| File name: | d08d191db5cdedde0a9d647ff4e33859f7ac11d594bf0beed41ad6cd19d9200c |
| Full analysis: | https://app.any.run/tasks/4d55777c-34a8-4bbf-992c-09d6c38e132e |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | February 24, 2025, 08:12:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
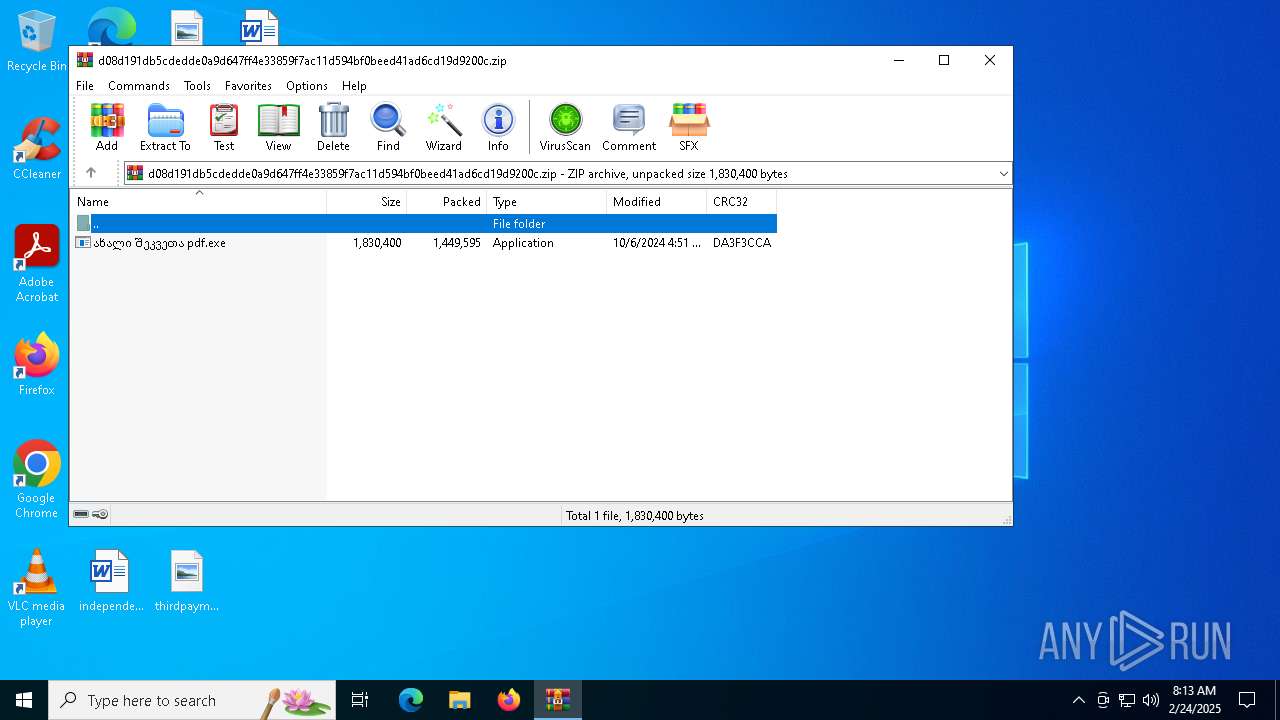
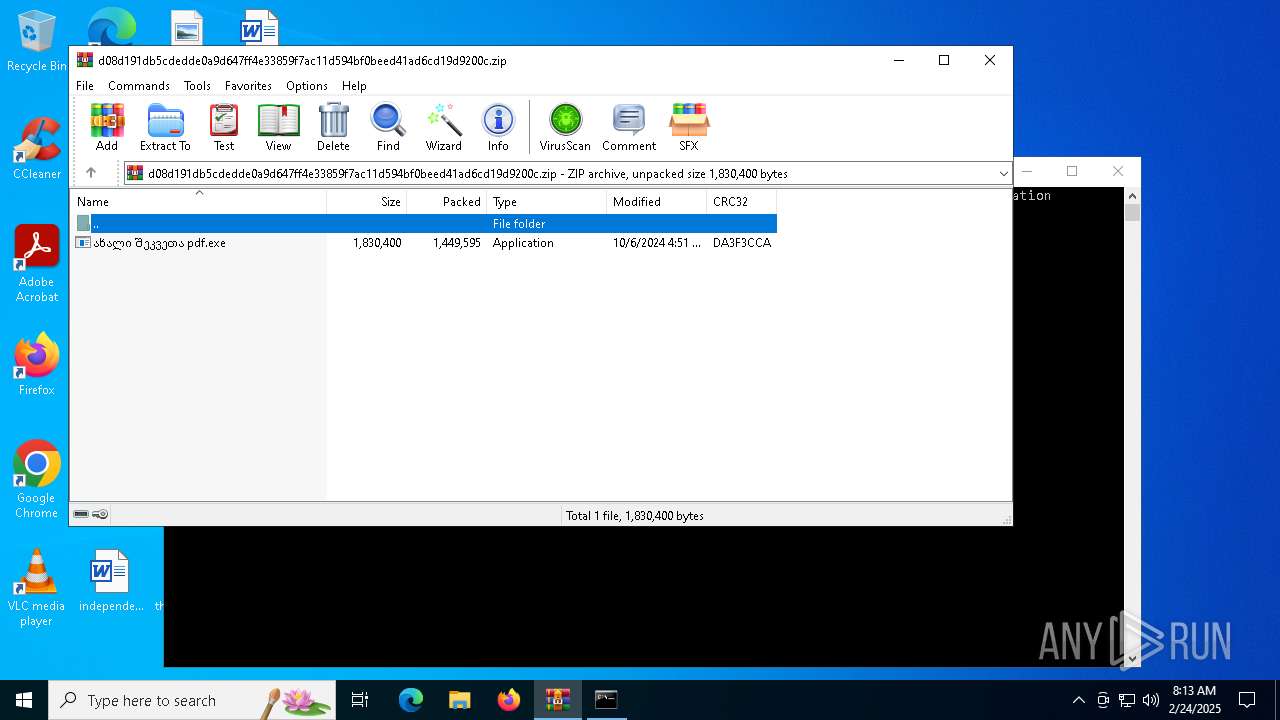
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | D0C645939DA021B05A6FF8D3E2586B08 |
| SHA1: | EC6C4AFEB76C267C3ABAC9209E308EABA3AA1255 |
| SHA256: | D08D191DB5CDEDDE0A9D647FF4E33859F7AC11D594BF0BEED41AD6CD19D9200C |
| SSDEEP: | 49152:0UqFuQ0W8nY0W032Xcu2py2t43W0xc4nhRn/tlTYqf85MboQazaqqhp/Hbs3YwEg:0U0uQ0M0WbXkNt4msVnTVFzboQazsL7a |
MALICIOUS
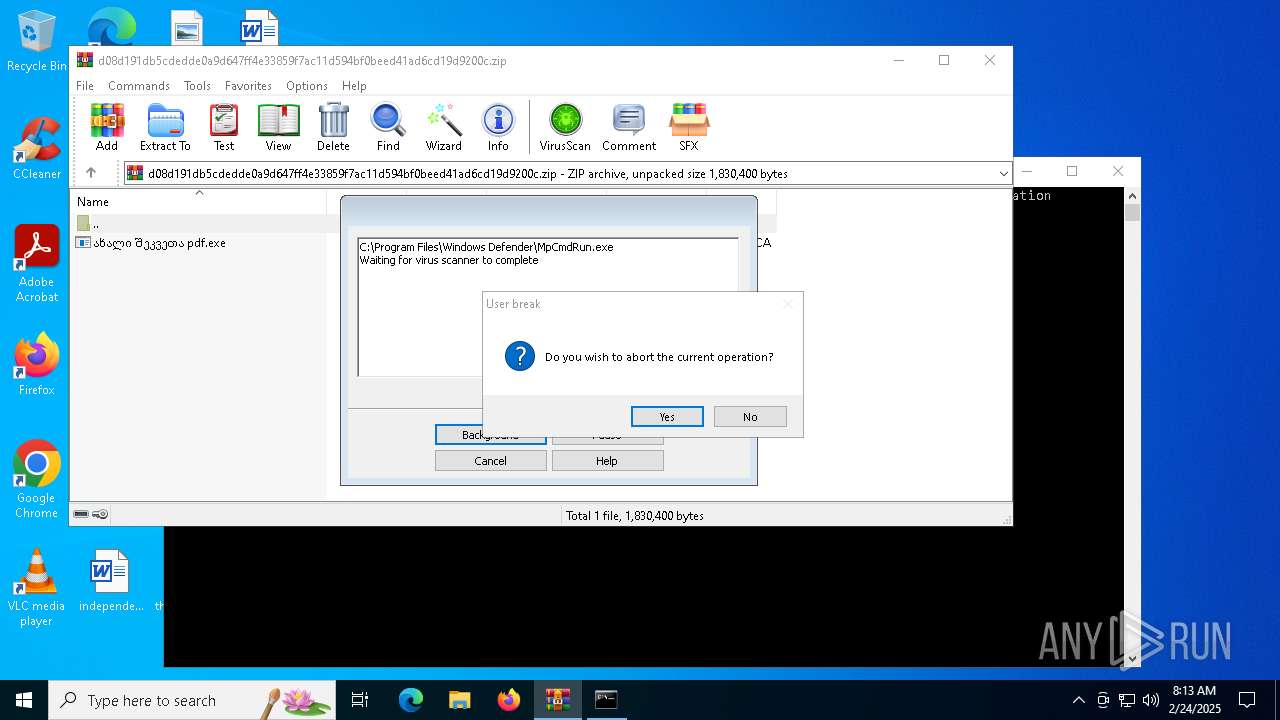
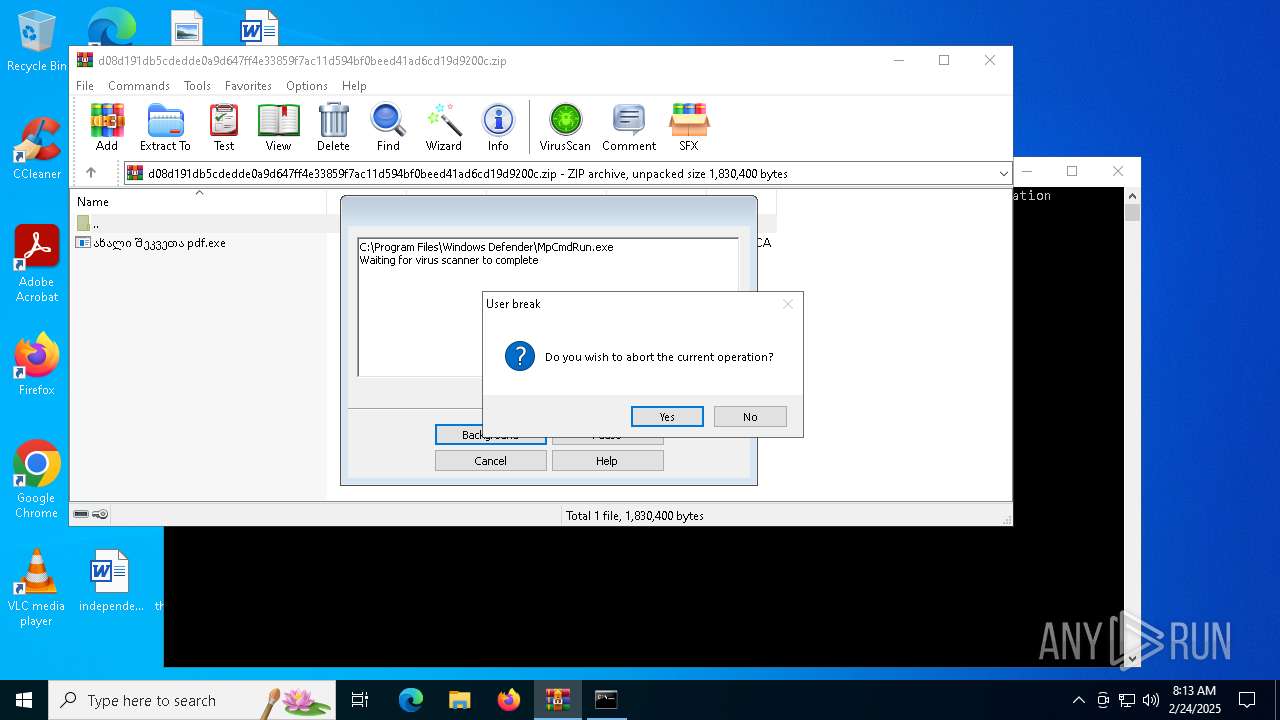
Generic archive extractor
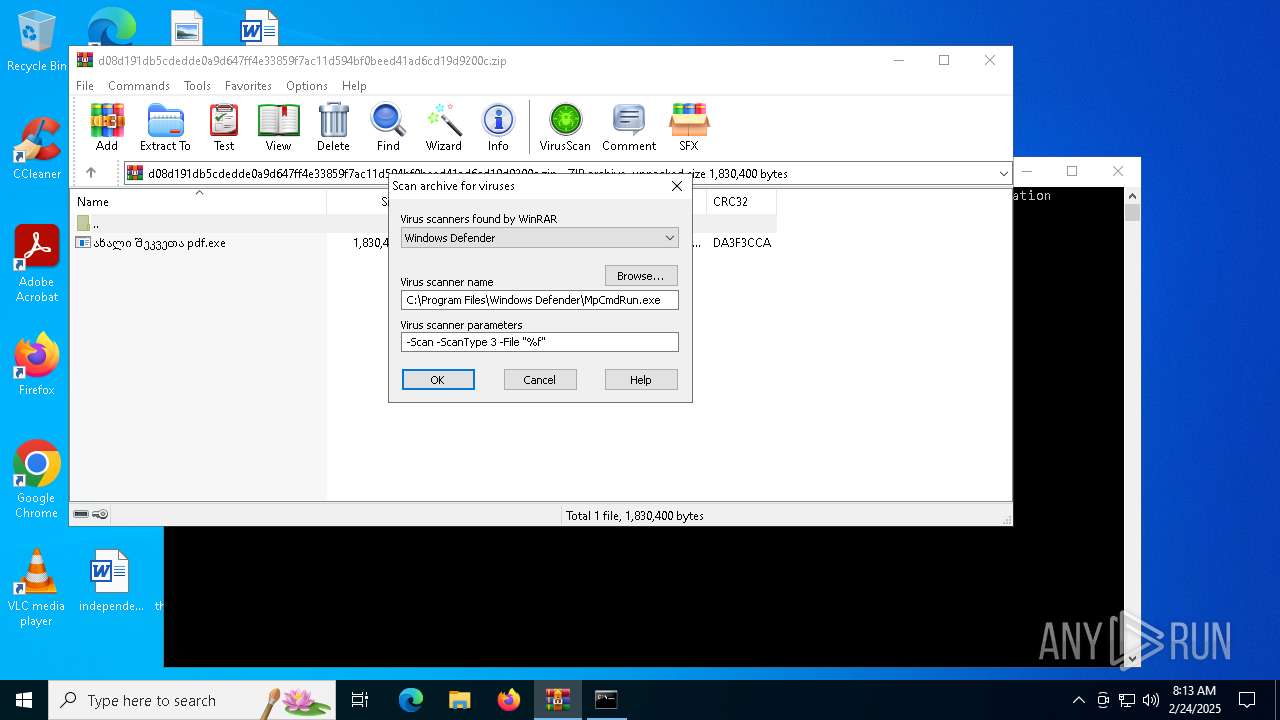
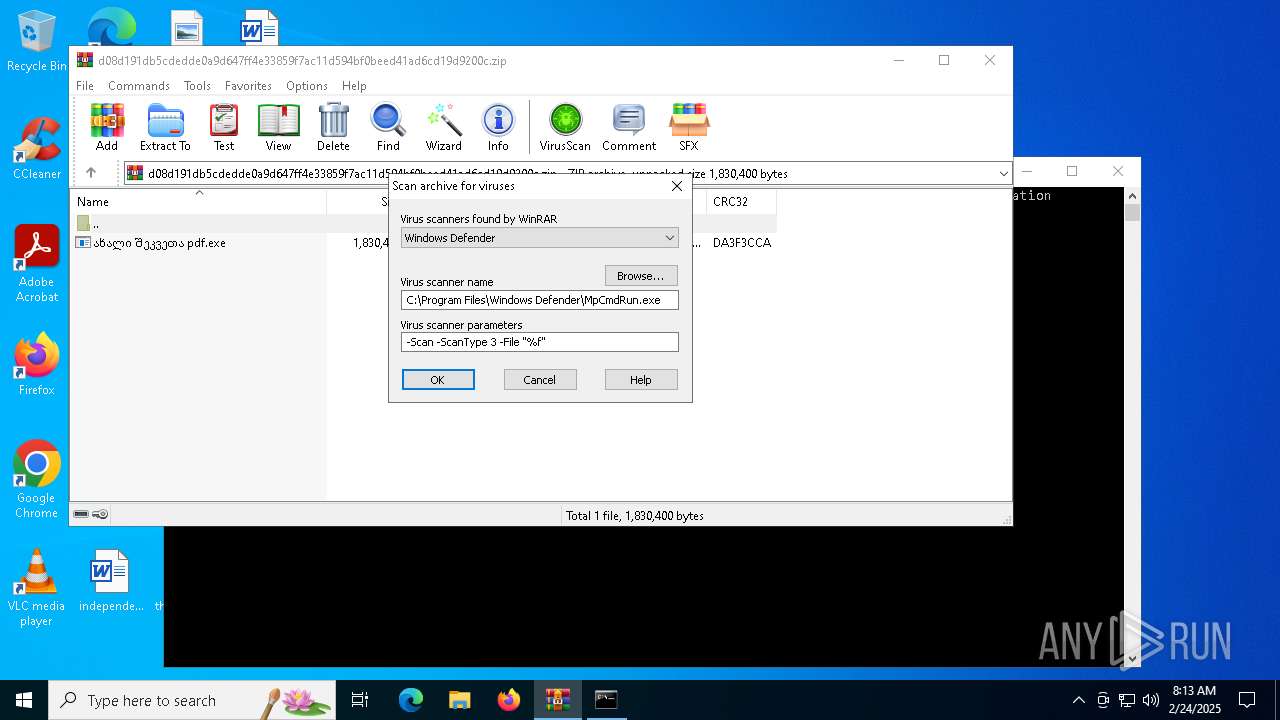
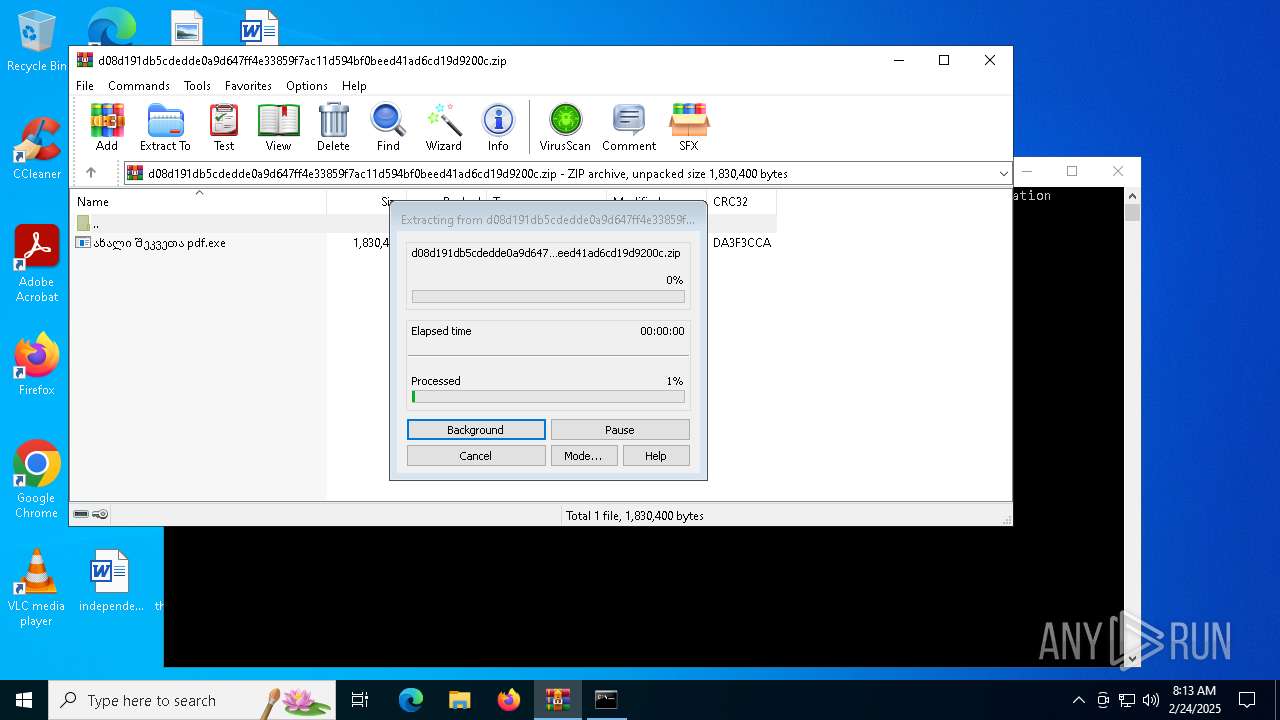
- WinRAR.exe (PID: 3172)
FORMBOOK has been detected
- explorer.exe (PID: 4488)
- WWAHost.exe (PID: 4516)
FORMBOOK has been detected (YARA)
- WWAHost.exe (PID: 4516)
FORMBOOK has been detected (SURICATA)
- explorer.exe (PID: 4488)
Connects to the CnC server
- explorer.exe (PID: 4488)
Create files in the Startup directory
- ახალი შეკვეთა pdf.exe (PID: 2136)
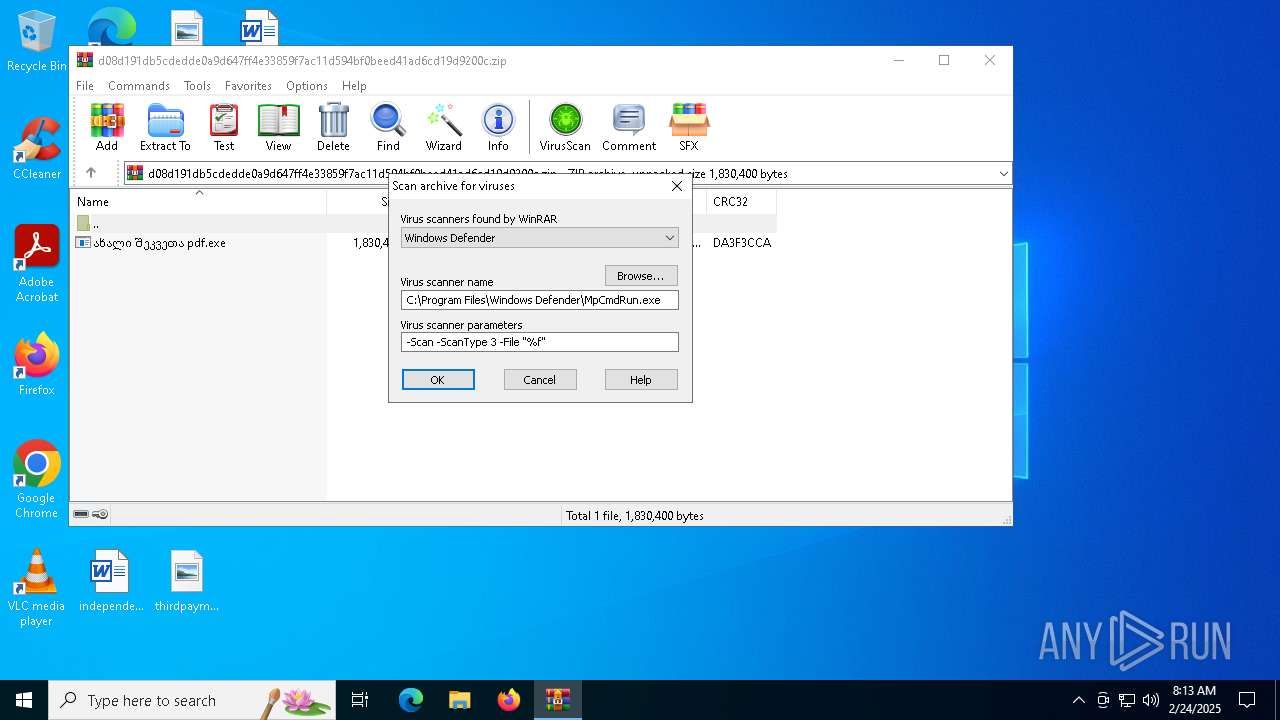
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3172)
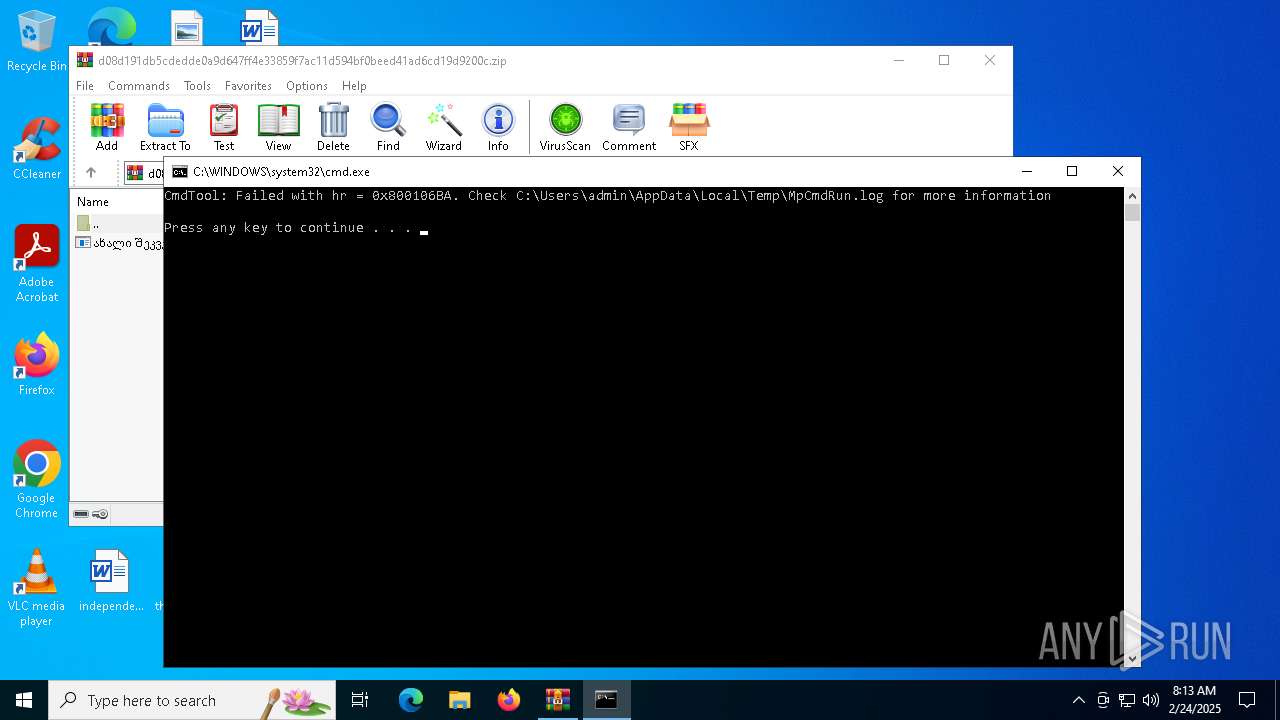
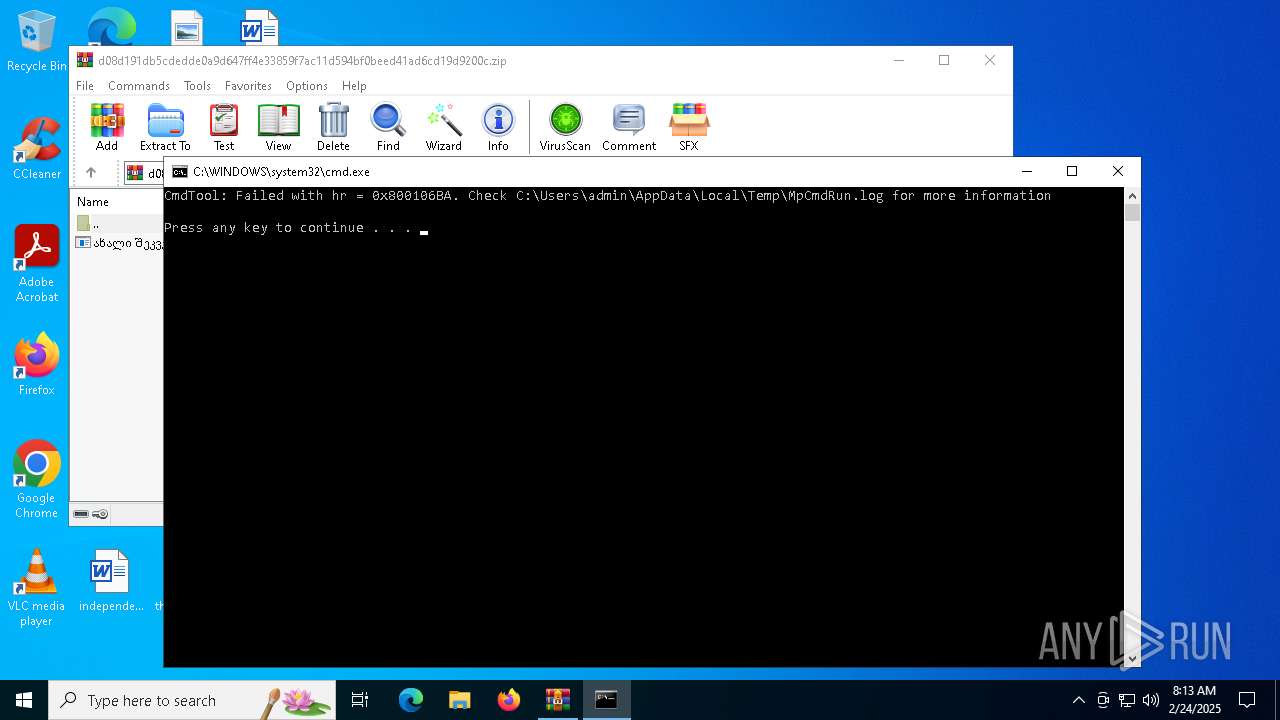
Executing commands from a ".bat" file
- WinRAR.exe (PID: 3172)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 3172)
- WWAHost.exe (PID: 4516)
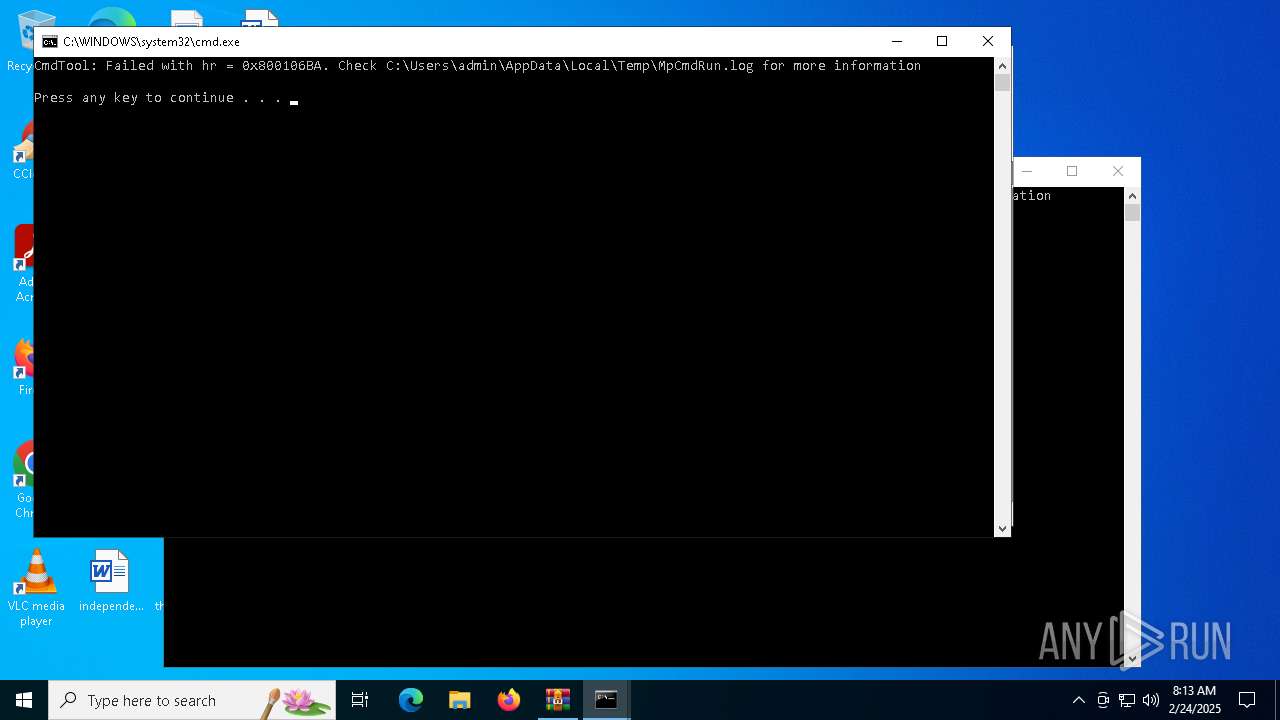
Deletes system .NET executable
- cmd.exe (PID: 4164)
Contacting a server suspected of hosting an CnC
- explorer.exe (PID: 4488)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
Checks supported languages
- ახალი შეკვეთა pdf.exe (PID: 2136)
- InstallUtil.exe (PID: 3732)
- MpCmdRun.exe (PID: 3040)
- MpCmdRun.exe (PID: 2212)
Manual execution by a user
- ახალი შეკვეთა pdf.exe (PID: 2136)
- autoconv.exe (PID: 4444)
- autoconv.exe (PID: 2160)
- autoconv.exe (PID: 4816)
- autoconv.exe (PID: 5236)
- autoconv.exe (PID: 1412)
- WWAHost.exe (PID: 4516)
- autoconv.exe (PID: 732)
- InstallUtil.exe (PID: 3732)
- autoconv.exe (PID: 3620)
Reads the machine GUID from the registry
- ახალი შეკვეთა pdf.exe (PID: 2136)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3172)
Reads the computer name
- MpCmdRun.exe (PID: 3040)
- MpCmdRun.exe (PID: 2212)
- InstallUtil.exe (PID: 3732)
- ახალი შეკვეთა pdf.exe (PID: 2136)
