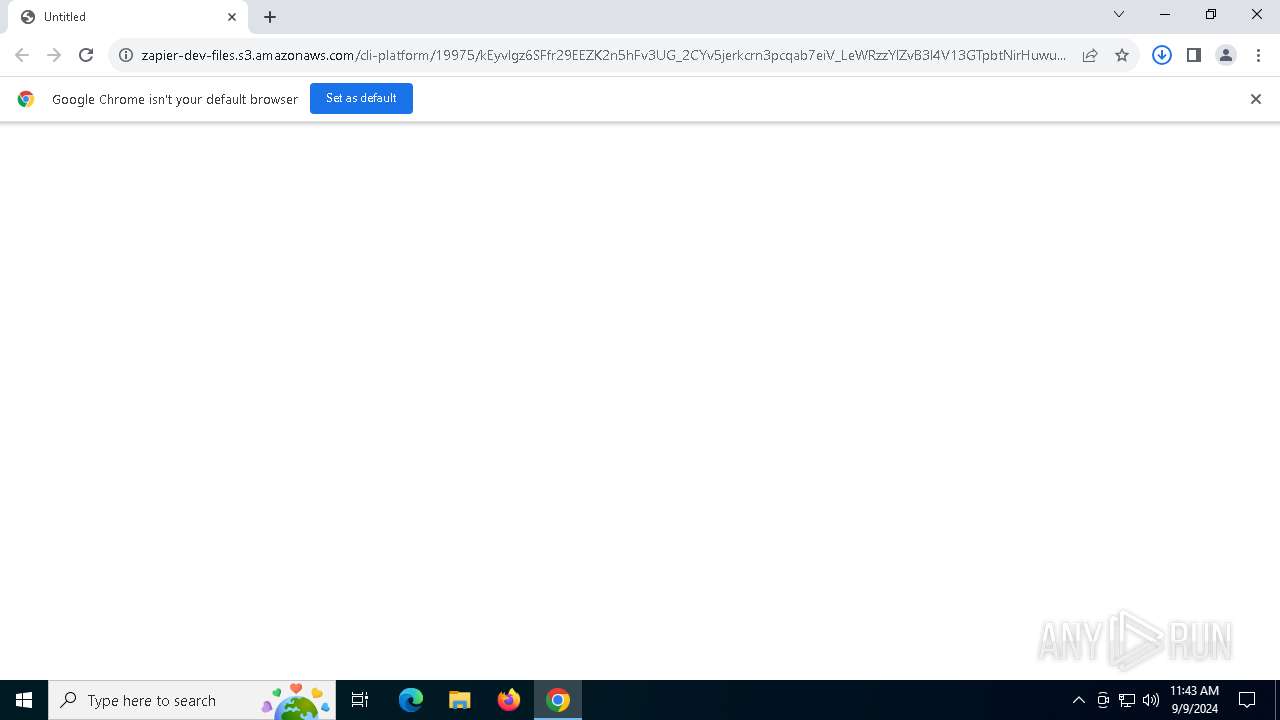
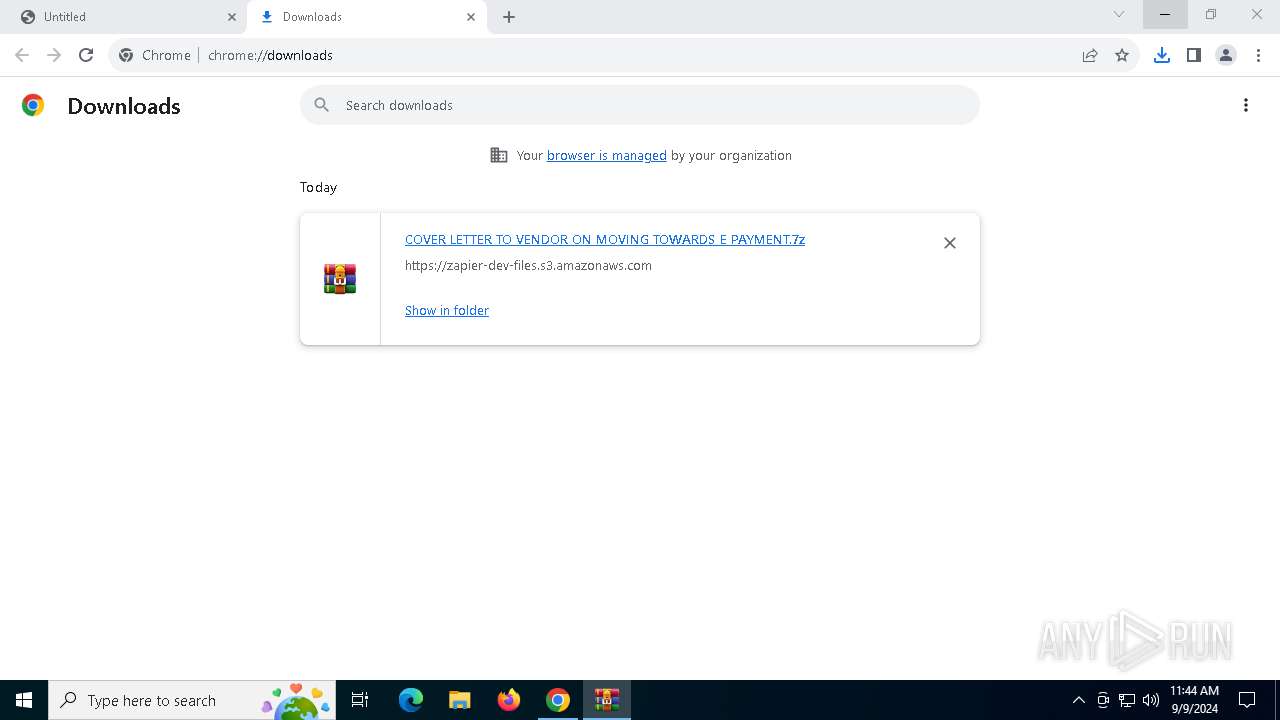
| URL: | https://zapier-dev-files.s3.amazonaws.com/cli-platform/19975/kEyvlgz6SFfr29EEZK2n5hFv3UG_2CYv5jerkcrn3pcqab7eiV_LeWRzzYlZvB3l4V13GTpbtNirHuwu5BDFSqNX9GLVStEVwOh9vC4M-HRb4D3jn_fK5I47bn_aWXhY8z5JwchJWCEUMRgmtiX5gyLyL1_eTu1SyXRsQ1PaNbI |
| Full analysis: | https://app.any.run/tasks/200b53fa-05a4-4284-8889-119dd0bab57e |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | September 09, 2024, 11:43:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
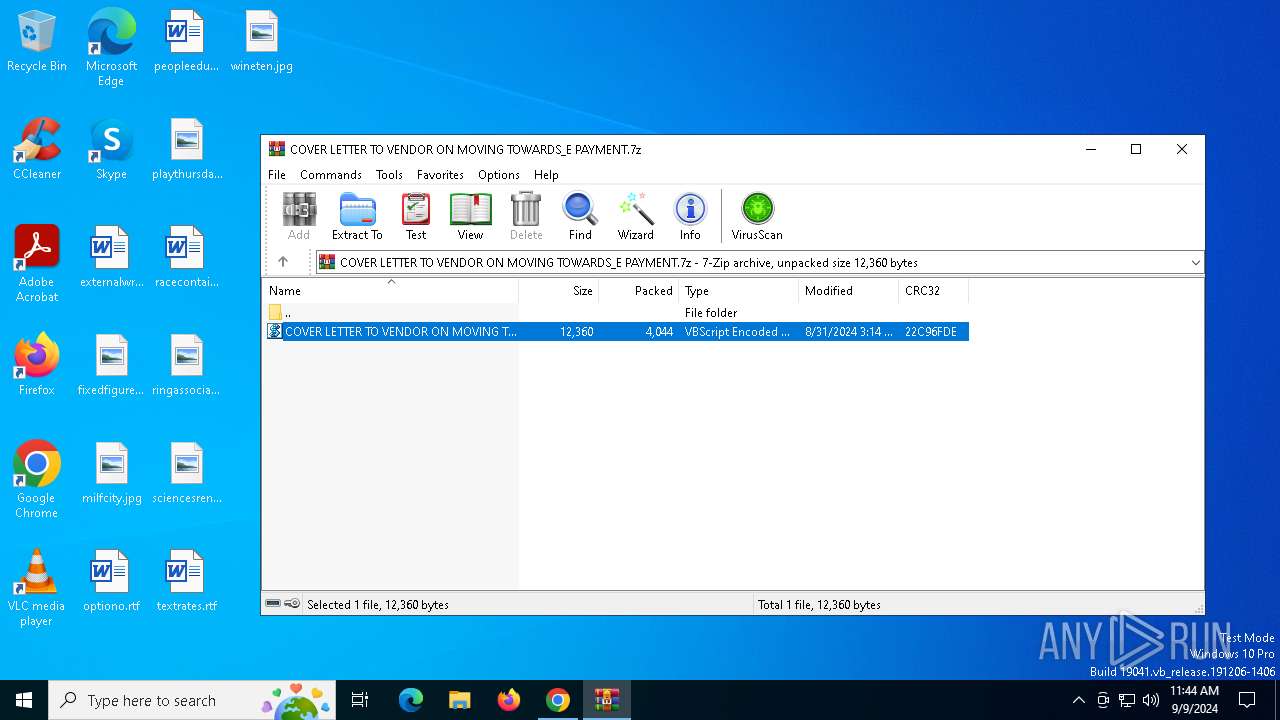
| MD5: | 7497D8E48A2468DA09574B1A78DAE9E8 |
| SHA1: | AD130343D159ACC2AF6EA7FDA88AA9118E57A900 |
| SHA256: | D07346FDB464EE9396526A4EC3C473FE7B23B4906B5D0F7DA6901A7C36F0F10E |
| SSDEEP: | 6:2RxHotJMPEjzT3ITGggU+XB9Y7TkRAv0L6zeYNiwqWCK0a:2Afjz7ITGo+bek26tYNTLRl |
MALICIOUS
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 4760)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 4760)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 4760)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 4760)
Gets context to execute command-line operations (SCRIPT)
- wscript.exe (PID: 4760)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 7076)
Connects to the CnC server
- chrome.exe (PID: 6556)
FORMBOOK has been detected (SURICATA)
- chrome.exe (PID: 6556)
Actions looks like stealing of personal data
- pcaui.exe (PID: 1176)
FORMBOOK has been detected (YARA)
- pcaui.exe (PID: 1176)
Stealers network behavior
- chrome.exe (PID: 6556)
SUSPICIOUS
Gets context to manipulate scheduled tasks (SCRIPT)
- wscript.exe (PID: 4760)
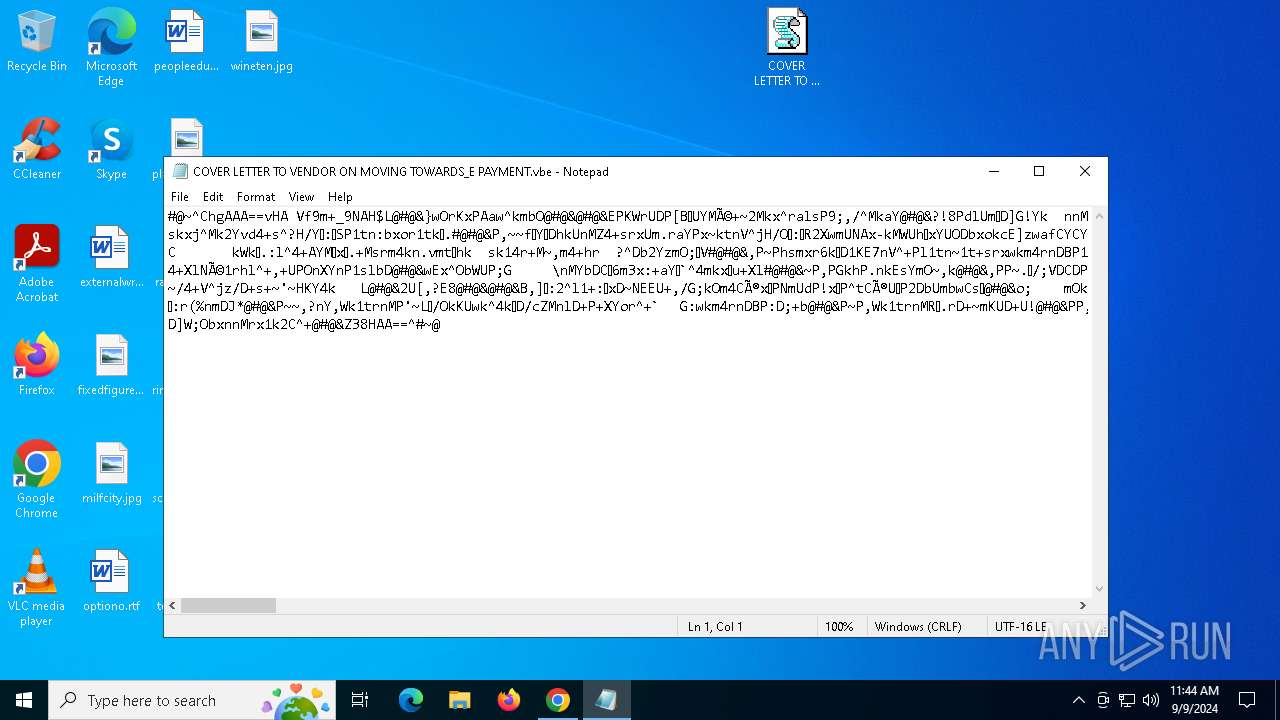
Runs shell command (SCRIPT)
- wscript.exe (PID: 4760)
- wscript.exe (PID: 7076)
Gets scheduled task context (SCRIPT)
- wscript.exe (PID: 4760)
Gets context to manipulate triggers of a scheduled task (SCRIPT)
- wscript.exe (PID: 4760)
Accesses object representing scheduled task trigger (SCRIPT)
- wscript.exe (PID: 4760)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 4760)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 4760)
Connects to the server without a host name
- wscript.exe (PID: 4760)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 7076)
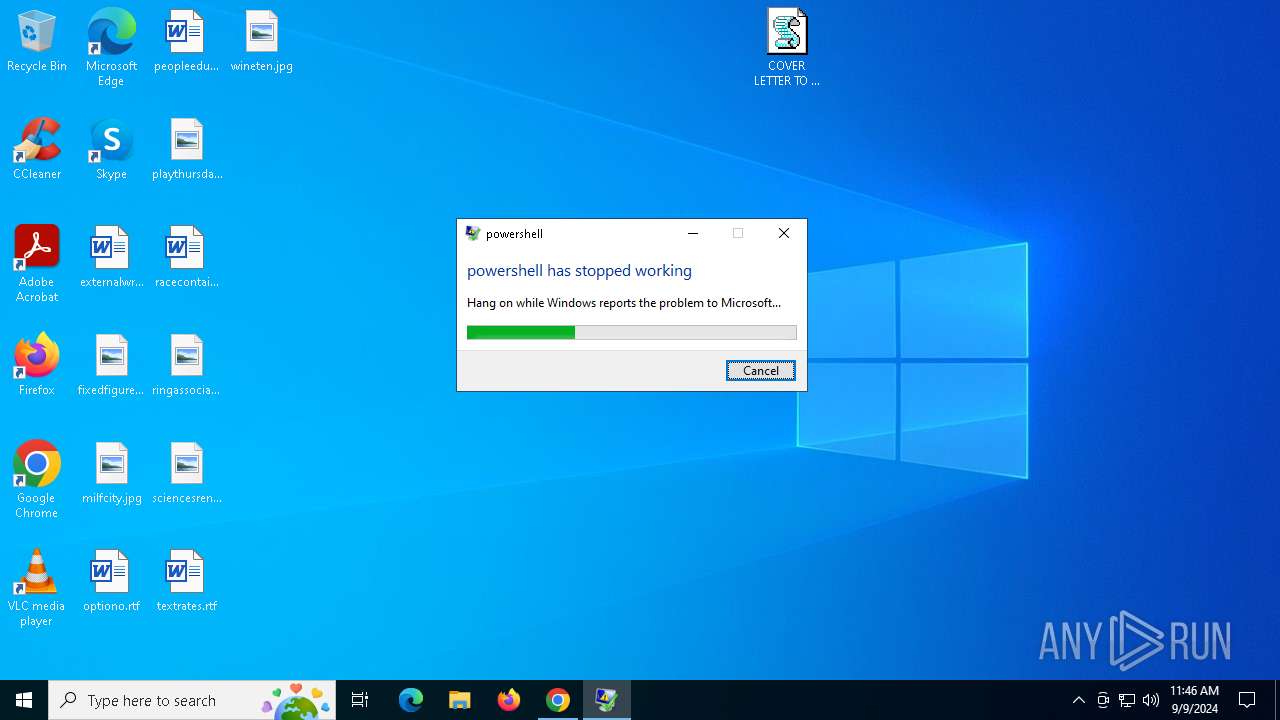
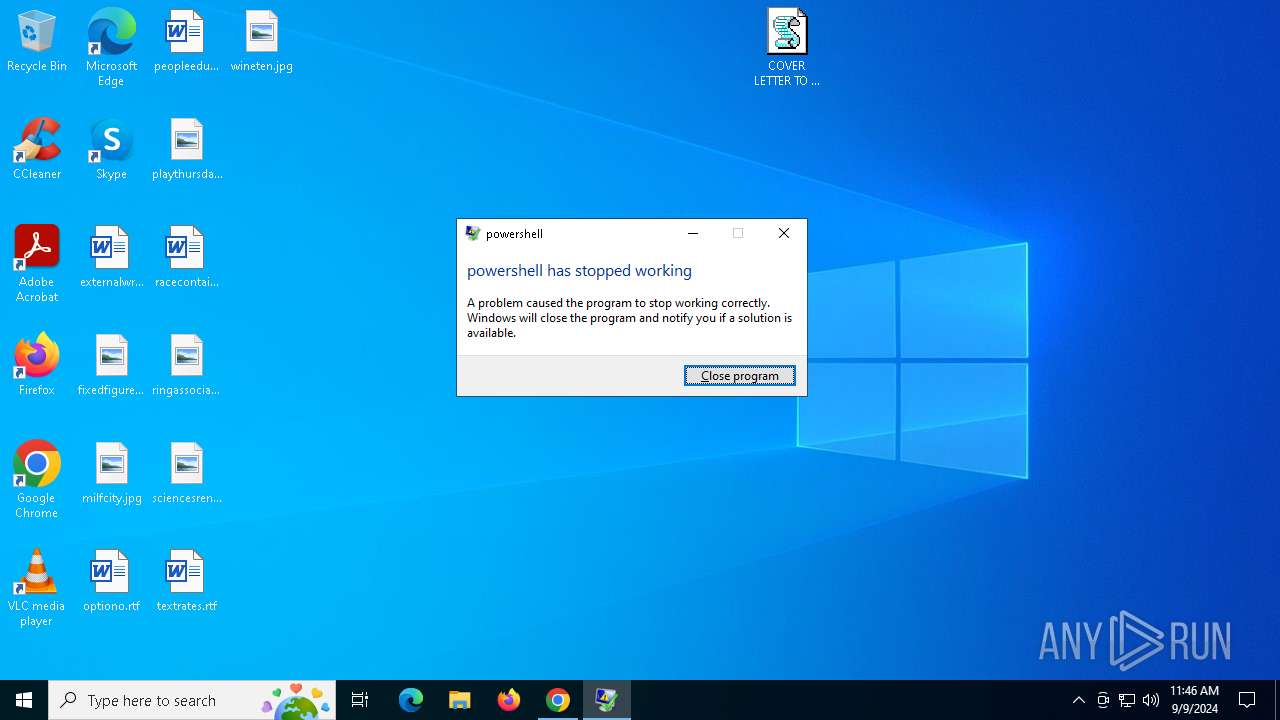
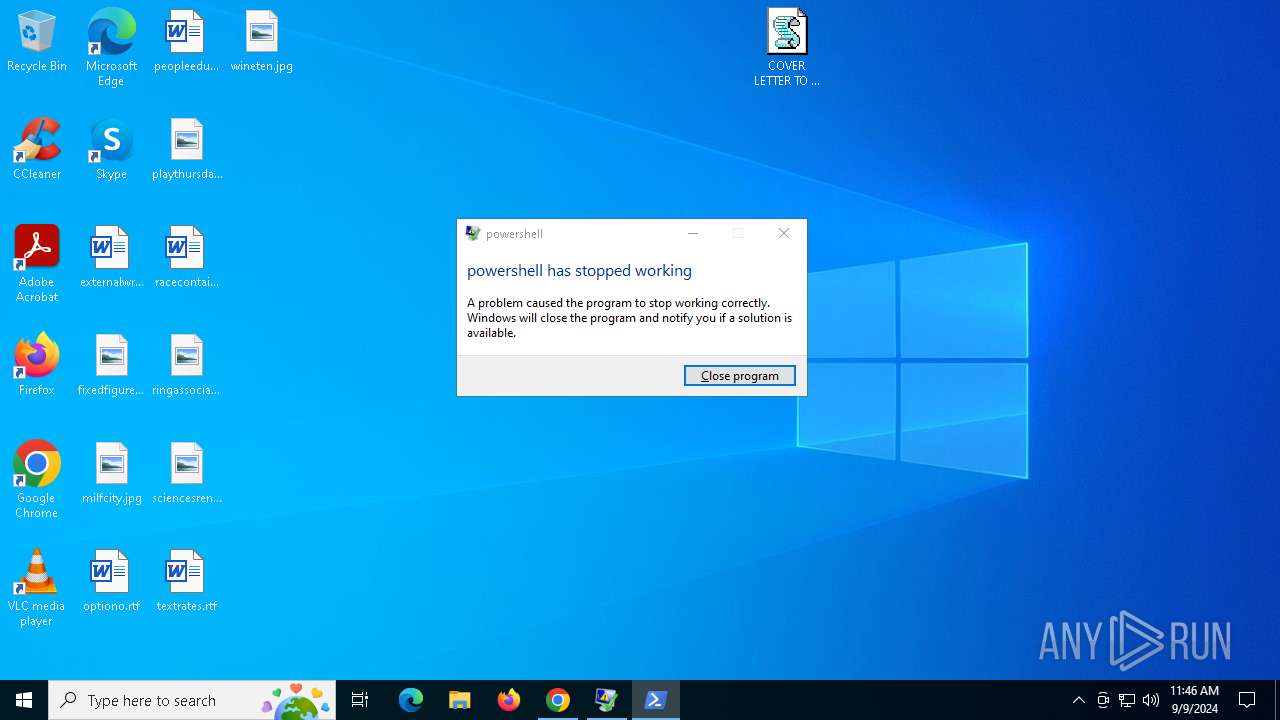
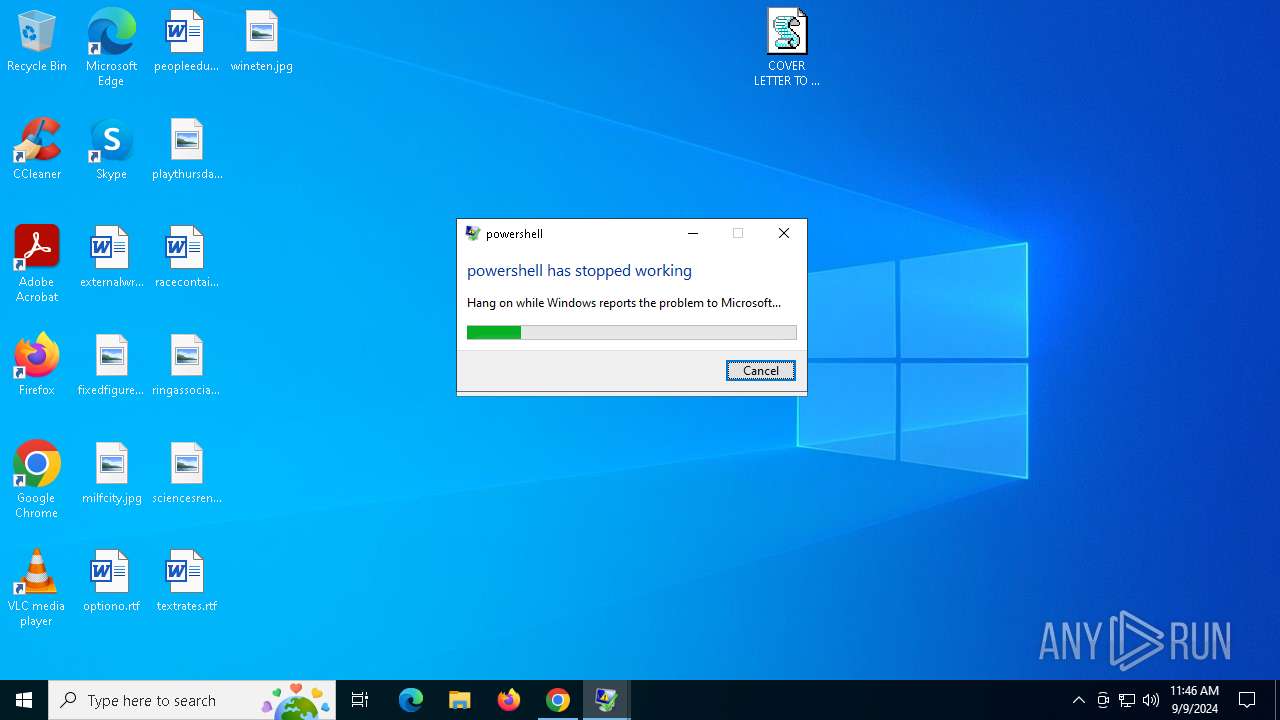
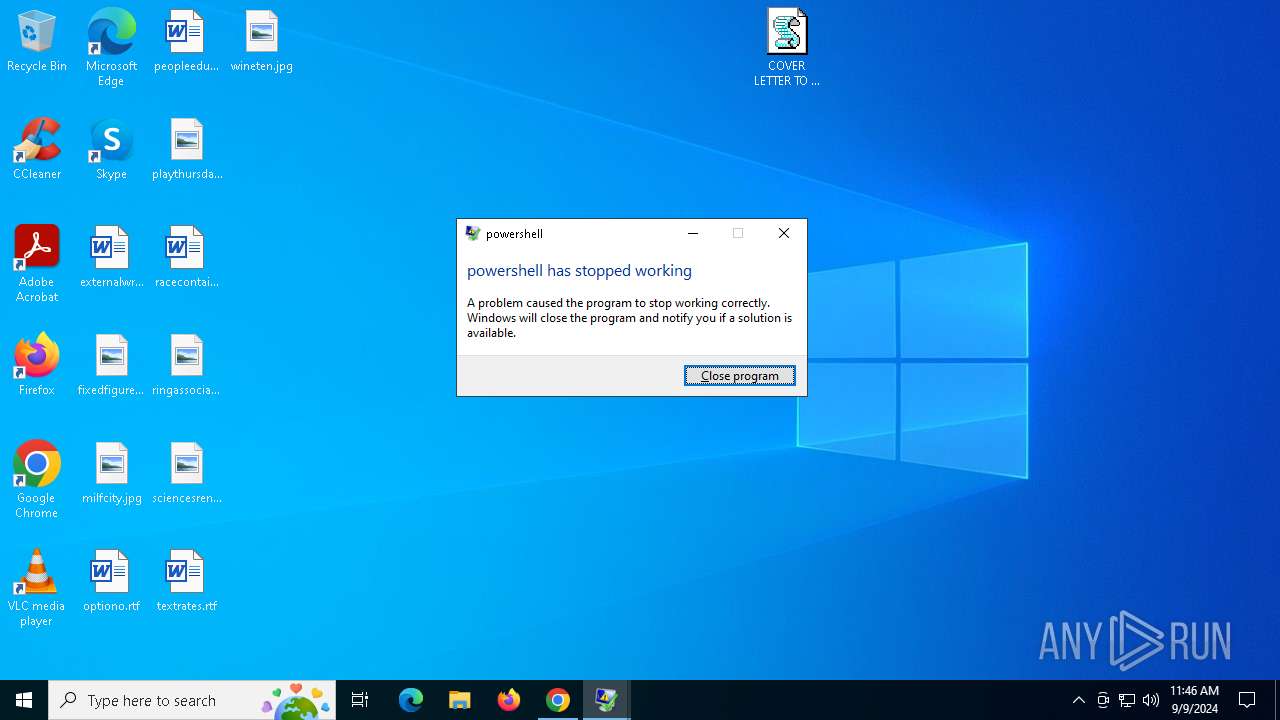
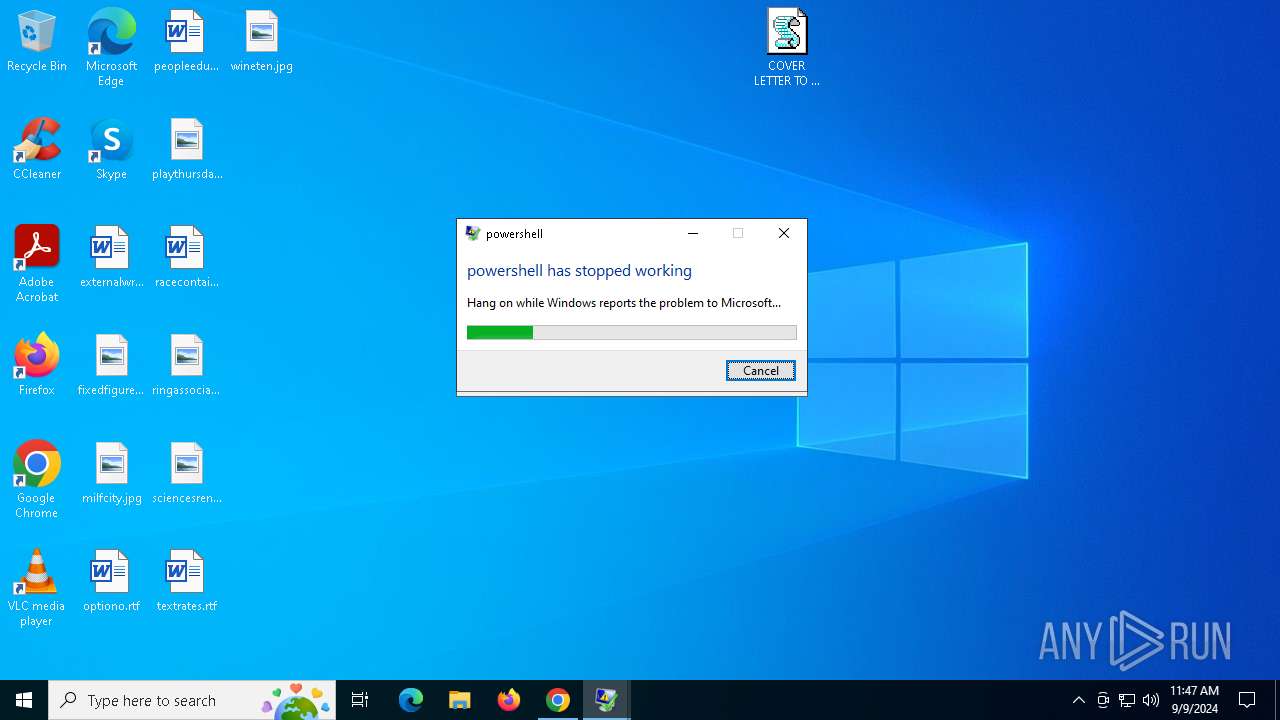
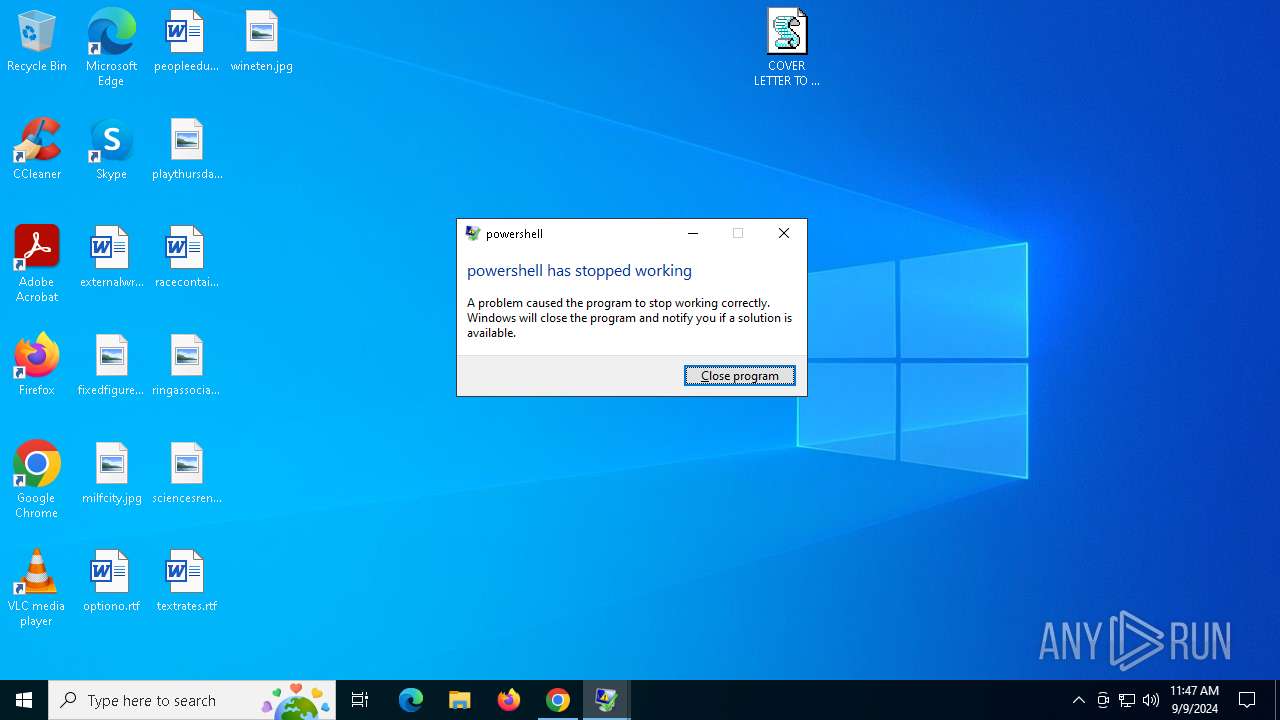
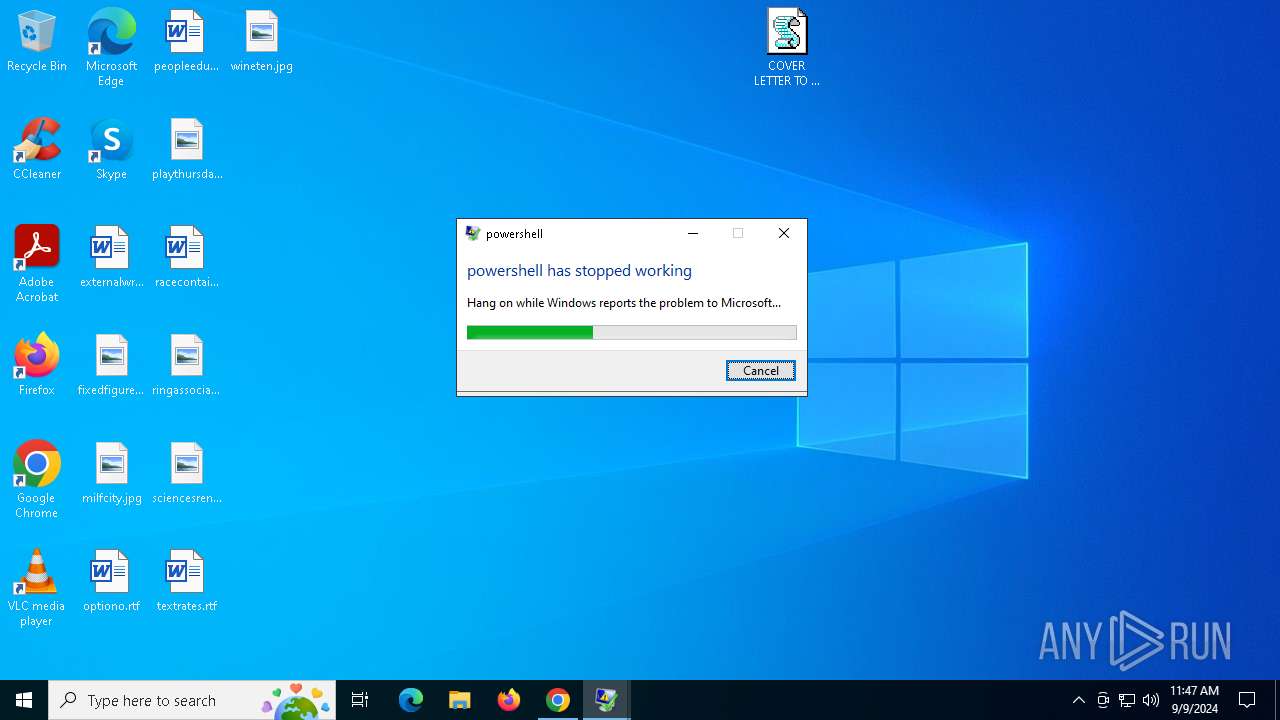
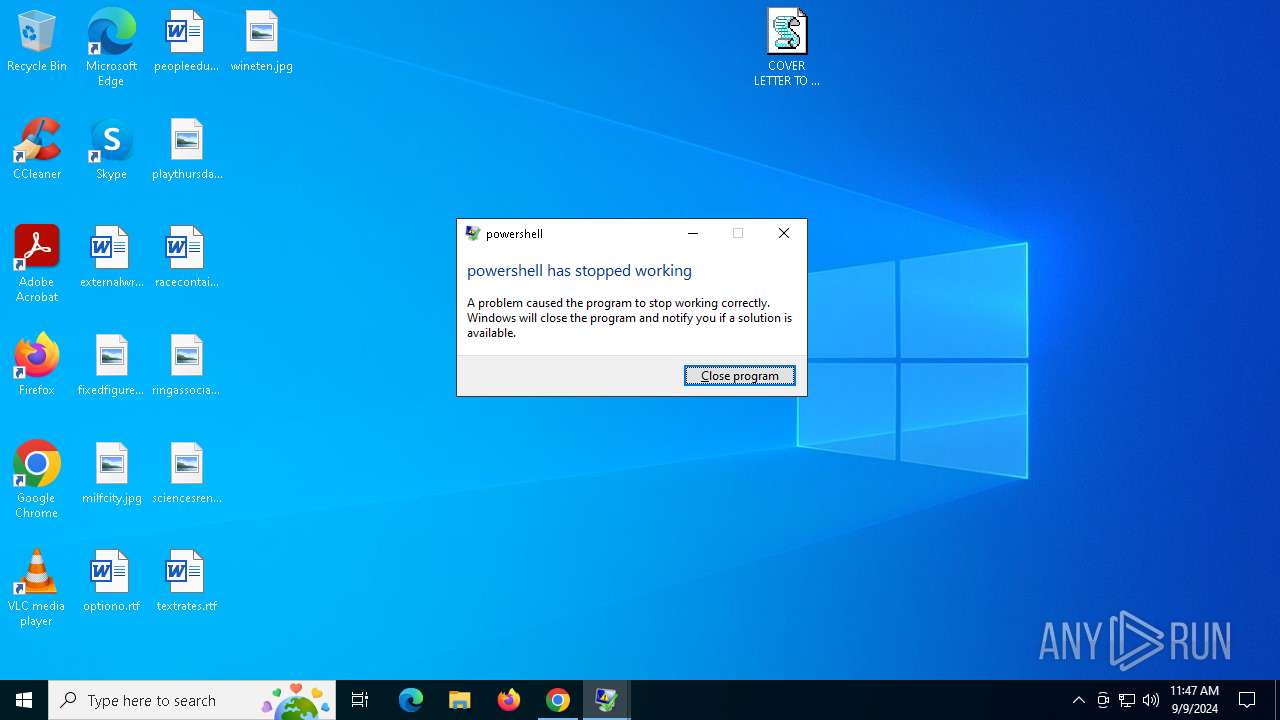
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7076)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6920)
- powershell.exe (PID: 6288)
- powershell.exe (PID: 6424)
- powershell.exe (PID: 6848)
- powershell.exe (PID: 5760)
- powershell.exe (PID: 7088)
- powershell.exe (PID: 6472)
The process creates files with name similar to system file names
- wermgr.exe (PID: 5128)
- wermgr.exe (PID: 6924)
- wermgr.exe (PID: 6244)
- wermgr.exe (PID: 1436)
- wermgr.exe (PID: 1232)
- wermgr.exe (PID: 6628)
The process executes via Task Scheduler
- wscript.exe (PID: 7076)
Contacting a server suspected of hosting an CnC
- chrome.exe (PID: 6556)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 6616)
- pcaui.exe (PID: 1176)
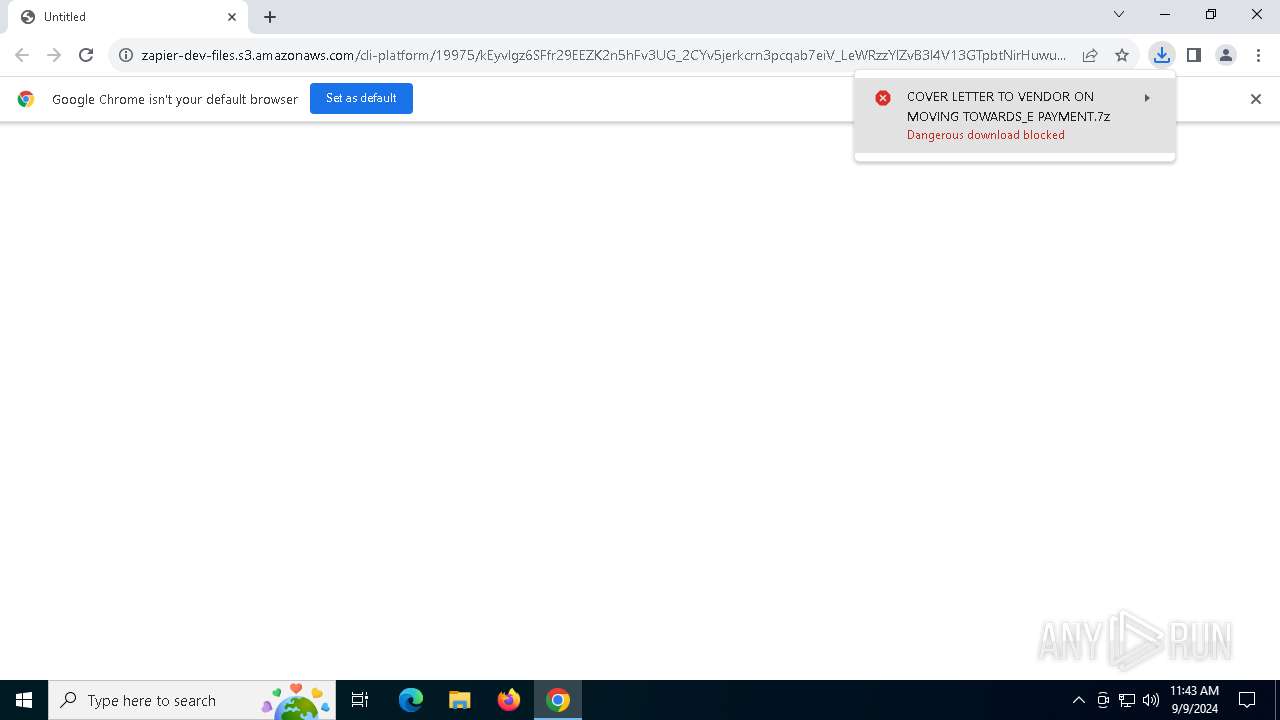
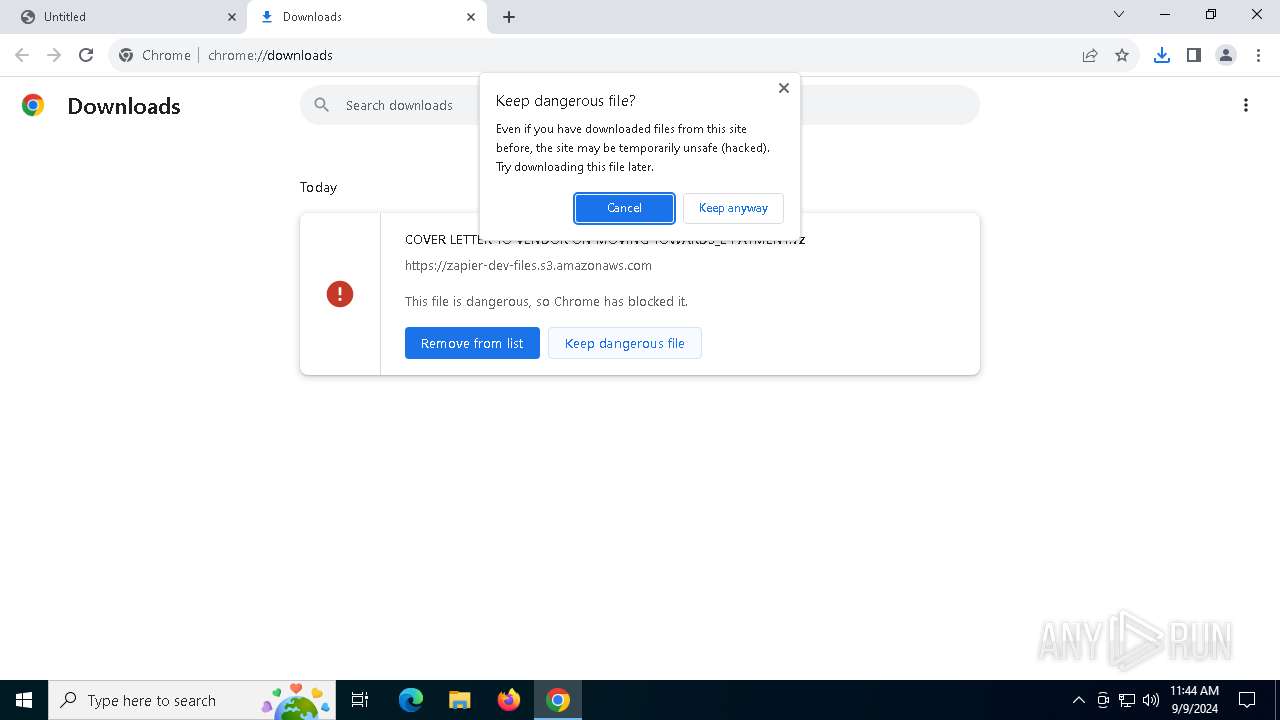
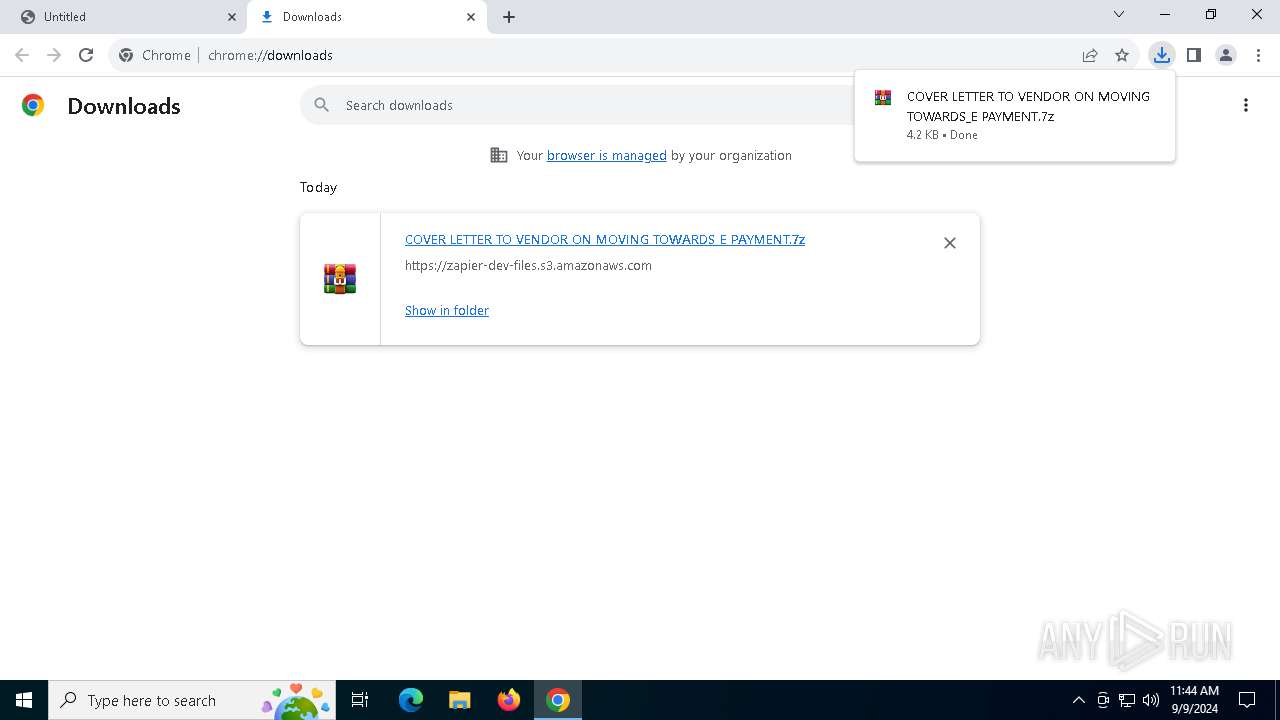
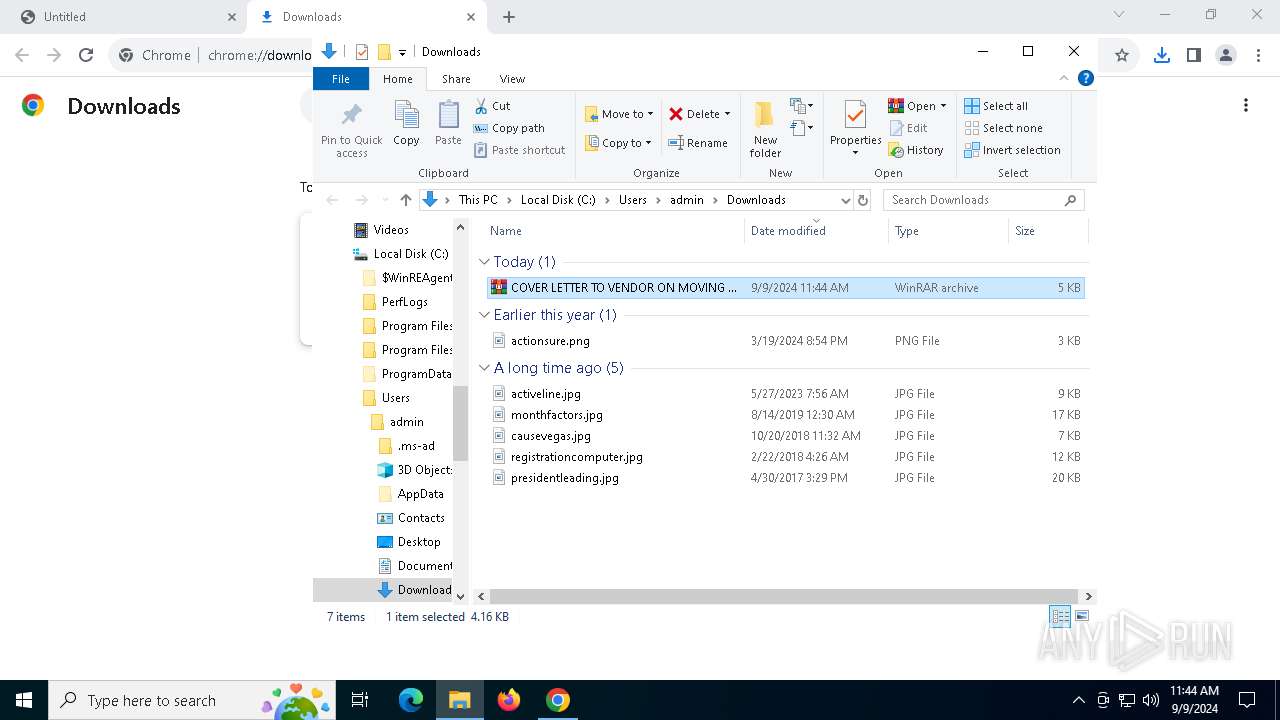
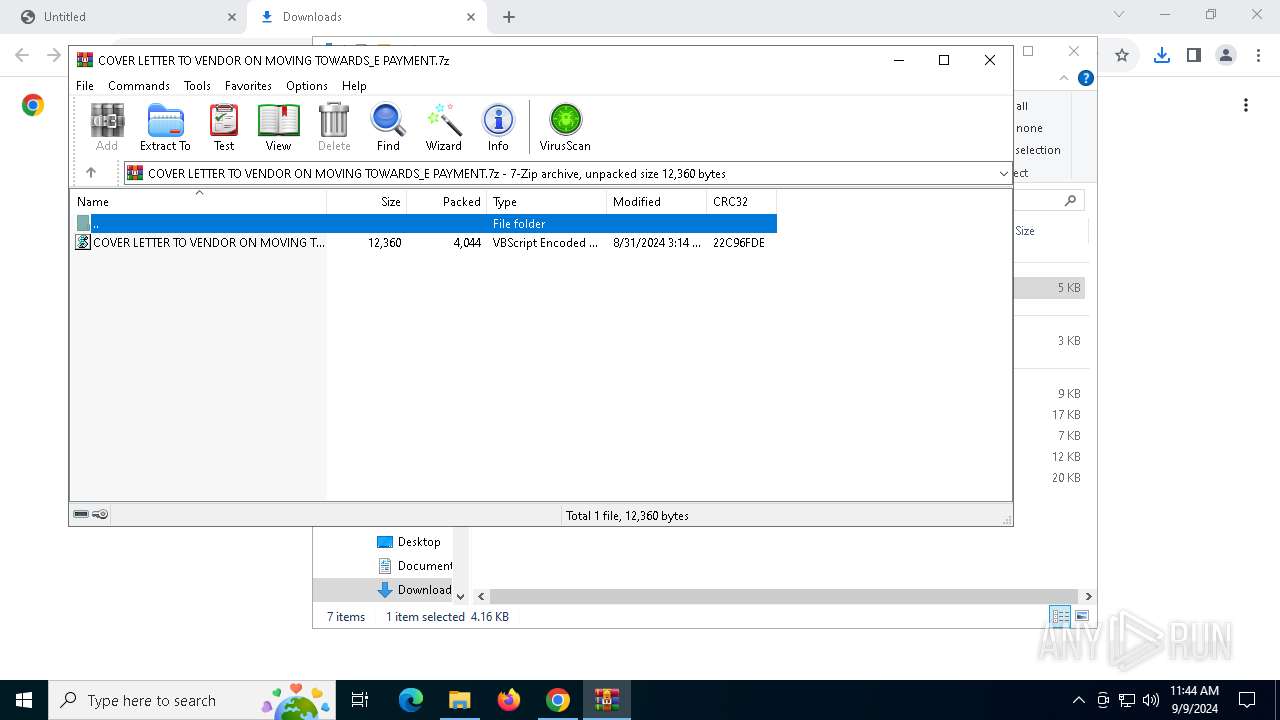
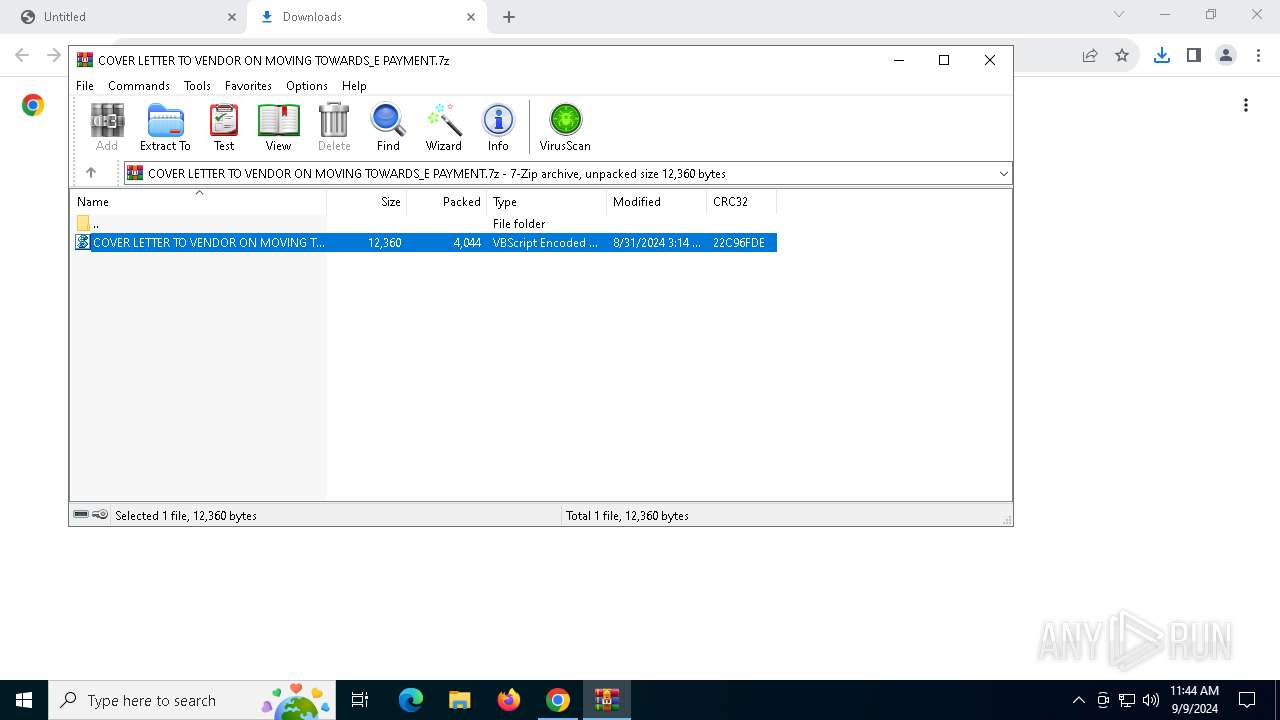
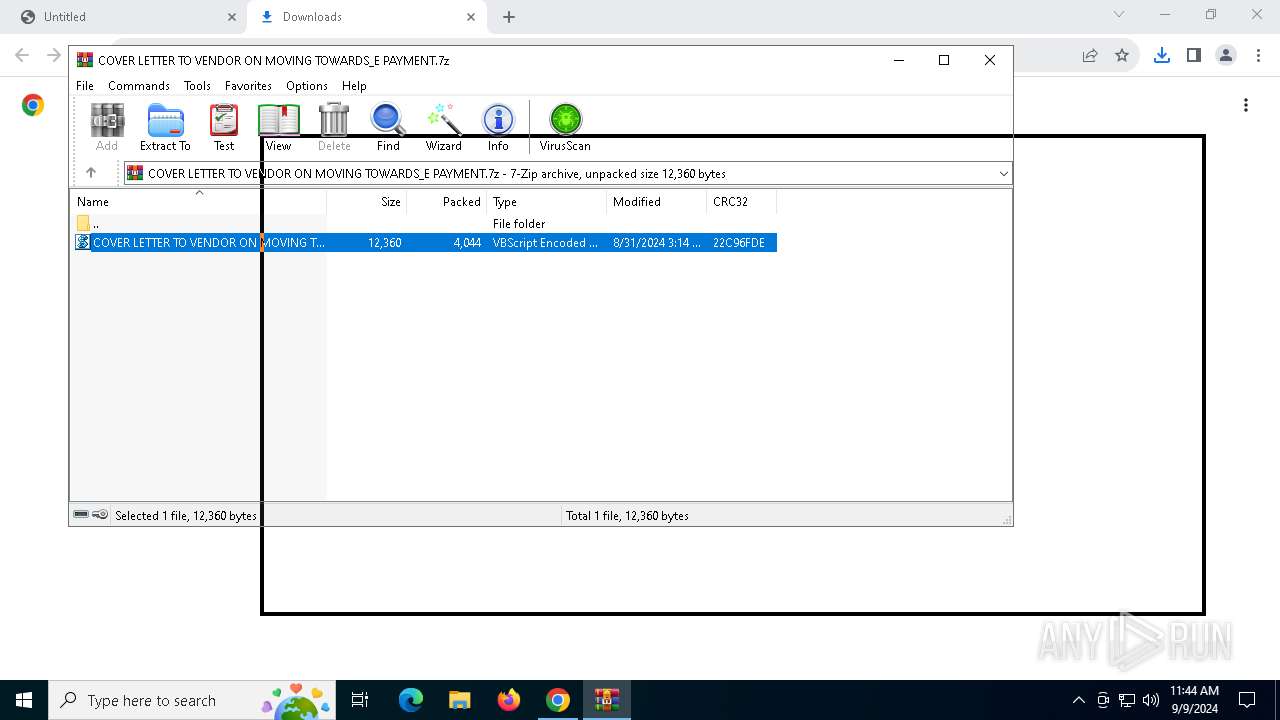
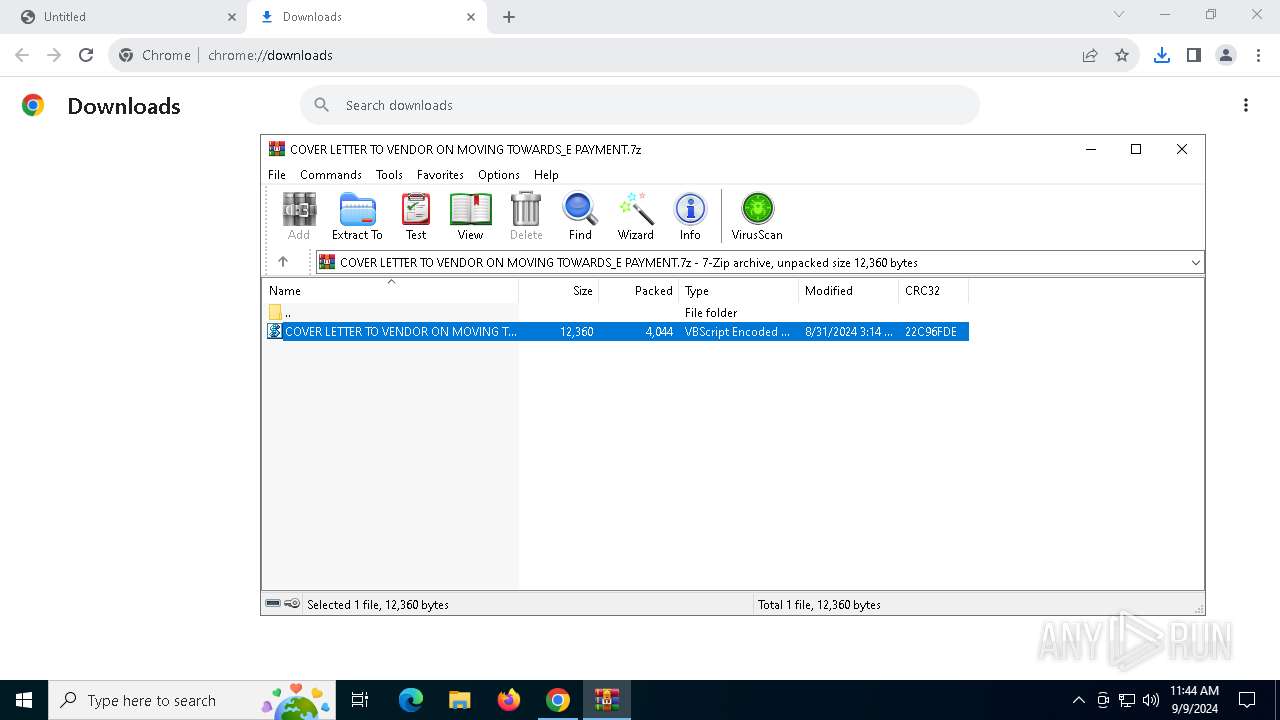
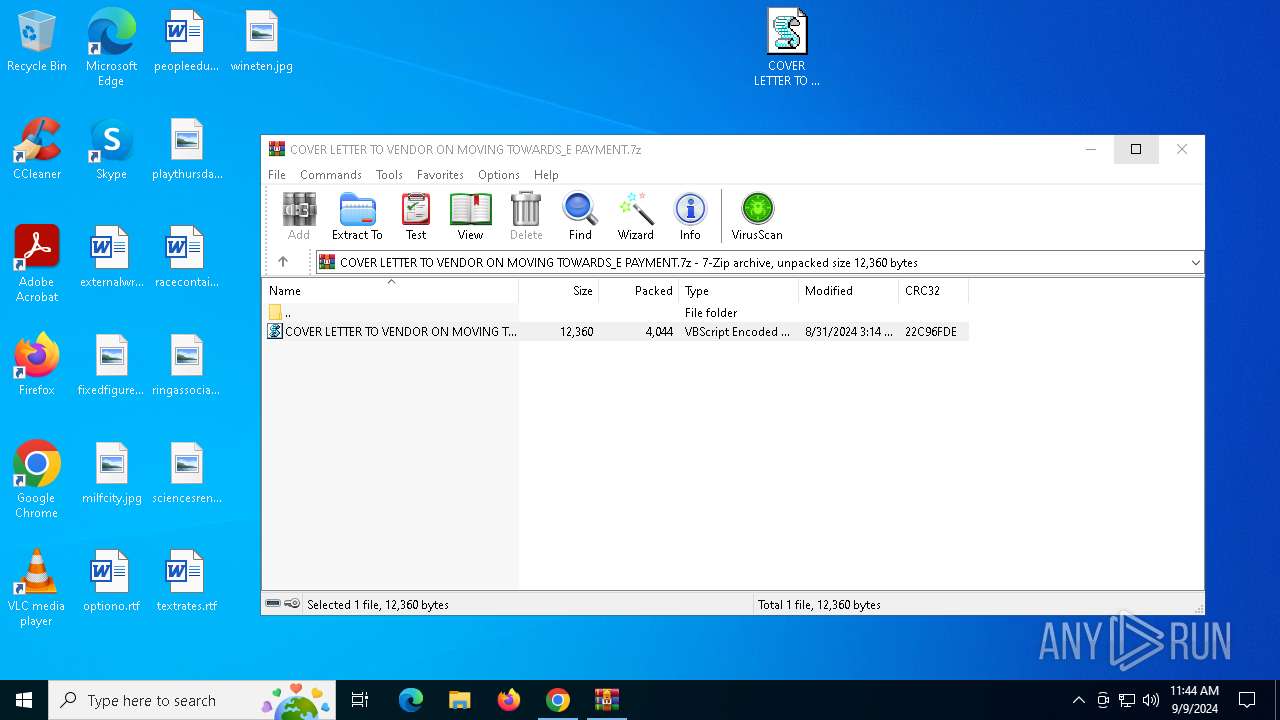
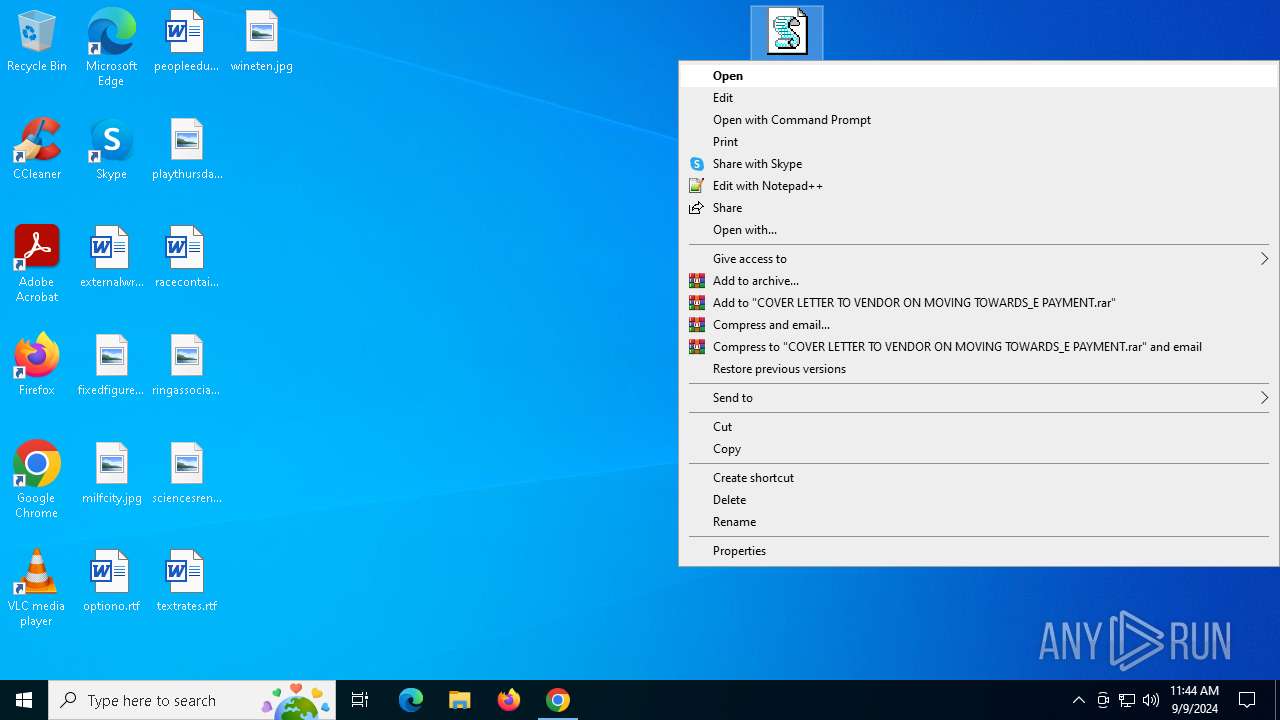
Manual execution by a user
- WinRAR.exe (PID: 6892)
- notepad.exe (PID: 6616)
- wscript.exe (PID: 4760)
The process uses the downloaded file
- chrome.exe (PID: 6248)
- WinRAR.exe (PID: 6892)
- powershell.exe (PID: 6920)
- powershell.exe (PID: 6288)
- wscript.exe (PID: 7076)
- powershell.exe (PID: 6424)
- powershell.exe (PID: 6848)
- powershell.exe (PID: 5760)
- powershell.exe (PID: 6472)
- powershell.exe (PID: 7088)
Creates files in the program directory
- powershell.exe (PID: 6920)
- powershell.exe (PID: 6288)
- powershell.exe (PID: 6424)
- powershell.exe (PID: 6848)
- powershell.exe (PID: 5760)
- powershell.exe (PID: 7088)
- powershell.exe (PID: 6472)
Checks current location (POWERSHELL)
- powershell.exe (PID: 6920)
- powershell.exe (PID: 6424)
- powershell.exe (PID: 6288)
- powershell.exe (PID: 6848)
- powershell.exe (PID: 5760)
- powershell.exe (PID: 7088)
- powershell.exe (PID: 6472)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6920)
- powershell.exe (PID: 6288)
- powershell.exe (PID: 6424)
- powershell.exe (PID: 6848)
- powershell.exe (PID: 5760)
- powershell.exe (PID: 6472)
- powershell.exe (PID: 7088)
Checks proxy server information
- wermgr.exe (PID: 5128)
- slui.exe (PID: 2008)
- wermgr.exe (PID: 6924)
- wermgr.exe (PID: 6244)
- wermgr.exe (PID: 1436)
- wermgr.exe (PID: 6628)
- wermgr.exe (PID: 1232)
- wermgr.exe (PID: 6956)
Reads the software policy settings
- wermgr.exe (PID: 5128)
- slui.exe (PID: 2008)
- slui.exe (PID: 236)
- wermgr.exe (PID: 6924)
- wermgr.exe (PID: 1436)
- wermgr.exe (PID: 6244)
- wermgr.exe (PID: 1232)
- wermgr.exe (PID: 6628)
- wermgr.exe (PID: 6956)
Checks supported languages
- AddInProcess32.exe (PID: 3548)
- AddInProcess32.exe (PID: 4772)
- AddInProcess32.exe (PID: 6704)
- AddInProcess32.exe (PID: 6552)
- AddInProcess32.exe (PID: 4824)
- AddInProcess32.exe (PID: 2904)
Application launched itself
- chrome.exe (PID: 6556)
Create files in a temporary directory
- pcaui.exe (PID: 1176)
Executable content was dropped or overwritten
- chrome.exe (PID: 6132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
196
Monitored processes
63
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2100 --field-trial-handle=1904,i,15311355813977807934,5344064823760692099,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1176 | "C:\Windows\SysWOW64\pcaui.exe" | C:\Windows\SysWOW64\pcaui.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Assistant User Interface Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "5760" "3028" "2944" "3032" "0" "0" "3036" "0" "0" "0" "0" "0" | C:\Windows\System32\wermgr.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4788 --field-trial-handle=1904,i,15311355813977807934,5344064823760692099,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1436 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "6848" "2896" "2848" "2900" "0" "0" "2904" "0" "0" "0" "0" "0" | C:\Windows\System32\wermgr.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4284 --field-trial-handle=1904,i,15311355813977807934,5344064823760692099,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2008 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2584 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
76 025
Read events
75 939
Write events
79
Delete events
7
Modification events
| (PID) Process: | (6556) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6556) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6556) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6556) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6556) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6248) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000000674F39BAD02DB01 | |||
| (PID) Process: | (6892) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6892) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\COVER LETTER TO VENDOR ON MOVING TOWARDS_E PAYMENT.7z | |||
| (PID) Process: | (6892) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6892) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
3
Suspicious files
227
Text files
77
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF12ae0b.TMP | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF12ae0b.TMP | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 6556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:F96D0EF8D63094D714514A441F8CD3FB | SHA256:2083625CA1E32D366F0B664D9B87B591791EF2EA2B770F4FA6ABE13FECA01196 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
71
DNS requests
46
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7072 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6356 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
4704 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1780 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4704 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6356 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
6356 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
6356 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
6356 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
4760 | wscript.exe | GET | 200 | 144.91.79.54:80 | http://144.91.79.54/2508/b15XM0jm9zZmZCn8Y57g.txt | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7072 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1356 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
508 | chrome.exe | 3.5.29.43:443 | zapier-dev-files.s3.amazonaws.com | AMAZON-AES | US | shared |
6556 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
508 | chrome.exe | 142.250.102.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6556 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
508 | chrome.exe | 142.250.185.110:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
7072 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
zapier-dev-files.s3.amazonaws.com |
| shared |
accounts.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
6556 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
6556 | chrome.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) M5 |
6556 | chrome.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6556 | chrome.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6556 | chrome.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6556 | chrome.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) M5 |
6556 | chrome.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6556 | chrome.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6556 | chrome.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) M5 |
3 ETPRO signatures available at the full report