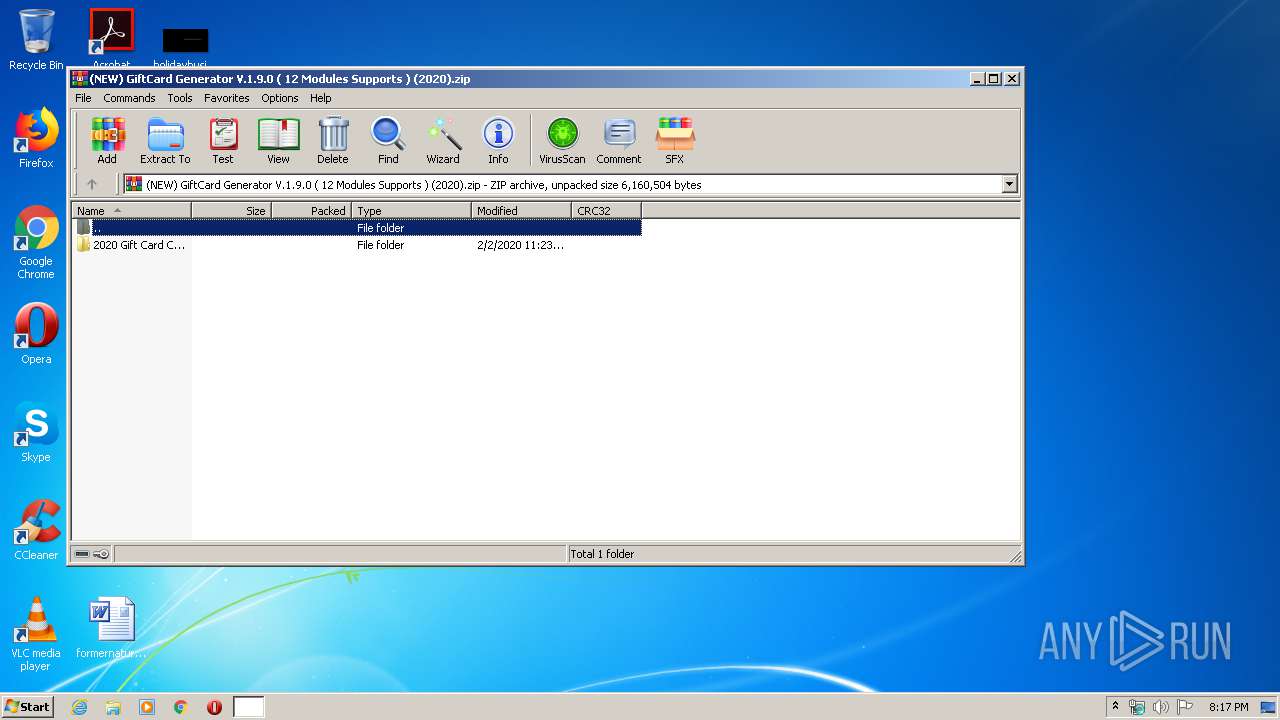
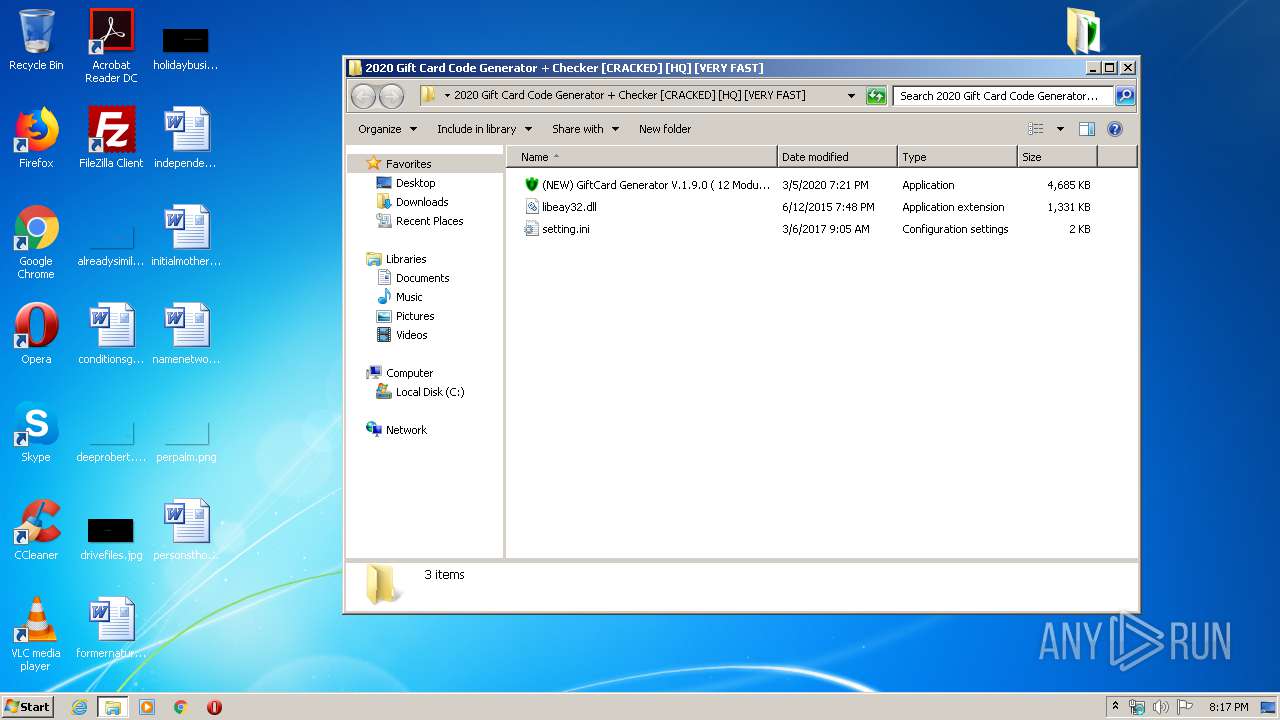
| File name: | (NEW) GiftCard Generator V.1.9.0 ( 12 Modules Supports ) (2020).zip |
| Full analysis: | https://app.any.run/tasks/e4b778bb-4444-47a7-a9a6-b58eda16e6c1 |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | March 06, 2020, 20:17:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 5CF2AF782B5FF35F116E26A5FAF885DF |
| SHA1: | D7D5EED168BBD82DE58A3345CEB8DC3C930F49F3 |
| SHA256: | CFE73AE21CD111E7CC6A812CA198CC37F0AB075FE9ABAE9BD12ACBA4E1F700AD |
| SSDEEP: | 12288:UjFIISzBmVDpCltx8ryV4dRWUb7nS+Y6690bNZ8yASt8c+ZWXCLg+G9iAUFlXPiH:YnSF8waHvrW9coTpZWEg+T9/OLQax |
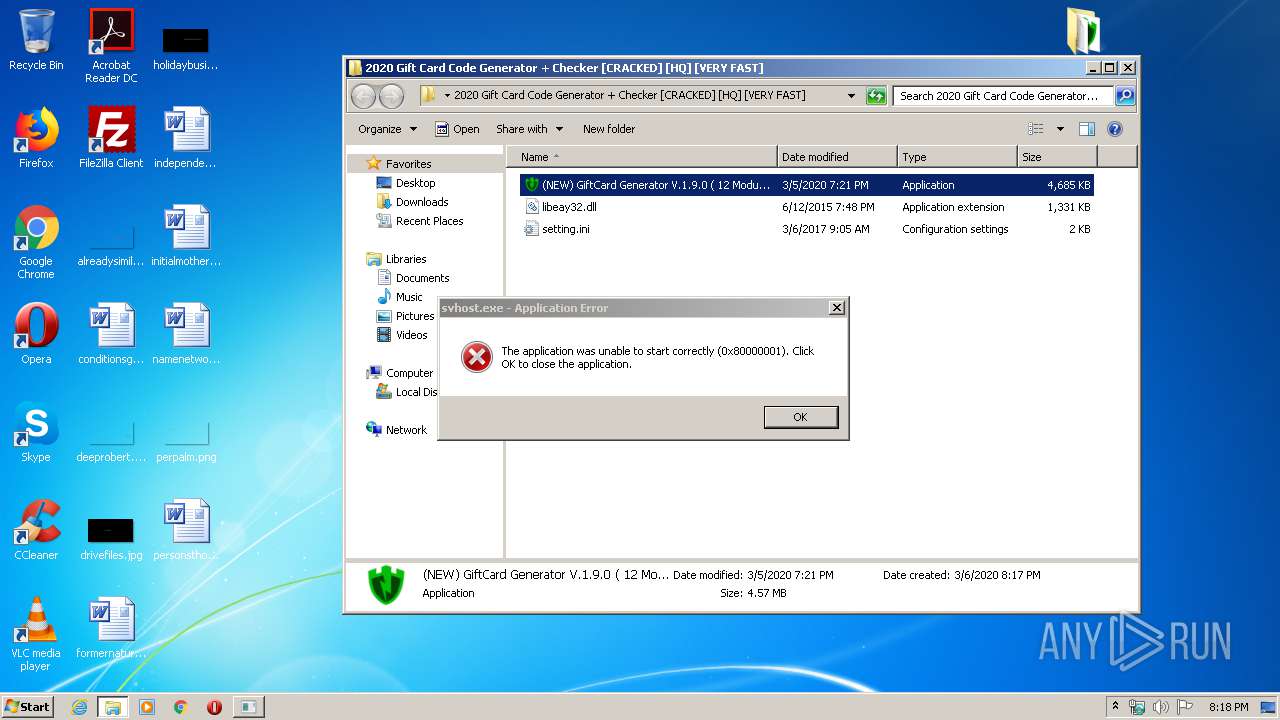
MALICIOUS
Application was dropped or rewritten from another process
- (NEW) GiftCard Generator V.1.9.0 ( 12 Modules Supports ) (2020).exe (PID: 3352)
- svhost.exe (PID: 3284)
- SafeFile.exe (PID: 1840)
- tmp.exe (PID: 3144)
- tmp.exe (PID: 3128)
- SafeFile.exe (PID: 1524)
- SafeFile.exe (PID: 3056)
- tmp.exe (PID: 564)
- tmp.exe (PID: 2676)
- SafeFile.exe (PID: 608)
- tmp.exe (PID: 2736)
- SafeFile.exe (PID: 2916)
- SafeFile.exe (PID: 3092)
- tmp.exe (PID: 1444)
- SafeFile.exe (PID: 2560)
- tmp.exe (PID: 2312)
- tmp.exe (PID: 3412)
- SafeFile.exe (PID: 3072)
- SafeFile.exe (PID: 3512)
- tmp.exe (PID: 1692)
- SafeFile.exe (PID: 3852)
- SafeFile.exe (PID: 3976)
- tmp.exe (PID: 2012)
- SafeFile.exe (PID: 2532)
- tmp.exe (PID: 3484)
- tmp.exe (PID: 1640)
- tmp.exe (PID: 2796)
- SafeFile.exe (PID: 3384)
- SafeFile.exe (PID: 3328)
- tmp.exe (PID: 3356)
- SafeFile.exe (PID: 2428)
- tmp.exe (PID: 3692)
- SafeFile.exe (PID: 3304)
- SafeFile.exe (PID: 3988)
- SafeFile.exe (PID: 2520)
- SafeFile.exe (PID: 4020)
- tmp.exe (PID: 2904)
- tmp.exe (PID: 604)
- tmp.exe (PID: 3676)
- SafeFile.exe (PID: 2376)
- SafeFile.exe (PID: 3468)
- tmp.exe (PID: 2956)
- tmp.exe (PID: 1688)
- SafeFile.exe (PID: 3832)
- SafeFile.exe (PID: 3308)
- SafeFile.exe (PID: 3040)
- SafeFile.exe (PID: 2336)
- tmp.exe (PID: 3172)
- tmp.exe (PID: 4060)
- SafeFile.exe (PID: 1828)
- tmp.exe (PID: 2516)
- SafeFile.exe (PID: 2480)
- tmp.exe (PID: 3956)
- tmp.exe (PID: 1832)
- tmp.exe (PID: 2212)
- SafeFile.exe (PID: 3192)
- tmp.exe (PID: 2276)
- SafeFile.exe (PID: 3996)
- SafeFile.exe (PID: 3824)
- SafeFile.exe (PID: 3500)
- tmp.exe (PID: 3204)
- SafeFile.exe (PID: 2356)
- SafeFile.exe (PID: 3196)
- tmp.exe (PID: 2508)
- tmp.exe (PID: 1760)
- SafeFile.exe (PID: 280)
- SafeFile.exe (PID: 3480)
- SafeFile.exe (PID: 2668)
- tmp.exe (PID: 3096)
- SafeFile.exe (PID: 2096)
- tmp.exe (PID: 2456)
- tmp.exe (PID: 2072)
- SafeFile.exe (PID: 3476)
- SafeFile.exe (PID: 1500)
- SafeFile.exe (PID: 2272)
- tmp.exe (PID: 3100)
- tmp.exe (PID: 3920)
- SafeFile.exe (PID: 3624)
- SafeFile.exe (PID: 3596)
- SafeFile.exe (PID: 2556)
- SafeFile.exe (PID: 2720)
- tmp.exe (PID: 1800)
- tmp.exe (PID: 3324)
- SafeFile.exe (PID: 1744)
- SafeFile.exe (PID: 2156)
- tmp.exe (PID: 3860)
- tmp.exe (PID: 2704)
- tmp.exe (PID: 2688)
- SafeFile.exe (PID: 3360)
- tmp.exe (PID: 3008)
- SafeFile.exe (PID: 628)
- SafeFile.exe (PID: 1748)
- tmp.exe (PID: 4184)
- SafeFile.exe (PID: 3032)
- tmp.exe (PID: 4588)
- SafeFile.exe (PID: 4332)
- SafeFile.exe (PID: 3612)
- SafeFile.exe (PID: 5060)
- SafeFile.exe (PID: 6096)
- tmp.exe (PID: 4944)
- tmp.exe (PID: 5672)
- SafeFile.exe (PID: 5012)
- SafeFile.exe (PID: 5300)
- tmp.exe (PID: 4508)
- tmp.exe (PID: 5888)
- tmp.exe (PID: 5412)
- tmp.exe (PID: 6068)
- SafeFile.exe (PID: 5652)
- tmp.exe (PID: 3436)
- SafeFile.exe (PID: 4660)
- tmp.exe (PID: 4168)
- tmp.exe (PID: 1916)
- SafeFile.exe (PID: 4684)
- SafeFile.exe (PID: 5400)
- SafeFile.exe (PID: 4108)
- SafeFile.exe (PID: 5660)
- SafeFile.exe (PID: 4720)
- tmp.exe (PID: 5572)
- SafeFile.exe (PID: 5688)
- tmp.exe (PID: 4908)
- SafeFile.exe (PID: 4804)
- SafeFile.exe (PID: 5736)
- SafeFile.exe (PID: 4692)
- tmp.exe (PID: 6132)
- tmp.exe (PID: 5680)
- SafeFile.exe (PID: 5260)
- tmp.exe (PID: 4408)
- SafeFile.exe (PID: 4964)
- SafeFile.exe (PID: 5604)
- tmp.exe (PID: 5900)
- tmp.exe (PID: 5460)
- tmp.exe (PID: 5476)
- SafeFile.exe (PID: 4796)
- SafeFile.exe (PID: 4812)
- tmp.exe (PID: 4160)
- tmp.exe (PID: 4900)
- tmp.exe (PID: 2784)
- tmp.exe (PID: 1792)
- tmp.exe (PID: 3752)
- SafeFile.exe (PID: 4556)
- SafeFile.exe (PID: 5108)
- SafeFile.exe (PID: 3924)
- tmp.exe (PID: 2888)
- tmp.exe (PID: 4344)
- SafeFile.exe (PID: 180)
- tmp.exe (PID: 4928)
- tmp.exe (PID: 3528)
- tmp.exe (PID: 5684)
- tmp.exe (PID: 1944)
- tmp.exe (PID: 4832)
- tmp.exe (PID: 5304)
- tmp.exe (PID: 4564)
- tmp.exe (PID: 4424)
- tmp.exe (PID: 4116)
- tmp.exe (PID: 4456)
- tmp.exe (PID: 3760)
- tmp.exe (PID: 5140)
- tmp.exe (PID: 5780)
- tmp.exe (PID: 1508)
- tmp.exe (PID: 4976)
- tmp.exe (PID: 5368)
- tmp.exe (PID: 5608)
- tmp.exe (PID: 3060)
- tmp.exe (PID: 6044)
- tmp.exe (PID: 4784)
- tmp.exe (PID: 4860)
- tmp.exe (PID: 7172)
- tmp.exe (PID: 6152)
- tmp.exe (PID: 6644)
- tmp.exe (PID: 7156)
- tmp.exe (PID: 7092)
- tmp.exe (PID: 8068)
- tmp.exe (PID: 7980)
- tmp.exe (PID: 8172)
- tmp.exe (PID: 7032)
- tmp.exe (PID: 7752)
- tmp.exe (PID: 6512)
- tmp.exe (PID: 3572)
- tmp.exe (PID: 7040)
- tmp.exe (PID: 7280)
- tmp.exe (PID: 6808)
- tmp.exe (PID: 7016)
- tmp.exe (PID: 6244)
- tmp.exe (PID: 7612)
- tmp.exe (PID: 4952)
- tmp.exe (PID: 8068)
- tmp.exe (PID: 7388)
- tmp.exe (PID: 6280)
- tmp.exe (PID: 7608)
- tmp.exe (PID: 7504)
- tmp.exe (PID: 5748)
- tmp.exe (PID: 7064)
- tmp.exe (PID: 6220)
- tmp.exe (PID: 6600)
- tmp.exe (PID: 7396)
- tmp.exe (PID: 6336)
- tmp.exe (PID: 2744)
Changes the autorun value in the registry
- reg.exe (PID: 2724)
- tmp.exe (PID: 3144)
AVEMARIA was detected
- tmp.exe (PID: 3144)
- SafeFile.exe (PID: 1840)
- SafeFile.exe (PID: 3056)
- tmp.exe (PID: 564)
- SafeFile.exe (PID: 608)
- SafeFile.exe (PID: 3092)
- tmp.exe (PID: 1444)
- SafeFile.exe (PID: 2560)
- SafeFile.exe (PID: 3512)
- SafeFile.exe (PID: 3976)
- tmp.exe (PID: 2012)
- SafeFile.exe (PID: 2532)
- tmp.exe (PID: 1640)
- SafeFile.exe (PID: 3384)
- SafeFile.exe (PID: 3328)
- SafeFile.exe (PID: 3304)
- tmp.exe (PID: 3692)
- SafeFile.exe (PID: 4020)
- tmp.exe (PID: 3676)
- tmp.exe (PID: 604)
- SafeFile.exe (PID: 3468)
- SafeFile.exe (PID: 2376)
- SafeFile.exe (PID: 2336)
- tmp.exe (PID: 3172)
- SafeFile.exe (PID: 2480)
- SafeFile.exe (PID: 3192)
- SafeFile.exe (PID: 3824)
- tmp.exe (PID: 3204)
- SafeFile.exe (PID: 3500)
- SafeFile.exe (PID: 3196)
- tmp.exe (PID: 1760)
- SafeFile.exe (PID: 3480)
- SafeFile.exe (PID: 2096)
- tmp.exe (PID: 3096)
- SafeFile.exe (PID: 3476)
- SafeFile.exe (PID: 2272)
- tmp.exe (PID: 3920)
- SafeFile.exe (PID: 1500)
- SafeFile.exe (PID: 2556)
- SafeFile.exe (PID: 3360)
- tmp.exe (PID: 3008)
- SafeFile.exe (PID: 1744)
- SafeFile.exe (PID: 2156)
- tmp.exe (PID: 2704)
- tmp.exe (PID: 2688)
- SafeFile.exe (PID: 628)
- SafeFile.exe (PID: 3032)
- SafeFile.exe (PID: 1748)
- tmp.exe (PID: 4588)
- tmp.exe (PID: 4944)
- SafeFile.exe (PID: 5060)
- SafeFile.exe (PID: 6096)
- tmp.exe (PID: 5672)
- SafeFile.exe (PID: 5012)
- SafeFile.exe (PID: 4108)
- SafeFile.exe (PID: 4660)
- tmp.exe (PID: 3436)
- tmp.exe (PID: 4168)
- tmp.exe (PID: 1916)
- SafeFile.exe (PID: 5660)
- SafeFile.exe (PID: 5688)
- SafeFile.exe (PID: 4720)
- tmp.exe (PID: 5572)
- tmp.exe (PID: 4908)
- SafeFile.exe (PID: 5736)
- SafeFile.exe (PID: 4964)
- SafeFile.exe (PID: 4692)
- SafeFile.exe (PID: 5260)
- tmp.exe (PID: 4408)
- SafeFile.exe (PID: 4812)
- SafeFile.exe (PID: 5604)
- SafeFile.exe (PID: 4796)
- tmp.exe (PID: 3752)
- tmp.exe (PID: 1792)
- tmp.exe (PID: 2784)
- SafeFile.exe (PID: 4556)
- SafeFile.exe (PID: 5108)
- SafeFile.exe (PID: 3924)
- tmp.exe (PID: 2888)
- SafeFile.exe (PID: 180)
- tmp.exe (PID: 4928)
- tmp.exe (PID: 3528)
- tmp.exe (PID: 4344)
- tmp.exe (PID: 4424)
- tmp.exe (PID: 4116)
- tmp.exe (PID: 4456)
- tmp.exe (PID: 4564)
- tmp.exe (PID: 1508)
- tmp.exe (PID: 5140)
- tmp.exe (PID: 3060)
- tmp.exe (PID: 6044)
- tmp.exe (PID: 5608)
- tmp.exe (PID: 5368)
- tmp.exe (PID: 4784)
- tmp.exe (PID: 6512)
- tmp.exe (PID: 7032)
- tmp.exe (PID: 7040)
- tmp.exe (PID: 8172)
- tmp.exe (PID: 7280)
- tmp.exe (PID: 7752)
- tmp.exe (PID: 7612)
- tmp.exe (PID: 6280)
- tmp.exe (PID: 7388)
- tmp.exe (PID: 7608)
- tmp.exe (PID: 5748)
- tmp.exe (PID: 7064)
- tmp.exe (PID: 7504)
Runs app for hidden code execution
- tmp.exe (PID: 3144)
- SafeFile.exe (PID: 3056)
- tmp.exe (PID: 564)
- SafeFile.exe (PID: 1840)
- SafeFile.exe (PID: 608)
- SafeFile.exe (PID: 3092)
- SafeFile.exe (PID: 2560)
- tmp.exe (PID: 1444)
- SafeFile.exe (PID: 3512)
- SafeFile.exe (PID: 3976)
- tmp.exe (PID: 2012)
- SafeFile.exe (PID: 2532)
- tmp.exe (PID: 1640)
- SafeFile.exe (PID: 3384)
- SafeFile.exe (PID: 3328)
- tmp.exe (PID: 3692)
- SafeFile.exe (PID: 3304)
- SafeFile.exe (PID: 4020)
- tmp.exe (PID: 3676)
- tmp.exe (PID: 604)
- SafeFile.exe (PID: 3468)
- SafeFile.exe (PID: 2376)
- SafeFile.exe (PID: 2336)
- tmp.exe (PID: 3172)
- SafeFile.exe (PID: 3192)
- SafeFile.exe (PID: 2480)
- SafeFile.exe (PID: 3824)
- SafeFile.exe (PID: 3500)
- tmp.exe (PID: 3204)
- SafeFile.exe (PID: 3196)
- tmp.exe (PID: 1760)
- SafeFile.exe (PID: 3480)
- SafeFile.exe (PID: 2096)
- tmp.exe (PID: 3096)
- SafeFile.exe (PID: 2272)
- SafeFile.exe (PID: 3476)
- SafeFile.exe (PID: 1500)
- tmp.exe (PID: 3920)
- SafeFile.exe (PID: 2556)
- SafeFile.exe (PID: 3360)
- tmp.exe (PID: 3008)
- SafeFile.exe (PID: 1744)
- SafeFile.exe (PID: 2156)
- tmp.exe (PID: 2704)
- tmp.exe (PID: 2688)
- SafeFile.exe (PID: 628)
- SafeFile.exe (PID: 1748)
- SafeFile.exe (PID: 3032)
- tmp.exe (PID: 4588)
- SafeFile.exe (PID: 5060)
- SafeFile.exe (PID: 6096)
- tmp.exe (PID: 4944)
- SafeFile.exe (PID: 5012)
- tmp.exe (PID: 5672)
- SafeFile.exe (PID: 4108)
- SafeFile.exe (PID: 4660)
- tmp.exe (PID: 3436)
- tmp.exe (PID: 4168)
- SafeFile.exe (PID: 5660)
- SafeFile.exe (PID: 5688)
- SafeFile.exe (PID: 4720)
- tmp.exe (PID: 1916)
- tmp.exe (PID: 5572)
- tmp.exe (PID: 4908)
- SafeFile.exe (PID: 5736)
- SafeFile.exe (PID: 4692)
- SafeFile.exe (PID: 4964)
- SafeFile.exe (PID: 5260)
- tmp.exe (PID: 4408)
- SafeFile.exe (PID: 4812)
- SafeFile.exe (PID: 5604)
- SafeFile.exe (PID: 4796)
- tmp.exe (PID: 2784)
- tmp.exe (PID: 3752)
- tmp.exe (PID: 1792)
- SafeFile.exe (PID: 4556)
- SafeFile.exe (PID: 5108)
- SafeFile.exe (PID: 3924)
- tmp.exe (PID: 4344)
- tmp.exe (PID: 2888)
- SafeFile.exe (PID: 180)
- tmp.exe (PID: 4928)
- tmp.exe (PID: 3528)
- tmp.exe (PID: 4424)
- tmp.exe (PID: 4456)
- tmp.exe (PID: 4564)
- tmp.exe (PID: 4116)
- tmp.exe (PID: 1508)
- tmp.exe (PID: 5140)
- tmp.exe (PID: 5608)
- tmp.exe (PID: 3060)
- tmp.exe (PID: 6044)
- tmp.exe (PID: 4784)
- tmp.exe (PID: 5368)
- tmp.exe (PID: 6512)
- tmp.exe (PID: 7032)
- tmp.exe (PID: 7040)
- tmp.exe (PID: 8172)
- tmp.exe (PID: 7752)
- tmp.exe (PID: 7280)
- tmp.exe (PID: 7612)
- tmp.exe (PID: 6280)
- tmp.exe (PID: 7608)
- tmp.exe (PID: 5748)
- tmp.exe (PID: 7388)
- tmp.exe (PID: 7504)
- tmp.exe (PID: 7064)
Runs injected code in another process
- SafeFile.exe (PID: 1840)
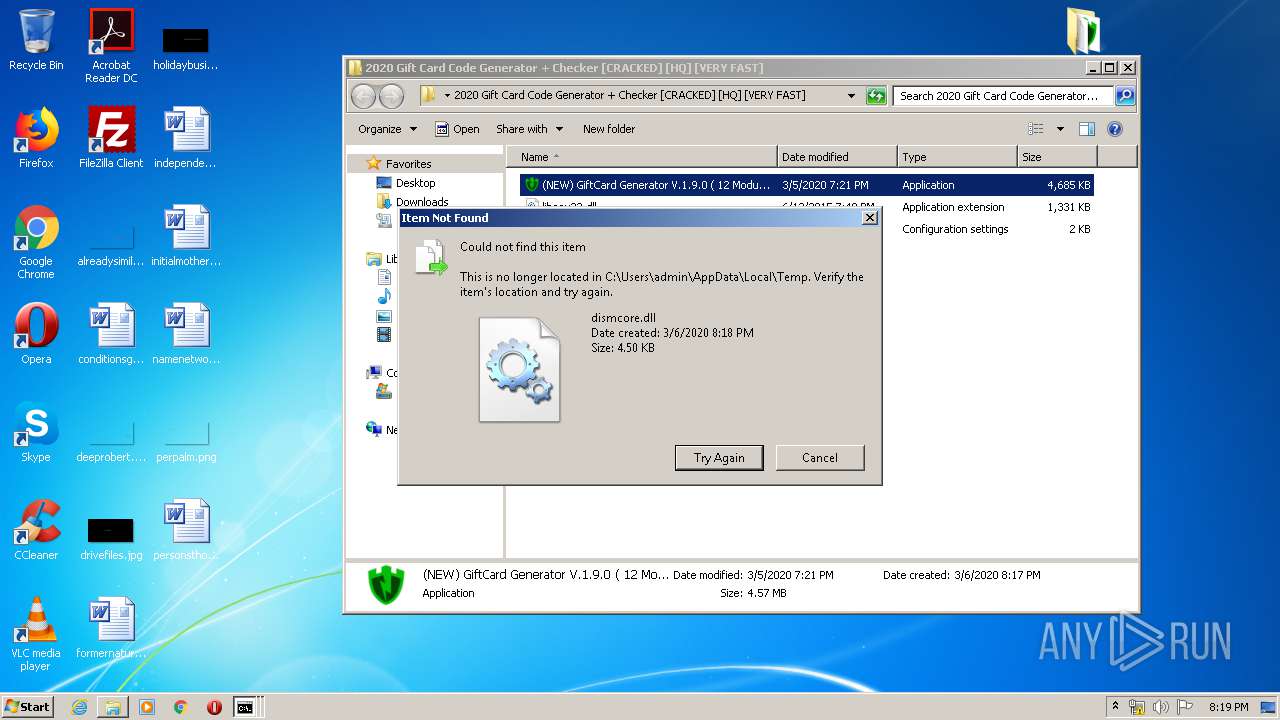
Loads dropped or rewritten executable
- dism.exe (PID: 4068)
- dism.exe (PID: 3760)
- dism.exe (PID: 2376)
- dism.exe (PID: 984)
- dism.exe (PID: 3576)
- dism.exe (PID: 3420)
- dism.exe (PID: 1488)
- dism.exe (PID: 2288)
- dism.exe (PID: 2276)
- dism.exe (PID: 2352)
- dism.exe (PID: 2428)
- dism.exe (PID: 3064)
- dism.exe (PID: 2880)
- dism.exe (PID: 2616)
- dism.exe (PID: 2152)
- dism.exe (PID: 4012)
- dism.exe (PID: 1348)
- dism.exe (PID: 3884)
- dism.exe (PID: 2464)
- dism.exe (PID: 2896)
- dism.exe (PID: 3368)
- dism.exe (PID: 1916)
- dism.exe (PID: 2760)
- dism.exe (PID: 2392)
- dism.exe (PID: 3016)
- dism.exe (PID: 2148)
- dism.exe (PID: 3016)
- dism.exe (PID: 3360)
- dism.exe (PID: 3712)
- dism.exe (PID: 3064)
- dism.exe (PID: 1844)
- dism.exe (PID: 1720)
- dism.exe (PID: 3344)
- dism.exe (PID: 6096)
- dism.exe (PID: 4260)
- dism.exe (PID: 916)
- dism.exe (PID: 4620)
- dism.exe (PID: 4784)
- dism.exe (PID: 5396)
- dism.exe (PID: 2800)
- dism.exe (PID: 4164)
- dism.exe (PID: 4516)
- dism.exe (PID: 4388)
- dism.exe (PID: 2492)
- dism.exe (PID: 5052)
- dism.exe (PID: 5428)
- dism.exe (PID: 4308)
- dism.exe (PID: 5984)
- dism.exe (PID: 4192)
- dism.exe (PID: 6048)
- dism.exe (PID: 664)
- dism.exe (PID: 4540)
- dism.exe (PID: 6056)
- dism.exe (PID: 5528)
- dism.exe (PID: 6708)
- dism.exe (PID: 6236)
- dism.exe (PID: 8164)
- dism.exe (PID: 6252)
- dism.exe (PID: 7484)
- dism.exe (PID: 7144)
- dism.exe (PID: 6492)
- dism.exe (PID: 7344)
- dism.exe (PID: 6648)
Application was injected by another process
- explorer.exe (PID: 372)
SUSPICIOUS
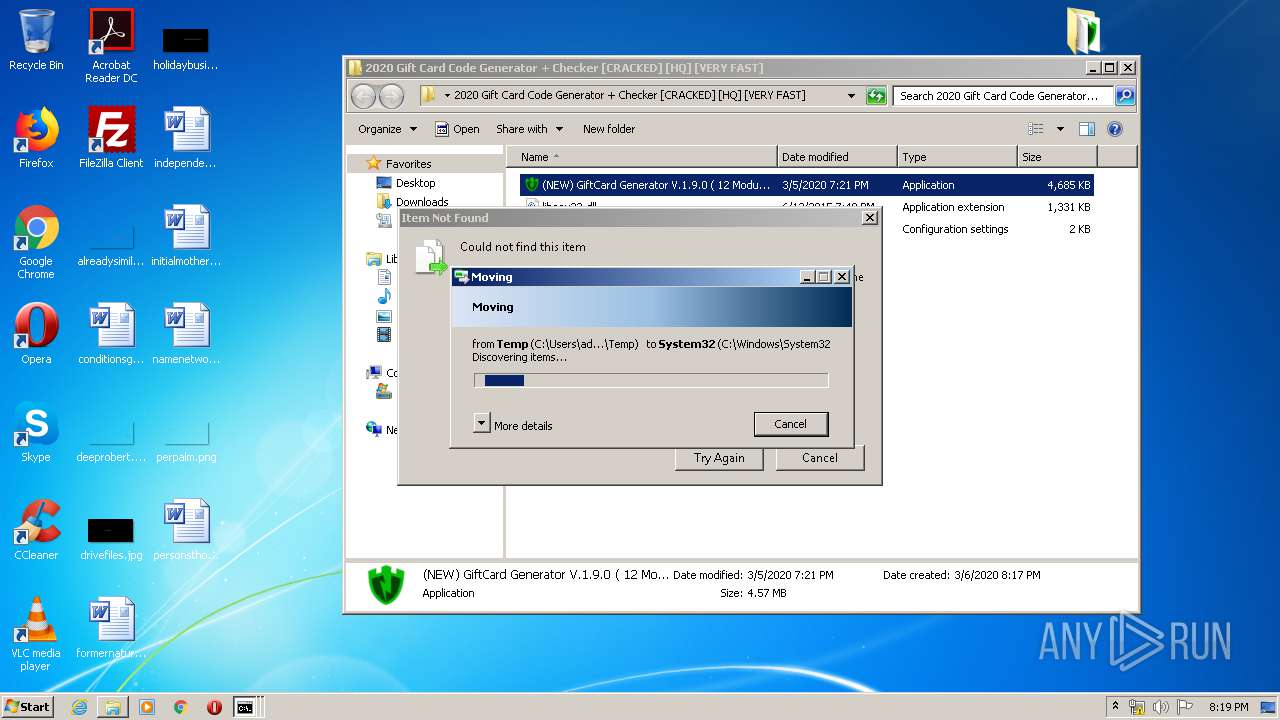
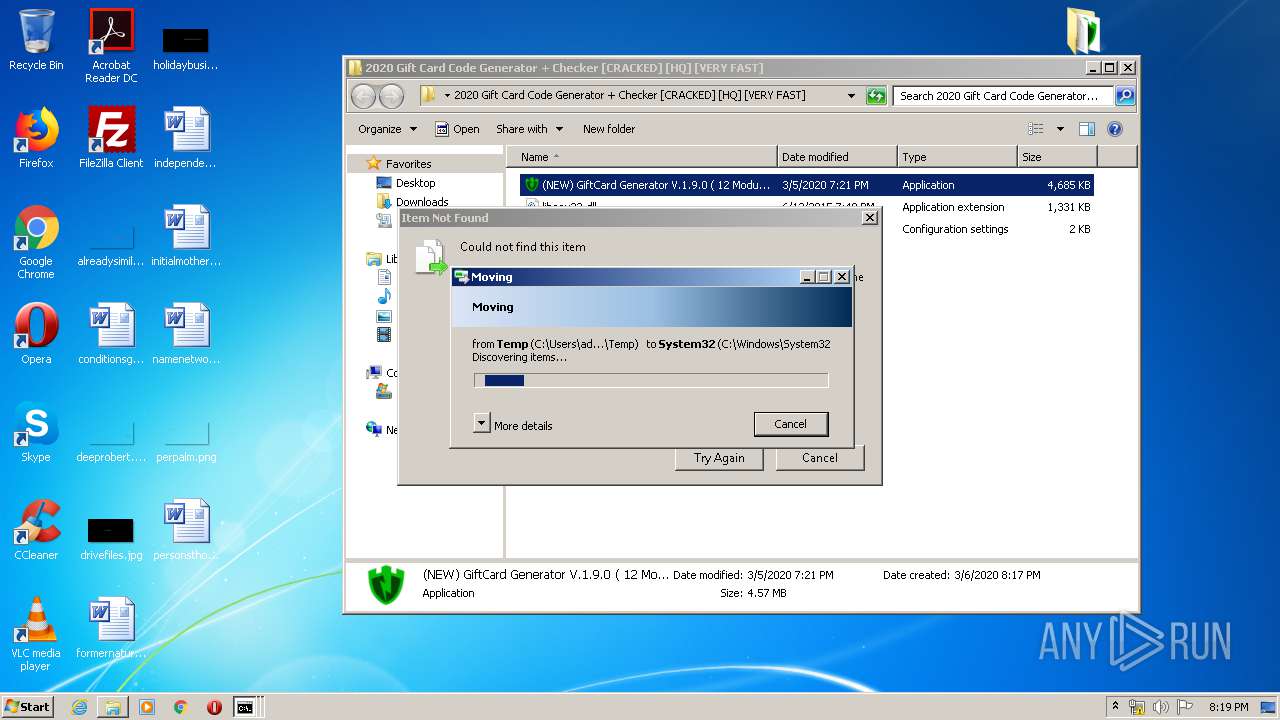
Executable content was dropped or overwritten
- cmd.exe (PID: 3968)
- tmp.exe (PID: 3144)
- (NEW) GiftCard Generator V.1.9.0 ( 12 Modules Supports ) (2020).exe (PID: 3352)
- cmd.exe (PID: 3232)
- DllHost.exe (PID: 3960)
- cmd.exe (PID: 2788)
- cmd.exe (PID: 3772)
- DllHost.exe (PID: 3804)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 3516)
- cmd.exe (PID: 1920)
- DllHost.exe (PID: 2672)
- cmd.exe (PID: 2244)
- cmd.exe (PID: 2216)
- cmd.exe (PID: 3556)
- cmd.exe (PID: 2600)
- DllHost.exe (PID: 3104)
- cmd.exe (PID: 3168)
- cmd.exe (PID: 1332)
- cmd.exe (PID: 3088)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 3260)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 1028)
- cmd.exe (PID: 4048)
- cmd.exe (PID: 2940)
- cmd.exe (PID: 3756)
- cmd.exe (PID: 3592)
- cmd.exe (PID: 3964)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 2452)
- cmd.exe (PID: 3616)
- cmd.exe (PID: 2632)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 2972)
- cmd.exe (PID: 880)
- cmd.exe (PID: 2284)
- cmd.exe (PID: 3948)
- cmd.exe (PID: 2412)
- cmd.exe (PID: 2712)
- cmd.exe (PID: 3636)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 3320)
- cmd.exe (PID: 3424)
- cmd.exe (PID: 3744)
- cmd.exe (PID: 2808)
- cmd.exe (PID: 2148)
- cmd.exe (PID: 3980)
- cmd.exe (PID: 3300)
- cmd.exe (PID: 2308)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 5916)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 6120)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 5336)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 6112)
- cmd.exe (PID: 480)
- cmd.exe (PID: 5264)
- cmd.exe (PID: 5076)
- cmd.exe (PID: 3112)
- cmd.exe (PID: 2836)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 5332)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 4728)
- cmd.exe (PID: 6036)
- cmd.exe (PID: 5124)
- cmd.exe (PID: 4772)
- cmd.exe (PID: 5912)
- cmd.exe (PID: 4180)
- cmd.exe (PID: 5496)
- cmd.exe (PID: 4980)
- cmd.exe (PID: 5732)
- cmd.exe (PID: 5704)
- cmd.exe (PID: 5024)
- cmd.exe (PID: 5616)
- cmd.exe (PID: 5164)
- cmd.exe (PID: 5320)
- cmd.exe (PID: 5764)
- cmd.exe (PID: 5476)
- cmd.exe (PID: 4552)
- cmd.exe (PID: 4732)
- cmd.exe (PID: 4284)
- cmd.exe (PID: 5192)
- cmd.exe (PID: 3380)
- cmd.exe (PID: 4236)
- cmd.exe (PID: 6056)
- cmd.exe (PID: 4876)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 7104)
- cmd.exe (PID: 7500)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 4848)
- cmd.exe (PID: 8012)
- cmd.exe (PID: 7484)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 6784)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1156)
Creates files in the user directory
- (NEW) GiftCard Generator V.1.9.0 ( 12 Modules Supports ) (2020).exe (PID: 3352)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 1348)
- tmp.exe (PID: 3144)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 304)
- powershell.exe (PID: 2664)
- powershell.exe (PID: 1812)
- powershell.exe (PID: 3600)
- powershell.exe (PID: 3316)
- powershell.exe (PID: 2420)
- powershell.exe (PID: 548)
- powershell.exe (PID: 3432)
- powershell.exe (PID: 376)
- powershell.exe (PID: 1468)
- powershell.exe (PID: 3588)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 3084)
- powershell.exe (PID: 3200)
- powershell.exe (PID: 3336)
- powershell.exe (PID: 2112)
- powershell.exe (PID: 3544)
- powershell.exe (PID: 2636)
- powershell.exe (PID: 2768)
- powershell.exe (PID: 1196)
- powershell.exe (PID: 3848)
- powershell.exe (PID: 748)
- powershell.exe (PID: 4056)
- powershell.exe (PID: 3276)
- powershell.exe (PID: 5064)
- powershell.exe (PID: 4464)
- powershell.exe (PID: 5576)
- powershell.exe (PID: 5236)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 5540)
- powershell.exe (PID: 5700)
- powershell.exe (PID: 4792)
- powershell.exe (PID: 5928)
- powershell.exe (PID: 4496)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 6860)
- powershell.exe (PID: 8084)
- powershell.exe (PID: 6352)
- powershell.exe (PID: 7912)
- powershell.exe (PID: 6788)
Starts CMD.EXE for commands execution
- (NEW) GiftCard Generator V.1.9.0 ( 12 Modules Supports ) (2020).exe (PID: 3352)
- tmp.exe (PID: 3144)
- SafeFile.exe (PID: 1840)
- SafeFile.exe (PID: 3056)
- tmp.exe (PID: 564)
- SafeFile.exe (PID: 608)
- SafeFile.exe (PID: 3092)
- tmp.exe (PID: 1444)
- SafeFile.exe (PID: 2560)
- SafeFile.exe (PID: 3512)
- SafeFile.exe (PID: 3976)
- tmp.exe (PID: 2012)
- SafeFile.exe (PID: 2532)
- tmp.exe (PID: 1640)
- SafeFile.exe (PID: 3384)
- SafeFile.exe (PID: 3328)
- SafeFile.exe (PID: 3304)
- tmp.exe (PID: 3692)
- SafeFile.exe (PID: 4020)
- tmp.exe (PID: 3676)
- tmp.exe (PID: 604)
- SafeFile.exe (PID: 2376)
- SafeFile.exe (PID: 3468)
- tmp.exe (PID: 3172)
- SafeFile.exe (PID: 2336)
- SafeFile.exe (PID: 3192)
- SafeFile.exe (PID: 2480)
- SafeFile.exe (PID: 3824)
- SafeFile.exe (PID: 3500)
- tmp.exe (PID: 3204)
- SafeFile.exe (PID: 3196)
- tmp.exe (PID: 1760)
- SafeFile.exe (PID: 3480)
- SafeFile.exe (PID: 2096)
- tmp.exe (PID: 3096)
- SafeFile.exe (PID: 2272)
- SafeFile.exe (PID: 3476)
- SafeFile.exe (PID: 1500)
- tmp.exe (PID: 3920)
- SafeFile.exe (PID: 2556)
- tmp.exe (PID: 3008)
- SafeFile.exe (PID: 3360)
- SafeFile.exe (PID: 1744)
- SafeFile.exe (PID: 2156)
- tmp.exe (PID: 2704)
- tmp.exe (PID: 2688)
- SafeFile.exe (PID: 628)
- SafeFile.exe (PID: 1748)
- SafeFile.exe (PID: 3032)
- tmp.exe (PID: 4588)
- tmp.exe (PID: 4944)
- SafeFile.exe (PID: 5060)
- SafeFile.exe (PID: 6096)
- tmp.exe (PID: 5672)
- SafeFile.exe (PID: 5012)
- SafeFile.exe (PID: 4108)
- tmp.exe (PID: 3436)
- tmp.exe (PID: 4168)
- SafeFile.exe (PID: 4660)
- SafeFile.exe (PID: 5660)
- SafeFile.exe (PID: 5688)
- SafeFile.exe (PID: 4720)
- tmp.exe (PID: 1916)
- tmp.exe (PID: 5572)
- tmp.exe (PID: 4908)
- SafeFile.exe (PID: 5736)
- SafeFile.exe (PID: 4692)
- SafeFile.exe (PID: 4964)
- SafeFile.exe (PID: 5260)
- tmp.exe (PID: 4408)
- SafeFile.exe (PID: 5604)
- SafeFile.exe (PID: 4796)
- SafeFile.exe (PID: 4812)
- tmp.exe (PID: 2784)
- tmp.exe (PID: 1792)
- tmp.exe (PID: 3752)
- SafeFile.exe (PID: 4556)
- SafeFile.exe (PID: 5108)
- SafeFile.exe (PID: 3924)
- tmp.exe (PID: 2888)
- tmp.exe (PID: 4344)
- tmp.exe (PID: 4928)
- SafeFile.exe (PID: 180)
- tmp.exe (PID: 3528)
- tmp.exe (PID: 4424)
- tmp.exe (PID: 4116)
- tmp.exe (PID: 4456)
- tmp.exe (PID: 4564)
- tmp.exe (PID: 1508)
- tmp.exe (PID: 5140)
- tmp.exe (PID: 5608)
- tmp.exe (PID: 3060)
- tmp.exe (PID: 6044)
- tmp.exe (PID: 4784)
- tmp.exe (PID: 5368)
- tmp.exe (PID: 6512)
- tmp.exe (PID: 7040)
- tmp.exe (PID: 7032)
- tmp.exe (PID: 8172)
- tmp.exe (PID: 7280)
- tmp.exe (PID: 7752)
- tmp.exe (PID: 7612)
- tmp.exe (PID: 6280)
- tmp.exe (PID: 7608)
- tmp.exe (PID: 5748)
- tmp.exe (PID: 7388)
- tmp.exe (PID: 7504)
- tmp.exe (PID: 7064)
Starts itself from another location
- tmp.exe (PID: 3144)
Executed via COM
- DllHost.exe (PID: 3960)
- DllHost.exe (PID: 3804)
- DllHost.exe (PID: 2672)
- DllHost.exe (PID: 3104)
Connects to unusual port
- SafeFile.exe (PID: 1840)
- tmp.exe (PID: 3128)
- SafeFile.exe (PID: 1524)
- SafeFile.exe (PID: 3056)
- tmp.exe (PID: 564)
- SafeFile.exe (PID: 608)
- tmp.exe (PID: 2736)
- SafeFile.exe (PID: 2916)
- SafeFile.exe (PID: 3092)
- tmp.exe (PID: 1444)
- SafeFile.exe (PID: 2560)
- SafeFile.exe (PID: 3512)
- tmp.exe (PID: 2312)
- SafeFile.exe (PID: 3072)
- SafeFile.exe (PID: 3852)
- SafeFile.exe (PID: 3976)
- tmp.exe (PID: 2012)
- SafeFile.exe (PID: 2532)
- tmp.exe (PID: 3484)
- SafeFile.exe (PID: 3384)
- tmp.exe (PID: 1640)
- SafeFile.exe (PID: 3328)
- tmp.exe (PID: 3356)
- SafeFile.exe (PID: 2520)
- SafeFile.exe (PID: 3304)
- tmp.exe (PID: 3692)
- SafeFile.exe (PID: 3988)
- SafeFile.exe (PID: 4020)
- tmp.exe (PID: 2904)
- tmp.exe (PID: 604)
- tmp.exe (PID: 3676)
- SafeFile.exe (PID: 2376)
- tmp.exe (PID: 1688)
- SafeFile.exe (PID: 1828)
- SafeFile.exe (PID: 2336)
- SafeFile.exe (PID: 3468)
- tmp.exe (PID: 3172)
- SafeFile.exe (PID: 3192)
- SafeFile.exe (PID: 2480)
- SafeFile.exe (PID: 3996)
- SafeFile.exe (PID: 3500)
- SafeFile.exe (PID: 3824)
- tmp.exe (PID: 2212)
- tmp.exe (PID: 3204)
- SafeFile.exe (PID: 3196)
- tmp.exe (PID: 2508)
- SafeFile.exe (PID: 2356)
- tmp.exe (PID: 1760)
- SafeFile.exe (PID: 280)
- SafeFile.exe (PID: 3480)
- SafeFile.exe (PID: 2096)
- tmp.exe (PID: 2456)
- tmp.exe (PID: 3096)
- SafeFile.exe (PID: 3476)
- SafeFile.exe (PID: 1500)
- tmp.exe (PID: 3100)
- SafeFile.exe (PID: 2272)
- SafeFile.exe (PID: 3596)
- tmp.exe (PID: 3920)
- SafeFile.exe (PID: 2556)
- tmp.exe (PID: 3324)
- SafeFile.exe (PID: 2720)
- SafeFile.exe (PID: 3360)
- tmp.exe (PID: 3008)
- SafeFile.exe (PID: 2156)
- tmp.exe (PID: 3860)
- tmp.exe (PID: 2704)
- SafeFile.exe (PID: 1744)
- tmp.exe (PID: 2688)
- SafeFile.exe (PID: 628)
- SafeFile.exe (PID: 1748)
- tmp.exe (PID: 4588)
- SafeFile.exe (PID: 3032)
- tmp.exe (PID: 4184)
- SafeFile.exe (PID: 3612)
- SafeFile.exe (PID: 5060)
- SafeFile.exe (PID: 4332)
- tmp.exe (PID: 4944)
- tmp.exe (PID: 5672)
- SafeFile.exe (PID: 6096)
- tmp.exe (PID: 6068)
- SafeFile.exe (PID: 4108)
- SafeFile.exe (PID: 4660)
- SafeFile.exe (PID: 5652)
- tmp.exe (PID: 4168)
- tmp.exe (PID: 1916)
- tmp.exe (PID: 3436)
- SafeFile.exe (PID: 5660)
- SafeFile.exe (PID: 4720)
- tmp.exe (PID: 4908)
- tmp.exe (PID: 5572)
- SafeFile.exe (PID: 5688)
- SafeFile.exe (PID: 5736)
- SafeFile.exe (PID: 4804)
- SafeFile.exe (PID: 4692)
- tmp.exe (PID: 5680)
- SafeFile.exe (PID: 4964)
- SafeFile.exe (PID: 5260)
- tmp.exe (PID: 4408)
- SafeFile.exe (PID: 4812)
- SafeFile.exe (PID: 5604)
- SafeFile.exe (PID: 4796)
- tmp.exe (PID: 4160)
- tmp.exe (PID: 3752)
- tmp.exe (PID: 1792)
- tmp.exe (PID: 2784)
- SafeFile.exe (PID: 3924)
- tmp.exe (PID: 2888)
- SafeFile.exe (PID: 4556)
- SafeFile.exe (PID: 5108)
- tmp.exe (PID: 4928)
- tmp.exe (PID: 4344)
- SafeFile.exe (PID: 180)
- tmp.exe (PID: 3528)
- tmp.exe (PID: 4564)
- tmp.exe (PID: 5304)
- tmp.exe (PID: 1508)
- tmp.exe (PID: 5140)
- tmp.exe (PID: 4976)
- tmp.exe (PID: 5608)
- tmp.exe (PID: 3060)
- tmp.exe (PID: 6044)
- tmp.exe (PID: 4784)
- tmp.exe (PID: 7092)
- tmp.exe (PID: 3572)
- tmp.exe (PID: 4424)
- tmp.exe (PID: 4116)
- tmp.exe (PID: 4456)
- tmp.exe (PID: 3760)
- tmp.exe (PID: 5368)
- tmp.exe (PID: 6512)
- tmp.exe (PID: 7280)
- tmp.exe (PID: 6808)
- tmp.exe (PID: 7504)
- tmp.exe (PID: 7016)
- tmp.exe (PID: 7388)
- tmp.exe (PID: 8068)
- tmp.exe (PID: 7608)
- tmp.exe (PID: 5748)
- tmp.exe (PID: 7064)
- tmp.exe (PID: 8172)
- tmp.exe (PID: 7032)
- tmp.exe (PID: 7040)
- tmp.exe (PID: 7752)
- tmp.exe (PID: 7612)
- tmp.exe (PID: 6280)
Executes PowerShell scripts
- tmp.exe (PID: 3128)
- SafeFile.exe (PID: 1524)
- tmp.exe (PID: 2736)
- SafeFile.exe (PID: 2916)
- tmp.exe (PID: 2312)
- SafeFile.exe (PID: 3072)
- SafeFile.exe (PID: 3852)
- tmp.exe (PID: 3484)
- tmp.exe (PID: 3356)
- SafeFile.exe (PID: 2520)
- SafeFile.exe (PID: 3988)
- tmp.exe (PID: 2904)
- tmp.exe (PID: 1688)
- SafeFile.exe (PID: 1828)
- SafeFile.exe (PID: 3996)
- tmp.exe (PID: 2212)
- SafeFile.exe (PID: 2356)
- tmp.exe (PID: 2508)
- SafeFile.exe (PID: 280)
- tmp.exe (PID: 2456)
- tmp.exe (PID: 3100)
- tmp.exe (PID: 3324)
- SafeFile.exe (PID: 3596)
- SafeFile.exe (PID: 2720)
- tmp.exe (PID: 3860)
- tmp.exe (PID: 4184)
- SafeFile.exe (PID: 3612)
- SafeFile.exe (PID: 4332)
- tmp.exe (PID: 6068)
- SafeFile.exe (PID: 5652)
- SafeFile.exe (PID: 4804)
- tmp.exe (PID: 5680)
- tmp.exe (PID: 4160)
- tmp.exe (PID: 5304)
- tmp.exe (PID: 3760)
- tmp.exe (PID: 4976)
- tmp.exe (PID: 7092)
- tmp.exe (PID: 3572)
- tmp.exe (PID: 6808)
- tmp.exe (PID: 8068)
- tmp.exe (PID: 7016)
INFO
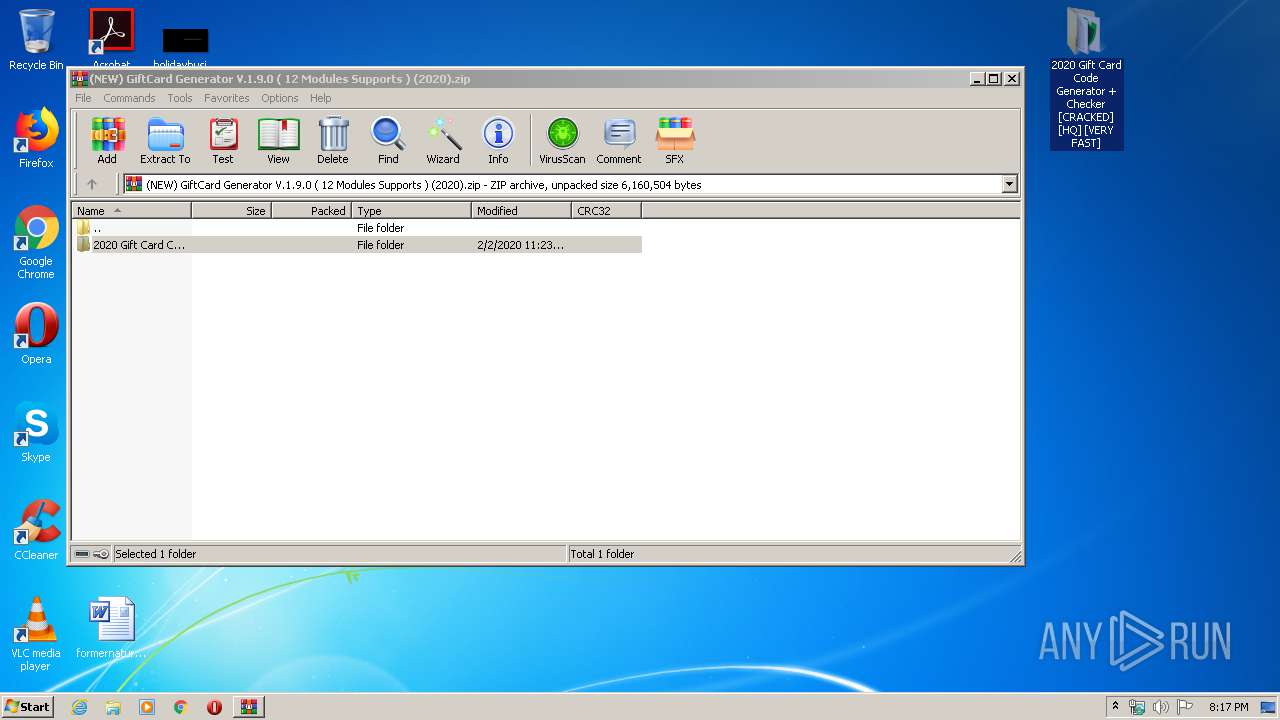
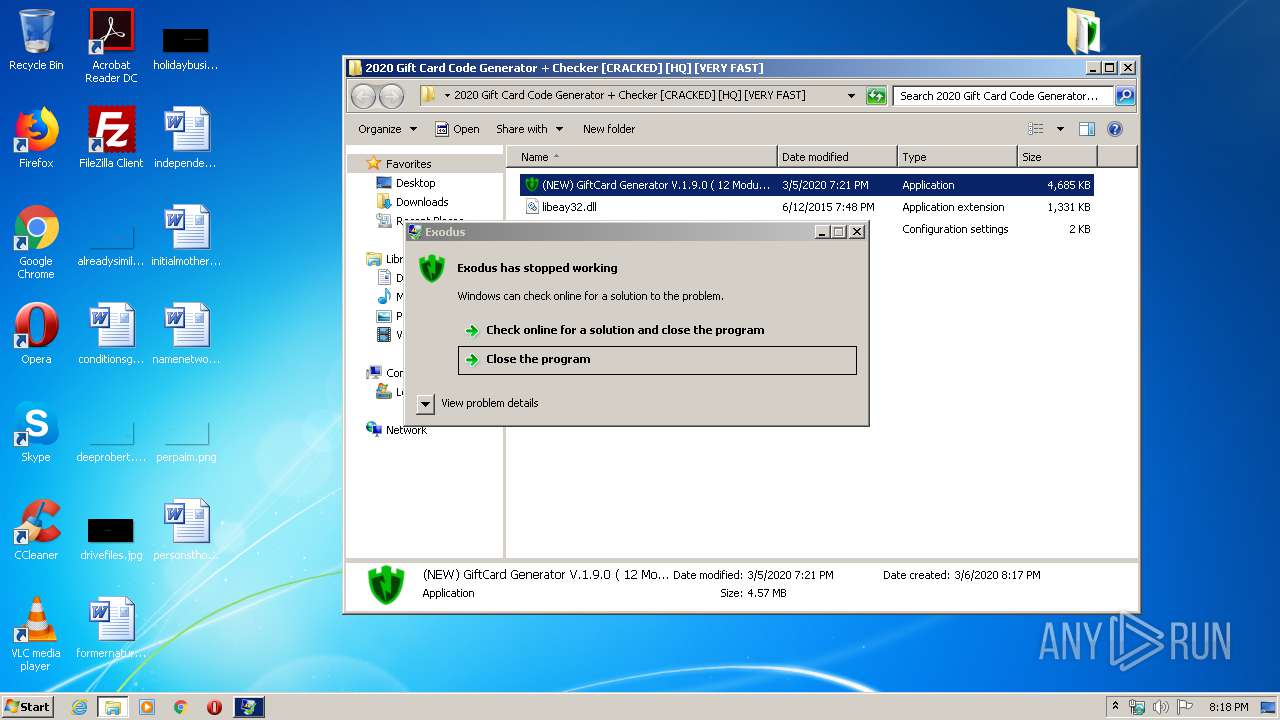
Manual execution by user
- (NEW) GiftCard Generator V.1.9.0 ( 12 Modules Supports ) (2020).exe (PID: 3352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:02:03 07:23:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
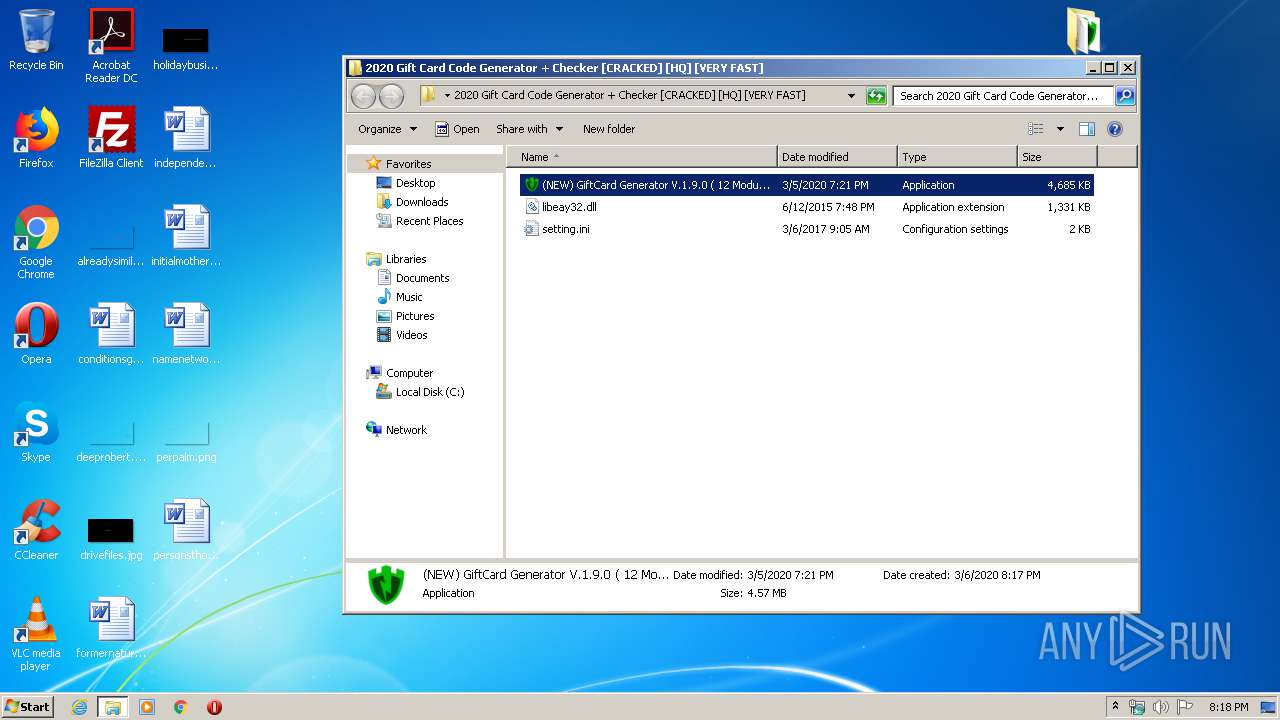
| ZipFileName: | 2020 Gift Card Code Generator + Checker [CRACKED] [HQ] [VERY FAST]/ |
Total processes
873
Monitored processes
545
Malicious processes
109
Suspicious processes
63
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Users\admin\AppData\Roaming\SafeFile.exe" | C:\Users\admin\AppData\Roaming\SafeFile.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 280 | "C:\Users\admin\AppData\Roaming\SafeFile.exe" | C:\Users\admin\AppData\Roaming\SafeFile.exe | dism.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 304 | powershell Add-MpPreference -ExclusionPath C:\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | SafeFile.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 348 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Package Manager Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 348 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | powershell Add-MpPreference -ExclusionPath C:\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | SafeFile.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 480 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | SafeFile.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 548 | powershell Add-MpPreference -ExclusionPath C:\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | tmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 564 | "C:\Users\admin\AppData\Roaming\tmp.exe" | C:\Users\admin\AppData\Roaming\tmp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
49 789
Read events
46 670
Write events
3 119
Delete events
0
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2564) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\(NEW) GiftCard Generator V.1.9.0 ( 12 Modules Supports ) (2020).zip | |||
| (PID) Process: | (2564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
102
Suspicious files
76
Text files
159
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2564.37376\2020 Gift Card Code Generator + Checker [CRACKED] [HQ] [VERY FAST]\libeay32.dll | — | |
MD5:— | SHA256:— | |||
| 2564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2564.37376\2020 Gift Card Code Generator + Checker [CRACKED] [HQ] [VERY FAST]\setting.ini | — | |
MD5:— | SHA256:— | |||
| 2564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2564.37376\2020 Gift Card Code Generator + Checker [CRACKED] [HQ] [VERY FAST]\(NEW) GiftCard Generator V.1.9.0 ( 12 Modules Supports ) (2020).exe | — | |
MD5:— | SHA256:— | |||
| 372 | explorer.exe | C:\Users\admin\Desktop\2020 Gift Card Code Generator + Checker [CRACKED] [HQ] [VERY FAST] | — | |
MD5:— | SHA256:— | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Y2BYMPY6VH921SWYKZ60.temp | — | |
MD5:— | SHA256:— | |||
| 304 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JKMO5J2M15LJBJ9RBGQT.temp | — | |
MD5:— | SHA256:— | |||
| 2420 | pkgmgr.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:— | SHA256:— | |||
| 304 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3968 | cmd.exe | C:\Users\admin\AppData\Roaming\FolderN\SafeFile.exe | executable | |
MD5:— | SHA256:— | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
234
DNS requests
13
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3056 | SafeFile.exe | 185.140.53.245:5200 | u868328.nvpn.so | myLoc managed IT AG | DE | malicious |
3128 | tmp.exe | 185.140.53.245:5200 | u868328.nvpn.so | myLoc managed IT AG | DE | malicious |
1840 | SafeFile.exe | 185.140.53.245:5200 | u868328.nvpn.so | myLoc managed IT AG | DE | malicious |
1524 | SafeFile.exe | 185.140.53.245:5200 | u868328.nvpn.so | myLoc managed IT AG | DE | malicious |
2736 | tmp.exe | 185.140.53.245:5200 | u868328.nvpn.so | myLoc managed IT AG | DE | malicious |
2916 | SafeFile.exe | 185.140.53.245:5200 | u868328.nvpn.so | myLoc managed IT AG | DE | malicious |
3092 | SafeFile.exe | 185.140.53.245:5200 | u868328.nvpn.so | myLoc managed IT AG | DE | malicious |
2560 | SafeFile.exe | 185.140.53.245:5200 | u868328.nvpn.so | myLoc managed IT AG | DE | malicious |
1444 | tmp.exe | 185.140.53.245:5200 | u868328.nvpn.so | myLoc managed IT AG | DE | malicious |
2312 | tmp.exe | 185.140.53.245:5200 | u868328.nvpn.so | myLoc managed IT AG | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
u868328.nvpn.so |
| unknown |
dns.msftncsi.com |
| shared |