| File name: | Dogusign Reader 1.26g.msi |
| Full analysis: | https://app.any.run/tasks/08856813-d77f-4121-b9de-15fdad5e34bf |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | January 10, 2025, 20:55:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Palsgravine, Author: Chaplainry Strudel, Keywords: Installer, Comments: This installer database contains the logic and data required to install Palsgravine., Template: Intel;1033, Revision Number: {823F9B91-5B1C-4363-89EB-5E534851E2CD}, Create Time/Date: Fri Jan 10 04:07:28 2025, Last Saved Time/Date: Fri Jan 10 04:07:28 2025, Number of Pages: 500, Number of Words: 10, Name of Creating Application: WiX Toolset (4.0.0.0), Security: 2 |
| MD5: | 35F774E65E57F419FFF8D8F74945EA51 |
| SHA1: | C3E1D2D50A9BBCA445576E0D71C6984CC1DC60BB |
| SHA256: | D00A3E22E53210ACBD5C3E39B85332E3D47C8EC001D2BBF7A13ABB07427BBBA2 |
| SSDEEP: | 98304:u6Q1TY/CdEG26wjPcEU9Z3eWXCiifD9sjT9abLW1WwqsZydr4oor437Ae5AKqSK3:UK/+bHYenoRPGg |
MALICIOUS
LUMMA mutex has been found
- explorer.exe (PID: 6468)
Actions looks like stealing of personal data
- explorer.exe (PID: 6468)
Connects to the CnC server
- explorer.exe (PID: 6980)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6764)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6708)
Executable content was dropped or overwritten
- RttHlp.exe (PID: 1512)
- RttHlp.exe (PID: 3680)
Starts itself from another location
- RttHlp.exe (PID: 1512)
- RttHlp.exe (PID: 3680)
Starts CMD.EXE for commands execution
- RttHlp.exe (PID: 3680)
- RttHlp.exe (PID: 5640)
Connects to the server without a host name
- explorer.exe (PID: 6980)
Connects to unusual port
- explorer.exe (PID: 6980)
INFO
The sample compiled with english language support
- msiexec.exe (PID: 6516)
- msiexec.exe (PID: 6708)
- RttHlp.exe (PID: 1512)
- RttHlp.exe (PID: 3680)
Checks supported languages
- msiexec.exe (PID: 6708)
- RttHlp.exe (PID: 1512)
- RttHlp.exe (PID: 3680)
- RttHlp.exe (PID: 5640)
Manages system restore points
- SrTasks.exe (PID: 4708)
Reads the computer name
- msiexec.exe (PID: 6708)
- RttHlp.exe (PID: 1512)
- RttHlp.exe (PID: 3680)
- RttHlp.exe (PID: 5640)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6708)
Creates files or folders in the user directory
- msiexec.exe (PID: 6708)
- RttHlp.exe (PID: 1512)
- RttHlp.exe (PID: 3680)
- explorer.exe (PID: 6980)
Creates a software uninstall entry
- msiexec.exe (PID: 6708)
Reads the software policy settings
- explorer.exe (PID: 6468)
Create files in a temporary directory
- RttHlp.exe (PID: 5640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
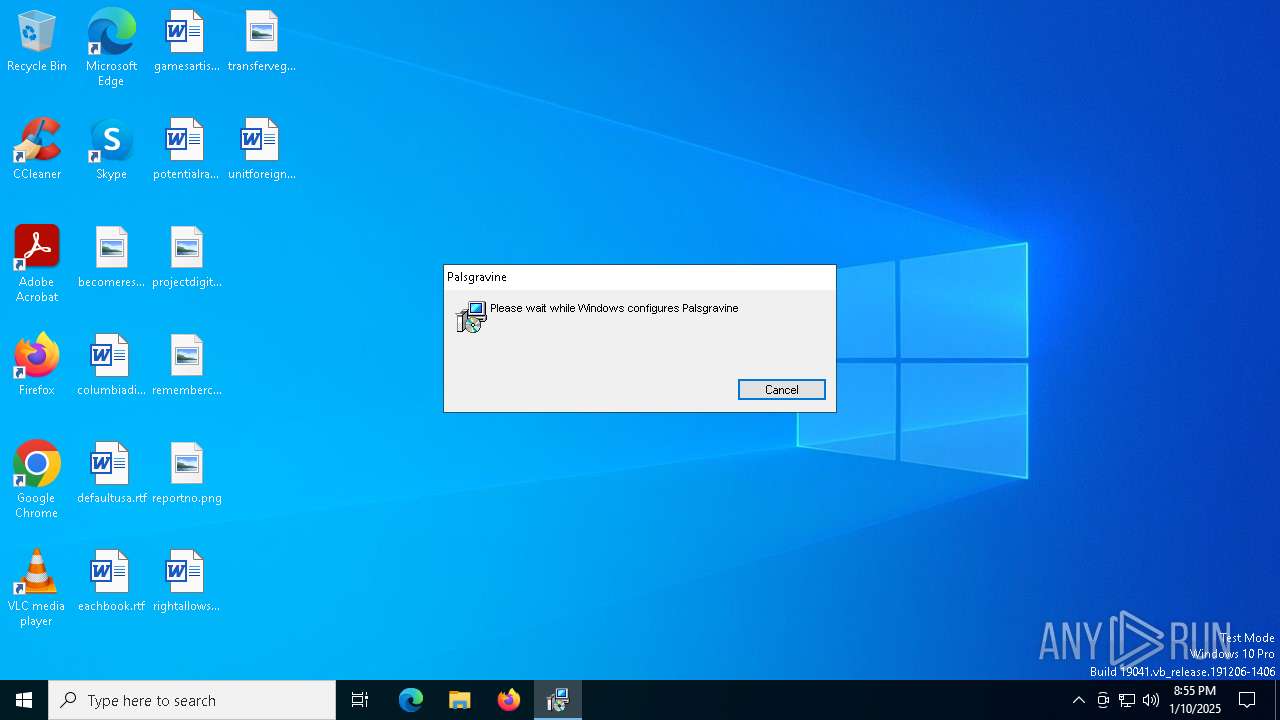
| Subject: | Palsgravine |
| Author: | Chaplainry Strudel |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Palsgravine. |
| Template: | Intel;1033 |
| RevisionNumber: | {823F9B91-5B1C-4363-89EB-5E534851E2CD} |
| CreateDate: | 2025:01:10 04:07:28 |
| ModifyDate: | 2025:01:10 04:07:28 |
| Pages: | 500 |
| Words: | 10 |
| Software: | WiX Toolset (4.0.0.0) |
| Security: | Read-only recommended |
Total processes
144
Monitored processes
14
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | RttHlp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\Users\admin\AppData\Local\Yarrow\RttHlp.exe" | C:\Users\admin\AppData\Local\Yarrow\RttHlp.exe | msiexec.exe | ||||||||||||
User: admin Company: IObit Integrity Level: MEDIUM Description: IObit RttHlp Exit code: 0 Version: 11.0.0.0 Modules
| |||||||||||||||
| 3140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3680 | C:\Users\admin\AppData\Roaming\configRemote_PZ4\RttHlp.exe | C:\Users\admin\AppData\Roaming\configRemote_PZ4\RttHlp.exe | RttHlp.exe | ||||||||||||
User: admin Company: IObit Integrity Level: MEDIUM Description: IObit RttHlp Exit code: 1 Version: 11.0.0.0 Modules
| |||||||||||||||
| 4540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4708 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5256 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | RttHlp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5640 | C:\Users\admin\AppData\Roaming\configRemote_PZ4\YEGPXJGHGKZZAQPHDPP\RttHlp.exe | C:\Users\admin\AppData\Roaming\configRemote_PZ4\YEGPXJGHGKZZAQPHDPP\RttHlp.exe | — | RttHlp.exe | |||||||||||
User: admin Company: IObit Integrity Level: MEDIUM Description: IObit RttHlp Exit code: 1 Version: 11.0.0.0 Modules
| |||||||||||||||
| 6468 | C:\WINDOWS\SysWOW64\explorer.exe | C:\Windows\SysWOW64\explorer.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 477
Read events
3 212
Write events
247
Delete events
18
Modification events
| (PID) Process: | (6708) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000430B2F04A263DB01341A00005C1A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6708) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000430B2F04A263DB01341A00005C1A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6708) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000DBCC7104A263DB01341A00005C1A0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6708) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000DBCC7104A263DB01341A00005C1A0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6708) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000AE317404A263DB01341A00005C1A0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6708) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000F6F87804A263DB01341A00005C1A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6708) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6708) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000E98FF204A263DB01341A00005C1A0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6708) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000FE59F704A263DB01341A0000DC1A0000E8030000010000000000000000000000381A058B1D2A894B9B6BD4D7C24F135600000000000000000000000000000000 | |||
| (PID) Process: | (6764) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000D7D50005A263DB016C1A0000001B0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
9
Suspicious files
26
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6708 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6708 | msiexec.exe | C:\Windows\Installer\13a1e1.msi | — | |
MD5:— | SHA256:— | |||
| 6708 | msiexec.exe | C:\Users\admin\AppData\Local\Yarrow\burro.ini | — | |
MD5:— | SHA256:— | |||
| 6708 | msiexec.exe | C:\Windows\Installer\13a1e3.msi | — | |
MD5:— | SHA256:— | |||
| 6708 | msiexec.exe | C:\Windows\Temp\~DF52FB1B4B3C40D9D6.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 6708 | msiexec.exe | C:\Windows\Installer\MSIA4EE.tmp | binary | |
MD5:09C68247F95AB19588CC942DDA010A3F | SHA256:4729D86BF9C0695014F5B23361CBFF674204692B0AE610A65E34F8E18BCD4767 | |||
| 6708 | msiexec.exe | C:\Config.Msi\13a1e2.rbs | binary | |
MD5:233259130B612FAFD6DE4DAB33A9D399 | SHA256:4A5186C856C23797C26E9B4A875D02630B8F4DAB31B6E58008F5846546848F4F | |||
| 6708 | msiexec.exe | C:\Windows\Temp\~DF89192A0AB44EC754.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 6708 | msiexec.exe | C:\Windows\Temp\~DFD53A321902CACDCE.TMP | binary | |
MD5:FCF7B4FF5F7AB0DD611416C7E29B7816 | SHA256:6C5991CC63F53F5789DB48DB0D381A045E27BA2845796D43C34ED7472696002C | |||
| 6708 | msiexec.exe | C:\Users\admin\AppData\Local\Yarrow\Register.dll | executable | |
MD5:40B9628354EF4E6EF3C87934575545F4 | SHA256:372B14FCE2EB35B264F6D4AEEF7987DA56D951D3A09EF866CF55ED72763CAA12 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
43
DNS requests
23
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.167:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6368 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6980 | explorer.exe | POST | 200 | 46.8.232.106:80 | http://46.8.232.106/ | unknown | — | — | malicious |
6856 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6856 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1684 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.167:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6980 | explorer.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
4 ETPRO signatures available at the full report