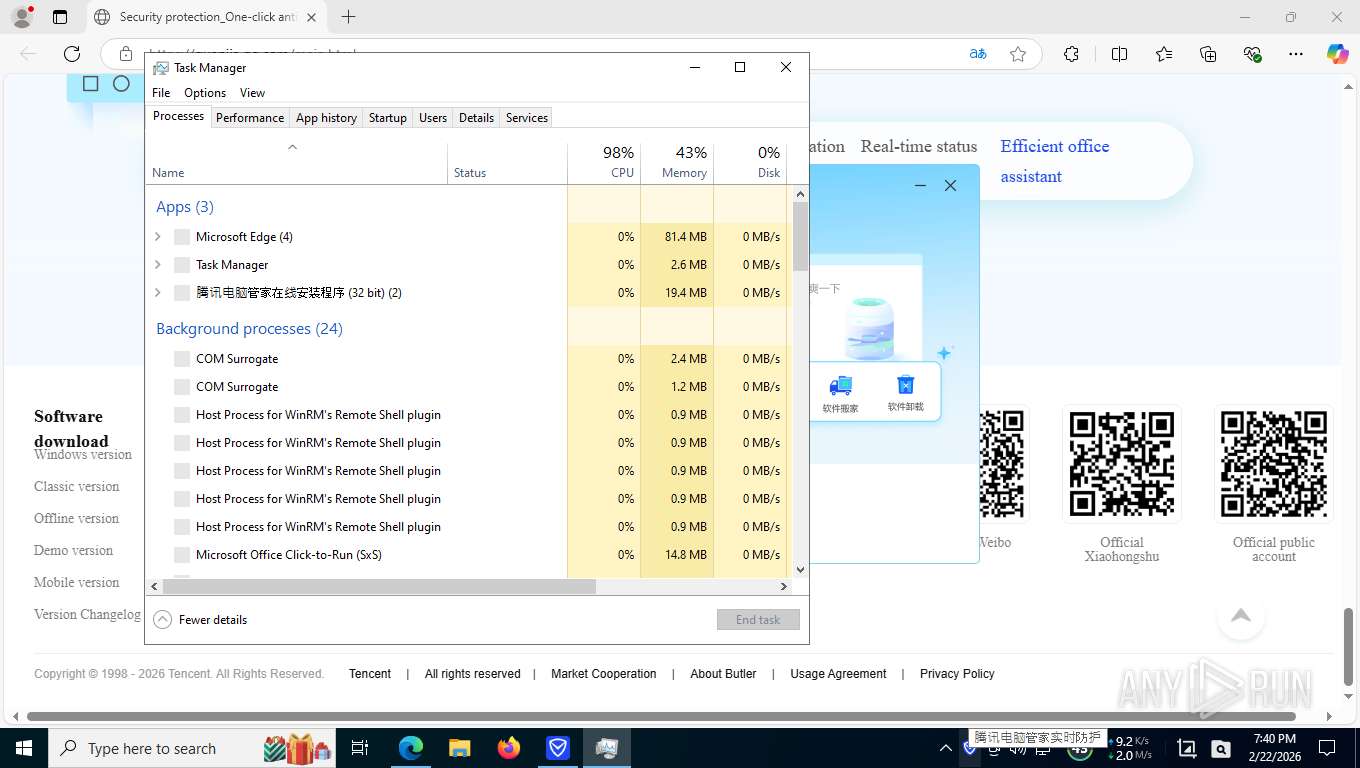
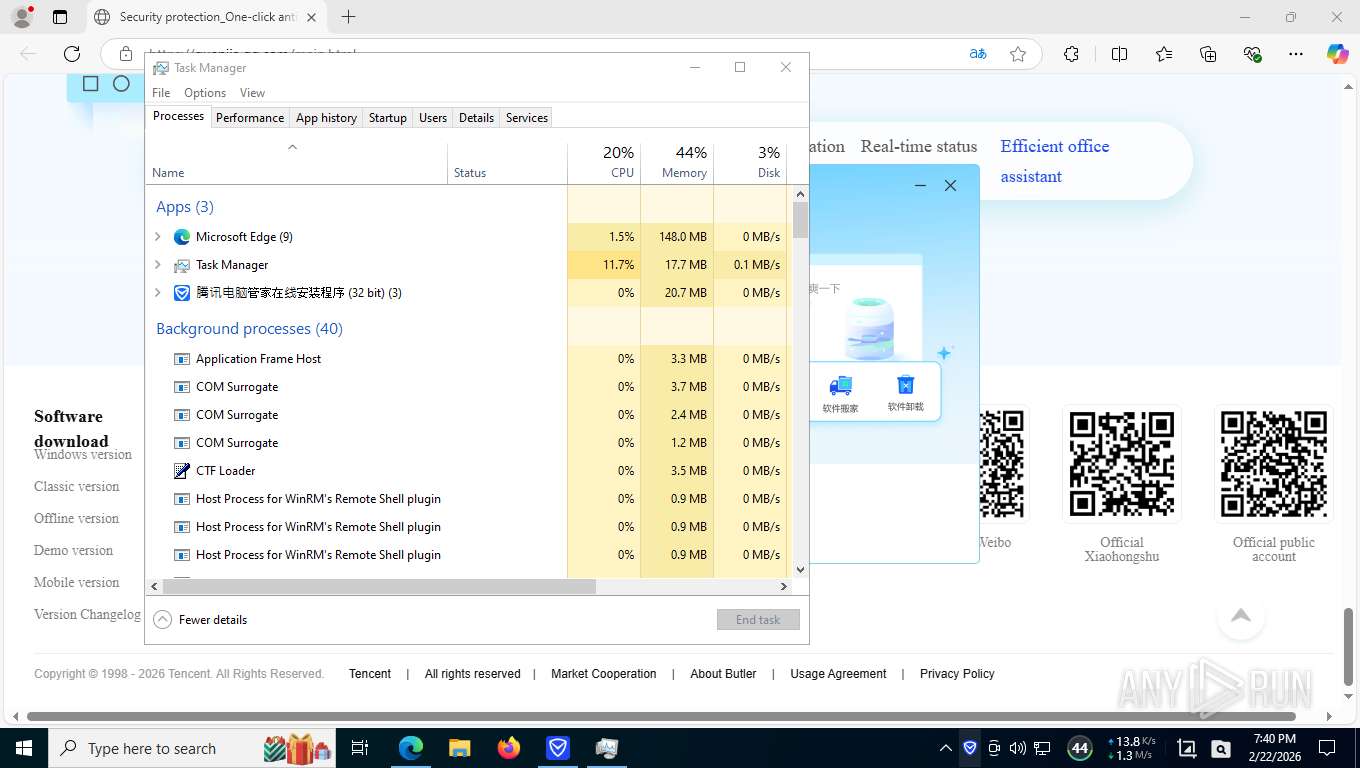
Manual execution by a user
- Taskmgr.exe (PID: 10508)
- Taskmgr.exe (PID: 10704)
Found Base64 encoded access to Marshal class via PowerShell (YARA)
- QQPCRTP.exe (PID: 8828)
Found Base64 encoded text manipulation via PowerShell (YARA)
- QQPCRTP.exe (PID: 8828)
Found Base64 encoded reference to WMI classes (YARA)
- QQPCRTP.exe (PID: 8828)
Found Base64 encoded network access via PowerShell (YARA)
- QQPCRTP.exe (PID: 8828)
Detects AutoHotkey samples (YARA)
- QQPCRTP.exe (PID: 8828)
VMProtect protector has been detected
- QQPCRTP.exe (PID: 8828)
UPX packer has been detected
- QQPCRTP.exe (PID: 8828)
PyInstaller has been detected (YARA)
- QQPCRTP.exe (PID: 8828)
Detects InnoSetup installer (YARA)
- QQPCRTP.exe (PID: 8828)
Drops encrypted JS script (Microsoft Script Encoder)
- QMGarbageAutoClean.exe (PID: 10544)
TEAMVIEWER has been detected
- QMGarbageAutoClean.exe (PID: 10544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(8828) QQPCRTP.exe
Decrypted-URLs (268)http://192.157.198.ui
http://205.209.169.ur
http://591ani.cn/html.htm
http://66lguet98.tuco-sala
http://80awufhjr.flare87.i
http://88.881215.com/88.htm
http://8hiql249h.setor800
http://aa.llsging.com/ww/new05.htm?013
http://aa.llsging.com/ww/new82.htm
http://aa.xxfgw.com/uM
http://aaa.udd05.cn/w6.htm
http://ad.171817.com/css/1.js
http://apartment-mall.cn/ind.php
http://api.browserinterop.com/sd/?c=42nybq==&u=$machine_idu5
http://awarefinance.com//2
http://bak116.we168.org/168368/add_154873.htm
http://bestentrypoint.com//1
http://bestsmartfind.com//5
http://big5.51job.com/gate/big5/i.ultimate-fight.netub
http://bjxiaojinster.googlepages.com/count.htm
http://blogbasters.com
http://botcraftman.ru//5
http://bwkjb.com/k.htm
http://ca.winvv.com/cn.htm
http://cc.wzxyq.com/10/1.js
http://cloudblueprintprogram.com/images4.php
http://czz.aeaer.com/c.htm
http://da.hhai01.com/shan.htm
http://dawnloadonline.com//4
http://daxincarving.com/to/um
http://dl.iwi
http://dl.iwin.com/games/gamesmanagerinstaller.exep
http://dl.xetapp.uspg
http://domstates.su/.nttpd
21-mips-be-t2-z.sh
http://dormister.com//2
http://down.136136.net/htm/
http://down.136136.net/htm/'
http://down.ackng.com/if.bin?id=
http://down.ackng.com/if.bin?id=wY
http://down.b
http://eelruxe.com//6
http://emailgoal.com//3
http://erotube.phalko.com/analytics
http://esecuritys.com//4
http://feedproxy.google.com/~r
http://feedproxy.google.com/~r//5
http://fikutuk.0adz.com/
http://find24hs.com
http://findinform.com//4
http://findthisall.com//1
http://foaptoa.com//6
http://fuadrenal.com/lib/index.php
http://gajgmpm.co.tv/?go=1
http://girrajwadi.com/css/aksu.msi
http://gluvoob.com//6
http://go0gie.com/sysupdate.aspx?req=sl
http://godsearchs.com//3
http://goo.gl/pdzspz
http://hardlyfind.com
http://hi.mmy88.cn/lx.htm
http://hilfe.com/index.asp
http://internetcountercheck.com/?click=
http://j5b.kr/bin/h.js
http://jestat.vicp.net/
http://jnvnai.tk/uo
http://joopsoa.com//6
http://jusqit.com/
http://kenion.com.mx/htaswift.hta
http://lehmanbrotherbankruptcy.com//5
http://mdksimon.su/vgasct.sctsS
http://media.randreports.org/
http://media.randreports.org/index.php?f=china_adiz.doc'
http://media.yesky.com/adjs/iframe-column/imp21.htm
http://mm.987999.com/abc.htm
http://mm.aa88567.cn/index/mm.js
http://monicahome001.blogspot.com
http://msgx1937.wi
http://mtv.myshw.net/
http://mtv.myshw.net/chengxu/index.htm
http://mydrugdir.com//3
http://niu.xinniankl.com/web/6619038.htm
http://ns.ipp.com.ru/ms/mm.htm
http://oalroax.com//6
http://oapsirs.com//6
http://odmarco.com/lib/index.php
http://old.44se44.com/vgaga.htm
http://oracle.zzhreceive.top/b2f628/rss.sh
http://p.myjobseye.comub
http://pastebin.com/api/api_post.phpaz
http://people.dohabayt.com/download/65f6434672fb?bQQfQbQeQbQbQbQeQbQdQsQ
http://ppp.749571.com/dm/
http://ppp.749571.com/ww/new82.htm
http://ppp.749571.com/ww/new888.htm?011
http://ppp.buyaoni.com/ww/new82.htm
http://pragmaticinquiry.org/hjergf76
http://py2web.store/m(mPp
http://qq3326.lndns.net.cn/xzz.htm
http://raisengine.com//3
http://resp.sjjnet.netuo
http://reycross.com/lib/index.php
http://riverside-resort.net
http://rocketcarrental.com//2
http://saintechelon.tk/tn
http://schemas.openxmlformats.org/package/2006/relationships
http://seachtop.com
http://signforcover.com//0
http://siteslocate.com
http://sitesworlds.com
http://starsearchtool.com//3
http://sto.farmsce
http://sto.farmscene.website/
http://sto.farmscene.website/track_ukieu.php?tim=1705921388i
http://storekit.xyz/api/v1/i.php
http://tech.google-s
http://thedirsite.com//3
http://u.1133.cc/showpage.php?pid=87840&show_t=2
http://u.cruze3.cn/u.htm
http://u.teknik.io/hukzo.pngs1
http://un.uiiiu.com/baidu.htm
http://uploads.shanatan.moe/ocnprx.doc
http://urseghy.com//6
http://v.naqigs.com/position/javas/cpm_2594_77604.js
http://w.aeaer.com/ae.htm
http://w.mh8888.cn/ad.htm?m
http://wangma.9966.org/wm.htm
http://wb.shijiediyi.net/wmwm/new.htm
http://web.lylss.com/id.htm
http://web.yulett.cn/count.htm
http://widesearchengine.com//5
http://ww.vip0.net/down.htm
http://www.1030829.com/0.htm
http://www.114oldest.com/ad/index.htm
http://www.20941.com.cn
http://www.2345.com/?k1535566291
http://www.333292.com/test.htm
http://www.3389guaiwu.com/xx.js
http://www.3ehaolihai.cn/down.htm
http://www.4399.com
http://www.480332.cn/1/index.htm
http://www.4threquest.me/310714d/310714_mb.exe?token=caiz0tmii3nm5bgyousexhlc8shcaiz0tmii3nm5bgyousexhlc8shcaiz0tmii3nm5bgyousexhlc8sh$_5_
http://www.5677.com.cn/vip.html
http://www.591my.cn/11/vip.htm
http://www.678ie.com/
http://www.798333.com/abc.htm
http://www.94to25.cn/down.htm
http://www.ac66.cn/88/index.htm
http://www.ac86.cn/88/index.htm
http://www.ads183.com/123/
http://www.aishengho.com/wm.htm
http://www.akbaidu.com/sm/ld.htm
http://www.baidu.com/index.php?tn=pubeihyj&fyb=0
http://www.baldu506.tkuo
http://www.bbs156.cn
http://www.boatebahamas.com/wp-includes/css/netflix/login/img/new/wheeesU
http://www.boatebahamas.com/wp-includes/css/update/nelsssMsTq5$05
http://www.cbala.com/
http://www.cndownz.com/js/1.htm
http://www.ctv163.com/wuhan/down.htm
http://www.daohang08.com/down/htmmm/mm.htm
http://www.dia-traffic.com/tds/in.cgi?two
http://www.dj0079.com.cn/test
http://www.fire456.cn/shan.htm
http://www.google.com.rw
http://www.google.com/url?q=http%3a%2f%2fgigaworkz.net%2ftmp%=b=JJ#J$J.J%J=J9J
http://www.googlvo.cn/all/index.htm?a
http://www.gorillawalker.com
http://www.hao123hao123.cn/ok/index.htm
http://www.hao489.com/
http://www.haogs.cn/m.htm
http://www.if56.cn/kan.htm
http://www.jzll-10.cn/zzll/12.htm
http://www.krvkr.com/worm.htm
http://www.krvkr.com/wormkr.htm
http://www.lingyinshu.cn/ln/md.htm
http://www.lovebak.com/qq.htm
http://www.mvoe.cn/all/index.htm?a
http://www.nice-doggy.xyz/run/updater.exe
http://www.p188.net/xm/xmxz.html
http://www.puma164.com/
http://www.ro521.com/test.htm
http://www.shengliw.com/ewebeditor/uJ
http://www.smxlykj.cn/mh/3333.htm
http://www.testks.com/gm/sd.htm
http://www.trackpixl.com/010914s/010914i.htm
http://www.wangzheqiaodan.com/girl/picture.htm
http://www.xinxinbaidu.com.cn/htm/mm.htm
http://www.xj305.gov.cn/admin/zhuanjia/date
http://www.xmsunyway.comuj
http://www.ygdyxx.com/inc/admin/haha.htm
http://www.zpx520.com/0.htm
http://www.zy98.com/
http://xeltuve.com//6
http://xtraserp.com
http://xx.ko51.com/index.htm
http://xxx.18dmm.com/newdm/new108.htm
http://xxx.mmma.biz/ps.htm
http://ydeepty.com//6
http://yftejum.com//6
http://yoyoa.vicp.net/
http://ysfjbxxvm.setor001.y
http://z.shavsl.com/nvidia.exe
https://a.pomfe.co/dhvkgfwB
https://accounts.google.com
https://b.catgirlsare.sexy/u2qe.doc
https://baarspo.ru//6
https://beadhouse.xyz
https://beadhouse.xyz/ss.php?a=3942
https://beadhouse.xyzi9
https://bologen.ru//6
https://botokaw.ru//4
https://cafij.co.za//5
https://colod.co.za//5
https://crophysi.ru//7
https://dafemum.ru//4
https://de.mt
https://docs.zohopublic.eu/downloaddocument.do?$2$G&++g75
https://druttle.ru//6
https://dugedepap.ru//4
https://fecuq.co.za//5
https://feedproxy.google.com/~r
https://feedproxy.google.com/~r//5
https://fokemale.ru//6
https://gimoguvi.ru//4
https://golowaki.ru//5
https://ipapi.co/org/'
https://ipmasheen.xyz/sjkdmncskdnjmc.php
https://ipmasheen.xyz/wtfjms.php
https://jacksth.ru//4
https://jottigo.ru//6
https://jumiwimov.ru//4
https://kuzutuzo.ru//4
https://lazav.co.za//5
https://leonvi.ru//5
https://loheb.co.za//!
https://lovig.co.za//5
https://lozipotod.ru//4
https://maypoin.ru
https://mezovuduw.ru//5
https://midufefew.ru//!
https://mifuj.co.za//5
https://netcdn.xyz/app/431946152//%
https://nipisod.ru//6
https://norin.co.za//5
https://novaprojects.ro/wp-css
https://pastebin.com/raw//3/K9$
https://pelibifir.ru//6
https://podar.co.za//5
https://ponafet.ru//6
https://public.adobecc.com/files/1u0crkntdsvboqihgmgo3qtkgtcfff?content_disposition=attachment
https://public.adobecc.com/files/1u0crkntdsvboqihgmgo3qtkgtcfff?content_disposition=attachment.:
https://ragaz.co.za//5
https://resalured.ru//3
https://seumenha.ru//6
https://soxebez.ru//6
https://stinkletjet.me/dir/mabtera.exe''
https://sunuf.co.za//5
https://tevav.co.za//5
https://vilenefex.ru//5
https://wirut.co.za//5
https://www.facebook.com/mp3enalgondrong'
https://xajibur.ru//4
https://xezojetit.ru//4
https://yafferge.ru//6
https://yafferge.ru/1/5
https://yoyep.co.za
https://yubit.co.za//5
https://zajinet.ru//6
Decrypted-URLs (5)http://dld.jxwan.com/d2/CDClient.dll
http://dsk.5636.com/index/getcfg?id=
http://www.58sky.com
http://www.58sky.com/index/getcfg?id=
http://www.ip138.com/
Decrypted-URLs (1047)http://021.17365.com/images/nsoft.gif
http://0512zx.com/god/index.htm
http://1.hao929.cn/1/4.js
http://111.213l23.net/14.htm
http://111.213l23.net/144.htm
http://111.213l23.net/lz.htm
http://111.213l23.net/real.htm
http://111.213l23.net/real11.htm
http://1122u.com/?new
http://1149.a38q.cn/lx.htm
http://120jia.cn
http://121.2006wyt.net/fzl.htm
http://121.213asdas.com
http://123.ko51.com/index.htm
http://140.a38q.cn/lx.htm
http://18dmm.com/down.htm
http://1intro.info/xplt/index.php
http://1t1t.vddns.net/g/g.htm
http://2ijdi.cn/x2/xx.html
http://3dcpw.net/house/404.htm
http://4.9797aiai.com/root/
http://51.15838.net/kewtqmk.htm
http://51gongnu.cn/js/user.exe
http://591ani.cn/html.htm
http://72960542.ee28.cn/htm/
http://878772.cn/bumian42.htm
http://88.881215.com/88.htm
http://9199203.k148.opensrs.cn
http://a.158dm.com/b3.htm?002
http://a.2-baidu.com/b3.htm?002
http://a.tnbdj.cn/14.htm'
http://a.tnbdj.cn/bfyy.htm'
http://a.tnbdj.cn/lz.htm'
http://a.tnbdj.cn/real.htm'
http://a.tnbdj.cn/real11.htm'
http://a0765645.xsph.ru/line/newpdf.php
http://a1.65862.com/count.html
http://a114.9966.org/2/5.htm
http://a814.cn/t.asp
http://aa.18dd.net/ww/new05.htm?013
http://aa.18dd.net/ww/new05.htm?075
http://aa.18dd.net/ww/new119.htm?2136
http://aa.531jx.cn/gm.js
http://aa.llsging.com/a2
http://aa.llsging.com/ww/new05.htm?013
http://aaa.369678.cn/bumian5.htm?1164
http://aaa.michael67.cn/
http://aaverturexs.eppureart.com/login.php
http://ad.171817.com/css/1.js
http://ad.171817.com/css/1.js0
http://ad.2365.us/103/
http://ad.l086.com/logo.gif
http://addonrock.ru/
http://adm.thaaly.com/xsystem/?a36j
http://adrienne.net/steel/bi-directional
http://ads.rzb.ir/image.php?size_id=7
http://ads.serveuser.com/ads
http://adserver.adtech.de/addyns5
http://adsl.jk33581.com/web/6032453.htm
http://advertbnr.com/cgi-bin/index.cgi?ad
http://aeu44ry.cn/x15/xx.html
http://agenenergyiq.com/?a=401336&c=cpc&s=240217';w:
http://ajax.googleapis.com/ajax/libs/jqueryui/1.11.2/themes/smoothness/jquery-ui.css'
http://alevel.wearewhy.co.uk/a1/excl.jpeg
http://allrss.com.cn/china/hi.php
http://apartment-mall.cn/ind.php
http://asrindragosanaokulu.com/
http://auto.notecm.com/post.php?cid=1&uid=78
http://avallon-informatique.fr/mllgkkei18
http://avra-beach.gr/mllgkkei22
http://b.kaobt.cn/img/p47.htm
http://b89369098.sq.u9idc.com/xyz/index.htm
http://basketballstrength.com/_borders/.htaccess.php
http://bb.congtouzailai.net/wmwm/new.htm
http://becomessubjectsslrsgates.net
http://berurn.com/vips'+$fos+$mo+$uy+$ji+$oe+$fd+$jik+$naw+$mo+$uy+$ji+$oe)
http://bixenon.webgalaxy.com.ua/system/disco.php
http://bjxiaojinster.googlepages.com/count.htm
http://blog.csdn.net/lake2/archive/2005/01/27/270921.aspx
http://boc.sbb22.com/home/index.htm
http://bookestheory.co.cc/img/
http://bot.gribokk.com/setup.php?aff_id=6113
http://brainmains.com/?a=401336&c=cpc&s=050217';wd
http://brightwasp.top/fphpd&
http://ca.winvv.com/cn.htm
http://cao4.gmwo01.com/
http://casanuntilor.ro/e-mariage-fest/immagini_regalo_matrimonio.php
http://catalogulafacerilor.com/s21/free/mw9/fwyw.php
http://cc.18dd.net/1.js
http://cc.haowangma.com/wmwm/
http://cc.haowangma.com/wmwm/new.htm
http://cc.wzxyq.com/10/1.js
http://cc.xiaofeifeifei2.cn
http://cedrussauna.com/jhg45s
http://chike01.3322.org/m.html
http://chike01.3322.org/m.html?1
http://chinea.vyrobce.cz/qphp.php
http://cletonuno.cx.cc/showthread.php?t=60800477
http://clrhy.512j.com/vhgf.htm
http://count1.count.xj.cn/images/images/1.css
http://count18.51yes.com/sa.aspx?id='+countid+yesdata+'
http://count26.51yes.com/sa.aspx?id='+countid+yesdata+'
http://css3.viens.la/css.js?tid=gb&pid=80
http://curem.net/t.php?id=677212
http://d.union.ijinshan.com/liebao/link/ksbinstaller_s_66_58860.exe
http://dadasdsadsa.3322.org/a/a6.htm?a272
http://davtraff.com/lib/index.php
http://ddtuser.kuaiwan.com/login/index3.asp?u=zhanzhang&i=1
http://description2011.ru/in.php?a=qqkfbwqhbaeabqqmekcjbqcebwuabaecaa==
http://dh.22dao.com/
http://dijaumatecido.com.br/177.188.18.180/index.php
http://directxex.com/uploads/408373870.out.exe
http://ditetec.com/ts.exe'+$fos+$mo+$uy+$ji+$oe+$fd+$jik+$naw+$mo+$uy+$ji+$oe)
http://dns.ll78.cn/reg.htm?a
http://dobusinessinmontana.com/wp-content/themes/./code-blue/../counter.php
http://dougdgordon.com/wp-content/uploads/2018/02/mainheader_reedit-1.jpg
http://down.136136.net/htm/
http://down.loot0mir2.com/test.htm
http://down.mala
http://down.malasc.cn/down/f3243.htm
http://down.malasc.cn/plmm.htm
http://down.onlinedowns.net/page/image/pd.htm
http://down.t6t8.com/js/tanchuang.htmlwk
http://download.uusee.com/pop1/qidian/uusee_qidian_setup_2488.e
http://dragosimport.com/js/sQ
http://duolaameng.diy.myrice.com/bushan.htm
http://eiueuiuewi.com/54n7js34b34d5nh34j/
http://erp.ivyacademicnetwork.com.pk/vendor/phpunit/phpunit/src/util/phprQ
http://exec51.com/cgi-bin/index.cgi?ad
http://f0844626.xsph.ru/fgg/fdxx.php
http://f0852652.xsph.ru/0000/webapp.php
http://f0855034.xsph.ru/webapp.php
http://f15.hkwordpress.com//wp-admin/xex/webapp.phpo)
http://f46.hkwordpress.com/wp-admin/@@../dhlpdf.php
http://fantasia-films.com/cache/march10.exe
http://fdisrv.qingdaochina.com/company1
http://ferstl-film.de/templates/beez5/javascript/news.php
http://fotoris.com/test/crop/1_4x6_g_i_b_y_2.php
http://fs8g78f8dduf.com/puke.de/jnbnjoklioeoctgljvb.php
http://fusionpoint.pk/dl/cK
http://fz1898.hostt.webad.cn/gg/eat.htm
http://gajgmpm.co.tv/?go=1
http://gb53.ru/cgi-bin/index.cgi?fgg
http://gdfcnt.info/ld/upl/'
http://ge.tt/api/1/files/233i9xt/0/blob?do
http://gelgit.tk
http://get.setheo.com/51.html
http://gg.haoliuliang.com/wmwm/new.htm
http://gg.haoliuliang.net/wmwm/new.htm
http://glondis.cn/in.cgis1
http://go.microsoft.com/fwlink/
http://goodyxmemooryx.com/?a=401336&c=cpc&s=050217';wL
http://google-ana1yticz.com/?click=45d01
http://google-stats.org/tracking/urchin.php'
http://gratwall.vv.cc/showthread.php?t=80480463
http://guoxiujing.vip.5944.net/index.htm
http://h.thec.cn/weilailong/index.htm
http://hackerwk.cn/cc/'
http://hamen.198.020ky.cn/ad.htm
http://han79.com/m.htm
http://heartofpole.net/xml.php')
http://heck654.512j.com/dare.htm
http://heifeng.xkwm.cn/1.htm
http://hi.baidu.com/yjhitxu1132/blog/item/9873440534ff771a728da51b.html
http://hi.mmy88.cn/lx.htm
http://hkgg.anyf.cn
http://hoursebuilds.cn/
http://hr.0596.net/0596/0596.html
http://html.2016win.win/v1/siteurls.php
http://hypmservices.com/wp-includes/elda/xlss.php
http://i.installwizz.com/static/mplayer/mplayer.zip
http://icons.iconarchive.com/icons/dakirby309
http://iii.wzxyq.com/root/bole.jss
http://il-falco.de/__installation/indexc.php
http://images.814e.com/tracker.html
http://img.namipan.com/downfile/7fc1edb70d88aede34c8c0b39ac8442f4eca179cdc050000/renchao.htm
http://imgaaa.net/t.php?id=6869404
http://imgbbb.net/t.php?id=12232093
http://imgbbb.net/t.php?id=14419269
http://imgbbb.net/t.phpwF
http://imgddd.net/t.php
http://imgddd.net/t.php?id=16599415
http://imgddd.net/t.php?id=17672224
http://inject.eh7.biz/css.js
http://internetcountercheck.com/?click=
http://j.thec.cn/luwei5851301/luwei/1.exe'
http://jejul.net/su/in.cgi?2
http://jestat.vicp.net/
http://jg54ikkhjdc.com/govinda.de/index.php
http://jingeng.web136.zgasp.com/gezi/index.htm
http://jjj.2012wyt.com
http://jkzj11.googlepages.com/vip.htm
http://jl.chura.pl/rc/
http://jqueryapi.info/?gp=1wT
http://js.tongji.yahoo.com.cn/0/462/490/ystat.gif
http://jugo.alt-rahlstedt.de
http://jywq.v1.5944.net/v1.htm
http://k4restportgonst34d23r.oftpony.at/
http://kabuy1.host1.nuno.cn/ok.htm
http://kao.gmwo03.com/97xxx/index.htm
http://kaott.cn/
http://keeppure.cn/wm/sj.htm?webshell
http://keywebtracker.com/?if=1&scr_w=
http://kiddy.online.sh.cn/upimages/test/index.htm'
http://kinoshkaxa.changeip.name/rsize.js
http://klaomta.com
http://kolkoman.com/lib/index.php
http://kullanilmisesyaalanlar.com/msfgttrj/js.js
http://la-liga.ro/kvpgvg2s/js.js
http://lake2.0x54.org
http://letbeservice.ru/in.php?a=qqkfbwqeaaadbgagekcjbqceaqedagwgbg==
http://letbeservice.ru/in.php?a=qqkfbwqeaaadbgagekcjbqceaqedbawbaa==
http://letbeservice.ru/in.php?a=qqkfbwqeaaadbgagekcjbqceaqwdawweda==
http://linbingchen.myrice.com/index.htm
http://lindyontherocks.com/data/remboursement.php
http://lingshi.sjsoo.com
http://lingshi.sjsoo.com/guama.j
http://lingshi.sjsoo.con/01.htm
http://lingshi.sjsoo.con/adu.htm
http://lingshi.sjsoo.con/muma.htm
http://lionhotelshropshire.co.uk/temp/u/myob%20inv%204182018.doc
http://litedownloadseek.cn/in.cgi?cocacola
http://llboss.com/admin/bole.js
http://lmydj.vip.5944.net/mm.htm
http://long.down988.cn/4.htm
http://mail.ppscn.com/public/image/projecticon.ico
http://manhun.cn/data/wm.js
http://market.zdnet.com.cn/files/redirectz.php
http://mary12345lt.zzyz.com/defaul.htm
http://mastercris.com/_vti_script/estilo.php
http://mavi1.org/forum
http://media.fc2.com/counter_img.php?id=50
http://metrogolf360.com/js/jquery.min.php'
http://mindgoodwits.com/?a=415195&c=brain&s=sss'wa
http://mister-f.com/qqqqq.exe
http://mixlong.cn/in/
http://mk.cxaaaa.cn/mk.htm
http://mkouh.webphoto.ir/photos/databasen.php
http://mm.987999.com/abc.htm
http://mm.aa88567.cn/index/mm.htm
http://mm.aa88567.cn/index/mm.js
http://mm.tt88567.cn/index/mm.htm
http://mm.uu88567.cn/index/mm.htm
http://mmm.black3389.com/
http://modesoli.com.br/lucianomartins/wp-admin/admin-ajax.php
http://money.hitempaya.cn/popwin/css/css.htm
http://mp3songzlyrics.blogspot.com
http://msound.cn/test/123.htm
http://mtv.myshw.net/
http://mtv.myshw.net/chengxu/index.htm
http://my.nbip.net/homepage/oldnb/mm/index.html
http://mycoohoo.cn/page/add_5454545.htm?3202-8823
http://mydork0731.go.3322.org
http://myfucking-pussy.com/tyrek/?t=5
http://myloveqrq.512j.com/inde.htm
http://mysportpics.blogspot.com/
http://netknight.go1.icpcn.com/index.htm
http://newdomme.changeip.name/rsize.js
http://news.chinaons.net/page/image/pd.htm
http://ntkrnlpa.cn/rc/
http://o.thec.cn/aiyi888/guang/guang.htm
http://oa.wlsh.cn/wlb/uu.htm
http://odmarco.com/lib/index.php
http://oo-ha.com/scripts/oohaportal.php
http://ordochao.com/vti/
http://ouxinfei.512j.com/1.htm
http://pdabattery.net/ads/counter.php')
http://petstop.co
http://pim.toyotamh.cz
http://plapla.go1.icpcn.com/plapla.htm
http://playart.org/sites/stats.php
http://po4c.ru/cgi-bin/index.cgi?ad
http://pokosa.com
http://poseyhumane.org/stats.php
http://pp.327666.com/abc.htm
http://pp.900666.com/abc.htm
http://ppp.749571.com/dm/
http://ppp.749571.com/ww/new888.htm?011
http://ppp.buyaoni.com/dm
http://prerre.com/counter2.php
http://presentesmorumbi.com.br/asyncrat-client.exe'
http://priestsforscotland.org.uk/wp-content/themes/blessing/0032904.php
http://protocolmindm.com/img2/count.htm
http://q16899.go.5944.net/paipai.html
http://qazwsx.3126.com
http://qi.ccbtv.net/btv.htm
http://qiulang.199.hezu1.com
http://qq3326.3video.cn/index.html
http://qq519873.12mf.cn/main.htm
http://qqq.aishengho.com/gm.htm
http://qqq.qq1680.com/do
http://raa.qwepoii.org/v4/gtg/
http://ramualdo.com/lib/index.php
http://ranatatravel.com/wp/client//ban.png
http://rapiseebrains.com/?a=401336&c=cpc&s=050217';wF
http://refer68.com/cgi-bin/index.cgi?ad
http://refhunter.ru/script/js.php?id=203417&adult=no
http://renjian1244.go1.icpcn.com/index.htm
http://reycross.com/lib/index.php
http://reycross.net/lib/index.php
http://rii.wo.tc/d.htm
http://romful.com/nero'+
http://romful.com/segw'+$fos+$mo+$uy+$ji+$oe$2$I(
http://rr7mdgjbjhbefvkhbashrg.ginnypecht.com/
http://rrr.rfhwfhw.com/1.htm
http://rx0031.8866.org/xman/2.htm
http://s.gcuj.com/bd.htm?1155
http://s109.cnzz.com/stat.php?id=418410&web_id=418410'
http://s31.cnzz.com/stat.php?id=1212086&web_id=1212086
http://s31.cnzz.com/stat.php?id=1408284&web_id=1408284
http://s48.cnzz.com/stat.htm?id=195662'+
http://safe.fusionk3ker.com/safe.html'
http://salsil.blogspot.com
http://samsmart.pk/wp-content/uploads/2022/newexcelmega.php'
http://sbsb520.go3.icpcn.com/ccet/index.htm
http://search.live.com/results.aspx?q=%e4%b8%9c%e4%ba%ac%e7%8c%ab%e7%8c%ab&mkt=zh-cn&form=ctnonj&format=&count=1&format=rss
http://search.live.com/results.aspx?q=%e5%b8%88%e5%a3%ab%e4%bc%a0%e8%af%b4&mkt=zh-cn&form=ctnonj&format=&count=1&format=rss
http://search.live.com/results.aspx?q=%e6%9c%ba%e5%8a%a8%e6%88%98%e5%a3%ab%e9%ab%98%e8%be%be&mkt=zh-cn&form=ctnonj&format=&count=1&format=rss
http://search.live.com/results.aspx?q=%e7%9f%bf%e5%b7%a5&mkt=zh-cn&form=ctnonj&format=&count=1&format=rss
http://seductivex.com/22060113021400.cgi
http://send.softwork.us/xsel.php
http://serpbe.net/index.php?tp=8bd2fc9516a67a13
http://service-google.cn/vip/cn1707.htm
http://serw.comcastraffic.pro/'
http://sf.sf325.com/kyo/index.htm
http://shao.xs.222173.cn/in.htm
http://shopsand.com/lib/403.shtml.php
http://skullsmod.com/eli/index.php?s=dbaa2a9443e61f8e5446d705757a205c
http://sniff.mmy88.cn/lx.htm
http://socialwork.hkwordpress.com/wp-includes/assets/sss/dhl.php
http://sorinnohoun.com/sc1/sct5'
http://spba.gcgs.gov.cn/img/en.htm
http://ssiwj.ifastnet.com/index.htm
http://stability.co.il/images/cy/mcy.php
http://stat1.vipstat.com/stat/iebarinstall_tc.htm?pid=27902&unionid=4&sid=18458&ktime=24
http://statanalyze.cn/lib/index.php
http://studypenang.com/_webboard/detail_news.php
http://sysysysys.com/track.php?ip=
http://tamabi.cn/default.asp
http://tamekajackson.org/images/page1.php
http://tarakan2011.ru/in.php?a=qqkfbwqeaaadbgagekcjbqceaqwdawweda==
http://tds5555.ddns.us
http://teamoneservices.com
http://tech.google-serv.cn/index.htm
http://testset.com
http://thedeadpit.com/?click=
http://thekapita.com/lib/index.php
http://themollymalone.es/12'
http://three.fsphost.com/google003/index.asp
http://tiao.go.3322.org
http://tier2win.serveronline.net/scripts/js/axp-libs.js
http://timeout.mmy88.cn/2007.htm
http://tongji.linezing.com/1240663/tongji.js
http://touchme.changeip.name/rsize.js
http://tsm.25u.com/local.html
http://tt.ee88567.cn/index/mm.htm
http://tx0168.cn/123.htm'
http://u.27955.com/advcode/sgopen.html
http://u.cruze3.cn/u.htm
http://u.vodone.com/wj/count.jsp
http://ukworkaccidentclaim.co.uk/gate.php')
http://un.uiiiu.com/baidu.htm
http://union.uiiiu.com/a.htm
http://union.uiiiu.com/links/home.htm?029
http://user.free.77169.net/bey8169/tt.htm
http://user.free.77169.net/heimahack/hack.htm
http://user.free.77169.net/usee/s.htm
http://user.free.77169.net/zhengh112/200721.htm
http://user.free2.77169.net/iluojian/vip.htm
http://user.free2.77169.net/loser
http://user.free2.77169.net/lsbby
http://user1.2002691.net/cb.js
http://user1.33225.net/bak.js
http://user1.fafa29.cn/
http://user1.fafa29.cn/real10.js
http://user1.jzm015.cn
http://user3.33391.net/ps.js
http://usharif3.com/main/wp-content/themes/blacklabel/js/jquery-1.5.2.min.jss7
http://usuarionovo.com/'
http://vccd.cn/m.htm
http://vksinema.blogspot.com/search/label/dangerous%20liaisonsaW
http://w.73734.cn/reg.htm?a
http://w.aeaer.com/ae.htm
http://w.mh8888.cn/ad.htm?a
http://w.mh8888.cn/ad.htm?m
http://w.qbbd.com/bd.htm
http://w47636.s33.freedns.name/ok/index.htm
http://w84965622.id666.com/user/w84965622/disk/yifan.htm
http://wangma.9966.org/wm.htm
http://wb.haoliuliang.com/xxx.js
http://wb.shijiediyi.net/one/hao8.htm?024
http://wczan521.512j.com/jie.htm
http://wdaoyao.go.3322.org/
http://web.59cn.cn/kevinhacker/wm.htm
http://web.baizc.com/301/
http://web.gze.cn/gzecn.js
http://web.lylss.com/id.htm
http://web.sway3322.cn
http://web.yulett.cn/count.htm
http://web2.163.sh.cn/~shidai/icyfox.htm
http://webfrogs.ru/in.php?a=qqkfbwqeaaadbgagekcjbqceaqqhagcgag==
http://webtest.lkidc.com/a.htm
http://weiweidiai.808.nuno.cn
http://wellingten.de/images/werf.exe
http://wenson545.vip.5944.net/dh.htm
http://wenson545.vip.5944.net/qm.htm
http://wgxb.psnic.cn/mm.htm
http://wi66db.cn/x50/xx.html
http://witvipgen.com/?a=401336&c=cpc&s=090117';wC
http://wm.168080.com/wm/wm.htm
http://wodehao448.jiazu.cn/du/index.htm
http://woj-tech.com/img/pl_forsale.php
http://wori360.tudou21.cn/
http://worldkazino.biz
http://worldrobotprintar.com/aop/pdfnf.phhQ
http://wow.a38q.cn/wow.htm
http://ww.vip0.net/down.htm
http://ww.viph.net/wuhan/down.htm
http://ww01.4512964.com/lz/index.htm?id=221154
http://ww01.9966.org/lz/index.htm?id=yyhlyl
http://ww1.pigzd.cn/am1.htm?47
http://ww3.tongji123.com/t1.aspx?id=34467917
http://www.029best.com/xzz/wangma.htm
http://www.029zhaosheng.cn/index.asp
http://www.0755jj.com/css/
http://www.0851.la/
http://www.0duwang.cn/
http://www.1030829.com/0.htm
http://www.114oldest.com/ad/index.htm
http://www.114oldest.com/zz/mm.htm
http://www.118bi.cn/all/aa.js
http://www.122ip.cn/hhh.htm
http://www.17789.com/3link.asp?44404bf'
http://www.17aq.com/17aq/tongji.htm
http://www.18cv.com/htm/
http://www.1mag.cn/qgw_down.html
http://www.1net.cc/kn.exe
http://www.20941.com.cn
http://www.223.ch
http://www.2hai.com.cn
http://www.333292.com/cb.js
http://www.333292.com/test.htm
http://www.3ehaolihai.cn/down.htm
http://www.456ii.cn/all/aa.js
http://www.480332.cn/1/index.htm
http://www.4slllj.cn/a328/fxx.htm
http://www.51laa.com/cc888.htm?003
http://www.520hsd.com/inc/index.htm
http://www.52cps.com/goto/mm.htm
http://www.5415.info/mo/11.htm
http://www.5677.com.cn/vip.html
http://www.591chuguo.com
http://www.591my.cn/11/vip.htm
http://www.5ibsj.com/kk/wm.htm
http://www.5l1l1.cn/
http://www.660083.com/qq/2.htm
http://www.666535.cn
http://www.666535.cn/168.htm
http://www.666535.cn/180.htm
http://www.66ki.cn/dan.htm
http://www.66ki.cn/index.htm
http://www.66ki.cn/jie.htm
http://www.66ki.cn/kai.htm
http://www.66ki.cn/rong.htm
http://www.6783.com/
http://www.68yu.cn/f11.htm
http://www.710sese.cn/a125/fxx.htm
http://www.71th.tw/wp-admin/network/other.php
http://www.71th.tw/wp-content/plugins/layerslider/locales/other.php
http://www.798333.com/abc.htm
http://www.820515.net/index.htm
http://www.851733.cn/htm/htm.htm
http://www.868wg.com/1/1/qq.jssW
http://www.8877.cc/js/tt.html
http://www.88feel.cn/ddd5.htm
http://www.88kv.cn/mm/index.htm
http://www.89188.cn/manage/1.htm
http://www.8es.cn/include/k.htm
http://www.9344.cn/mm.htm
http://www.94to25.cn/down.htm
http://www.99391.net/u24.html
http://www.aaemc.com.cn/bbs/admin/data.htm
http://www.ac66.cn/88/index.htm
http://www.ac86.cn/66/index.htm
http://www.ac86.cn/88/index.htm
http://www.aishengho.com/wm.htm
http://www.akbaidu.com/sm/ld.htm
http://www.back88.cn/index.html
http://www.balas.nadrag.ro/photogallery/nadrag/logo/love.htm
http://www.baomaaa.cn/a2/fxx.htm
http://www.bebinak.com/dl/wce.html
http://www.bhp159.net/a.htm
http://www.bjwto.gov.cn/wto/forum05/databackup/2.htm
http://www.bluewow.cn/index.htm
http://www.bsv-pongau.at/site/media/inc.php
http://www.cb71.cn/a.js
http://www.cd365.net/cd365/admin/show_oder.htm
http://www.china-hotspring.com/admin/link/link.htm
http://www.ciudad.com.ar/ar/popunder/p_submit.asp?site=personales.ciudad.com.ar
http://www.cnbsci.com
http://www.cnky.com/ry/fuck.htm
http://www.codeforum.cn/free/max1.htm
http://www.coolroge.cn/1114/wangma/index.htm
http://www.cqzjz.cn
http://www.csccx.cn/
http://www.ctv163.com/wuhan/down.htm
http://www.cunweb.com/bbs/uploadfile/2006-10/index1.htm
http://www.dadaip.cn/6789.html
http://www.daohang08.com/down/htmmm/mm.htm
http://www.darcyservices.com.au/blog/wp-content/uploads/2014/12/myob_logo.jpg
http://www.defhack.tk/index.html
http://www.dgdbr.com/blog/2.htm?1
http://www.dhtianyu.net/noopxp/oo/ico.gif?1717
http://www.dia-traffic.com/tds/in.cgi?two
http://www.dicp103.com/bbs/laoding.htm
http://www.dzy520.com/cs.htm?id=blizzard-12
http://www.era.fm/capsule/default.aspx
http://www.facebook.com/plugins/lik
http://www.facebook.com/plugins/like.php?href='
http://www.facebook.com/widgets/like.php
http://www.facebook.com/widgets/like.php?href=
http://www.gambinohomes.com/modules/img/pop.php
http://www.gamezonetw.com/pop/index.htm
http://www.gaoso.com/3link.asp?44404bf'
http://www.gcxxc.cn
http://www.gczxw.com/images/arcdd.jpg
http://www.gdxjn.com/admin/xyz.html
http://www.geoiptool.com/?ip=$ip$3
http://www.ggoto.com/gjfz/js/wm.htm
http://www.glms.cn/article/long.htm
http://www.goldwindos2000.com/krratwo/hker.htm
http://www.good6368.cn/b3.htm
http://www.google.com/s2/favicons?domain='+strmaindomain;s_sW#:'489#29#wjw
http://www.googleadsl.com/spcode/jquery.j
http://www.googlvo.cn/all/index.htm?a
http://www.grelka.com.ua/map/tfile.txt
http://www.gxtdsky.net/buy/kw/yd.htm
http://www.gzwa.net/gzwa/010/2.htm
http://www.h148.cn/
http://www.hackings.cn/11.htm
http://www.haofbi.com/js/w.js
http://www.haogs.cn/html/
http://www.haogs.cn/m.htm
http://www.hhy8.com/movie/liuliang/klxc.asp
http://www.idiw.cn
http://www.if56.cn/bill.htm?id=gogel01
http://www.if56.cn/kan.htm
http://www.ik8.cn/new.html
http://www.jade-china.com/noone.html
http://www.jltao8.com/include/css/1.asp
http://www.jou.com.cn/pic/seeker.htm
http://www.jsyzzx.cn/inc/20051018.jpg
http://www.jsyzzx.cn/inc/kv.htm
http://www.kaspersky-norton.ws/new/traff.php'
http://www.krvkr.com/worm.htm
http://www.krvkr.com/wormkr.htm
http://www.ksdnewr.com/js/w.js
http://www.lady361.net/aa/cooperate.aspx?action=goto&id=52
http://www.ledhp.com/tie/2.htm
http://www.lijinjituan.com/index.html
http://www.lingyinshu.cn/ln/md.htm
http://www.lkjrc.cn/456.htm
http://www.lm8n.cn/9/fl/fl.htm
http://www.lovebak.com/qq.htm
http://www.lovefengling.com.cn
http://www.luckbird8.cn/top.js
http://www.m5k8.com/gr.htm
http://www.manage.com.cn
http://www.mavi1.org
http://www.mdqjx.com
http://www.medclub.com.tw/simple/newly/image/1.htm
http://www.mhfdc.net/repla.asp
http://www.miao88.com/wm/index.htm
http://www.miggiebella.com
http://www.mjlz.net/images/dns.htm
http://www.mmexe.com/51la/6.htm
http://www.mmstore.cn/dk/2.htm
http://www.mmstore.cn/dk/2.js
http://www.mobaoge.net
http://www.muma.com/mm.htm(
http://www.music100000.cn/wm/aaa.htm
http://www.mvoe.cn/all/index.htm?a
http://www.mvpsf.com/kb/vip.htm
http://www.mydirvers.net/page/image/pd.htm
http://www.myziy.com/hits.asp
http://www.n85853.cn/index.htm
http://www.nuvid.com/video/2753066/spitroasted-by-strapons
http://www.opensite.cn/noone.html
http://www.orjinkrem.net
http://www.p188.net/xm/xmxz.html
http://www.plize.com/manage/images/muma.htm
http://www.puma164.com/pi/9687.htm?9169
http://www.puma166.com/1.htm
http://www.qizhouhuinong.com/ie/index.htm
http://www.qqjipin.com/tan.html
http://www.qznanhuan-crafts.com/manager/count/images/test/index.htm
http://www.real.dp.ua/img/upload/item/207/stats.php'
http://www.real2.cn/ad.htm
http://www.rich21.com/admin/
http://www.rich21.com/admin/gg.htm
http://www.rich21.com/admin/hh.htm
http://www.ro521.com/test.htm
http://www.rootkit.net.cn
http://www.ruantaoonline.com/admin/huiyuan/gezi.htm
http://www.ruker.net
http://www.rxjh58.cn/web.htm
http://www.rzguanhai.com/001/updata.htm
http://www.saldiri.org/summer/ciz.js
http://www.sf-express.com/.galleries/favicon.ico
http://www.shengbaosm.com
http://www.shijiediyi.net/one/hao8.htm?015
http://www.shthyx.com/jyw/qg.htm
http://www.shyhack.cn
http://www.skypka.com/bit.php
http://www.skyttc.com/xm/cike.htm
http://www.smxlykj.cn/mh/3333.htm
http://www.socosoco.cn/goal/mm.htm
http://www.soooon.3322.org/darkteam.htm
http://www.souxse.cn/ing/4547.htm
http://www.syscgj.gov.cn/data/of.htm
http://www.szyanwei.com/uploadfilessms06014.htm
http://www.tchedu.com/bbs/huoyan.htm
http://www.tdsse.com/tds/go.php?sid=16'
http://www.te
http://www.testks.com/gm/sd.htm
http://www.thcity.com/admin/popup.php
http://www.tjbfqy.com/index.htm
http://www.tongji123.org/i1231.swf
http://www.touba4.cn/01/0001.htm
http://www.toyouo130.cn/a97/fxx.htm
http://www.trenz.pl/rc/
http://www.tt16888.net/index.htm
http://www.turningpoint.hu/w3vtqvyg/js.js
http://www.tzsteel.com.cn/index.htm
http://www.uc21cn.com/ln/md.htm
http://www.up36.com/
http://www.usuarionovo.com/'
http://www.viruswom.org/default.htm
http://www.vlike.com/ourgg/bd.htm
http://www.wangzheqiaodan.com/girl/picture.htm
http://www.webye163.cn/js/top.js
http://www.wgcn.net.cn/admin/flash/index.html
http://www.whrsj.gov.cn/img/index.htm
http://www.wvyi.com/mu/hack.htm
http://www.wzkfc.com/ip/22.htm
http://www.xiangxue.org/222/index.htm
http://www.xinxinbaidu.com.cn/htm/mm.htm
http://www.xj305.gov.cn/admin/zhuanjia/date/11.htm
http://www.xj305.gov.cn/admin/zhuanjia/date/a.htm
http://www.xjlan.com/wm/gr.htm
http://www.xqt158.cn/index.htm
http://www.xtzspxw.com/admin506/tt.htm
http://www.xx.cn/1.htm
http://www.ybhbjc.com/menu/index.html
http://www.yes5l.com/index.htm
http://www.yjyjyj.cn/1/main.htm
http://www.youknownow.ruha
http://www.yujingsh.cn/admin/meinv.html
http://www.zhaobaow.cn
http://www.zpx520.com/0.htm
http://www.zy98.com/
http://www70.jqueryapi.info/
http://x.asom.cn
http://x.mi5656.cn/a.htm
http://x.shit123.com/grw/index.html
http://xanjan.cn/in.cgi