Create files in a temporary directory
- MpCmdRun.exe (PID: 3040)
Creates files or folders in the user directory
- ახალი შეკვეთა pdf.exe (PID: 2136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(4516) WWAHost.exe
C2www.eautifulnewworld.info/ka18/
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)dityainfotech.shop
ebseller.top
oxyroxy.store
olar-systems-panels-64244.bond
ediora.health
ech-ethan.xyz
erradaibiapaba.online
s94ngz.pro
ameishop.sbs
insosuksmono.info
kyro.ovh
mmn.fun
4-abua.help
rder5700.info
eto.health
hekio.online
balan.net
pt9y5.mom
aterfeed.online
ogic-tent.xyz
tss.world
6816416.vip
arrrroto.top
ceheidong.net
y051.xyz
etkaizen.info
ebrastream.online
g51-fyie993.vip
on-espace-client-sofinc0.shop
agerit.info
lcbmovies.live
entist-dental-care-75596.bond
iporexinaluvo.click
0-25-jpzxn8.vip
okerdom-online-games-36.top
olar-panel-4872.click
rancoisinnovation.net
agproject.net
eregasasha.store
aksymkushnirov.pro
0it-compserv.life
iscgolfscene.travel
opsjdl.xyz
igmatylerman.club
0vryerf.shop
atik178.online
arsh.store
egafinds-latina.shop
enovhojecnhi.shop
ontractapproval.help
he-bahamas-travel-green.sbs
edmaw.xyz
etboro.now
acqua.shop
9000.net
nlockyourapprovedratetoday.xyz
ragmetrric.top
av01.cyou
esvo.net
avebigonpolicydealsnow.xyz
770303.net
okqrgb.top
asy2go.online
101asubatayidistsatlari.xyz
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:10:06 05:51:58 |
| ZipCRC: | 0xda3f3cca |
| ZipCompressedSize: | 1449595 |
| ZipUncompressedSize: | 1830400 |
| ZipFileName: | ახალი შეკვეთა pdf.exe |
Total processes
135
Monitored processes
21
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 732 | "C:\Windows\SysWOW64\autoconv.exe" | C:\Windows\SysWOW64\autoconv.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto File System Conversion Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | "C:\Windows\SysWOW64\autoconv.exe" | C:\Windows\SysWOW64\autoconv.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto File System Conversion Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\Desktop\ახალი შეკვეთა pdf.exe" | C:\Users\admin\Desktop\ახალი შეკვეთა pdf.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: yeni sifariş Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2160 | "C:\Windows\SysWOW64\autoconv.exe" | C:\Windows\SysWOW64\autoconv.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto File System Conversion Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR3172.12135" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2624 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR3172.10452\Rar$Scan7399.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3040 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR3172.10452" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3172 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\d08d191db5cdedde0a9d647ff4e33859f7ac11d594bf0beed41ad6cd19d9200c.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
3 293
Read events
3 267
Write events
26
Delete events
0
Modification events
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000602D6 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010014000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C0000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000000D0000000000000053006B007900700065002E006C006E006B003E0020007C000000130000000000000061006C00620075006D0069006E0063006500730074002E006A00700067003E002000200000000E000000000000006100720065006200750073002E007200740066003E00200020000000110000000000000062006F00780063006F0075007200730065002E0070006E0067003E002000200000001A0000000000000069006E0064006500700065006E00640065006E00740065006E0067006C0061006E0064002E007200740066003E0020002000000012000000000000006D0069006E0064007200650061006400650072002E006A00700067003E0020002000000011000000000000006D00750073006900630072006100740065002E007200740066003E002000200000001A000000000000006E006100740069006F006E0061006C00720065007300740061007500720061006E0074002E007200740066003E0020002000000012000000000000006E0075006D006200650072006D006F00760065002E007200740066003E002000200000001A0000000000000073006300690065006E006300650069006E0074006500720065007300740069006E0067002E007200740066003E002000200000001400000000000000740068006900720064007000610079006D0065006E0074002E006A00700067003E002000200000001100000000000000770068006F006C0065006F00680069006F002E007200740066003E00200020000000480000000000000064003000380064003100390031006400620035006300640065006400640065003000610039006400360034003700660066003400650033003300380035003900660037006100630031003100640035003900340062006600300062006500650064003400310061006400360063006400310039006400390032003000300063002E007A00690070003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001400000000000000000000000000000000000000803F0000004008000000803F0000404009000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F0000000040000080401000000000400000A040110000004040000000001200000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F0700000040400000803F1300 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 142ABC6700000000 | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\d08d191db5cdedde0a9d647ff4e33859f7ac11d594bf0beed41ad6cd19d9200c.zip | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
2
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4488 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 3172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3172.12135\d08d191db5cdedde0a9d647ff4e33859f7ac11d594bf0beed41ad6cd19d9200c.zip\ახალი შეკვეთა pdf.exe | executable | |
MD5:628C83E58275913F3BDF1B328D89D39E | SHA256:B49F42E5F590D5CFA26C7DDE4F0DF0B283351A9652FE42C41227FD4EB5FACC38 | |||
| 2136 | ახალი შეკვეთა pdf.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\IsClosed.vbs | text | |
MD5:6AC1D10B99E6EE955EFABE8AAAF005D3 | SHA256:A12F20865A14013D1ECE974D507A9A485442B1D5A9F5B4A303443B3FF1197AC5 | |||
| 3172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3172.10452\d08d191db5cdedde0a9d647ff4e33859f7ac11d594bf0beed41ad6cd19d9200c.zip\ახალი შეკვეთა pdf.exe | executable | |
MD5:628C83E58275913F3BDF1B328D89D39E | SHA256:B49F42E5F590D5CFA26C7DDE4F0DF0B283351A9652FE42C41227FD4EB5FACC38 | |||
| 3172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3172.12135\Rar$Scan24509.bat | text | |
MD5:4CB85491AAFE40049B47AD91542F5D83 | SHA256:CD3E41F248CFCC6398000D6FF2CBDB7C81686A2059AE71B14863BFE996490F2A | |||
| 3172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3172.10452\Rar$Scan7399.bat | text | |
MD5:149517A199E2237E43DA9420DF8A173F | SHA256:B8D1482338E0D3E7B927A1B3A33995C315BFAD9901A720F378AC1C9D1047B109 | |||
| 3040 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | binary | |
MD5:932BA2CC18A5BDD380B3CB0254EF43F5 | SHA256:1BDD54C9234DDB2D7A5D6369F2C295E7945696A8726105EC23A1BD68111A81F3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
20
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
488 | svchost.exe | GET | 200 | 23.48.23.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
488 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 301 | 76.223.105.230:80 | http://www.arsh.store/ka18/?DT_l=+QC9LkfKp7e5t1rvBKoBbJ+BPhNTS74CSsnHxVer9IwXgrItV1p1NXVRMZkU3MHNv6r1&VjCD=npv0jh4xpVk | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
488 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.123.104.35:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
488 | svchost.exe | 23.48.23.138:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
488 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4488 | explorer.exe | 76.223.105.230:80 | www.arsh.store | AMAZON-02 | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.s94ngz.pro |
| unknown |
www.eautifulnewworld.info |
| unknown |
www.etkaizen.info |
| unknown |
www.ediora.health |
| unknown |
www.ceheidong.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4488 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |