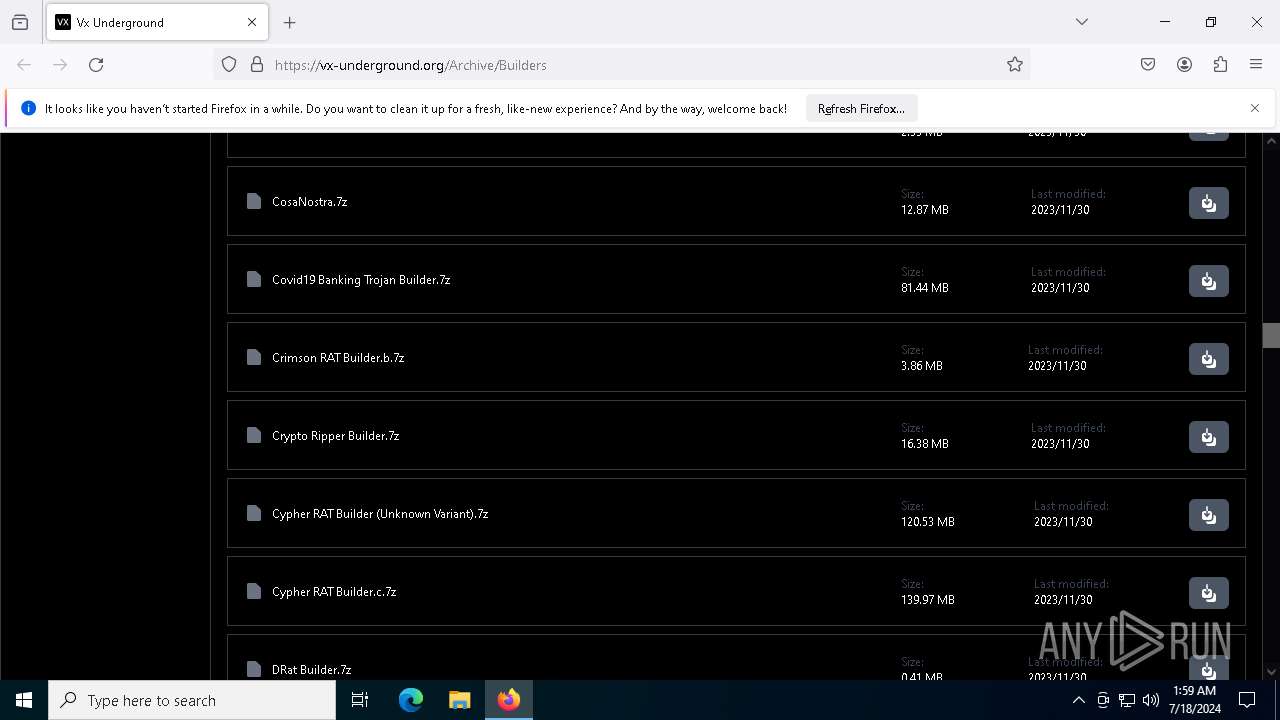
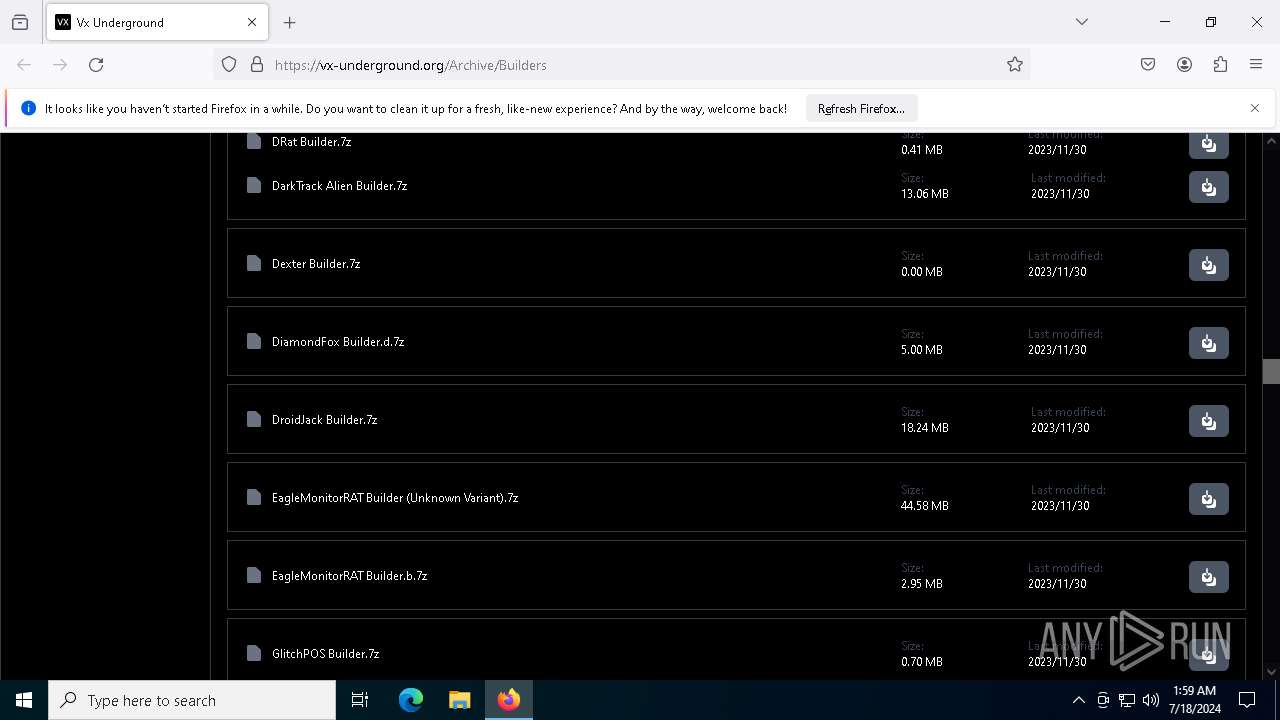
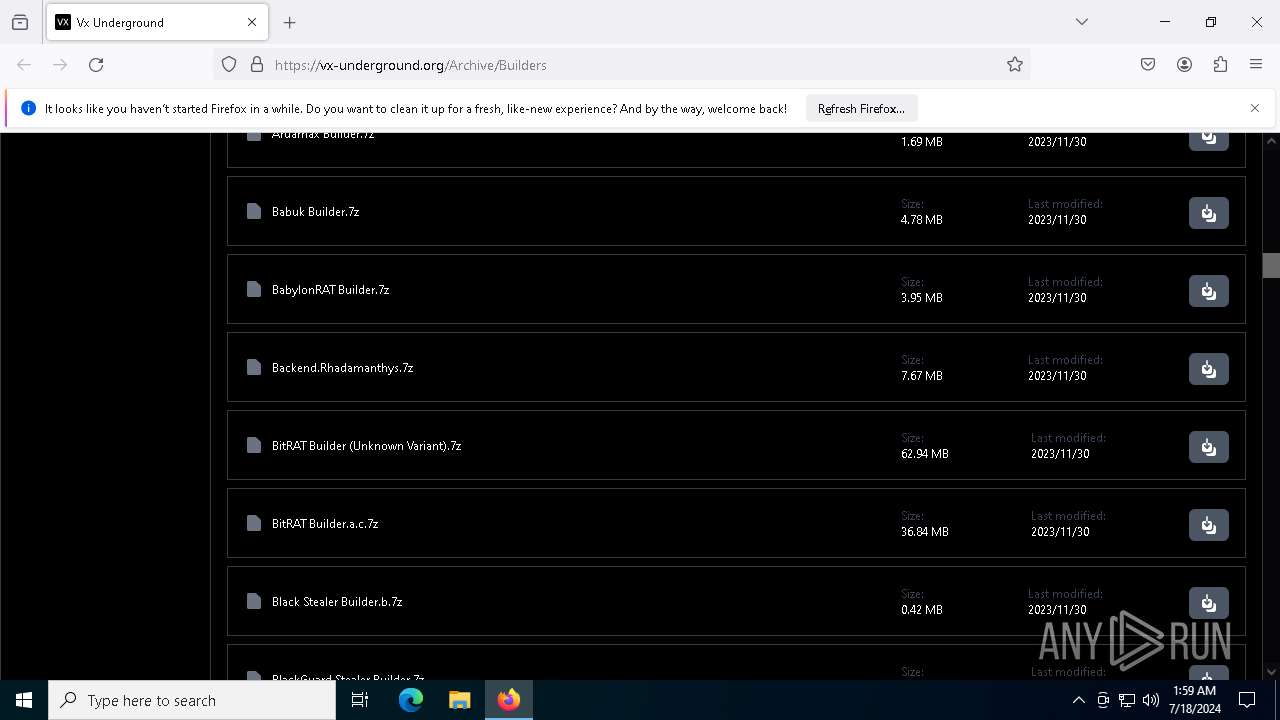
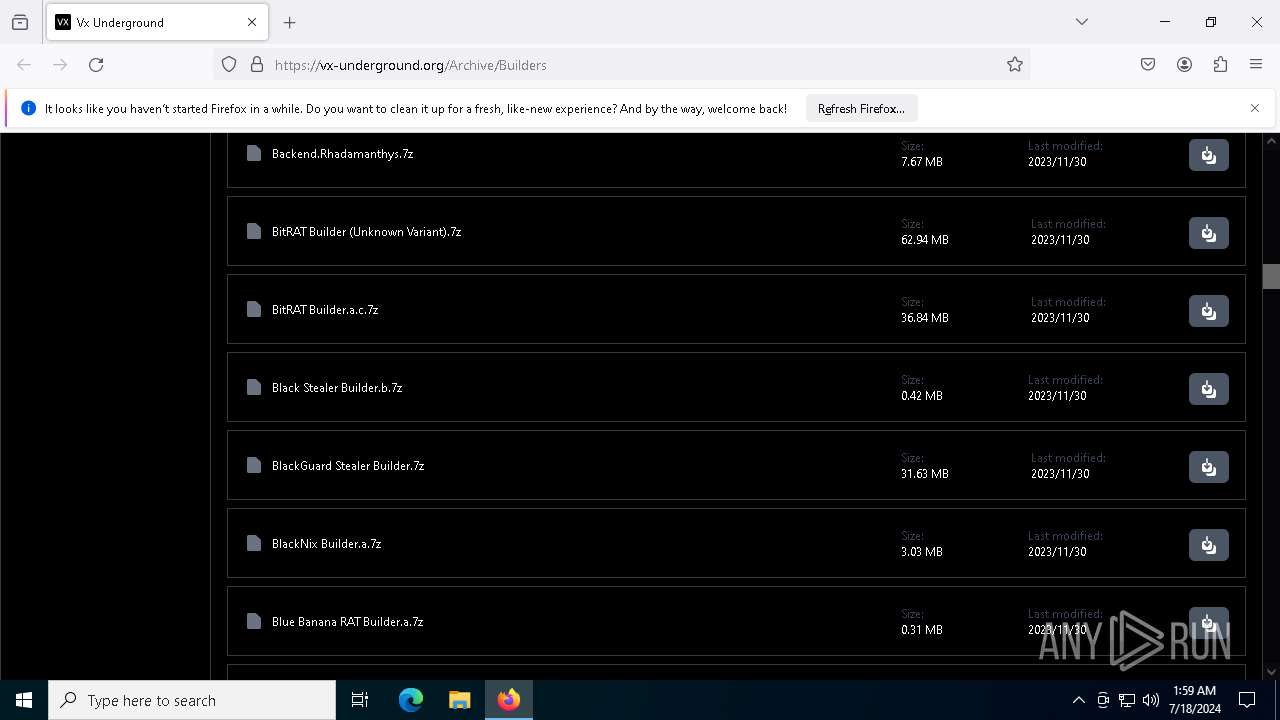
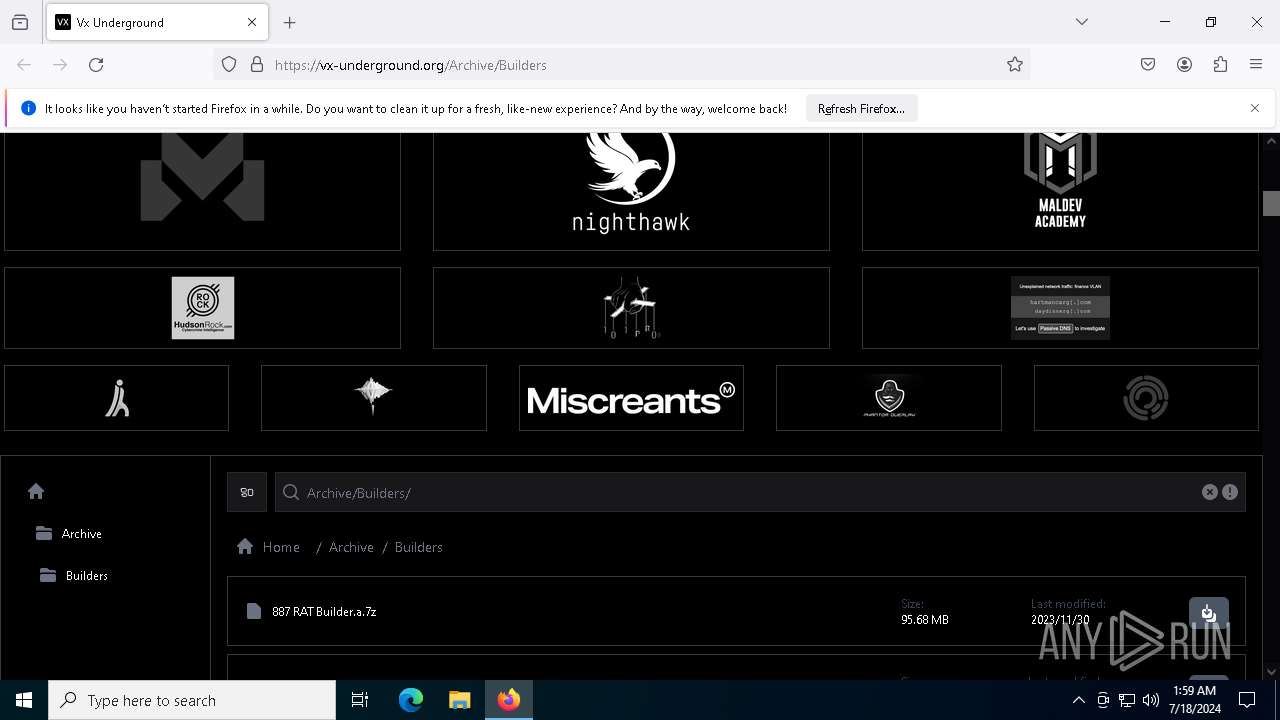
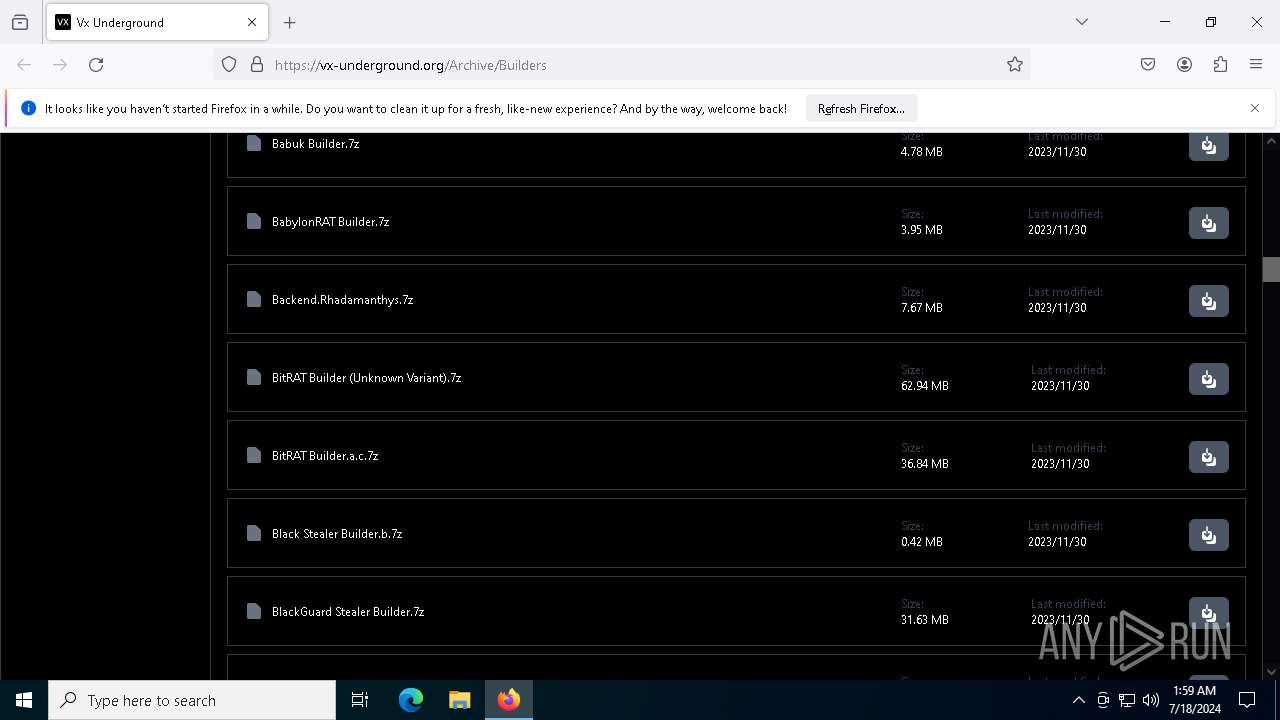
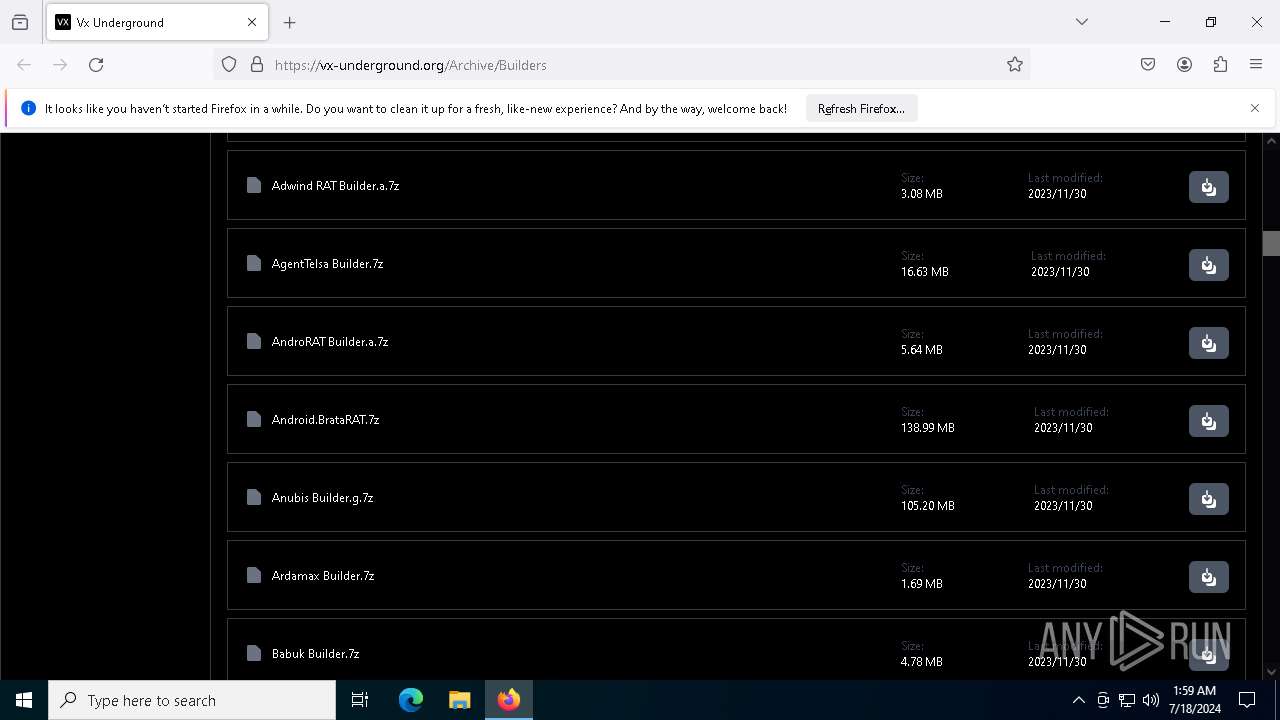
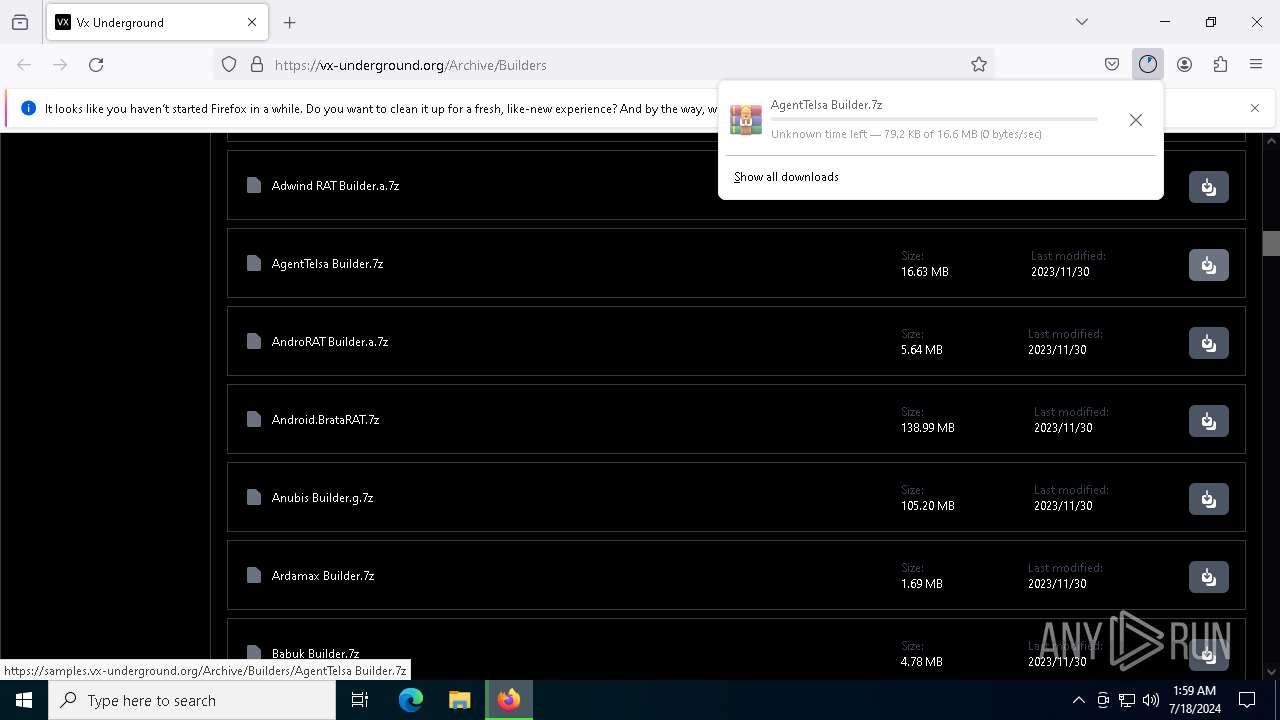
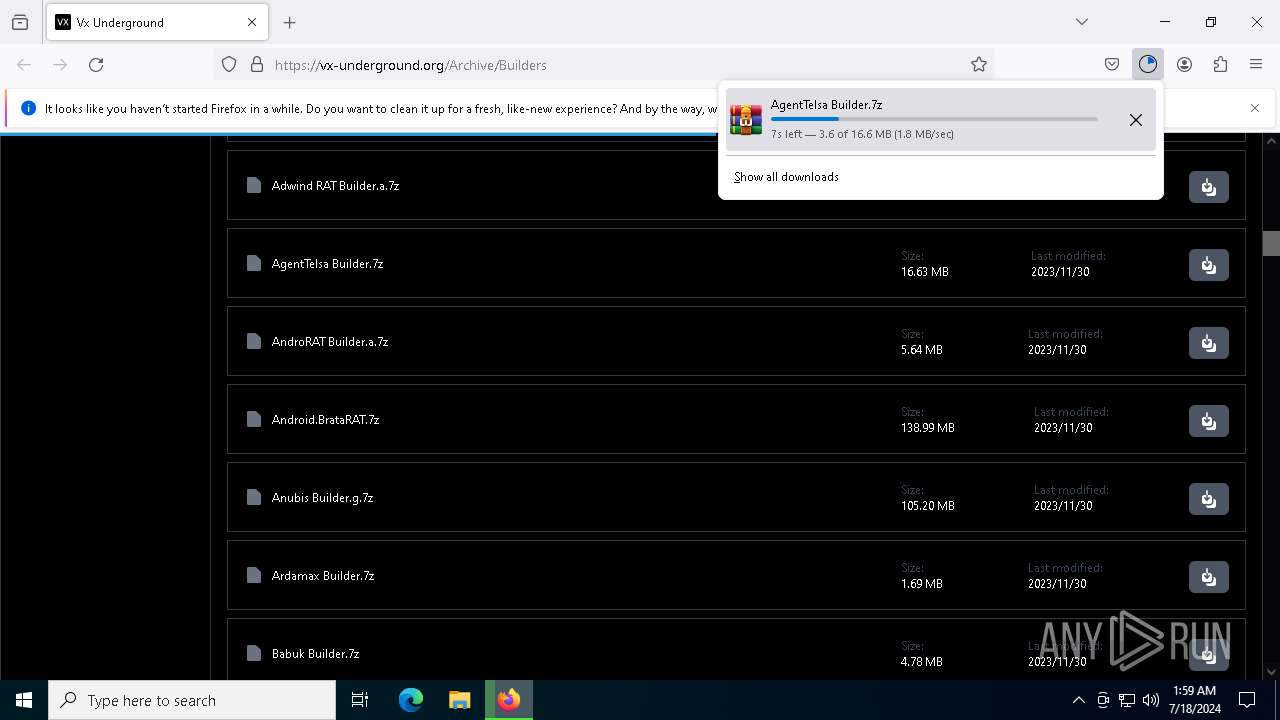
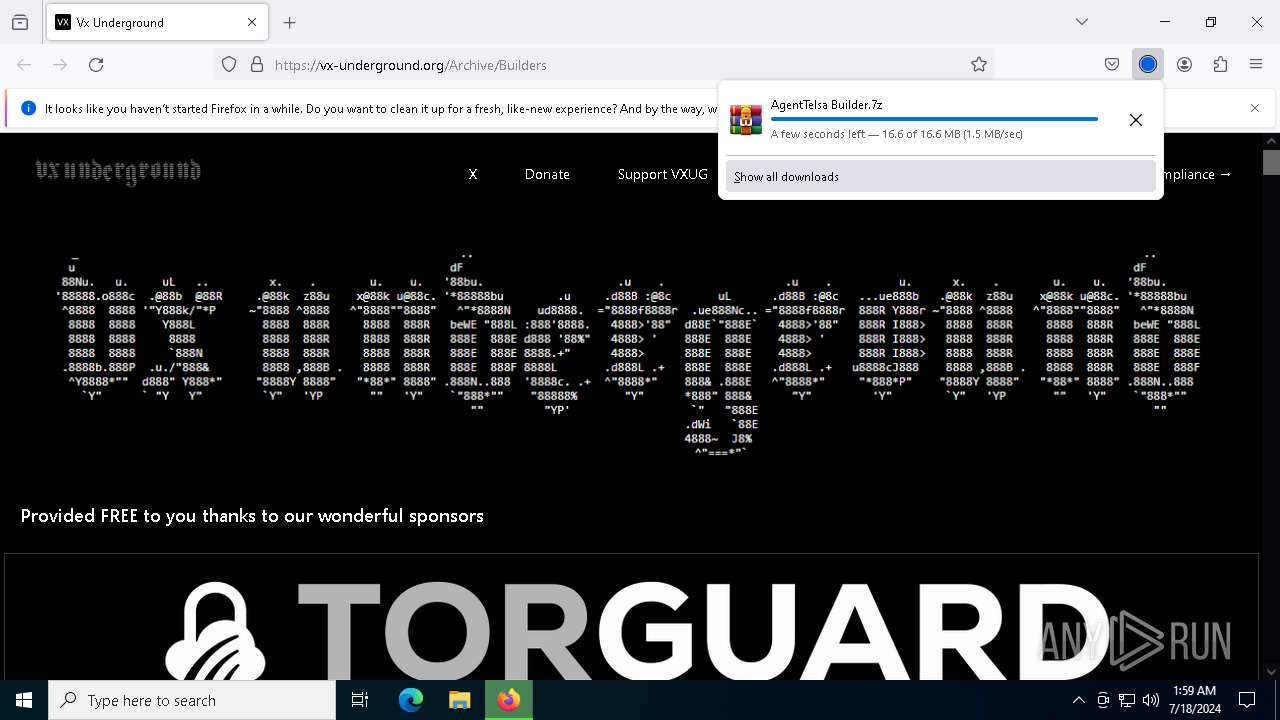
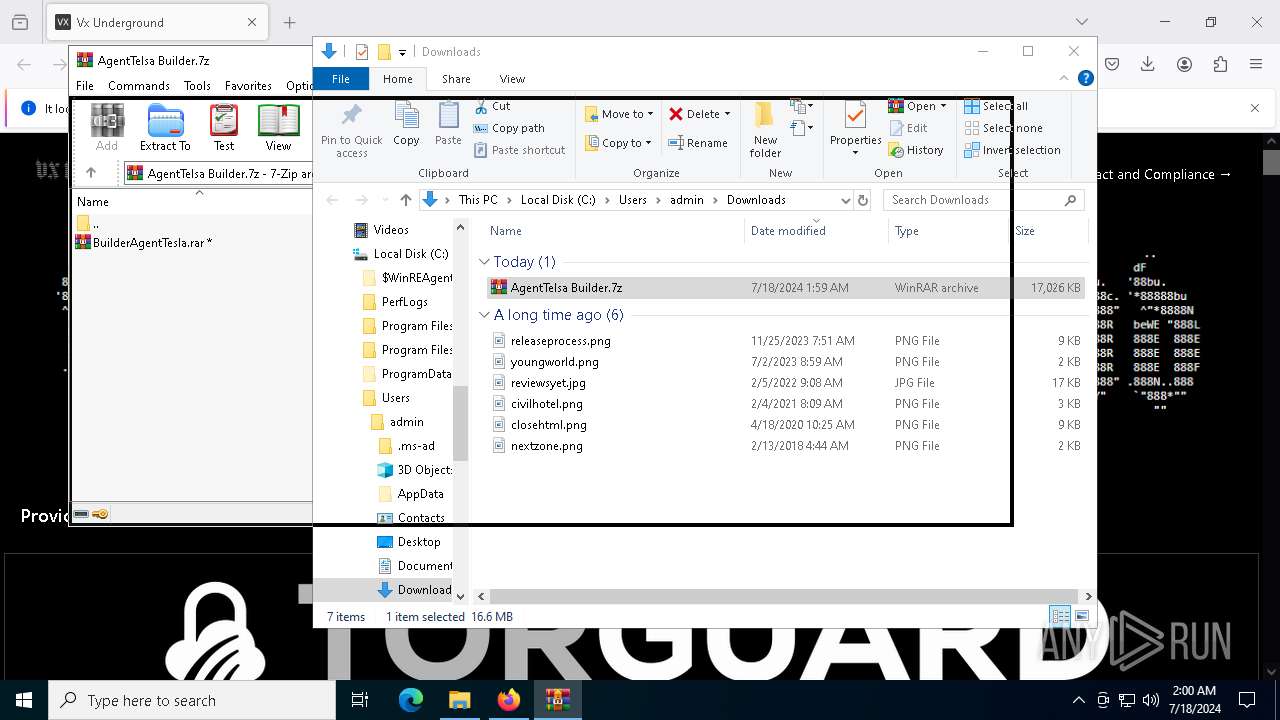
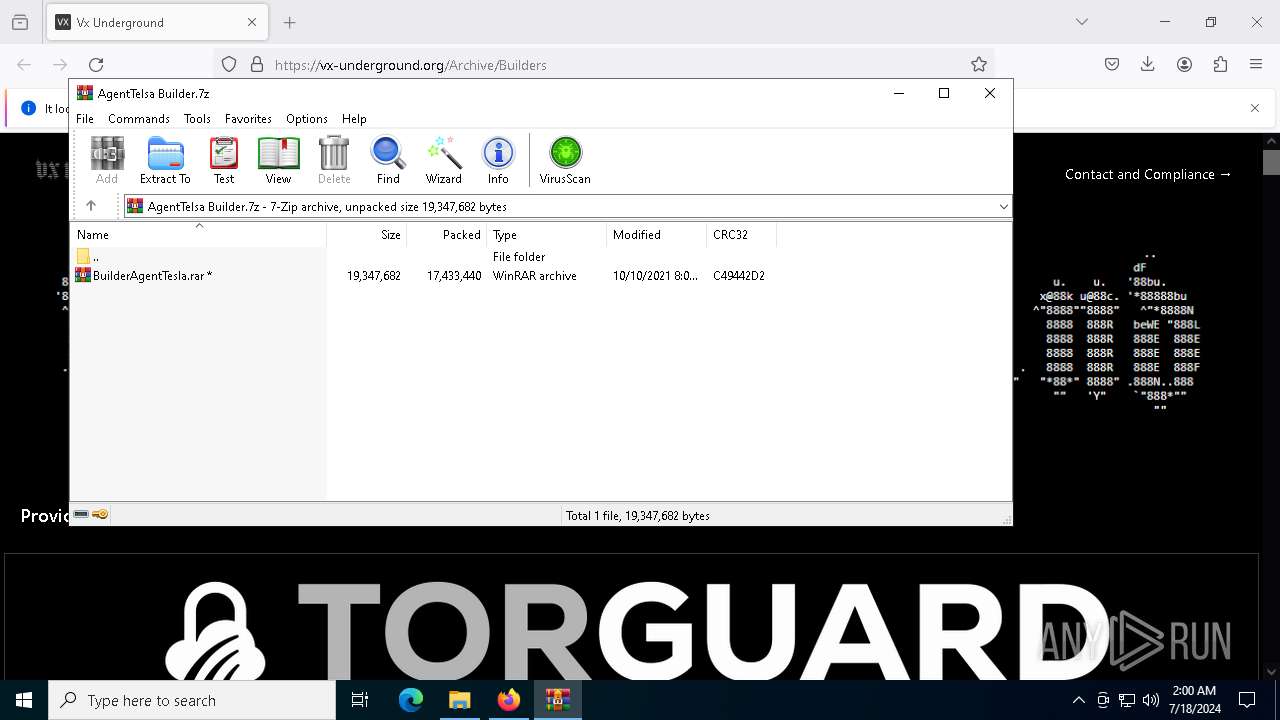
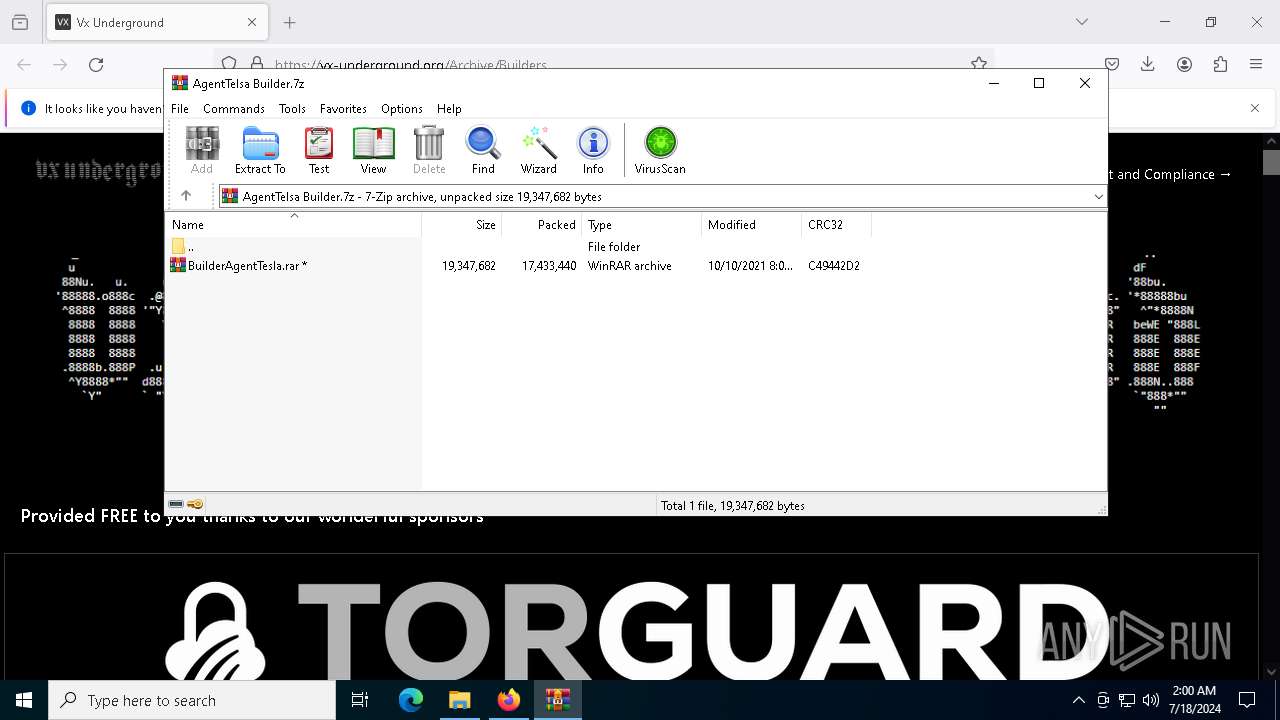
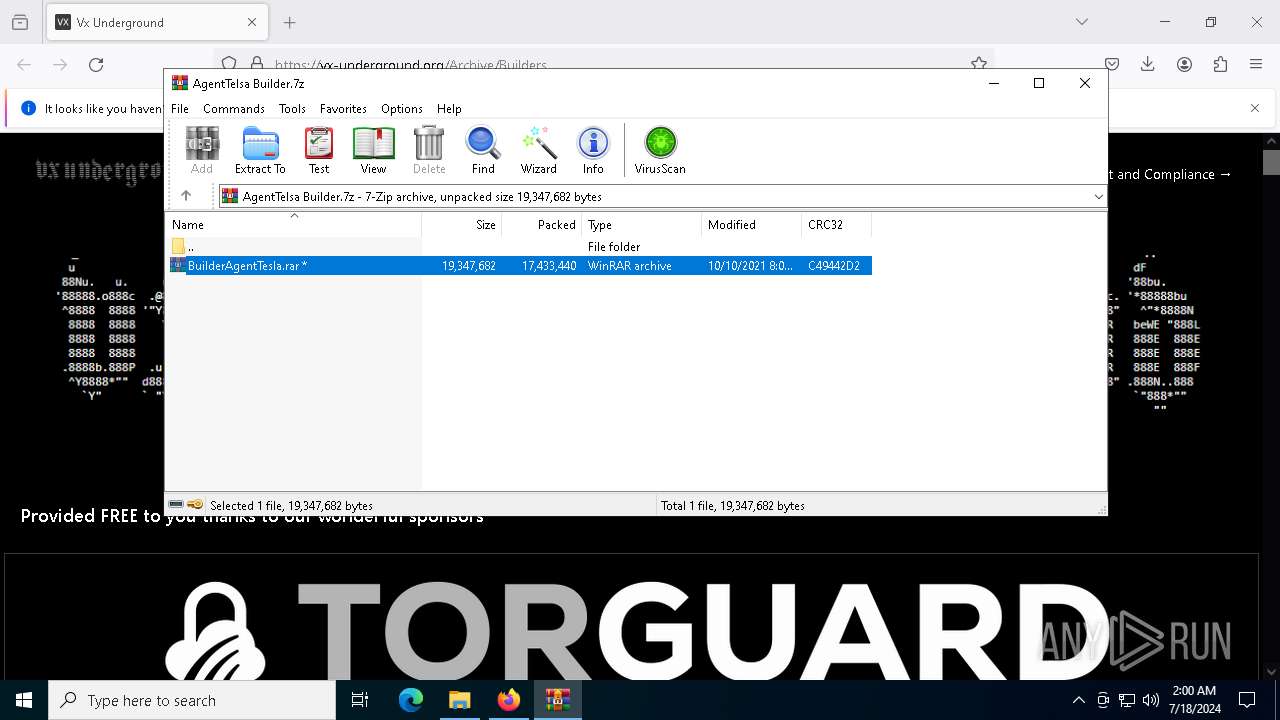
| URL: | https://vx-underground.org/Archive/Builders |
| Full analysis: | https://app.any.run/tasks/489adc66-5ec3-48e2-ab3e-a01cc2eeabf6 |
| Verdict: | Malicious activity |
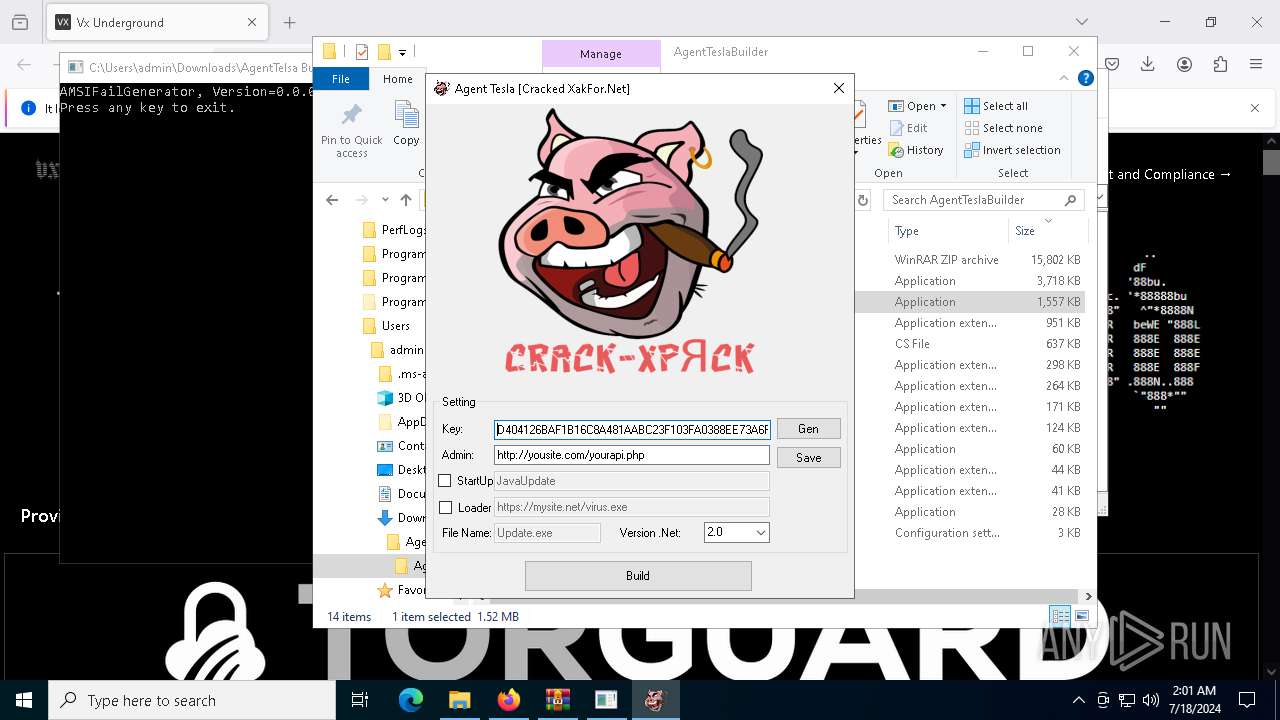
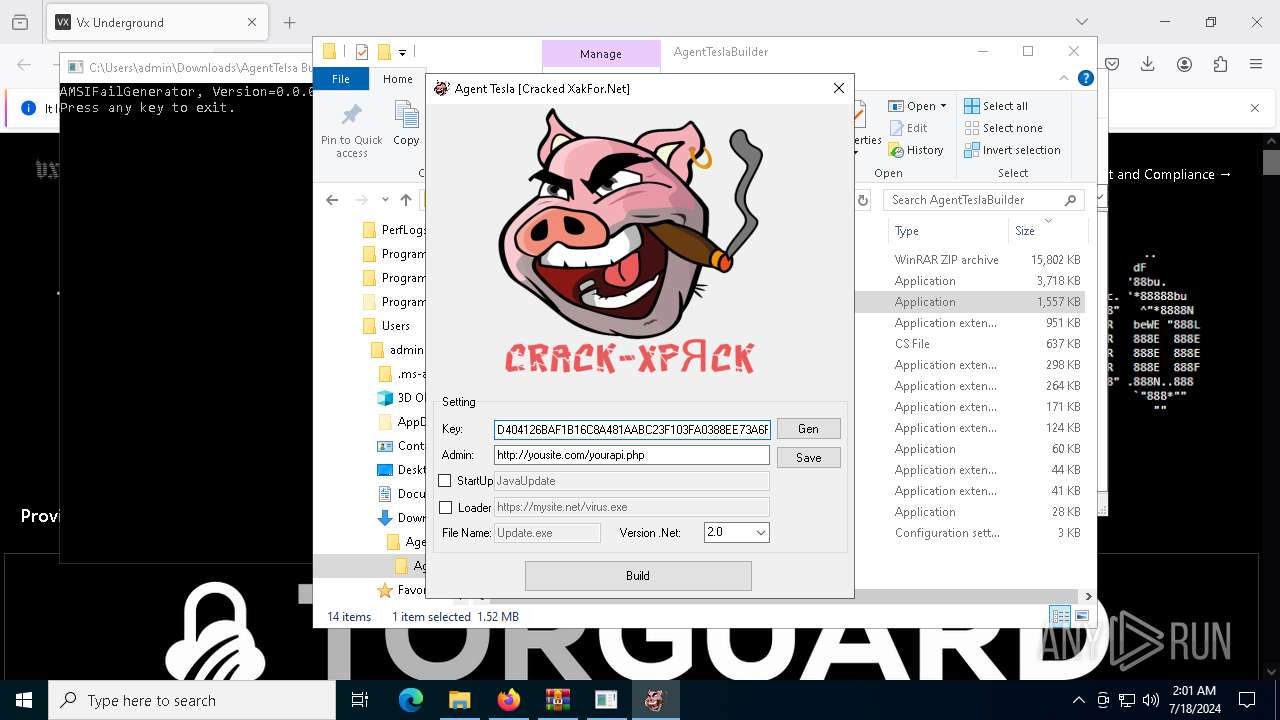
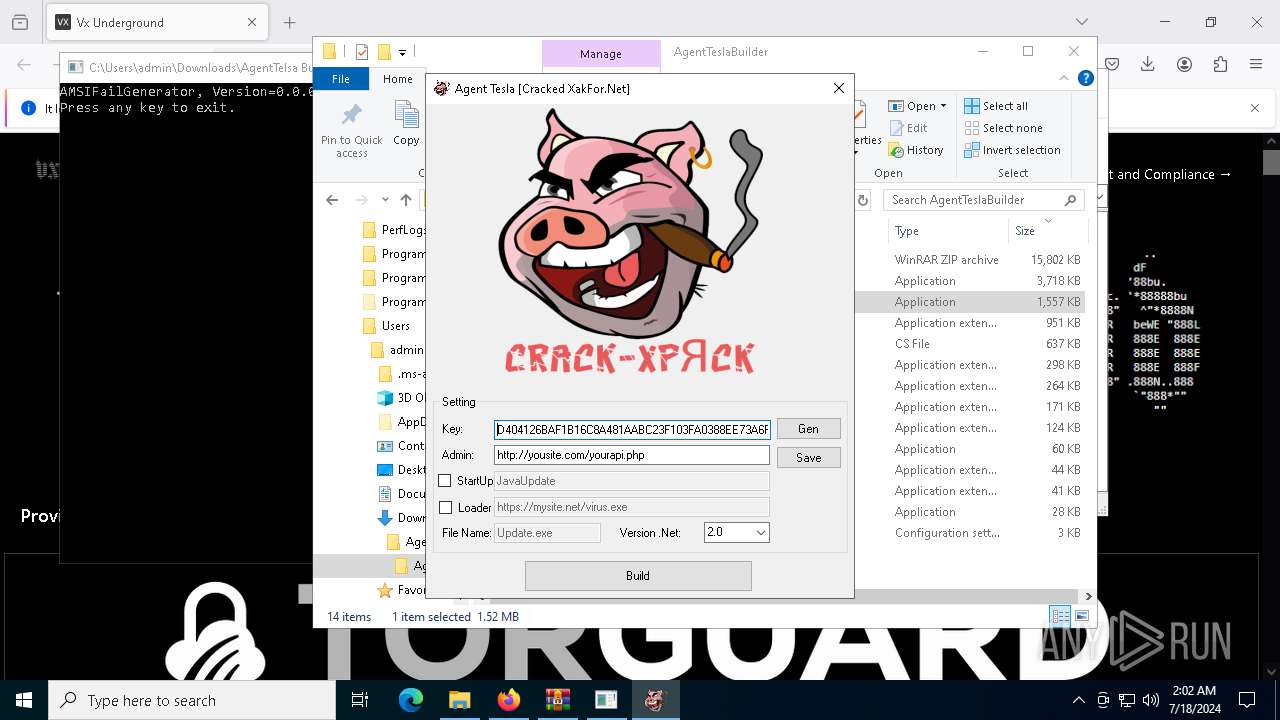
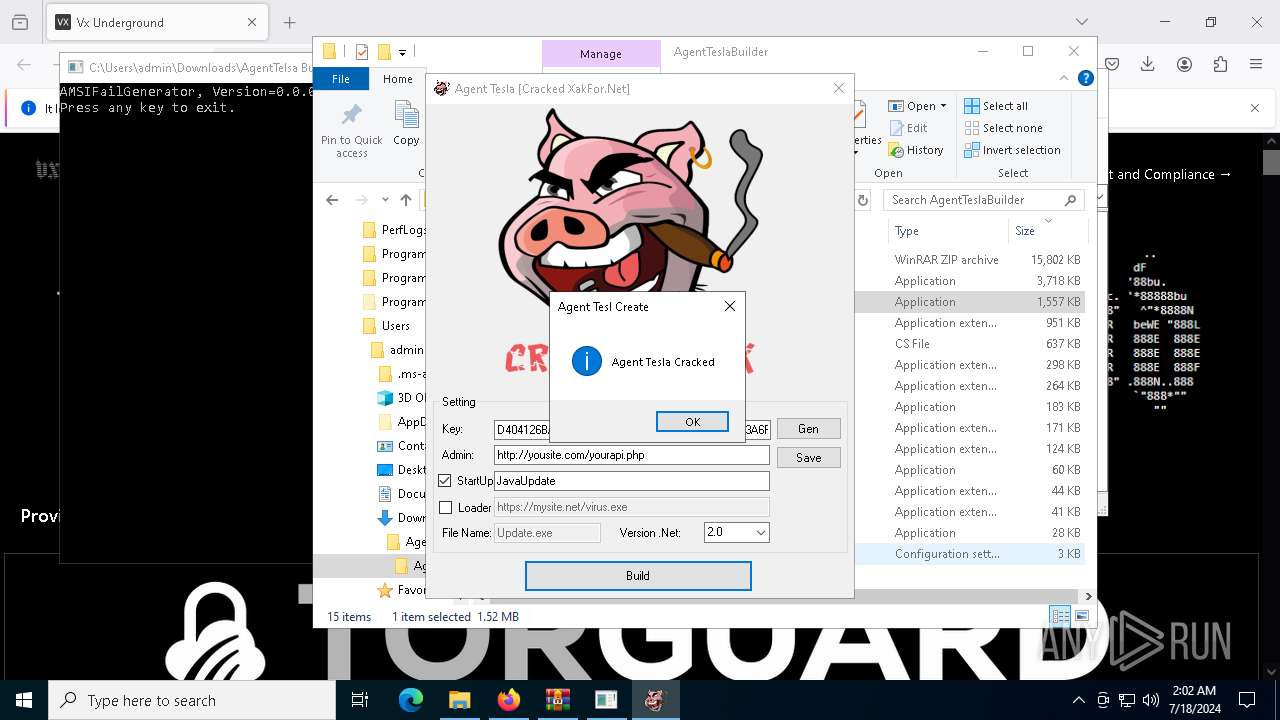
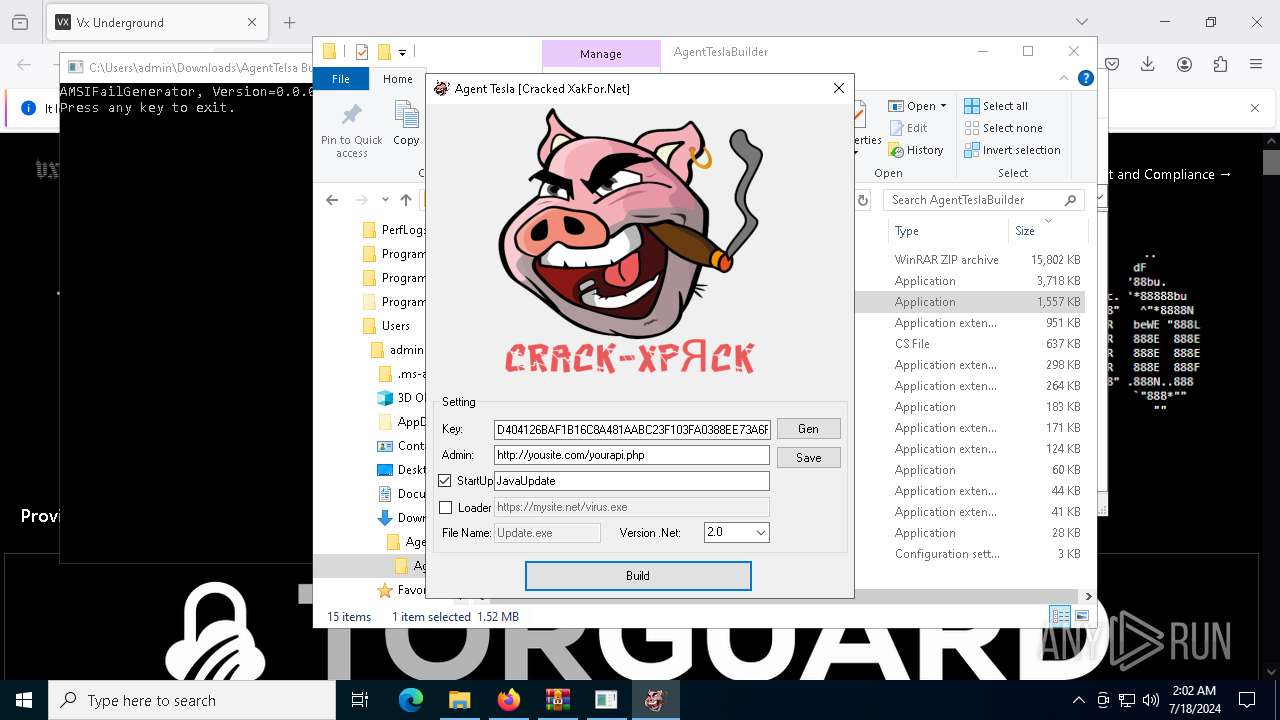
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
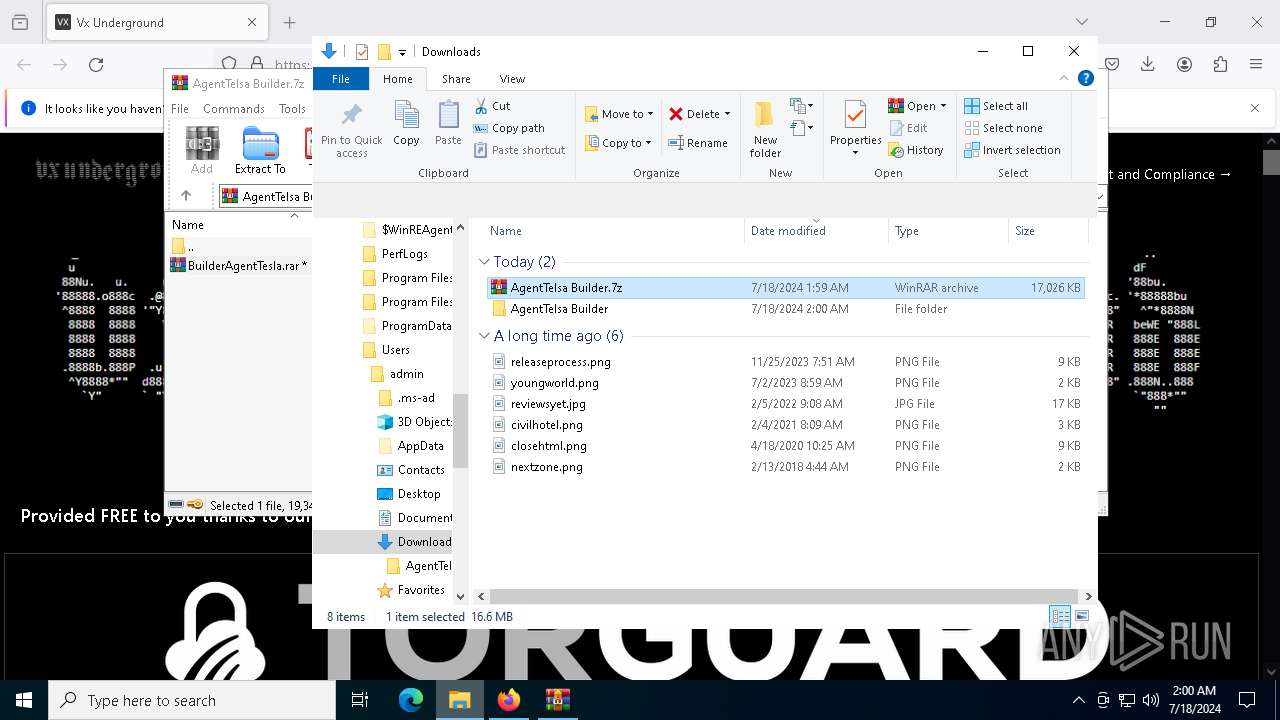
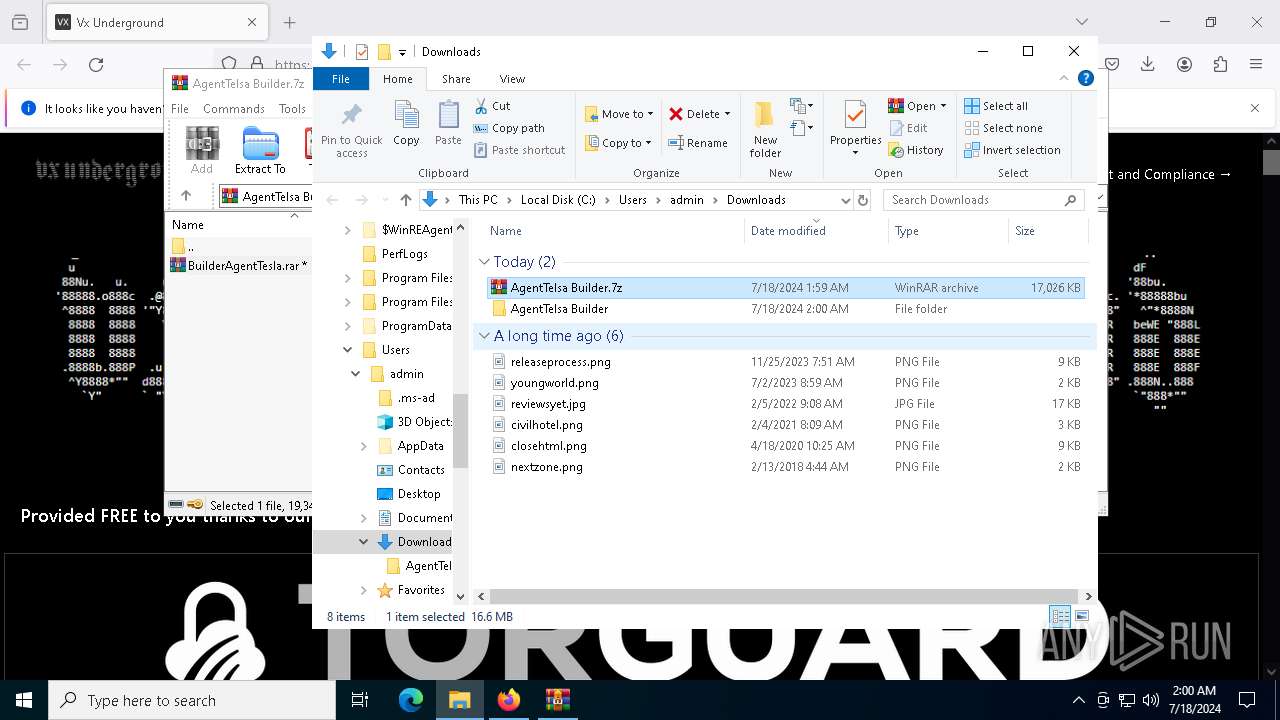
| Analysis date: | July 18, 2024, 01:59:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BD65EE197FBC5868C26C3FE01BDAD042 |
| SHA1: | 18D3FF446E6A89D59E1BA0A2BC4E4F7FE7E89352 |
| SHA256: | D02CD71DA3DE6694E699B23DB311AFA4CF06A2DE8ABF242A9A6CAFF263E8B0A0 |
| SSDEEP: | 3:N83rGNMM8Zd:23raz8Zd |
MALICIOUS
Uses AES cipher (POWERSHELL)
- bye.exe (PID: 524)
Dynamically loads an assembly (POWERSHELL)