http://xiaomi-mall.com/system/engine/wetransfer/wetransfer/files/favicon.ico
http://xqhao.com.ru/head.htm
http://xx.522love.cn/html/ani.htm
http://xx.9365.org/ip/1.htm
http://xx.ko51.com/index.htm
http://xxtvb.cn/arp/httpweb.htm
http://xxx.00696.com/index.html
http://xxx.18dmm.com/newdm/new05.htm?075
http://xxx.745970.com/newdm/new05.htm?075
http://xxx.hao1680.com/wm
http://xxx.hao1680.com/xx.htm?id=60
http://xxx.mmma.biz/ps.htm
http://xxx.xxxxxx.com/web.htm
http://xz135.free3.dns8cn.com
http://y6j0j0b4.skottles.com/lib/index.php
http://yoyoa.vicp.net/
http://yyhaomm.cn
http://yyy.2012wyt.net
http://yyy.2012wyt.net/newer
http://zief.pl/rc/
http://zjs.vxv.cn/
http://zsmxjy520.512j.com/vip.htm
http://zzhaomm.cn
https://619708.selcdn.ru/ssh/signin/jquery.min.js
https://aadcdn.msauth.net/shared/1.0/content/images/microsoft_logo_564db913a7fa0ca42727161c6d031bef.svg
https://agenciaoneway.net/wp-includes/az/new_po.php
https://aldigital.es/wp-admin/network/admin/01/04/007/anydomain.php
https://api.telegram.org/bot
https://api.telegram.org/bot6546628146:aafglumvq7bsshweuibsmvn6vtfpb2ig8vk/sendmessage?chat_id=-1002016417277
https://api.telegram.org/bot7025099545:aahhr4rml1ndmozrgy2flfpqio11mba1l3a/sendmessage?chat_id=-1002089663282vO
https://app.form2chat.io/f/oG
https://app.formester.com/forms/6a2cbf65-4edf-4b33-b17f-e6530de432cf/submissions
https://app.formester.com/forms/a338f043-6ec4-4671-b1e0-b389b09c6de3/submissions
https://assetsdigital.io/wp-admi
https://authedmine.com/authenticate.html
https://authentic.com.vn/
https://autohawk.no/dbx.php
https://benjaminsoverbooty.com/fedex/fdx.php
https://benti-energies.com/pph/adhl.php
https://bestfurnitureservices.com/bed/fedexx.php
https://bhandarienterprises.in/wp-admin/3pending
https://biggerfun.org/hqn5bkc3vU
https://birminghamcontainerparking.com/wp-includes/dhl-invoice/nwdhl.php
https://bit.ly/2x9l37s
https://bnfwuij.com/able/bigger/newx.php
https://box2boxstore.com.br/wp-content/user/zz.php?email=sK
https://bttelecommuhytw.weebly.com/
https://bttelecommuhytw.weebly.com/uploads/1/4/1/8/141858750/published/index.png?1652612790
https://burjnahargroup.com/bhagejfx/next.php
https://c.tenor.com/i6kn-6x7nhaaaaaj/loading-buffering.gif
https://campitubos.pt/test/desk/lognet1.php
https://carnereara.sa.com/dbx.phpoT
https://cdn.jsinit.directfwd.com/sk-jspark_init.ph
https://cdn.mcauto-images-production.sendgrid.net/32724a092ad701f7/c6e2282d-8a53-44c8-9b7c-262
https://cerradurasonline.com.es/modules/dashtrends/views/fonts/system-info.php'
https://championsports.ie/ay/excel.phprM
https://championsports.ie/whr/excel.php
https://coatingstoday.bop21.com/vonfig/next.phpuRuPfeudaugdubhufiubiub4ugcub5ugcugeufbugc
https://code.jquery.com.de/jquery-3.5.1.m
https://cospub.cantonfair.org.cn/461100754573217792/1646935520314-757f4e6d-a8b3-4b1d-89a5-84e7dce1e8de.png
https://cprgvacations.com/wp-includes/j/excel.phpo*
https://cumdrenchedcuties.com/deppd/exc.pho/
https://cumdrenchedcuties.com/payment/exc.php
https://dev-corne.pantheonsite.io/
https://dev-corne.pantheonsite.io/exs/newx.php
https://dev-hbjb.pantheonsite.io/
https://dev-juck.pantheonsite.io/po/epdf
https://dev-telai.pantheonsite.io/b78/adobe
https://dev-zgfdgfutyiuiujolj.pantheonsite.io/wpd/awoko.php
https://devqeury.org/mxn9mb9h
https://download.logo.wine/logo/microsoft_excel/microsoft_excel-logo.wine.pk=
https://eakhan.buet.ac.bd/wp-content/show/attach.php
https://easyraze.se/old/wp-content/zz/file.php'mX
https://elearning-diversite.fr/wp-content/plugins/oebpxlzkbs/dbx.php
https://encrypted-tbn0.gstatic.com/images?q=tbn:and9gcqcdtcmj8ouf85y74bnlwiaukf74gye3jsjyw&usqp=jpg
https://encrypted-tbn0.gstatic.com/images?q=tbn:and9gcqvlldnwgexilipq3t3ytz9jyzpzcsdks8ymsjubxdpvaafh_lr5r6yjxh91om9vwhdrge&usqp=cau
https://encrypted-tbn0.gstatic.com/images?q=tbn:and9gcsqjixysomqxpqdpnxcovgmucqsmrlullrvzg&usqp=cau
https://enrichearth.com/wp-content/duc/lognet1.php
https://esquadriasalupar.com.br/dbx.php
https://estell.biz/specialist/money-market-account/concretehH
https://euunclaimedpymt.com/a.php'
https://famelanguages.com/wp-admin/nn/next.php
https://farsonka.co/trb.exe'+$fos++3+M?&
https://firebasestorage.googleapis.com
https://fonts.googleapis.com/css?family=montserrat:100
https://fonts.googleapis.com/css?family=roboto:300
https://forfbidrecrossboot.pages.dev/503.js
https://formbold.com/s/w
https://formcarry.com/s/d5xcyonpyz
https://formcarry.com/s/rackyorqii
https://formspree.io
https://formspree.io/f/mbjeqngl
https://formspree.io/f/mlevlzze
https://formspree.io/f/xgvwodjy
https://fortcollinsadventurerentals.com/wp-content/figo/lognet1.phhP
https://frookshop-winsive.com
https://frookshop-winsive.com/wn
https://futanostra.win/fo
https://glooming.duckdns.org/dc/pdfnglw.phoE
https://gmora.com.mx/.xyz/next.php
https://godunlimited.org/cgi-bin/excel.php
https://goldenmedia.com.mx/dbx.php
https://goo.gl/9lozxy
https://grajmyrazem.pl/wp-includes/gb/gb.php
https://gremar.si/wp-admin/css/colors/blue/po/new_po.php
https://gst.taxmann.com/images/loading.gif
https://gswaters.com/sample/exc.php
https://hkjgy.mypi.co/tesx/new_po.php
https://i.gyazo.com/070981e23f173a30947bd2974860b602.png
https://i.gyazo.com/3095c0c48a2ebe32abca6d150d2ff4df.png
https://i.gyazo.com/4522caeb250b902767ea9d7dbee510fb.png
https://i.gyazo.com/4522caeb250b902767ea9d7dbee510fb.png)
https://i.gyazo.com/52a11ae9fe6936093d1a147ffb24ad16.png
https://i.gyazo.com/52a11ae9fe6936093d1a147ffb24ad16.png)
https://i.gyazo.com/5b0bfd9810f4c1f76356f79a731ce855.gif
https://i.gyazo.com/67b6fb6904bb7a3515af8d66ac3520a8.png
https://i.gyazo.com/68f952de6300fe4e1176d351768b817c.png
https://i.gyazo.com/6cf6b944f9e0419ffe45f8ed9943c431.png
https://i.gyazo.com/716e7fd047ac2ebf6e514daff53792be.png')
https://i.gyazo.com/7ae773ff61e2c8a88bda5530c3b2aa13.png
https://i.gyazo.com/7fcc6ef238718d6b97710fecd685391a.png
https://i.gyazo.com/8333092bcb73600350d4c4b4dd8b2f3b.png:large
https://i.gyazo.com/83cffd1ebf23ed93aa925eb9529f5348.png
https://i.gyazo.com/934cee31d5268a86c613c5ac8999f886.png')
https://i.gyazo.com/9e0695ea85e62ede58d86dc81201f410.png
https://i.gyazo.com/b0
https://i.gyazo.com/c5327eab7ec3f0256b0287d14d490a62.jpg
https://i.gyazo.com/d1748870a749bda1019c919dff50ed75.png
https://i.gyazo.com/d98673b9fae3586a1783f1f1d410ea84.png
https://i.gyazo.com/e3f18d47c9d91b87e40db71b5106bdc2.png')
https://i.ibb.co/j80t78w/cbimage.jpg
https://i.ibb.co/pqqspg9/bg-1.png
https://i.ibb.co/qnj7bsz/other1.png')
https://i.ibb.co/tbt5dff/dwl.png
https://i.ibb.co/y6sll5r/logo.png
https://i.ibb.co/zvtvqzf/colll.jpg
https://i.imgur.com/4rhyhzw.pn
https://i.imgur.com/4rhyhzw.png
https://i.imgur.com/5klh2y9.png
https://i.imgur.com/nwumbtb.png')
https://i.imgur.com/zihumzk.png)
https://i.pinimg.com/236x/de/15/a0/de15a0ad5083aadd313ada08e050c272--jakarta-indonesia.jpg)
https://i.postimg.cc/nfkybkh2/png-item-1791525.pnm!
https://i.stack.imgur.com/vzbuq.jpg
https://i.ytimg.com/vi/txoshp-bqge/maxresdefault.jpg
https://i0.wp.com/www.jayom.net/wp-content/uploads/2020/09/microsoft-excel-logo.jpg?fit=300%2c169&ssl=1
https://imgur.com/gr50fqt.png)
https://imgur.com/vavjt9c.png
https://ipapi.co/org/'
https://isc.sans.edu/diaryimages/images/blurred.jpg)
https://isisanplastik.com/jsd/683-6833470_transparent-ms-fice-png-misoft-office-mexcel.png
https://isisanplastik.com/jsd/68iMiG
https://isisanplastik.com/tof/wojd9isjdi9s.jpg')
https://jacksautobody.ca/w/excel.php
https://jiejiaoniupai.com/mail/exc.php
https://journal.grnedv.ru/assets/images/css/lognet1.php
https://jxp3.sa.com/new/line.php
https://kafatanmor.org/wp-includes/login-doc/new_po
https://kanyinicare.com.au/wp-includes/ama/excle.php
https://kb.planethoster.com/wp-content/uploads/2021/08/logindetails_incorrect.png
https://khoms222.ir/au/js/arch/file.php'aT
https://km.zhl8.za.comoc
https://kvwpca.com/chsxcl/macus_ssw.phhC
https://kvwpca.com/xclpan/macus_ssw.ph
https://kvwpca.com/xeclz/macus_ssw.php
https://linetoday.me/client/xls.php
https://login.live.com/logout.srf?response_type=code
https://logo.clearbit.com/$
https://magesource.su/mage.js'
https://manojcaterers.com/forms/css/css/css/hjdjksos.php
https://marled-blasts.000webhostapp.com/hsbc_logo.jpg
https://mcduplessis.co.za/cgi-bin/site.php'
https://media-exp1.licdn.com/dms/image/c561baqejraw1vg8fga/company-background_10000/0/1578408521231?eb&
https://medicallist.ru/salescontract/xls.php
https://mkfouad.best/
https://mobileoffers-es-download.com/974/109?utm_source=w@
https://multiplai.io/wp-admin/xz/3pending
https://musexpd-dev.site/milli/dhlz.php
https://mx.azizrajelvivaaxraf.shop/app/8b1fbe0.php
https://mydhl.express.dhl/index/en.html
https://mydhl.express.dhl/us/en
https://mydhlplus.dhl.com/etc/designs/dhl/favicon.ginQ
https://mydiywebapp.com/dbx.php
https://myprintscreen.com/soft/myp0912.exe'
https://nenias.ru.com/dbx.php
https://netkromsolution.com/ders/leop.php'
https://nocodeform.io/f
https://nocodeform.io/f/6532352006843a6e24340859
https://nocodeform.io/f/65acc261677f4282f7477b44
https://nocodeform.io/f/65cab649b02eda5a31c3b2car:
https://nocodeform.io/f/65e5c1e620b902e1df3643de
https://nocodeform.io/f/6602bb6c8f08516891889cb1
https://nocodeform.io/f/661fe0fa8416614908b7fe4d
https://nocodeform.io/f/663357252acab5ebd7dc4doP
https://nocodeform.io/f/6654ed0db157851950245460
https://nocodeform.io/f/6660f49f05c1db20c3c41328oB
https://nocodeform.io/f/66616f361817e5ce359512cah=
https://nocodeform.io/f/667ac665fe345d16bfa5168c
https://nocodeform.io/f/66oF
https://nocodeform.io/fr2
https://nocodeform.io/fv&
https://norsmoker.sa.com/excel.phpoU
https://nr.ornx7.ru.com/http/dhlz.php
https://ois.is/images/logo.png
https://onlinefreshfruits.co.nz/s/excel.p
https://op.ziel5.ru.com/duc/excel.phph$
https://oslo.sveif.com/wp-admin/
gb.php
https://outlook.live.com/mail/0/inbox
https://palmlake.com.au/wp-includes/tw/madh.php
https://pantyl.com/mu/fedexx.php
https://personaltrainerperme.sa.com//php/fedex.php
https://phone.chandragirinews.com/inv/xlss.php
https://pilatesbykristin.comdj
https://po00000004498.000webhostapp.com/ttttt/ksss.php
https://poly-genz.duckdns.org//wp-admin/dc/pdfnglw.php
https://qefgghx.ga/.well-known/e/drp.php
https://rainfordane.com/urgent/exc.phptA
https://raw.githubusercontent.com/itesfites/test/master/invoice.doc
https://ronaldobelo.com.br/gag/zz.php?emr:
https://ronaldobelo.com.br/user/zz.php?email=o3oDydf4+3!67
https://ronlunsford.ru.com/uer/drpbo.php
https://rumah-hijab.com/wp-content/lkx/linkedin.php
https://s.wsj.net/public/resources/images/bn-tq260_2yuci_or_20170529004947.jpg
https://s3.amazonaws.com/rewqqq/anabel.exe
https://s3.amazonaws.com/rewqqq/wizzy.exe
https://sapanagrossi.com/w_/lognet1.pr
https://se.bsxm5.za.com/htp/excel.php
https://secure05b.chase.com/
https://securemail.us.hsbc.com/brand/br/us_hsbc_en/rv/833b6/resources/common/icon_encrypted.png
https://shopget24.com/images/sampledata/hack-
https://shoppingcart.gcstation.net/scripts/jquery.min.js
https://smallpdf.com/file#s=3bad29f0-b7e6-4738-926a-be54c92347a9
https://smartforms.dev/submit/65a1ecdb5df1517d48d8c3a1
https://smartforms.dev/submit/66b155bb5df1517d48d92230
https://smartforms.dev/submitmM
https://submit-form.com
https://submit-form.com/
https://submit-form.com/0caprhunw
https://submit-form.com/2ajdurvf8
https://submit-form.com/2ee4liik
https://submit-form.com/2on85hcu
https://submit-form.com/3edxro1ib
https://submit-form.com/3wvw8ofd
https://submit-form.com/6p2duvfqc
https://submit-form.com/6txowyzh
https://submit-form.com/76kkkdre9
https://submit-form.com/8puq8ubh8
https://submit-form.com/aQ
https://submit-form.com/aff4yp5l
https://submit-form.com/bgwzvsp8u
https://submit-form.com/bilgr1vho
https://submit-form.com/c0tkamrea
https://submit-form.com/cbasemlvi
https://submit-form.com/chxkfnu9
https://submit-form.com/cvqeffxlq
https://submit-form.com/djhcrfv4aeC
https://submit-form.com/dll9c60x
https://submit-form.com/ebzgv387
https://submit-form.com/eiehc6zx
https://submit-form.com/enlodk3j
https://submit-form.com/fD
https://submit-form.com/fmjgnmk7
https://submit-form.com/fq6urgdfx
https://submit-form.com/g0phkum5j
https://submit-form.com/gskudflwh
https://submit-form.com/hvvtcib6e
https://submit-form.com/i3ighvr8p
https://submit-form.com/ia4i0qbom
https://submit-form.com/ioe941n1l
https://submit-form.com/iqtst6yay
https://submit-form.com/jpkawfua
https://submit-form.com/jythjdcfs
https://submit-form.com/jzgqwvfpo
https://submit-form.com/k1cvdmtpr
https://submit-form.com/kmedpfjuh
https://submit-form.com/kqw112la
https://submit-form.com/lbhfwcilk
https://submit-form.com/ldwewlmg
https://submit-form.com/llcsw6ujk
https://submit-form.com/lmptu8hoh
https://submit-form.com/lrzcpr1h
https://submit-form.com/lxwbl42z6
https://submit-form.com/mX
https://submit-form.com/meubzxxc3
https://submit-form.com/mgfkhddrpm]
https://submit-form.com/nxyhfhncv
https://submit-form.com/nz8ngufex
https://submit-form.com/o05tapohmI
https://submit-form.com/o[
https://submit-form.com/olm8iphzj
https://submit-form.com/ovgwqjm1f
https://submit-form.com/pgpihyda
https://submit-form.com/pkpf0zmxm
https://submit-form.com/povnxeoyj
https://submit-form.com/q2vsjwxqw
https://submit-form.com/q2ypwoy4n
https://submit-form.com/qdskcanu
https://submit-form.com/qomoswfy
https://submit-form.com/r2ae0zqkj
https://submit-form.com/rI
https://submit-form.com/rM
https://submit-form.com/rp1om2tsq
https://submit-form.com/sexzu1fj
https://submit-form.com/slj7cpecz
https://submit-form.com/srppqotok
https://submit-form.com/stpmnmysu
https://submit-form.com/tN
https://submit-form.com/tpskpkdb
https://submit-form.com/tw1lyzlej
https://submit-form.com/usxdukmf
https://submit-form.com/utfo5fxh7
https://submit-form.com/utzvmcuz
https://submit-form.com/vxvlfh4rb
https://submit-form.com/vzedihoj
https://submit-form.com/w
https://submit-form.com/wwytr1ern
https://submit-form.com/x31atct1q
https://submit-form.com/x7pcavu0v
https://submit-form.com/xplcrdxq
https://submit-form.com/y5hvesul
https://submit-form.com/yhpa0fyqv
https://submit-form.com/ypyj8amqe
https://submit-form.com/yqmmdalm
https://submit-form.com/z2d6t6n22
https://submit-form.com/zo8xw81mk
https://submit-form.comdp
https://submit-form.comfg
https://submit-form.como3
https://submit-form.comrl
https://suzhoupack.za.com//index/fedex.php
https://tezorepoace.shop/
https://thebrand-bomb.com/payment/exc.phd$
https://thumbs.dreamstime.com/b/dhl-logo-editorial-illustrative-white-bac
https://thumbs.dreamstime.com/b/dhl-logo-editorial-illustrative-white-background-eps-download-vector-jpeg-banner-dhl-logo-editorial-illustrative-white-208329232.jpg
https://tinyurl.com/2fzd45n3
https://tinyurl.com/9n5e8mtp
https://tinyurl.com/yvemcwzc/dbx.phpft
https://togeldulu.net/wp-content/themes/pridmag/_n0tes./_all.fl/excel/excel.phrB
https://ufabumtorg.ru/assets/images/dhl/dhlphpoyin.php
https://upload.wikim
https://upload.wikimedia.org/wikipedia/commons/thumb/3/34/microsoft_
https://upload.wikimedia.org/wikipedia/commons/thumb/3/34/microsoft_office_excel_%282019%e2%80%93present%29.svg/
https://upload.wikimedia.org/wikipedia/commons/thumb/3/34/microsoft_office_excel_%282019%e2%80%93present%29.svg/2203px-microsoft_office_excel
https://upload.wikimedia.org/wikipedia/commons/thumb/3/34/microsoft_office_excel_%282019%e2%80%93present%29.svg/2203px-microsoft_office_excel_%282019%e2%80%93present%29.svg.png
https://veckerglobal.com/jo/lognet1.phpe!
https://vostoabzar.com/excelsheet/xls.php
https://webcdnstore.pw/jqueryui.js'
https://winepress.top/clear/excell.php
https://www.2345.com/?k54067673
https://www.actionforms.io/e/r/chi
https://www.adobe.com/favicon.ico
https://www.auspareparts.com/po/exc.php
https://www.ax4.com/ax4/pix/loginpage/business/backgrounds/2012421/bg.jpg
https://www.billboardarena.com.ng/w@/lognet1.php
https://www.blogger.com/navbar.g?targetblogid
https://www.deltasociety.com.au/assets/img/logo-deltasoc.jpg
https://www.dhl.com/content/dam/dhl/glo
https://www.facebook.com/dukomputer's(
https://www.fedex.com
https://www.fedex.com/content/dam/fedex/us-united-statesbU
https://www.fedex.com/en-us/home.html.html
https://www.fedex.com/etc.clientlibs/designs/fedex-common/images/resources/fx-favicon.ico
https://www.formbackend.com/f/0eeb73ce9c75ef84
https://www.formbackend.com/f/64d8c5d3d6d94174
https://www.googlet
https://www.hostingcloud.racing/'
https://www.patrickmaulion.com/images/logomotion/15-dhl.gif
https://www.paypal.com/us/cgi-bin/webscr?cmd=xpt/marketing/popup/olcwhatispaypal-outside'
https://www.paypalobjects.com/en_us/i/icon/pp_favicon_x.ic
https://www.pflasterbau-dumler.de/wp-includes/js/dist/vendor/regenerator-runtime.min.js?ver=0.13.7'
https://www.socialenterprisebsr.net/wp-content/uploads/2018/11/wetransfer-logo.png
https://www.sugarsync.com/pf/d3318892_838_463584328?directdownload=true
https://www.upload.ee/download/
https://www.witafood.com/bank/swift
https://xn----7sbehjpo0aloefjp8kya.xn--p1ai/akk/excel.php
https://yhwx.mypi.co/fed/fdxx.php
https://ziafud.com/aba/ade.php
https://zlehxan.com/new_po.php
https://zooidec.tk/dbx.php
https://zresiiler.za.com/fdx/fdxx.php
(PID) Process(6020) QMDL.exe
Decrypted-URLs (1)https://pm.myapp.com/invc/xfspeed/plugin/Release/QMSoftMgrSetup_17.12.29269.301__1770301803198.exe?keyid=1309fd27661caa185ecde3f621420684
Decrypted-URLs (1)https://pm.myapp.com/invc/xfspeed/plugin/Release/QMFileSmashProSetup_17.11.28973.206__1764299558601.exe?keyid=c66358d480afcb9b5d3d18bfdb18c66d
Decrypted-URLs (5)https://dldir2.qq.com/invc/xfspeed/tavupdate/R13800T20260119213215Engine.zip?keyid=e26081f5444851ec4754b7d19d709307
https://dldir2.qq.com/invc/xfspeed/tavupdate/R13800T20260126213213LibDef.zip?keyid=5030e8d91dafbddb97f409887fa3aeca
https://pm.myapp.com/invc/xfspeed/plugin/Release/QMFileSmashProSetup_17.11.28973.206__1764299558601.exe?keyid=c66358d480afcb9b5d3d18bfdb18c66d
https://pm.myapp.com/invc/xfspeed/plugin/Release/QMSoftMgrSetup_17.12.29269.301__1770301803198.exe?keyid=1309fd27661caa185ecde3f621420684
https://webcdn.m.qq.com/pcmgr_plugin/SoftMgrCtrl_17.12.29269.301_1770360444803.xml?keyid=fb4d631af9bdb30cc26e5b3e0e5c4893
DcRat
(PID) Process(8828) QQPCRTP.exe
C2 (1)http://m.facebook.com/login.php
Total processes
295
Monitored processes
147
Malicious processes
11
Suspicious processes
24
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 524 | --connect-timeout 3 --location --request POST "https://otheve.beacon.qq.com/analytics/v2_upload" --header "Content-Type: application/json" --data-raw "{\"common\": {\"A2\": \"\", \"A3\": \"\", \"A23\": \"10072\", \"A153\": \"\", \"HY99\": \"\", \"HY502\": \"4\", \"HY501\": \"Install failed: 80\"}, \"events\": [{\"eventCode\": \"install_finish\", \"eventTime\": \"1771807127000\"}], \"appVersion\": \"2.56.0.621\", \"sdkId\": \"js\", \"sdkVersion\": \"\", \"mainAppKey\": \"0WIN06DPC0UV5DHL\", \"platformId\": \"3\"}" | C:\Windows\Temp\report_helper.exe | yuanbao_10072_x64.exe | ||||||||||||
User: admin Company: curl, https://curl.haxx.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 7.64.1.1 Modules
| |||||||||||||||
| 1176 | "C:\Program Files (x86)\Tencent\QQPCMgr\17.11.28973.206\QQPCSoftCmd.exe" /command=GetQimei | C:\Program Files (x86)\Tencent\QQPCMgr\17.11.28973.206\QQPCSoftCmd.exe | QQPCRTP.exe | ||||||||||||
User: SYSTEM Company: Tencent Integrity Level: SYSTEM Description: 电脑管家-软件管理外部进程 Version: 17.11.28973.206 Modules
| |||||||||||||||
| 1368 | "C:\Program Files (x86)\Tencent\QQPCMgr\17.11.28973.206\InjectHostExe64.exe" | C:\Program Files (x86)\Tencent\QQPCMgr\17.11.28973.206\InjectHostExe64.exe | — | QQPCTray.exe | |||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: 腾讯电脑管家-文件搜索注入辅助 Exit code: 0 Version: 17.11.28973.206 Modules
| |||||||||||||||
| 1400 | consent.exe 1032 444 000001AEED227AA0 | C:\Windows\System32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1400 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5536,i,7185560769999294903,15822164138349350352,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6052 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1424 | "C:\Users\admin\Downloads\QQPCDownload_home_310053.exe" | C:\Users\admin\Downloads\QQPCDownload_home_310053.exe | — | msedge.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 腾讯电脑管家在线安装程序 Exit code: 3221226540 Version: 2.0.6.27 Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=4104,i,7185560769999294903,15822164138349350352,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7340 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6112,i,7185560769999294903,15822164138349350352,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7028 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7036,i,7185560769999294903,15822164138349350352,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6652 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1944 | "C:\Users\admin\Downloads\QQPCDownload_home_310053.exe" | C:\Users\admin\Downloads\QQPCDownload_home_310053.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 腾讯电脑管家在线安装程序 Version: 2.0.6.27 Modules
| |||||||||||||||
Total events
185 153
Read events
180 464
Write events
4 381
Delete events
308
Modification events
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000000000000000000 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000001501F0 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456E9BC50E45F05DB4C86F7D791C25A96C7 | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{e0a1eae5-0243-f936-e0ad-4ff9a16fd458}\Root\InventoryDevicePnp\pci/ven_8086&dev_100e&subsys_11001af4&rev_03/3&13c0b0c5&0&18 |
| Operation: | write | Name: | Model |
Value: Intel(R) PRO/1000 MT Network Connection | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{e0a1eae5-0243-f936-e0ad-4ff9a16fd458}\Root\InventoryDevicePnp\pci/ven_8086&dev_100e&subsys_11001af4&rev_03/3&13c0b0c5&0&18 |
| Operation: | write | Name: | Manufacturer |
Value: Intel | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{e0a1eae5-0243-f936-e0ad-4ff9a16fd458}\Root\InventoryDevicePnp\pci/ven_8086&dev_100e&subsys_11001af4&rev_03/3&13c0b0c5&0&18 |
| Operation: | write | Name: | DriverName |
Value: e1g6032e.sys | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{e0a1eae5-0243-f936-e0ad-4ff9a16fd458}\Root\InventoryDevicePnp\pci/ven_8086&dev_100e&subsys_11001af4&rev_03/3&13c0b0c5&0&18 |
| Operation: | write | Name: | ParentId |
Value: acpi\pnp0a03\1 | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{e0a1eae5-0243-f936-e0ad-4ff9a16fd458}\Root\InventoryDevicePnp\pci/ven_8086&dev_100e&subsys_11001af4&rev_03/3&13c0b0c5&0&18 |
| Operation: | write | Name: | MatchingID |
Value: pci\ven_8086&dev_100e | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{e0a1eae5-0243-f936-e0ad-4ff9a16fd458}\Root\InventoryDevicePnp\pci/ven_8086&dev_100e&subsys_11001af4&rev_03/3&13c0b0c5&0&18 |
| Operation: | write | Name: | Class |
Value: net | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{e0a1eae5-0243-f936-e0ad-4ff9a16fd458}\Root\InventoryDevicePnp\pci/ven_8086&dev_100e&subsys_11001af4&rev_03/3&13c0b0c5&0&18 |
| Operation: | write | Name: | ClassGuid |
Value: {4d36e972-e325-11ce-bfc1-08002be10318} | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{e0a1eae5-0243-f936-e0ad-4ff9a16fd458}\Root\InventoryDevicePnp\pci/ven_8086&dev_100e&subsys_11001af4&rev_03/3&13c0b0c5&0&18 |
| Operation: | write | Name: | Description |
Value: Intel(R) PRO/1000 MT Network Connection | |||
Executable files
1 057
Suspicious files
909
Text files
589
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8108 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e5179.TMP | — | |
MD5:— | SHA256:— | |||
| 8108 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e5179.TMP | — | |
MD5:— | SHA256:— | |||
| 8108 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e5179.TMP | — | |
MD5:— | SHA256:— | |||
| 8108 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8108 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8108 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e5179.TMP | — | |
MD5:— | SHA256:— | |||
| 8108 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e5179.TMP | — | |
MD5:— | SHA256:— | |||
| 8108 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e5179.TMP | — | |
MD5:— | SHA256:— | |||
| 8108 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8108 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
438
TCP/UDP connections
692
DNS requests
194
Threats
159
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 314 b | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
3352 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:uL2bK8p1q5yIrBVCMqa0EpcrL8QN_lsKPIjxJvxFabA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 98 b | whitelisted |
3352 | msedge.exe | GET | 200 | 13.107.246.45:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
3352 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1771807098&lafgdate=0 | US | text | 4.47 Kb | whitelisted |
3352 | msedge.exe | GET | 200 | 43.135.106.241:443 | https://guanjia.qq.com/main.html | CN | html | 97.8 Kb | unknown |
3352 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
3352 | msedge.exe | GET | 200 | 43.135.106.241:443 | https://guanjia.qq.com/assets/css/style-v17.css?_t=202302151815 | CN | text | 29.7 Kb | unknown |
3352 | msedge.exe | GET | 200 | 43.135.106.241:443 | https://guanjia.qq.com/assets/css/header-v17.css?_t=20230209 | CN | text | 14.3 Kb | unknown |
3352 | msedge.exe | GET | 200 | 2.16.204.141:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | text | 665 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8068 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5180 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.204.141:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.63.118.230:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3352 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
guanjia.qq.com |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5180 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
3352 | msedge.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
1944 | QQPCDownload_home_310053.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
7408 | yuanbao_10072_x64.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] NSIS INetC plugin User-Agent observed in HTTP request |
3700 | 25814.exe | Generic Protocol Command Decode | SURICATA HTTP URI terminated by non-compliant character |
3700 | 25814.exe | Generic Protocol Command Decode | SURICATA HTTP METHOD terminated by non-compliant character |
3700 | 25814.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Invalid HTTP Method |
8828 | QQPCRTP.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Invalid HTTP Method |
8828 | QQPCRTP.exe | Generic Protocol Command Decode | SURICATA HTTP METHOD terminated by non-compliant character |
4948 | QQPCTray.exe | Generic Protocol Command Decode | SURICATA HTTP Request line incomplete |
Process | Message |
|---|---|
QQPCMgr_Setup.exe | "cacls" "C:\Program Files (x86)\Tencent\QQPCMgr\17.11.28973.206" /t /e /c /g SYSTEM:f |
QQPCSoftCmd.exe |
=========== mem dump after here is valid ========
|
QQPCMgr_Setup.exe | "C:\Program Files (x86)\Tencent\QQPCMgr\17.11.28973.206\QQPCRTP.exe" -e |
QQPCMgr_Setup.exe | "C:\Program Files (x86)\Tencent\QQPCMgr\17.11.28973.206\QQPCRTP.exe" -s |
QQPCMgr_Setup.exe | "C:\Program Files (x86)\Tencent\QQPCMgr\17.11.28973.206\QQPCTray.exe" /regrun |
QQPCMgr_Setup.exe | "C:\Users\admin\AppData\Local\Temp\Tencent\QQPCMgr\~1f1779\UpdateTrayIcon.exe" -t QQPCTray.exe -c 1 -p 1 -v 0 -h "" -d "C:\Program Files (x86)\Tencent\QQPCMgr\17.11.28973.206\" |
explorer.exe | [InjectStubDll]CreateWindowQMFileSearchClassNew{B672D2D5-2762-44AF-A358-BEBEB9080E59} |
explorer.exe | [19:40:31.592][P:4972][T:4264][271][LogTaskBarAlwaysOnTopState] TrayRocket taskBarAlwaysOnTop true.
|
explorer.exe | [19:40:31.592][P:4972][T:4264][281][LogTaskBarSmallIconsState] TrayRocket taskBarSmallIcons false.
|
explorer.exe | [19:40:31.592][P:4972][T:4264][1200][InstallHook] TrayRocket InstallHook Success
|