| File name: | Akira.exe |
| Full analysis: | https://app.any.run/tasks/72f98a58-4554-425b-a0e7-93af31fa1a53 |
| Verdict: | Malicious activity |
| Threats: | Akira Ransomware emerged in March 2023 and compromised over 250 organizations by January 2024 with approximately $42 million in ransom payments. It employs double extortion tactics exfiltrating data before encryption and threatening to publish it on a dedicated website. |
| Analysis date: | November 24, 2024, 06:50:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | 68729B85AA01CD8C9F4CCD137DDDE137 |
| SHA1: | 960B01AB967E96FD6D875EB157667E8EF7FF1C4A |
| SHA256: | D0510E1D89640C9650782E882FE3B9AFBA00303B126EC38FDC5F1C1484341959 |
| SSDEEP: | 12288:KR4bbb4DT8Rx92j5PeMJcyWEOrYlohFVdnpi:KR4X0fcx94teMJcyWERlY3i |
MALICIOUS
AKIRA has been detected (YARA)
- Akira.exe (PID: 4556)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 5008)
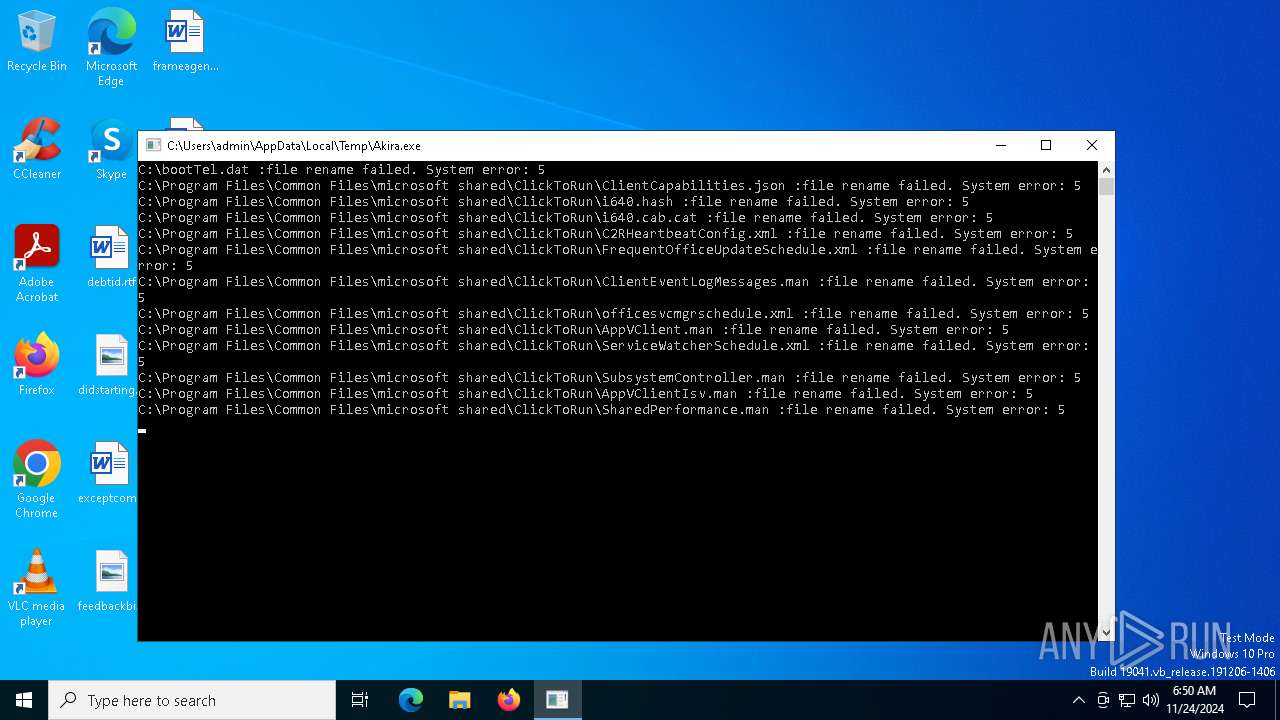
Creates file in the systems drive root
- Akira.exe (PID: 4556)
INFO
Checks supported languages
- Akira.exe (PID: 4556)
Reads the computer name
- Akira.exe (PID: 4556)
Reads the machine GUID from the registry
- Akira.exe (PID: 4556)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:05:31 11:16:27+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.35 |
| CodeSize: | 425984 |
| InitializedDataSize: | 169472 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x35710 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
127
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4556 | "C:\Users\admin\AppData\Local\Temp\Akira.exe" | C:\Users\admin\AppData\Local\Temp\Akira.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 5000 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Akira.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5008 | powershell.exe -Command "Get-WmiObject Win32_Shadowcopy | Remove-WmiObject" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5560 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 761
Read events
4 732
Write events
23
Delete events
6
Modification events
| (PID) Process: | (4556) Akira.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 2 | |||
| (PID) Process: | (4556) Akira.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: CC11000048F1EA1D3D3EDB01 | |||
| (PID) Process: | (4556) Akira.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: A8B6680AF5CFD8D5D97FC8A3ED761087DD0531F9070D1ED84CE284419E0376C5 | |||
| (PID) Process: | (4556) Akira.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (4556) Akira.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\ConnectedDevicesPlatform\L.admin\ActivitiesCache.db-shm | |||
| (PID) Process: | (4556) Akira.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFilesHash |
Value: 22C64696419CC435DAFE5CDCC769F27B72873BD4F16AC541EFD23D4B4E2A0554 | |||
| (PID) Process: | (4556) Akira.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0002 |
| Operation: | write | Name: | Owner |
Value: CC11000048F1EA1D3D3EDB01 | |||
| (PID) Process: | (4556) Akira.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0002 |
| Operation: | write | Name: | SessionHash |
Value: 50472348ACF3AA180F8BA8ACCC30356513AEEAAB4755C1A60AFE7516E56E2BA6 | |||
| (PID) Process: | (4556) Akira.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0002 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (4556) Akira.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0002 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\ConnectedDevicesPlatform\L.admin\ActivitiesCache.db-wal | |||
Executable files
0
Suspicious files
1 710
Text files
813
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4556 | Akira.exe | C:\Program Files\Mozilla Firefox\omni.ja | — | |
MD5:— | SHA256:— | |||
| 4556 | Akira.exe | C:\Program Files\Common Files\microsoft shared\ClickToRun\i640.hash | binary | |
MD5:5456BDEFDE0367FF36802C711D8CF45B | SHA256:FA3010BAE0B1DF43FCF102B6234E454AABF55E2A62D83569B39D299D0642C2C9 | |||
| 4556 | Akira.exe | C:\Program Files\Common Files\microsoft shared\ClickToRun\C2RHeartbeatConfig.xml | binary | |
MD5:7C891249B66DADD6E1C9E169D2B6C9C8 | SHA256:8DBE8C1EE4148330D9F52E4CAF6959AFF10E5A2ED25C8B86CAAE636A9BFDD1DE | |||
| 5008 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0ugsedqt.ih4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5008 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:5DB8BD38515569285B39989833A95C28 | SHA256:859FCEDF66F39D25610B748BEC43B79568187AC6FD7023CC73604B9E5EE2409B | |||
| 4556 | Akira.exe | C:\Users\admin\3D Objects\akira_readme.txt | text | |
MD5:04B587981E1E6BA871EA627CA3BAEF38 | SHA256:E718E02254D7EB465192DFD4B86CE1B05761415B5A7106AA9DCECCFB203796EB | |||
| 4556 | Akira.exe | C:\Program Files\Common Files\microsoft shared\ClickToRun\ClientCapabilities.json | binary | |
MD5:8CAF1F2D8E31FE382BD43CD3521DC15C | SHA256:3FE0A96D26F7EA3C88390E586DB6CCA078B4D09E30EC9EF4462884AD5FA241BE | |||
| 4556 | Akira.exe | C:\Program Files\Common Files\microsoft shared\ClickToRun\SubsystemController.man | binary | |
MD5:97CD2ED268CC1FB3D106A821C7FBA49F | SHA256:7E35F664E831C63E64D4F2CFE9D92DB94B6A553EC26E9A253E9D67A71F314E81 | |||
| 4556 | Akira.exe | C:\Program Files\Common Files\microsoft shared\ClickToRun\ServiceWatcherSchedule.xml | binary | |
MD5:B834F6C7966EF75CE97028B8017D0589 | SHA256:8F14DC3AC07A8560F162BD6244E7AABB608B133ED5797D330657153BC4C5D608 | |||
| 4556 | Akira.exe | C:\bootTel.dat | binary | |
MD5:344EFF403E5473ECA8C8544139C4CE71 | SHA256:199B1057928A634D99F42E88ACCE208DF0EBA3CB1BB9CDA26CFE377016BAB25E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3040 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6412 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6412 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6076 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 23.212.110.177:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |