| File name: | d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479 |
| Full analysis: | https://app.any.run/tasks/d95a9f05-5978-4e27-bdc3-30d672bf7f4b |
| Verdict: | Malicious activity |
| Threats: | RisePro, an information-stealing malware, targets a wide range of sensitive data, including credit cards, passwords, and cryptocurrency wallets. By compromising infected devices, RisePro can steal valuable information and potentially cause significant financial and personal losses for victims. |
| Analysis date: | September 03, 2025, 17:36:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | CC800AEE4D8F6B42601BE444E284354E |
| SHA1: | EF00C39A62B2B5CC4CCD2FEA63C0DFA8AADB85C2 |
| SHA256: | D0295C334677DA7CA28746B3FEFF2E82320314322D99AF837090C4E87B362479 |
| SSDEEP: | 98304:CqSJyKWf+qKVjxijewmHLIg65vtQIzvbaJdEx6Q55d6ZLax173mpMz2yruwnd/+7:zVLBo |
MALICIOUS
Executing a file with an untrusted certificate
- d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe (PID: 4948)
Generic malware mutex has been detected
- d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe (PID: 4948)
GENERIC has been found (auto)
- d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe (PID: 4948)
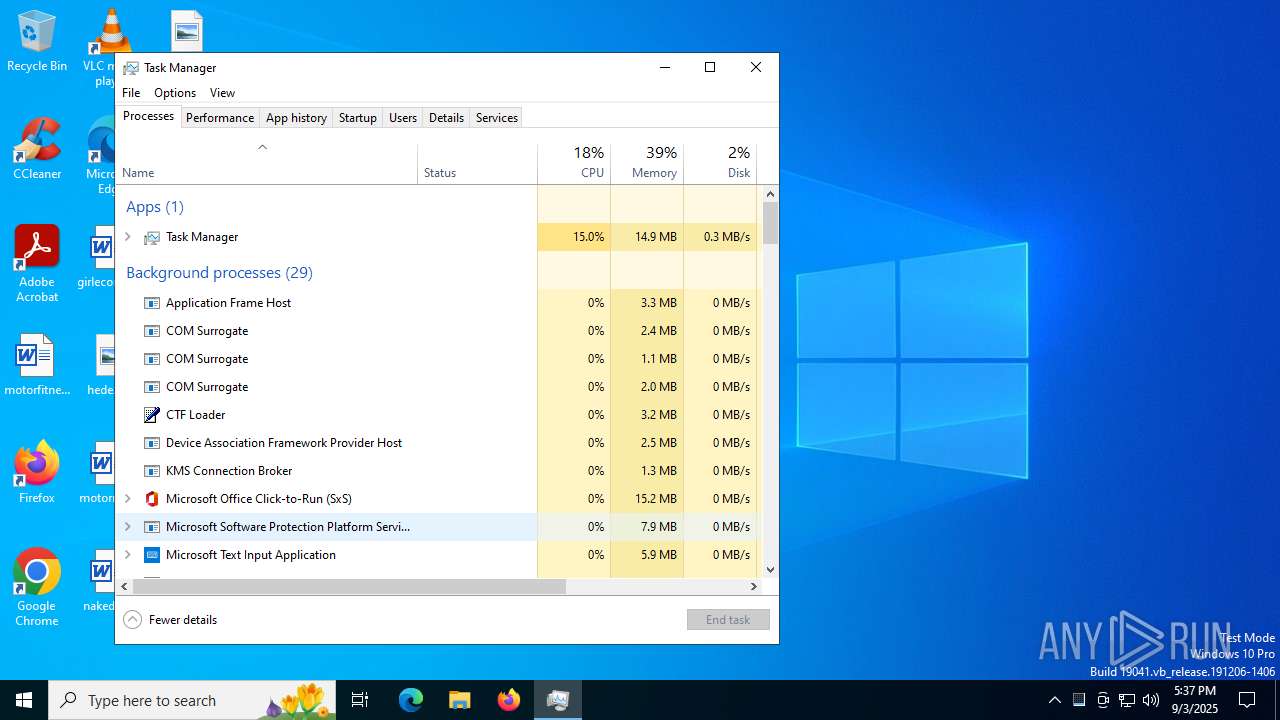
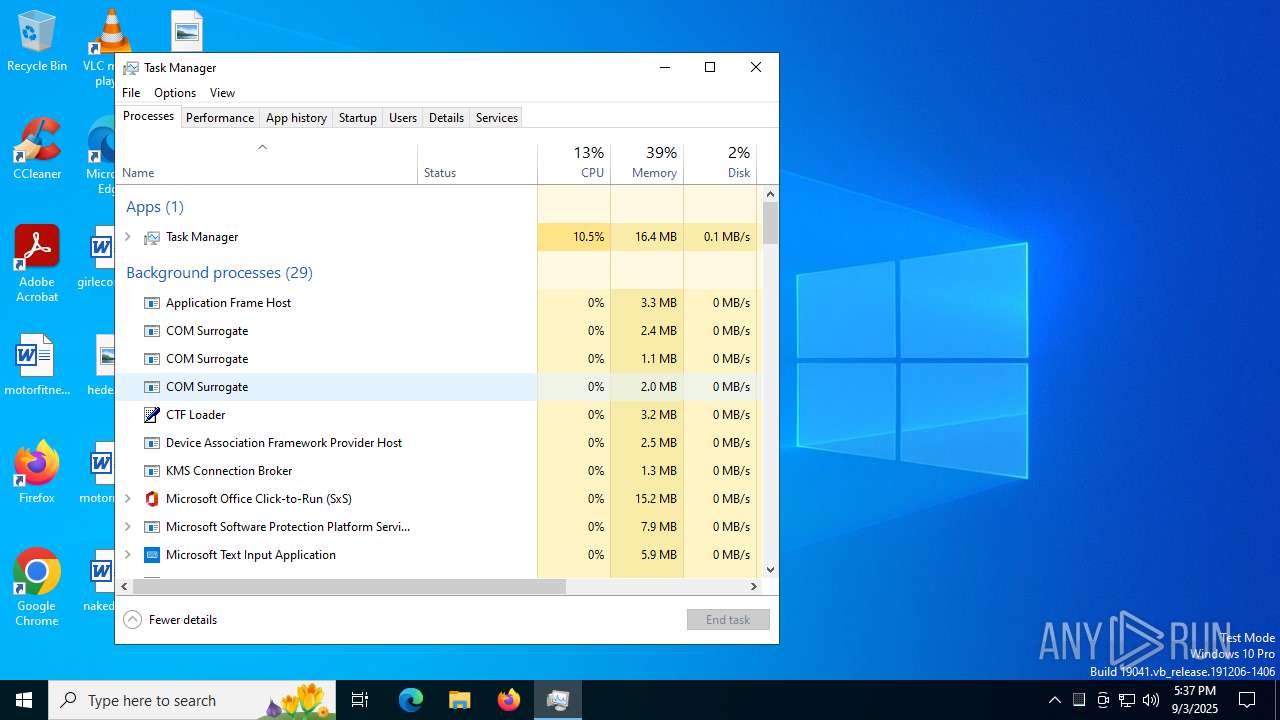
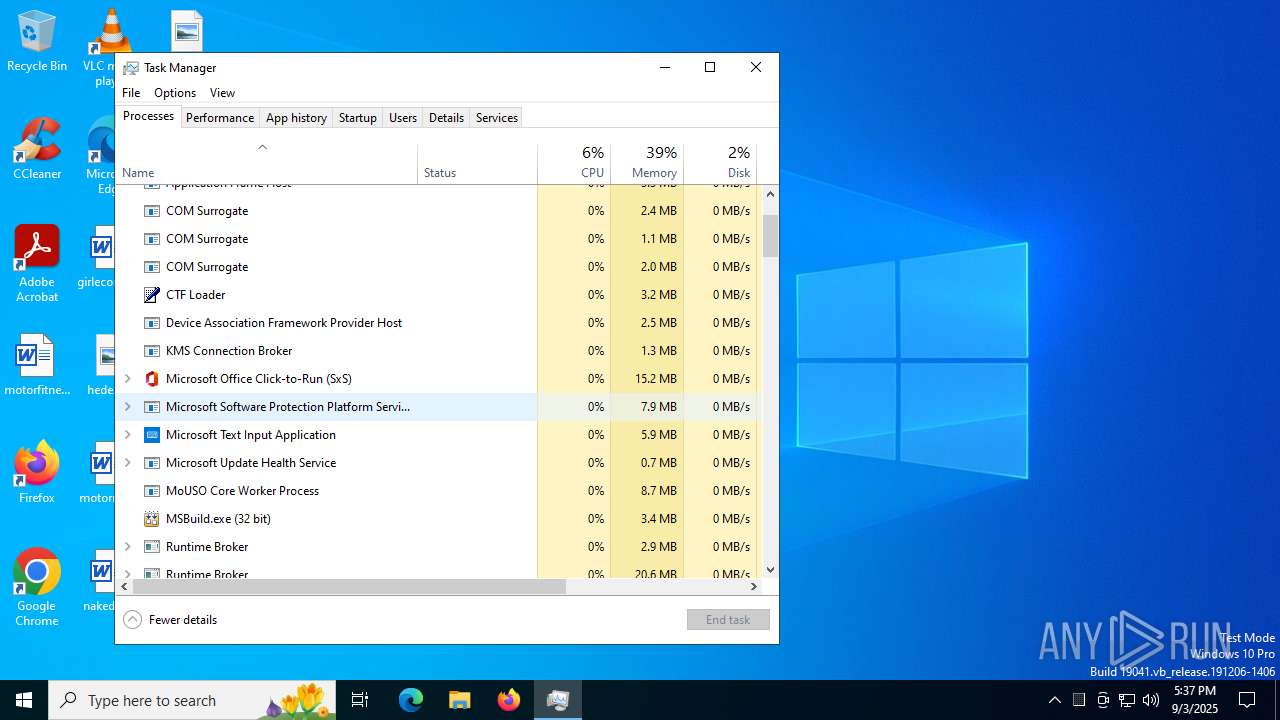
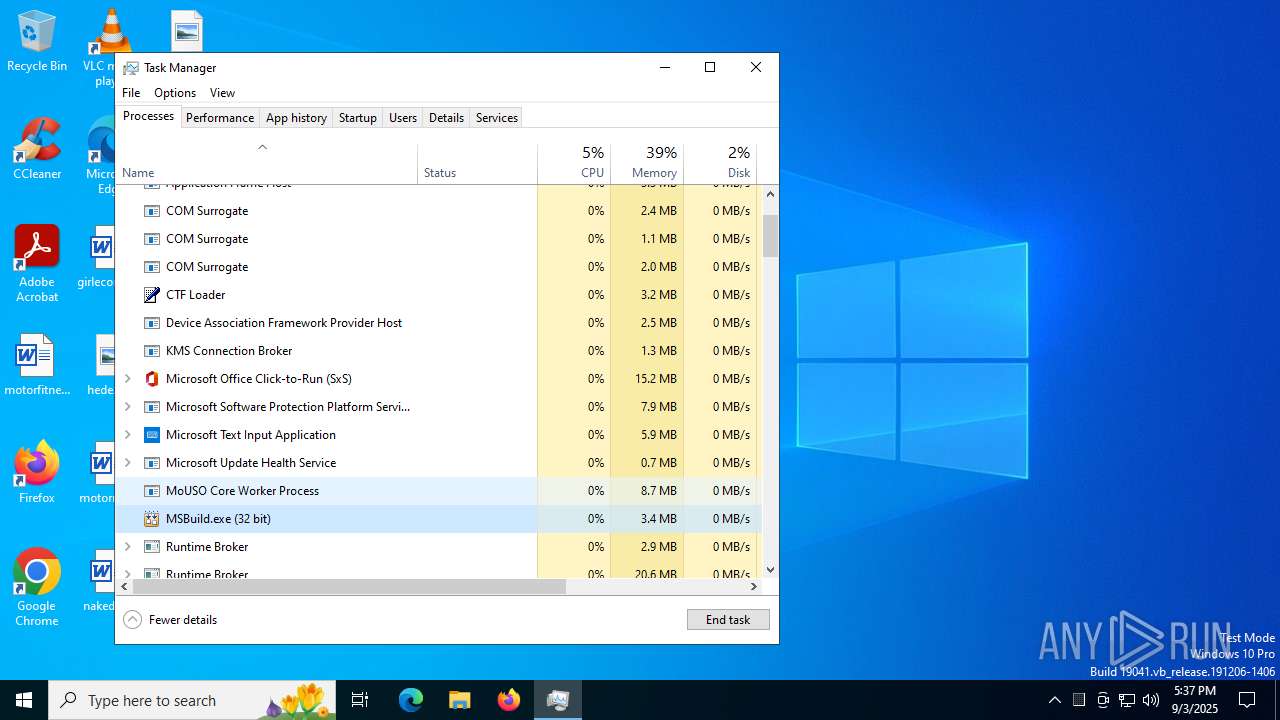
RISEPRO has been detected (YARA)
- MSBuild.exe (PID: 7004)
SUSPICIOUS
Executable content was dropped or overwritten
- d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe (PID: 4948)
Connects to unusual port
- MSBuild.exe (PID: 7004)
INFO
Reads the computer name
- d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe (PID: 4948)
- MSBuild.exe (PID: 7004)
Checks supported languages
- d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe (PID: 4948)
- MSBuild.exe (PID: 7004)
Reads the machine GUID from the registry
- d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe (PID: 4948)
.NET Reactor protector has been detected
- d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe (PID: 4948)
Create files in a temporary directory
- d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe (PID: 4948)
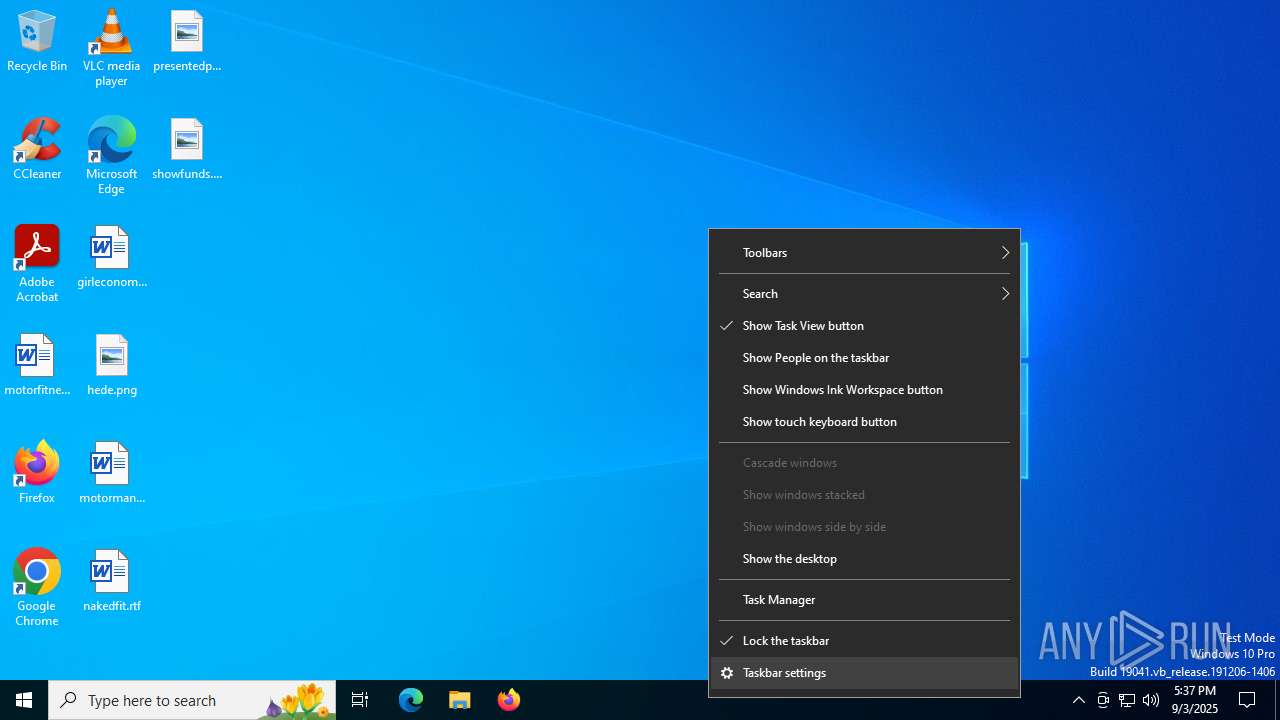
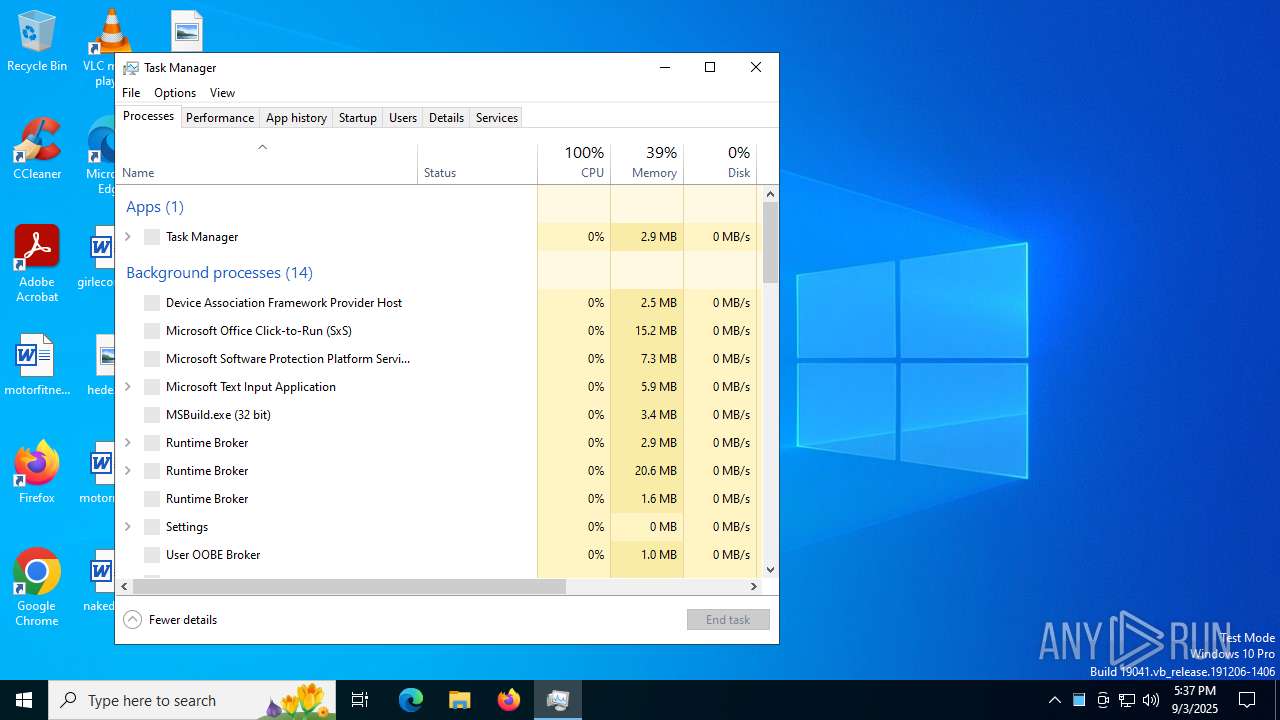
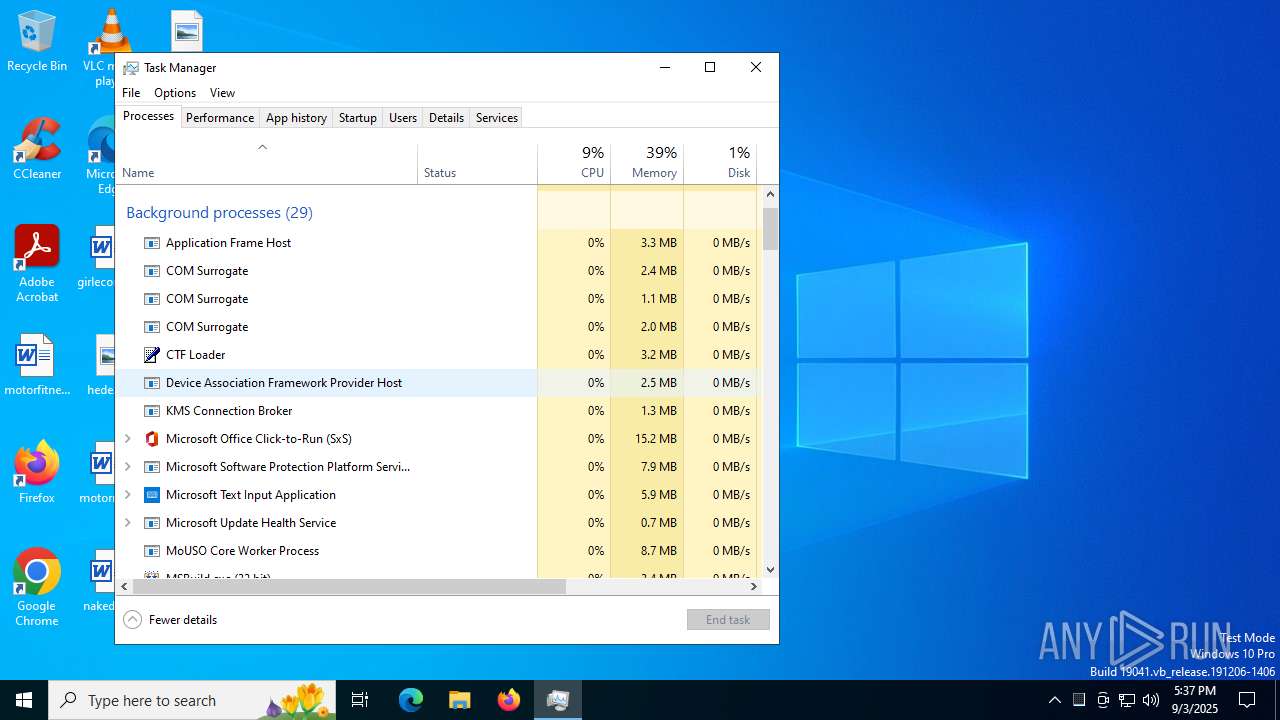
Manual execution by a user
- Taskmgr.exe (PID: 2716)
- Taskmgr.exe (PID: 5372)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 2716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RisePro
(PID) Process(7004) MSBuild.exe
C2 (1)45.15.156.9:50500
Strings (52)\FileZilla
\TotalCommander
C:\program files\steam
\ICQ\0001
\Growtopia\save.dat
\.lunarclient\settings\games\accounts.txt
VaultOpenVault
\Skype
C:\program files (x86)\steam
\Games
\Messengers
\Element\Local Storage
APPDATA
\databases
\Steam
VaultCloseVault
\GHISLER\wcx_ftp.ini
\wcx_ftp.ini
\.minecraft\launcher_accounts.json
\Pidgin
\TLauncher
\.purple
\OpenVPN Connect\profiles
\save.dat
\config.json
\Microsoft\Skype for Desktop\Local Storage
\Signal
\.minecraft\launcher_msa_credentials.bin
\accounts.json
\config
\.minecraft\launcher_profiles.json
|5{`f
\.feather\accounts.json
\Session Storage
VaultGetItem
\FeatherClient
\Battle.net
\tlauncher_profiles.json
logins
\Minecraft
\accounts.xml
\ey_tokens.txt
\launcher_accounts.json
\OpenVPN Connect
\Growtopia
\LunarClient
\launcher_msa_credentials.bin
\accounts.txt
WSASend
\Local Storage
\launcher_profiles.json
\Element
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2080:10:17 21:04:38+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 4638208 |
| InitializedDataSize: | 84992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x46e43e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.4.0.1 |
| ProductVersionNumber: | 7.4.0.1 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Bandisoft.com |
| FileDescription: | Bandizip Updater |
| FileVersion: | 7.4.0.1 |
| InternalName: | Bandizip Updater |
| LegalCopyright: | Copyright(C) 2008-2020 Bandisoft.com. All rights reserved. |
| OriginalFileName: | Updater.exe |
| ProductName: | Bandizip Updater |
| ProductVersion: | 7.4.0.1 |
Total processes
140
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1612 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2620 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MsBuild.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2716 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4948 | "C:\Users\admin\AppData\Local\Temp\d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe" | C:\Users\admin\AppData\Local\Temp\d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe | explorer.exe | ||||||||||||
User: admin Company: Bandisoft.com Integrity Level: MEDIUM Description: Bandizip Updater Exit code: 0 Version: 7.4.0.1 Modules
| |||||||||||||||
| 5372 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7004 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MsBuild.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
RisePro(PID) Process(7004) MSBuild.exe C2 (1)45.15.156.9:50500 Strings (52)\FileZilla \TotalCommander C:\program files\steam \ICQ\0001 \Growtopia\save.dat \.lunarclient\settings\games\accounts.txt VaultOpenVault \Skype C:\program files (x86)\steam \Games \Messengers \Element\Local Storage APPDATA \databases \Steam VaultCloseVault \GHISLER\wcx_ftp.ini \wcx_ftp.ini \.minecraft\launcher_accounts.json \Pidgin \TLauncher \.purple \OpenVPN Connect\profiles \save.dat \config.json \Microsoft\Skype for Desktop\Local Storage \Signal \.minecraft\launcher_msa_credentials.bin \accounts.json \config \.minecraft\launcher_profiles.json |5{`f \.feather\accounts.json \Session Storage VaultGetItem \FeatherClient \Battle.net \tlauncher_profiles.json logins \Minecraft \accounts.xml \ey_tokens.txt \launcher_accounts.json \OpenVPN Connect \Growtopia \LunarClient \launcher_msa_credentials.bin \accounts.txt WSASend \Local Storage \launcher_profiles.json \Element | |||||||||||||||
Total events
4 883
Read events
4 881
Write events
1