- bye.exe (PID: 524)
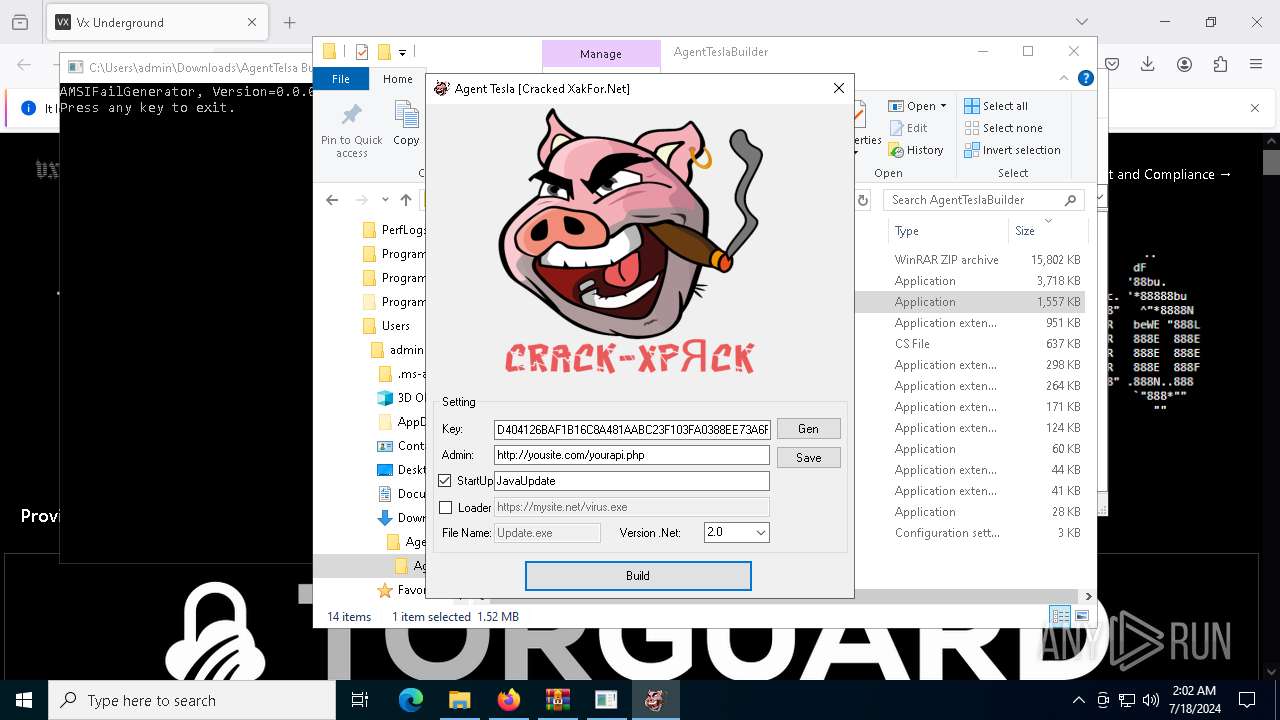
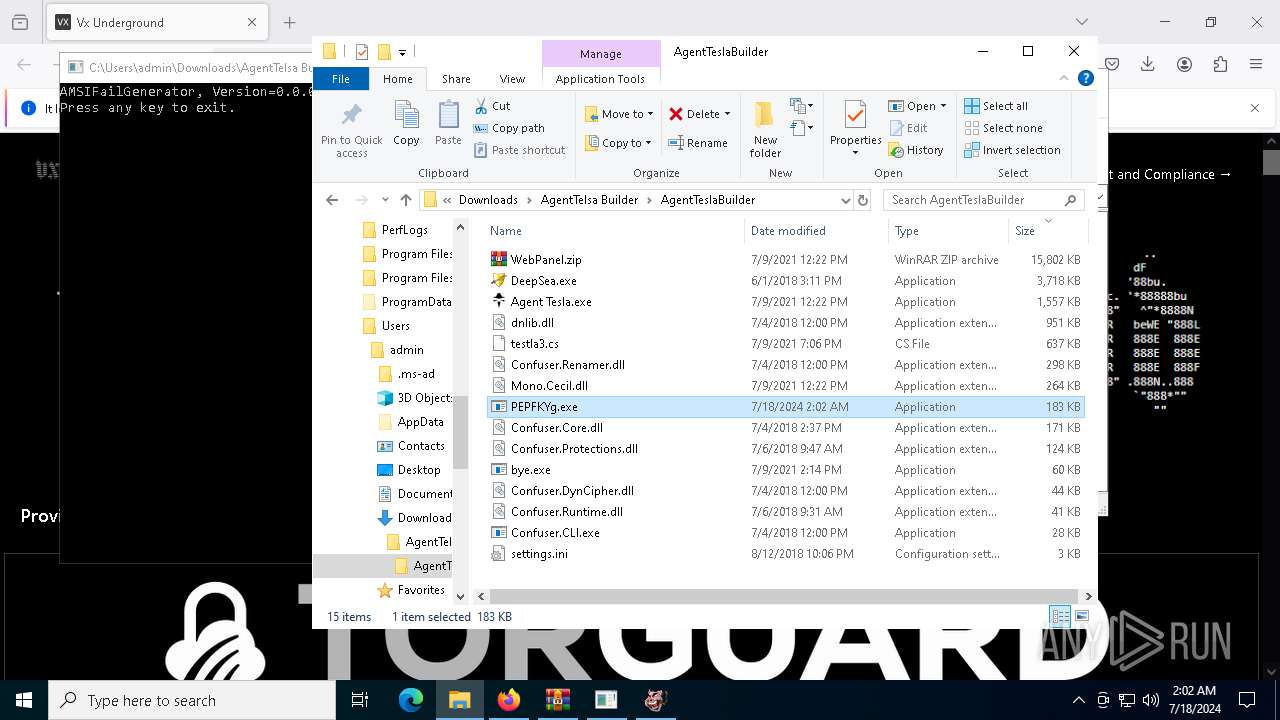
AGENTTESLA has been detected (YARA)
- Agent Tesla.exe (PID: 5332)
- PEPFKYg.exe (PID: 5880)
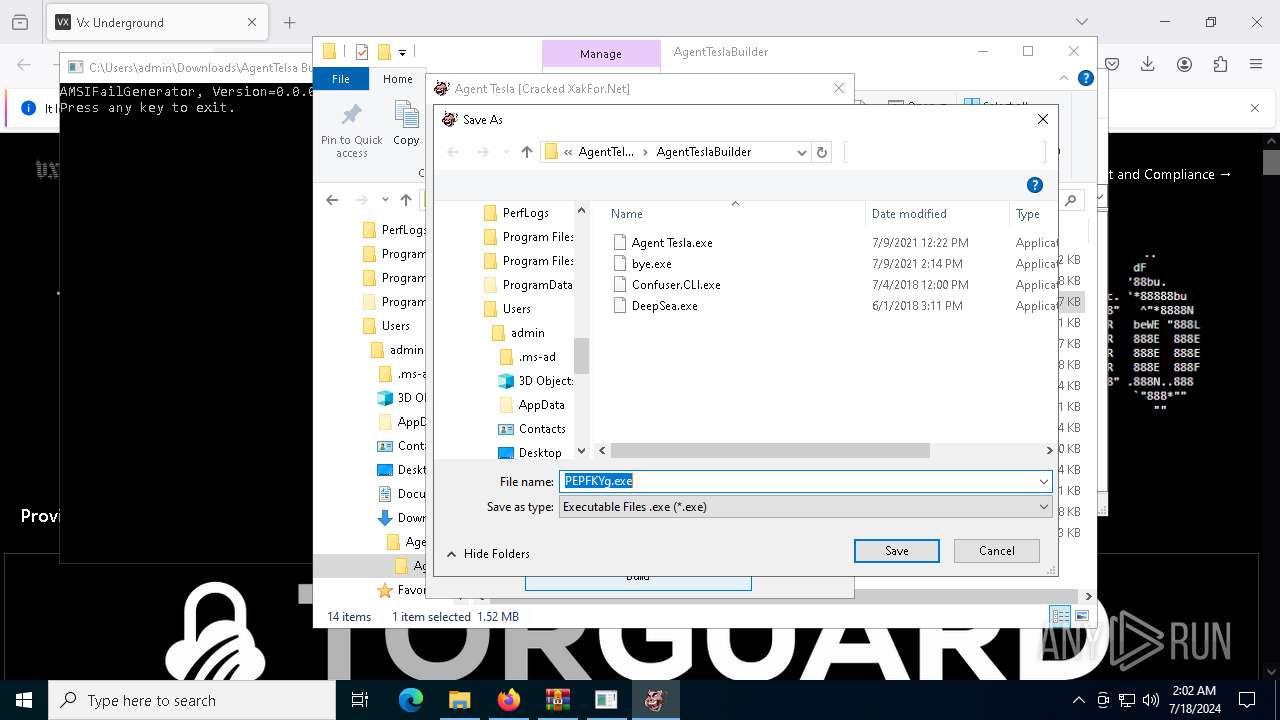
Drops the executable file immediately after the start
- Agent Tesla.exe (PID: 5332)
- PEPFKYg.exe (PID: 5880)
Connects to the CnC server
- PEPFKYg.exe (PID: 5880)
Actions looks like stealing of personal data
- PEPFKYg.exe (PID: 5880)
AGENTTESLA has been detected (SURICATA)
- PEPFKYg.exe (PID: 5880)
Changes the autorun value in the registry
- PEPFKYg.exe (PID: 5880)
Scans artifacts that could help determine the target
- PEPFKYg.exe (PID: 5880)
AGENTTESLA was detected (strings)
- PEPFKYg.exe (PID: 5880)
Steals credentials from Web Browsers
- PEPFKYg.exe (PID: 5880)
SUSPICIOUS
Reads security settings of Internet Explorer
- bye.exe (PID: 524)
- Agent Tesla.exe (PID: 5332)
- PEPFKYg.exe (PID: 5880)
Checks Windows Trust Settings
- bye.exe (PID: 524)
Reverses array data (POWERSHELL)
- bye.exe (PID: 524)
Uses base64 encoding (POWERSHELL)
- bye.exe (PID: 524)
Converts a string into array of characters (POWERSHELL)
- bye.exe (PID: 524)
Executable content was dropped or overwritten
- Agent Tesla.exe (PID: 5332)
- PEPFKYg.exe (PID: 5880)
Creates file in the systems drive root
- Agent Tesla.exe (PID: 5332)
Checks for external IP
- PEPFKYg.exe (PID: 5880)
Contacting a server suspected of hosting an CnC
- PEPFKYg.exe (PID: 5880)
INFO
Reads Microsoft Office registry keys
- firefox.exe (PID: 884)
- PEPFKYg.exe (PID: 5880)
Application launched itself
- firefox.exe (PID: 4180)
- firefox.exe (PID: 884)
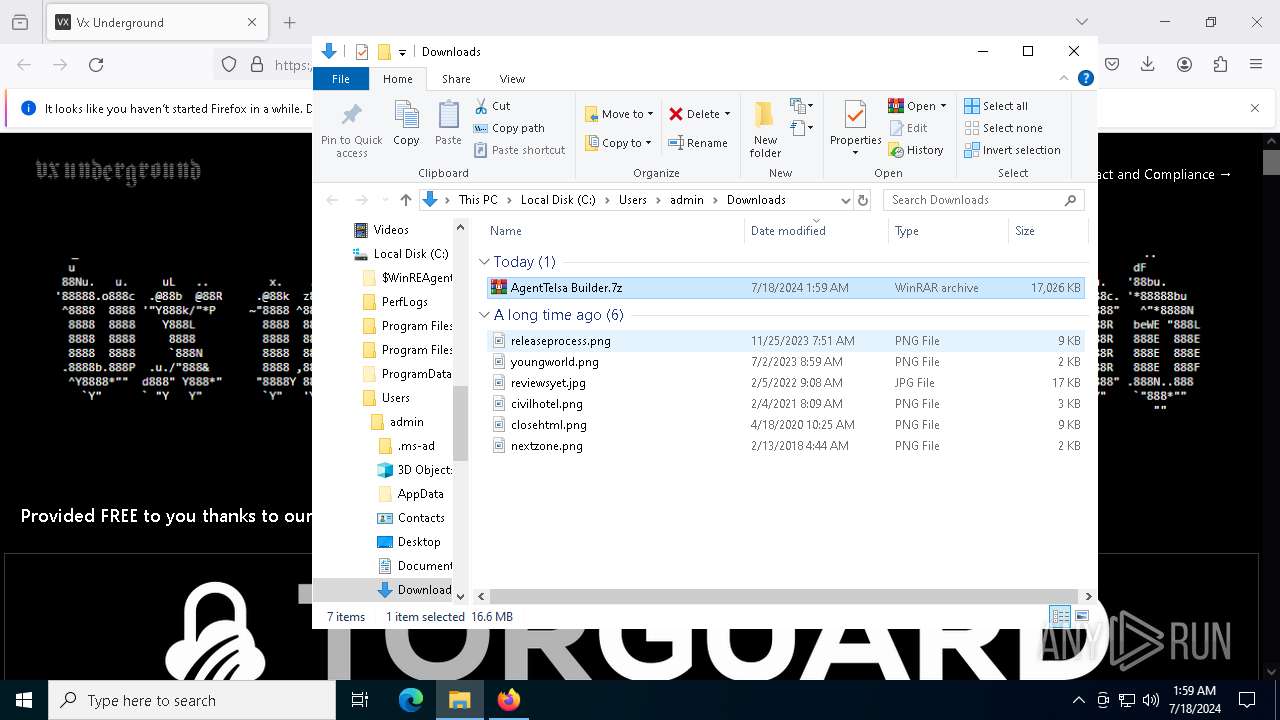
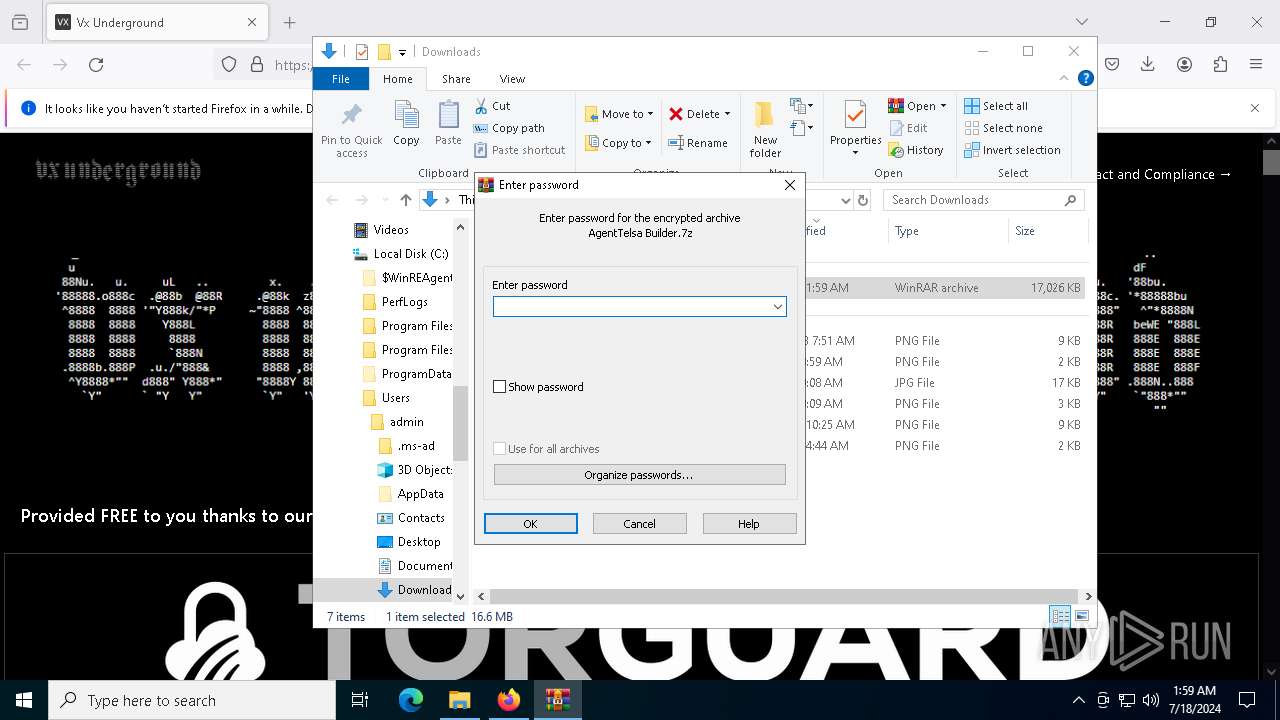
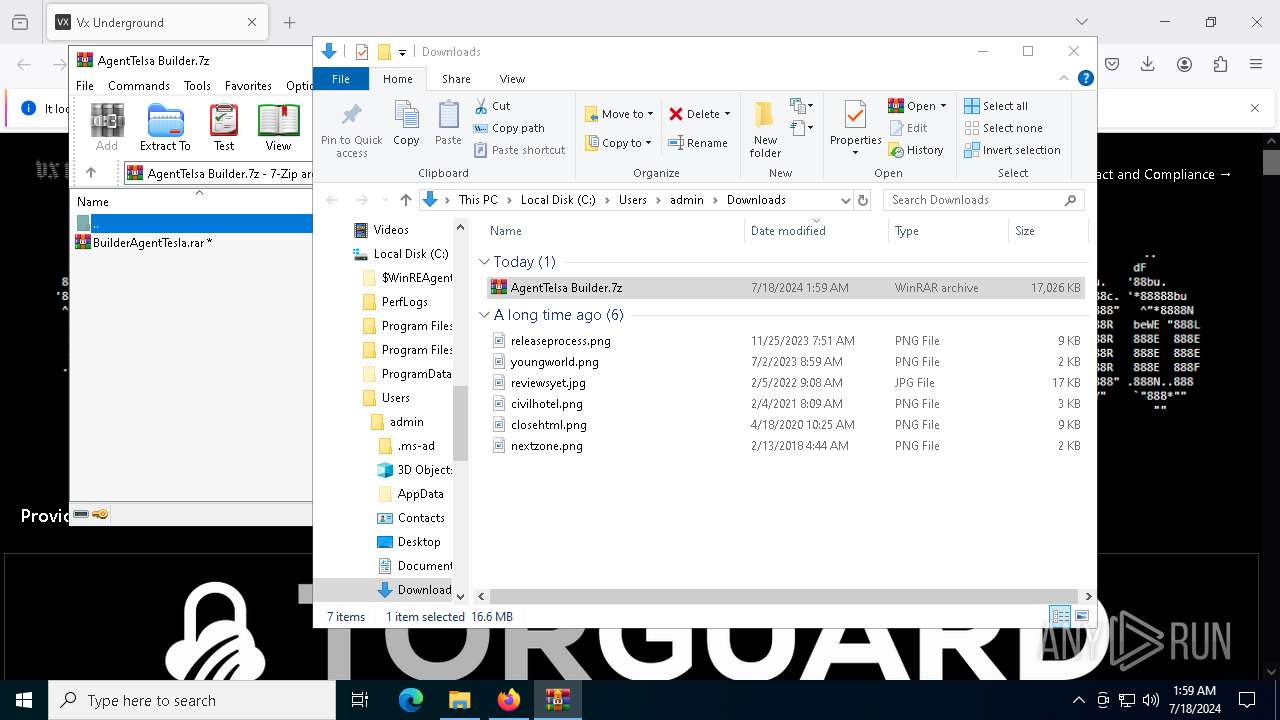
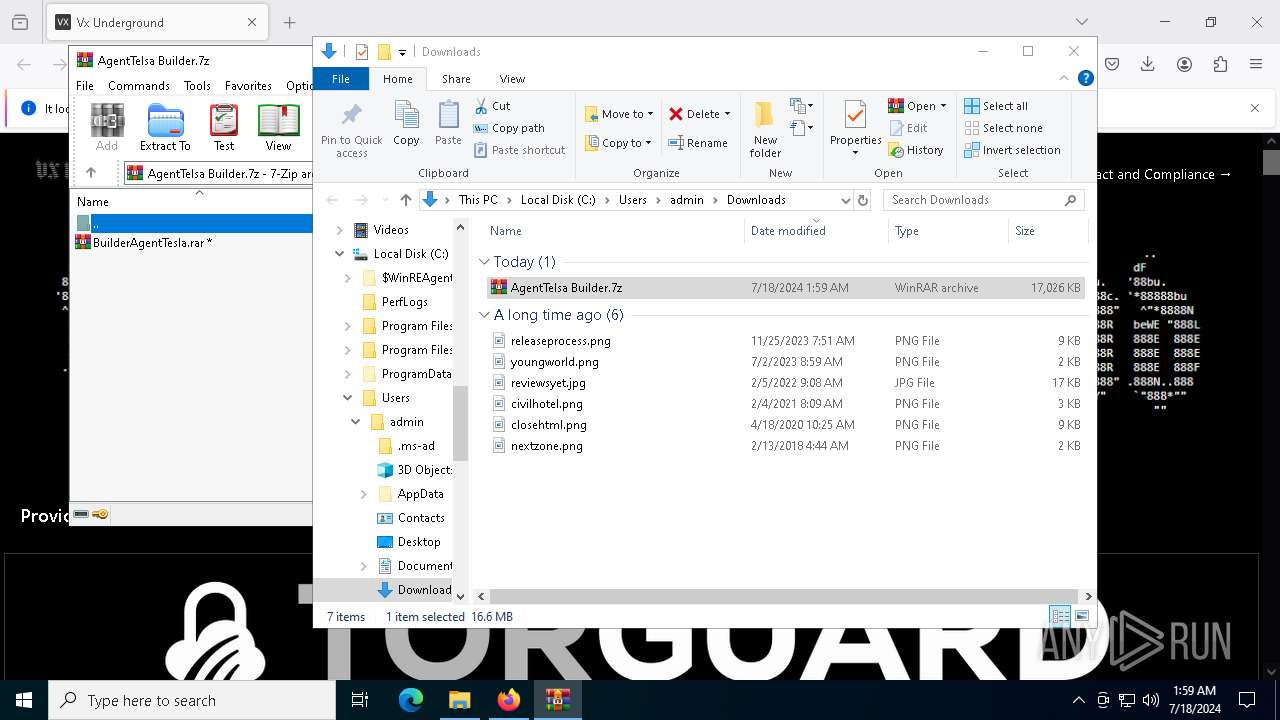
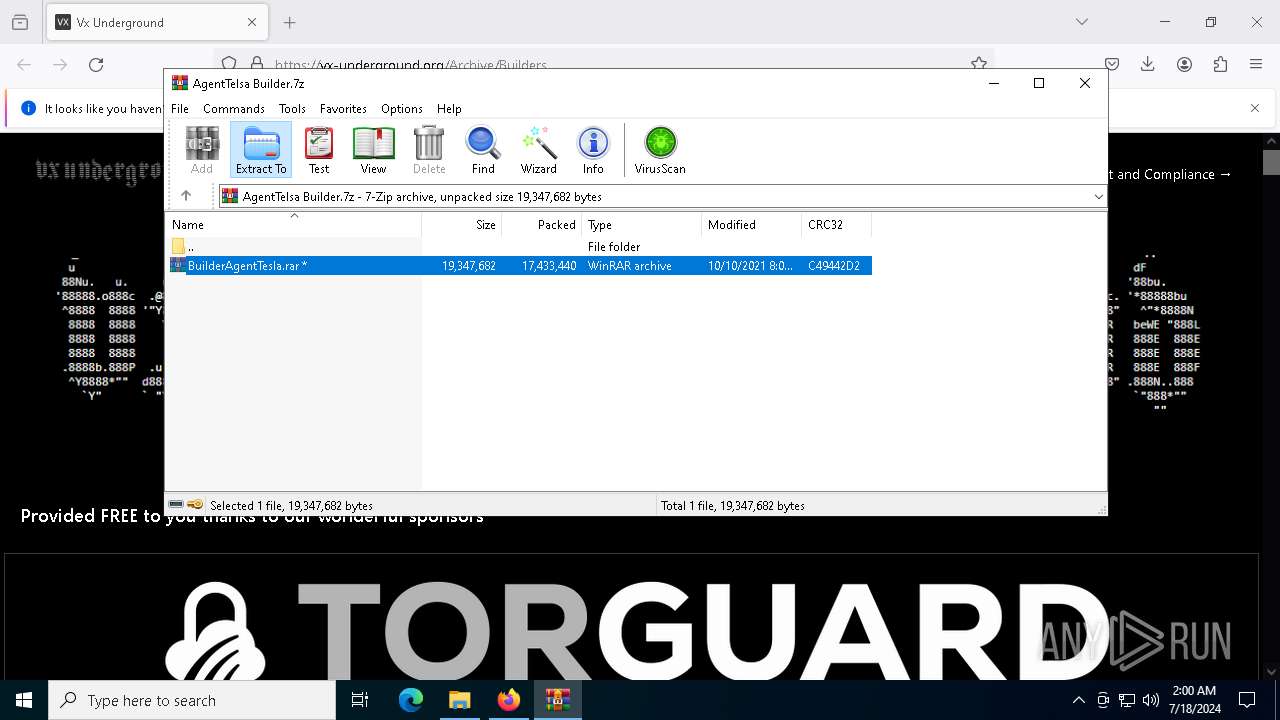
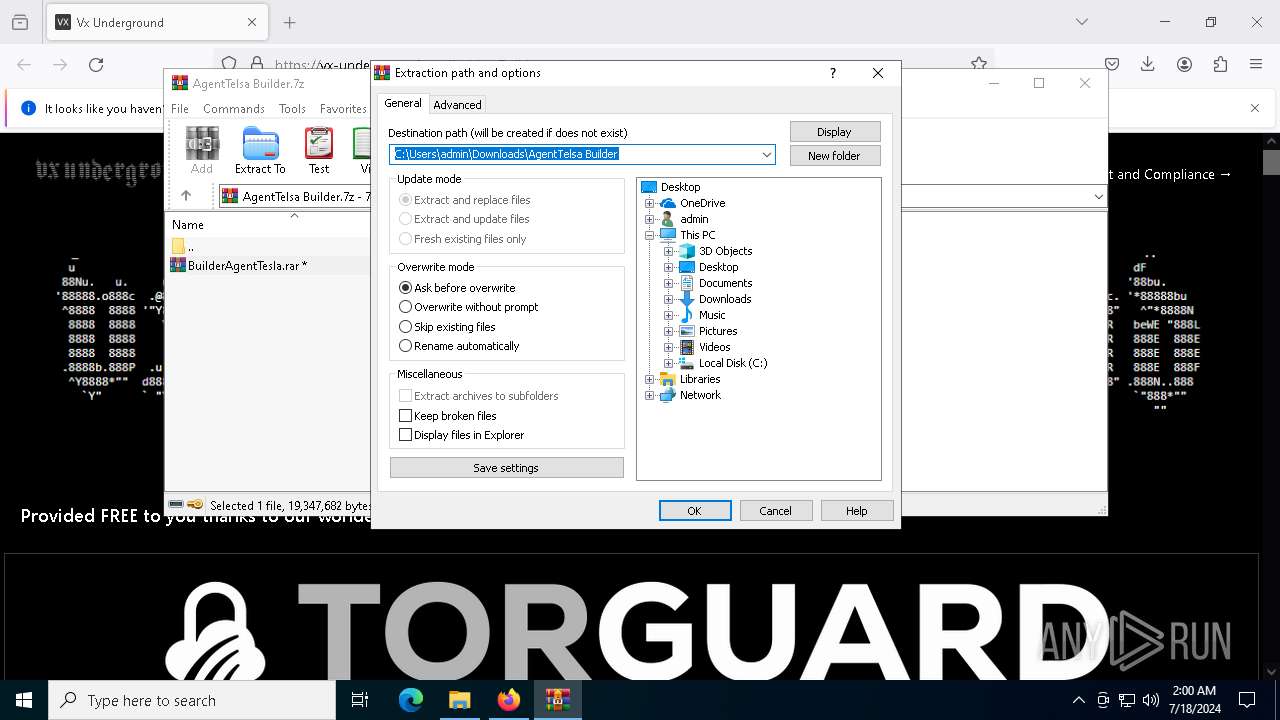
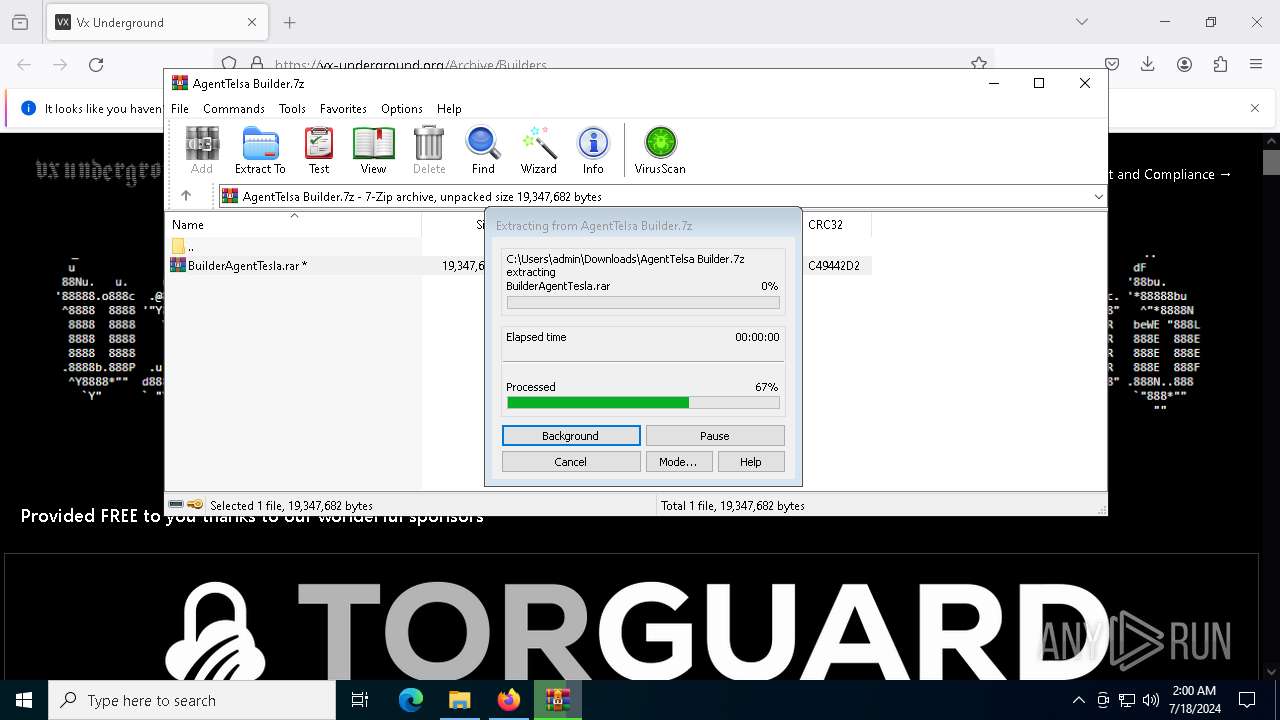
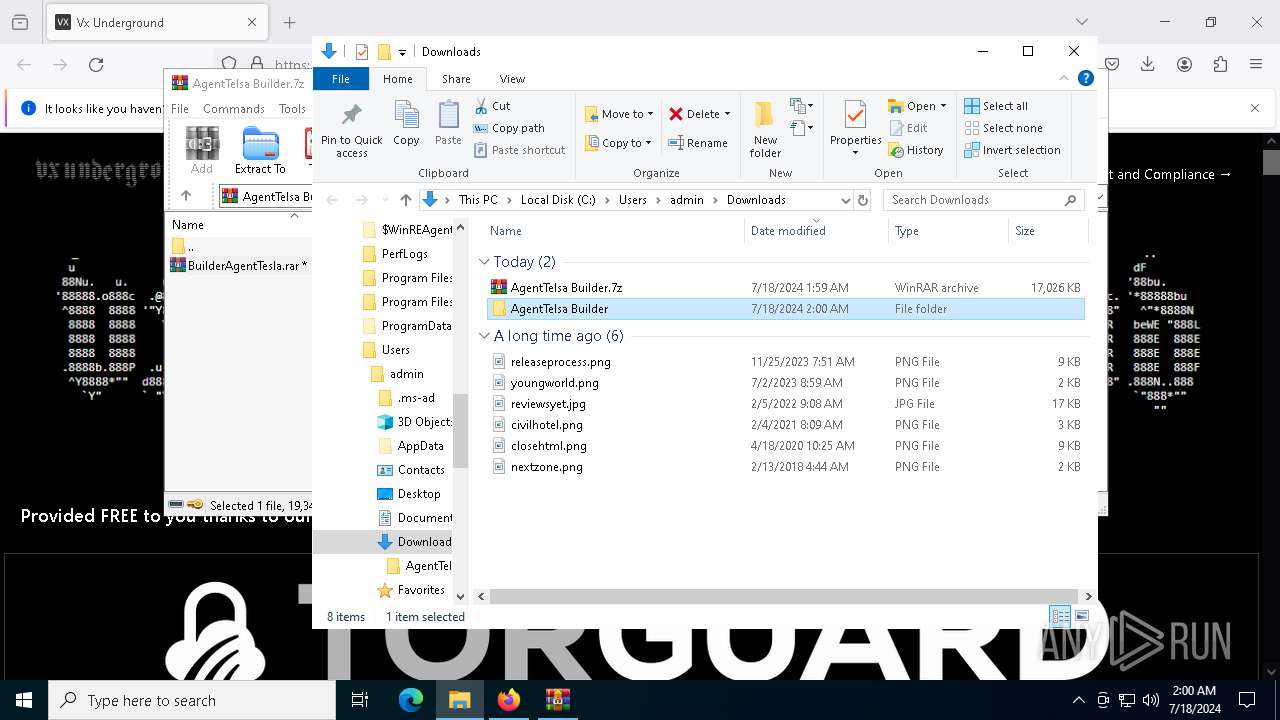
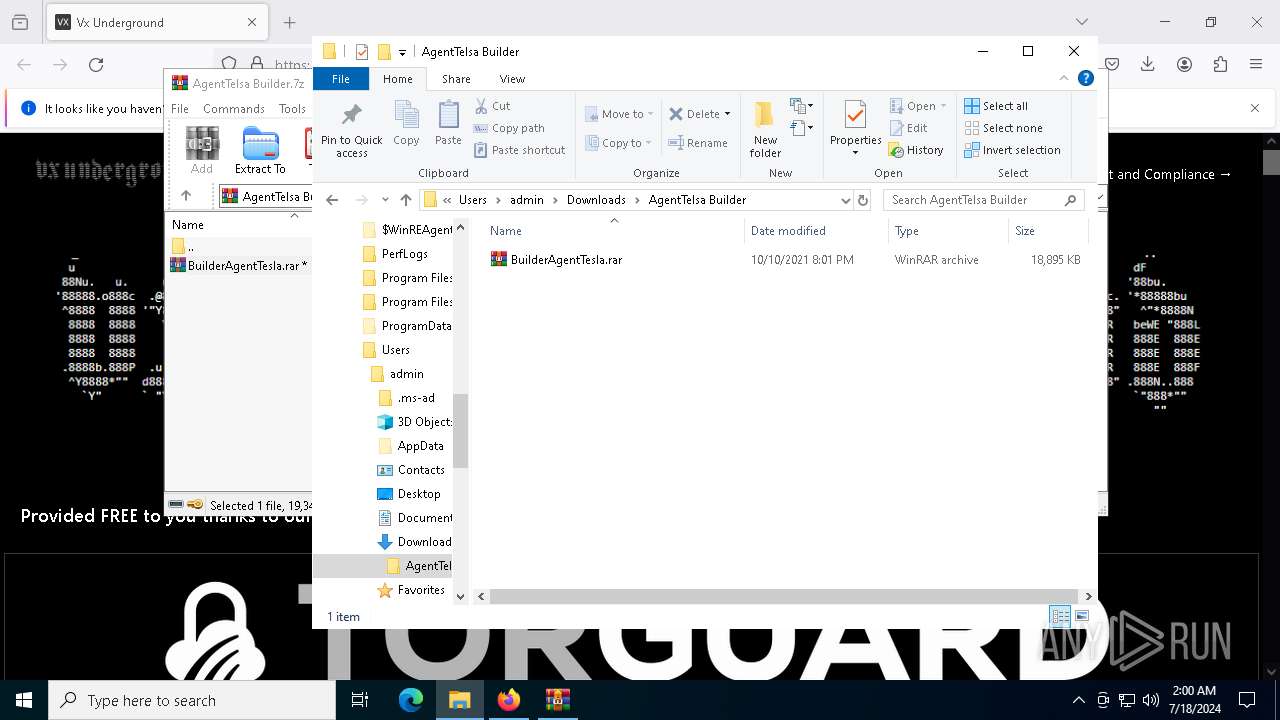
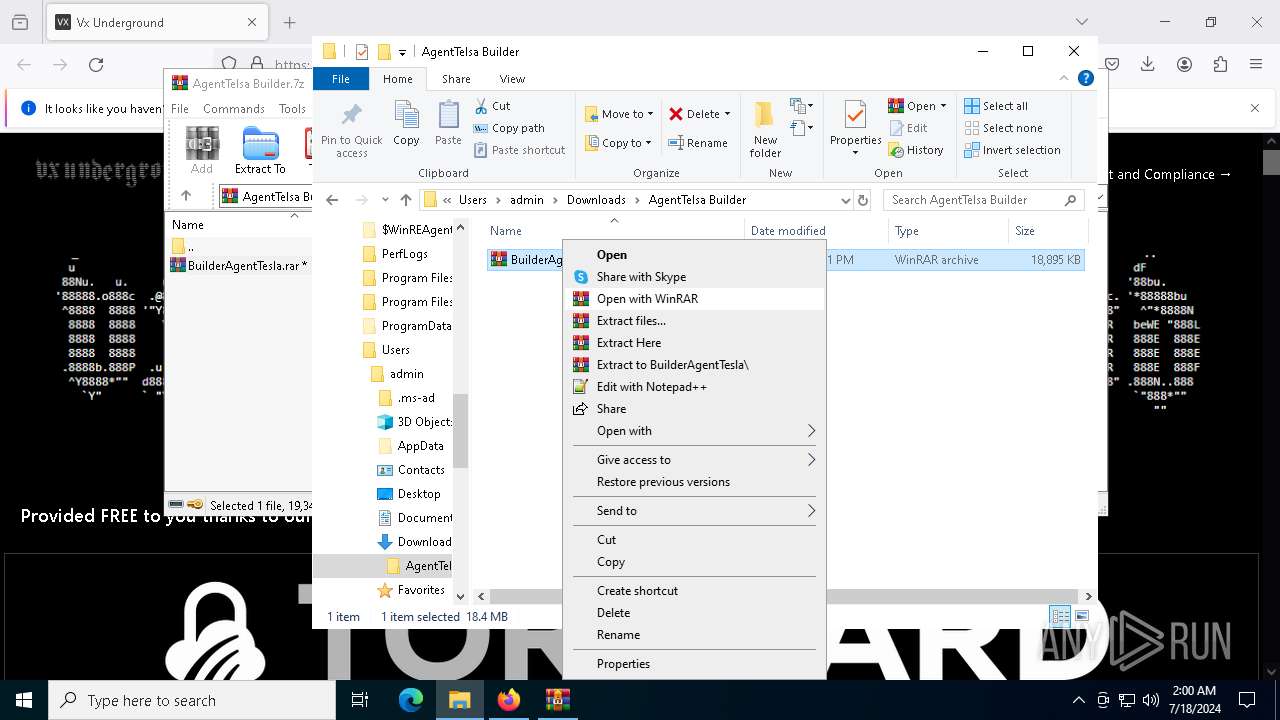
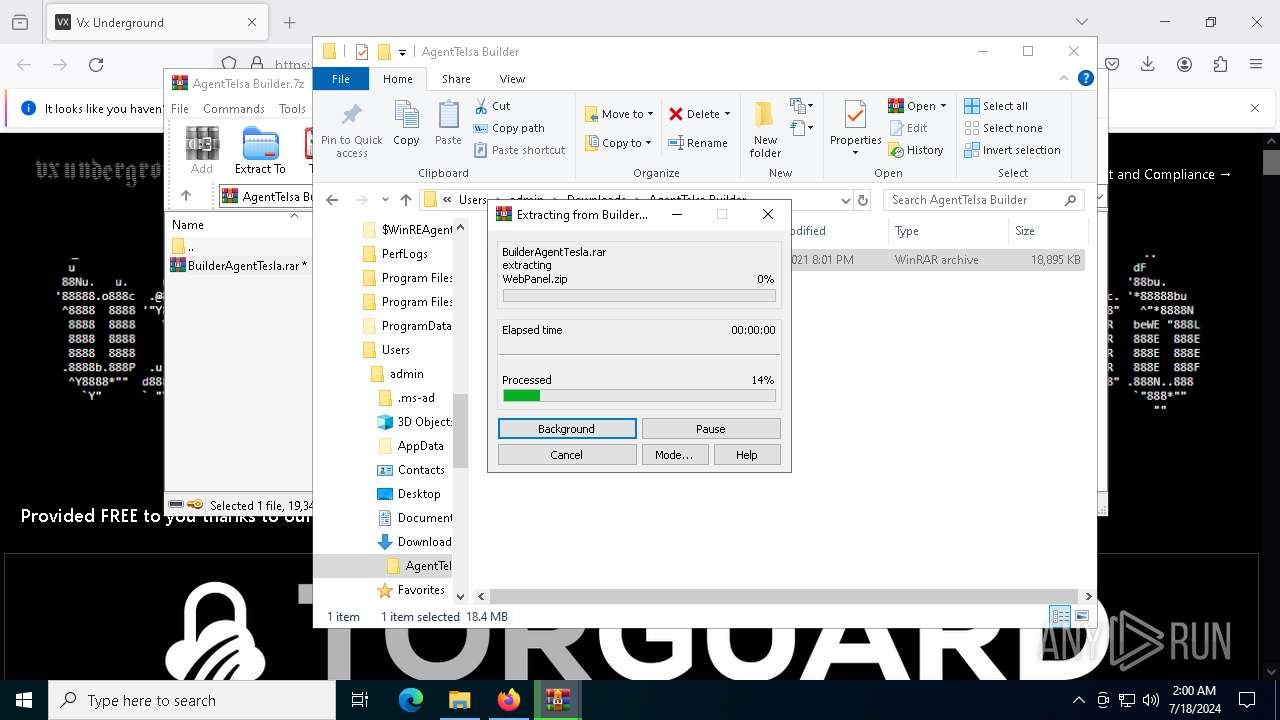
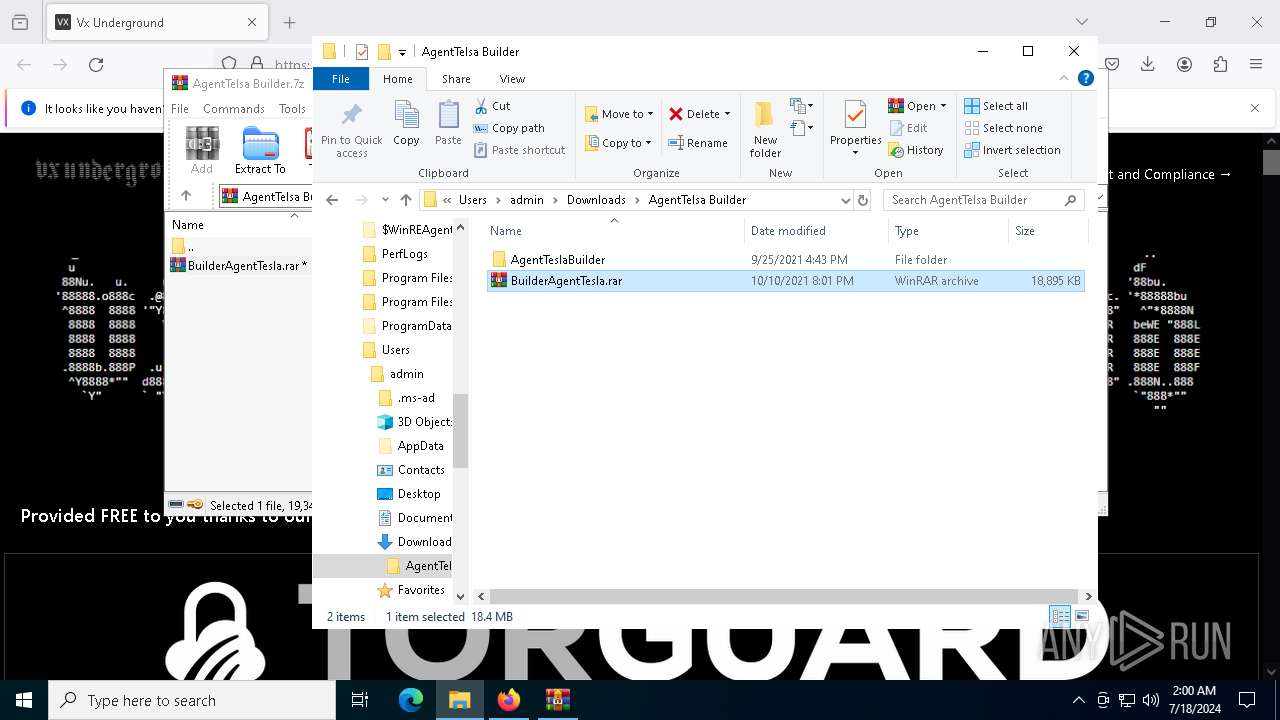
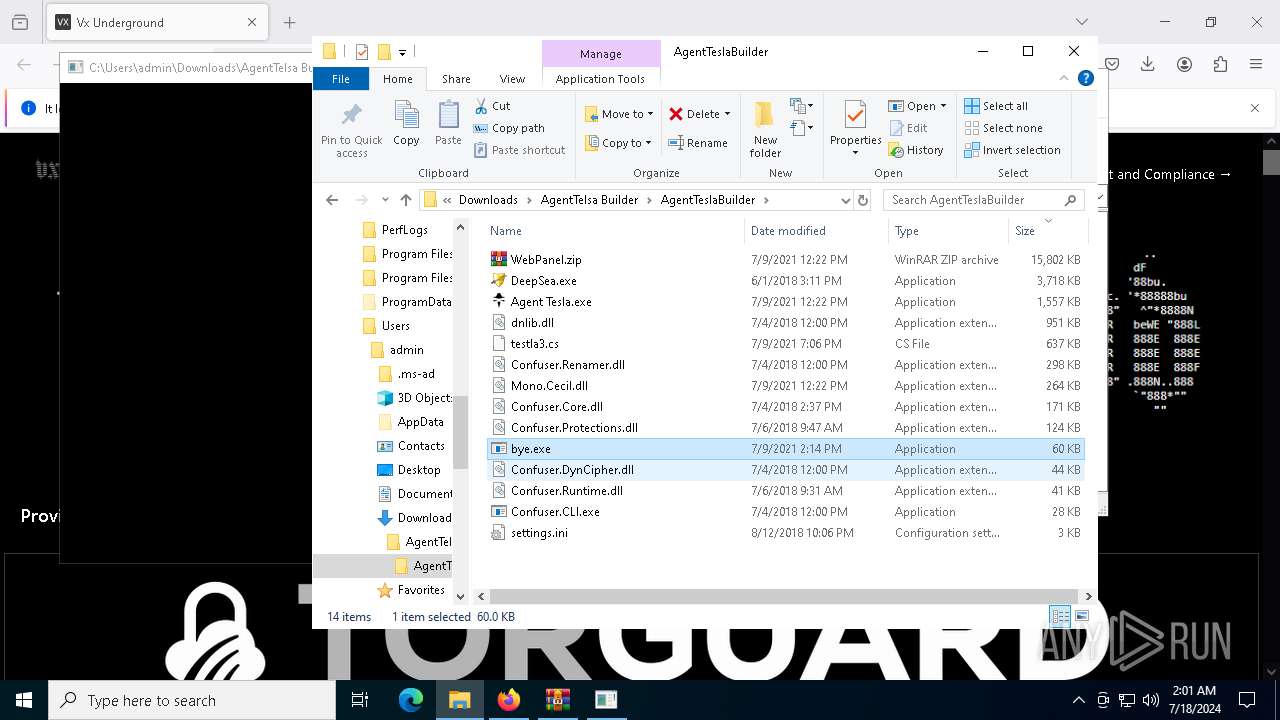
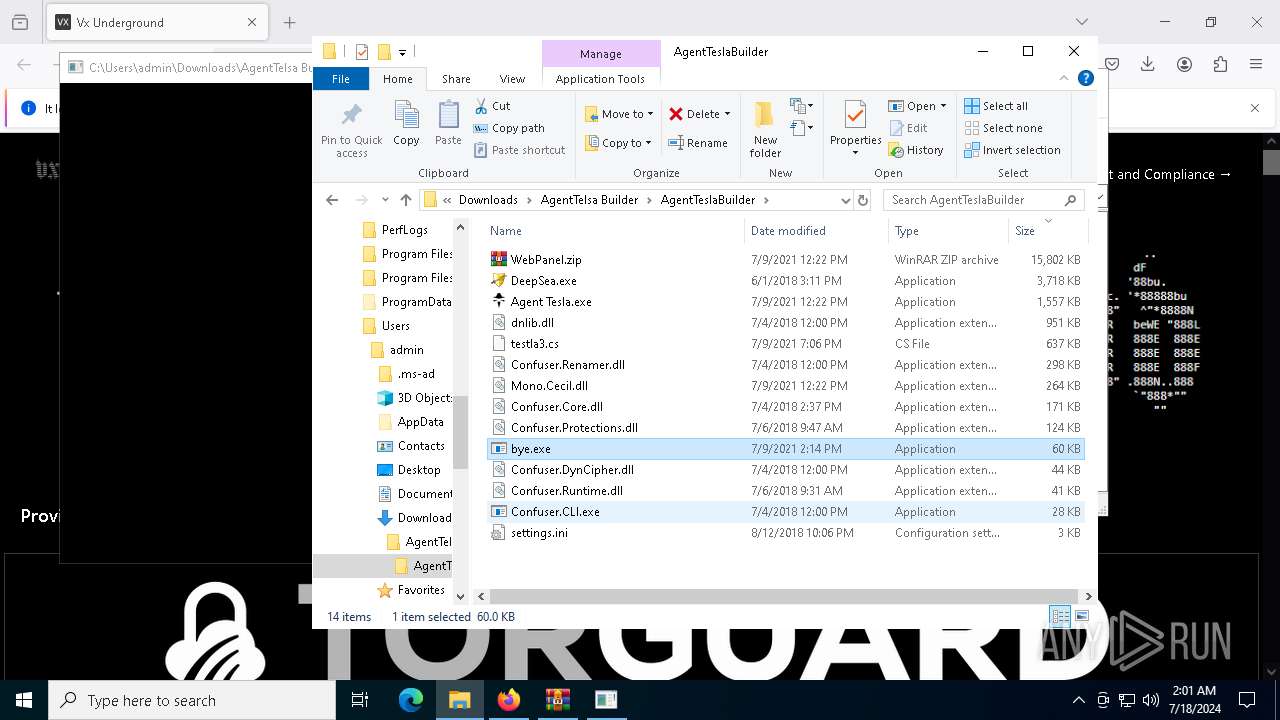
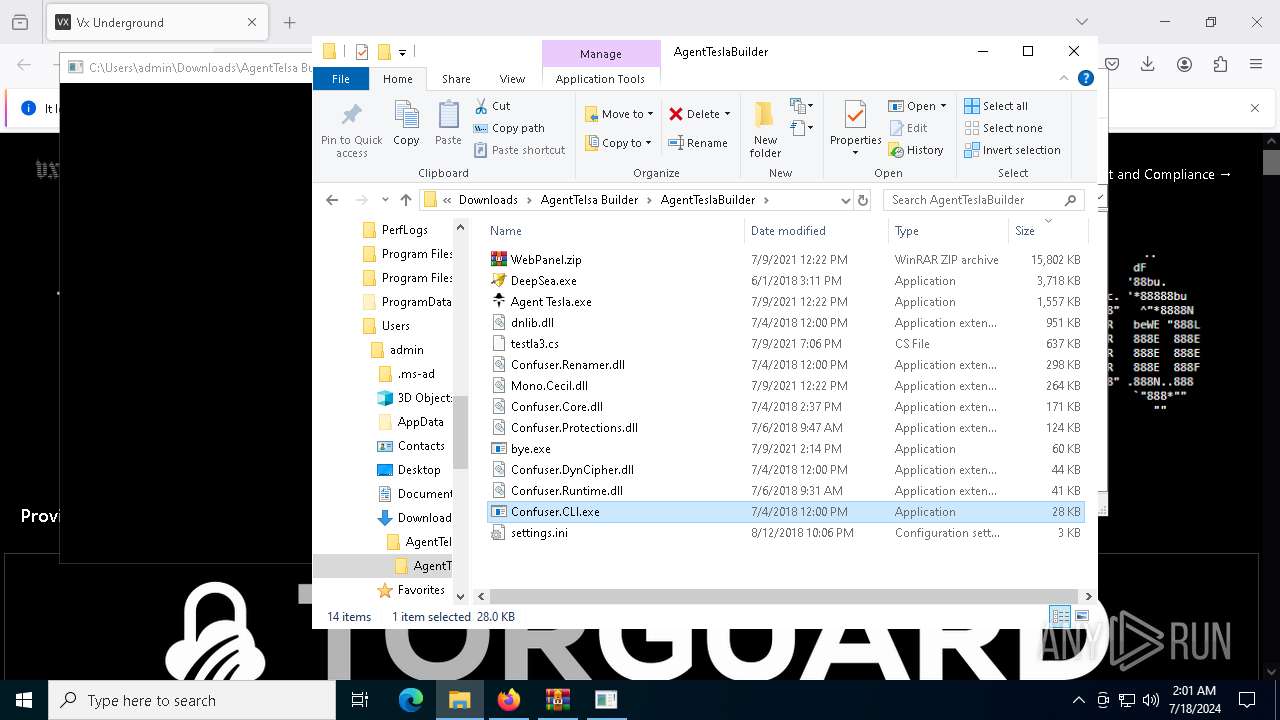
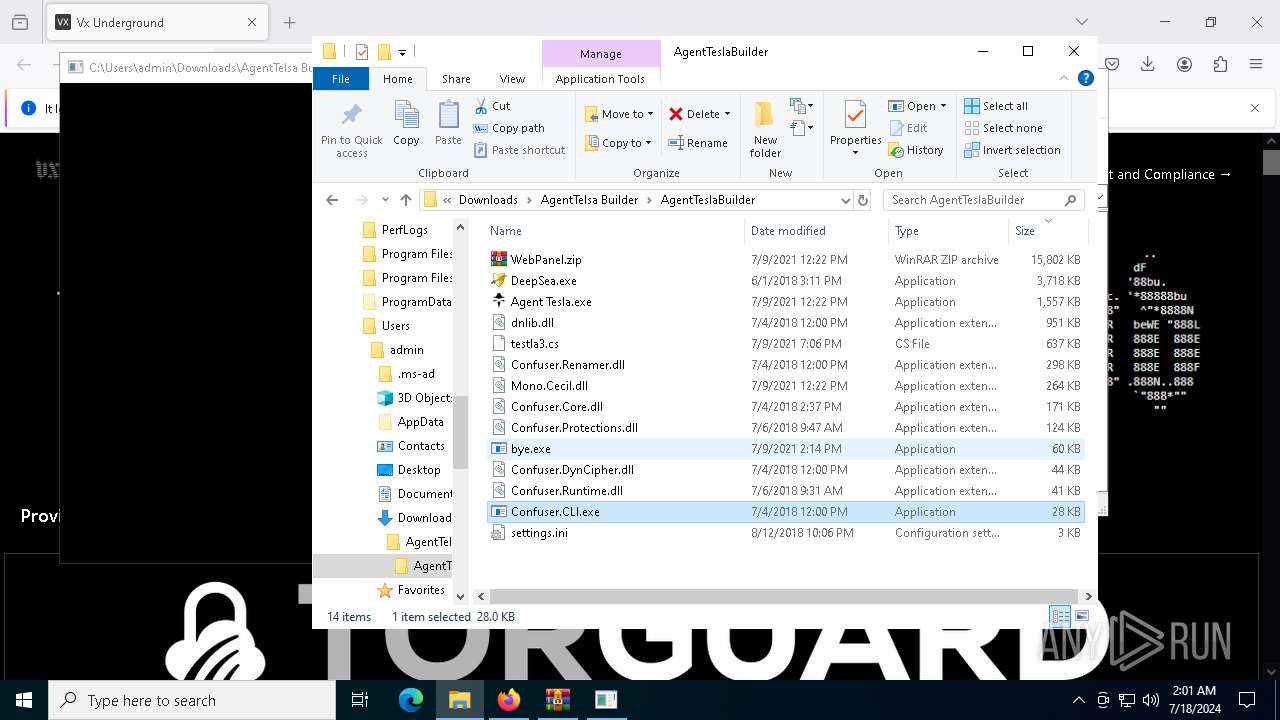
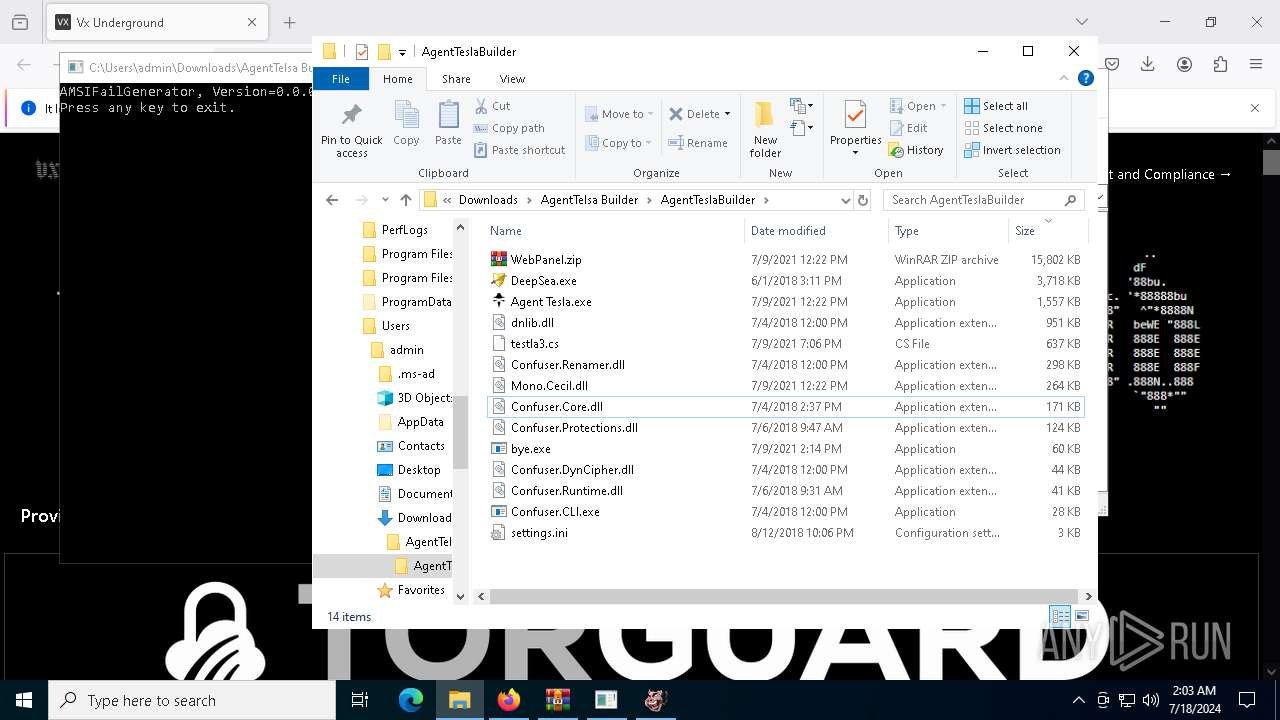
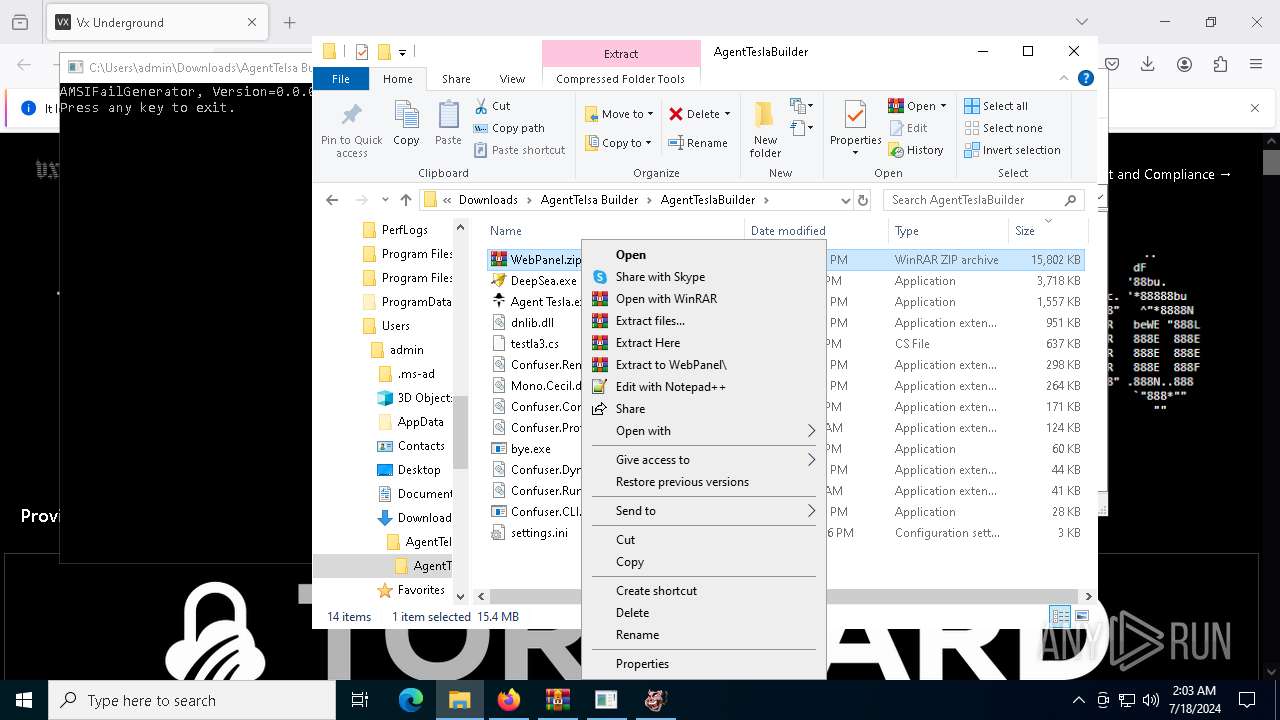
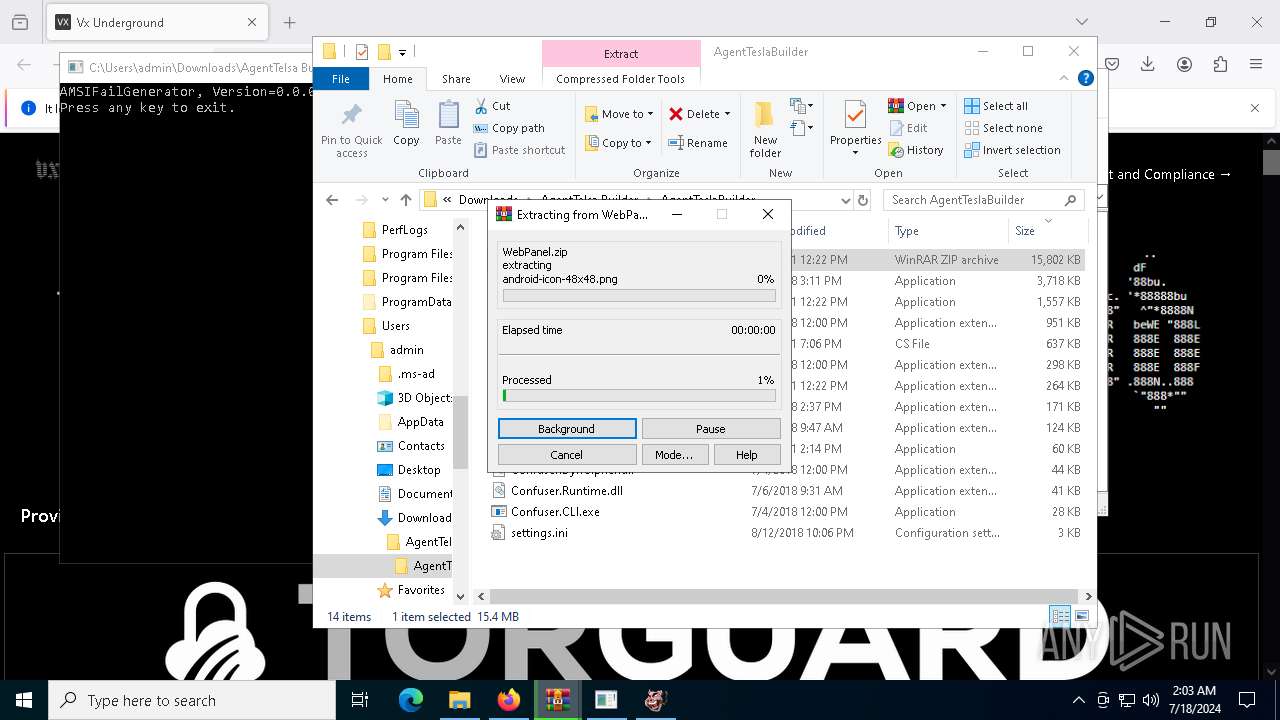
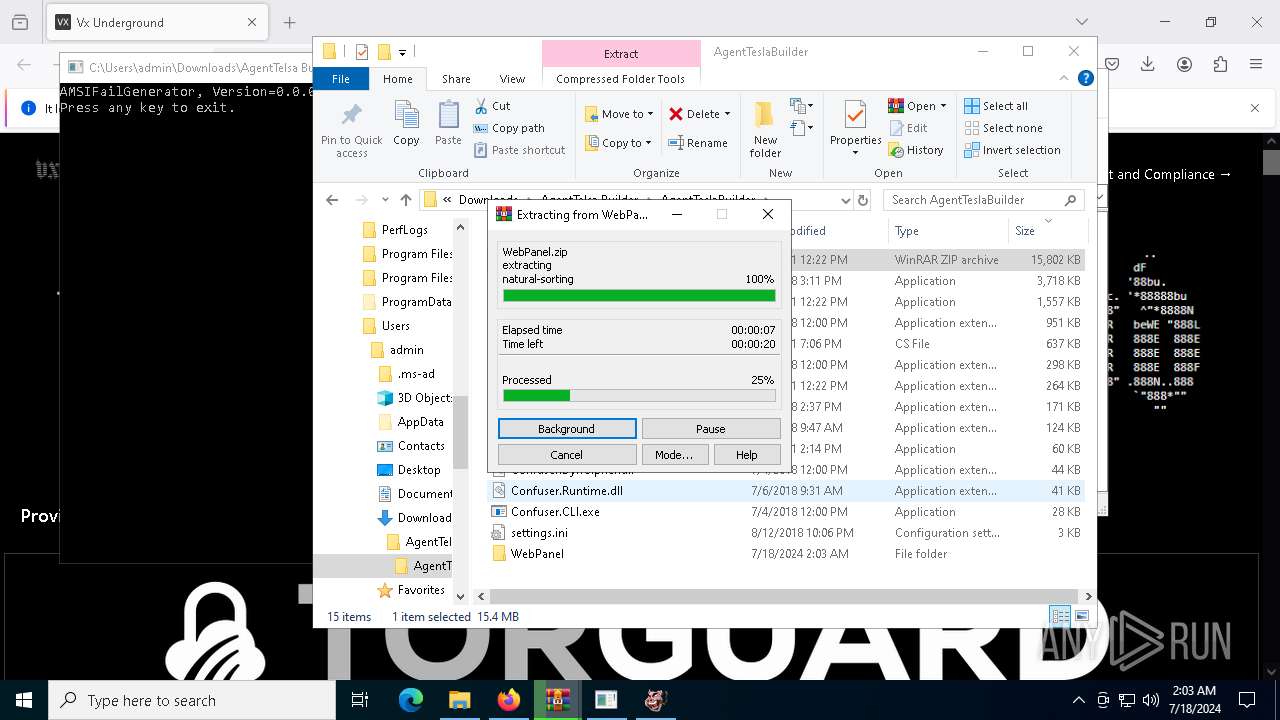
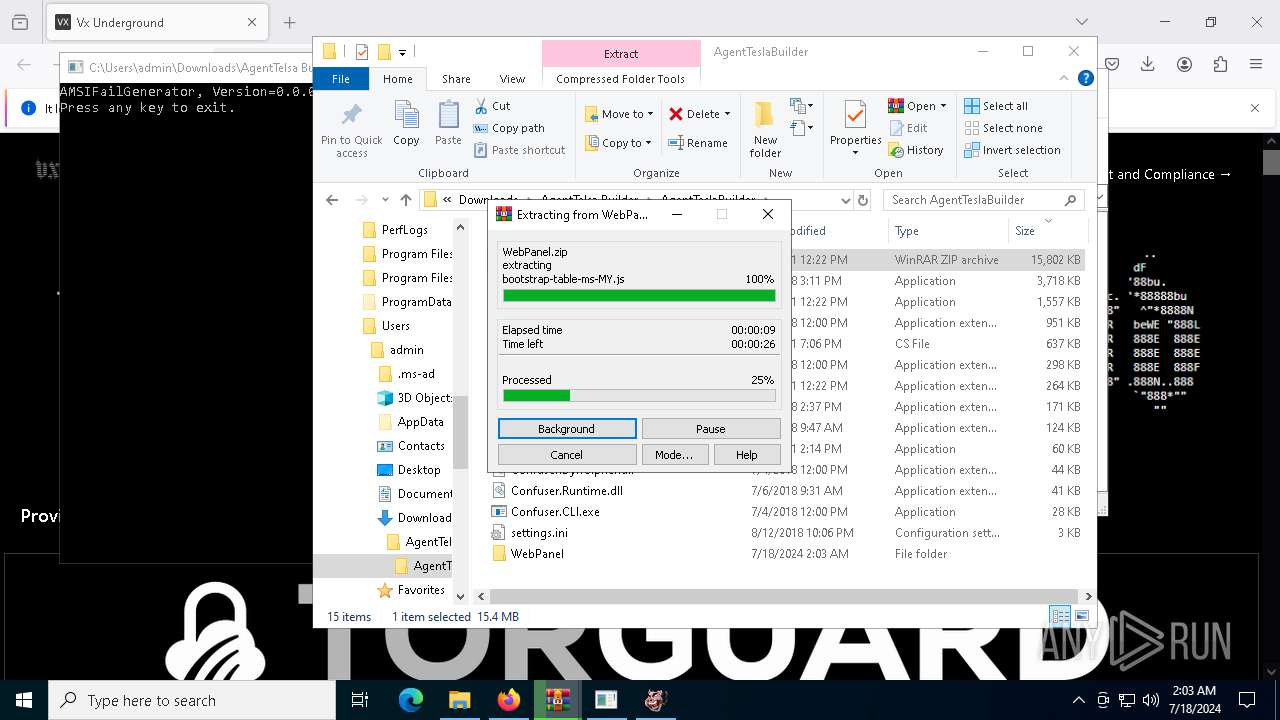
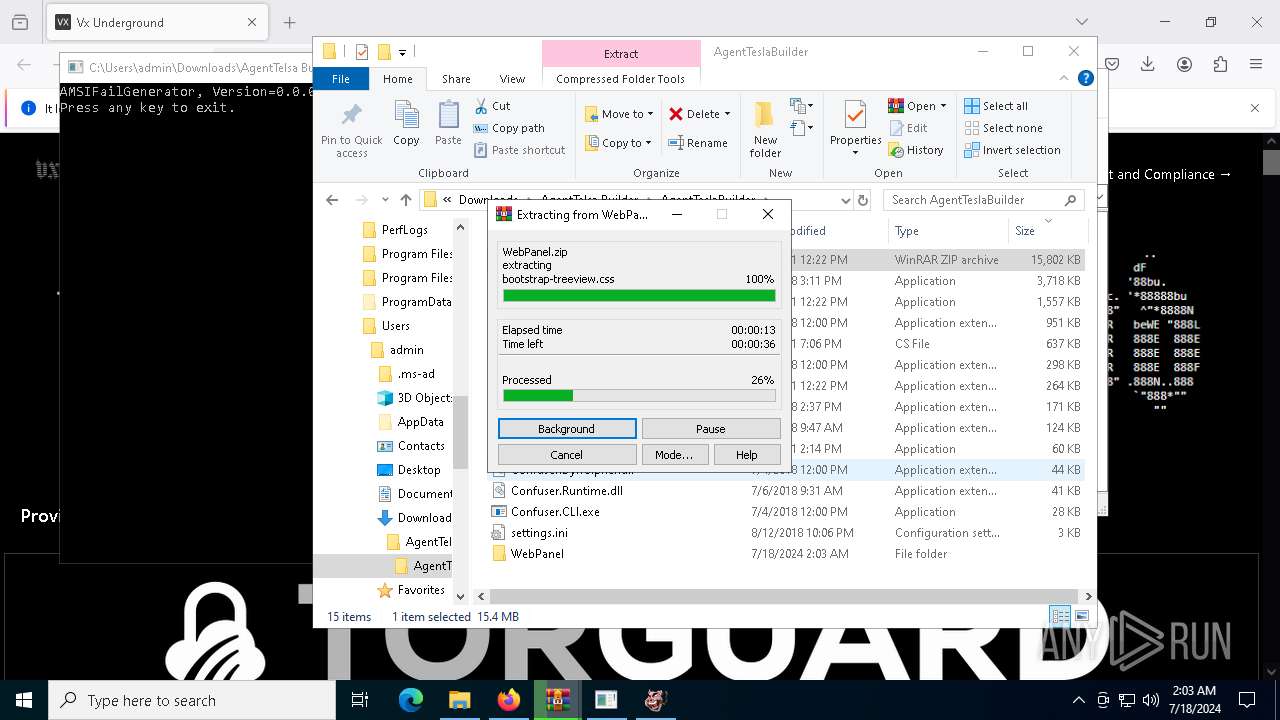
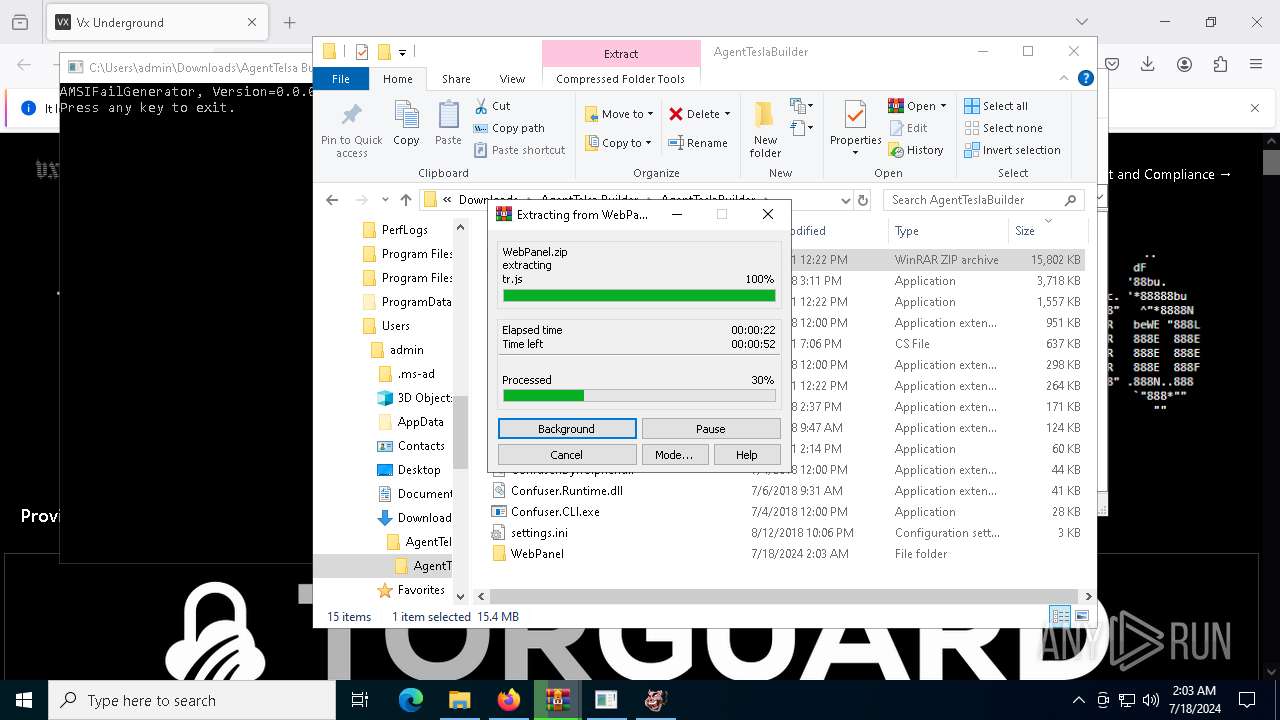
Manual execution by a user
- WinRAR.exe (PID: 6708)
- WinRAR.exe (PID: 7516)
- bye.exe (PID: 524)
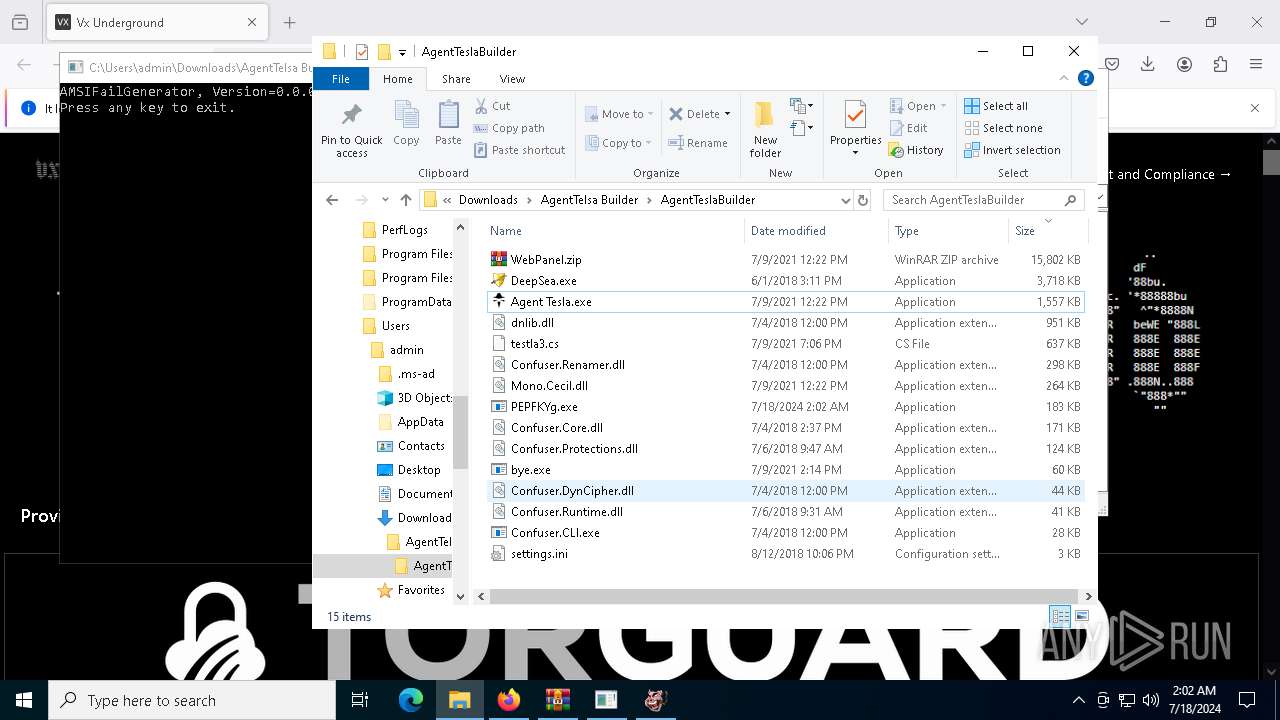
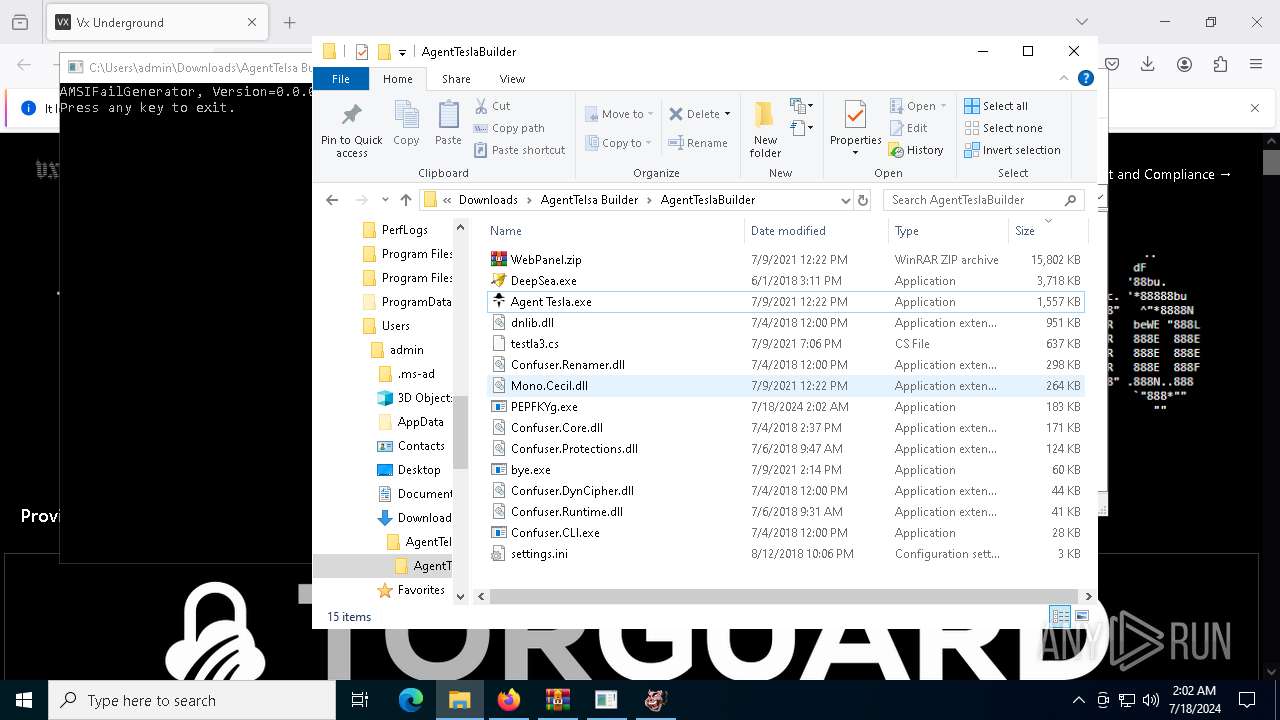
- DeepSea.exe (PID: 6248)
- Agent Tesla.exe (PID: 5332)
- Confuser.CLI.exe (PID: 7072)
- PEPFKYg.exe (PID: 5880)
- WinRAR.exe (PID: 6216)
Reads the software policy settings
- slui.exe (PID: 1700)
- slui.exe (PID: 6036)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7516)
- firefox.exe (PID: 884)
The process uses the downloaded file
- WinRAR.exe (PID: 6708)
- firefox.exe (PID: 884)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 7516)
- firefox.exe (PID: 884)
Checks supported languages
- bye.exe (PID: 524)
- Confuser.CLI.exe (PID: 7072)
- DeepSea.exe (PID: 6248)
- Agent Tesla.exe (PID: 5332)
- PEPFKYg.exe (PID: 5880)
Reads the computer name
- bye.exe (PID: 524)
- Confuser.CLI.exe (PID: 7072)
- DeepSea.exe (PID: 6248)
- Agent Tesla.exe (PID: 5332)
- PEPFKYg.exe (PID: 5880)
Reads the machine GUID from the registry
- bye.exe (PID: 524)
- Confuser.CLI.exe (PID: 7072)
- DeepSea.exe (PID: 6248)
- Agent Tesla.exe (PID: 5332)
- PEPFKYg.exe (PID: 5880)
Create files in a temporary directory
- bye.exe (PID: 524)
Reads Environment values
- bye.exe (PID: 524)
- PEPFKYg.exe (PID: 5880)
Gets data length (POWERSHELL)
- bye.exe (PID: 524)
Checks proxy server information
- slui.exe (PID: 6036)
- PEPFKYg.exe (PID: 5880)
Disables trace logs
- PEPFKYg.exe (PID: 5880)
Reads Windows Product ID
- PEPFKYg.exe (PID: 5880)
Creates files or folders in the user directory
- PEPFKYg.exe (PID: 5880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
163
Monitored processes
26
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 428 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1808 -parentBuildID 20240213221259 -prefsHandle 1736 -prefMapHandle 1728 -prefsLen 30537 -prefMapSize 244343 -appDir "C:\Program Files\Mozilla Firefox\browser" - {58c223ee-c00a-4adb-9cfb-3bccd7fa4695} 884 "\\.\pipe\gecko-crash-server-pipe.884" 2044e4c2110 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
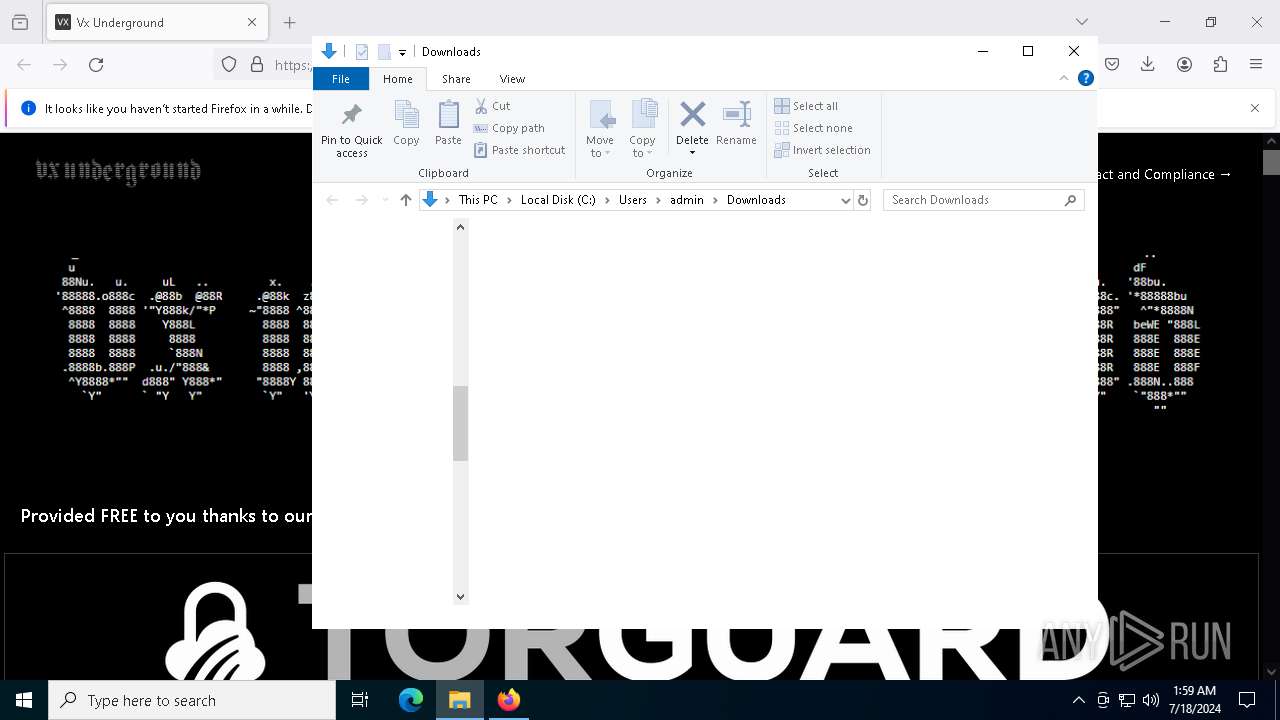
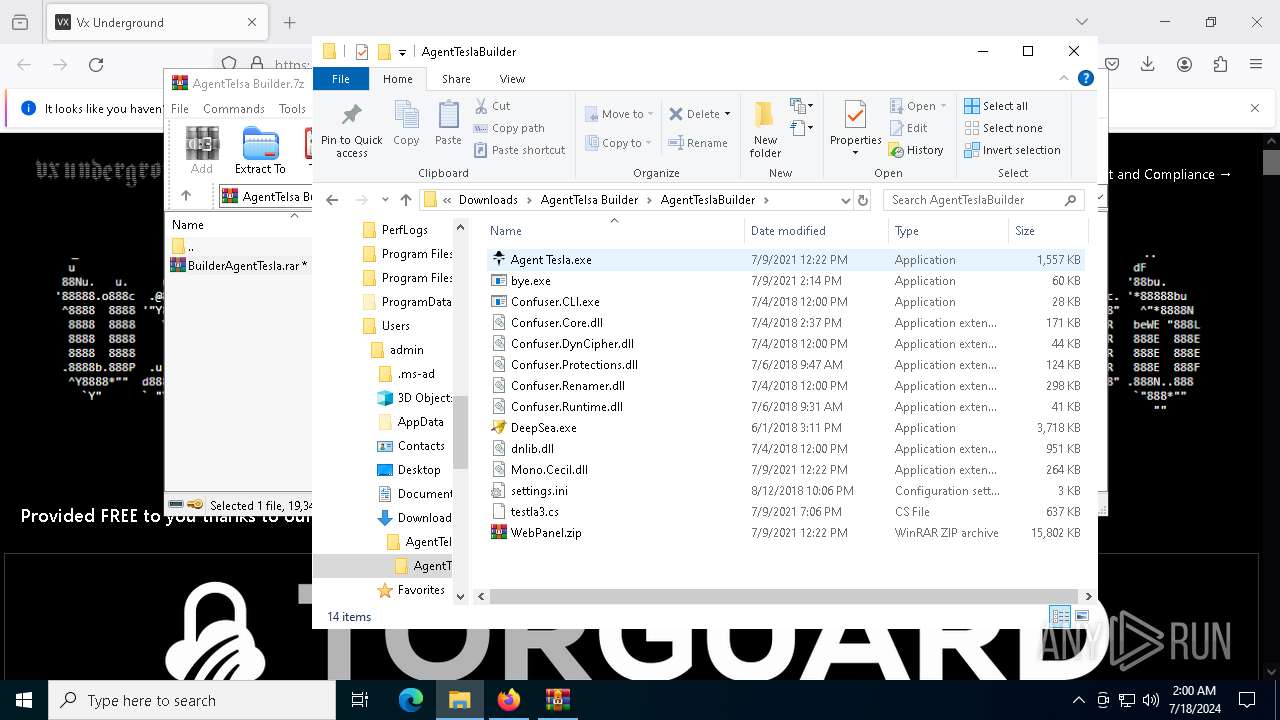
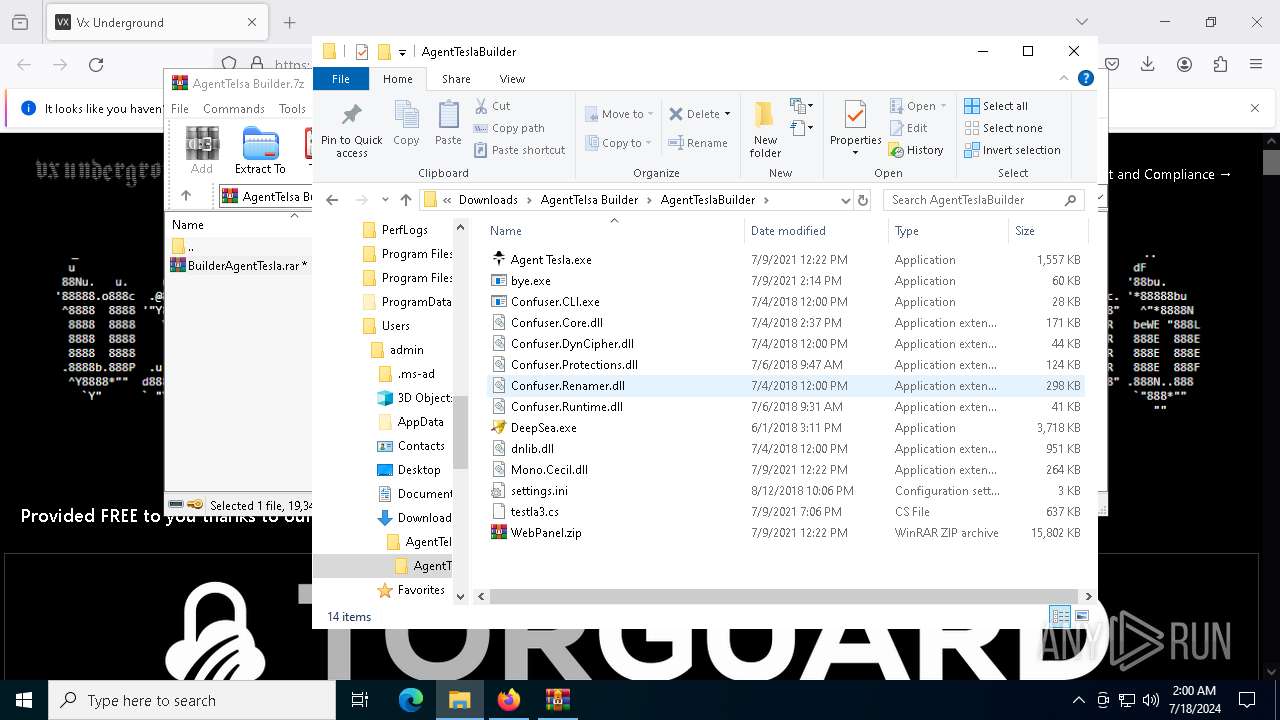
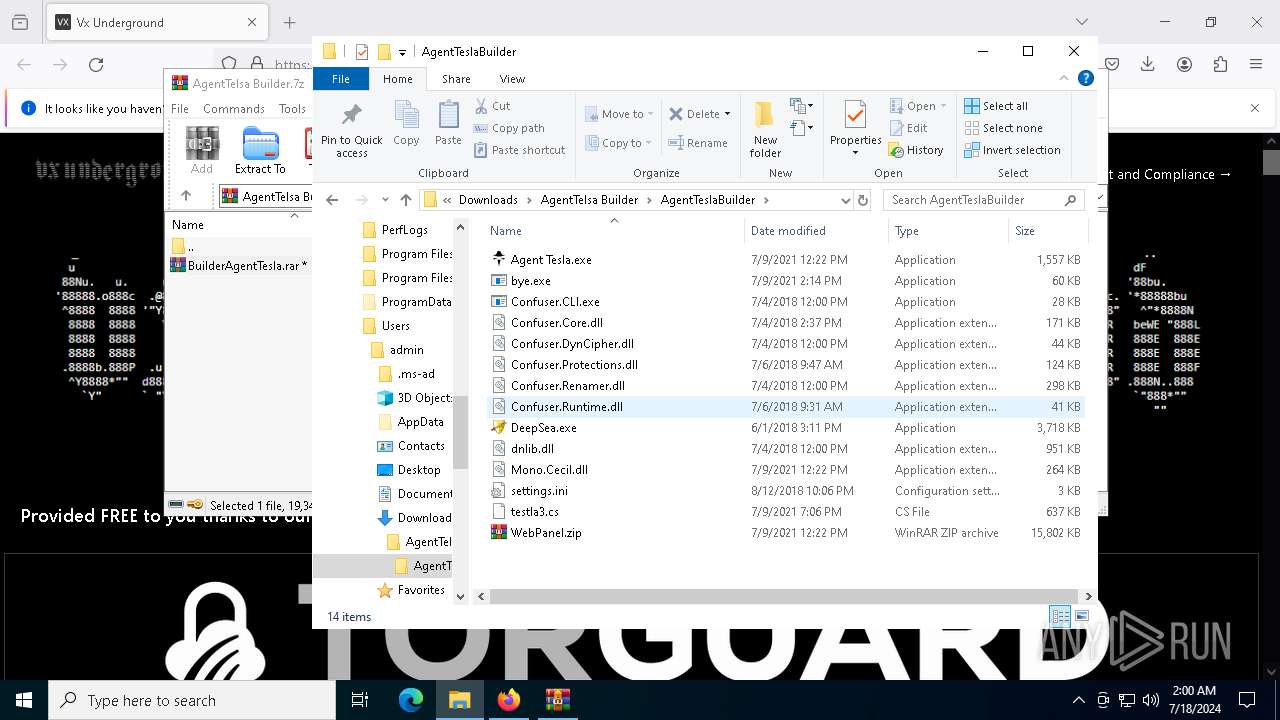
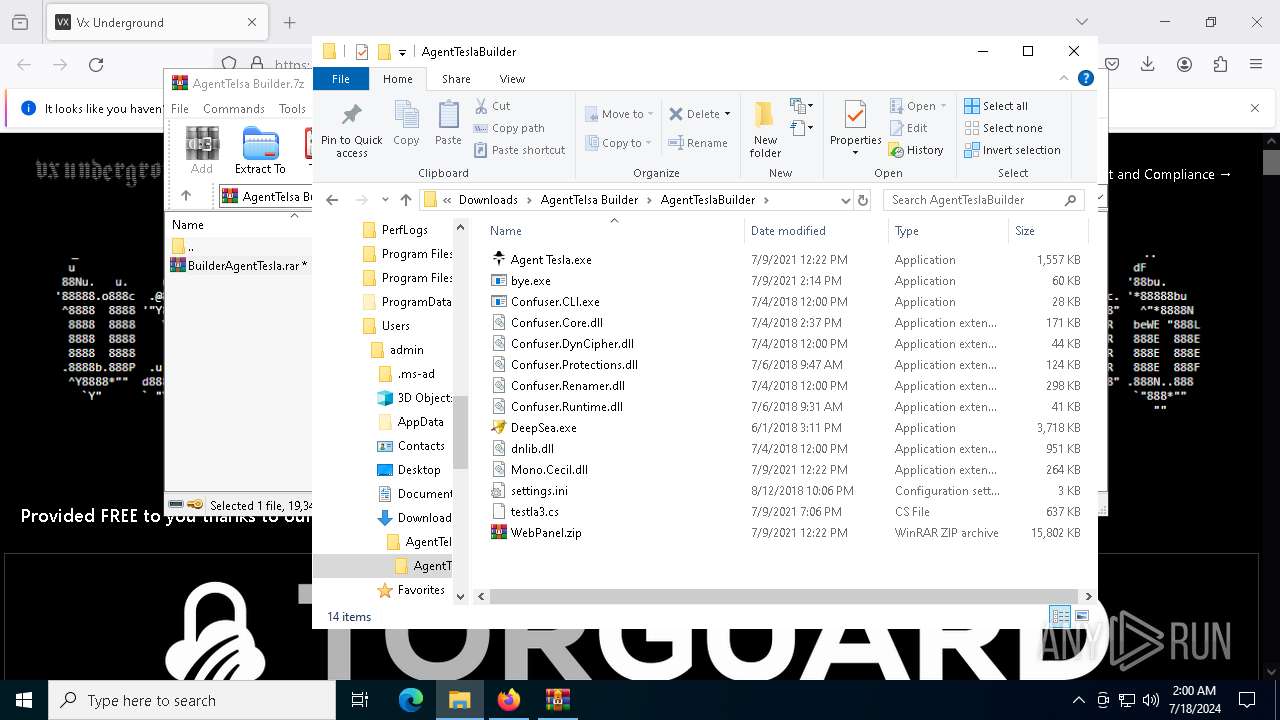
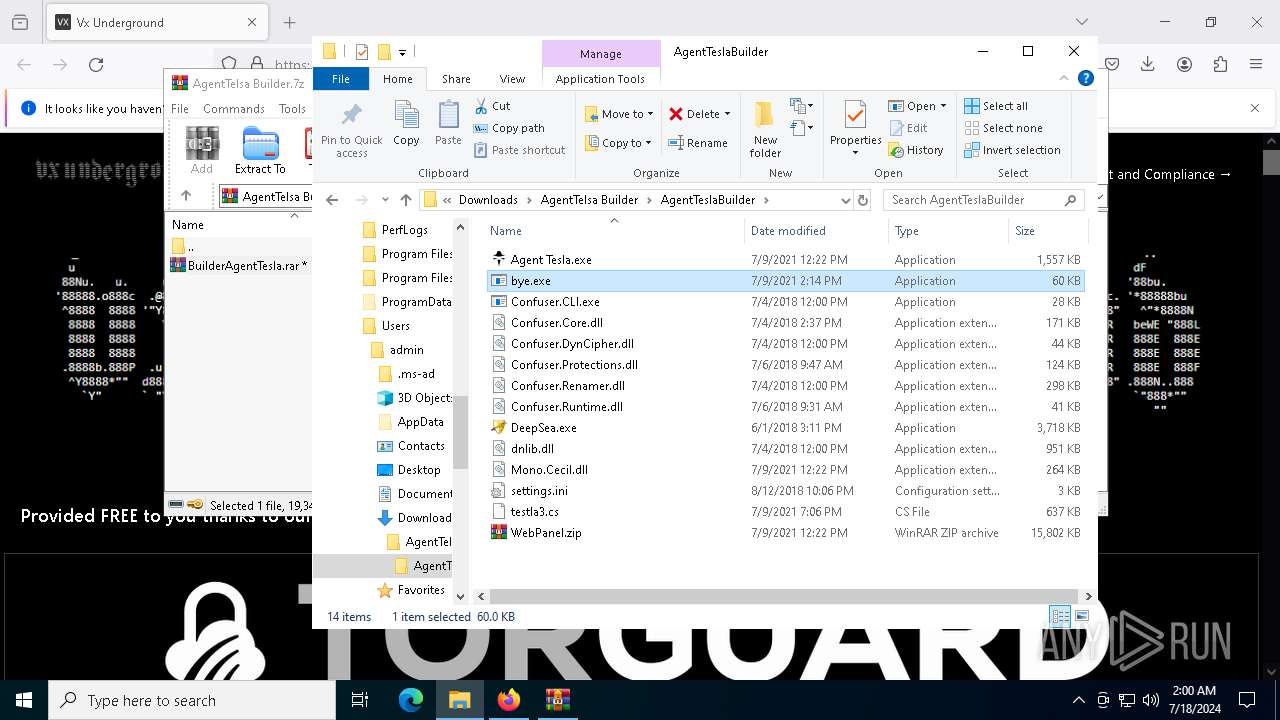
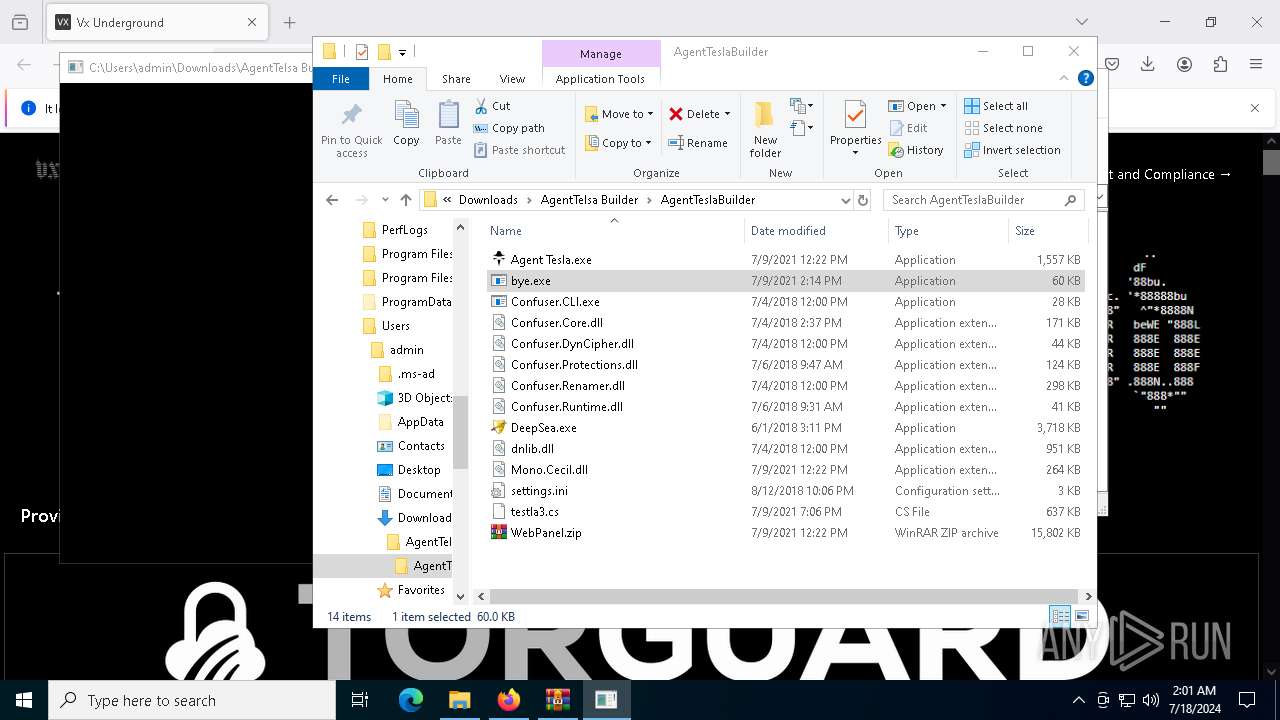
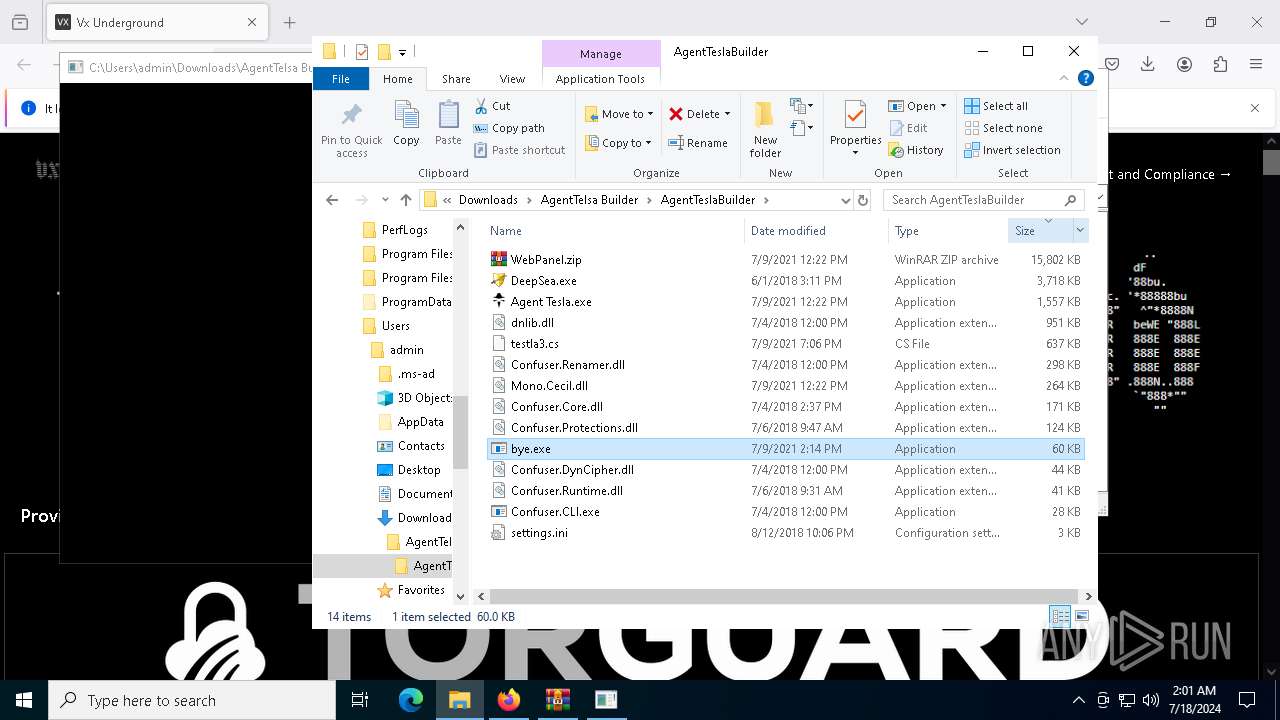
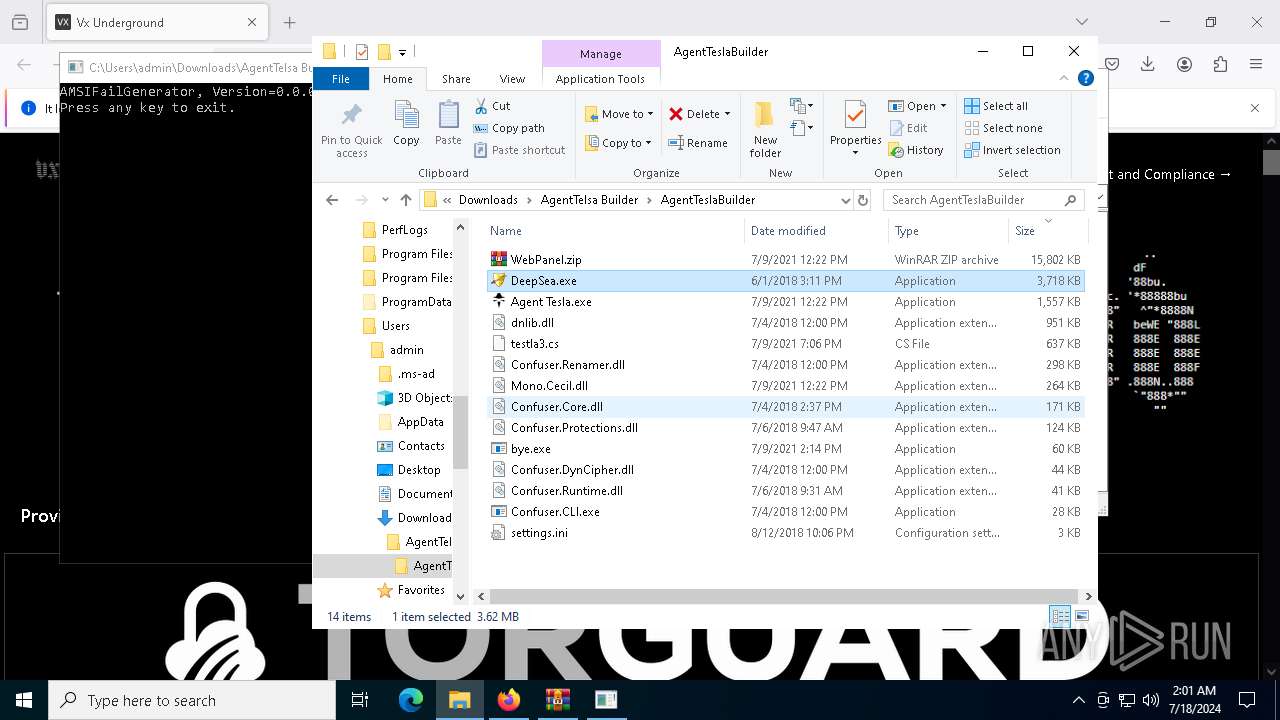
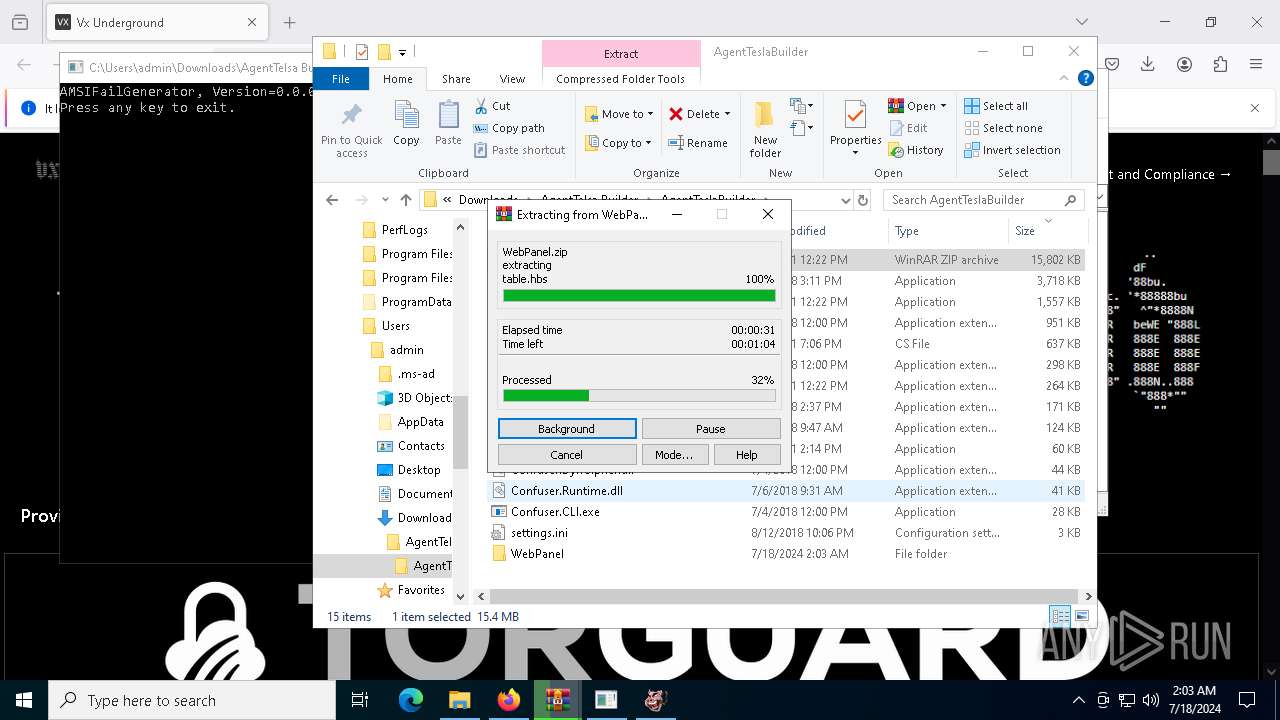
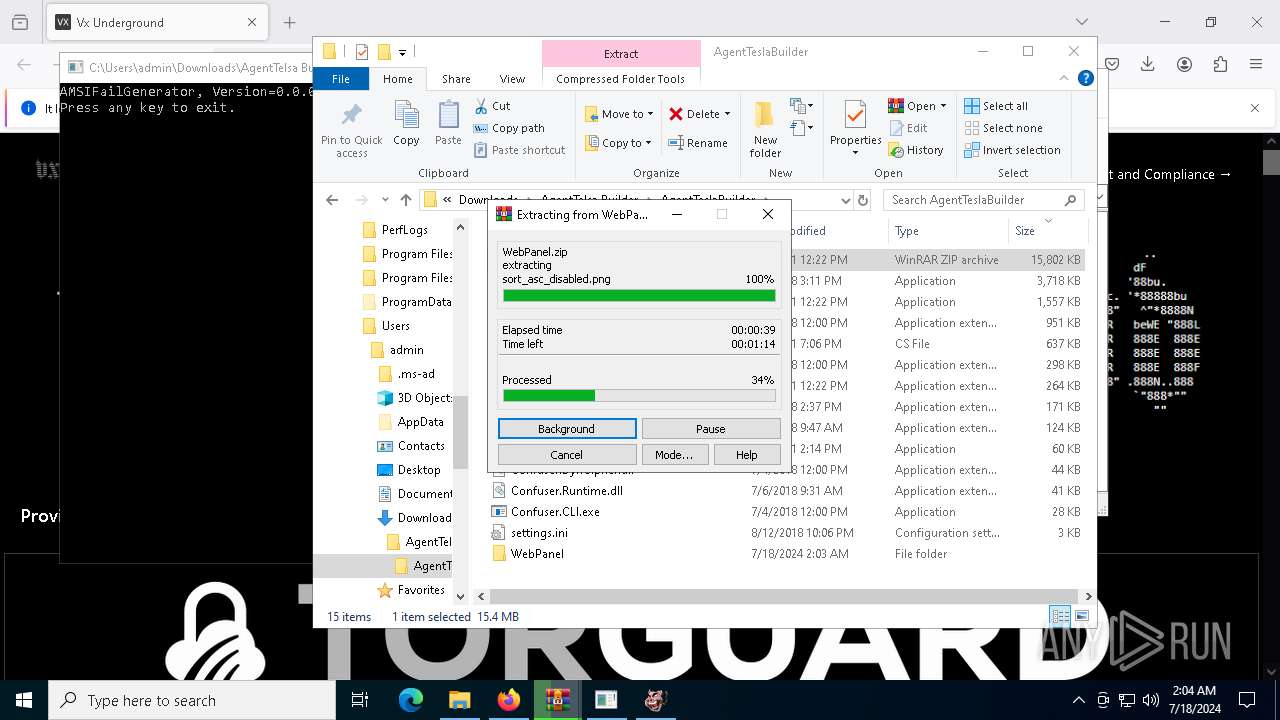
| 524 | "C:\Users\admin\Downloads\AgentTelsa Builder\AgentTeslaBuilder\bye.exe" | C:\Users\admin\Downloads\AgentTelsa Builder\AgentTeslaBuilder\bye.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://vx-underground.org/Archive/Builders | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1700 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3220 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2192 -parentBuildID 20240213221259 -prefsHandle 2184 -prefMapHandle 2180 -prefsLen 30537 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {b2f4a6ae-cd44-47e1-8b35-90fbb31d96c9} 884 "\\.\pipe\gecko-crash-server-pipe.884" 2044267f910 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3908 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4180 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://vx-underground.org/Archive/Builders" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
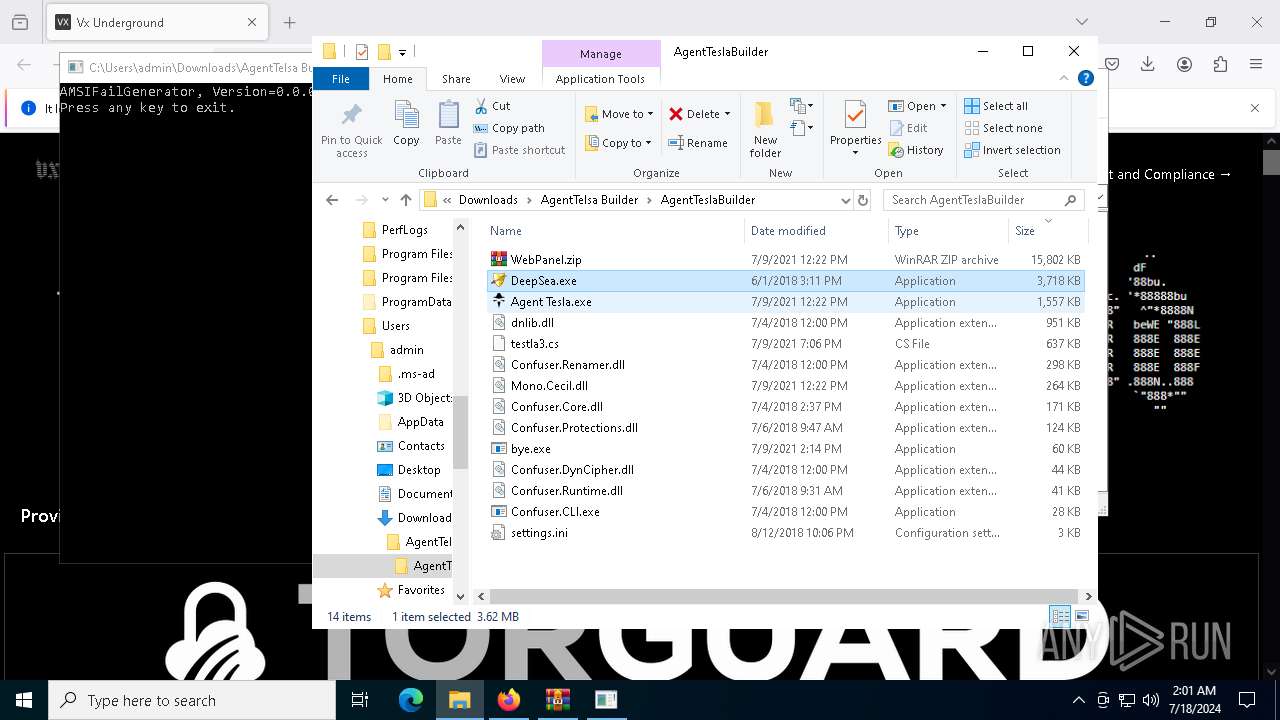
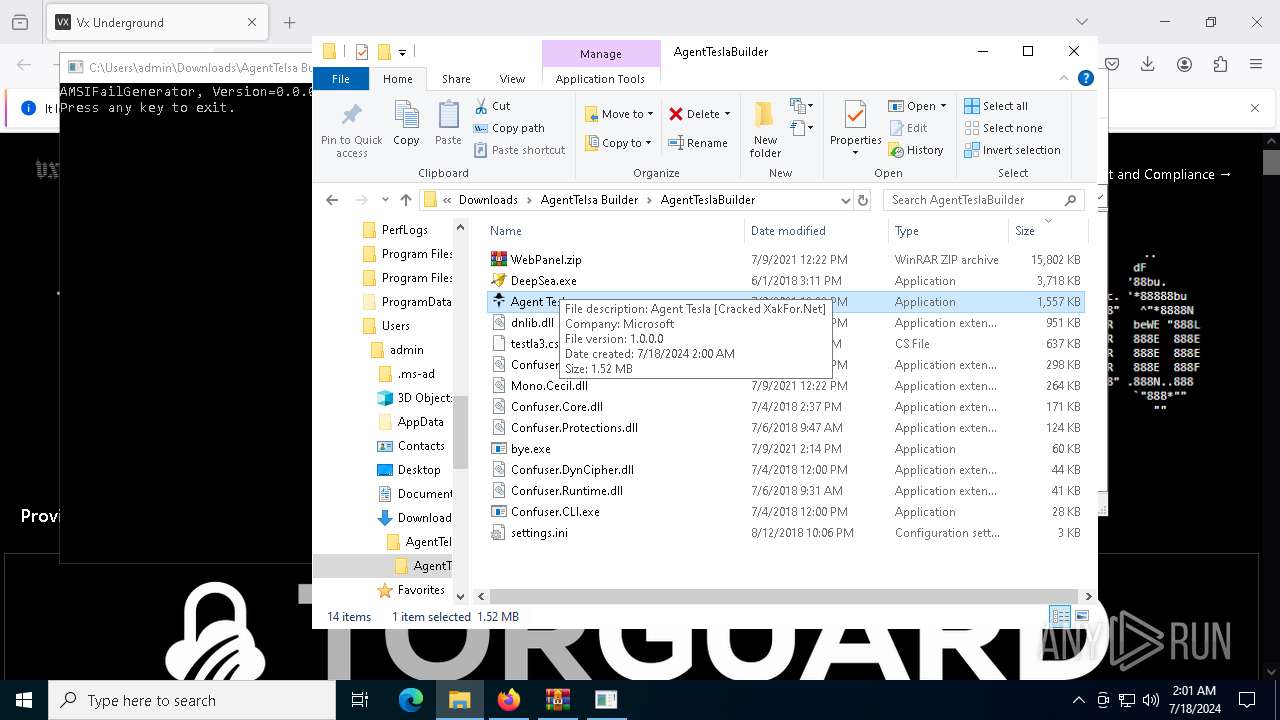
| 5332 | "C:\Users\admin\Downloads\AgentTelsa Builder\AgentTeslaBuilder\Agent Tesla.exe" | C:\Users\admin\Downloads\AgentTelsa Builder\AgentTeslaBuilder\Agent Tesla.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Agent Tesla [Cracked XakFor.Net] Version: 1.0.0.0 Modules
| |||||||||||||||
| 5532 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | bye.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5880 | "C:\Users\admin\Downloads\AgentTelsa Builder\AgentTeslaBuilder\PEPFKYg.exe" | C:\Users\admin\Downloads\AgentTelsa Builder\AgentTeslaBuilder\PEPFKYg.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
32 751
Read events
32 626
Write events
120
Delete events
5
Modification events
| (PID) Process: | (4180) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 8B226C9401000000 | |||
| (PID) Process: | (884) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 79316E9401000000 | |||
| (PID) Process: | (884) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 0 | |||
| (PID) Process: | (884) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 1 | |||
| (PID) Process: | (884) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Installer\308046B0AF4A39CB |
| Operation: | delete value | Name: | installer.taskbarpin.win10.enabled |
Value: | |||
| (PID) Process: | (884) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (884) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (884) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (884) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Enabled |
Value: 1 | |||
| (PID) Process: | (884) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
Executable files
18
Suspicious files
448
Text files
990
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 884 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 884 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 884 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 884 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 884 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 884 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:EFD1AD33304F24A642464966196CEDD1 | SHA256:D49ACE38B1702AE4FF4BF54A60B9312169DE2D664275F2103447B0C374CAD71D | |||
| 884 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:7A97B8DBC4F98D175F958C00F463A52A | SHA256:92074D2ED1AA1FD621287E35DB9EF1AE3DC04777EFAE5F09E7A3B4534C201548 | |||
| 884 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 884 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:7A97B8DBC4F98D175F958C00F463A52A | SHA256:92074D2ED1AA1FD621287E35DB9EF1AE3DC04777EFAE5F09E7A3B4534C201548 | |||
| 884 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
138
DNS requests
116
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5932 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6500 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
884 | firefox.exe | POST | 200 | 184.24.77.54:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
— | — | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4448 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
884 | firefox.exe | POST | 200 | 142.250.185.67:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
884 | firefox.exe | POST | 200 | 95.101.54.131:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6068 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1792 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
4448 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
4656 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
884 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
vx-underground.org |
| malicious |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
5880 | PEPFKYg.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
5880 | PEPFKYg.exe | Malware Command and Control Activity Detected | ET MALWARE AgentTesla Communicating with CnC Server |
5880 | PEPFKYg.exe | Malware Command and Control Activity Detected | ET MALWARE AgentTesla Communicating with CnC Server |
5880 | PEPFKYg.exe | Malware Command and Control Activity Detected | ET MALWARE AgentTesla Communicating with CnC Server |
5880 | PEPFKYg.exe | Malware Command and Control Activity Detected | ET MALWARE AgentTesla Communicating with CnC Server |
5880 | PEPFKYg.exe | Malware Command and Control Activity Detected | ET MALWARE AgentTesla Communicating with CnC Server |
7 ETPRO signatures available at the full report