Delete events
1
Modification events
| (PID) Process: | (2716) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (2716) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100016B00000034000000130300008C020000E80300000000000000000000000000000F000000010000000000000058AAEE82F77F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AAEE82F77F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AAEE82F77F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AAEE82F77F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AAEE82F77F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000ABEE82F77F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028ABEE82F77F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050ABEE82F77F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AAEE82F77F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070ABEE82F77F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088ABEE82F77F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8ABEE82F77F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8ABEE82F77F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0ABEE82F77F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010ACEE82F77F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AAEE82F77F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AAEE82F77F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AAEE82F77F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040ACEE82F77F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068ACEE82F77F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090ACEE82F77F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8ACEE82F77F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8ACEE82F77F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8ACEE82F77F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028ABEE82F77F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AAEE82F77F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020ADEE82F77F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040ADEE82F77F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068ADEE82F77F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AAEE82F77F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050ABEE82F77F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AAEE82F77F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070ABEE82F77F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088ABEE82F77F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8ABEE82F77F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8ABEE82F77F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AAEE82F77F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088ADEE82F77F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8ADEE82F77F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0ADEE82F77F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AEEE82F77F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AEEE82F77F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AEEE82F77F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AEEE82F77F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2716 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 4948 | d0295c334677da7ca28746b3feff2e82320314322d99af837090c4e87b362479.exe | C:\Users\admin\AppData\Local\Temp\Protect544cd51a.dll | executable | |
MD5:544CD51A596619B78E9B54B70088307D | SHA256:DFCE2D4D06DE6452998B3C5B2DC33EAA6DB2BD37810D04E3D02DC931887CFDDD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
107
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.18.244.223:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | FR | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 72.246.158.76:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
4168 | svchost.exe | GET | 200 | 23.203.176.221:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
2312 | SIHClient.exe | GET | 200 | 72.246.158.76:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | US | binary | 419 b | whitelisted |
2312 | SIHClient.exe | GET | 200 | 72.246.158.76:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | US | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1040 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.18.244.223:80 | crl.microsoft.com | Akamai International B.V. | FR | whitelisted |
1268 | svchost.exe | 72.246.158.76:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4168 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4168 | svchost.exe | 23.203.176.221:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |